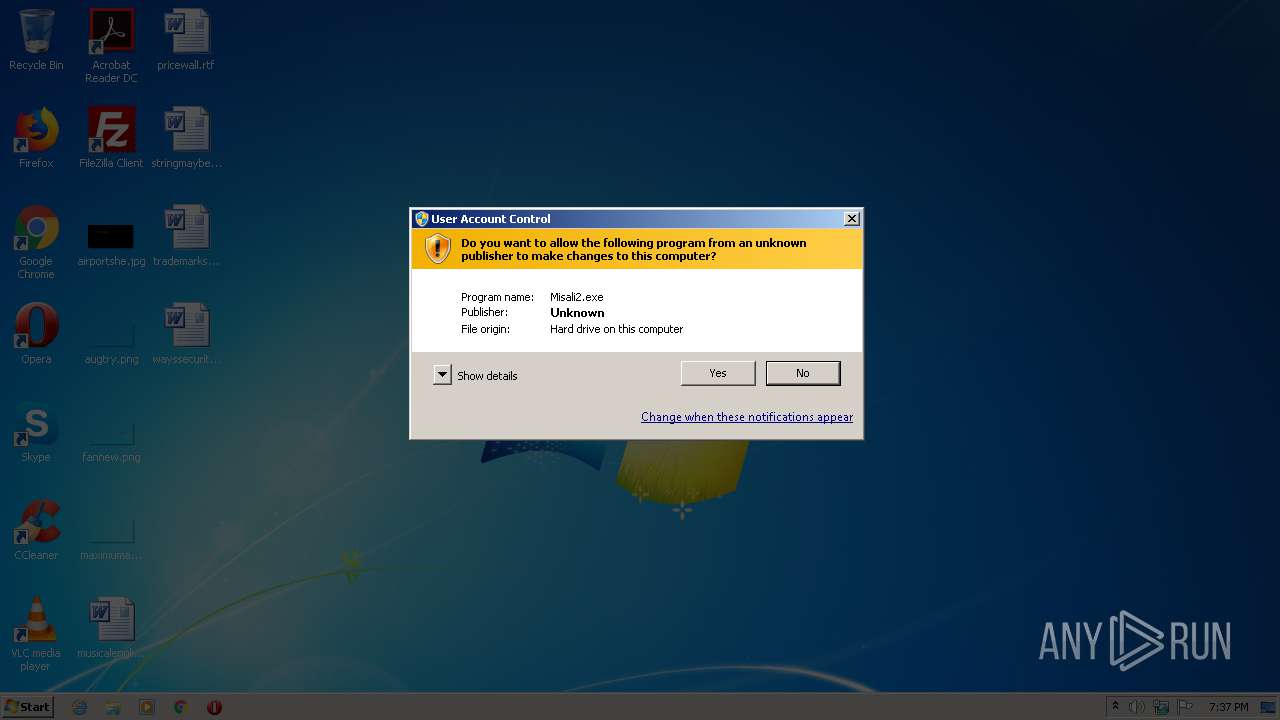
| File name: | Misali2.exe |
| Full analysis: | https://app.any.run/tasks/b475bf7e-df12-48a9-9db0-6f8de24ec89d |
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2021, 18:37:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3610647641C2955FBB8CBDDB2E26BC24 |
| SHA1: | 0F3797EEBF2C92AC086F585083CF5B1910E17691 |
| SHA256: | 99C24A257852F7C45267CDFBBF8FE6D96CE9B547F5FD621D9DBD22A4AD713B78 |
| SSDEEP: | 98304:+5KfRSJ1OK2Lvq9tr/Qpm9OeAN3iAuEZ5NufYFcwMOdOLm:6Kf0J1OK2LY/9ANT5aKxT |
MALICIOUS
Changes settings of System certificates
- Misali2.exe (PID: 1076)
SUSPICIOUS
Application launched itself
- Misali2.exe (PID: 1440)
Creates files in the user directory
- Misali2.exe (PID: 1076)
Reads internet explorer settings
- Misali2.exe (PID: 1076)
Adds / modifies Windows certificates
- Misali2.exe (PID: 1076)
INFO
Dropped object may contain TOR URL's
- Misali2.exe (PID: 1076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| ProductVersion: | 1, 0, 0, 1 |
|---|---|
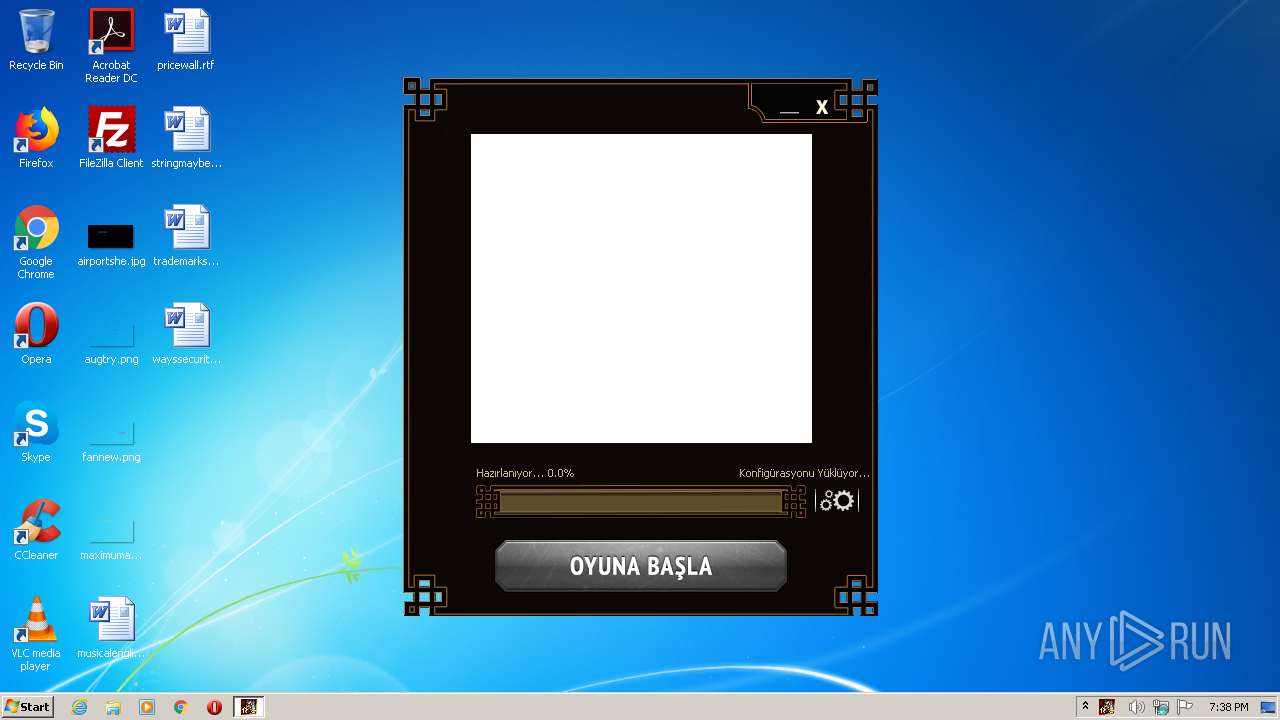
| ProductName: | Metin2 Patcher |
| OriginalFileName: | metin2_patcher.exe |
| LegalCopyright: | Copyright (C) 2011 |
| InternalName: | metin2_patcher |
| FileVersion: | 1.0.44037.1 |
| FileDescription: | Metin2 Patcher |
| CharacterSet: | Unicode |
| LanguageCode: | Korean |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0017 |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.44037.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x1bb45f |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1245184 |
| CodeSize: | 2335232 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2014:06:26 12:05:15+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jun-2014 10:05:15 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| FileDescription: | Metin2 Patcher |
| FileVersion: | 1.0.44037.1 |
| InternalName: | metin2_patcher |
| LegalCopyright: | Copyright (C) 2011 |
| OriginalFilename: | metin2_patcher.exe |
| ProductName: | Metin2 Patcher |
| ProductVersion: | 1, 0, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 26-Jun-2014 10:05:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0023A00A | 0x0023A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63917 |
.rdata | 0x0023C000 | 0x0009D5F2 | 0x0009D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06154 |
.data | 0x002DA000 | 0x000482DC | 0x00019A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.53388 |
.tls | 0x00323000 | 0x00000002 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.SHARED | 0x00324000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00325000 | 0x000020E4 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.99402 |
.reloc | 0x00328000 | 0x00047EF4 | 0x00048000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.718 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.35118 | 692 | UNKNOWN | Korean - Korea | RT_VERSION |
2 | 3.90768 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 4.11949 | 3752 | UNKNOWN | English - United States | RT_ICON |
101 | 2.36401 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
MSWSOCK.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
Total processes
41
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | "C:\Users\admin\AppData\Local\Temp\Misali2.exe" | C:\Users\admin\AppData\Local\Temp\Misali2.exe | Misali2.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Metin2 Patcher Exit code: 0 Version: 1.0.44037.1 Modules
| |||||||||||||||
| 1440 | "C:\Users\admin\AppData\Local\Temp\Misali2.exe" | C:\Users\admin\AppData\Local\Temp\Misali2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Metin2 Patcher Exit code: 4294967295 Version: 1.0.44037.1 Modules
| |||||||||||||||
Total events
528
Read events
504
Write events
24
Delete events
0
Modification events
| (PID) Process: | (1440) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1440) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1076) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1076) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1076) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1076) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1076) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1076) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1076) Misali2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1076) Misali2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
4
Text files
43
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1076 | Misali2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\metin2torrent.config[1].xml | — | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\crclist[1] | — | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\Local\Temp\CabB56.tmp | — | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\Local\Temp\TarB57.tmp | — | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\KNltneez6RY[1].css | text | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\AVW91ONJ.txt | text | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DDEDF268117918D1D277A171D8DF7B_2685E00BE4AE5CA73CAE5513FF0886E2 | binary | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\169976960_2383495455128619_3871316603718227084_n[1].jpg | image | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_2685E00BE4AE5CA73CAE5513FF0886E2 | der | |
MD5:— | SHA256:— | |||
| 1076 | Misali2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\sdk[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
11
DNS requests
7
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1076 | Misali2.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAGpGO85yE2IjS7H9cUAMYU%3D | US | der | 471 b | whitelisted |
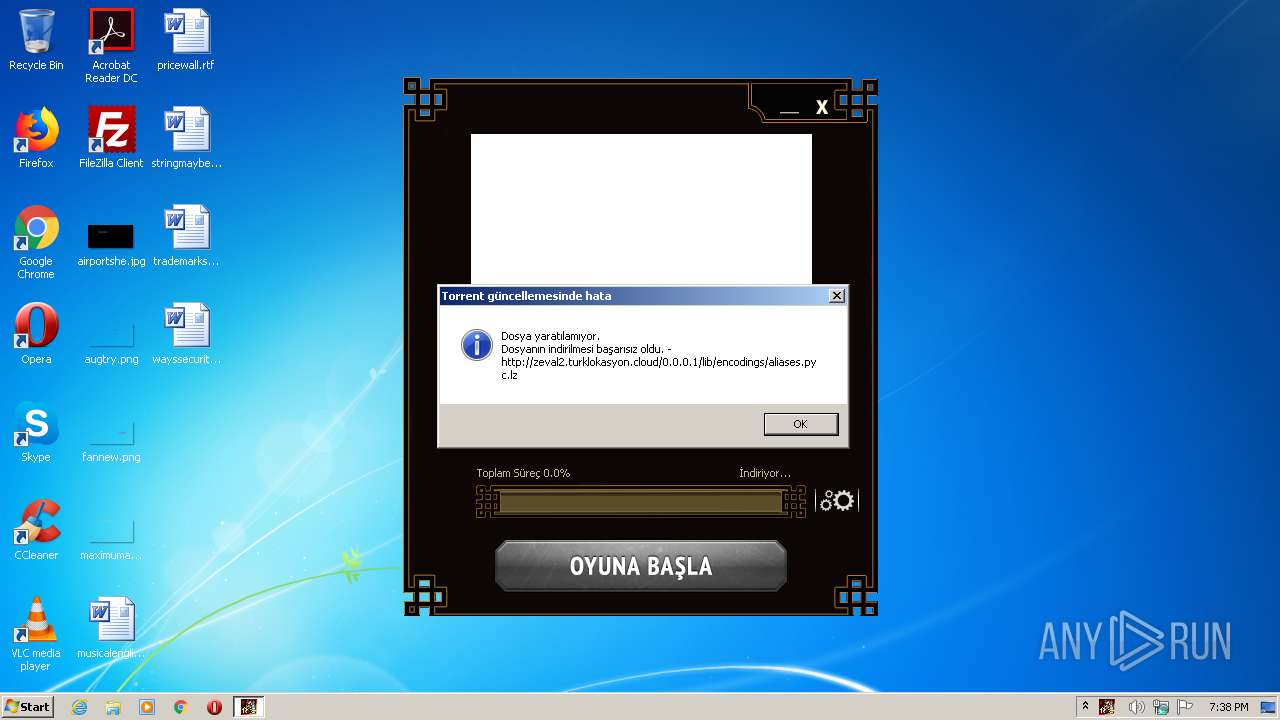
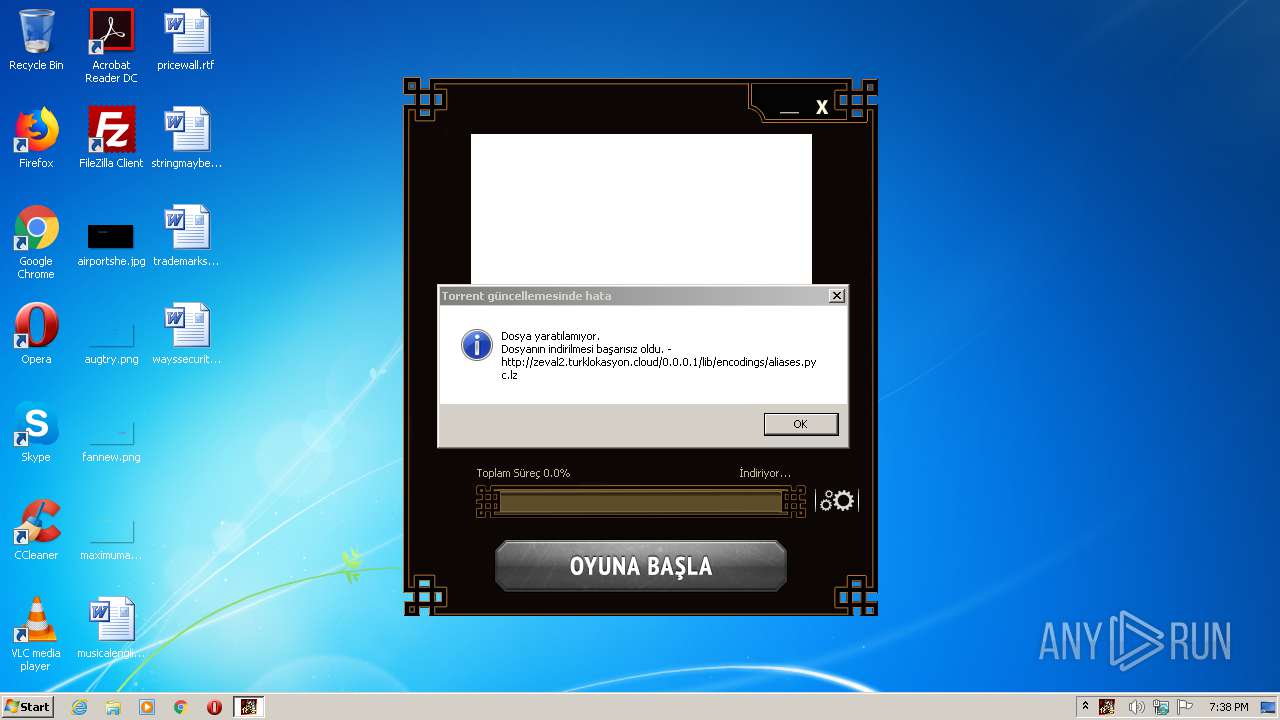
1076 | Misali2.exe | GET | 200 | 104.21.7.132:80 | http://zeval2.turklokasyon.cloud/0.0.0.1/crclist | US | text | 17.0 Kb | suspicious |
1076 | Misali2.exe | GET | 200 | 185.59.220.198:80 | http://patchx0llq.misali2.com/metin2torrent.config.xml | DE | text | 521 b | suspicious |
1076 | Misali2.exe | GET | 200 | 104.21.7.132:80 | http://zeval2.turklokasyon.cloud/0.0.0.1/lib/encodings/aliases.pyc.lz | US | binary | 5.52 Kb | suspicious |
1076 | Misali2.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1076 | Misali2.exe | GET | 200 | 185.59.220.198:80 | http://patchx0llq.misali2.com/ | DE | html | 670 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | Misali2.exe | 185.59.220.198:80 | patchx0llq.misali2.com | Datacamp Limited | DE | suspicious |
1076 | Misali2.exe | 104.21.7.132:80 | zeval2.turklokasyon.cloud | Cloudflare Inc | US | suspicious |
1076 | Misali2.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1076 | Misali2.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
1076 | Misali2.exe | 31.13.92.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
1076 | Misali2.exe | 185.60.217.28:443 | scontent-ber1-1.xx.fbcdn.net | Facebook, Inc. | IE | unknown |
1076 | Misali2.exe | 31.13.92.14:443 | static.xx.fbcdn.net | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
patchx0llq.misali2.com |
| suspicious |
zeval2.turklokasyon.cloud |
| suspicious |
connect.facebook.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.facebook.com |
| whitelisted |
static.xx.fbcdn.net |
| whitelisted |
scontent-ber1-1.xx.fbcdn.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1076 | Misali2.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
1076 | Misali2.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |