| File name: | MAS_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/da5aff19-94fb-48a9-8ce0-1dc319e78715 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 04:56:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (348), with CRLF line terminators |
| MD5: | 51D1A565DAFB87D618FEC0487618DADD |
| SHA1: | D818C140B322DCB6D1097A6FE0DBB2F29E4EFB63 |
| SHA256: | 99B9D8E20701DDCA02676146F7878ECC79BC403CB7B51FBB1B15B2D8D8BC64C4 |
| SSDEEP: | 6144:pjI2yBqk05WIgcEvTUQMb9lnccN4Zk0ykzB+uw:pjI2y1PcEvTU33c+kk0ykzBo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7356)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7604)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7628)
- cmd.exe (PID: 7356)
- powershell.exe (PID: 7748)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7228)
Application launched itself
- cmd.exe (PID: 7628)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 7604)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 7776)
- ClipUp.exe (PID: 1164)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 4024)
Windows service management via SC.EXE
- sc.exe (PID: 7428)
- sc.exe (PID: 8140)
- sc.exe (PID: 6516)
- sc.exe (PID: 8156)
- sc.exe (PID: 7672)
- sc.exe (PID: 6808)
- sc.exe (PID: 1116)
- sc.exe (PID: 7568)
- sc.exe (PID: 2192)
- sc.exe (PID: 900)
- sc.exe (PID: 4436)
- sc.exe (PID: 6044)
- sc.exe (PID: 5324)
- sc.exe (PID: 5984)
- sc.exe (PID: 7244)
- sc.exe (PID: 1132)
- sc.exe (PID: 7220)
- sc.exe (PID: 7236)
- sc.exe (PID: 3676)
- sc.exe (PID: 6944)
- sc.exe (PID: 5720)
- sc.exe (PID: 7948)
- sc.exe (PID: 7400)
- sc.exe (PID: 4696)
- sc.exe (PID: 3884)
- sc.exe (PID: 8172)
- sc.exe (PID: 8052)
- sc.exe (PID: 1388)
- sc.exe (PID: 6656)
- sc.exe (PID: 7148)
- sc.exe (PID: 7276)
- sc.exe (PID: 5436)
- sc.exe (PID: 6752)
- sc.exe (PID: 300)
- sc.exe (PID: 1328)
- sc.exe (PID: 6080)
- sc.exe (PID: 2040)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7356)
- cmd.exe (PID: 5072)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 7604)
- powershell.exe (PID: 7224)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 2288)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 7776)
- powershell.exe (PID: 4024)
- cmd.exe (PID: 6184)
Executing commands from a ".bat" file
- powershell.exe (PID: 7748)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7604)
Executing commands from ".cmd" file
- cmd.exe (PID: 7356)
- powershell.exe (PID: 7748)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 8068)
Executes script without checking the security policy
- powershell.exe (PID: 7748)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 896)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 8024)
- powershell.exe (PID: 5772)
- powershell.exe (PID: 5740)
- powershell.exe (PID: 7276)
- powershell.exe (PID: 924)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 8172)
- powershell.exe (PID: 1388)
- powershell.exe (PID: 1452)
- powershell.exe (PID: 7776)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 4024)
Starts SC.EXE for service management
- cmd.exe (PID: 7356)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7604)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7356)
- cmd.exe (PID: 5072)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 8032)
- powershell.exe (PID: 7224)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 7036)
- powershell.exe (PID: 7776)
- cmd.exe (PID: 6184)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 4024)
- powershell.exe (PID: 7252)
Hides command output
- cmd.exe (PID: 5072)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 1056)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 300)
- cmd.exe (PID: 4172)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5072)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 6184)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5072)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 6156)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 896)
- powershell.exe (PID: 5772)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 896)
- powershell.exe (PID: 5772)
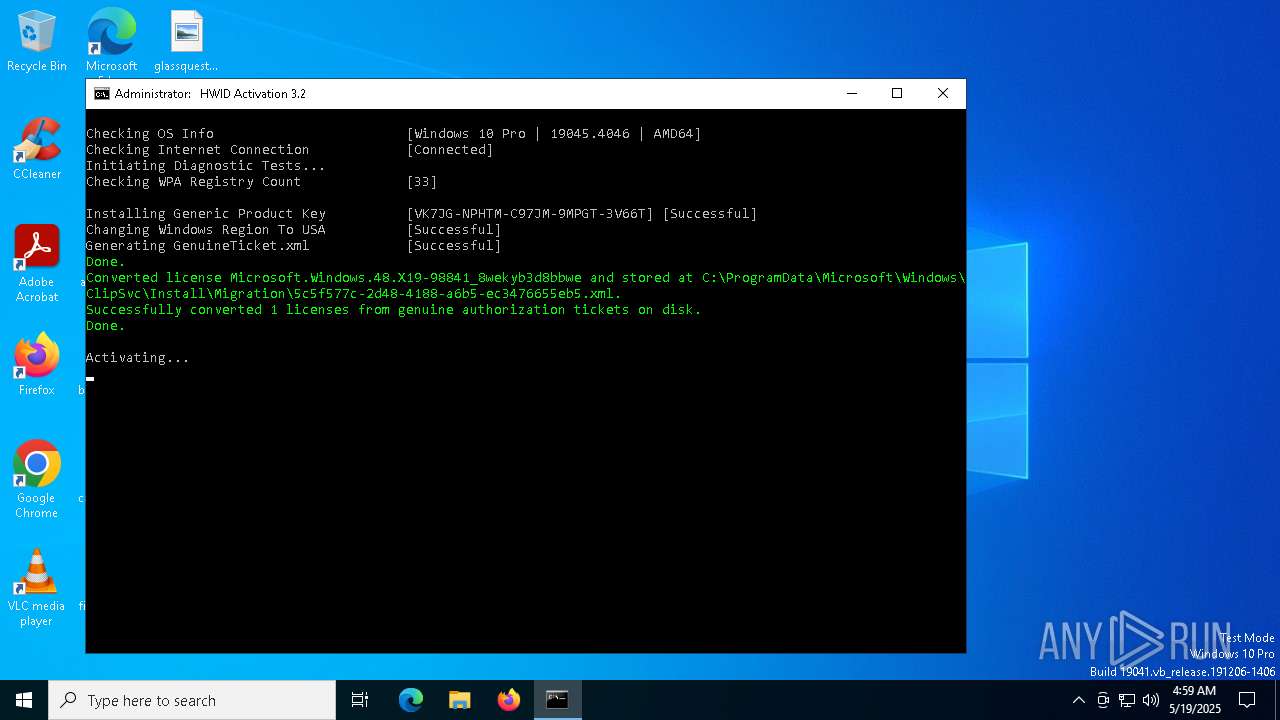
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7604)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 896)
- powershell.exe (PID: 5772)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 1188)
- cmd.exe (PID: 7604)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 3020)
Probably file/command deobfuscation
- cmd.exe (PID: 8032)
- cmd.exe (PID: 6184)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 7224)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 7776)
- powershell.exe (PID: 4024)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7604)
- cmd.exe (PID: 1056)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 6800)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 7604)
INFO
Checks operating system version
- cmd.exe (PID: 7356)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7604)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 896)
- powershell.exe (PID: 5772)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 896)
- powershell.exe (PID: 5772)
Starts MODE.COM to configure console settings
- mode.com (PID: 7496)
- mode.com (PID: 8080)
- mode.com (PID: 4008)
- mode.com (PID: 7620)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 896)
- powershell.exe (PID: 5772)
Checks supported languages
- mode.com (PID: 7496)
- mode.com (PID: 4008)
- mode.com (PID: 8080)
- mode.com (PID: 7620)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1184)
- WMIC.exe (PID: 1628)
- WMIC.exe (PID: 5936)
- WMIC.exe (PID: 7312)
- WMIC.exe (PID: 7696)
- WMIC.exe (PID: 904)
- WMIC.exe (PID: 6112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
437
Monitored processes
298
Malicious processes
11
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | sc start KeyIso | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | C:\WINDOWS\System32\cmd.exe /c reg query "HKCU\Control Panel\International\Geo" /v Name 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v ErrorControl | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | wmic path SoftwareLicensingProduct where (LicenseStatus='1' and GracePeriodRemaining='0' and PartialProductKey is not NULL AND LicenseDependsOn is NULL) get Name /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | ping -n 1 l.root-servers.net | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v Description | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_AIO.cmd.bat') -split ':winsubstatus\:.*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | sc query wlidsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | reg query HKLM\SYSTEM\CurrentControlSet\Services\wlidsvc /v DependOnService | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
127 197
Read events
127 188
Write events
2
Delete events
7
Modification events
| (PID) Process: | (7276) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Name |
Value: US | |||
| (PID) Process: | (7276) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Nation |
Value: 244 | |||
| (PID) Process: | (8056) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\ExtendedProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8056) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Property |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8056) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Token\{D6D5A677-0872-4AB0-9442-BB792FCE85C5} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8056) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Token |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8056) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8056) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8056) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
3
Text files
55
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7352 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_44ujf2wb.ycs.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1odvpak3.uq5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5892 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jcuyf5ux.mzv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5772 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v2ltuvpx.ipj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1852 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cmw533if.zew.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7352 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ywep54qi.5ew.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uwihihy3.tqc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 896 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gcebdq5b.llp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1852 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lodxc4qp.gxj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7748 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:18C014318BEED7E61A4D48A15E0F080B | SHA256:6CE9804D39AEBB6E8611E8BA32C2F0BCF08C7002793ADE7EC03AA3D2E8BE0C3C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 23.67.160.244:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7424 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7424 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activated.win |
| unknown |
updatecheck32.activated.win |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |