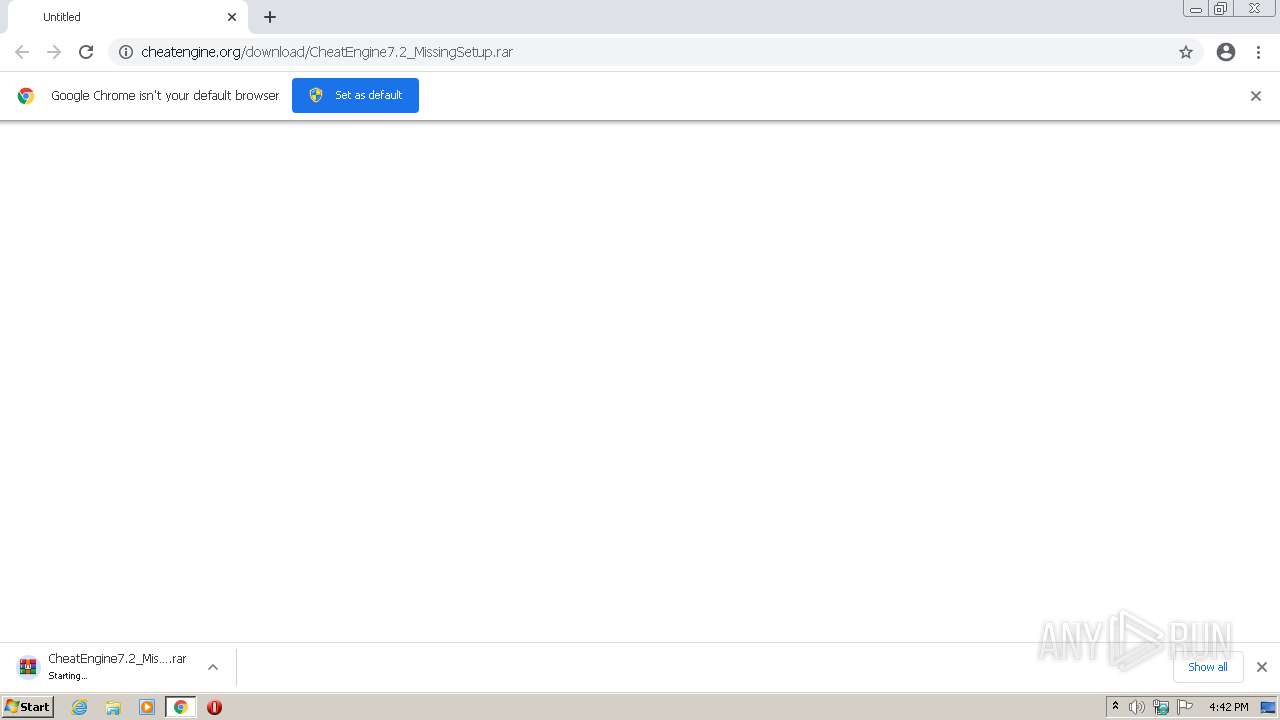
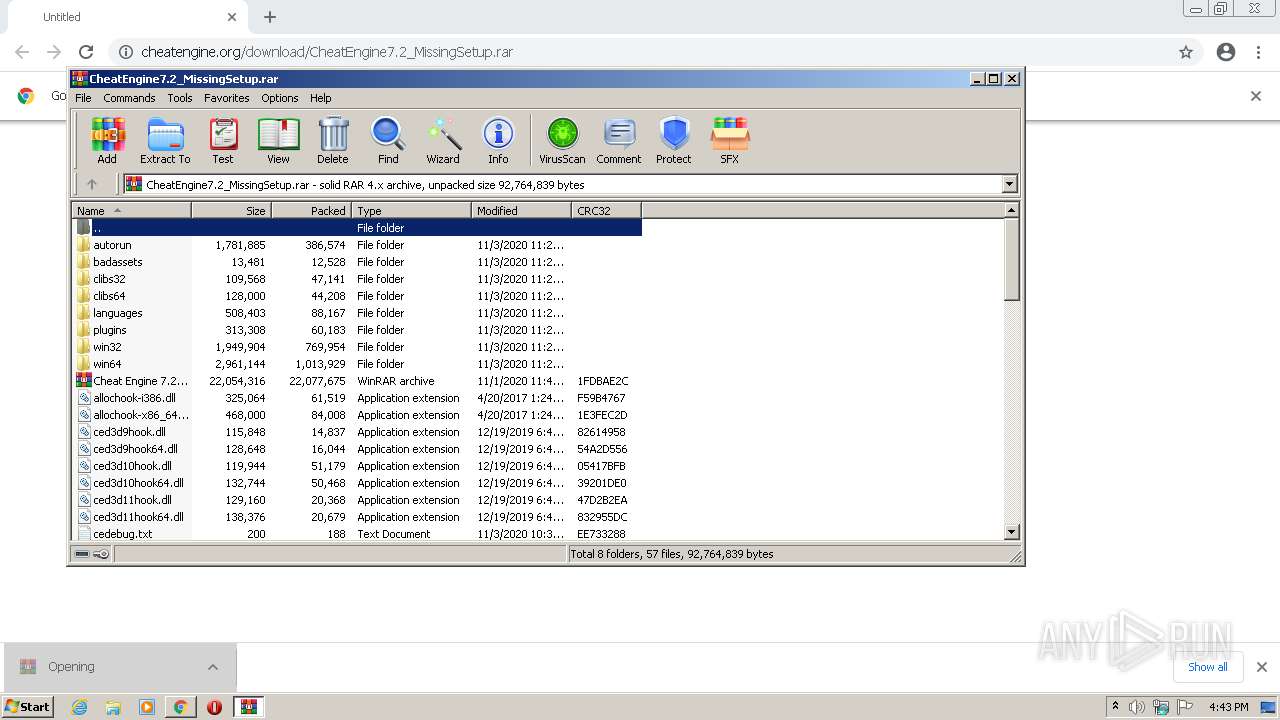
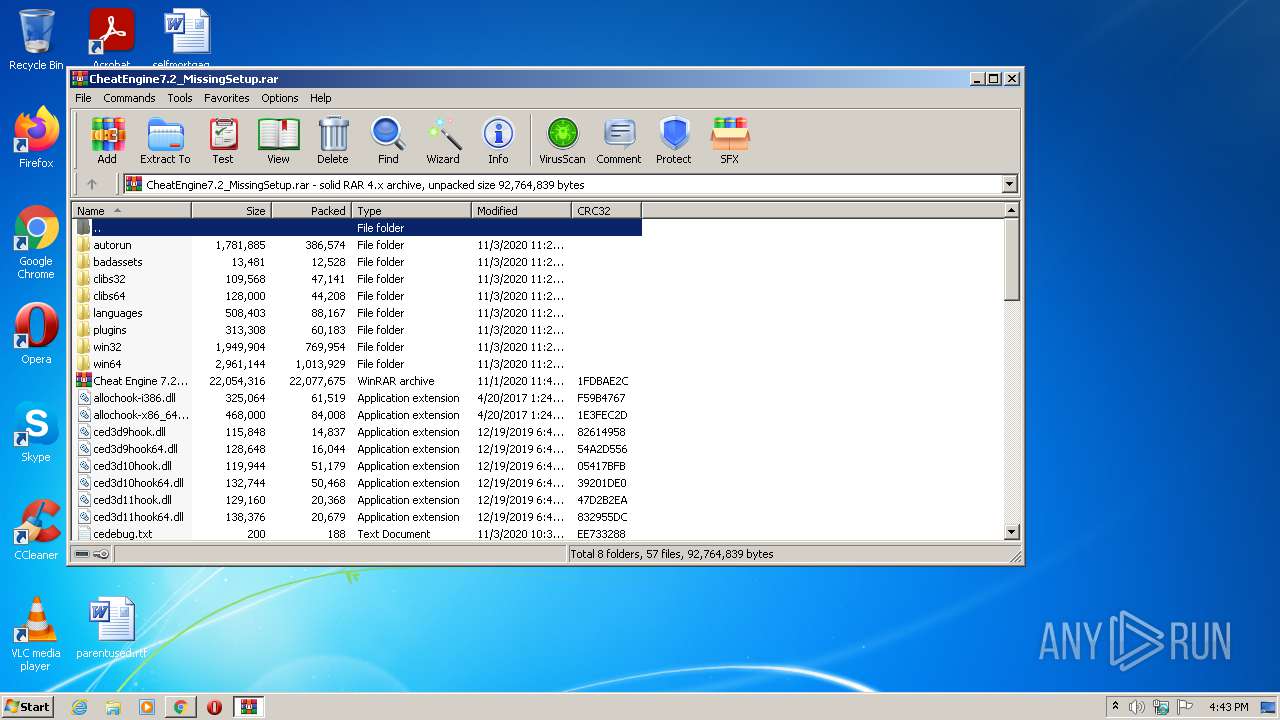
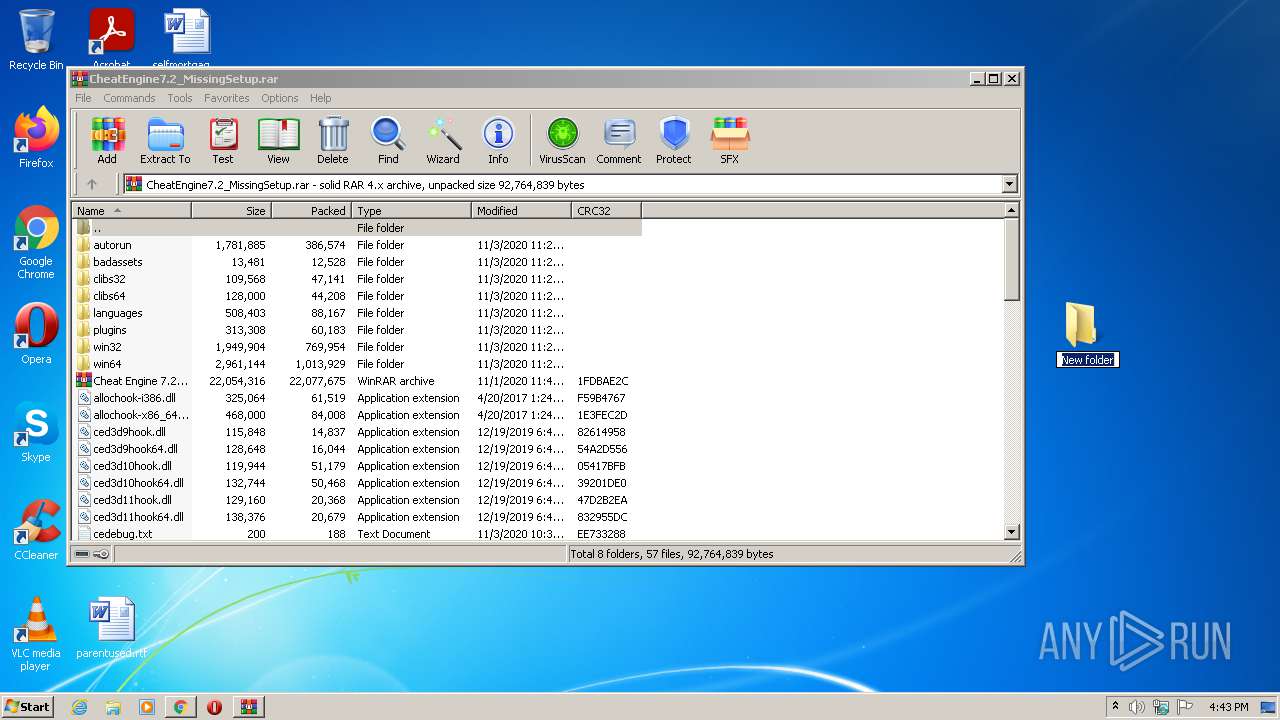
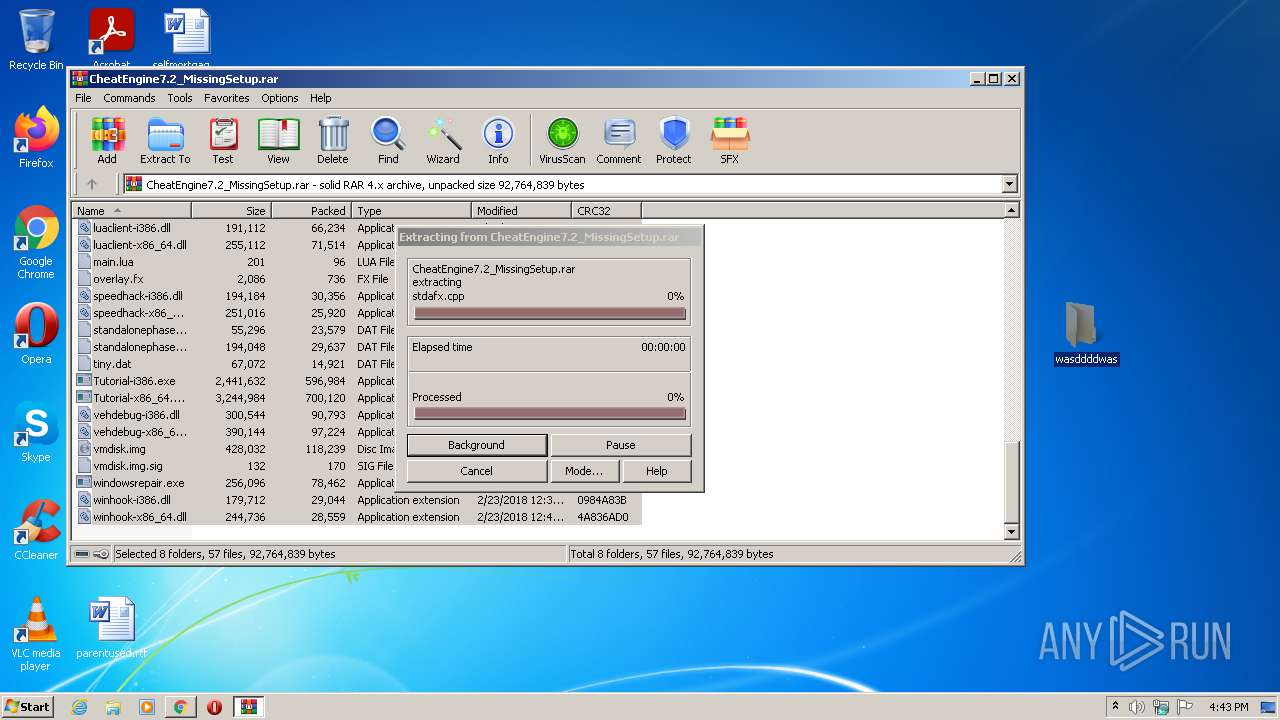
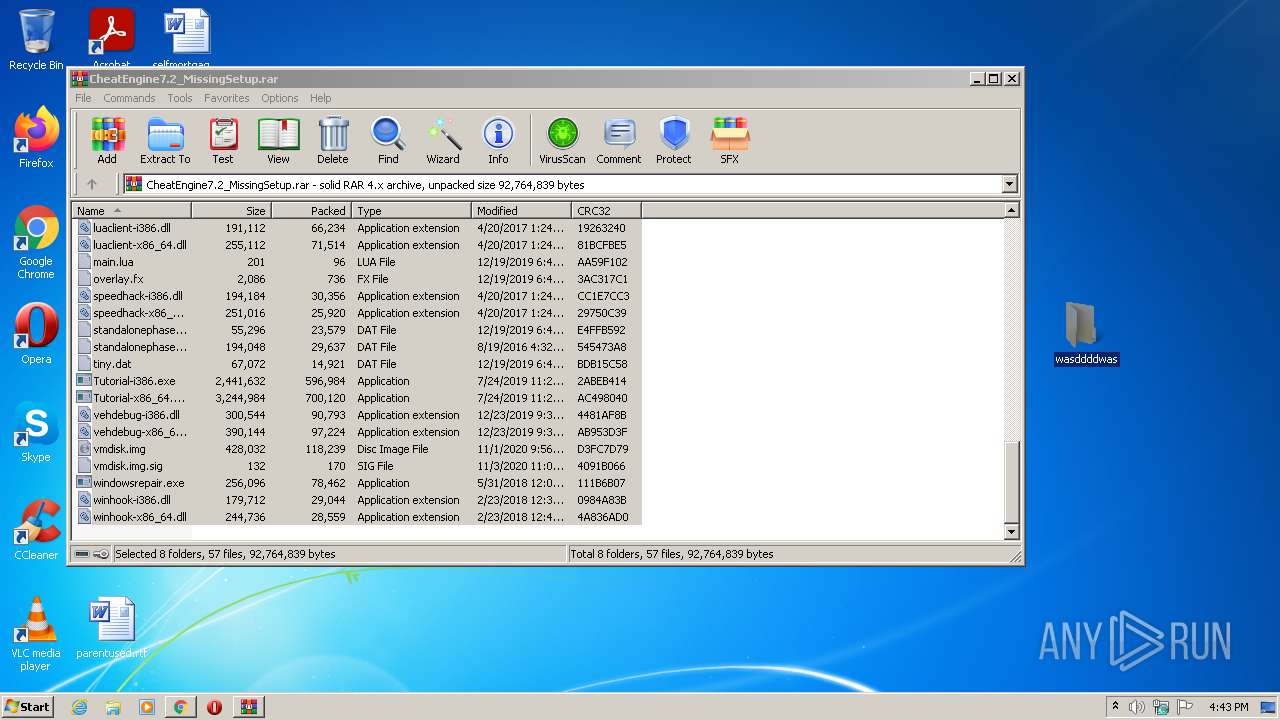
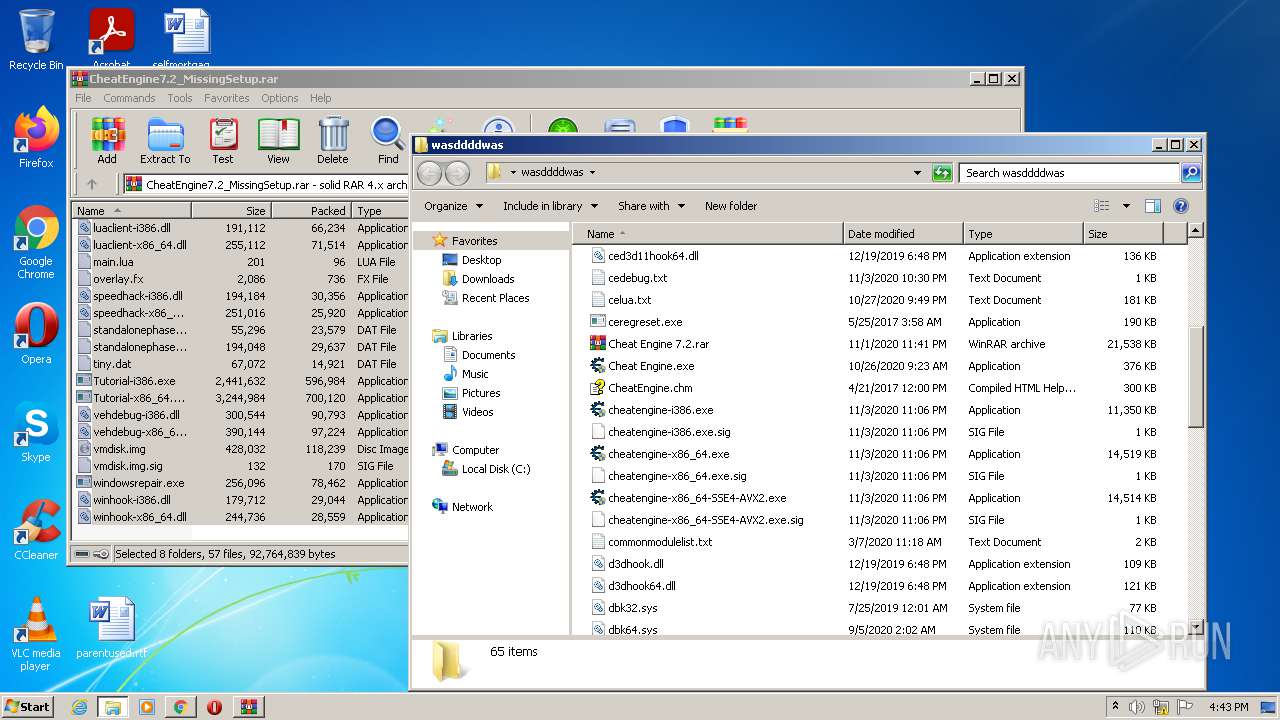
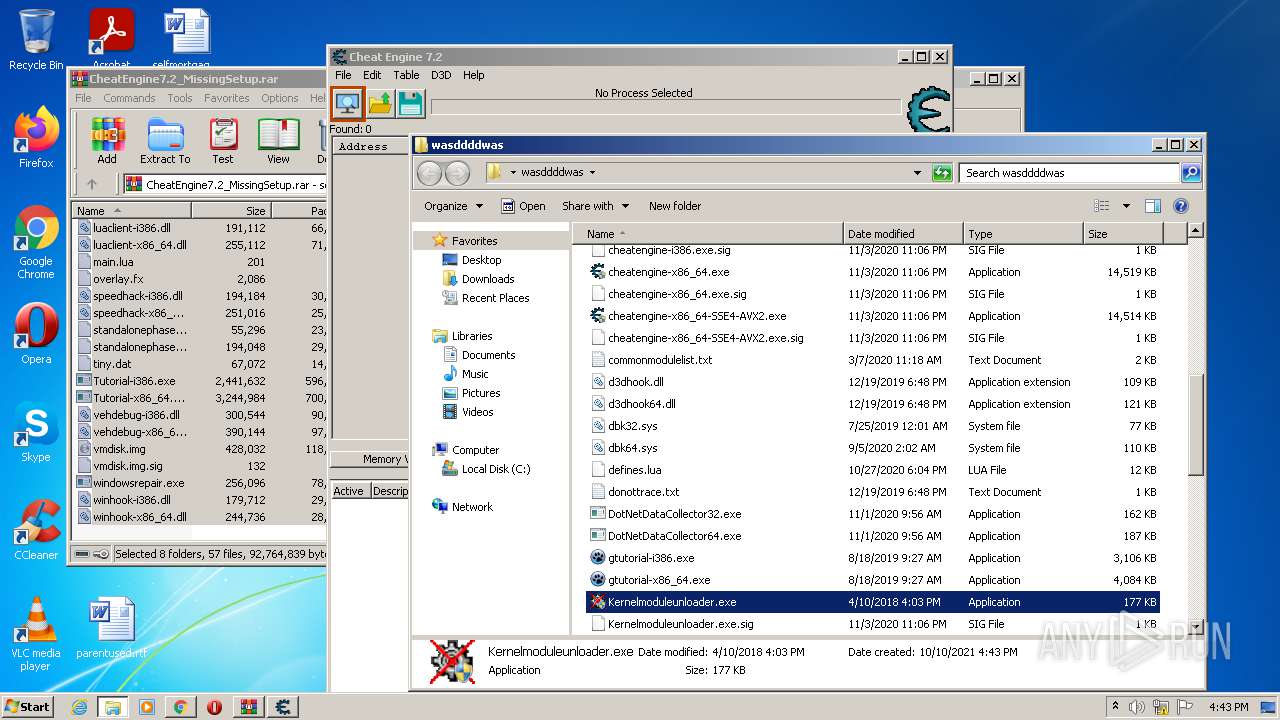
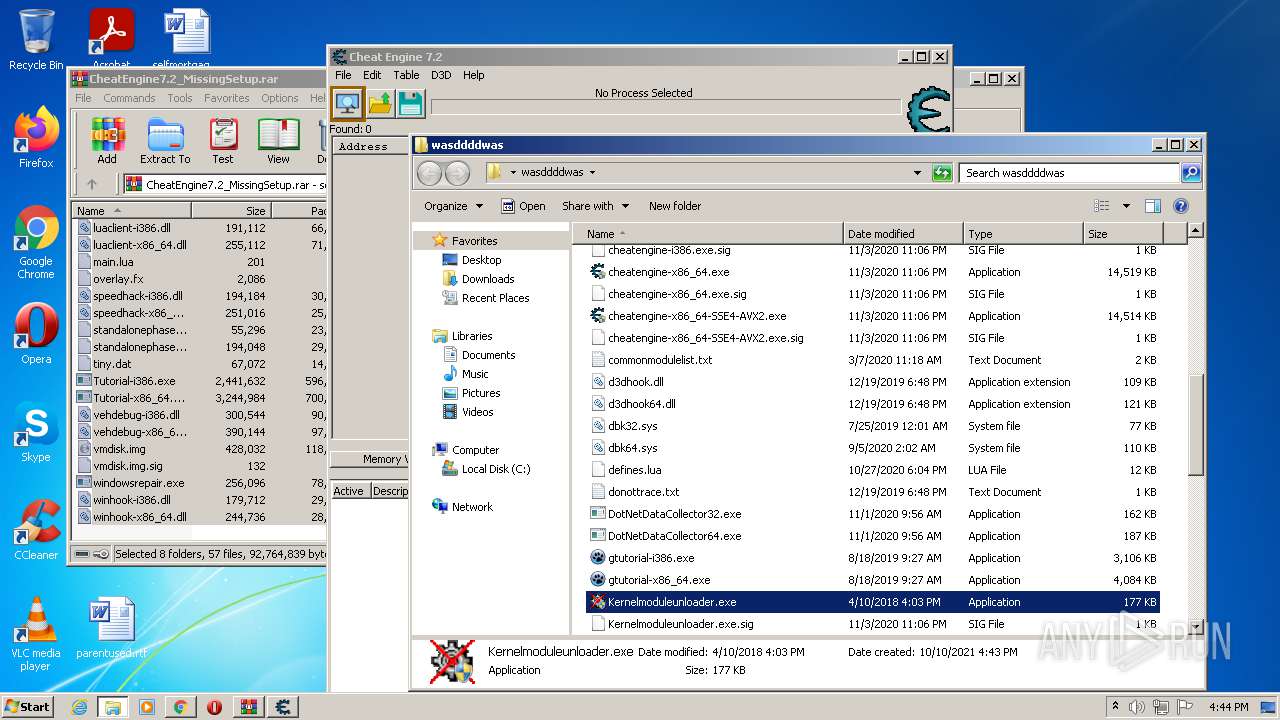
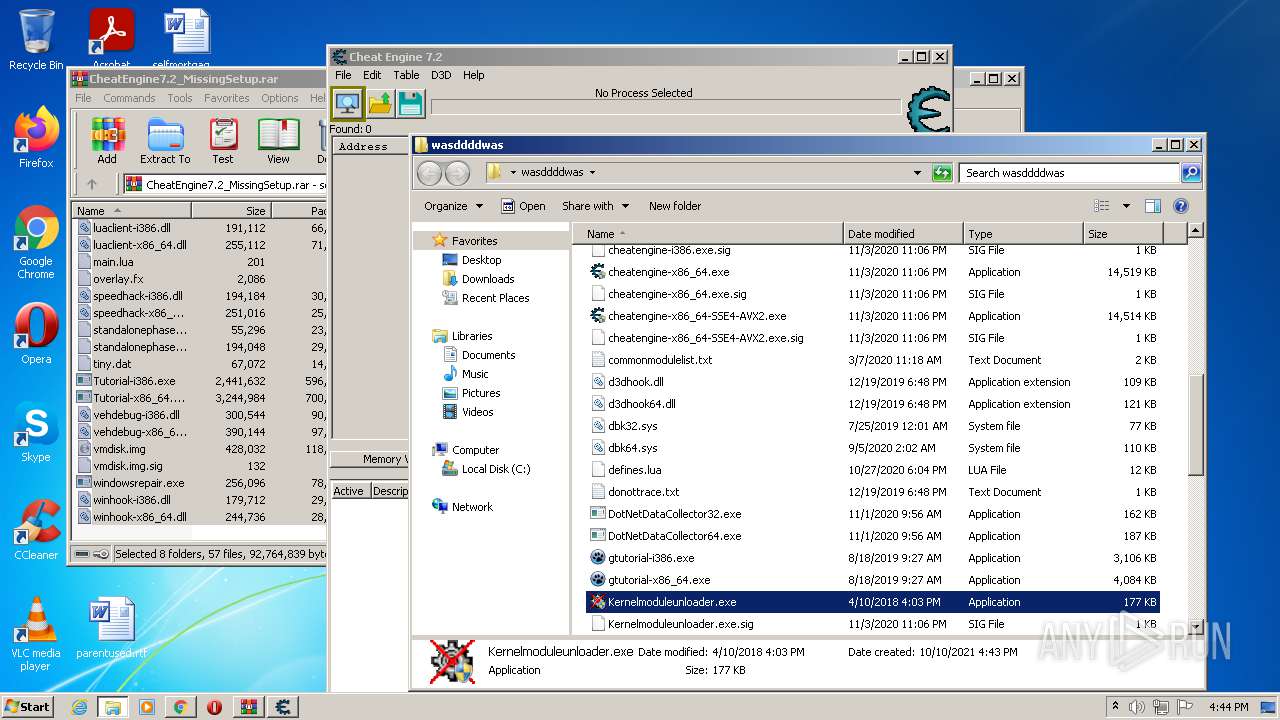
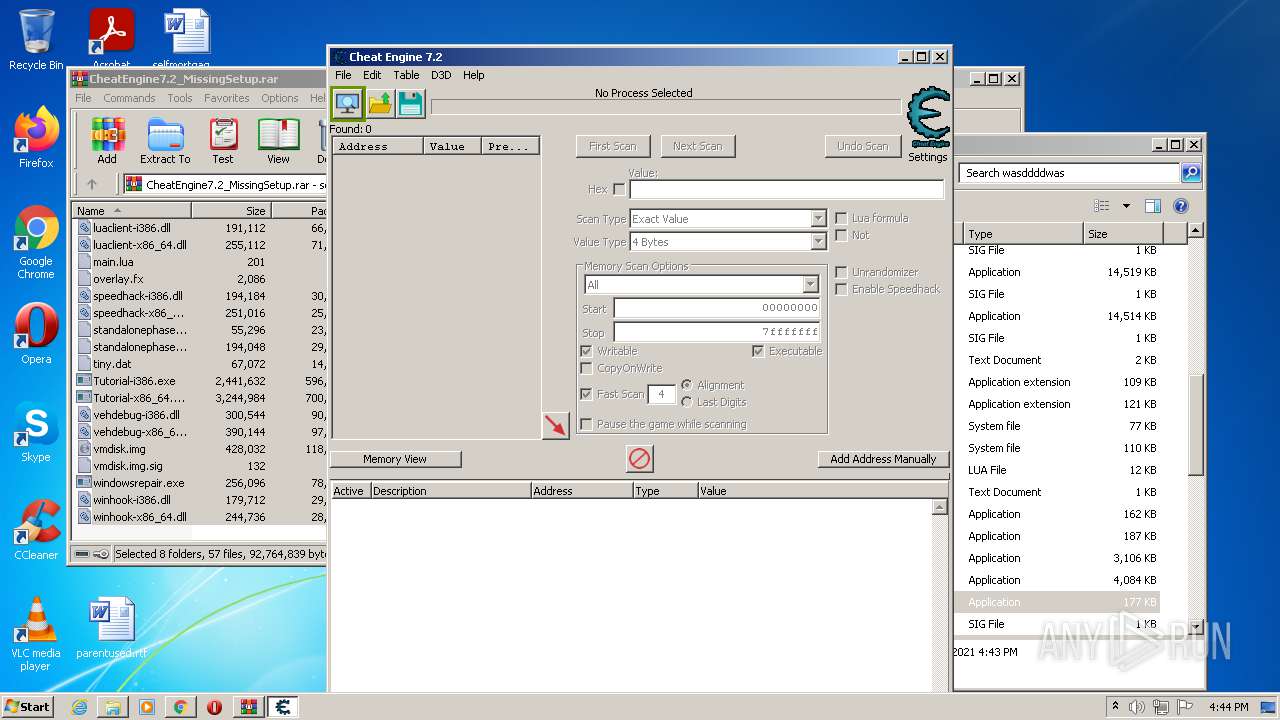
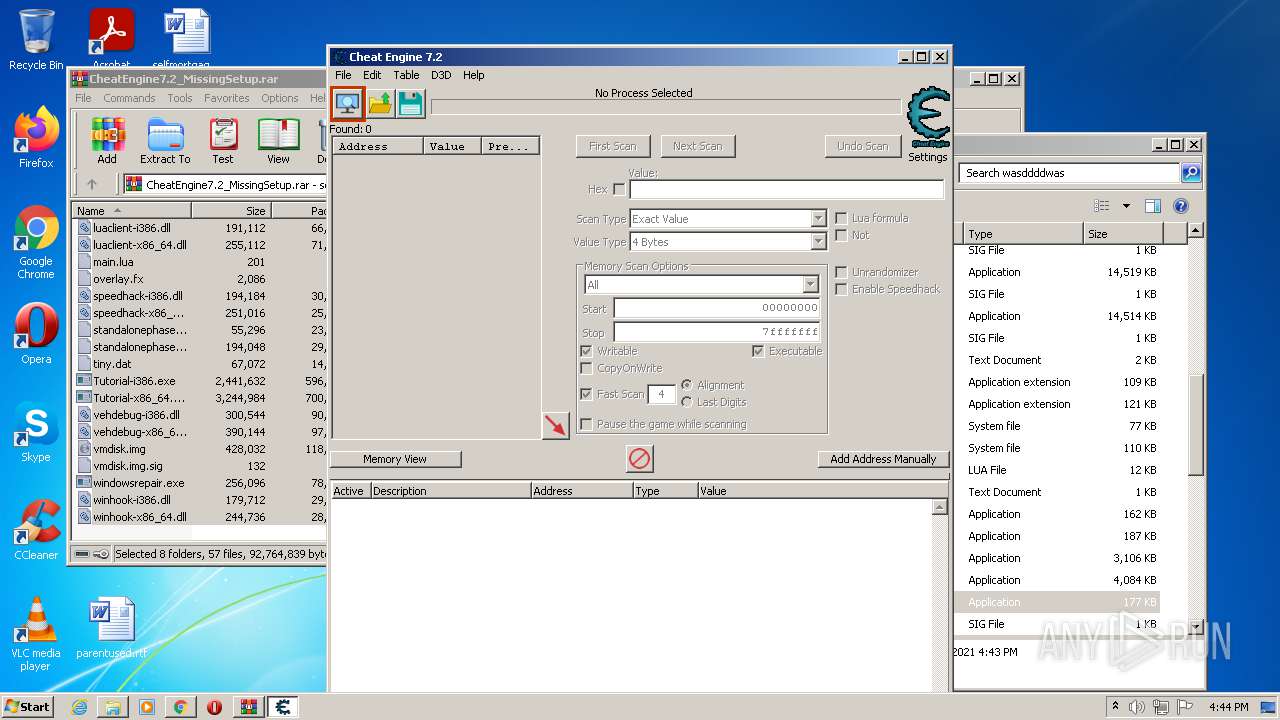
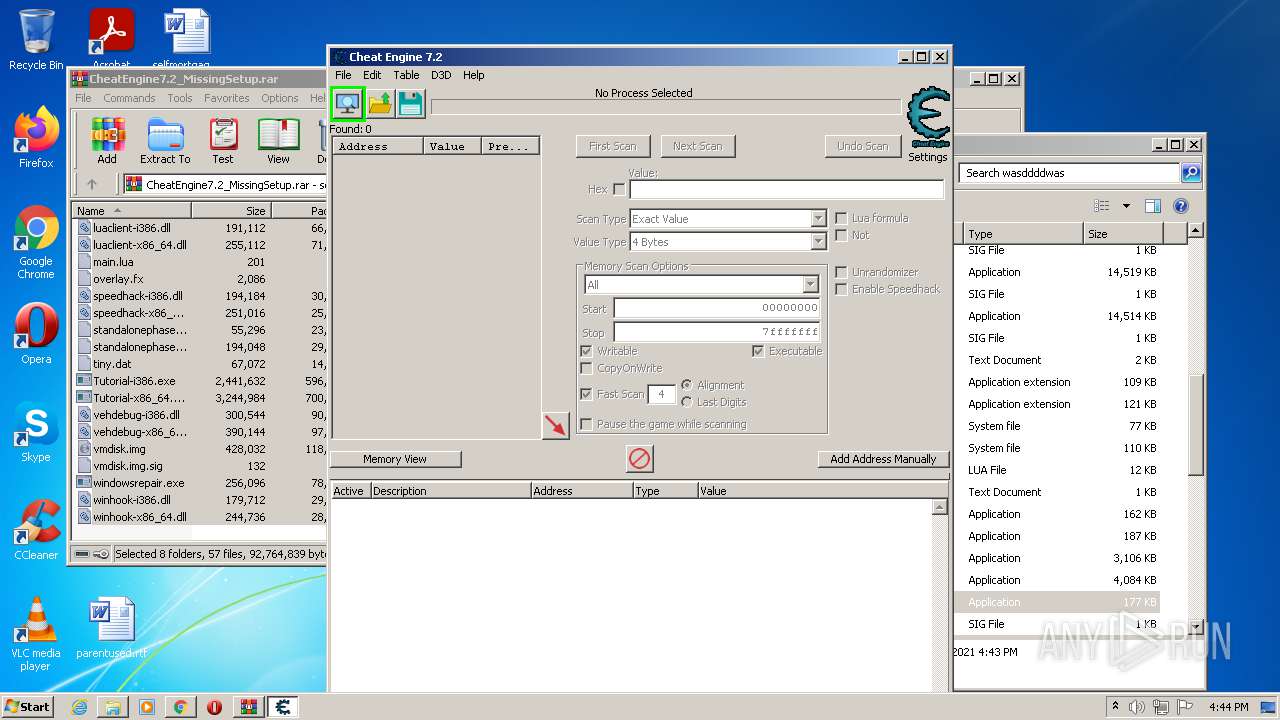
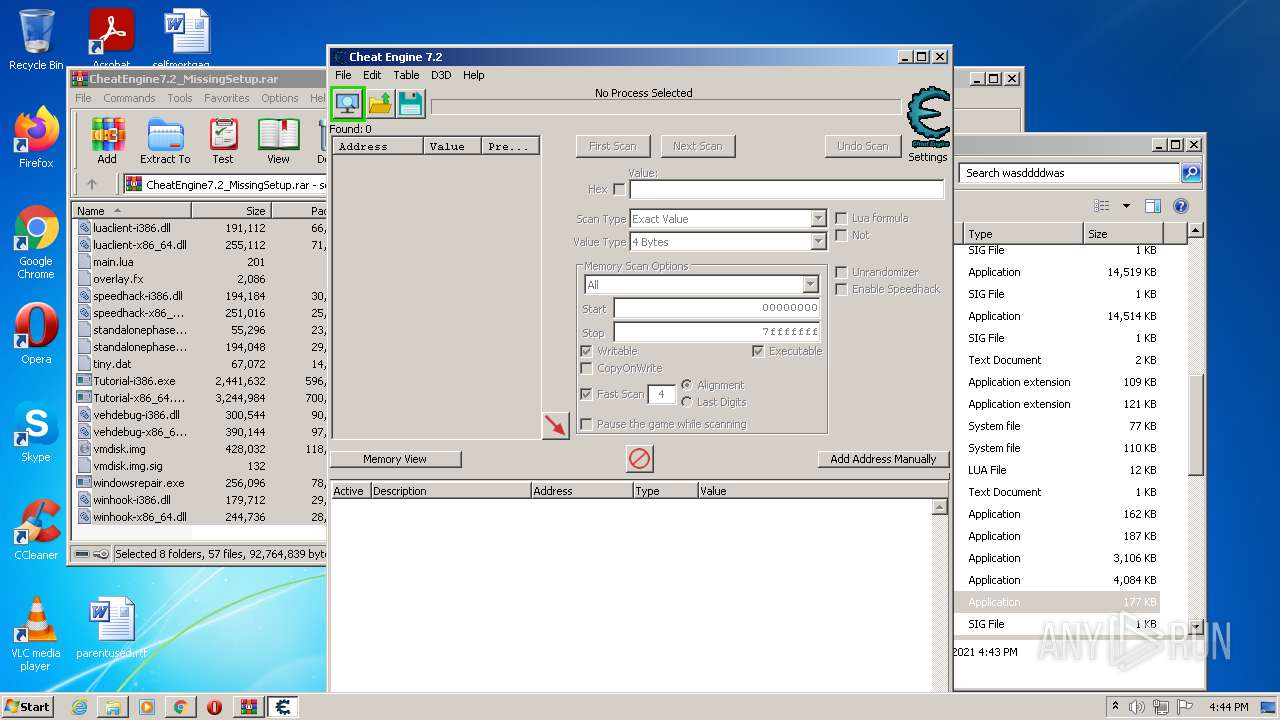
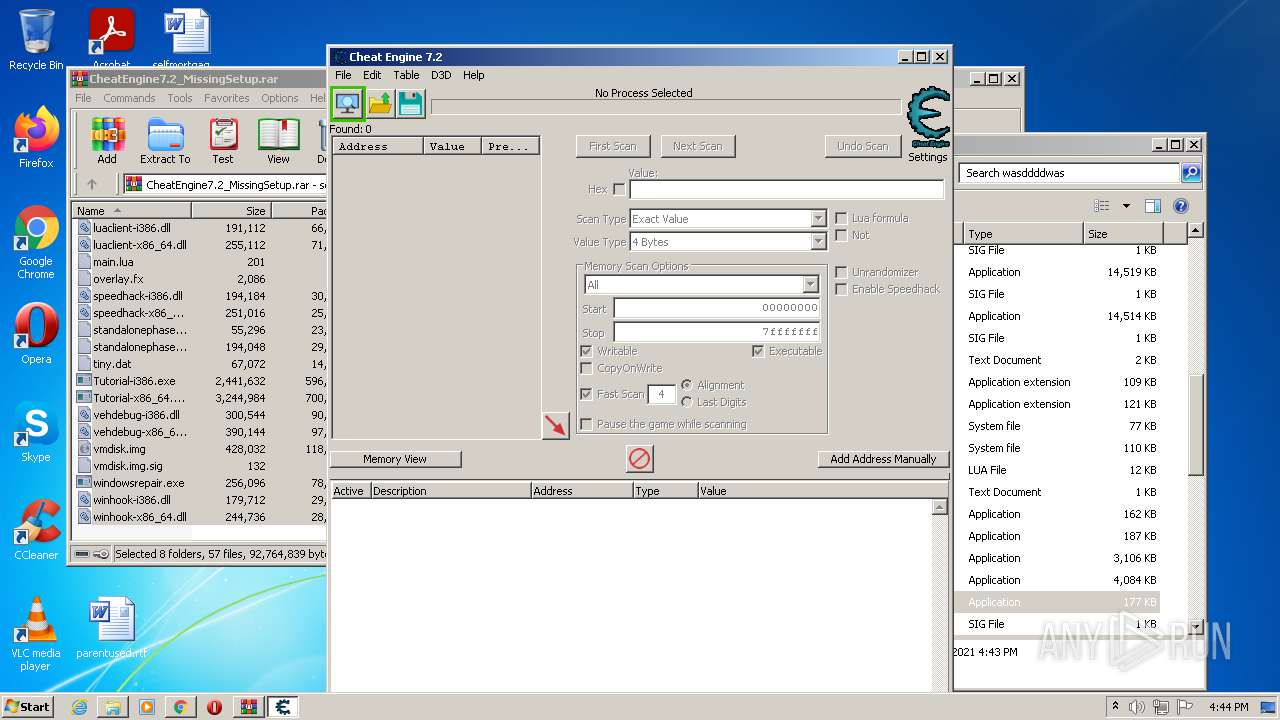
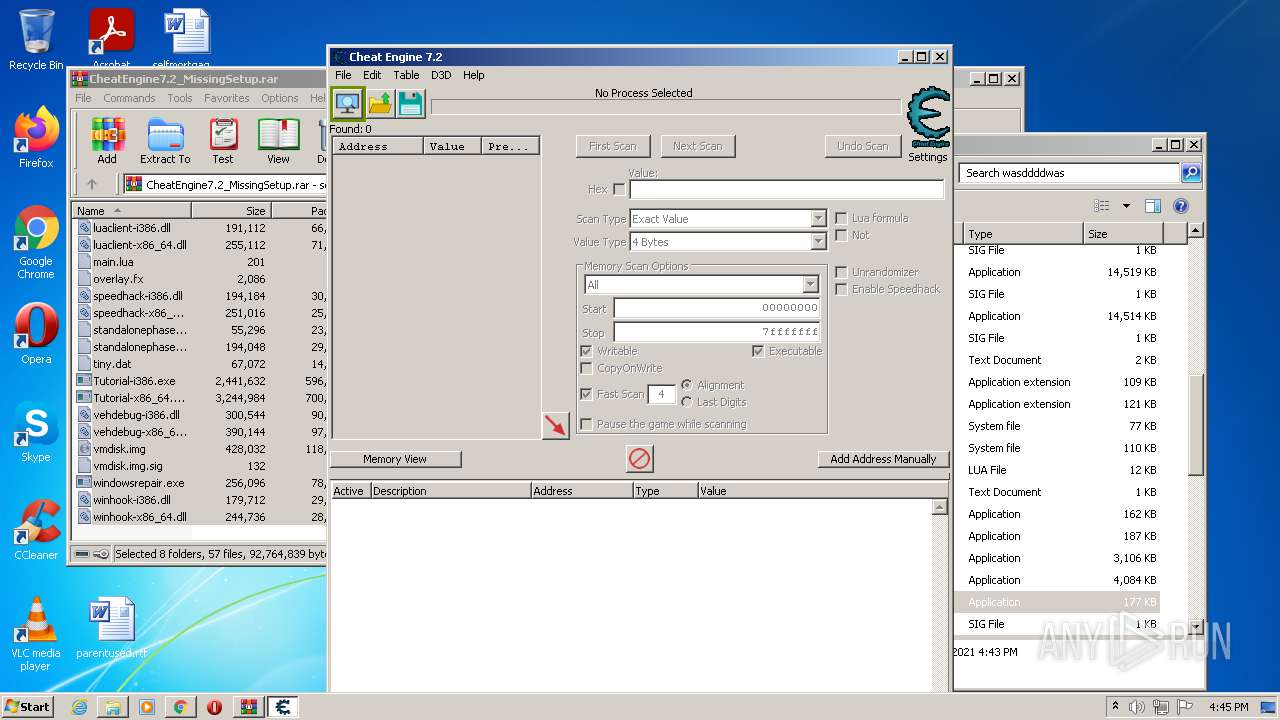
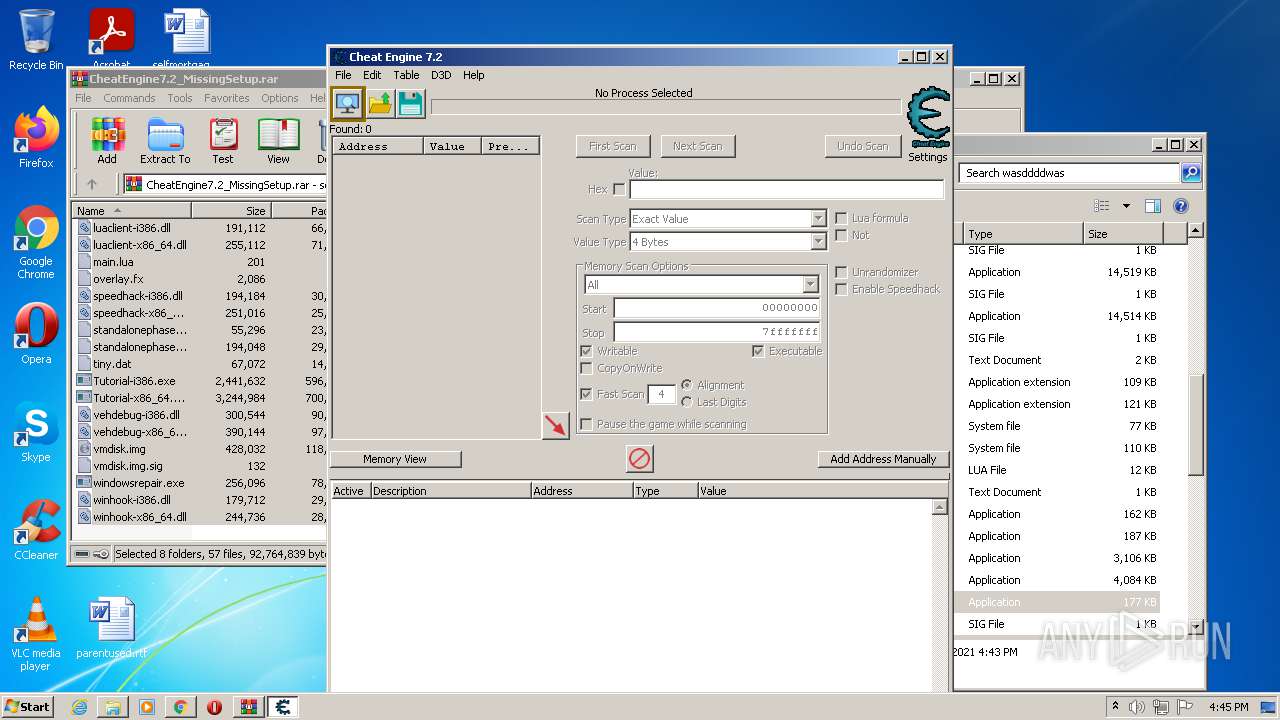
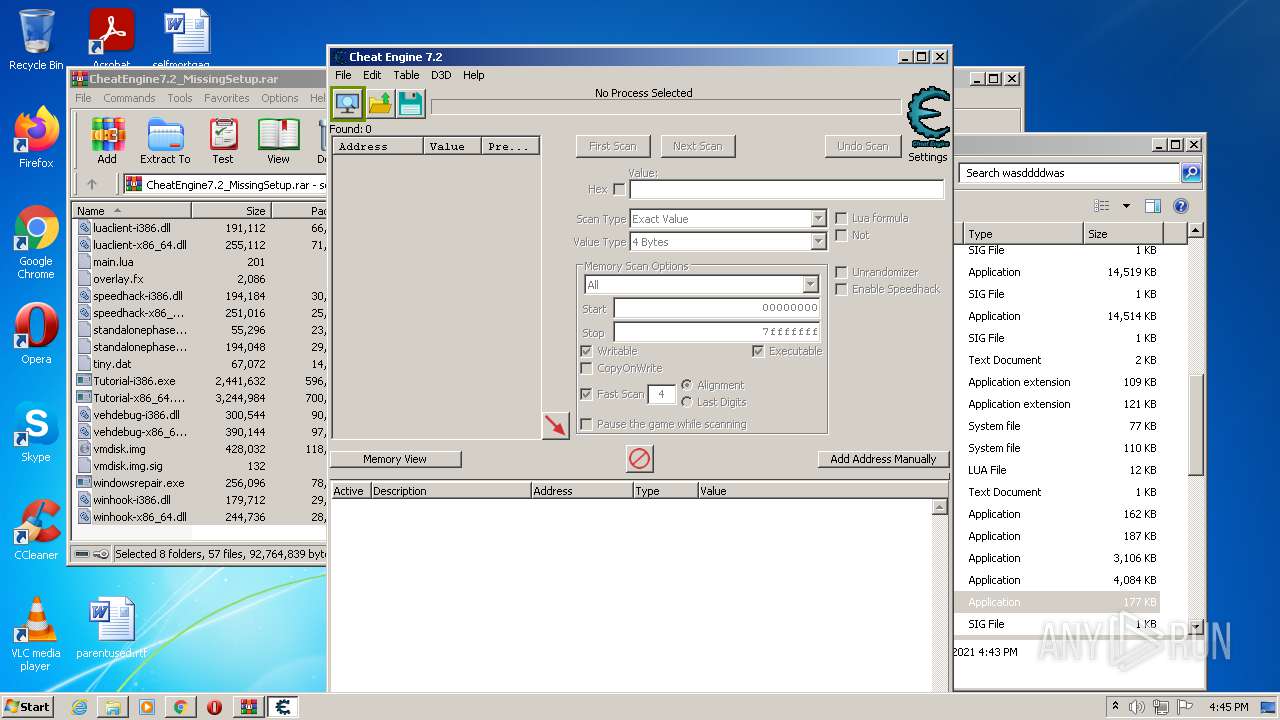
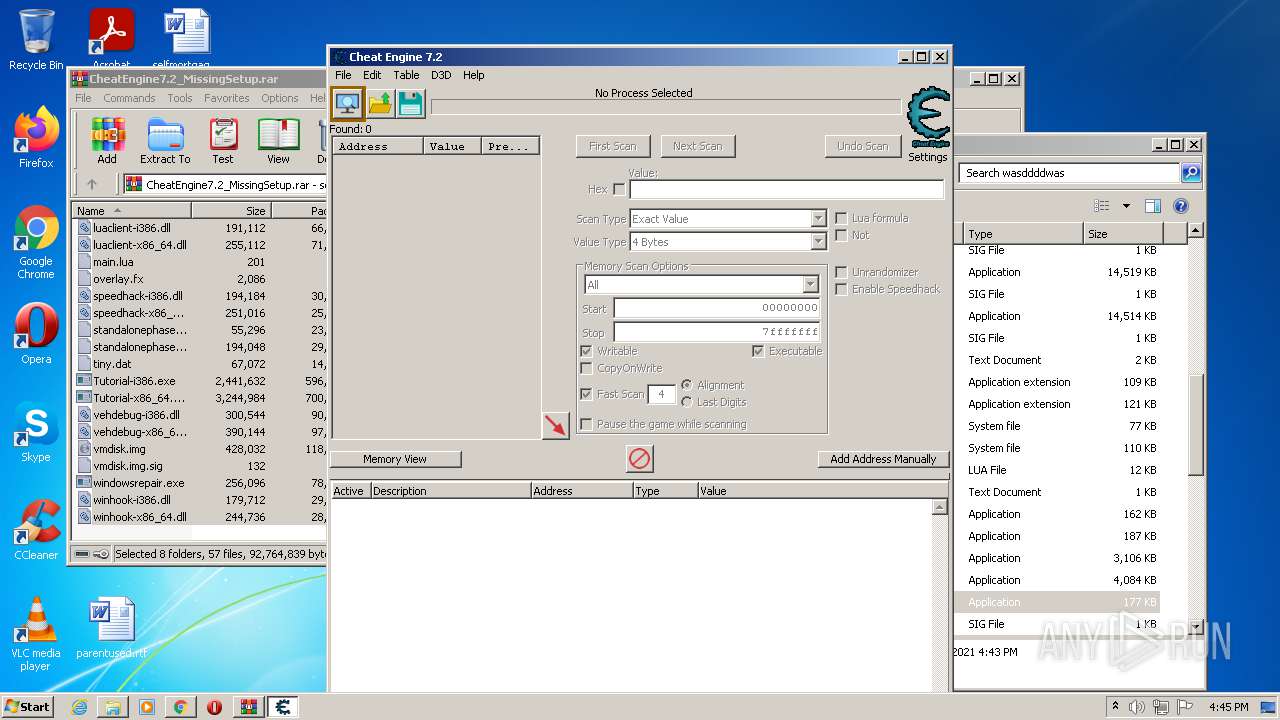
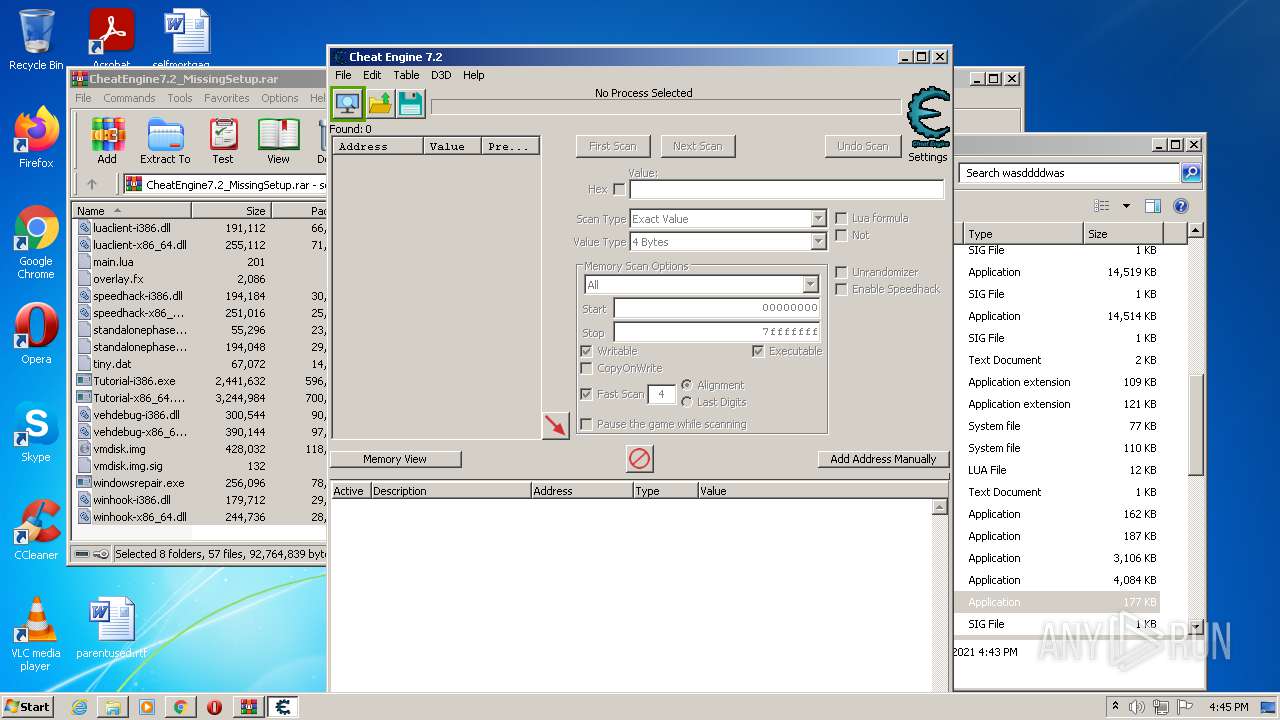
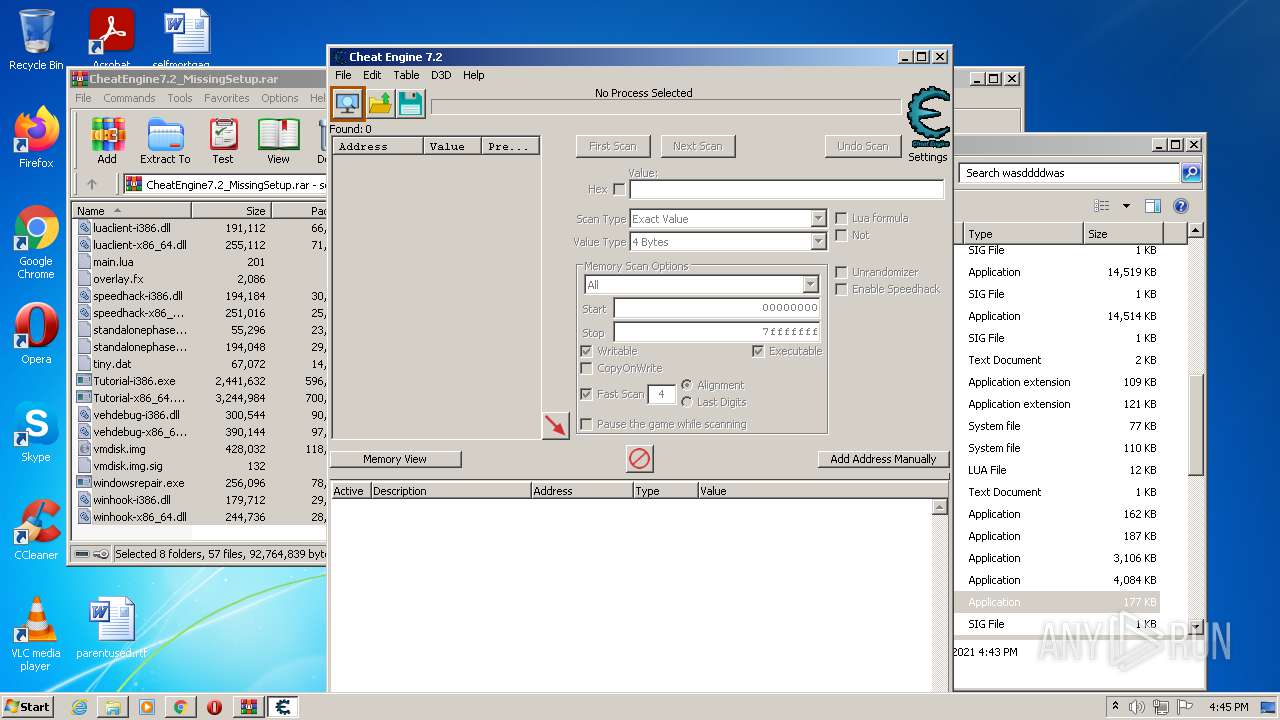
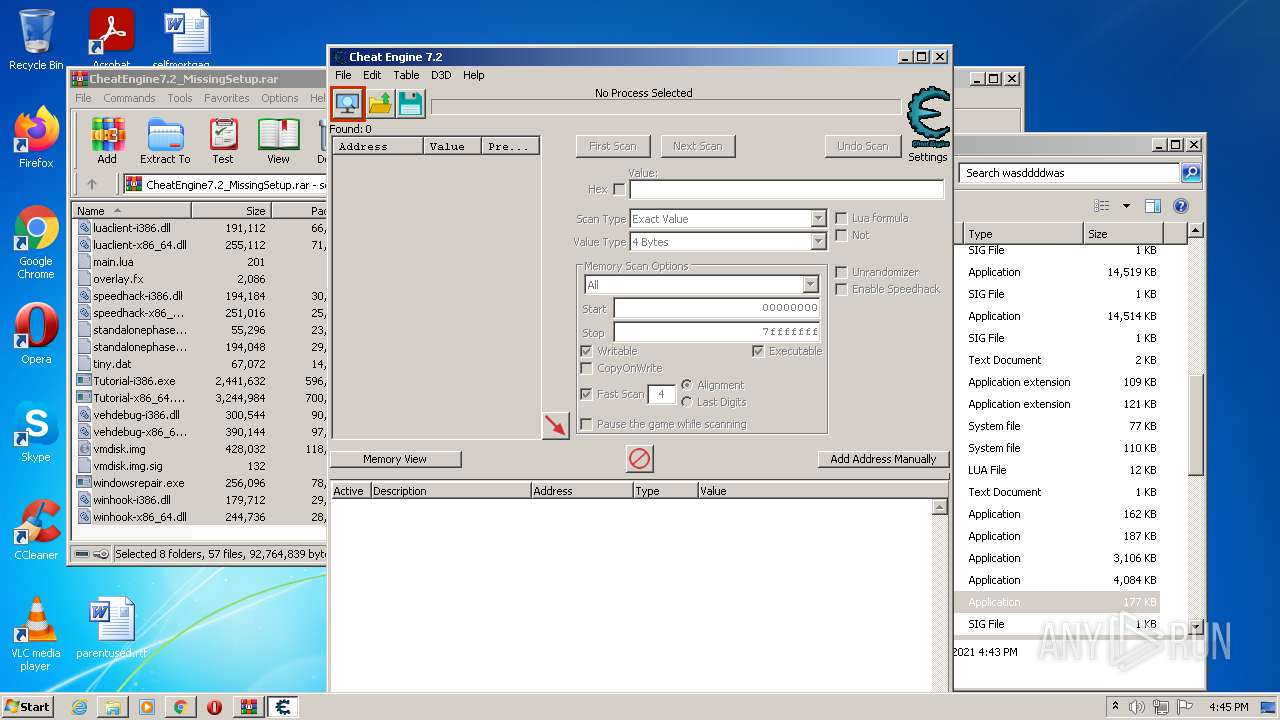
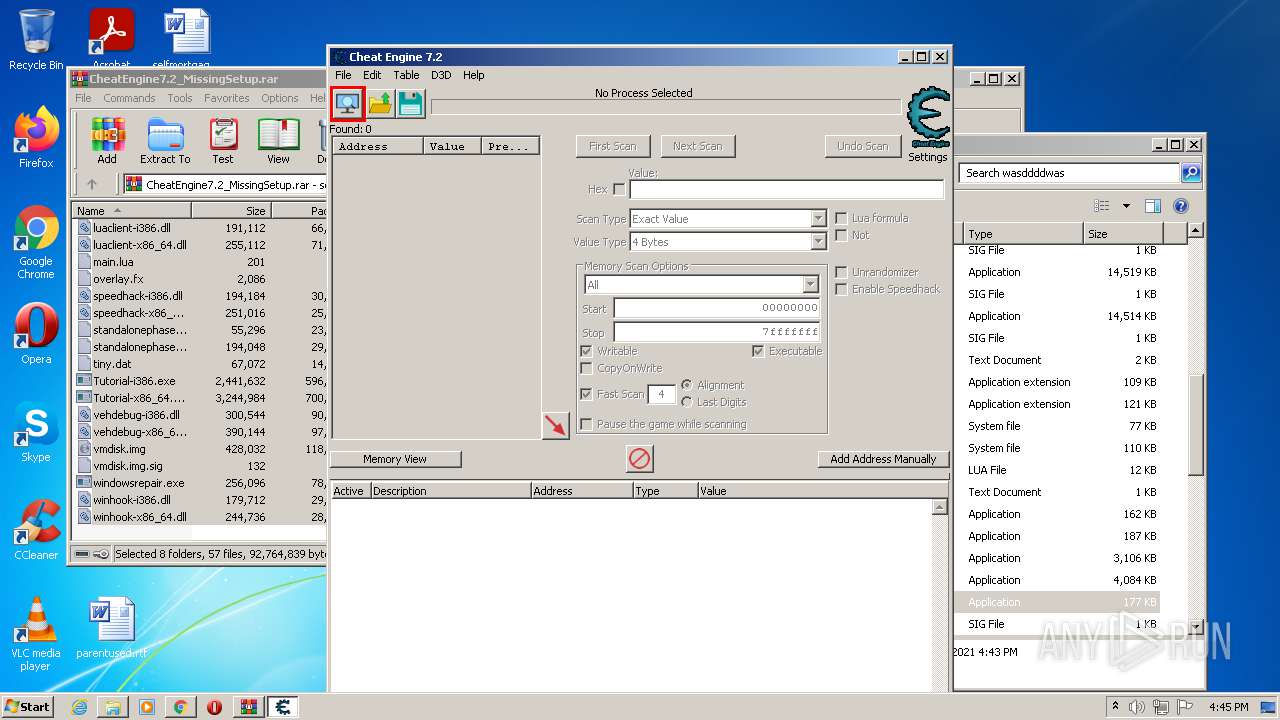
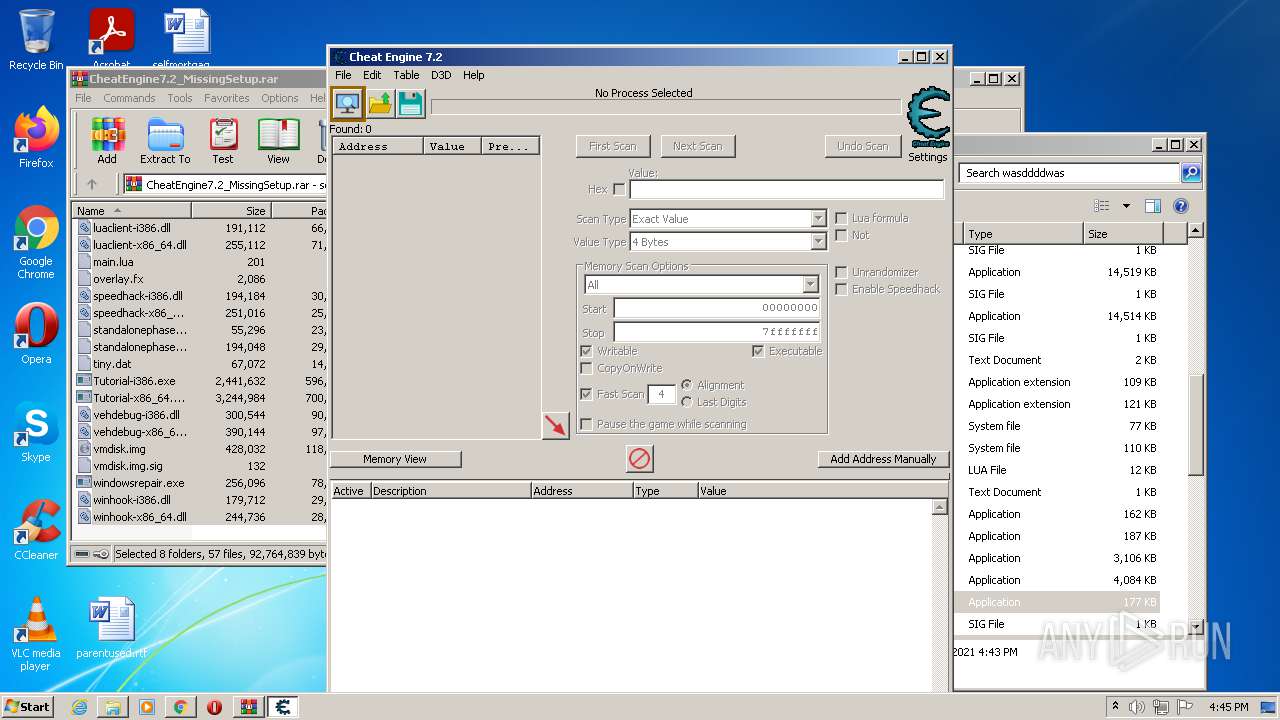
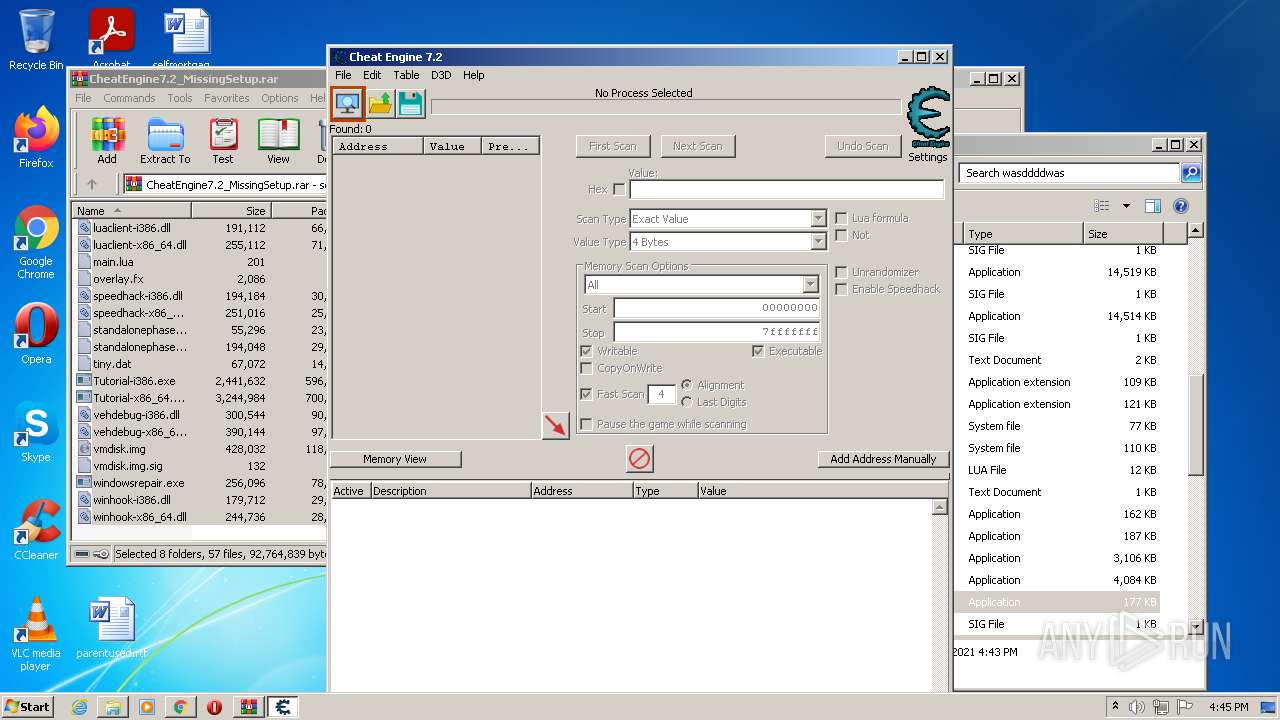
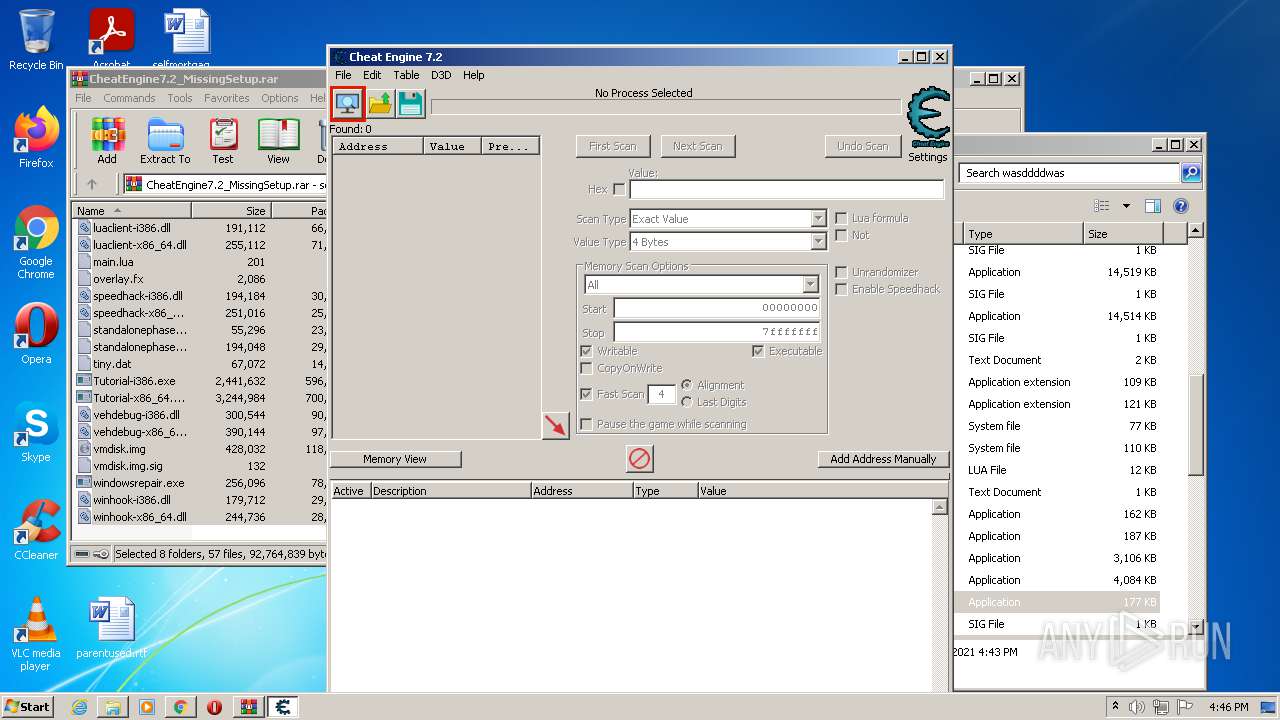
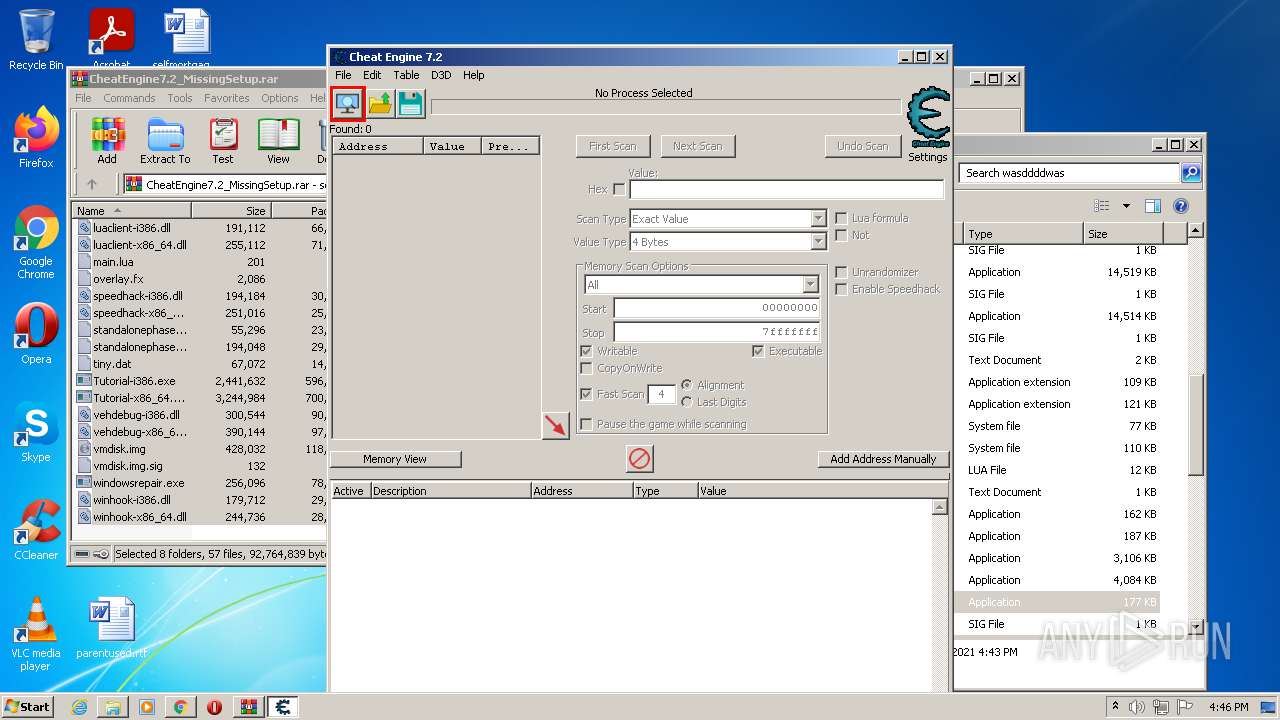
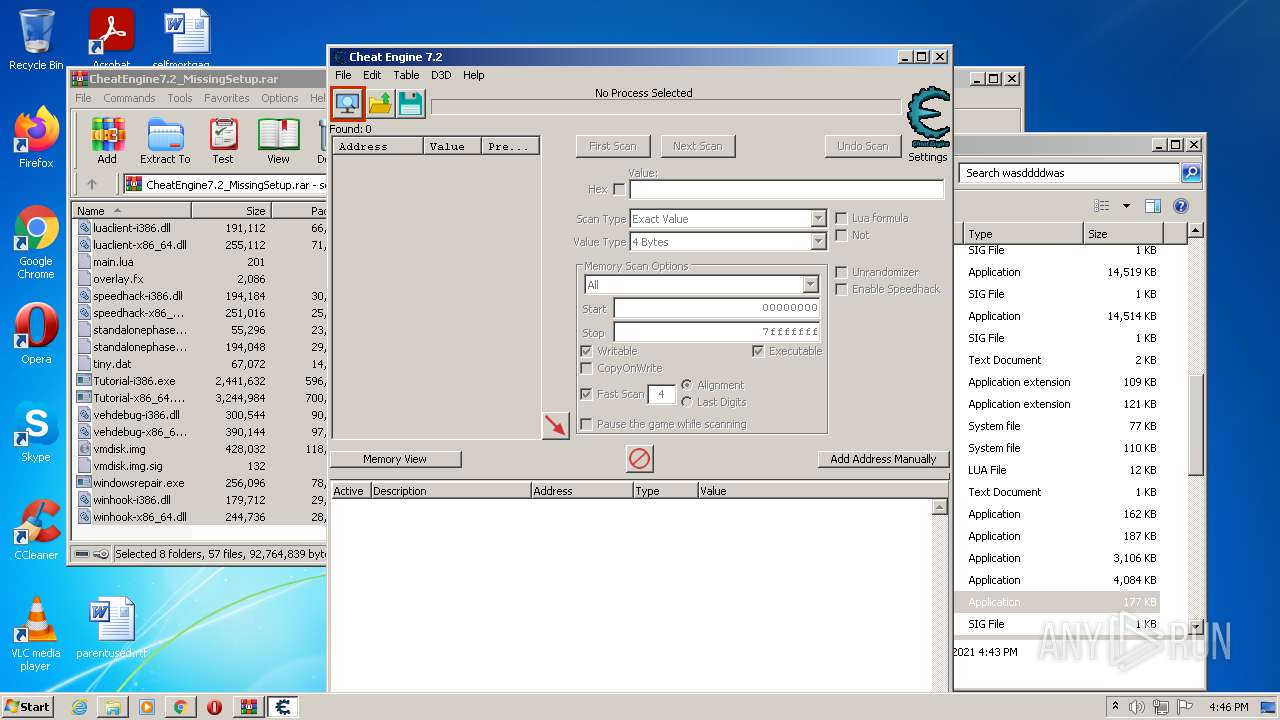
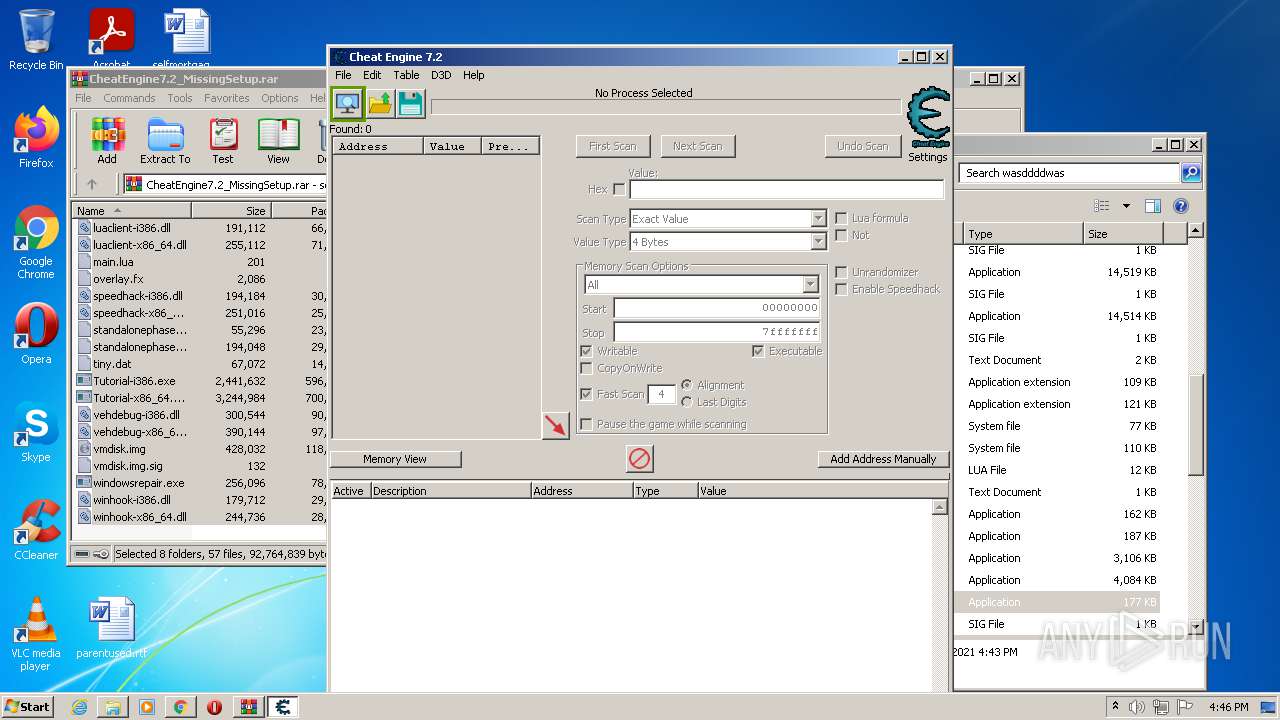
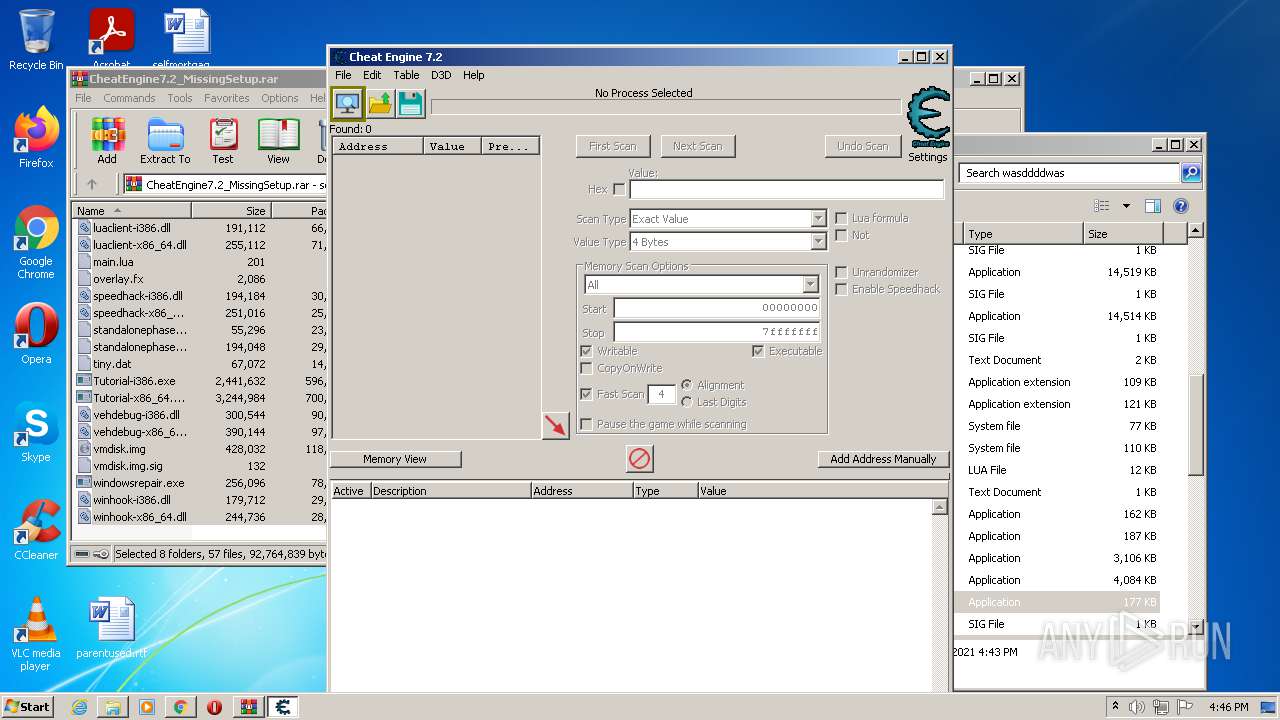
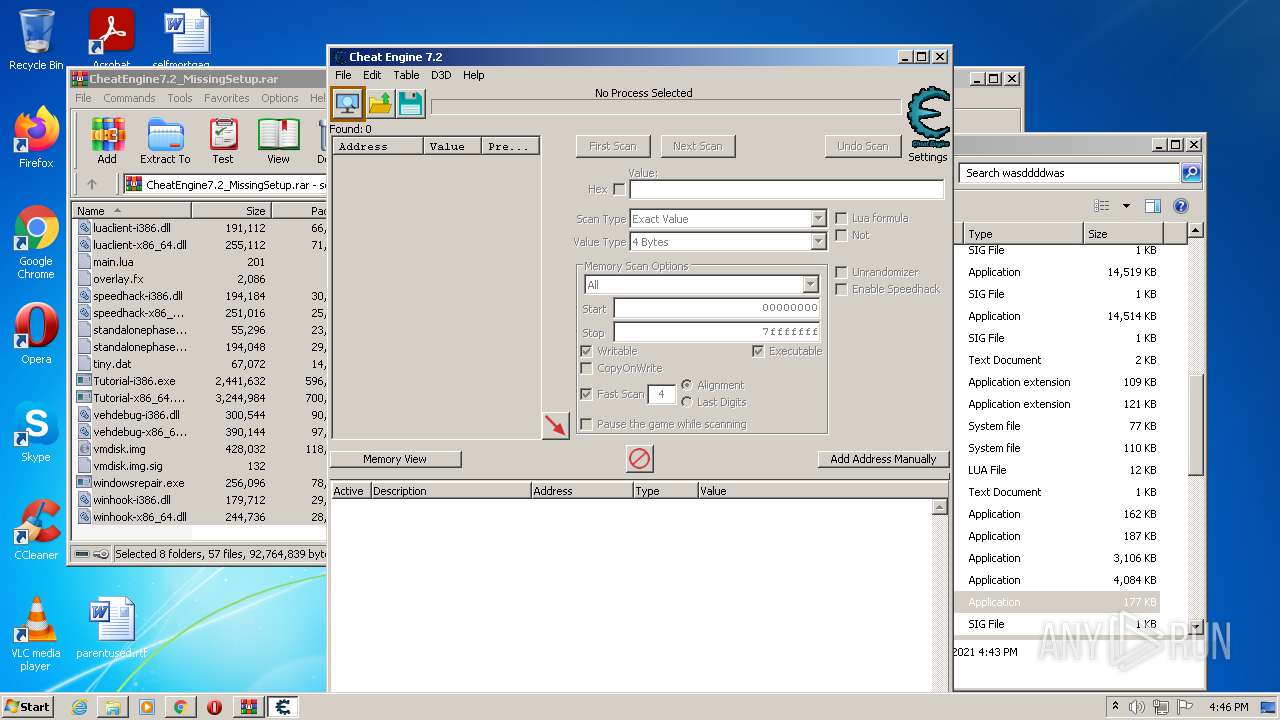
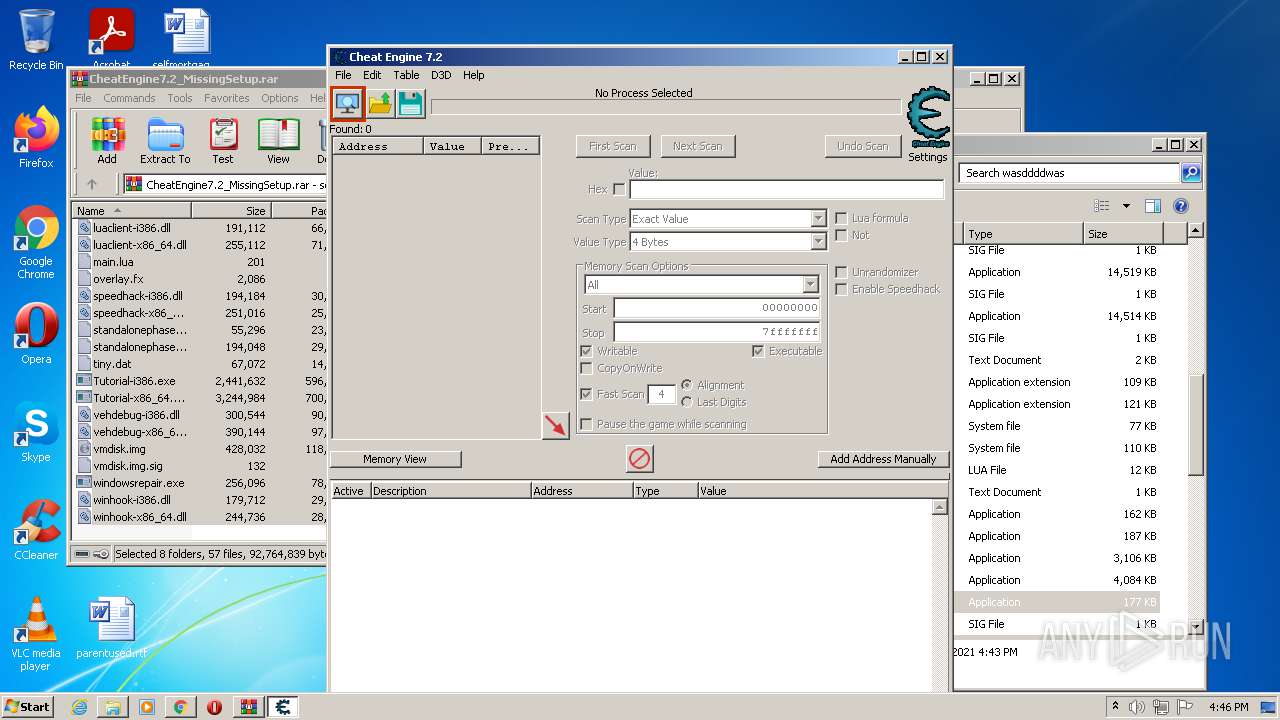
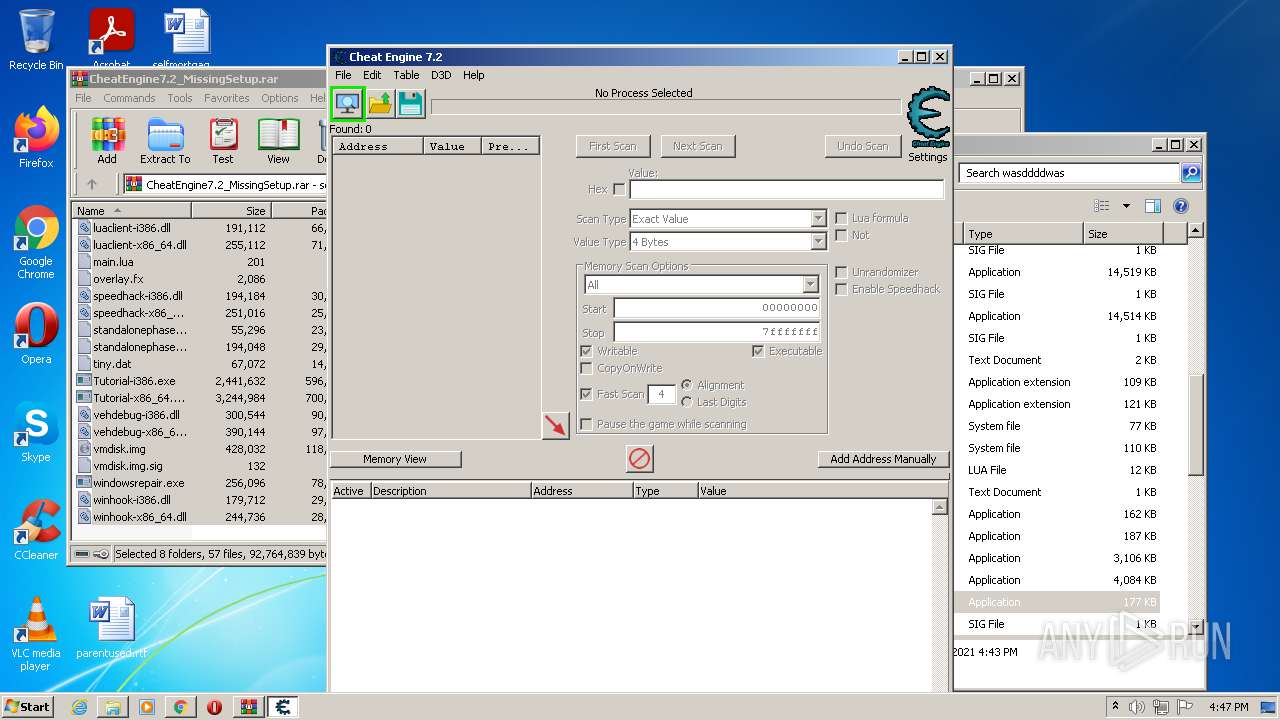
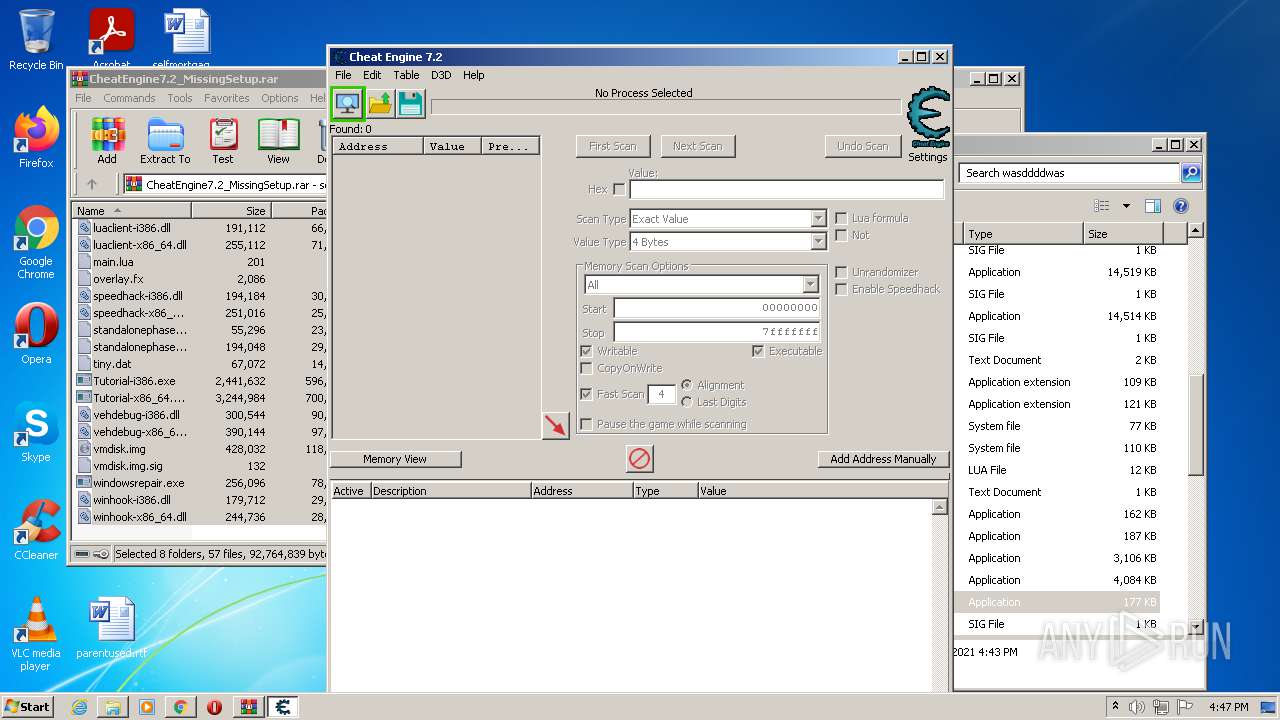
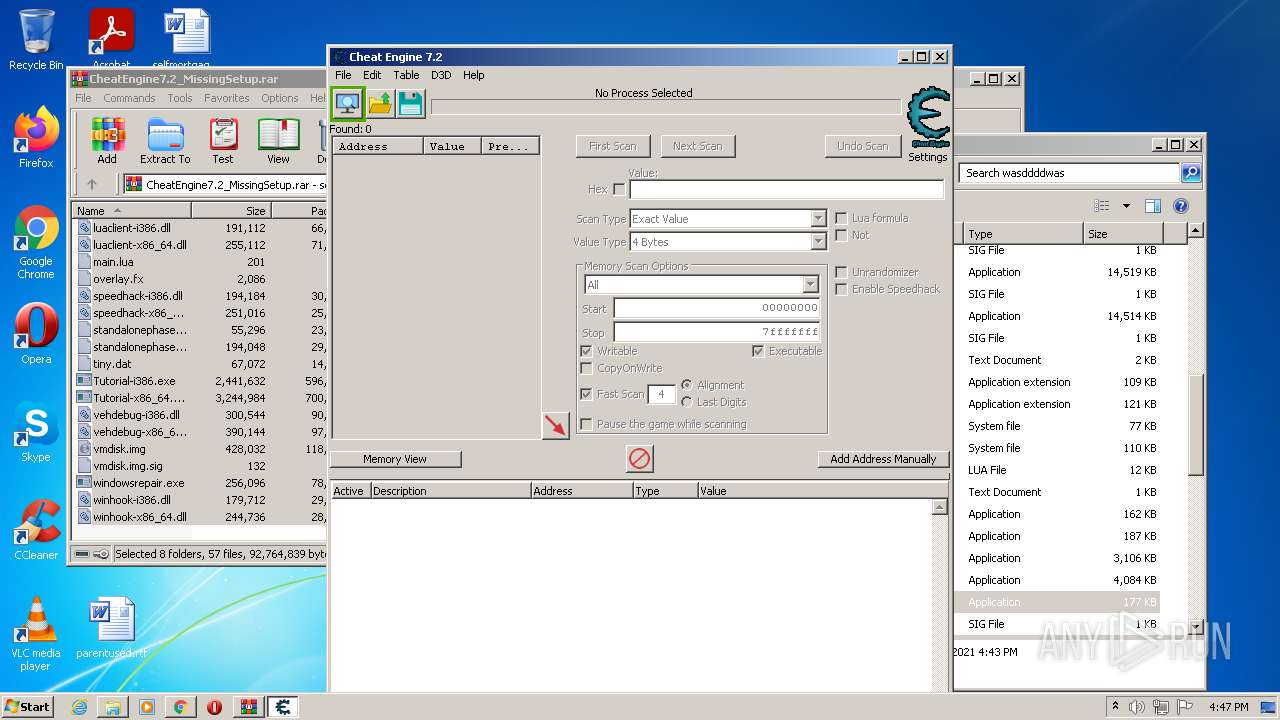
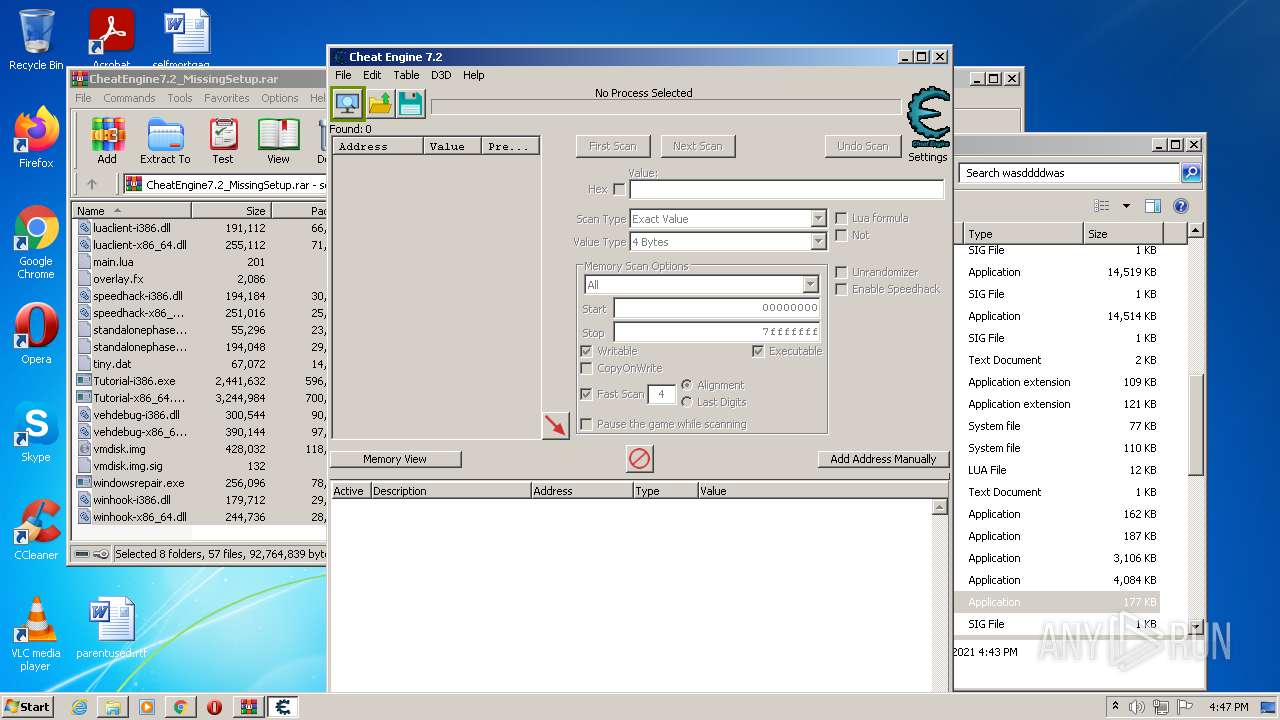
| URL: | https://www.cheatengine.org/download/CheatEngine7.2_MissingSetup.rar |
| Full analysis: | https://app.any.run/tasks/cb249f4d-7c5f-4a3c-a598-9b4e05f99404 |
| Verdict: | Malicious activity |
| Analysis date: | October 10, 2021, 15:42:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 30C97EDF97B047B20CCE0256D3F4D956 |
| SHA1: | 6B6C8158FC6B13ED1746850E6B30D5B525FBF713 |
| SHA256: | 99C10653498535BC53B86CB1CC86A641E246B55C6B543328EA6059C19BFE5FCA |
| SSDEEP: | 3:N8DSLHQ6hzMrGoGKKyan:2OLHDK/GKKya |
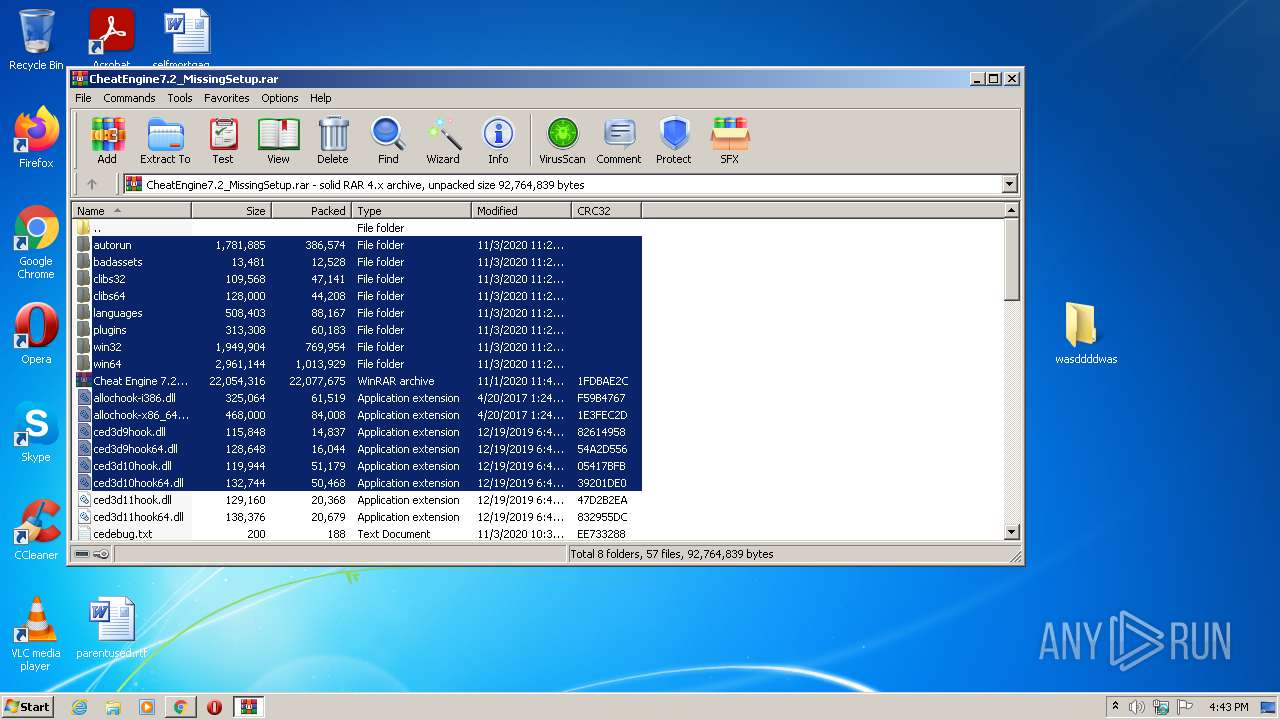
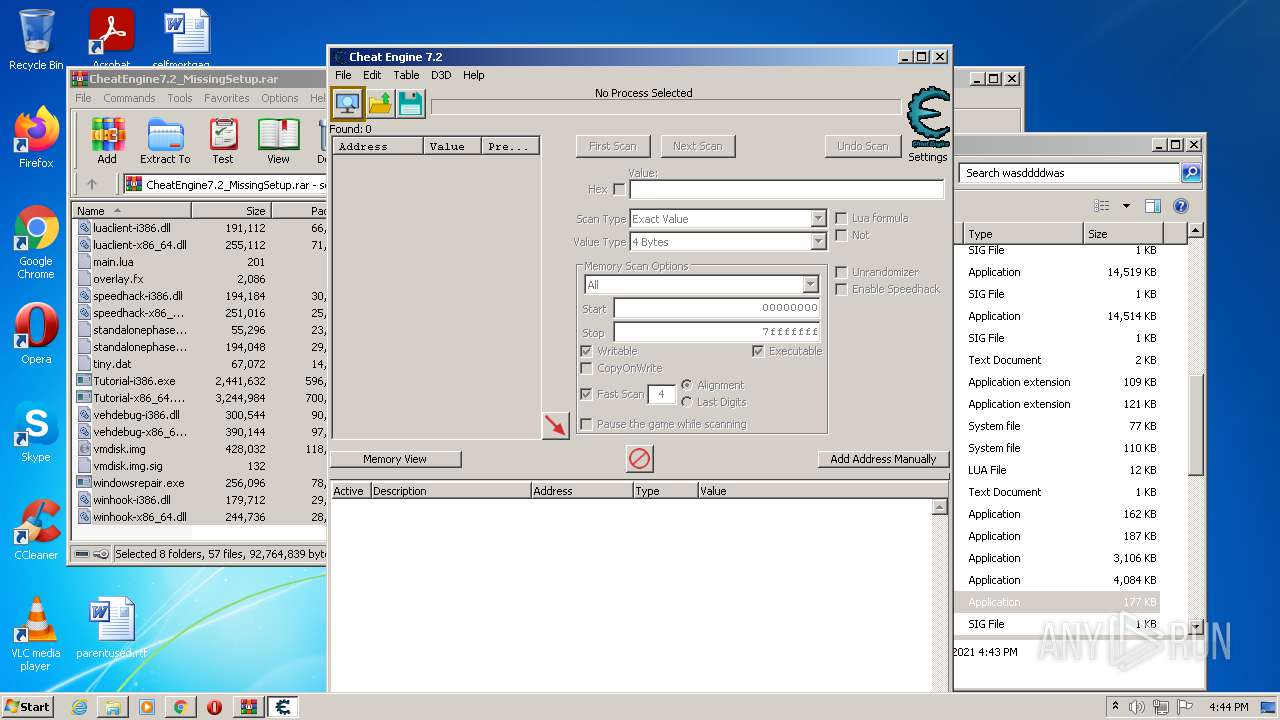
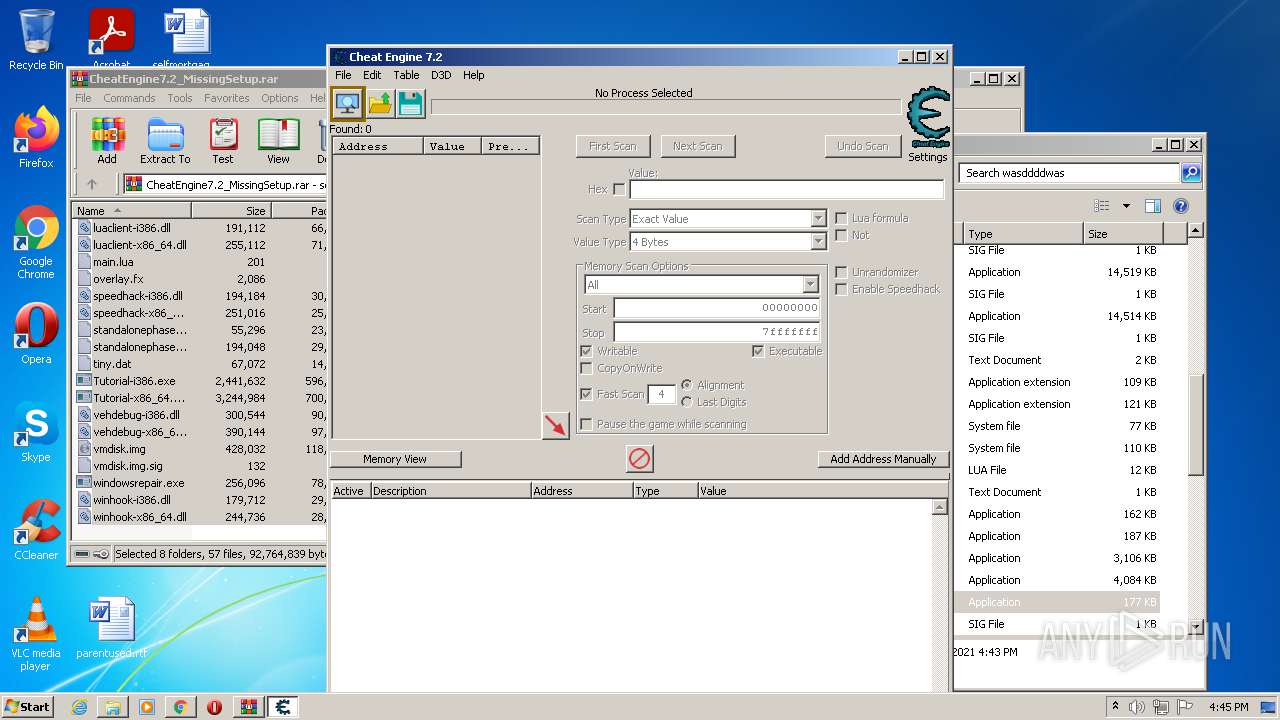
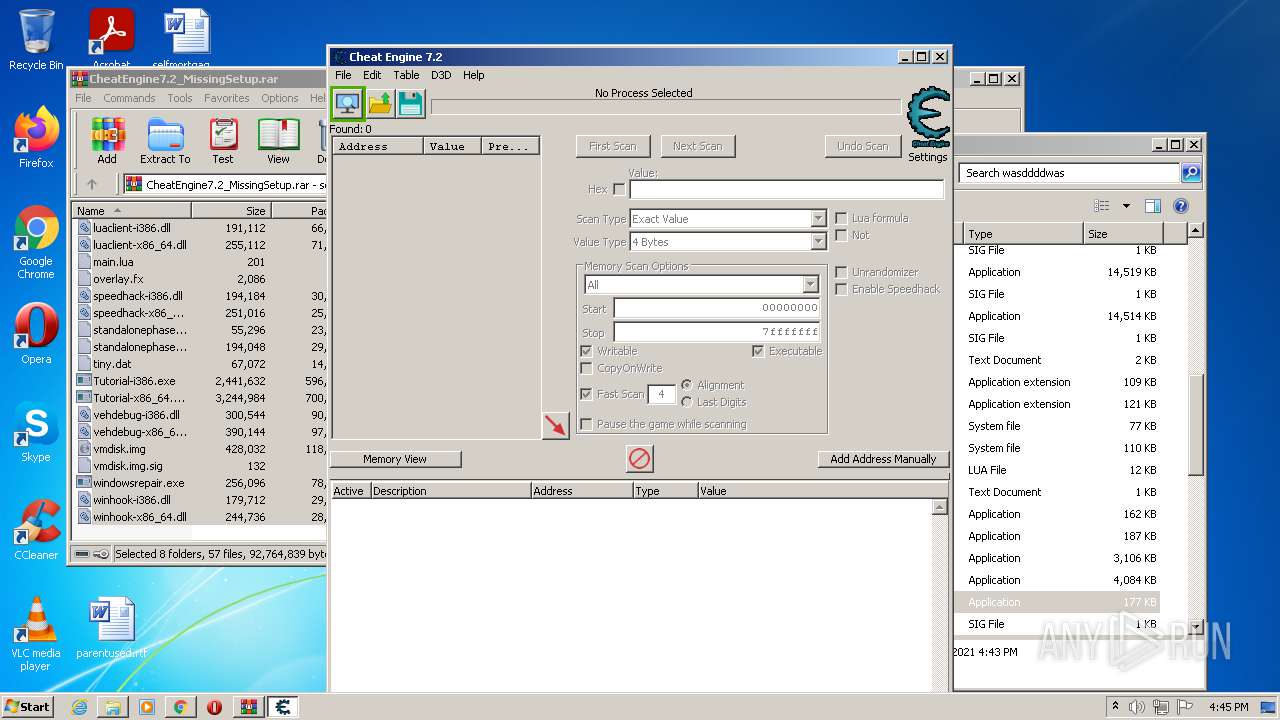
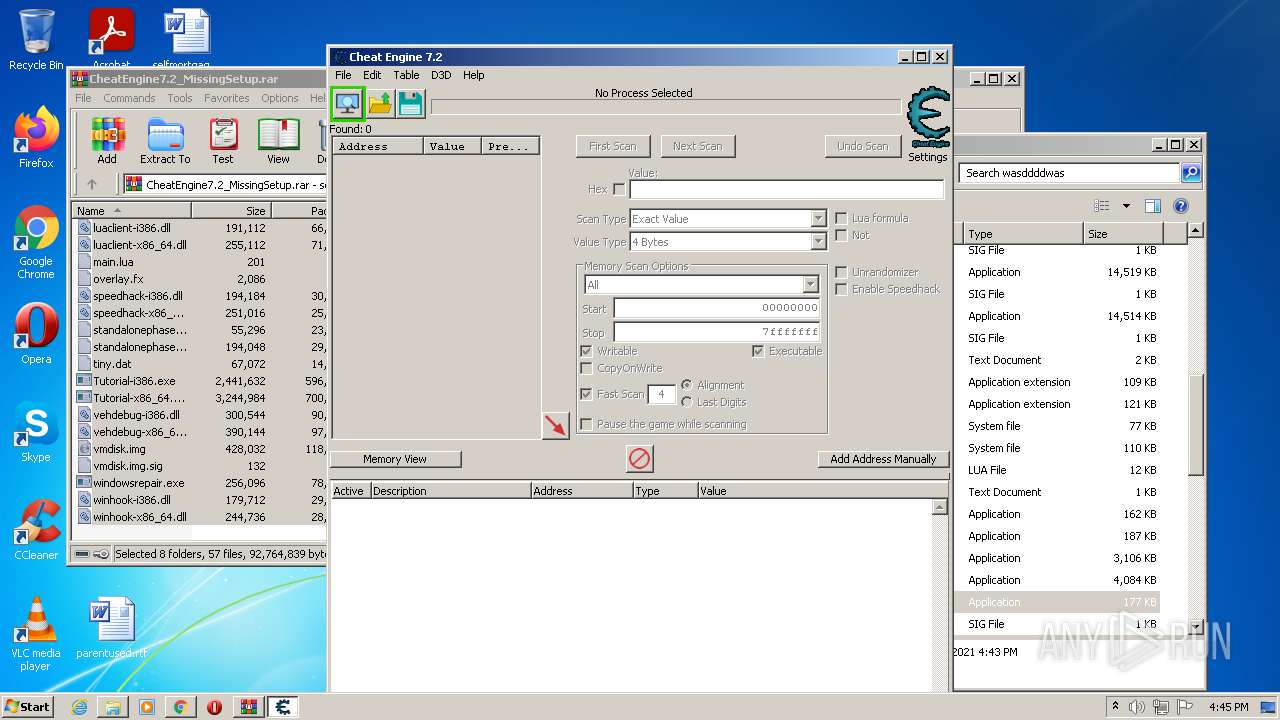
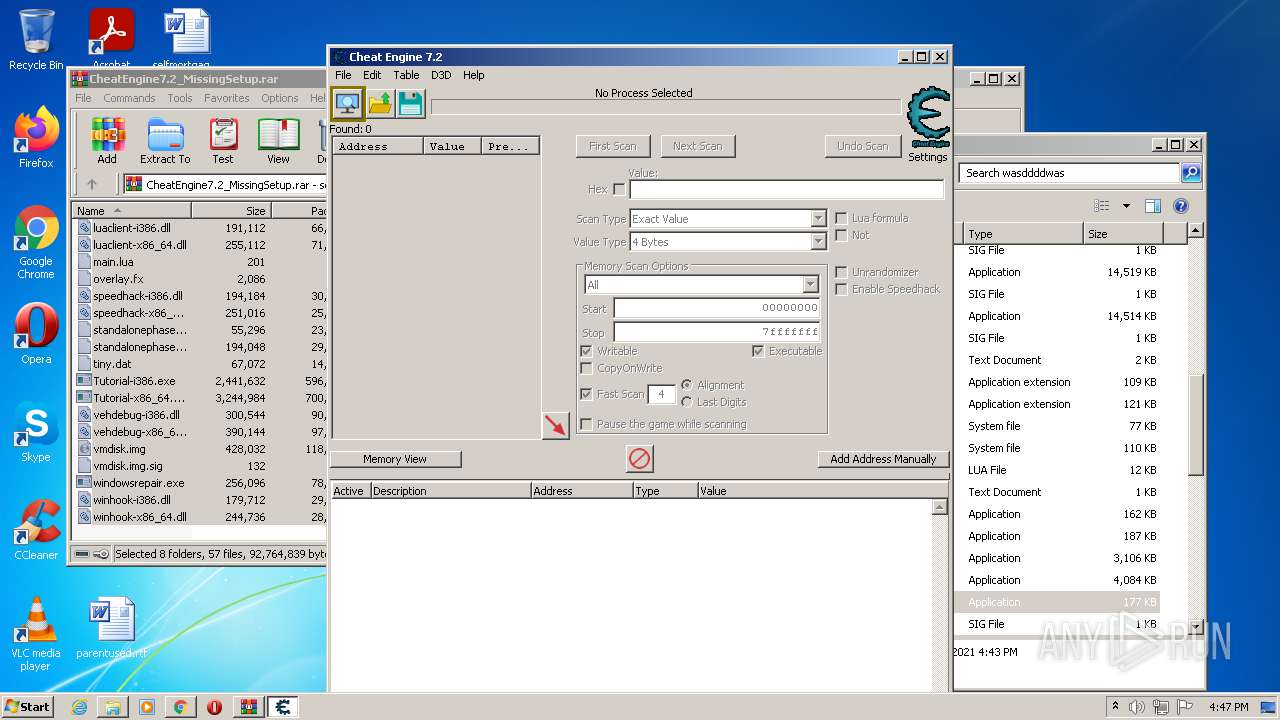
MALICIOUS
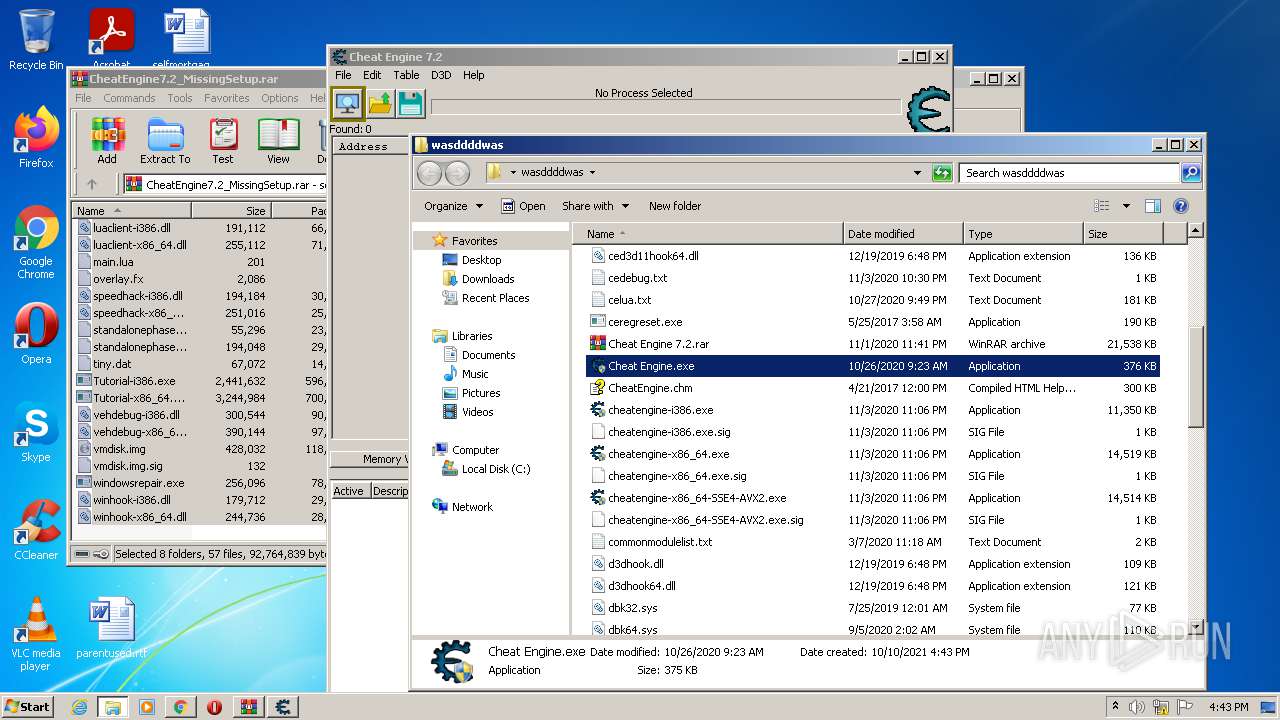
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2952)
- cheatengine-i386.exe (PID: 120)
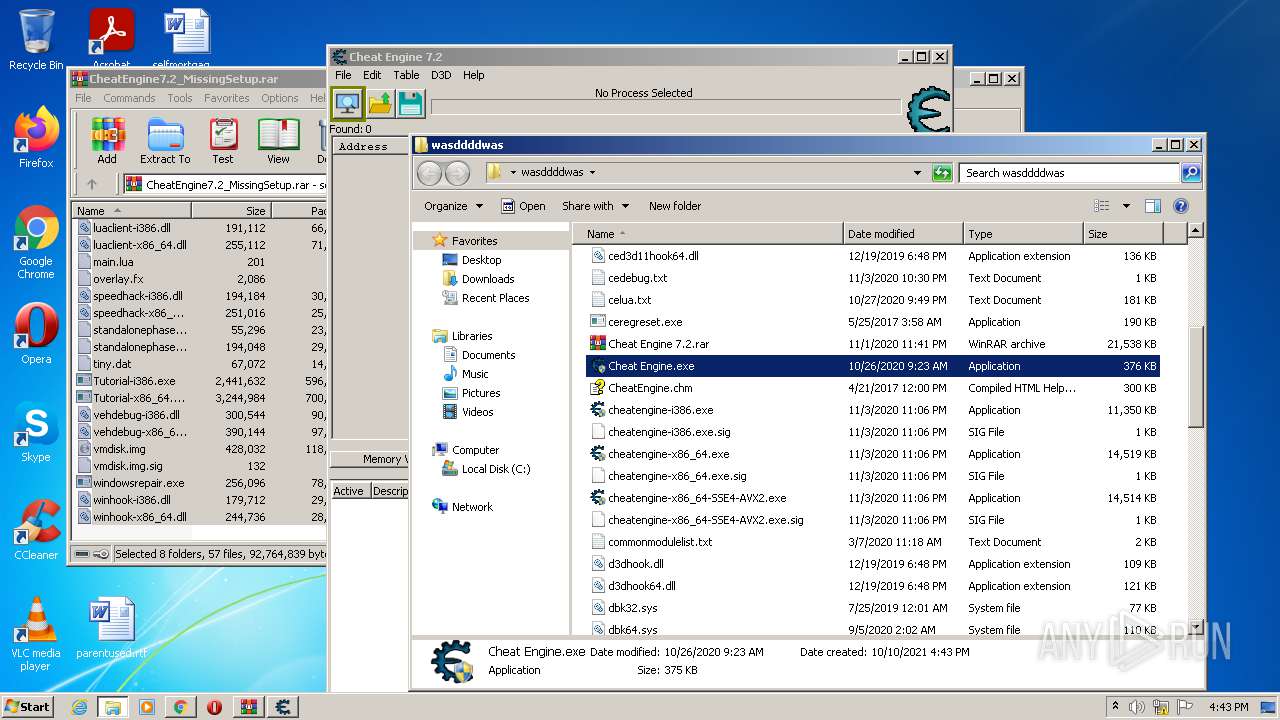
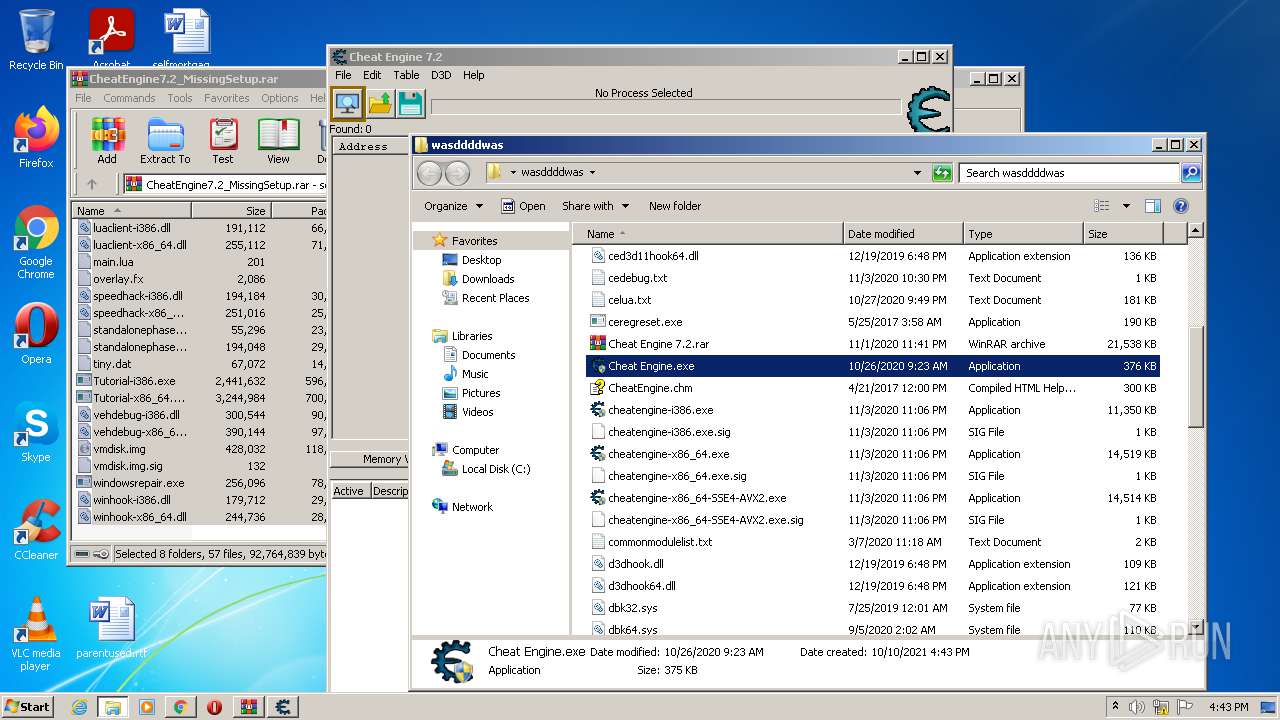
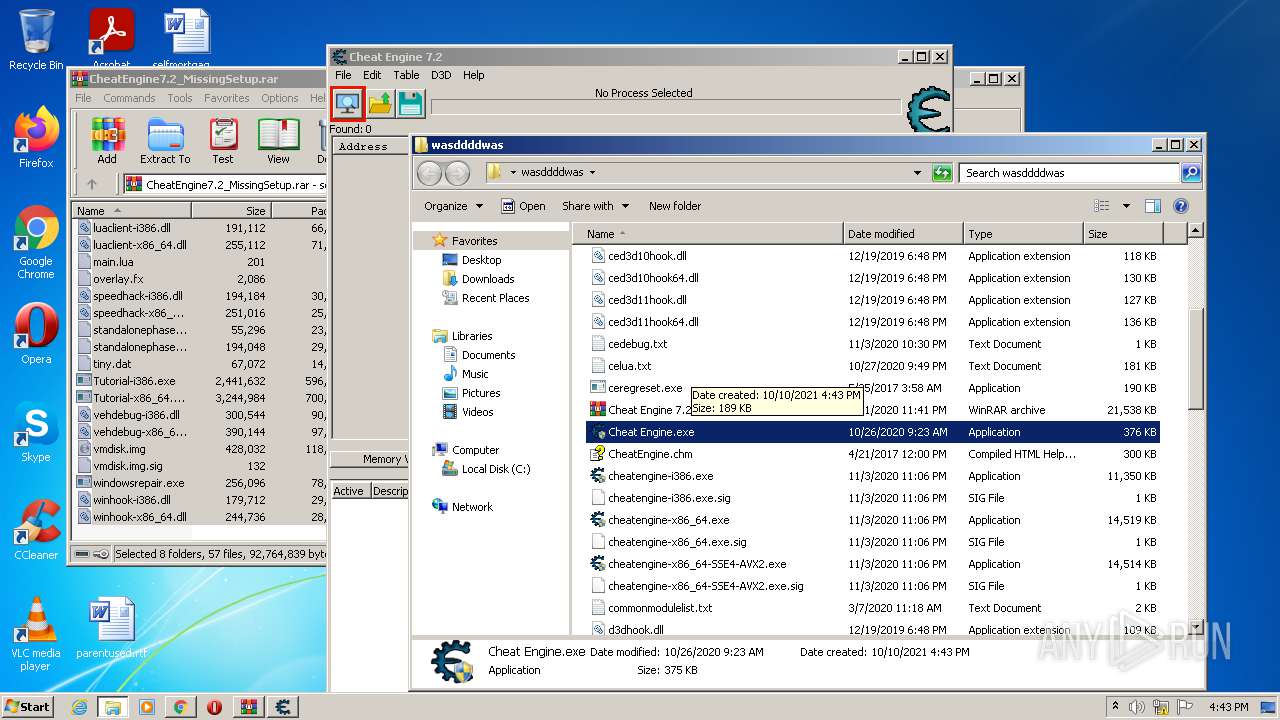
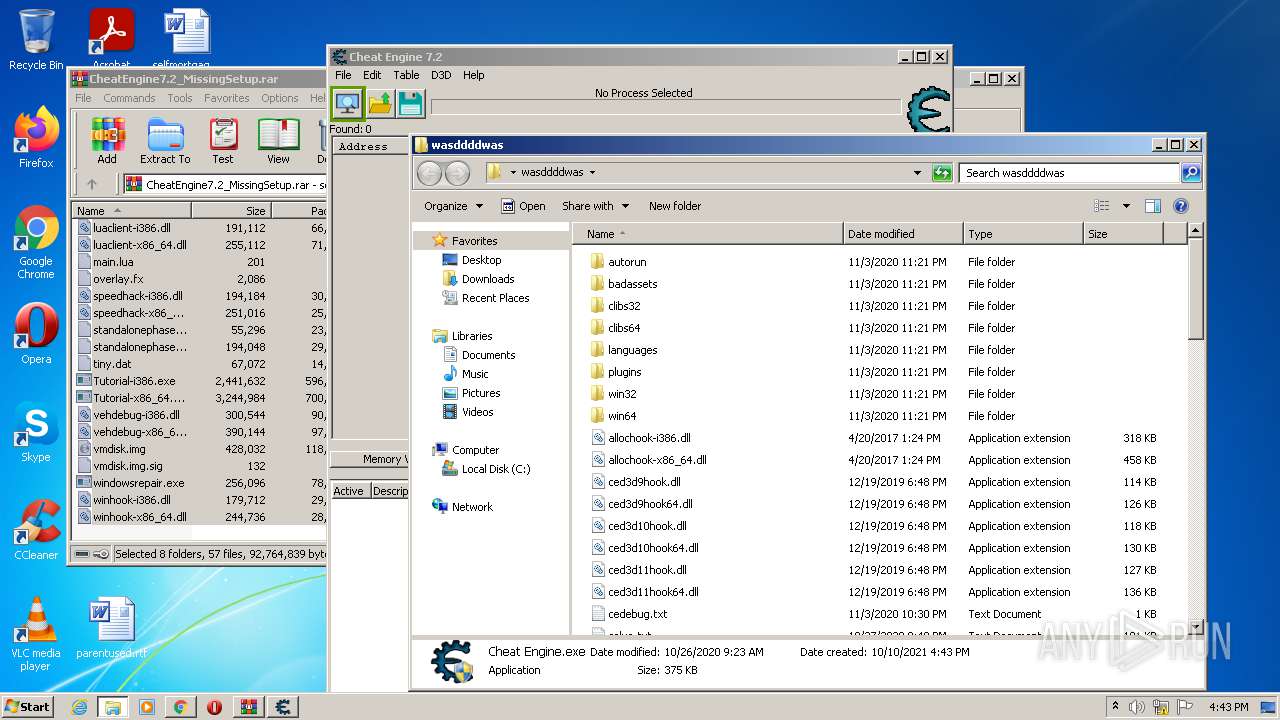
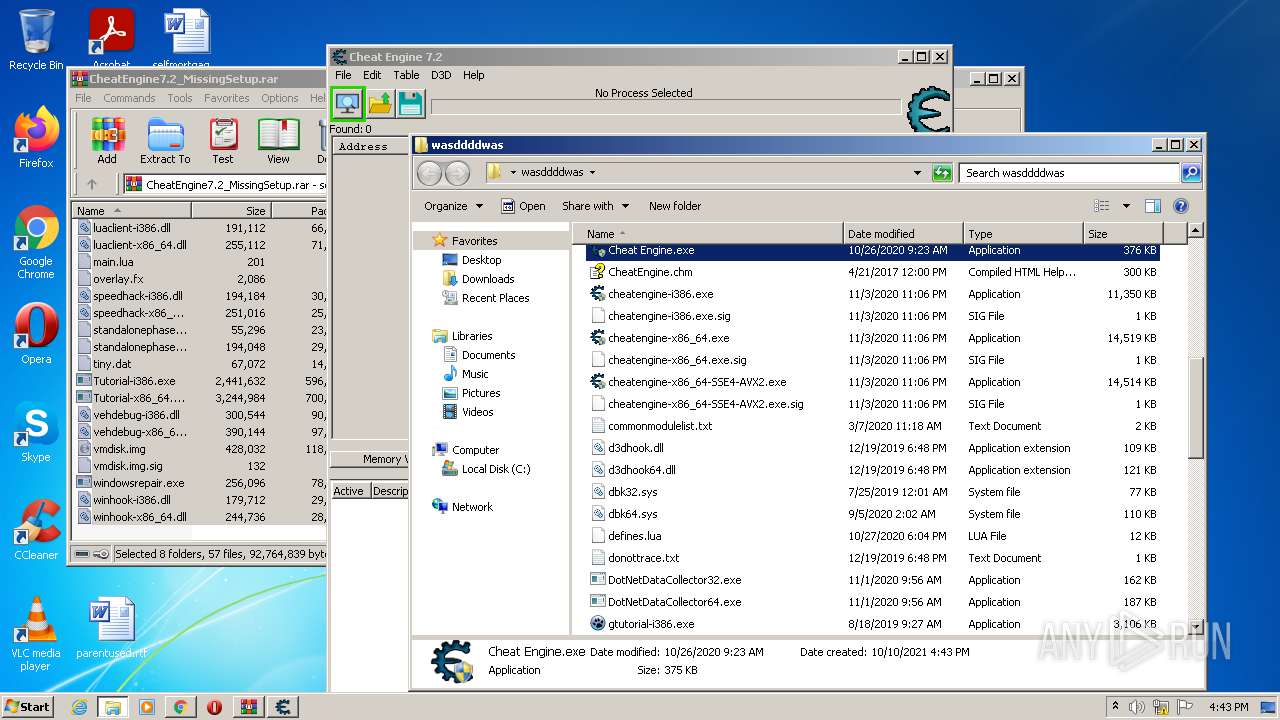
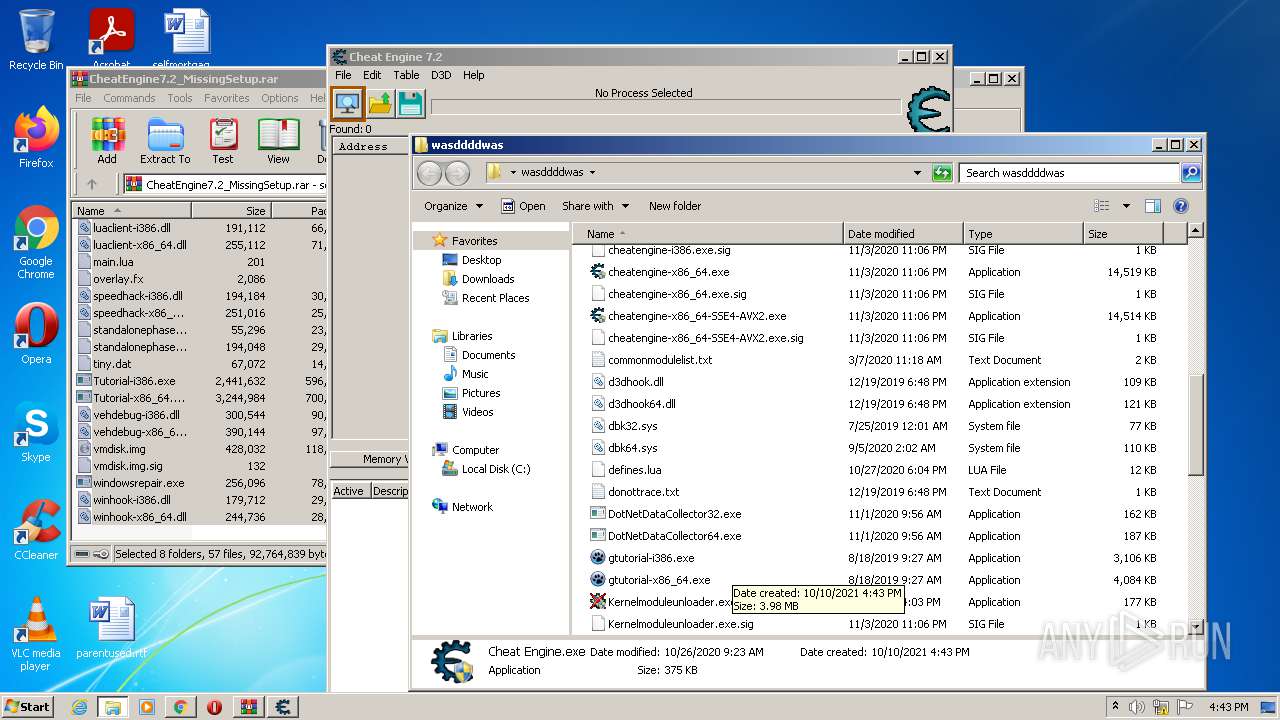
Application was dropped or rewritten from another process
- Cheat Engine.exe (PID: 3148)
- Cheat Engine.exe (PID: 2100)
- cheatengine-i386.exe (PID: 120)
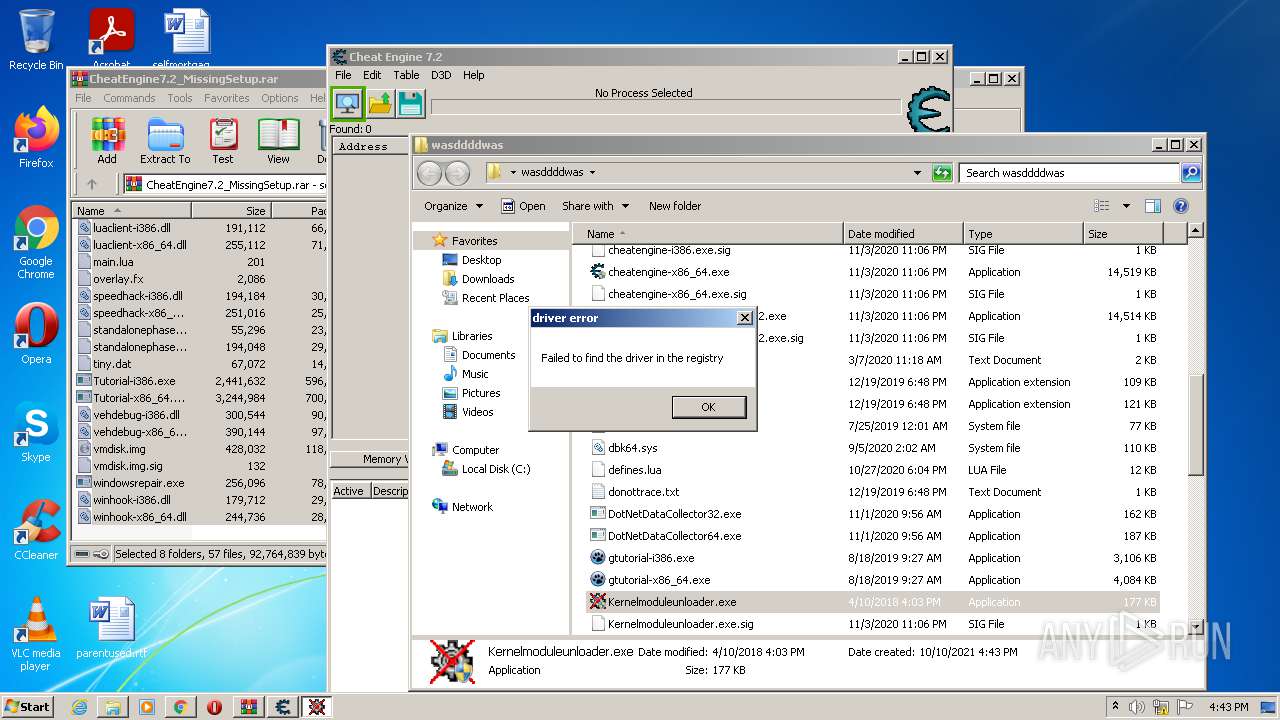
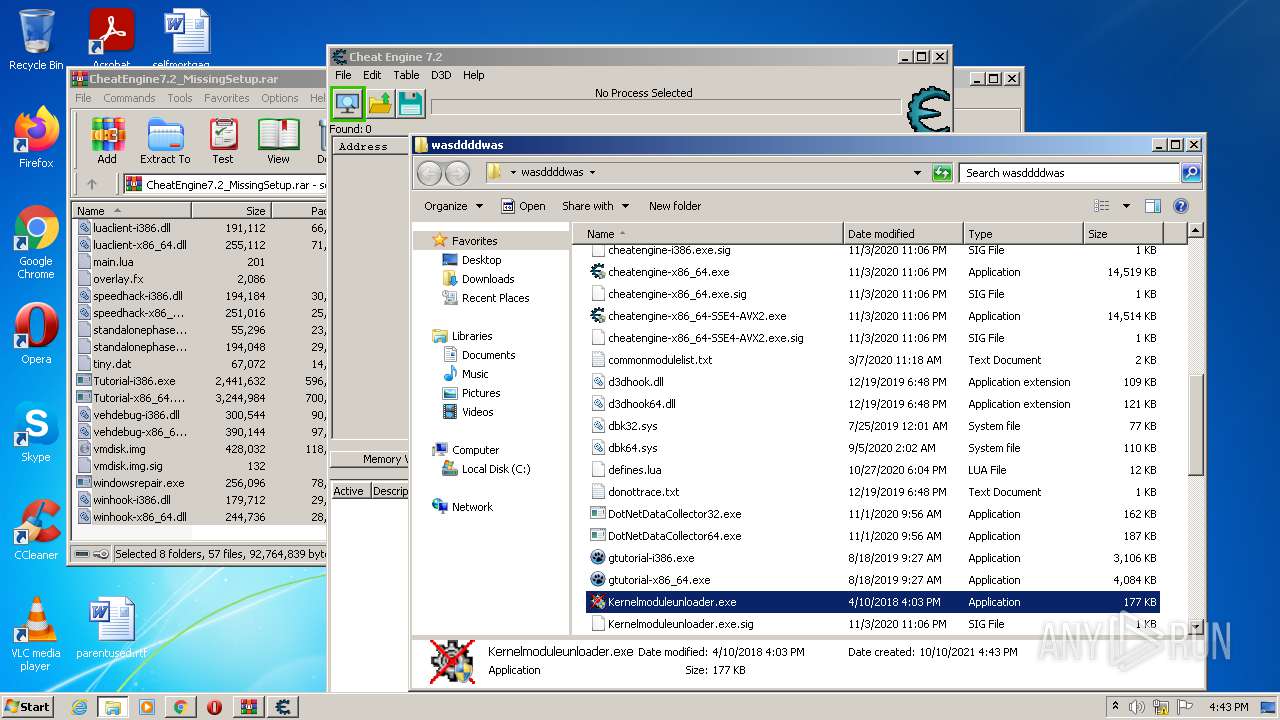
- Kernelmoduleunloader.exe (PID: 1060)
- Kernelmoduleunloader.exe (PID: 1584)
Drops executable file immediately after starts
- chrome.exe (PID: 2520)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3524)
- Cheat Engine.exe (PID: 2100)
- cheatengine-i386.exe (PID: 120)
- Kernelmoduleunloader.exe (PID: 1584)
Reads the computer name
- WinRAR.exe (PID: 3524)
- Cheat Engine.exe (PID: 2100)
- cheatengine-i386.exe (PID: 120)
- Kernelmoduleunloader.exe (PID: 1584)
Reads default file associations for system extensions
- WinRAR.exe (PID: 3524)
- SearchProtocolHost.exe (PID: 2952)
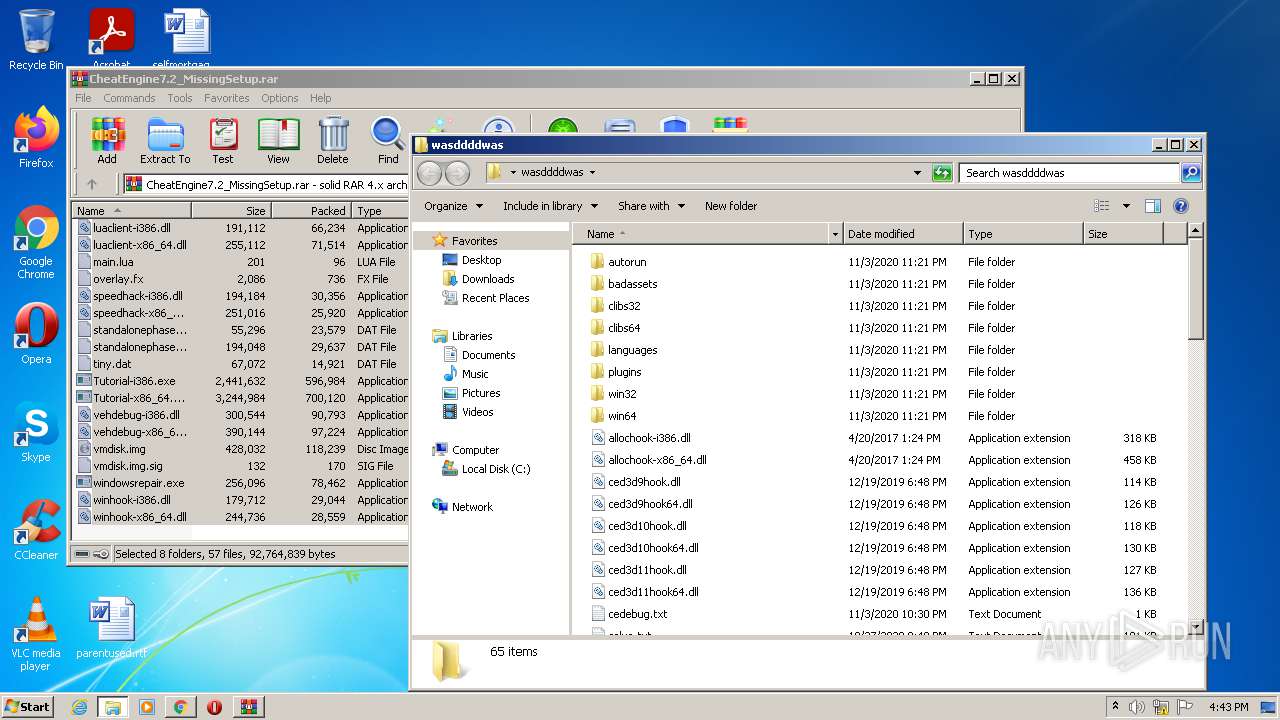
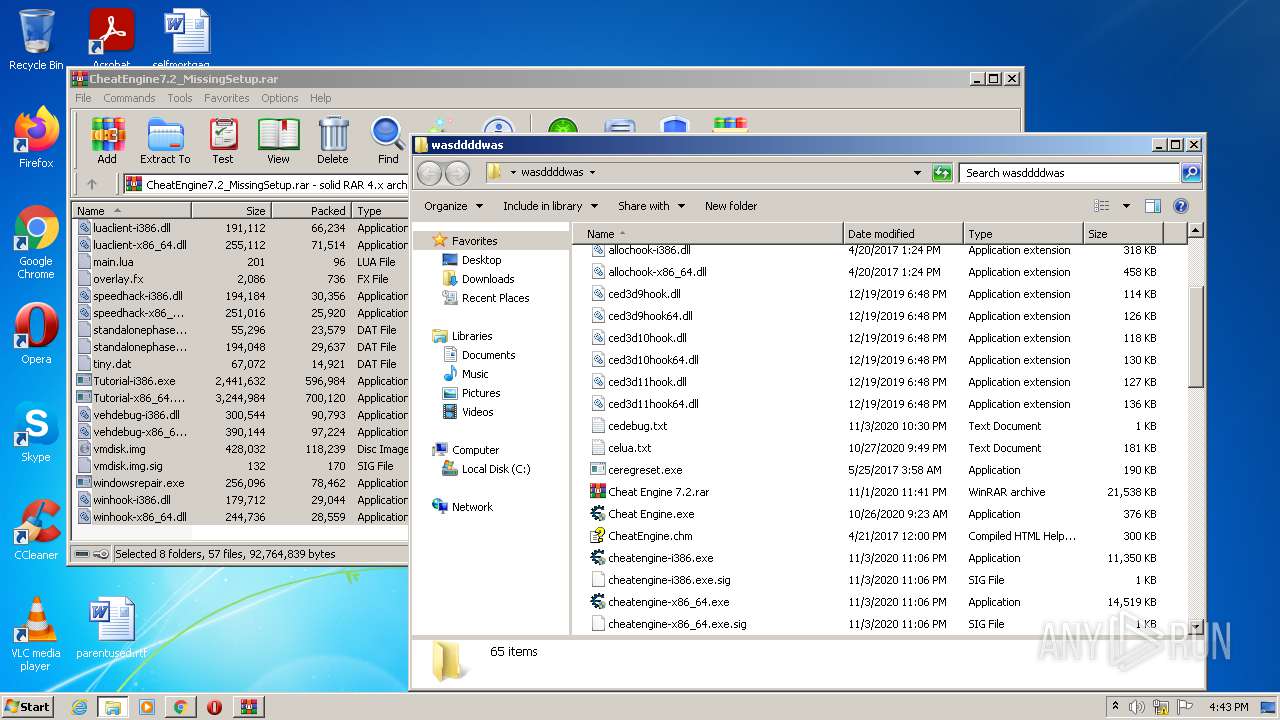
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3524)
- chrome.exe (PID: 2520)
Drops a file with too old compile date
- WinRAR.exe (PID: 3524)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3524)
- chrome.exe (PID: 2520)
INFO
Checks supported languages
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2012)
- chrome.exe (PID: 1832)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 920)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 2968)
- chrome.exe (PID: 1300)
- chrome.exe (PID: 3364)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 1800)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 1912)
Reads the computer name
- chrome.exe (PID: 3092)
- chrome.exe (PID: 920)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 3752)
Reads the hosts file
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3728)
Reads settings of System Certificates
- chrome.exe (PID: 3728)
Application launched itself
- chrome.exe (PID: 3092)
Reads the date of Windows installation
- chrome.exe (PID: 2624)
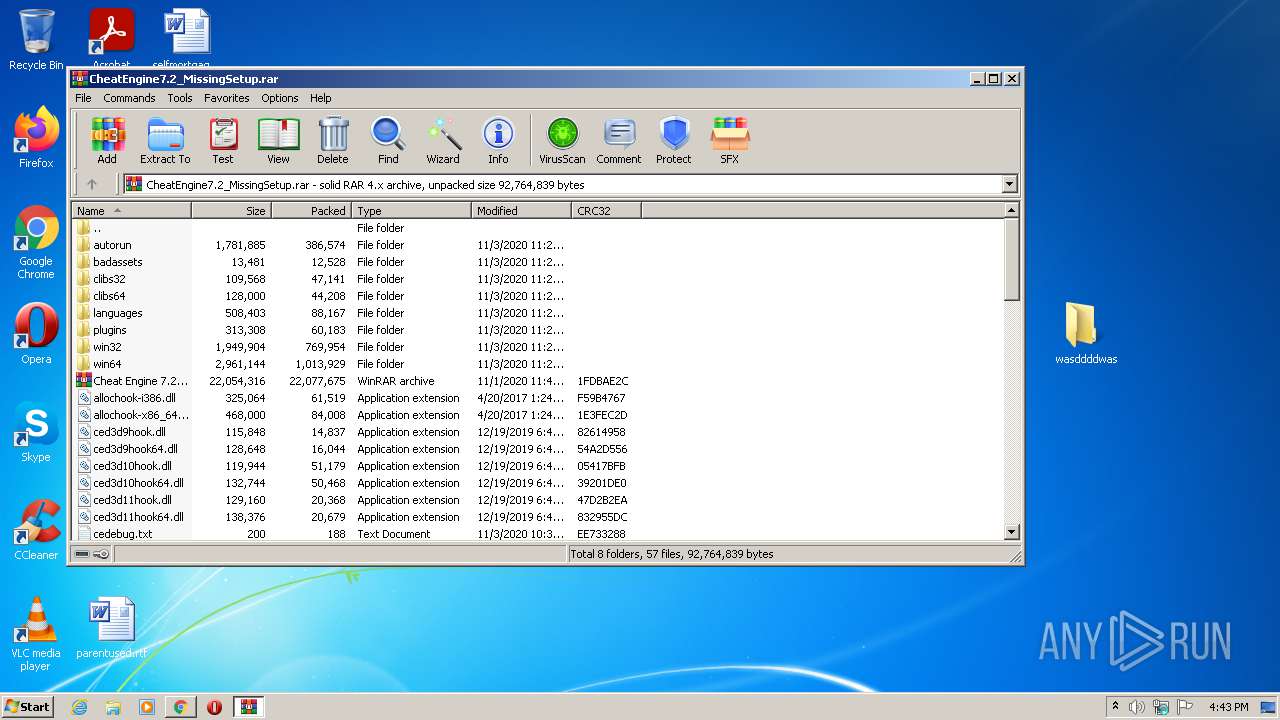
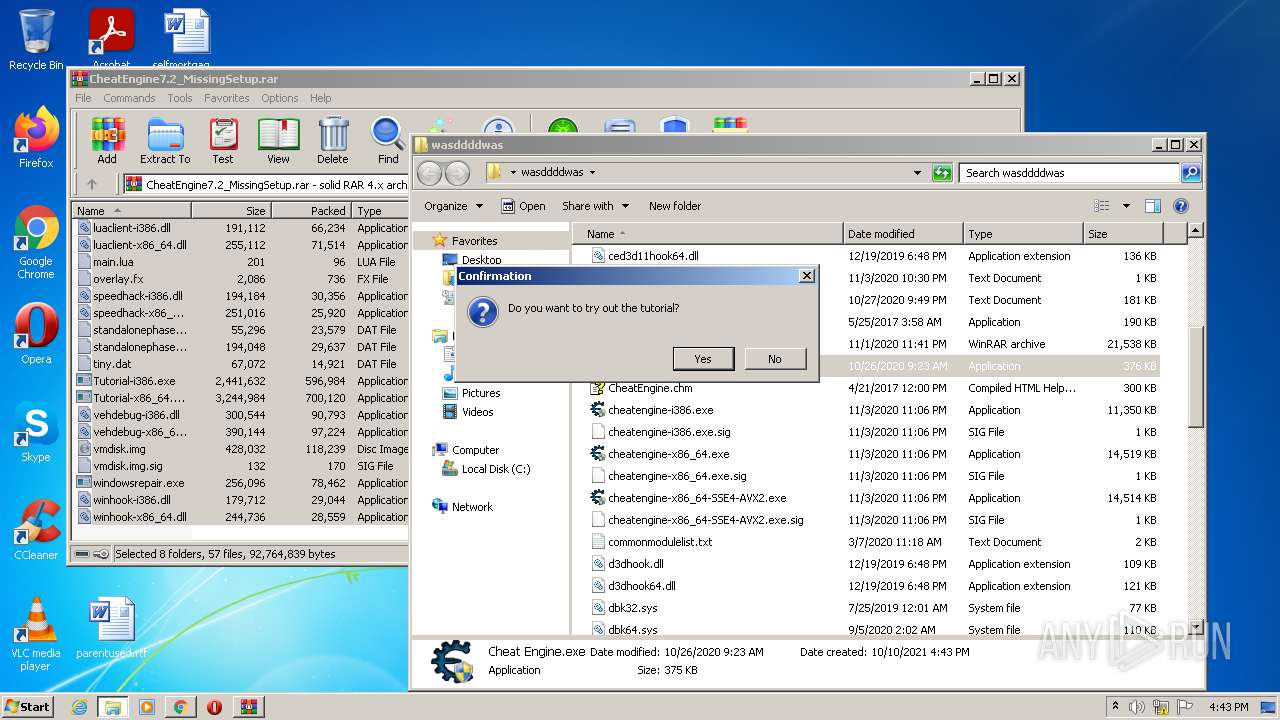
Manual execution by user
- Cheat Engine.exe (PID: 3148)
- Cheat Engine.exe (PID: 2100)
- Kernelmoduleunloader.exe (PID: 1060)
- Kernelmoduleunloader.exe (PID: 1584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
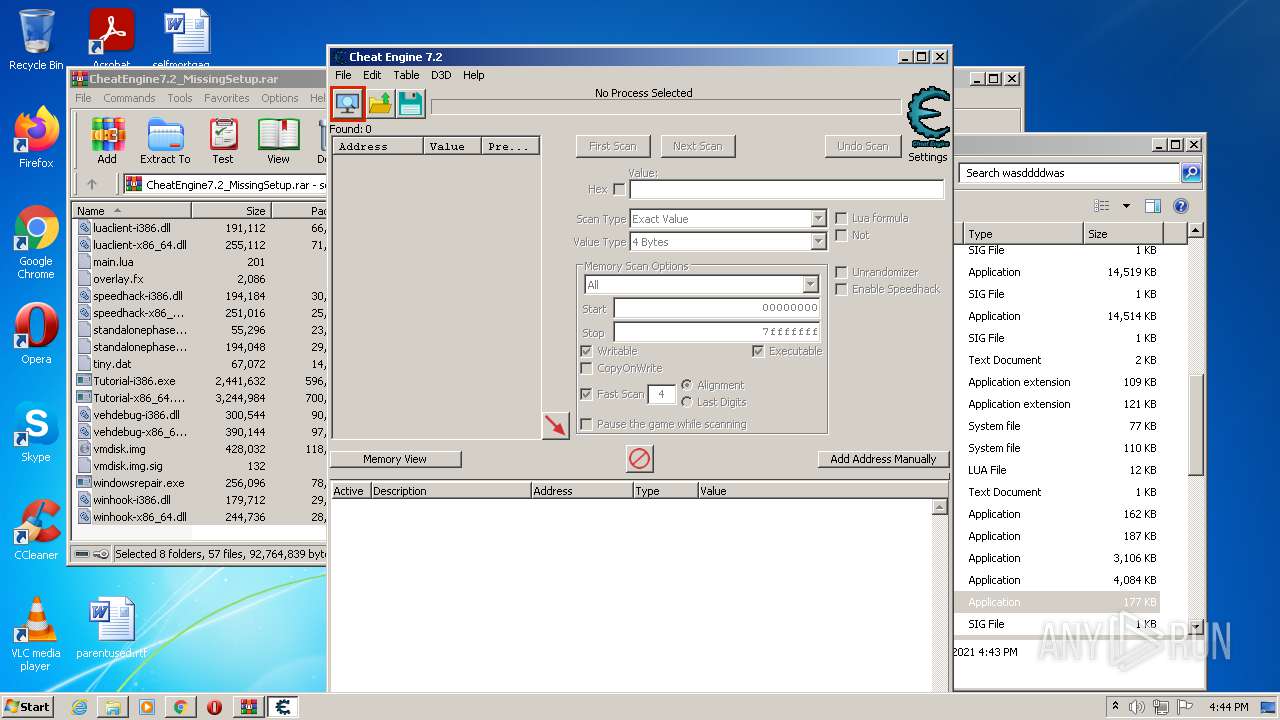
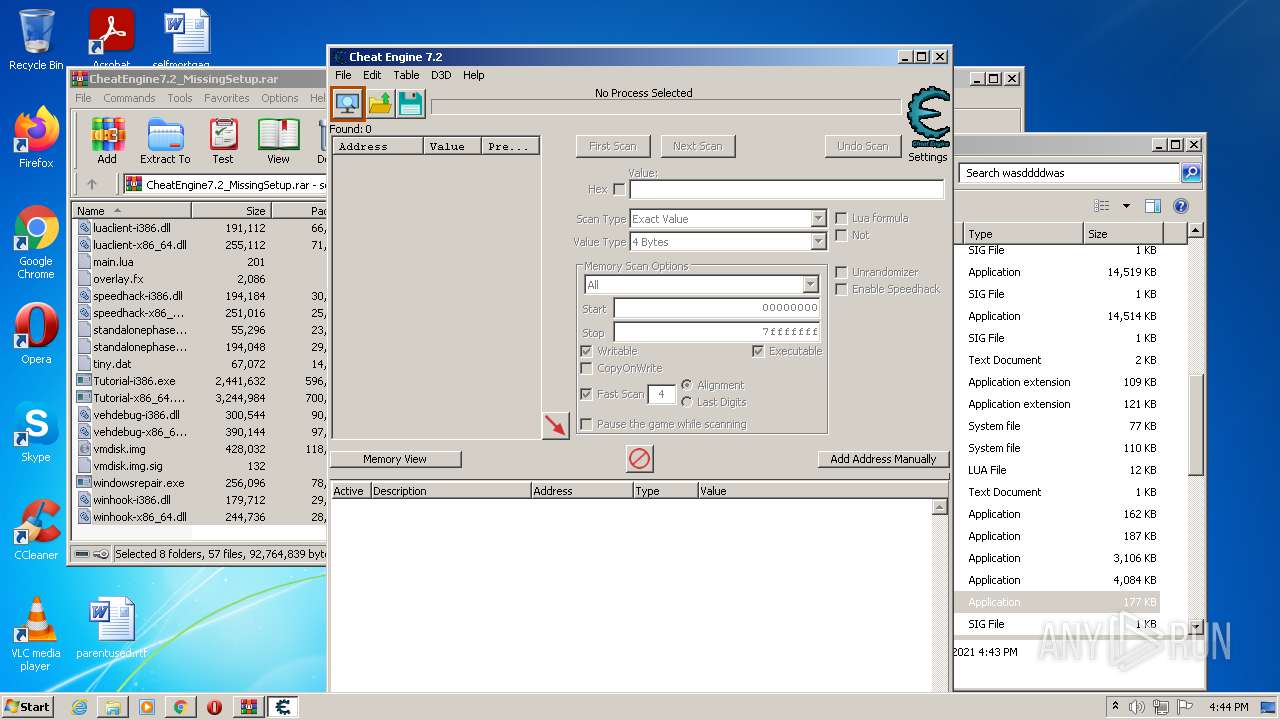
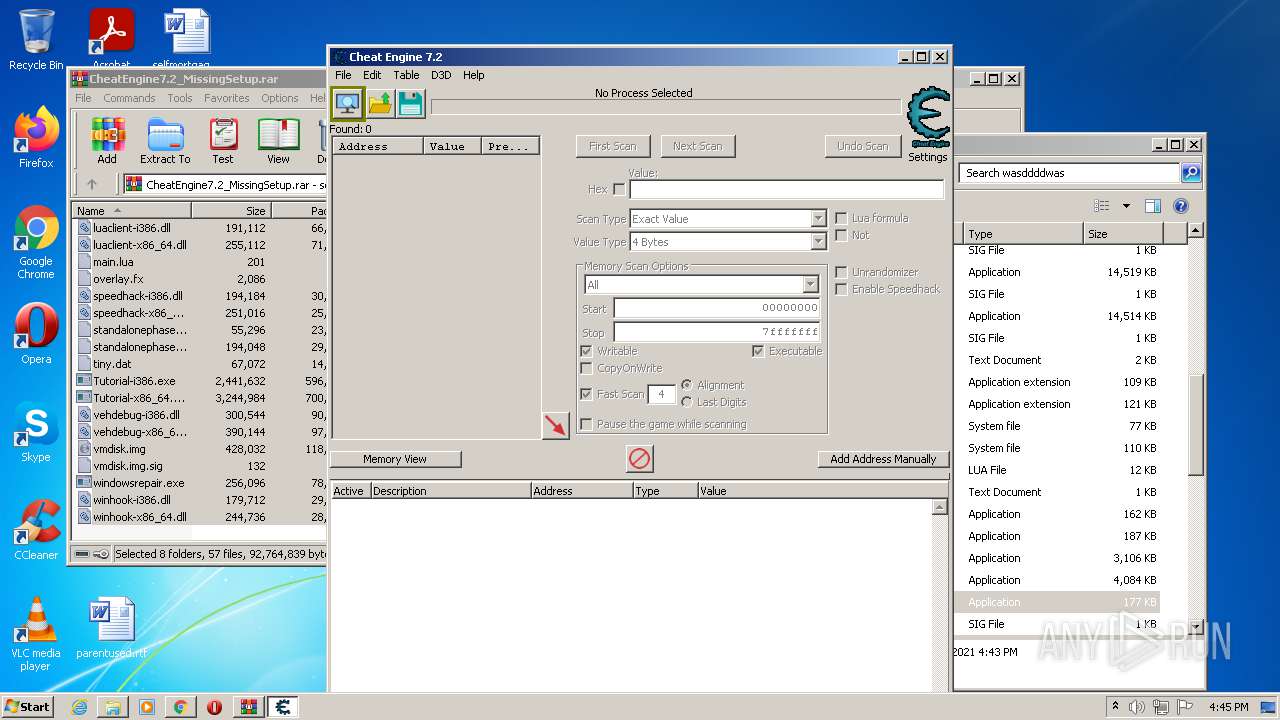
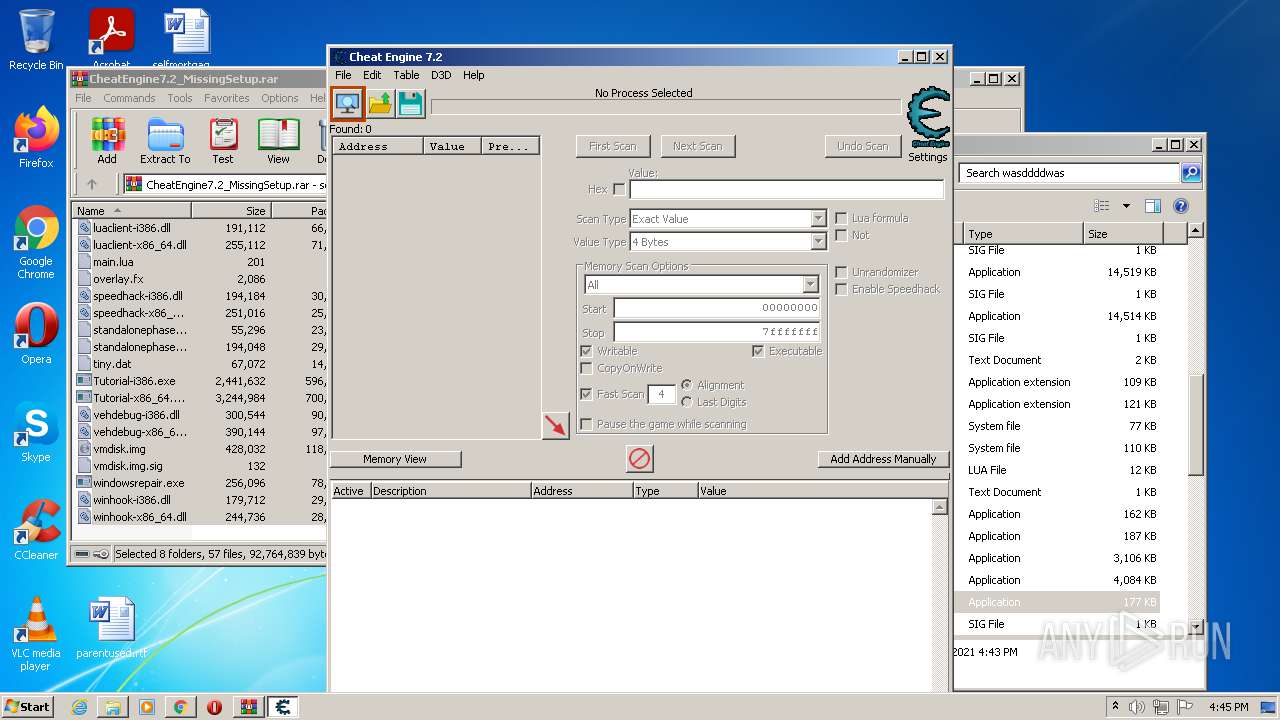
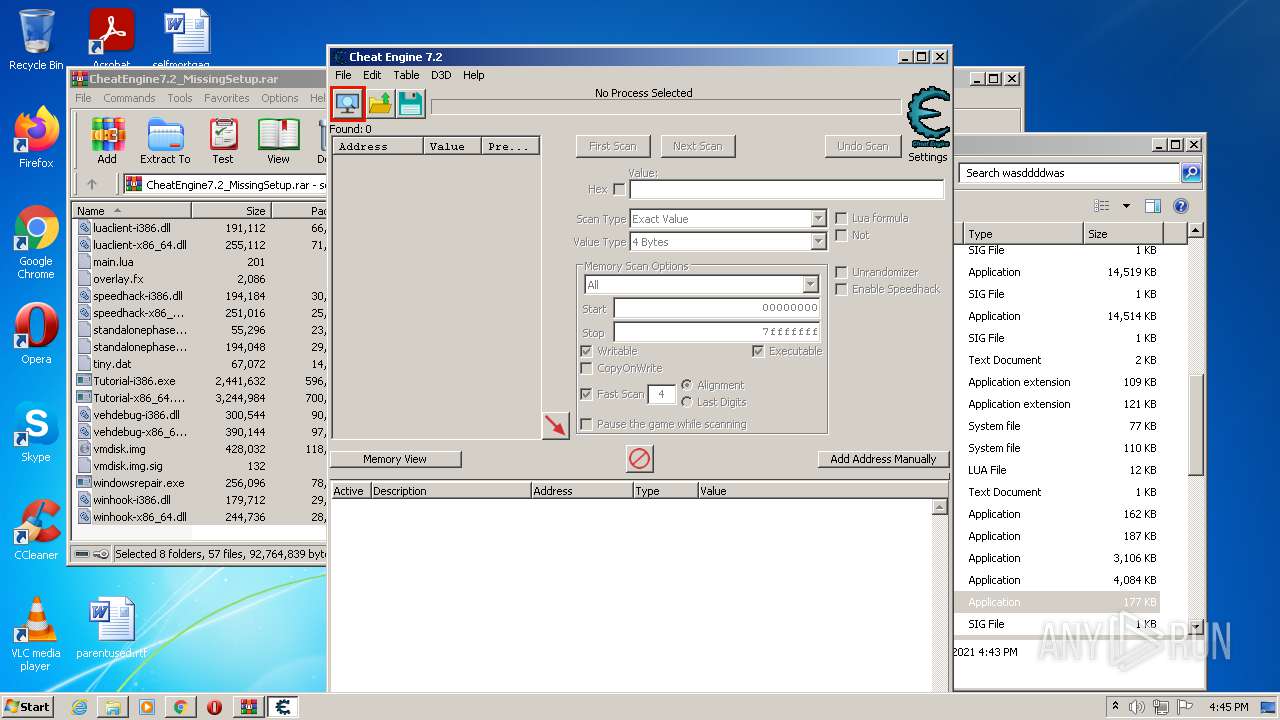
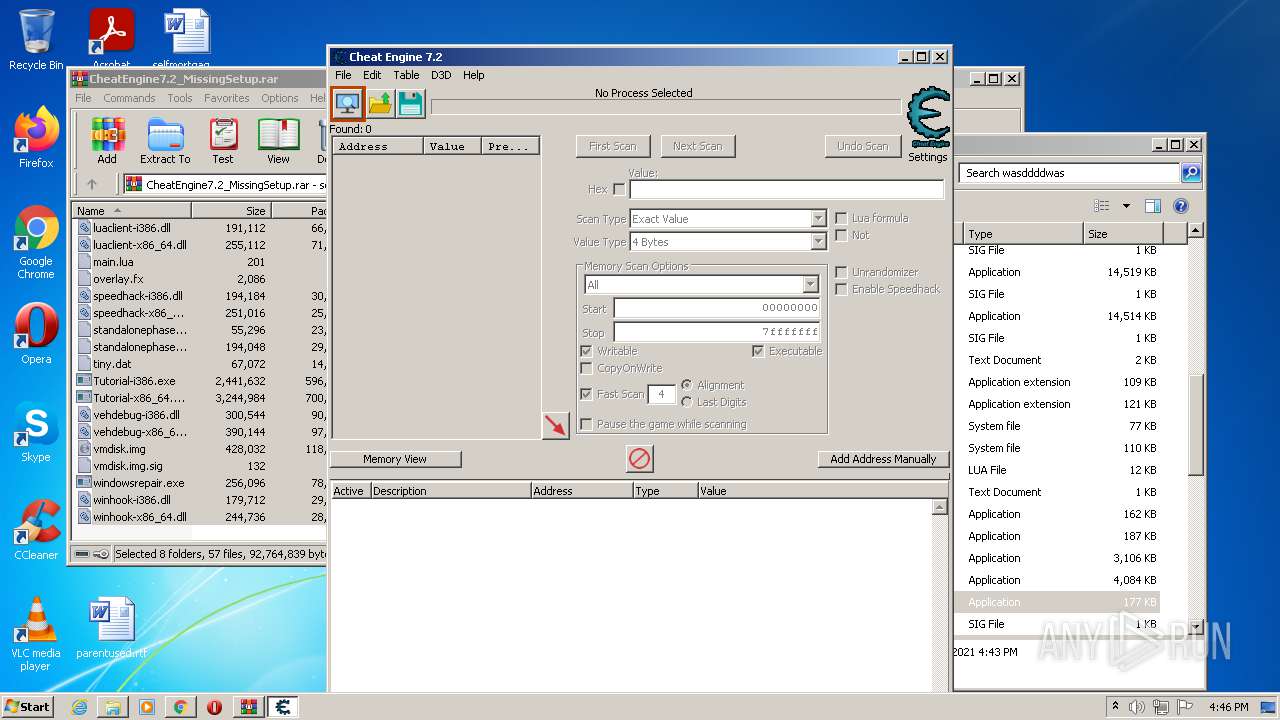
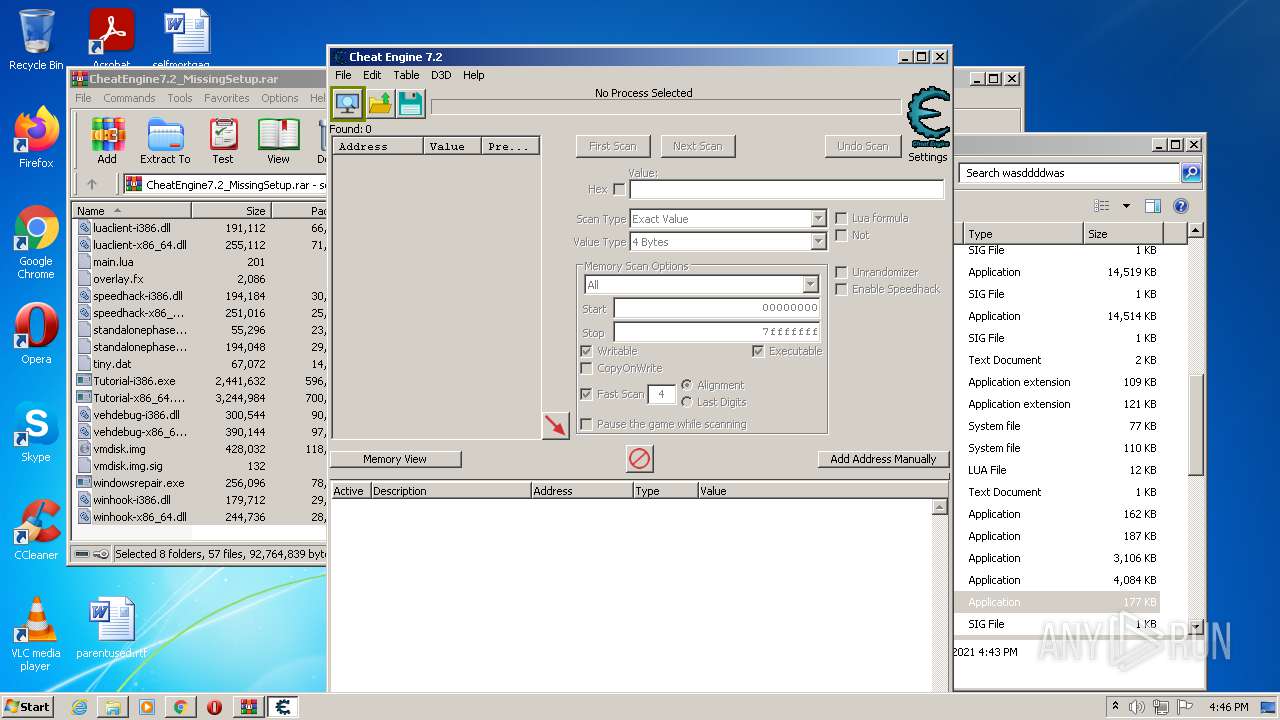
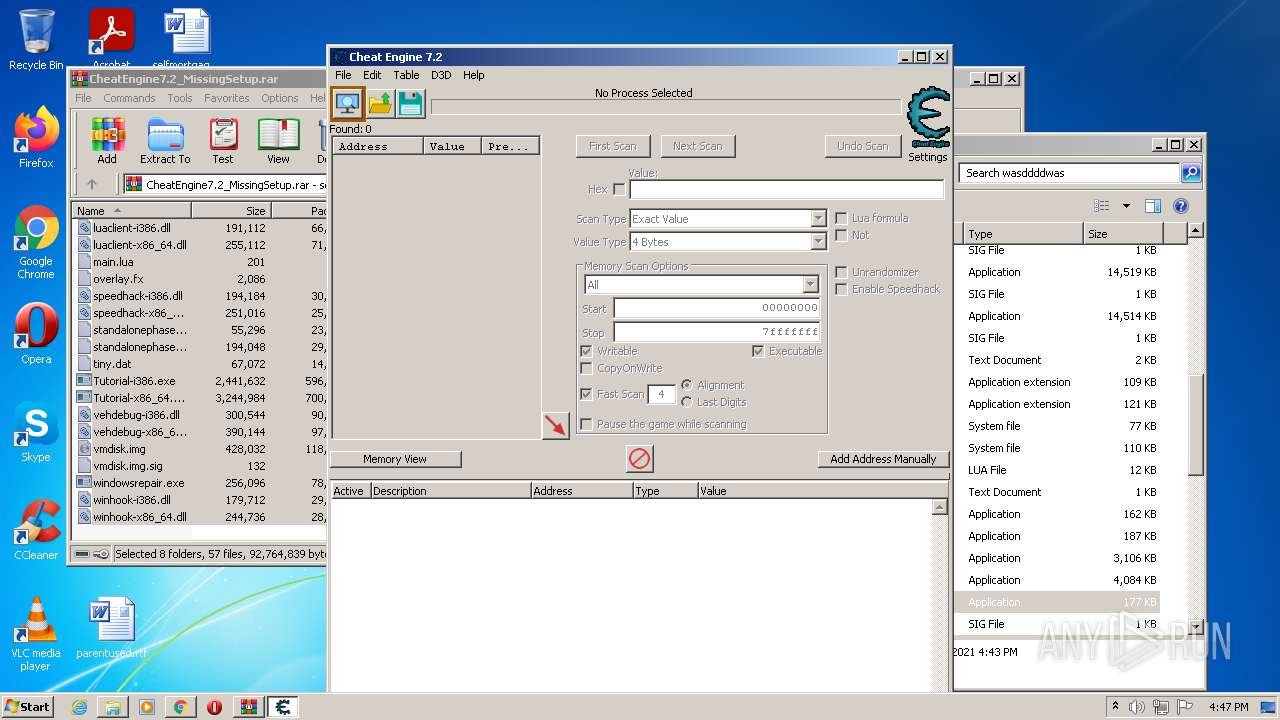
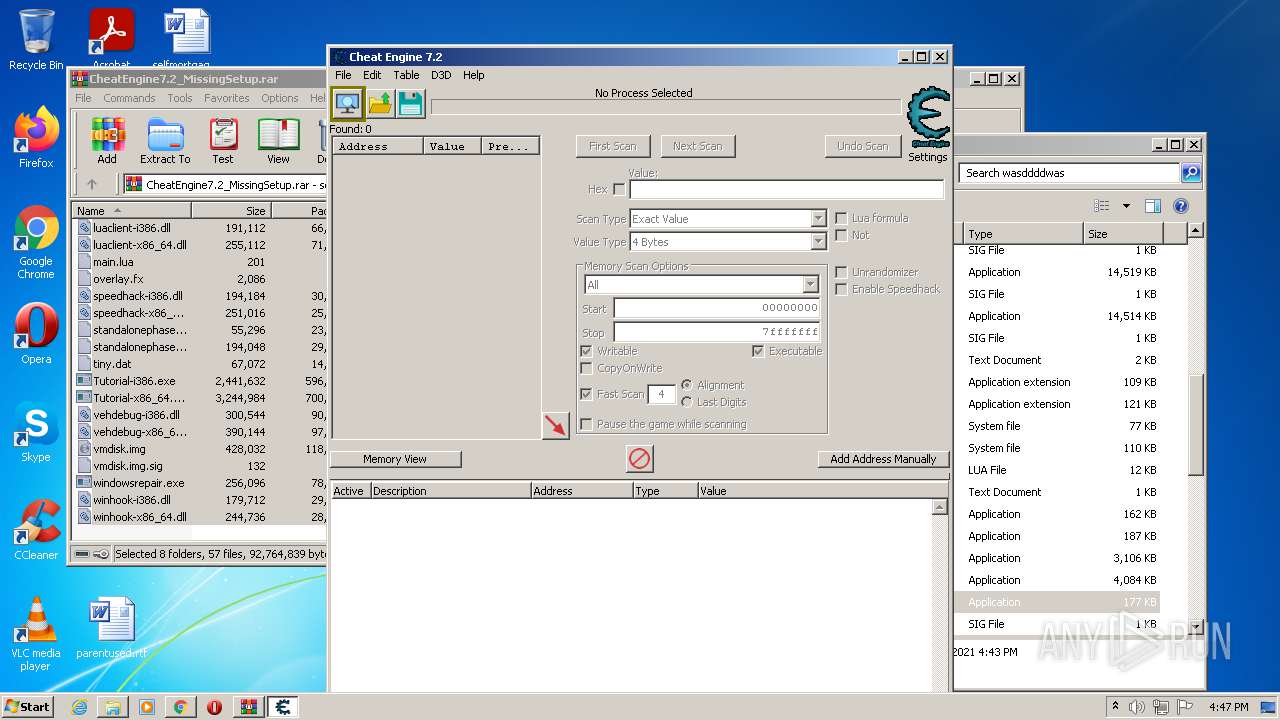
Total processes
77
Monitored processes
33
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
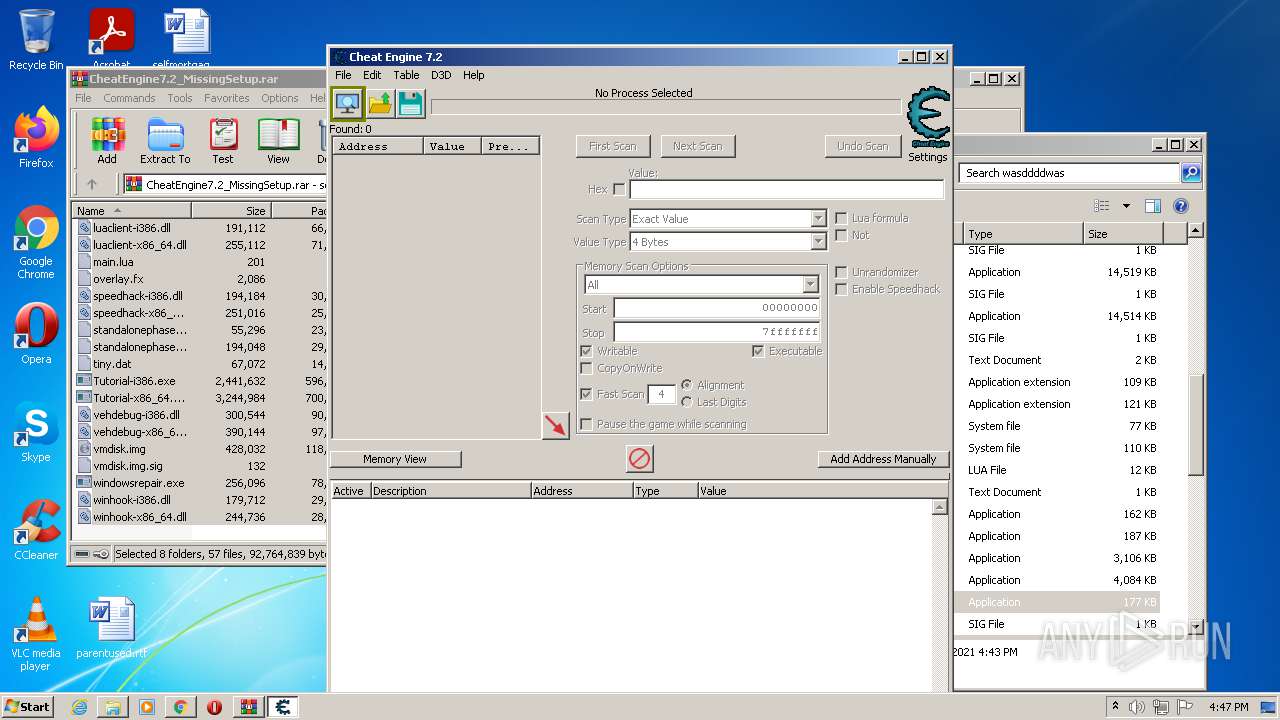
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
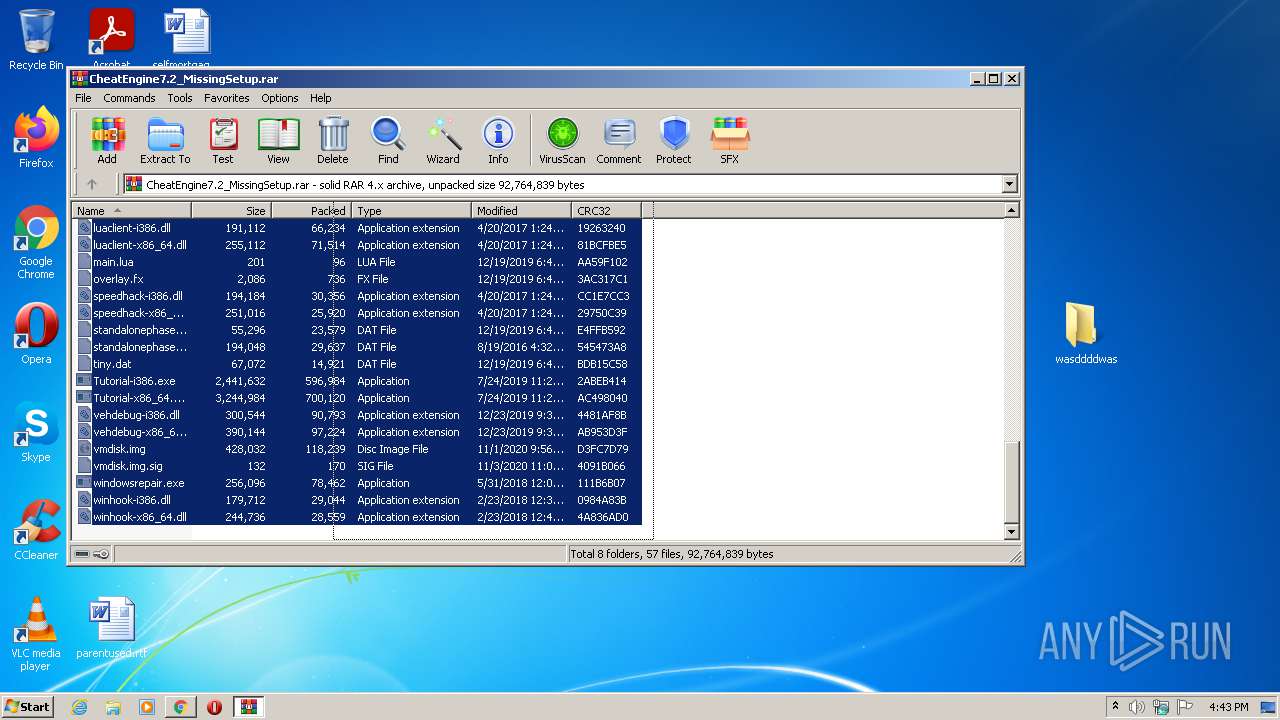
| 120 | "C:\Users\admin\Desktop\wasddddwas\cheatengine-i386.exe" | C:\Users\admin\Desktop\wasddddwas\cheatengine-i386.exe | Cheat Engine.exe | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Exit code: 0 Version: 7.2.0.6541 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,2367599248051035986,2577628109455649624,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2656 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1060 | "C:\Users\admin\Desktop\wasddddwas\Kernelmoduleunloader.exe" | C:\Users\admin\Desktop\wasddddwas\Kernelmoduleunloader.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,2367599248051035986,2577628109455649624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2220 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,2367599248051035986,2577628109455649624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1584 | "C:\Users\admin\Desktop\wasddddwas\Kernelmoduleunloader.exe" | C:\Users\admin\Desktop\wasddddwas\Kernelmoduleunloader.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,2367599248051035986,2577628109455649624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1744 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6de5d988,0x6de5d998,0x6de5d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,2367599248051035986,2577628109455649624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,2367599248051035986,2577628109455649624,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
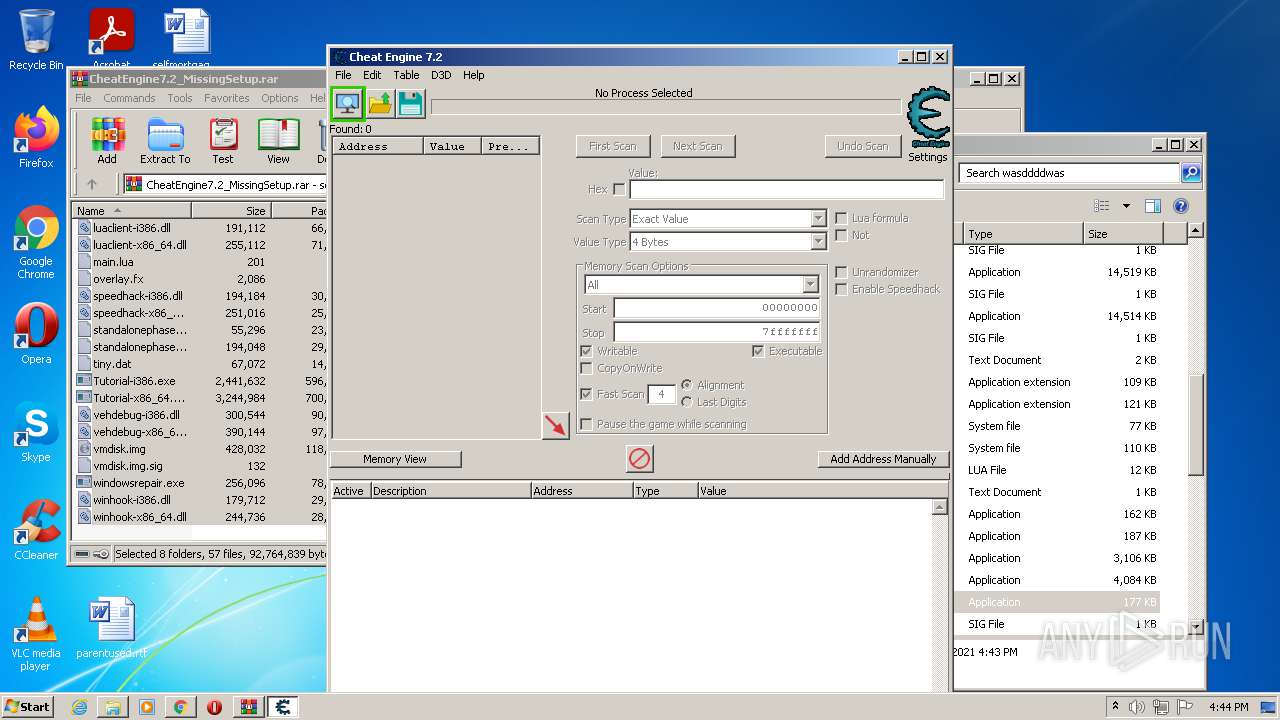
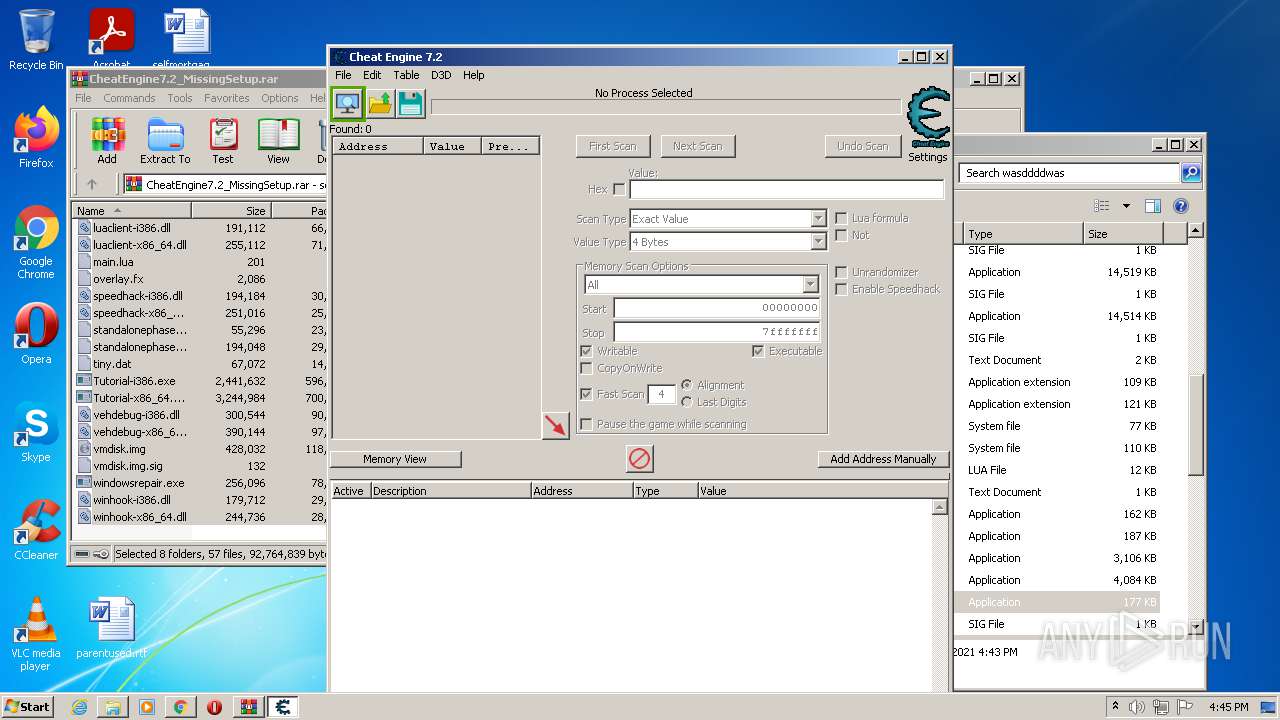
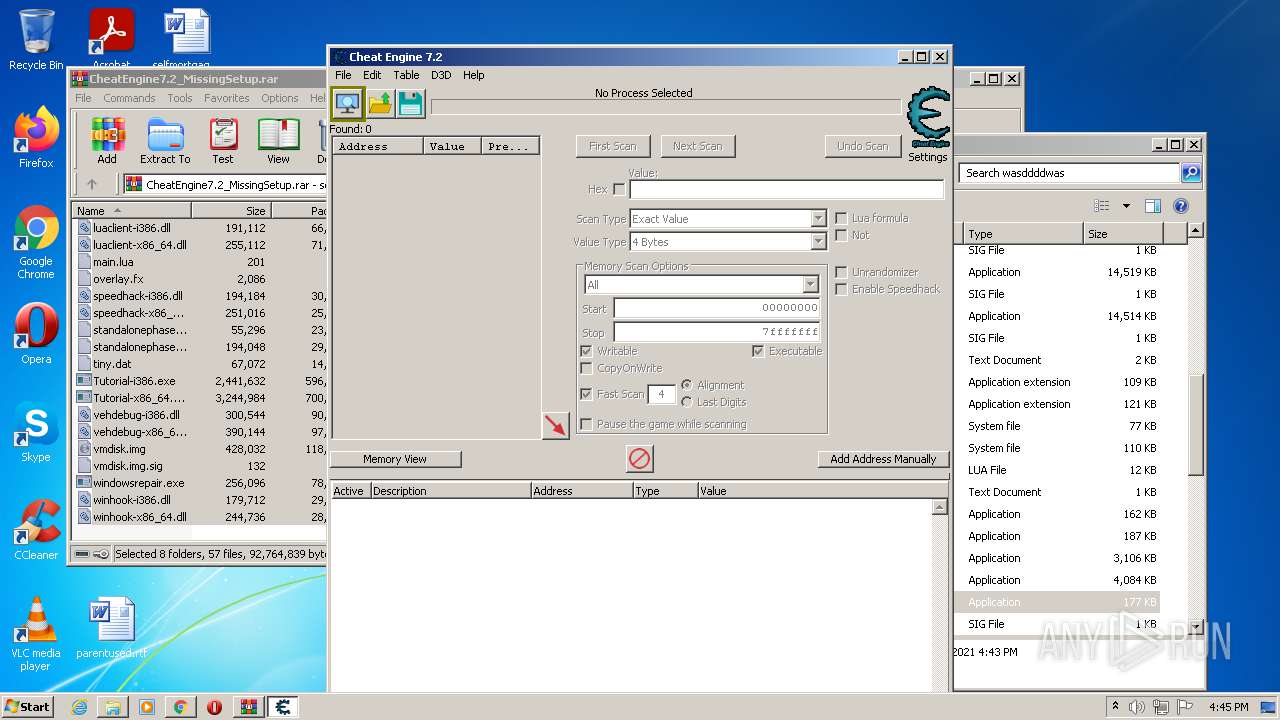
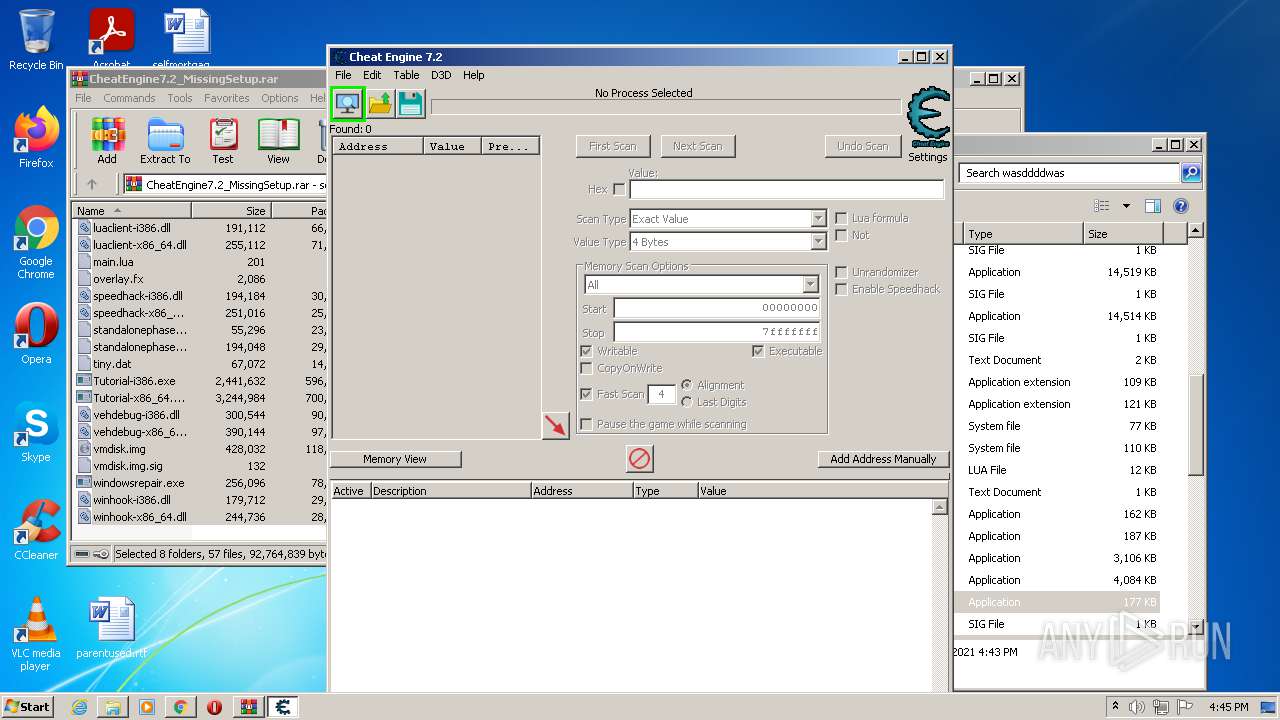
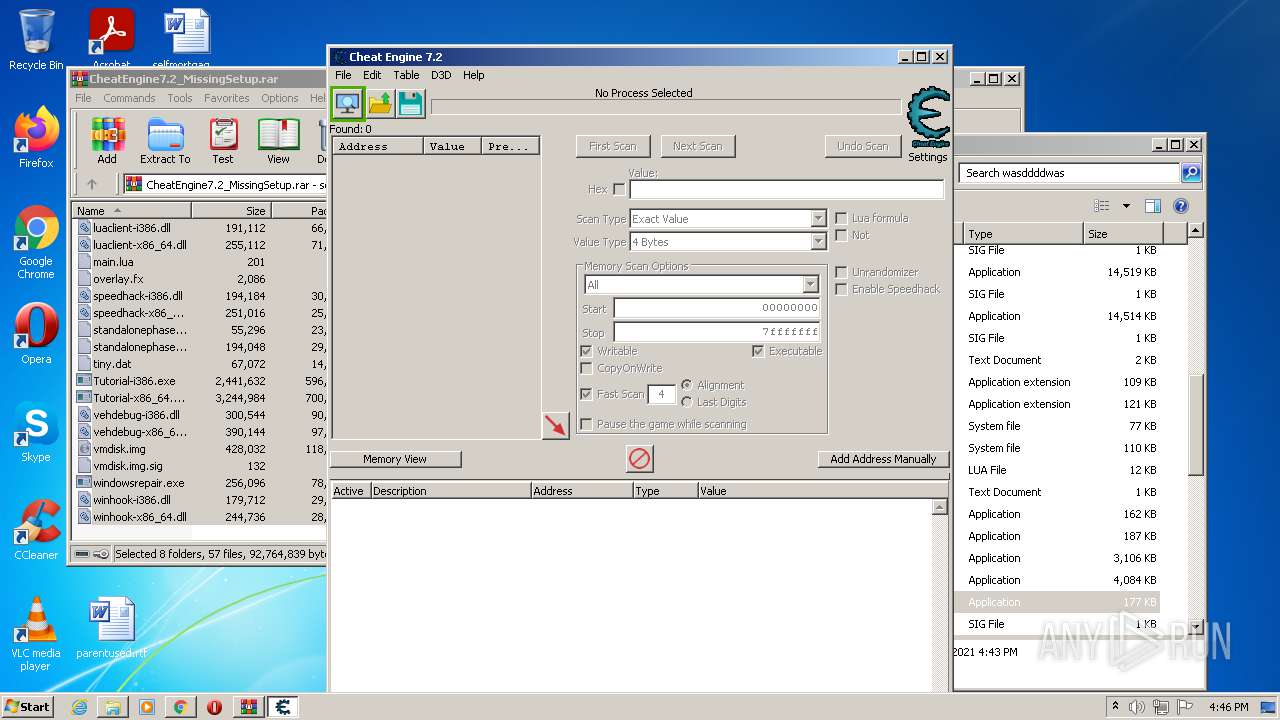
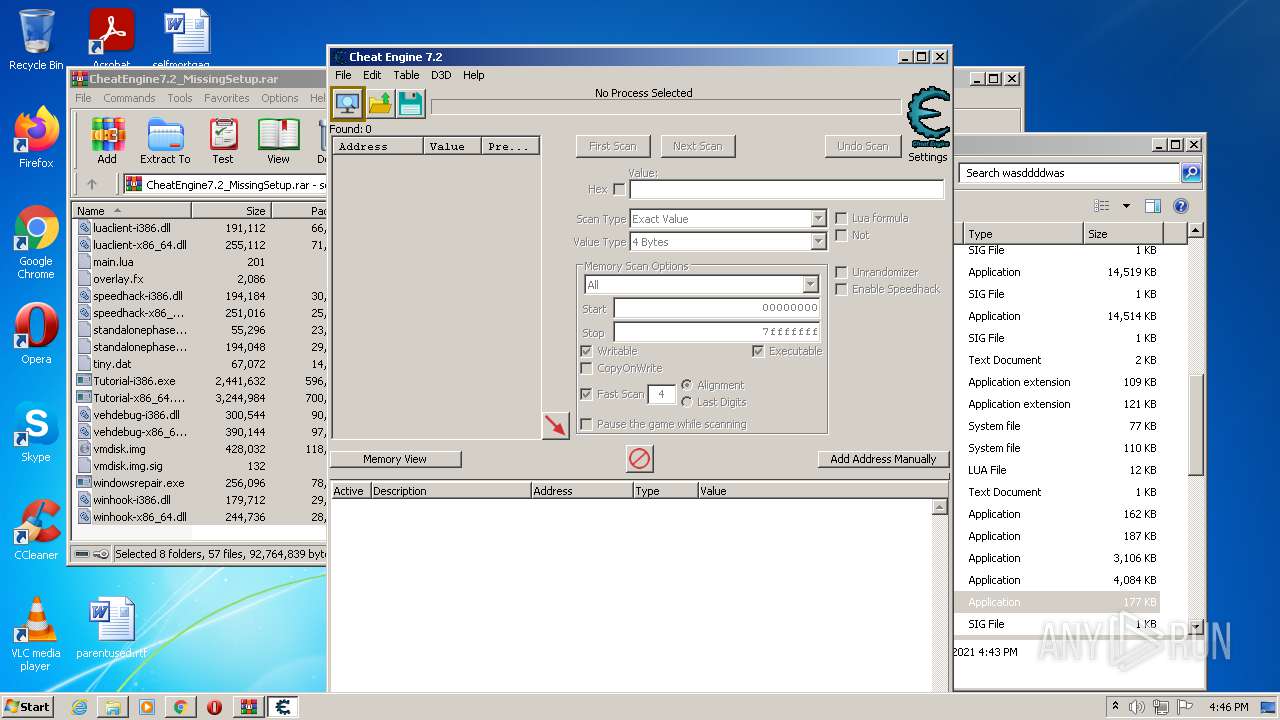
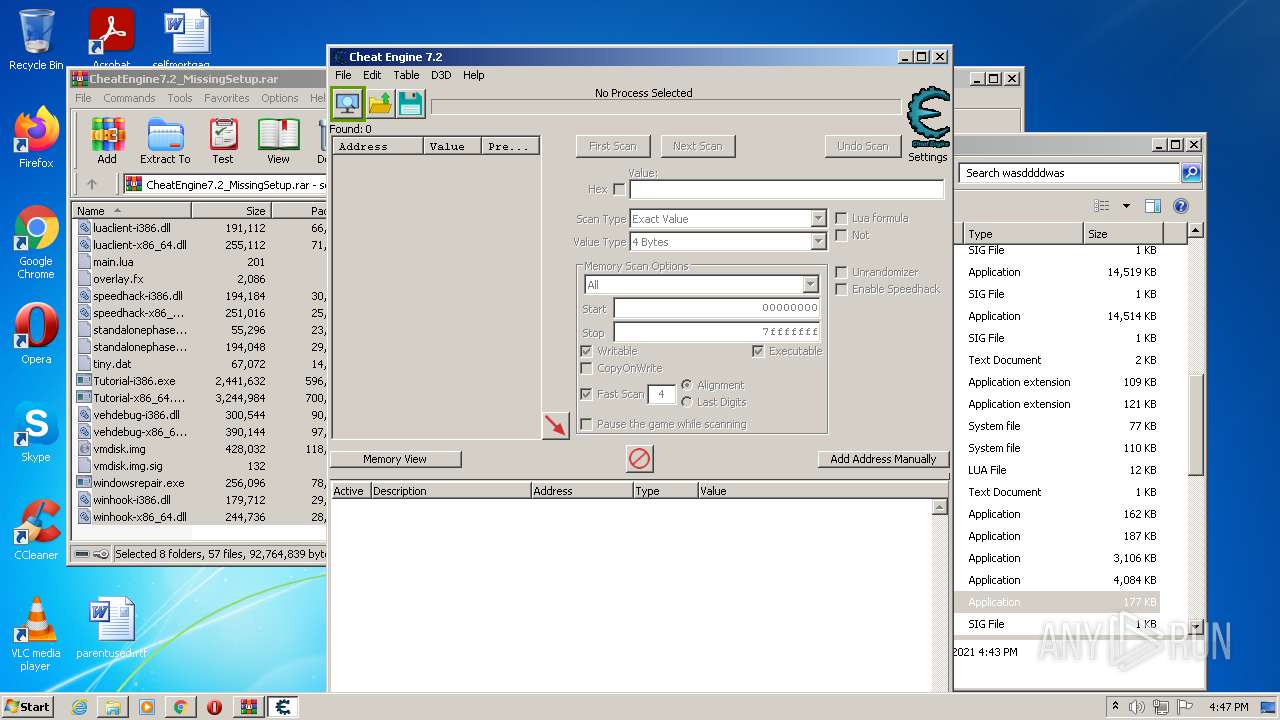
Total events
16 132
Read events
15 978
Write events
149
Delete events
5
Modification events
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
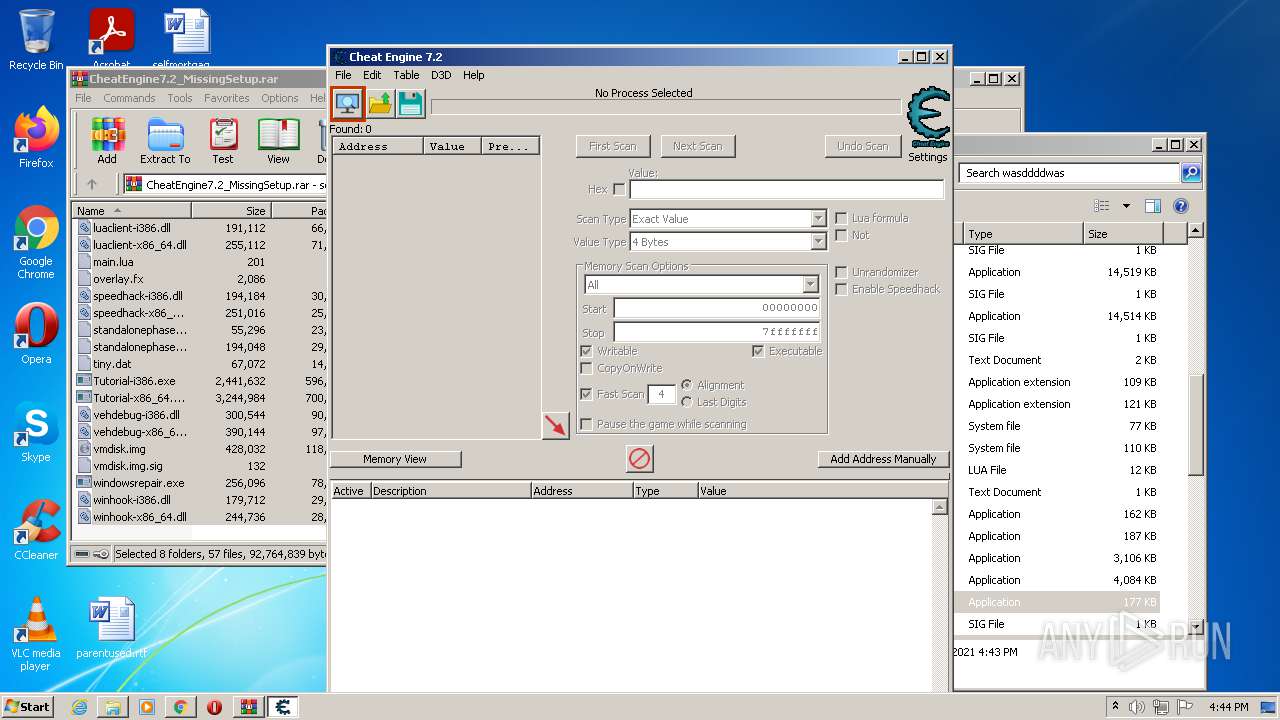
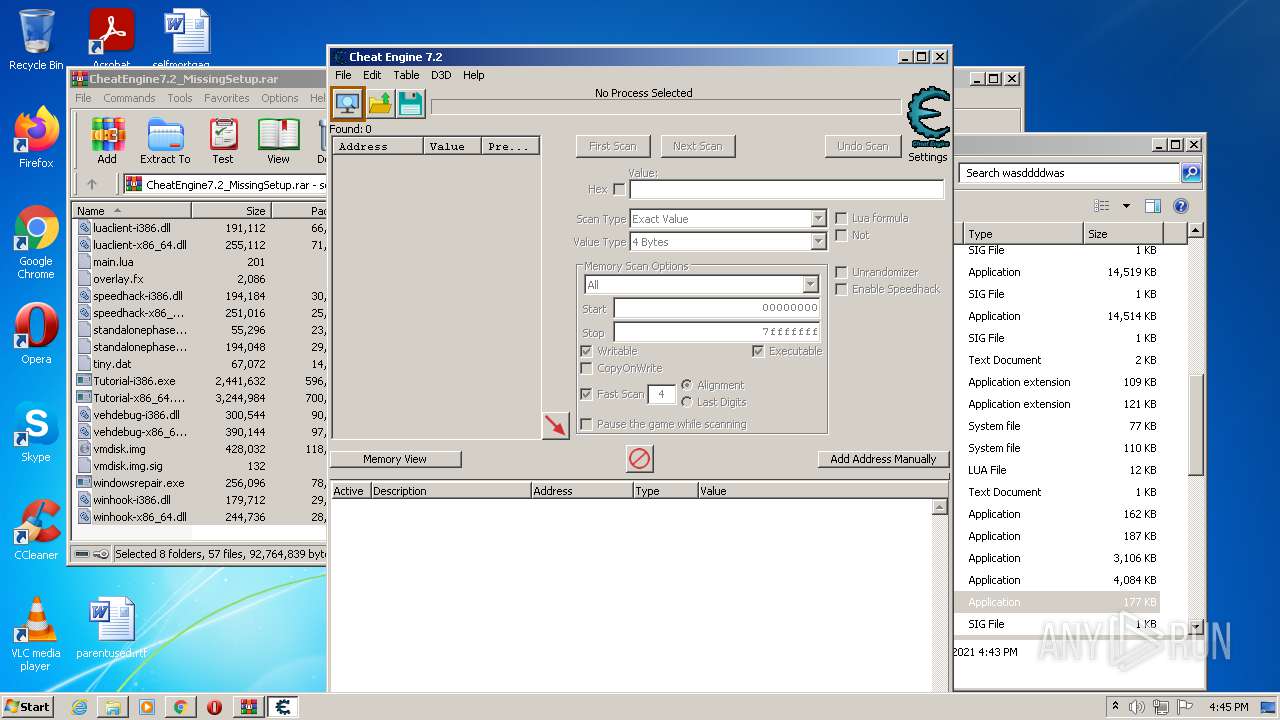
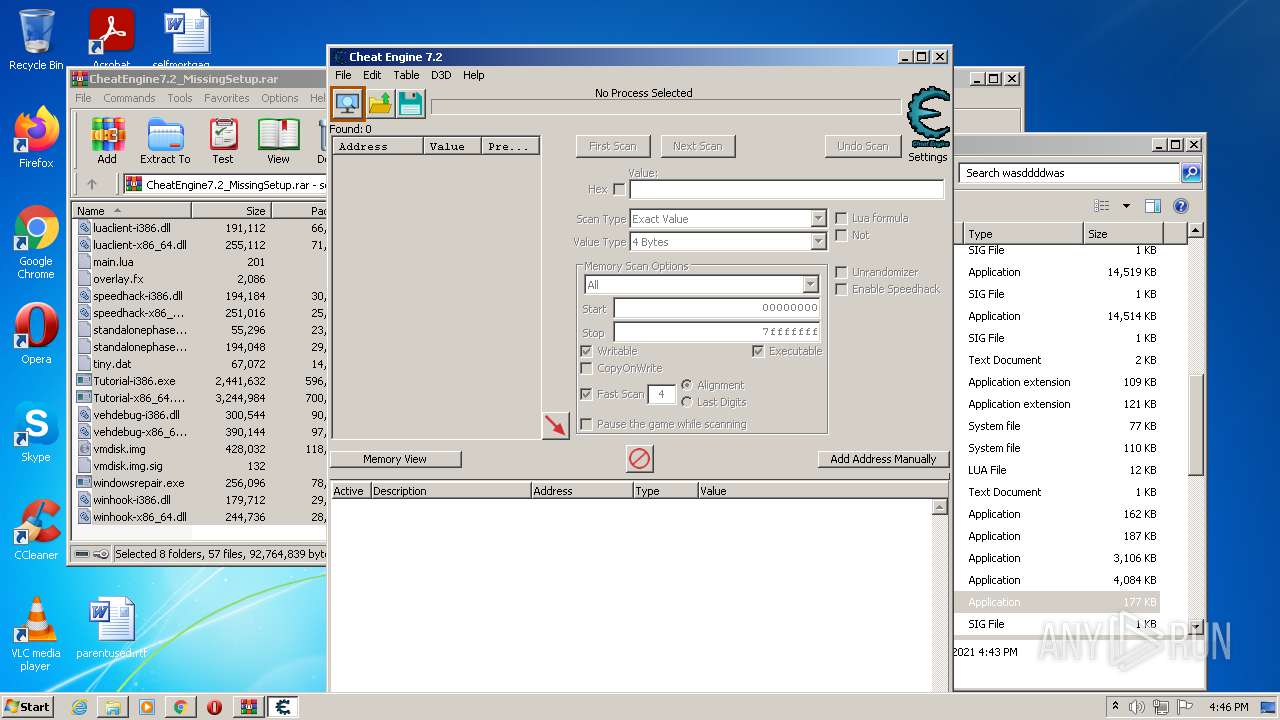
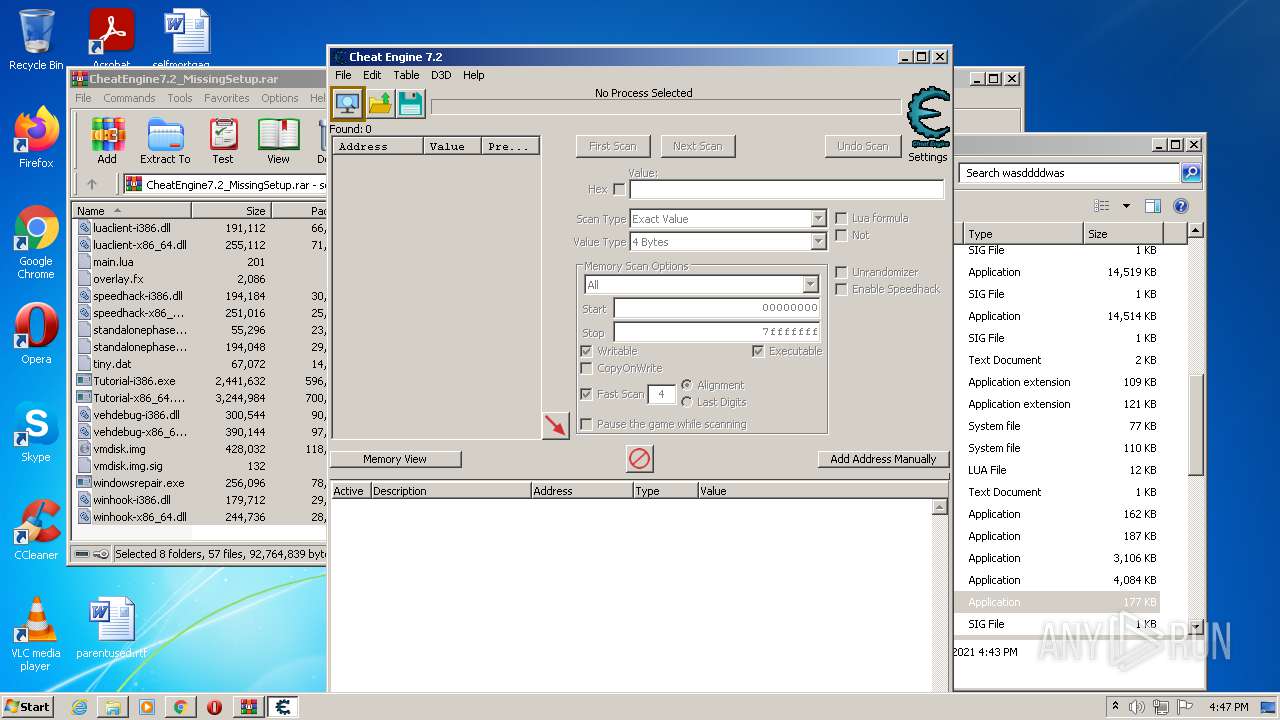
Executable files
57
Suspicious files
43
Text files
262
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-616309F1-C14.pma | — | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f343faf6-7d7e-4fc2-bf09-a3d8581b7c2d.tmp | text | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF101a31.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\MANIFEST-000001 | binary | |
MD5:5AF87DFD673BA2115E2FCF5CFDB727AB | SHA256:F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4 | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF101a50.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\CURRENT | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF101b4a.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
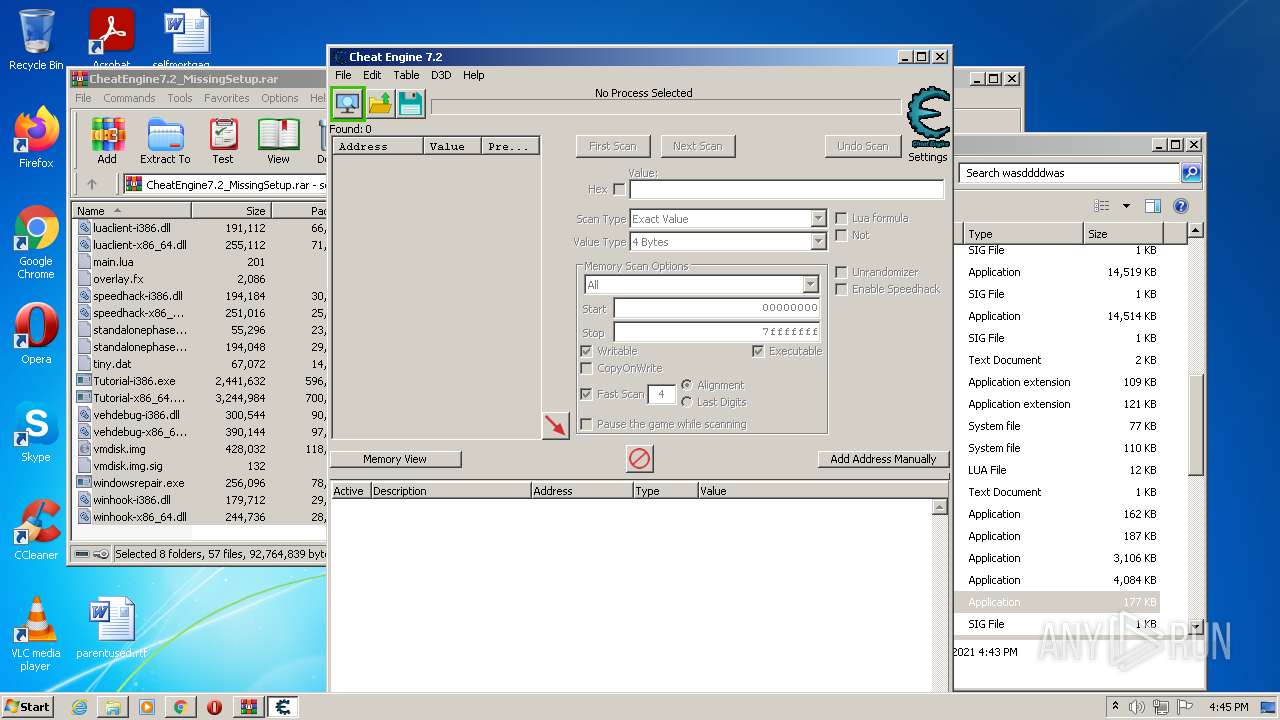
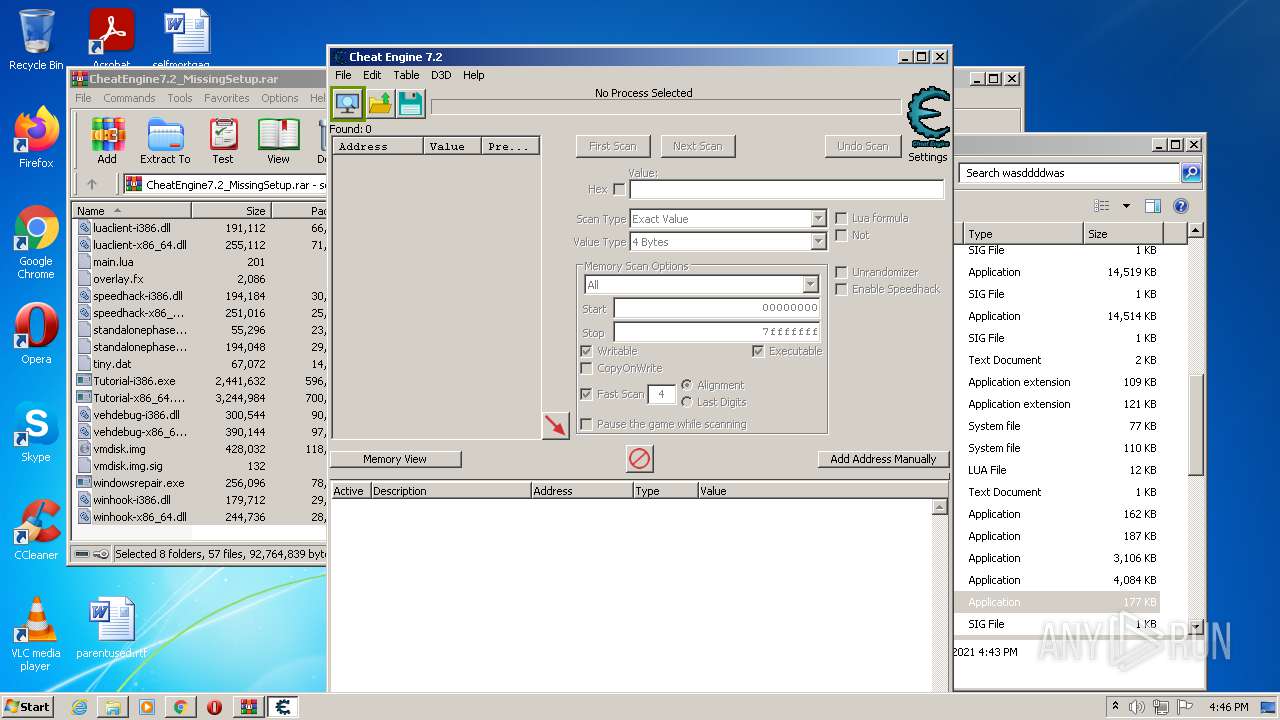
HTTP(S) requests
31
TCP/UDP connections
10
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | vc | 6.55 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k5w7hvgv3ze3vzwxqvfmzgvkoe_2711/jflookgnkcckhobaglndicnbbgbonegd_2711_all_adagdhwnthqndo74hfwl6k3rqsya.crx3 | US | binary | 5.63 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k5w7hvgv3ze3vzwxqvfmzgvkoe_2711/jflookgnkcckhobaglndicnbbgbonegd_2711_all_adagdhwnthqndo74hfwl6k3rqsya.crx3 | US | vc | 6.55 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 89.0 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/YGkwa4MXjfWSuERyWQYP_A_4/aapLKTSZ439A-0g3nqJr3Q | US | crx | 2.81 Kb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODZmQUFYS2VOaGowdjdSeVBvWFBSTDIxdw/1.0.0.9_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | crx | 2.81 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k5w7hvgv3ze3vzwxqvfmzgvkoe_2711/jflookgnkcckhobaglndicnbbgbonegd_2711_all_adagdhwnthqndo74hfwl6k3rqsya.crx3 | US | binary | 10.2 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 358 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 45.0 Kb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | crx | 1.80 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3728 | chrome.exe | 172.67.33.171:443 | www.cheatengine.org | — | US | unknown |
3728 | chrome.exe | 142.250.185.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 142.250.185.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
— | — | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
3728 | chrome.exe | 142.250.186.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 142.250.186.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.cheatengine.org |
| unknown |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
cheatengine-i386.exe | setDPIAware |
cheatengine-i386.exe | p3 |
cheatengine-i386.exe | DisassemblerThumb init |
cheatengine-i386.exe | arm disassembler |
cheatengine-i386.exe | MainUnit2 |
cheatengine-i386.exe | Offset of LBR_Count=768 |
cheatengine-i386.exe | sizeof fxstate = 512 |
cheatengine-i386.exe | start |
cheatengine-i386.exe | TSymbolListHandler.create 1 |
cheatengine-i386.exe | TSymbolListHandler.create 2 |