| File name: | main.exe |
| Full analysis: | https://app.any.run/tasks/6acf8512-fb6a-4b4e-a65e-c69141debfb3 |
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2023, 10:30:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 8A731AD583F492235A0A2E2954A14DC9 |
| SHA1: | F4288948F93584FAFDF64799896AAE8F56B38F4E |
| SHA256: | 99A16944EB17FA13A9AEB07E52C67C599EB74BC6999DC90CC03D628F449EB90D |
| SSDEEP: | 49152:MRT+Hd+mVuuLKCvQmZSmj9vsO70EBL9CsIzVIcv0xc5RnBxQY6OWeIDRO8KQ97eB:MRo9xTZSUHIz75aY7IyyCh |
MALICIOUS
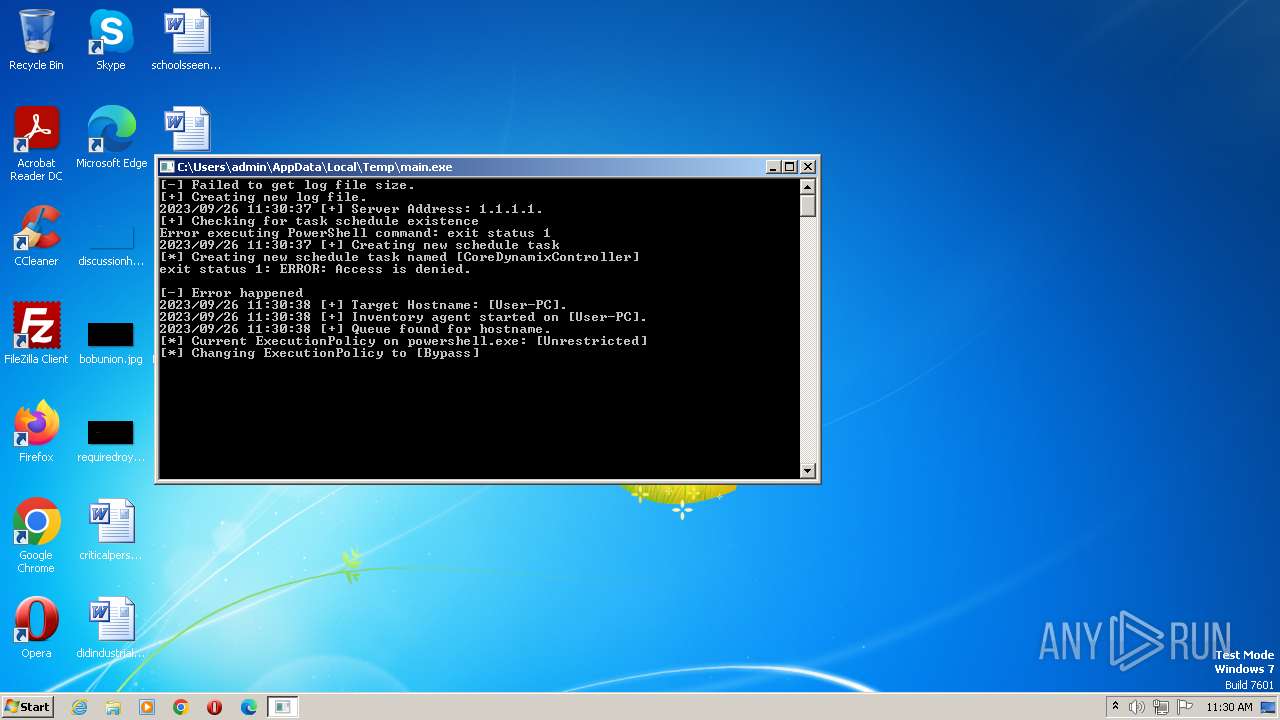
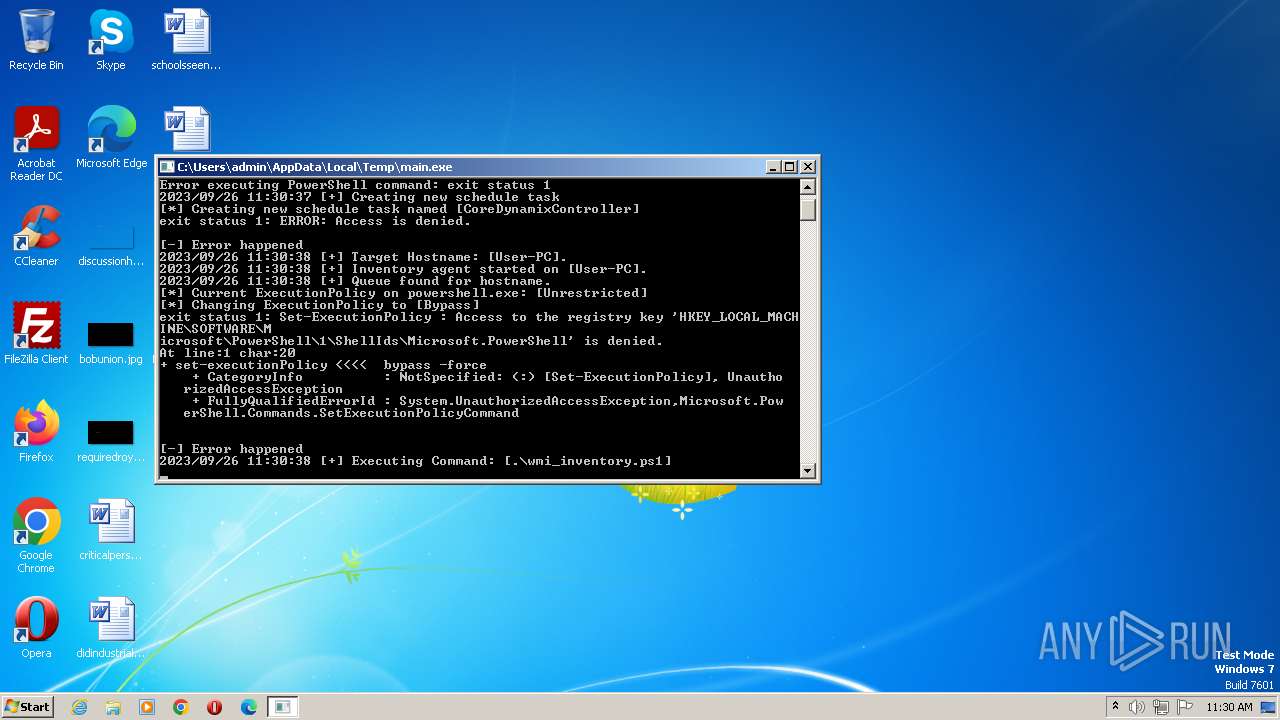
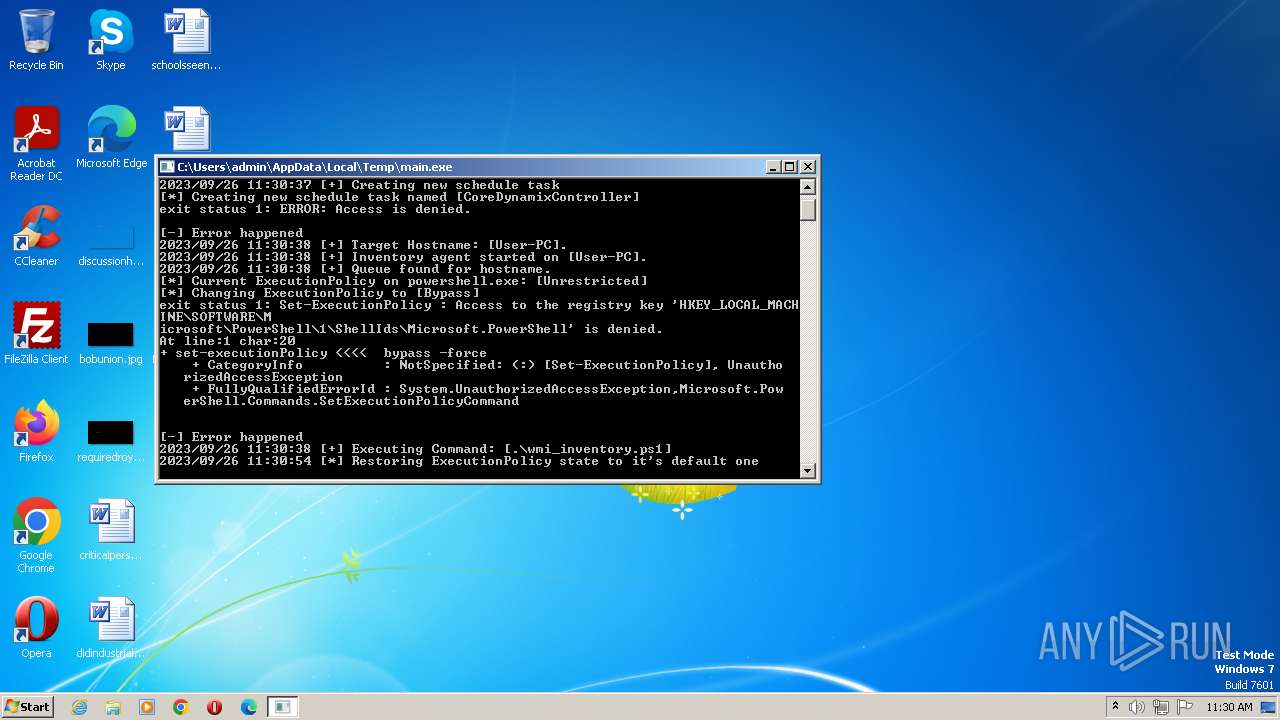
Bypass execution policy to execute commands
- powershell.exe (PID: 3904)
Changes powershell execution policy (Bypass)
- main.exe (PID: 3564)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 2932)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- main.exe (PID: 3564)
Powershell version downgrade attack
- powershell.exe (PID: 2932)
- powershell.exe (PID: 3904)
- powershell.exe (PID: 2612)
- powershell.exe (PID: 3328)
- powershell.exe (PID: 600)
- powershell.exe (PID: 2732)
Uses ATTRIB.EXE to modify file attributes
- main.exe (PID: 3564)
The process executes Powershell scripts
- main.exe (PID: 3564)
Reads the Internet Settings
- powershell.exe (PID: 3328)
INFO
Checks supported languages
- main.exe (PID: 3564)
Create files in a temporary directory
- main.exe (PID: 3564)
Gets the execution policy for the powershell session
- main.exe (PID: 3564)
Creates files or folders in the user directory
- main.exe (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6.1 |
| ImageVersion: | 1 |
| OSVersion: | 6.1 |
| EntryPoint: | 0x63a70 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 219648 |
| CodeSize: | 2470400 |
| LinkerVersion: | 3 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit, No debug |
| TimeStamp: | 0000:00:00 00:00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Total processes
47
Monitored processes
9
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | powershell.exe -Command "if (Get-ScheduledTask -TaskName CoreDynamixController -ErrorAction SilentlyContinue) { Write-Output \"True\" } else { Write-Output \"False\" }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1628 | "C:\Windows\system32\schtasks.exe" /create /xml CoreDynamixController.xml /tn CoreDynamixController | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | powershell.exe Get-ExecutionPolicy | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | powershell.exe "set-executionPolicy Unrestricted -force" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | powershell.exe "schtasks /create /xml \"CoreDynamixController.xml\" /tn \"CoreDynamixController\"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | attrib "+h \"wmi_inventory.ps1\"" | C:\Windows\System32\attrib.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3328 | powershell.exe .\wmi_inventory.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3564 | "C:\Users\admin\AppData\Local\Temp\main.exe" | C:\Users\admin\AppData\Local\Temp\main.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3904 | powershell.exe "set-executionPolicy bypass -force" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 380
Read events
17 048
Write events
332
Delete events
0
Modification events
| (PID) Process: | (600) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2932) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2612) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3904) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3328) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3328) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3328) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3328) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3328) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2732) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
19
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 600 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JL9U308814WF3TPFCY0R.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 2932 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 3564 | main.exe | C:\Users\admin\AppData\Local\Temp\CoreDynamixController.xml | xml | |
MD5:9B7BD2495247019E82AAD2CD10C0D305 | SHA256:1243BA946801ED0CD2E08A055F38E391C8FD33B5FF5C36510E2965560FFCB1CA | |||
| 2612 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFf8023.TMP | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 2612 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RDTD0BIPI12L1TT9WQFL.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 3564 | main.exe | C:\Users\admin\AppData\Local\Temp\wmi_inventory.ps1 | text | |
MD5:C3819FFCB32E2C246164B27A31308E3C | SHA256:FD96396FD73B6E69B048B1A36827DB36FD4E4FA22DC9531A8EE9A80C7965BB5D | |||
| 2932 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZLB89MUHSZVIYKSBX05Z.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 3904 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X7HJA97SPKJ7IXSKNRCR.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 2612 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 600 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFf7c4b.TMP | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3564 | main.exe | 1.1.1.1:443 | — | CLOUDFLARENET | — | unknown |