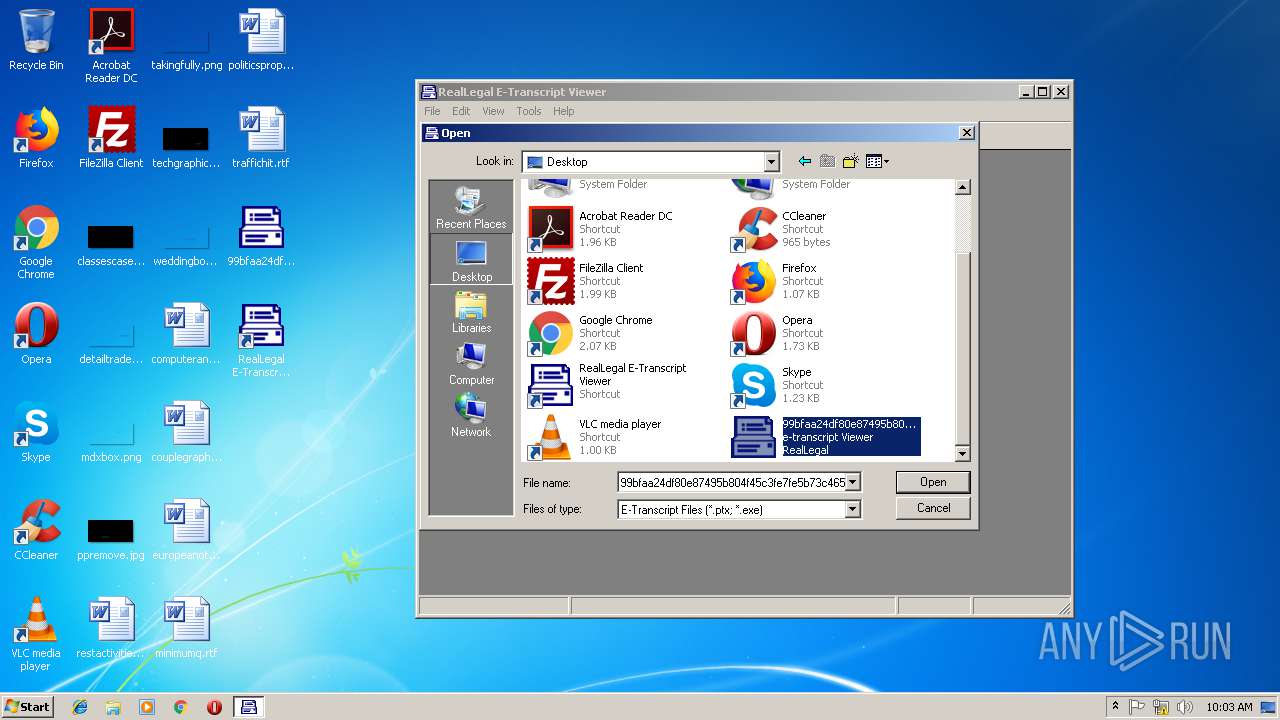
| File name: | 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785 |
| Full analysis: | https://app.any.run/tasks/fc2a617d-0bb5-49e7-b243-2db5ce8cb0ac |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2019, 09:59:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D9707DD1159A28D2D6620AB08C54F4E1 |
| SHA1: | ABB102BEDB7B61C9341CD5C2152379DFD5FFEB5B |
| SHA256: | 99BFAA24DF80E87495B804F45C3FE7FE5B73C465BCB2FDE5ACEDC5D03EEED785 |
| SSDEEP: | 12288:bLgJzehRILw/pxzJc+/dcnNy3/Z9CcTSbMAXd1IFe+0:bLgsIAenwPP2Td1qT0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
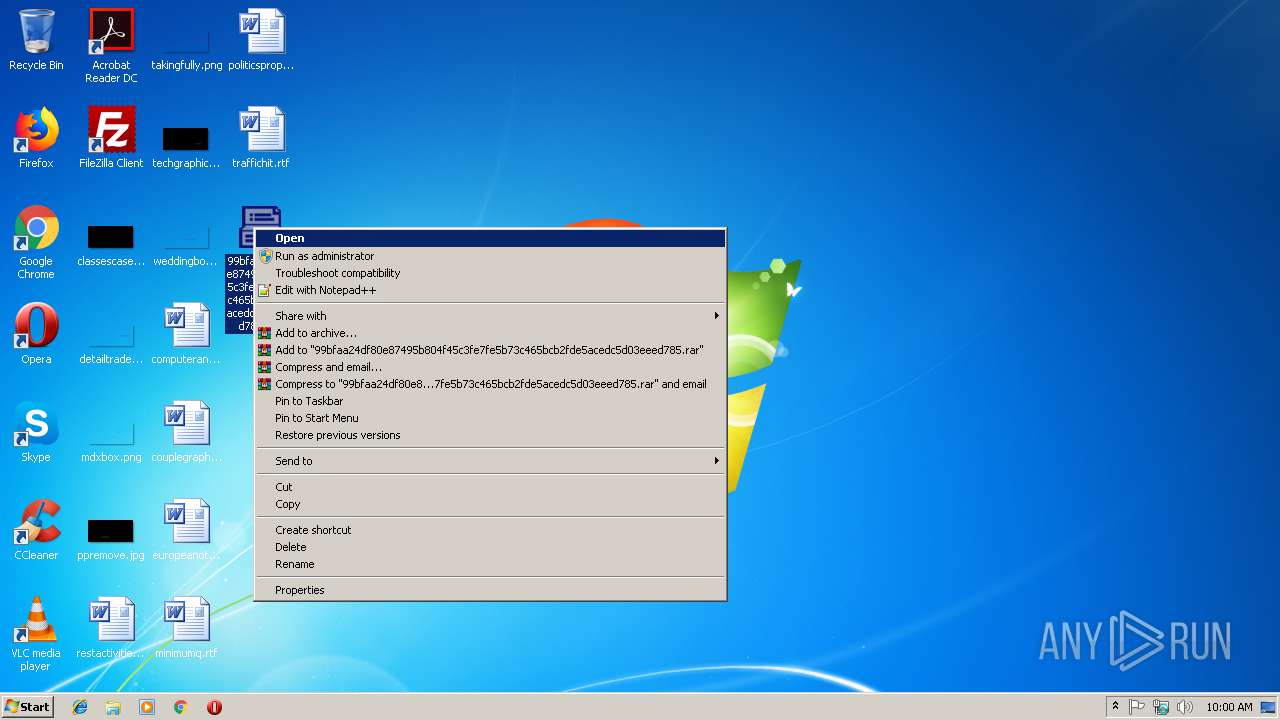
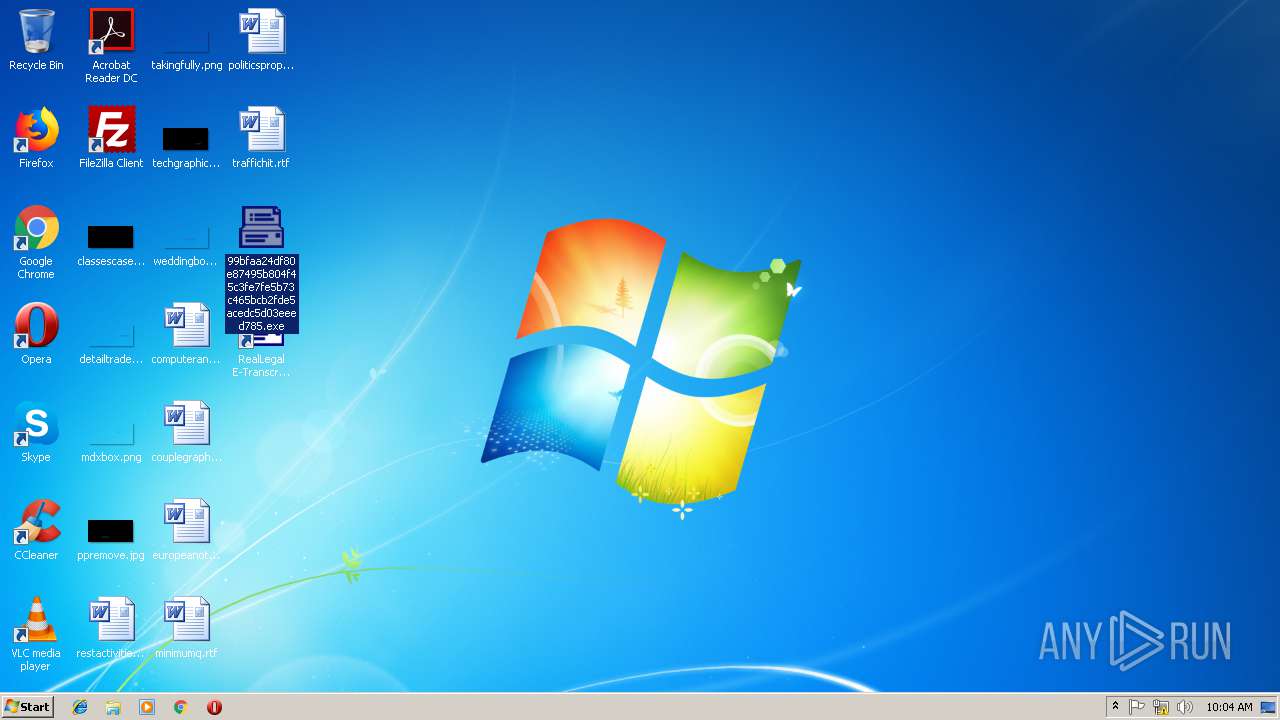
Modifies the open verb of a shell class
- 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe (PID: 4068)
Creates files in the program directory
- 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe (PID: 4068)
Executable content was dropped or overwritten
- 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe (PID: 4068)
Reads internet explorer settings
- helppane.exe (PID: 1808)
Creates files in the Windows directory
- 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe (PID: 4068)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (36.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.1) |
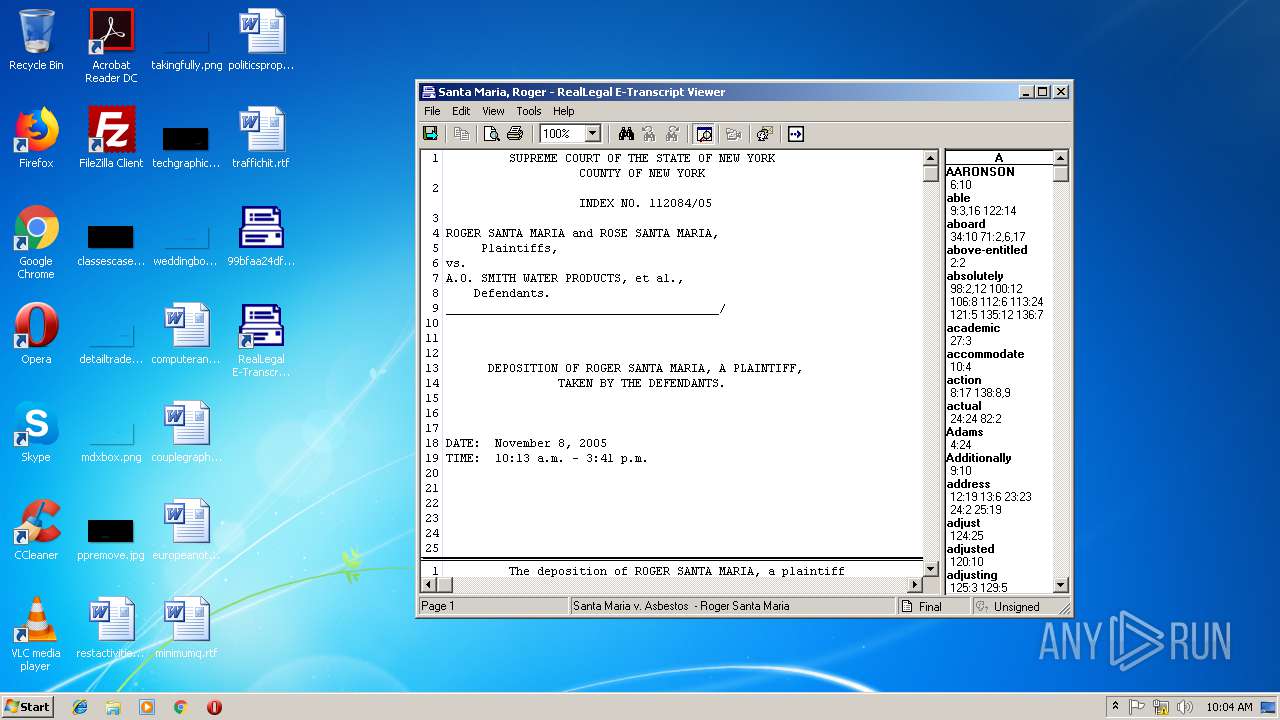
| .ptx | | | RealLegal E-Transcript (13.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2003:12:31 20:29:22+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 307200 |
| InitializedDataSize: | 200704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x34c69 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
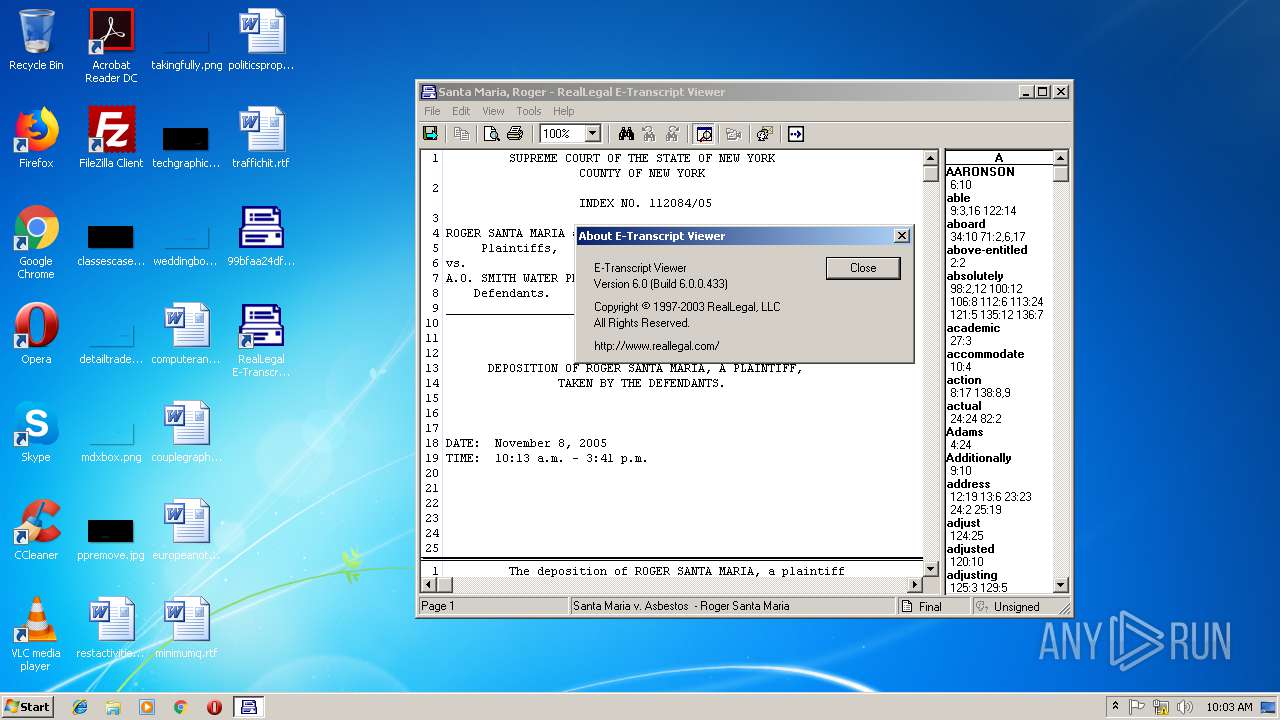
| FileVersionNumber: | 6.0.0.433 |
| ProductVersionNumber: | 6.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
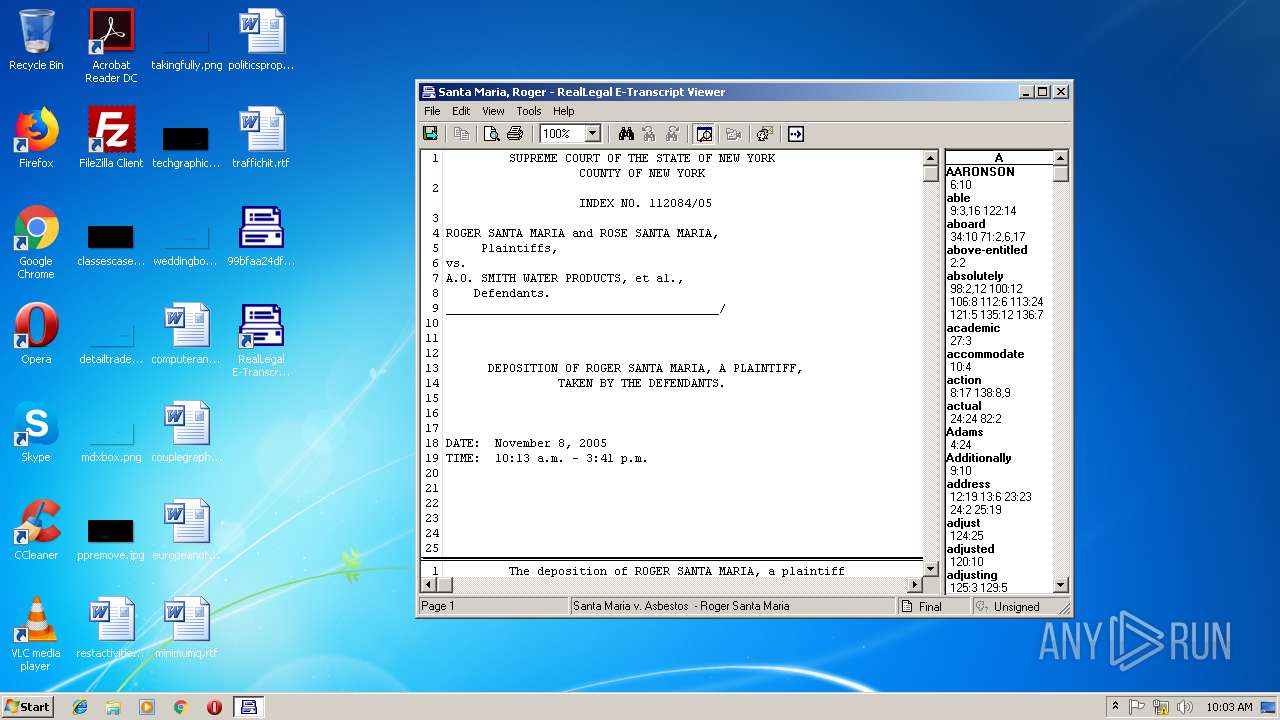
| CompanyName: | RealLegal |
| FileDescription: | e-transcript Viewer |
| FileVersion: | 6.0.0.433 |
| InternalName: | ENVELOPE |
| LegalCopyright: | Copyright © 1996-2003, RealLegal, LLC |
| OriginalFileName: | ENVELOPE.EXE |
| ProductName: | e-transcript |
| ProductVersion: | 6.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2003 19:29:22 |
| Detected languages: |
|
| CompanyName: | RealLegal |
| FileDescription: | e-transcript Viewer |
| FileVersion: | 6.0.0.433 |
| InternalName: | ENVELOPE |
| LegalCopyright: | Copyright © 1996-2003, RealLegal, LLC |
| OriginalFilename: | ENVELOPE.EXE |
| ProductName: | e-transcript |
| ProductVersion: | 6.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 31-Dec-2003 19:29:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004A2AA | 0x0004B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52404 |
.rdata | 0x0004C000 | 0x00008EDE | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92742 |
.data | 0x00055000 | 0x0000FC25 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.73903 |
.rsrc | 0x00065000 | 0x00017D58 | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.19371 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.39802 | 748 | UNKNOWN | English - United States | RT_VERSION |
2 | 2.80609 | 160 | UNKNOWN | English - United States | RT_STRING |
3 | 2.79487 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 2.194 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.42751 | 308 | UNKNOWN | English - United States | RT_CURSOR |
63 | 3.07946 | 494 | UNKNOWN | English - United States | RT_STRING |
65 | 1.36124 | 50 | UNKNOWN | English - United States | RT_STRING |
66 | 1.79073 | 60 | UNKNOWN | English - United States | RT_STRING |
67 | 3.13895 | 1078 | UNKNOWN | English - United States | RT_STRING |
68 | 2.66652 | 172 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
WINSPOOL.DRV |
Total processes
41
Monitored processes
5
Malicious processes
0
Suspicious processes
1
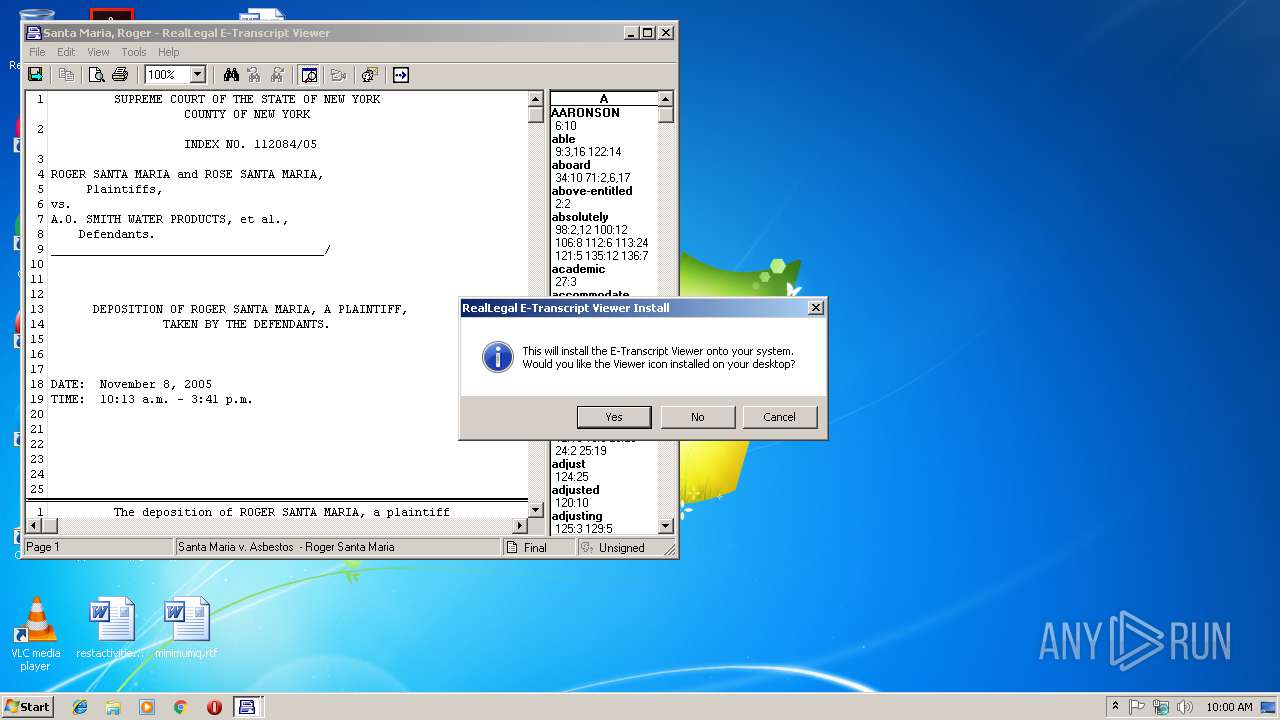
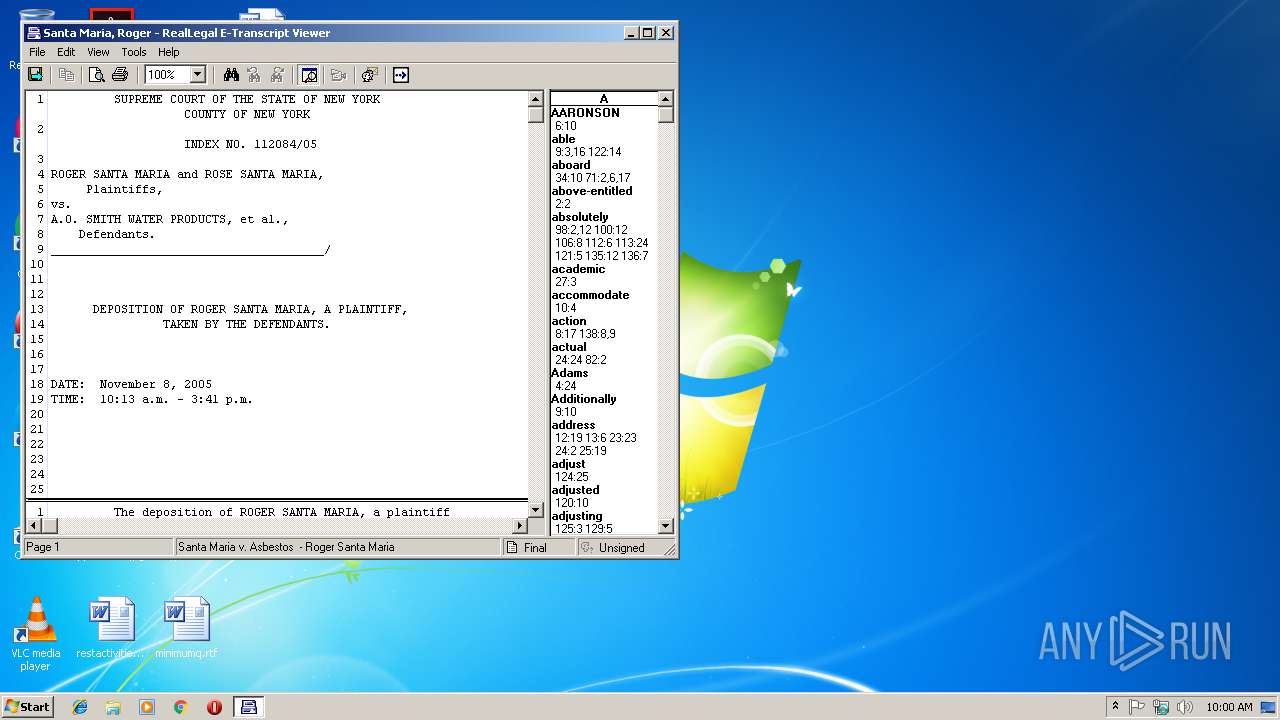
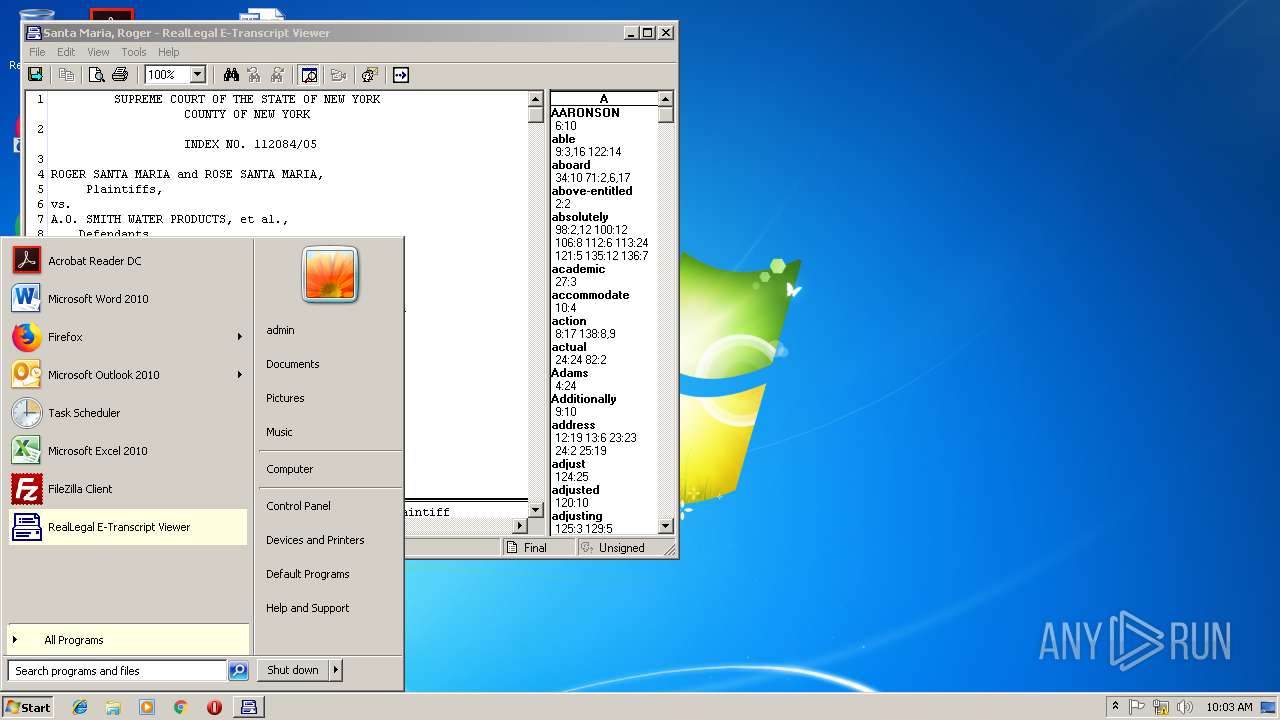
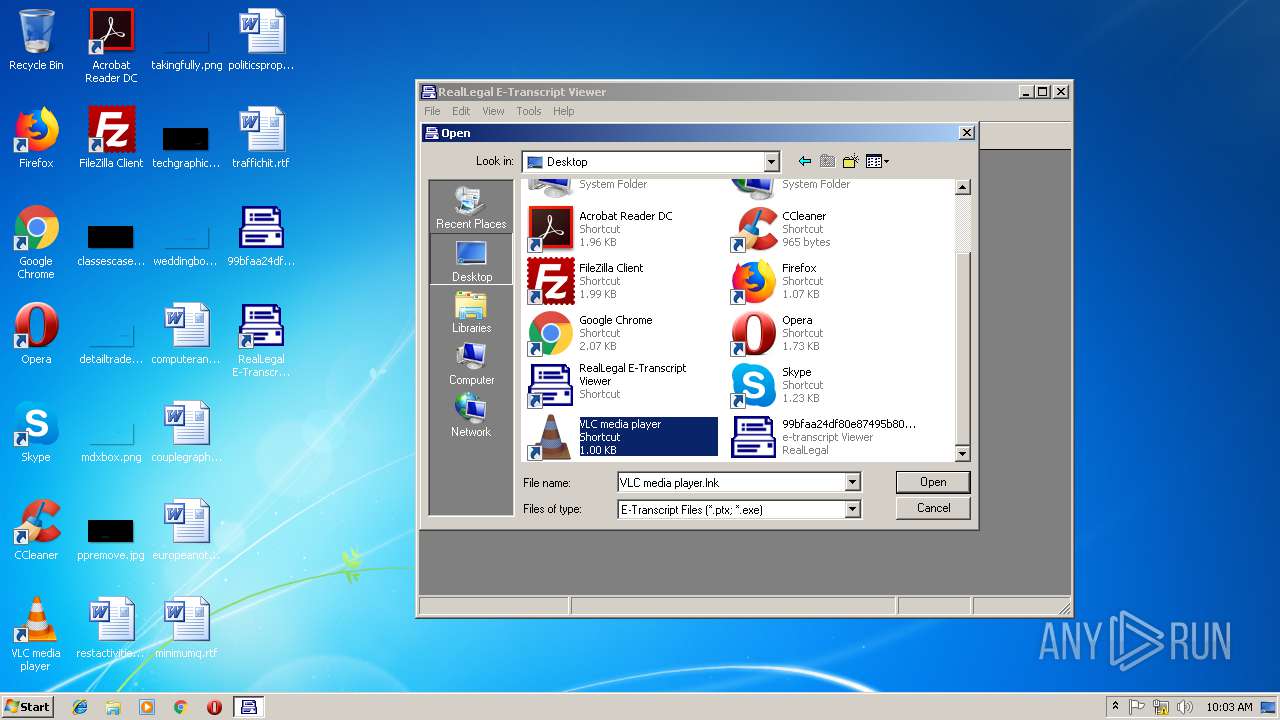
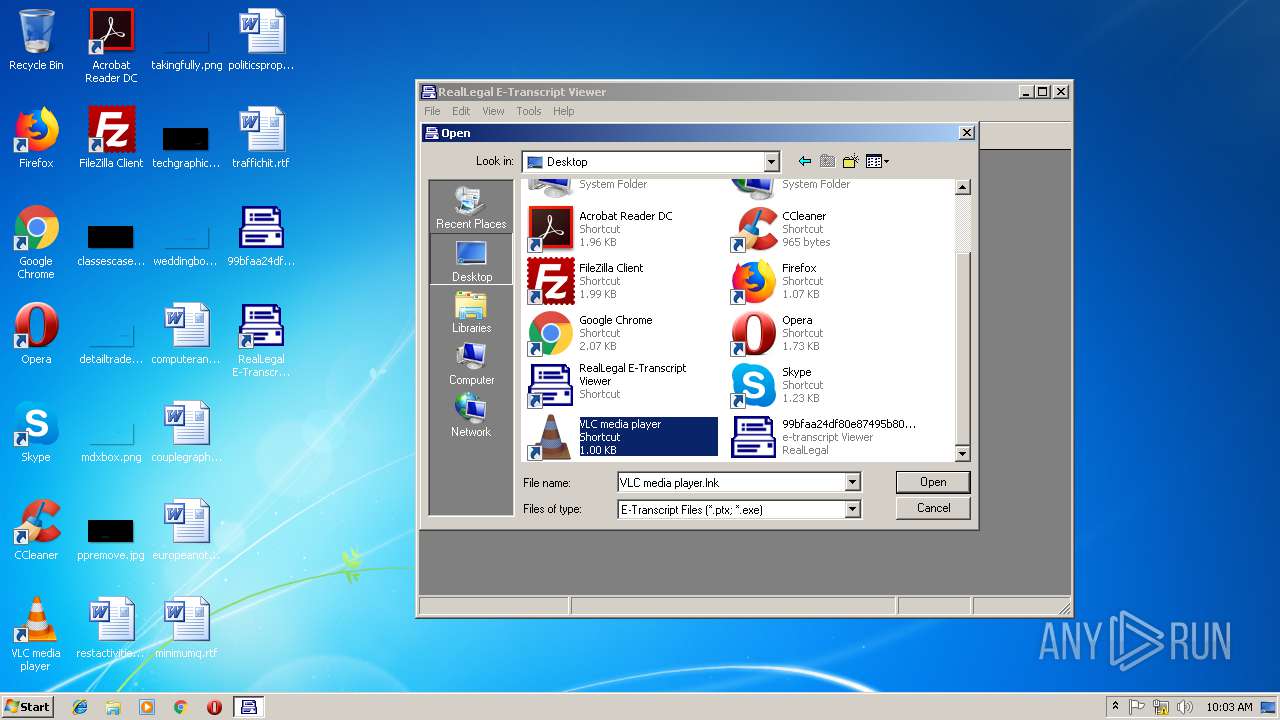
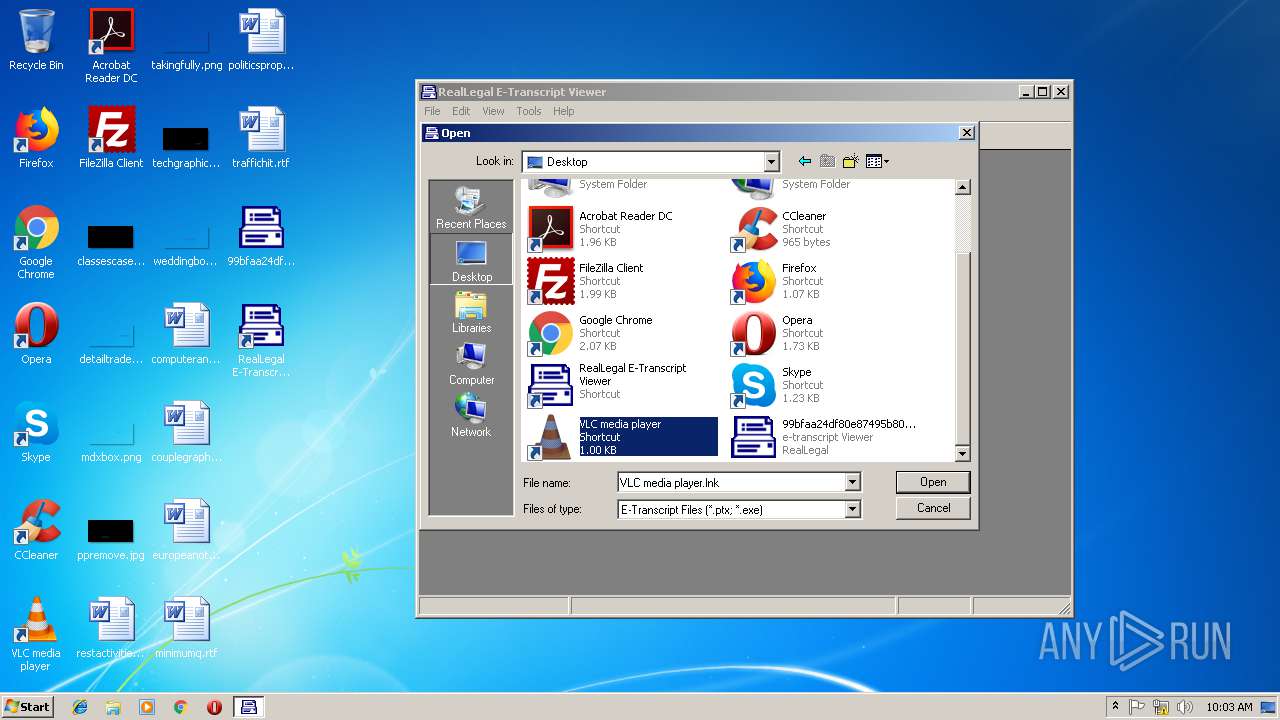
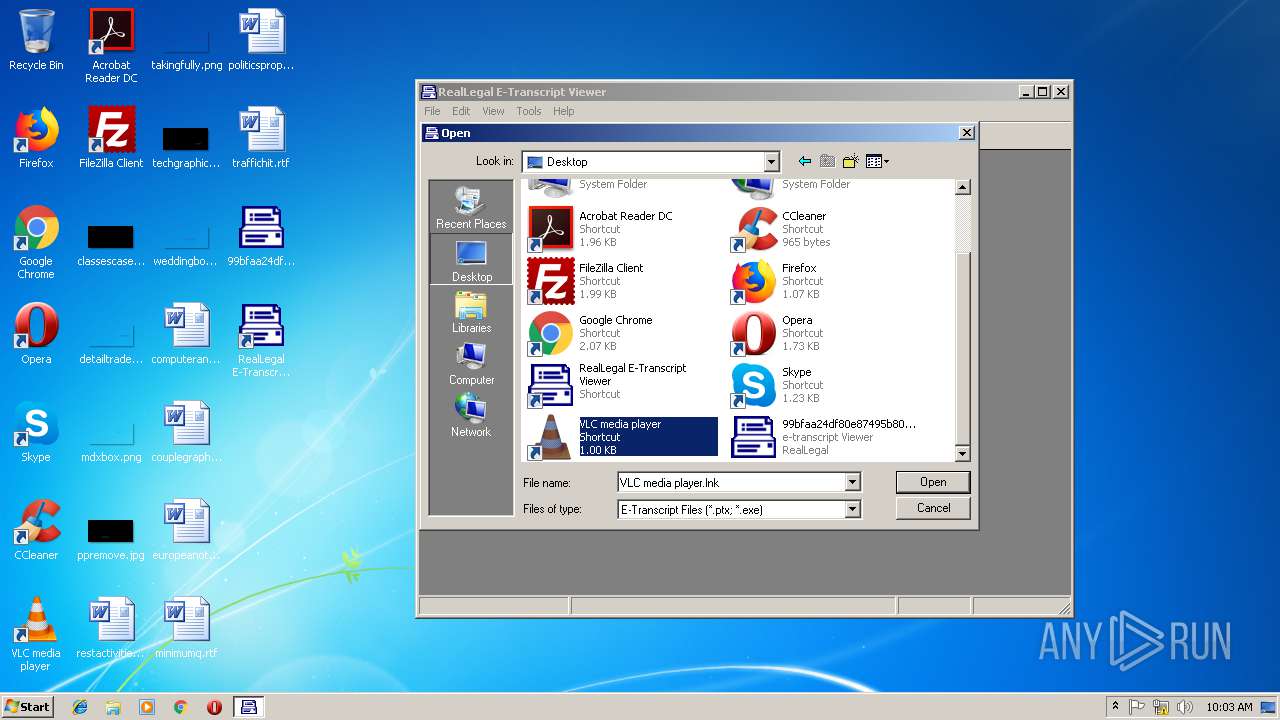
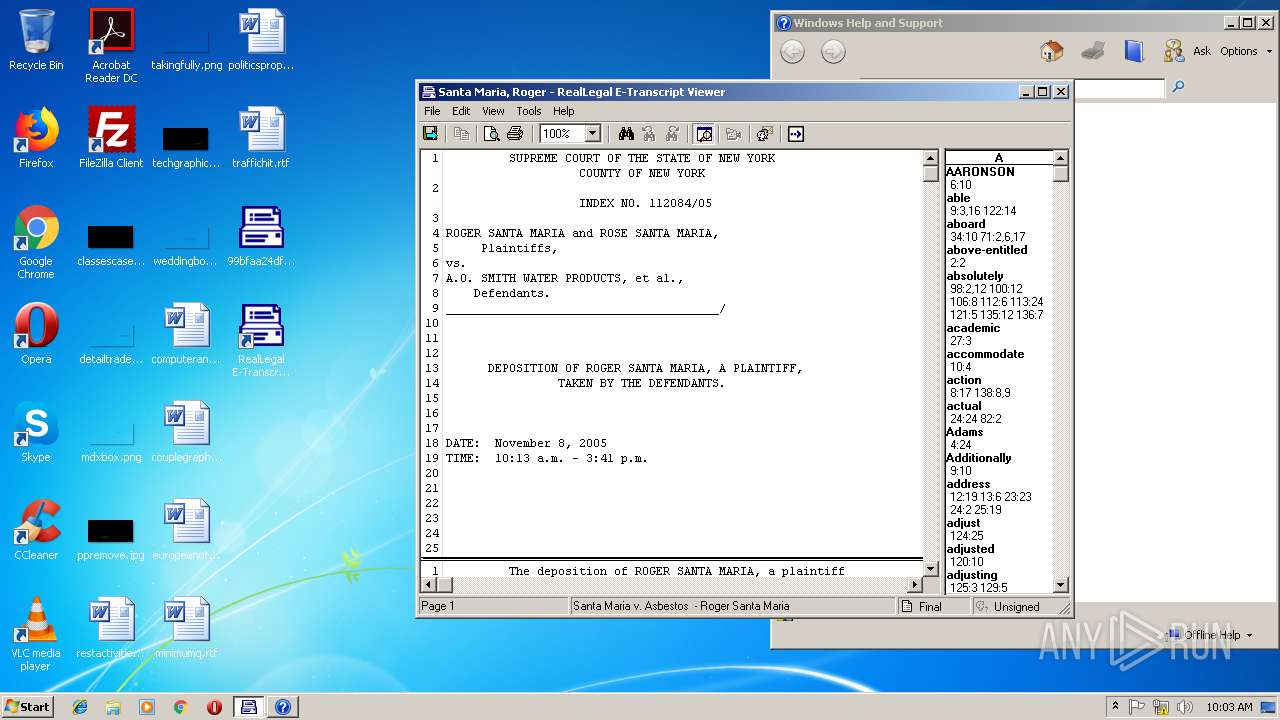
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1808 | C:\Windows\helppane.exe -Embedding | C:\Windows\helppane.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Help and Support Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
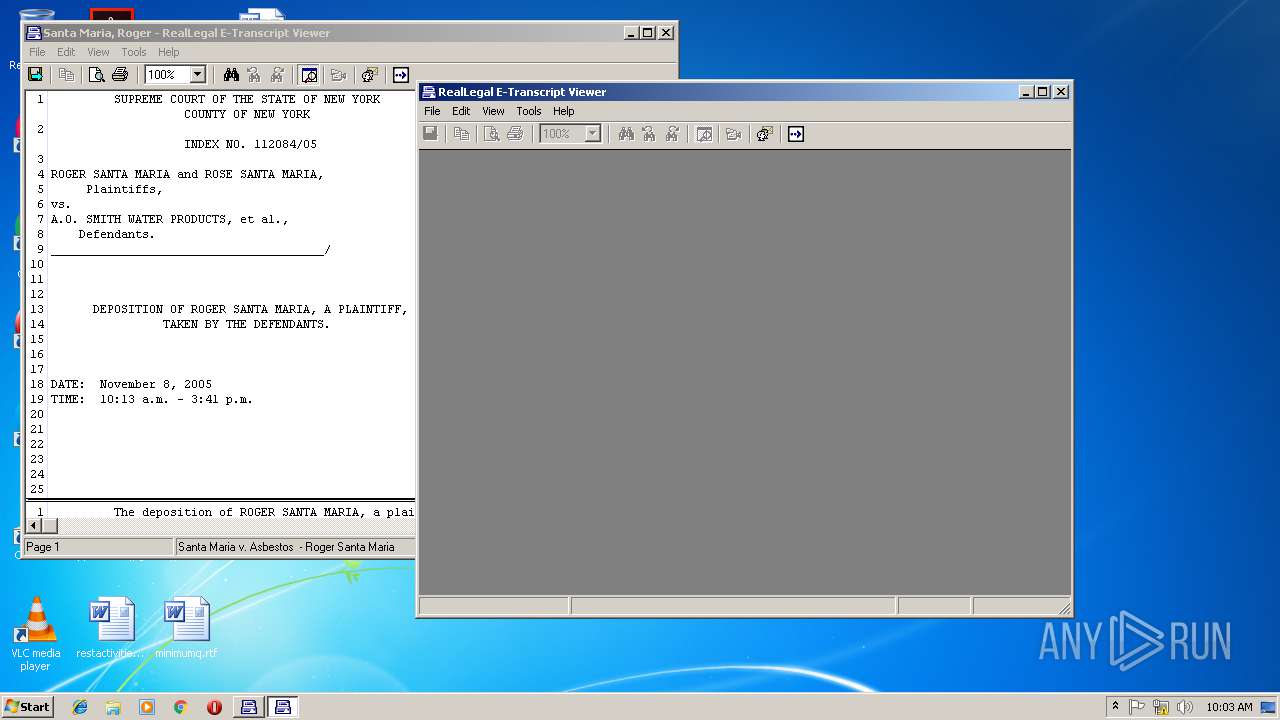
| 3136 | "C:\Users\admin\Desktop\99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe" | C:\Users\admin\Desktop\99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | — | explorer.exe | |||||||||||
User: admin Company: RealLegal Integrity Level: MEDIUM Description: e-transcript Viewer Exit code: 0 Version: 6.0.0.433 Modules
| |||||||||||||||
| 3292 | winhlp32.exe -x | C:\Windows\winhlp32.exe | — | etrnview.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Winhlp32 Stub Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
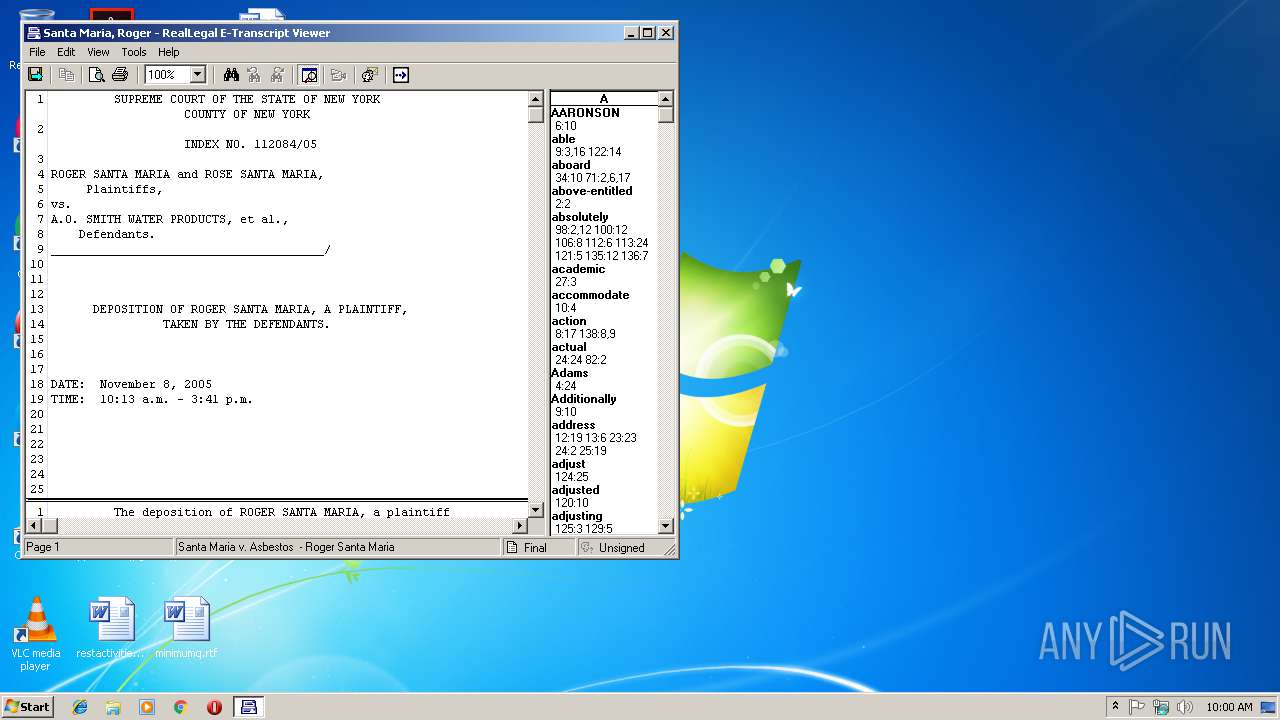
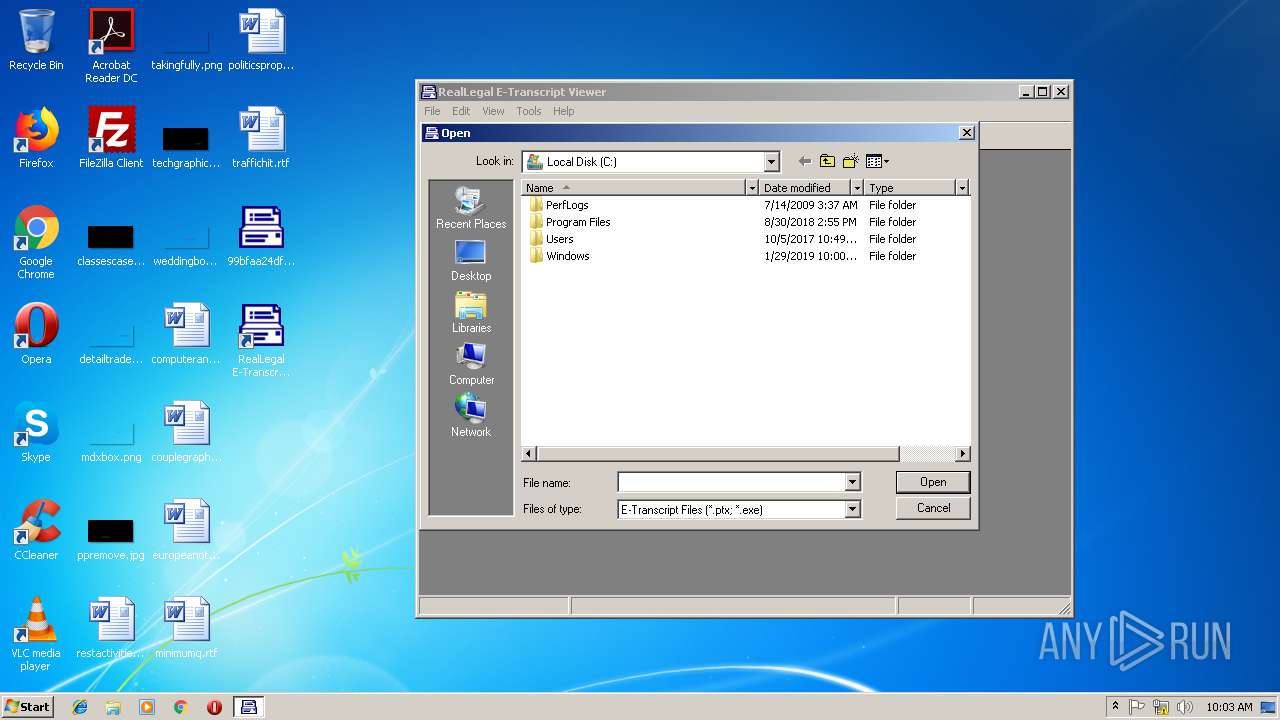
| 3648 | "C:\Windows\etrnview.exe" | C:\Windows\etrnview.exe | — | explorer.exe | |||||||||||
User: admin Company: RealLegal Integrity Level: MEDIUM Description: e-transcript Viewer Exit code: 0 Version: 6.0.0.433 Modules
| |||||||||||||||
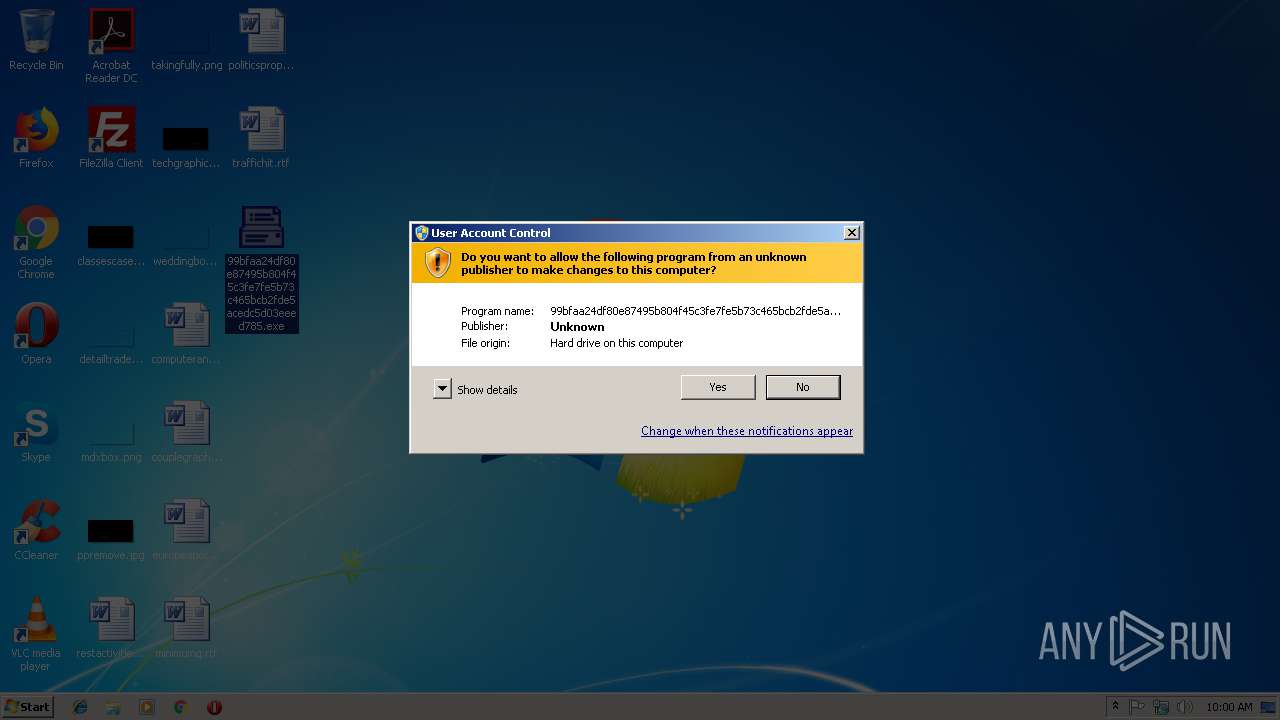
| 4068 | "C:\Users\admin\Desktop\99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe" | C:\Users\admin\Desktop\99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | explorer.exe | ||||||||||||
User: admin Company: RealLegal Integrity Level: HIGH Description: e-transcript Viewer Exit code: 0 Version: 6.0.0.433 Modules
| |||||||||||||||
Total events
773
Read events
675
Write events
97
Delete events
1
Modification events
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ETXViewerLib.ETXViewerApp |
| Operation: | write | Name: | |
Value: ETXViewerLib.ETXViewerApp | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{DE013754-81DE-46BC-BEEB-492C810900BF} |
| Operation: | write | Name: | |
Value: ETXViewerLib.ETXViewerApp | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ETXViewerLib.ETXViewerApp\CLSID |
| Operation: | write | Name: | |
Value: {DE013754-81DE-46BC-BEEB-492C810900BF} | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{DE013754-81DE-46BC-BEEB-492C810900BF}\ProgID |
| Operation: | write | Name: | |
Value: ETXViewerLib.ETXViewerApp | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{DE013754-81DE-46BC-BEEB-492C810900BF}\InprocHandler32 |
| Operation: | write | Name: | |
Value: ole32.dll | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{DE013754-81DE-46BC-BEEB-492C810900BF}\LocalServer32 |
| Operation: | write | Name: | |
Value: C:\Users\admin\Desktop\99BFAA~1.EXE | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ptx |
| Operation: | write | Name: | |
Value: ptxfile | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ptx |
| Operation: | write | Name: | ContentType |
Value: application/x-etranscript | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ptxfile |
| Operation: | write | Name: | |
Value: E-Transcript File | |||
| (PID) Process: | (4068) 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ptxfile\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Windows\etrnview.exe" %1 | |||
Executable files
1
Suspicious files
0
Text files
92
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
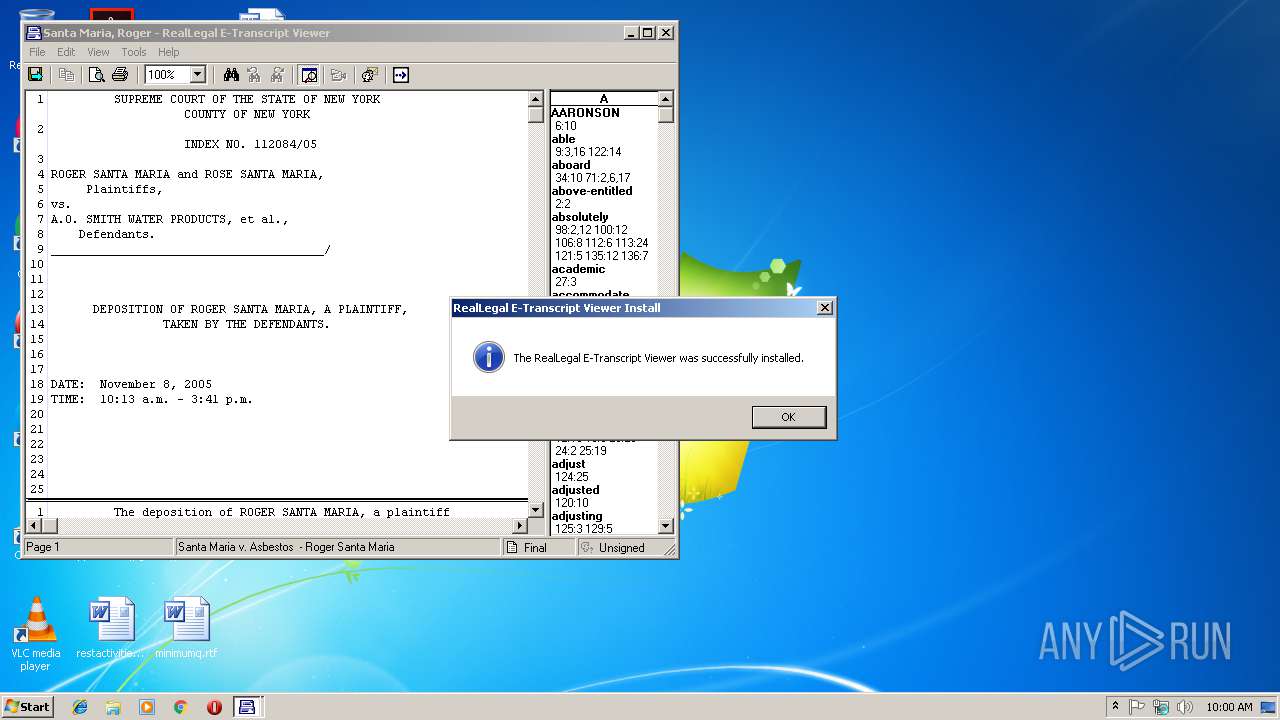
| 4068 | 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | C:\Windows\etrnview.exe | executable | |
MD5:— | SHA256:— | |||
| 4068 | 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | C:\Windows\pnxtrvu.ini | text | |
MD5:— | SHA256:— | |||
| 3136 | 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\pnxtrvu.ini | text | |
MD5:— | SHA256:— | |||
| 4068 | 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\RealLegal E-Transcript Viewer\RealLegal E-Transcript Viewer.lnk | lnk | |
MD5:— | SHA256:— | |||
| 4068 | 99bfaa24df80e87495b804f45c3fe7fe5b73c465bcb2fde5acedc5d03eeed785.exe | C:\Users\Public\Desktop\RealLegal E-Transcript Viewer.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3648 | etrnview.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\pnxtrvu.ini | text | |
MD5:— | SHA256:— | |||
| 3648 | etrnview.exe | C:\Users\admin\AppData\Local\Temp\viewhelp.hlp | hlp | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report