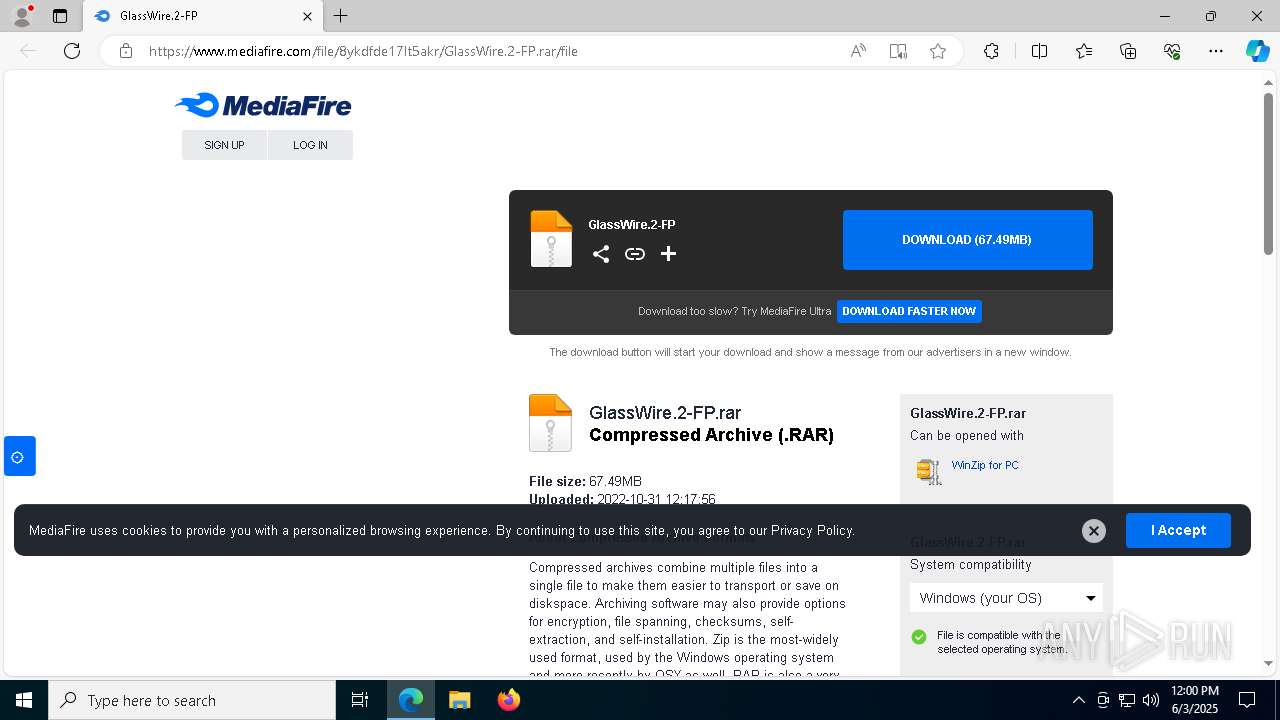
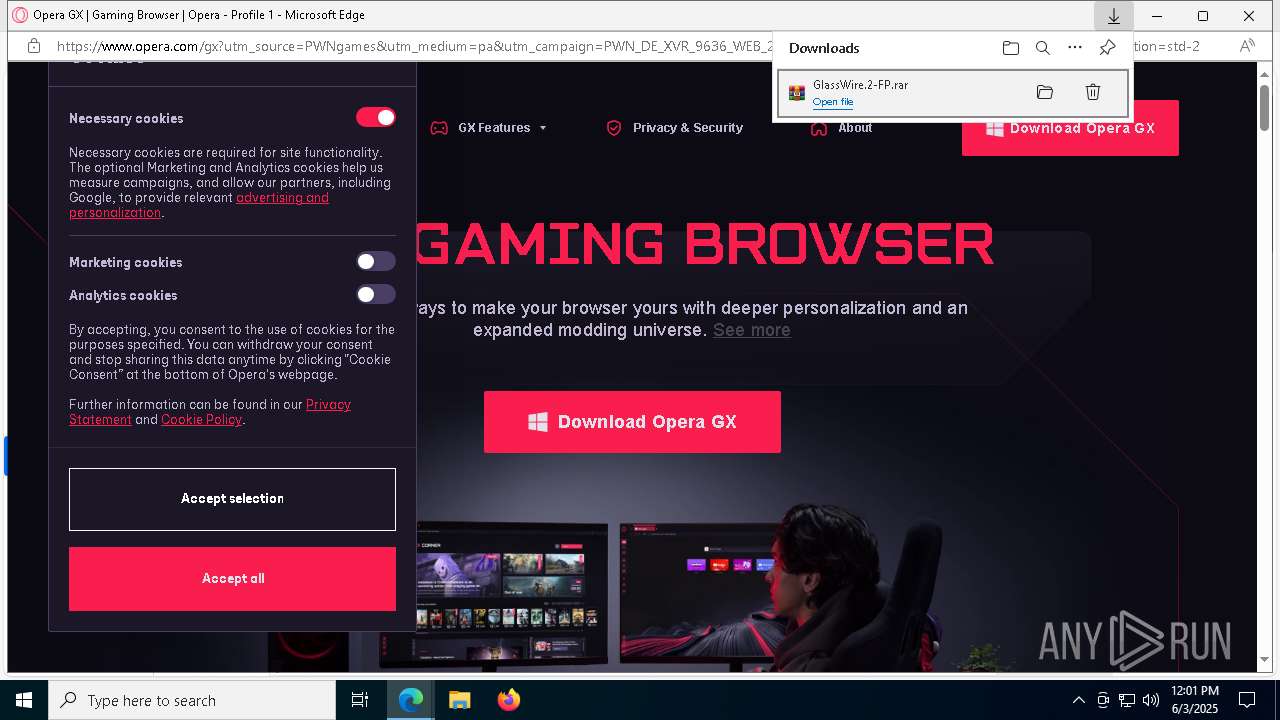
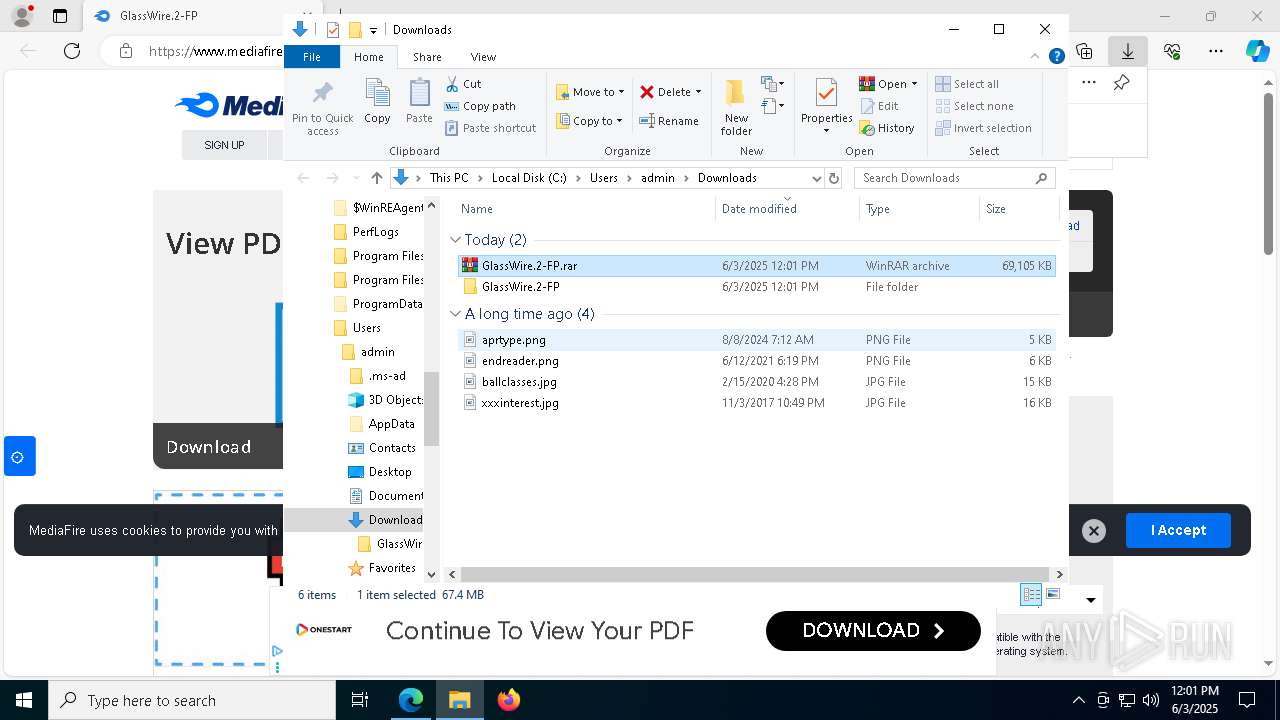
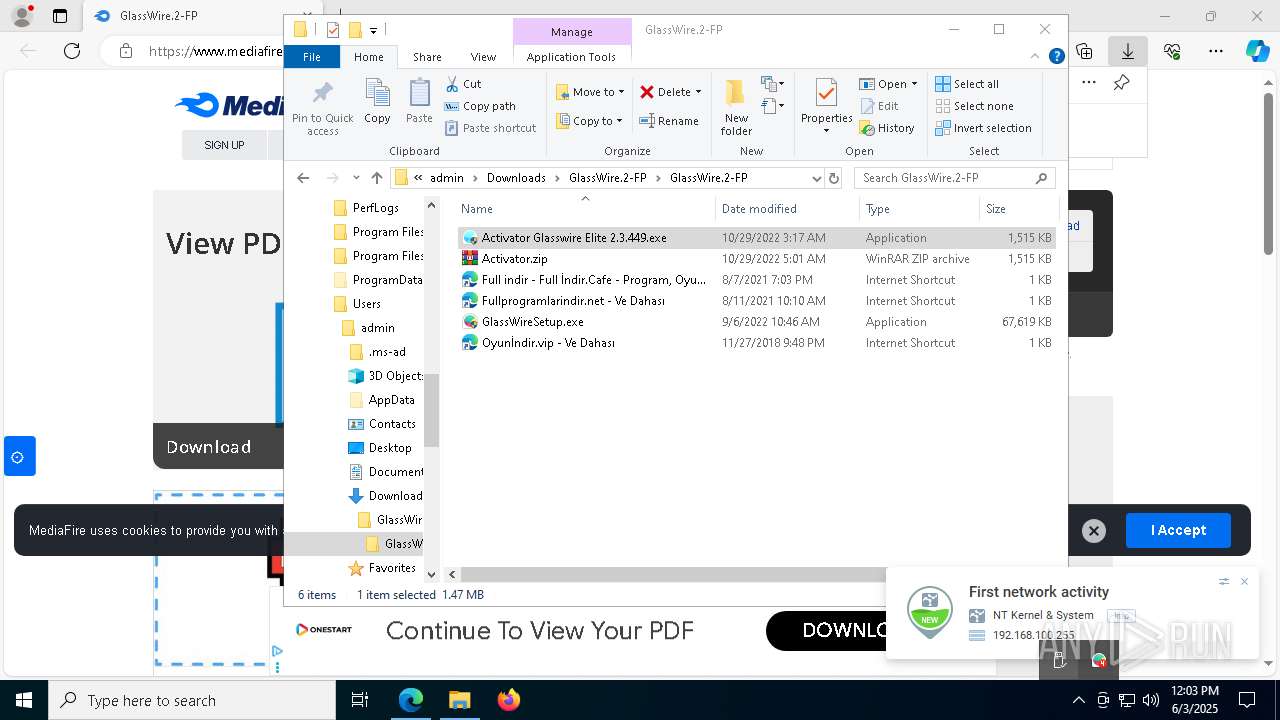
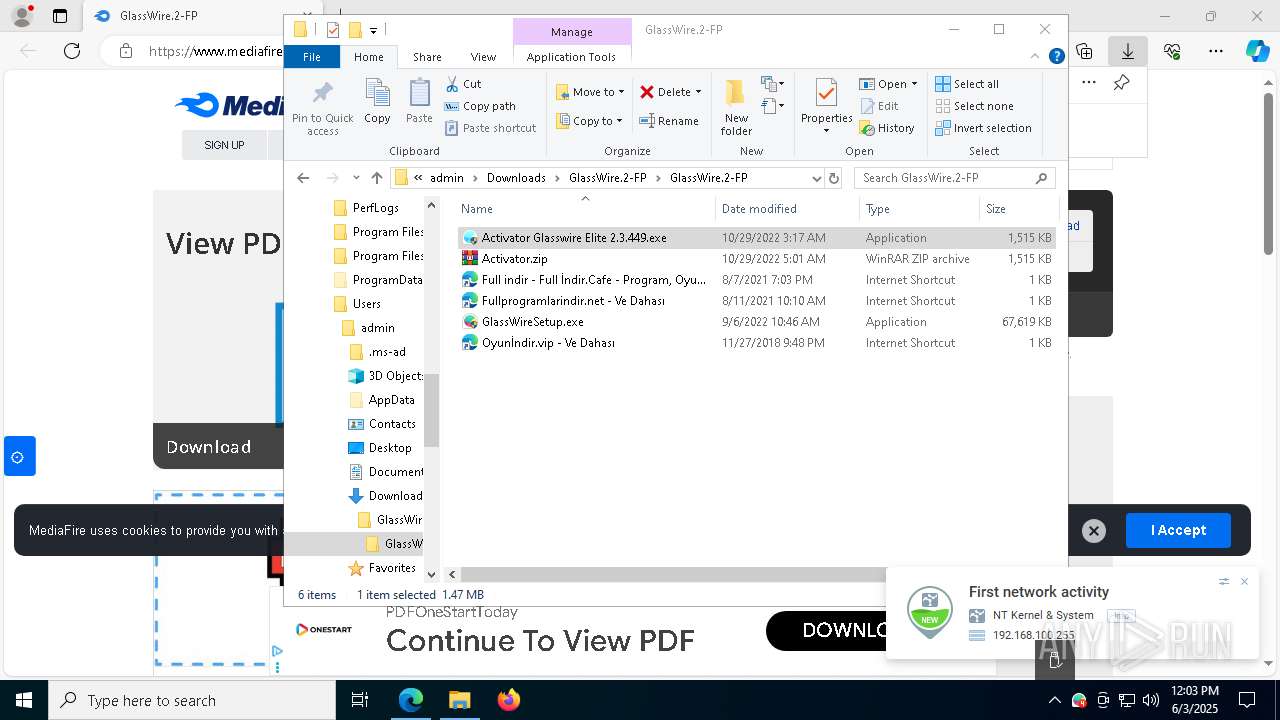
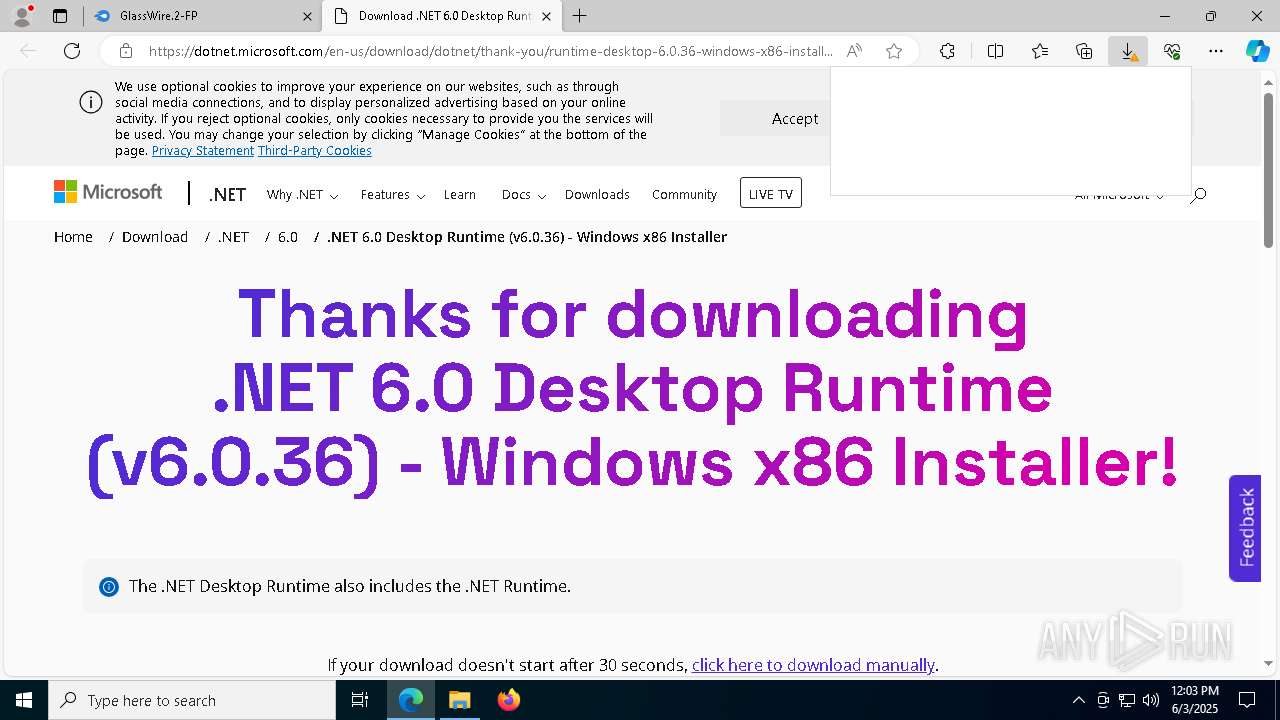
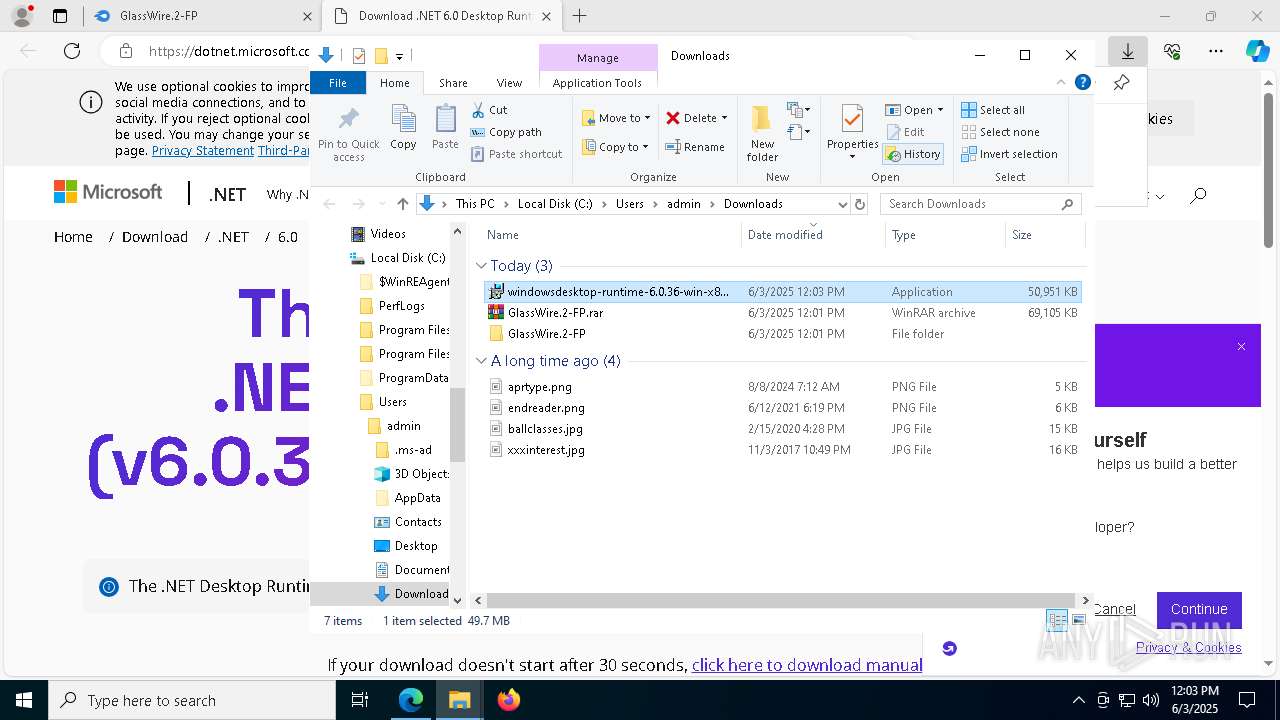
| URL: | https://www.mediafire.com/file/8ykdfde17lt5akr/GlassWire.2-FP.rar/file |
| Full analysis: | https://app.any.run/tasks/04a7eb71-6a26-46ac-a316-5cb2ab2c66b9 |
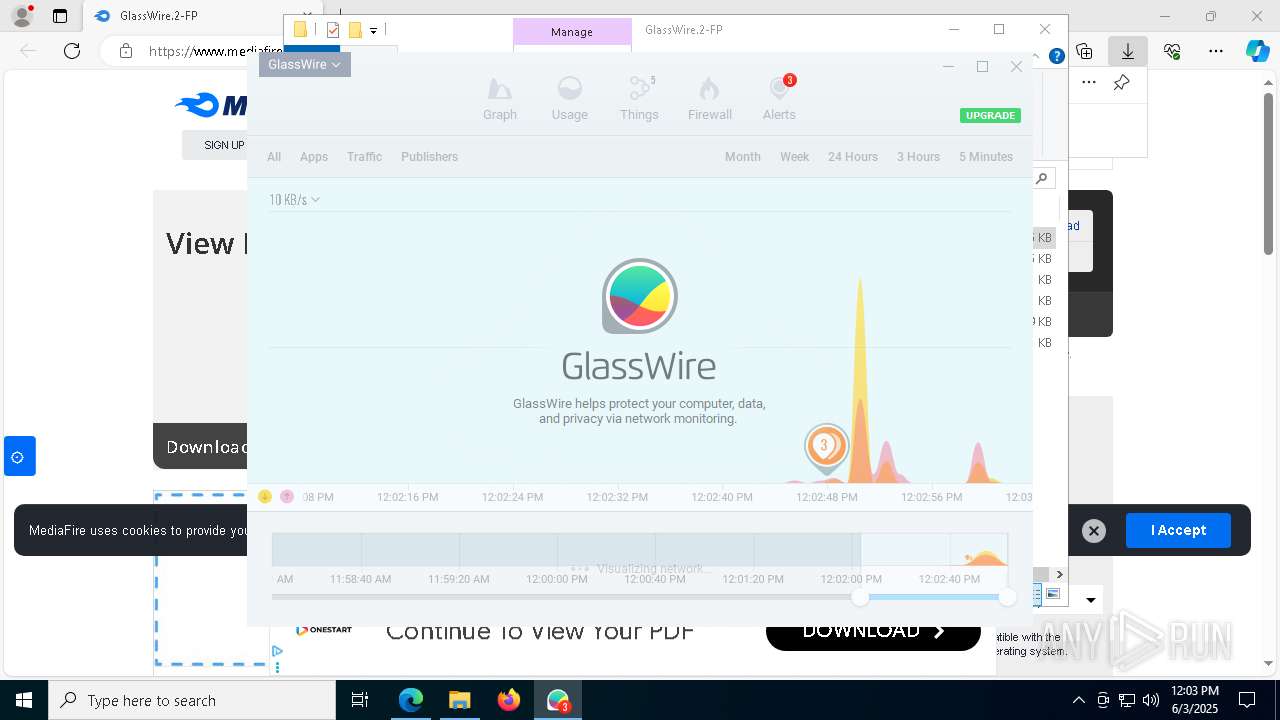
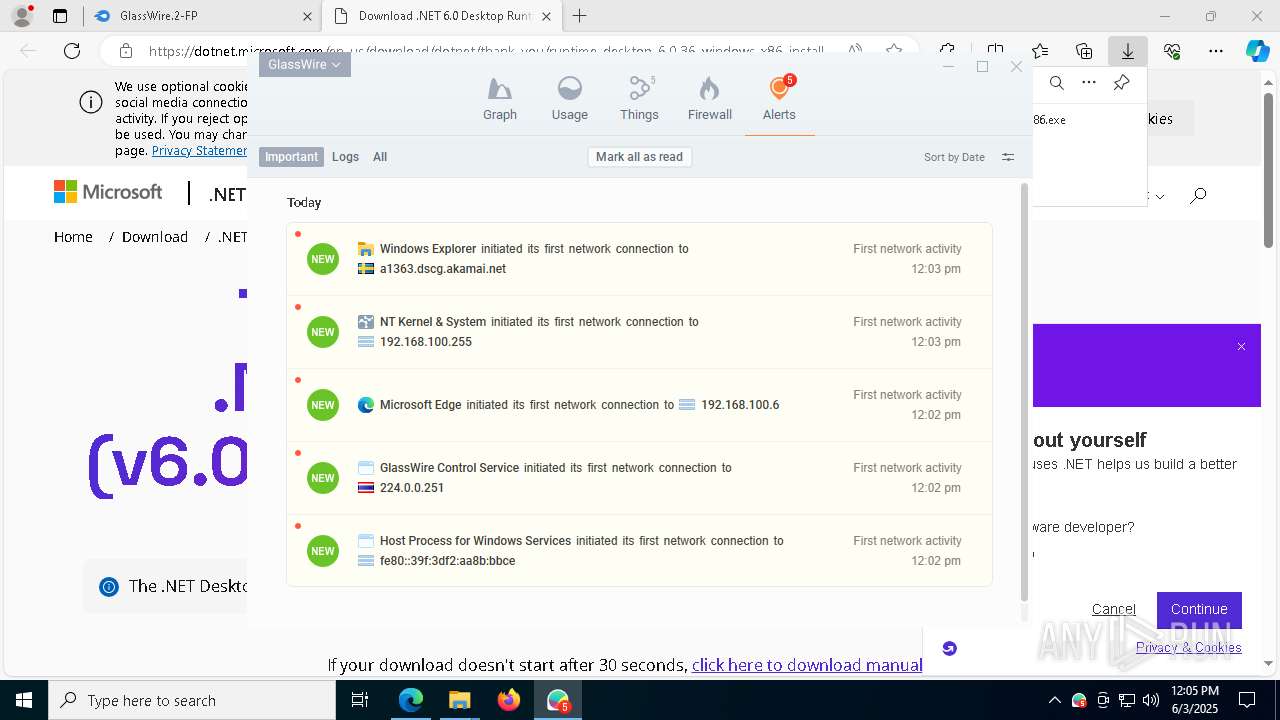
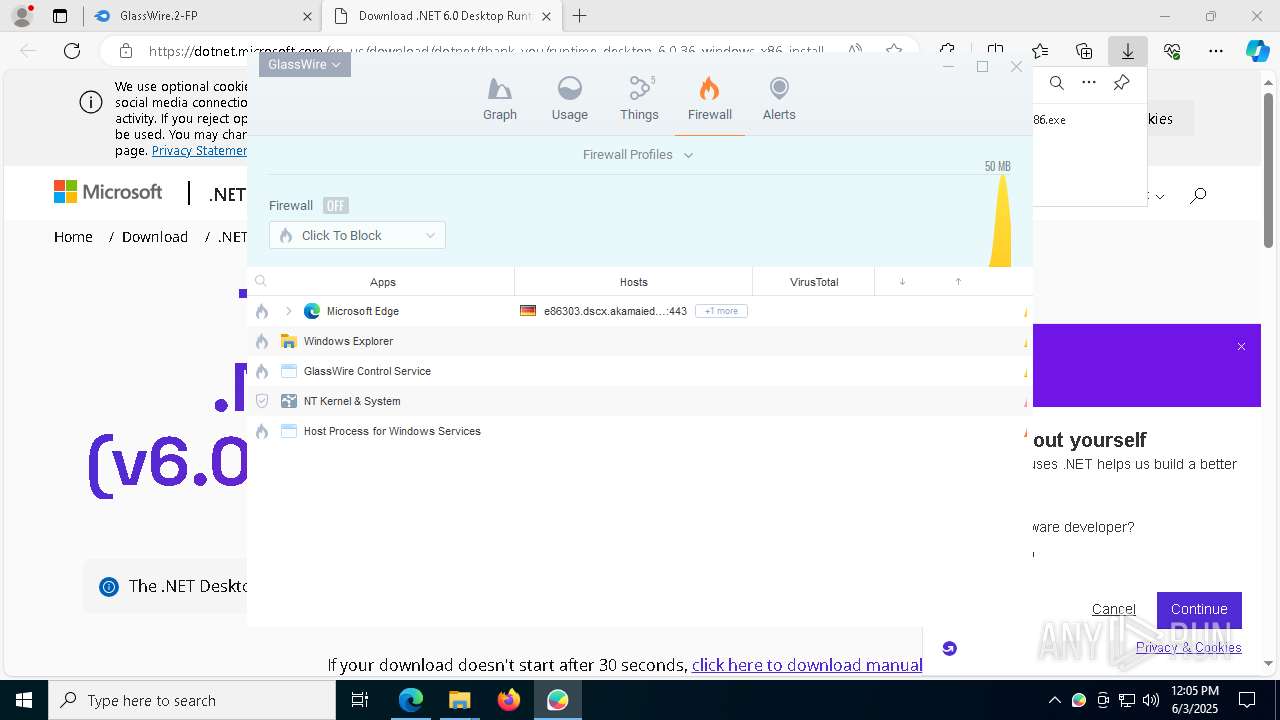
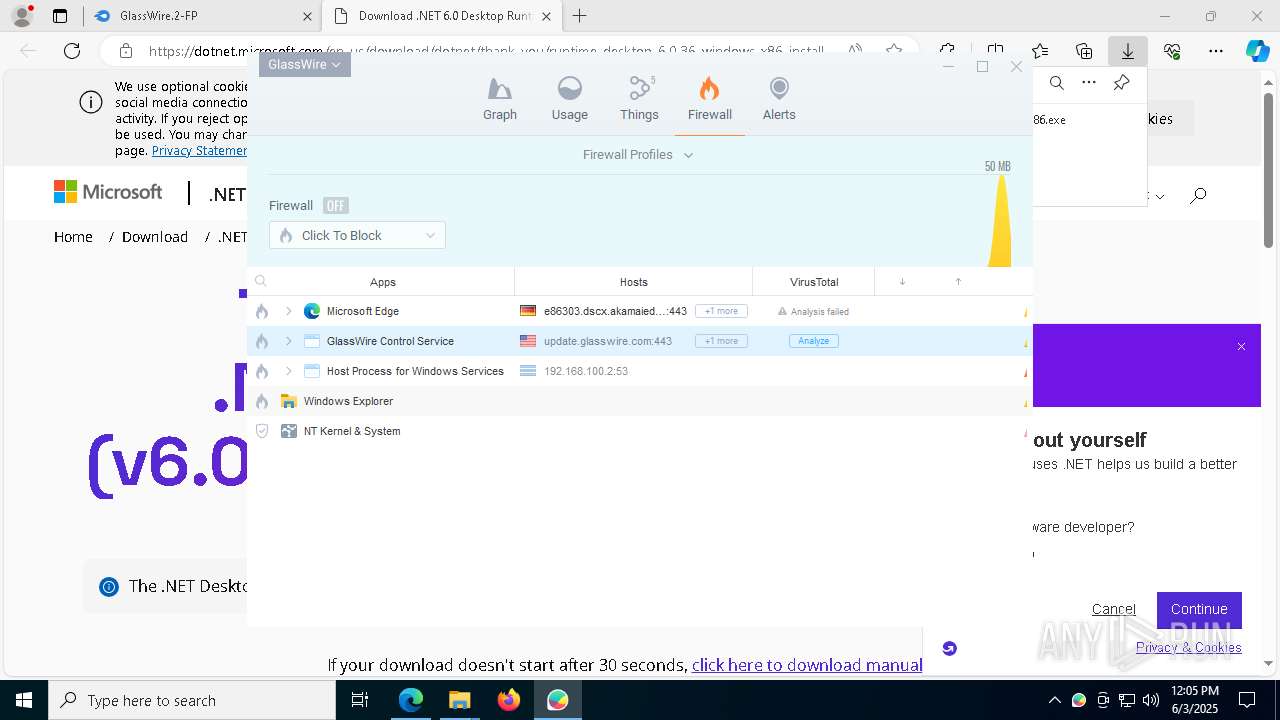
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2025, 12:00:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6D8D313335DD3E56D135EBE3B6E7CC47 |
| SHA1: | 374DDCEC71E015FAC2B81BEB8D36FEC0C015291B |
| SHA256: | 99861CC55C2BF86BB6CAF89DC3646FD0F29B9AEDAA1CF278867CFFA1CC979370 |
| SSDEEP: | 3:N8DSLw3eGUodVSJjeGeOkKcA:2OLw3eG5VrGeOkKcA |
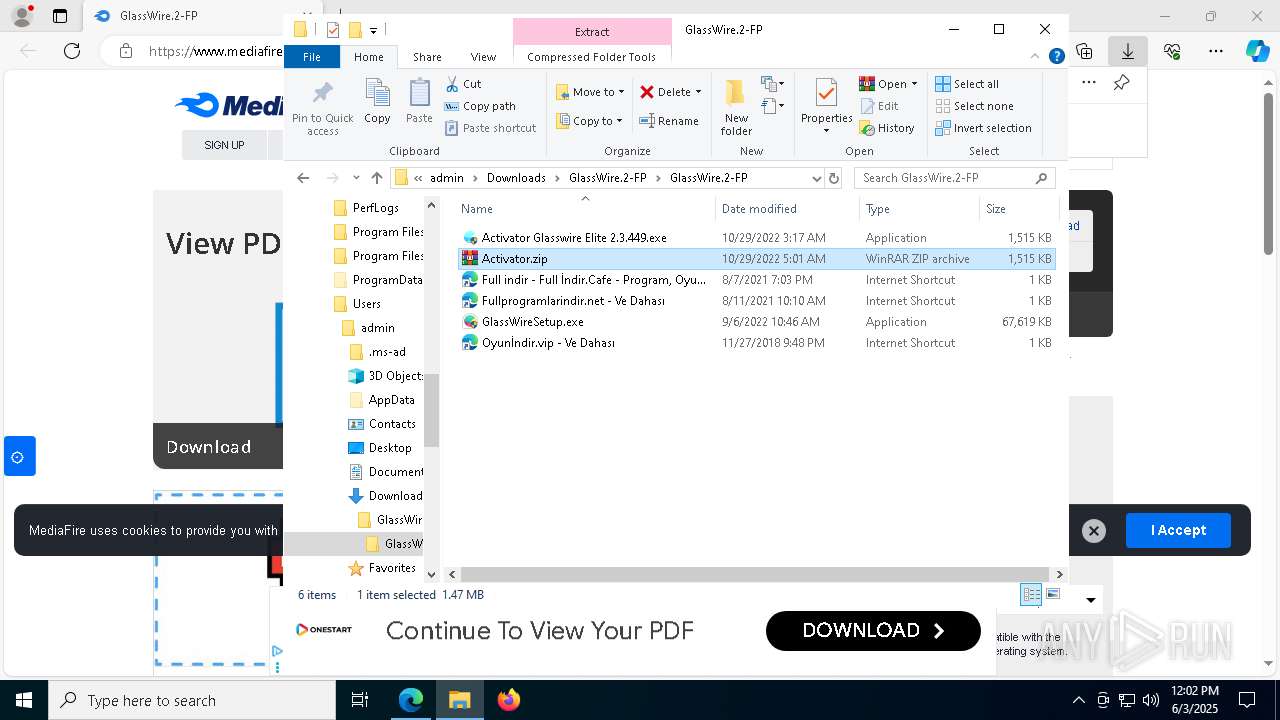
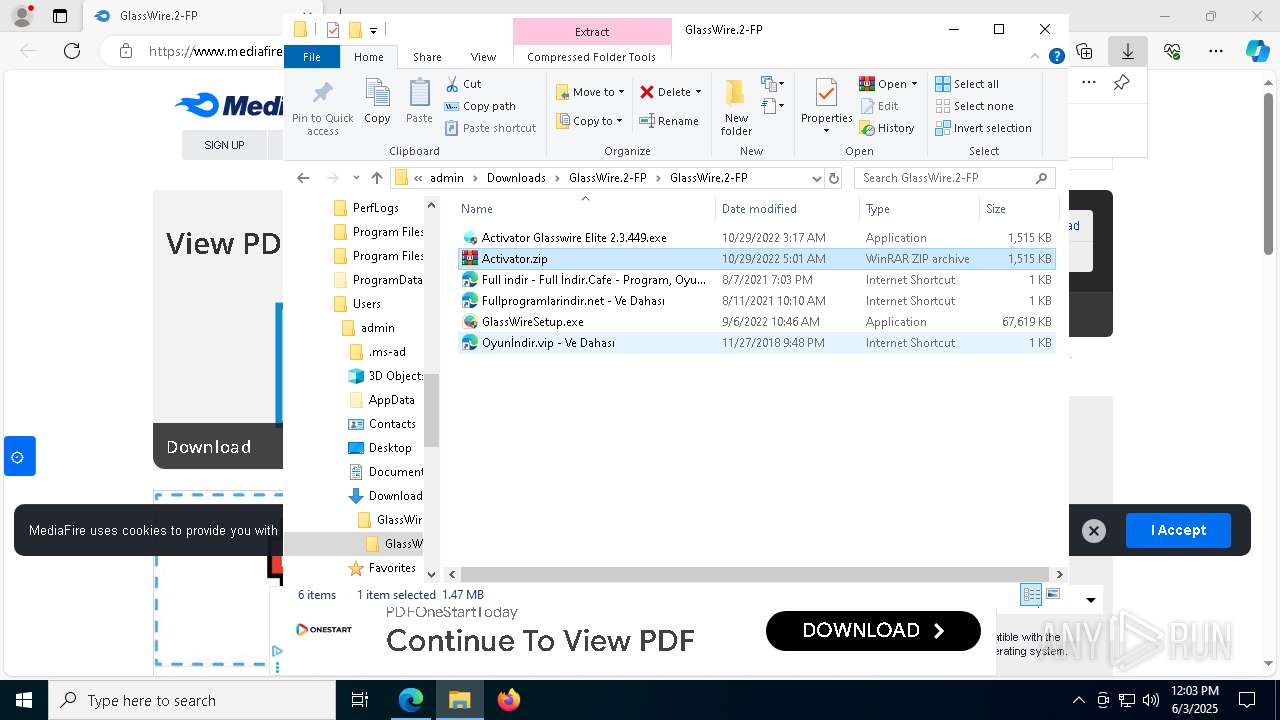
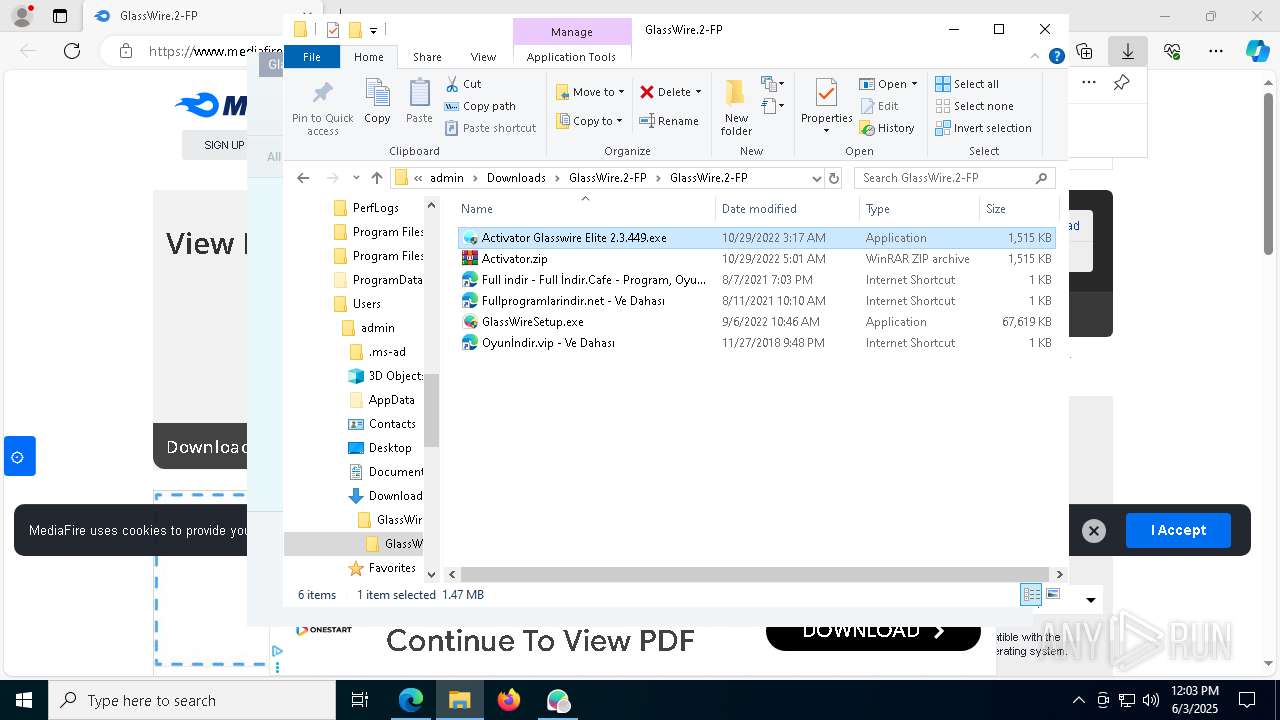
MALICIOUS
Starts NET.EXE for service management
- net.exe (PID: 2612)
- net.exe (PID: 472)
- cmd.exe (PID: 7288)
- GlassWireSetup.exe (PID: 5376)
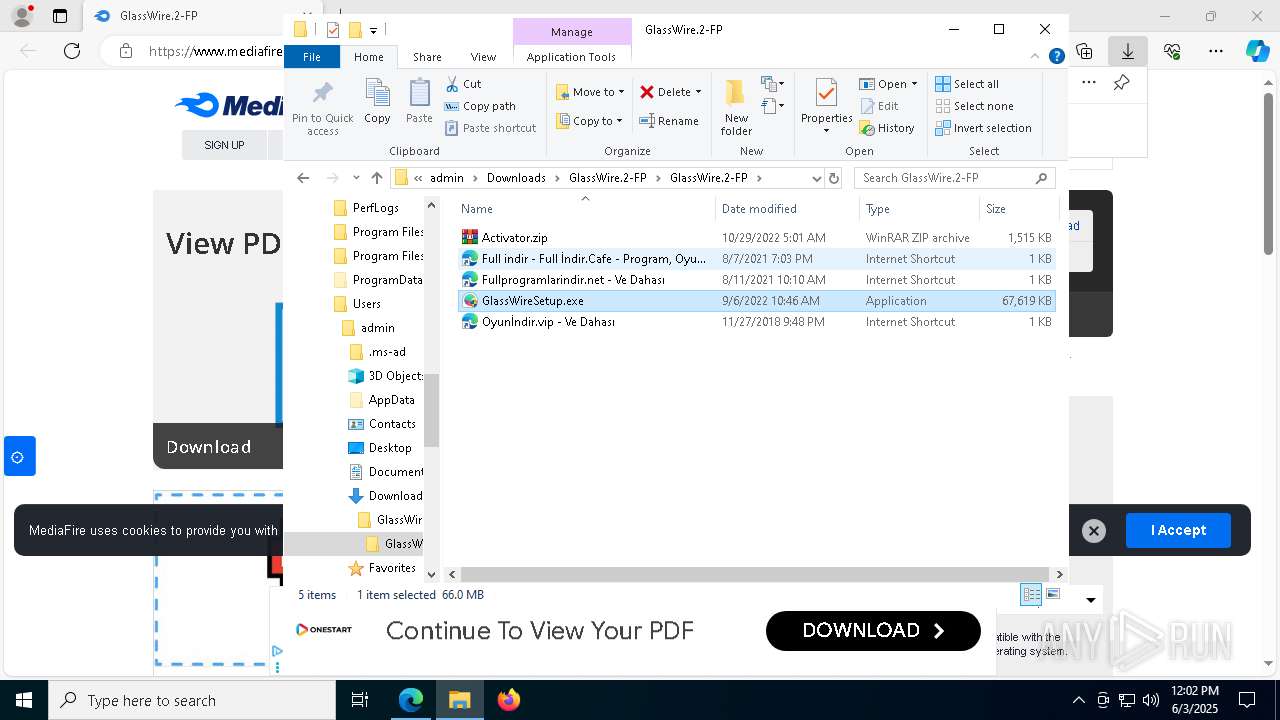
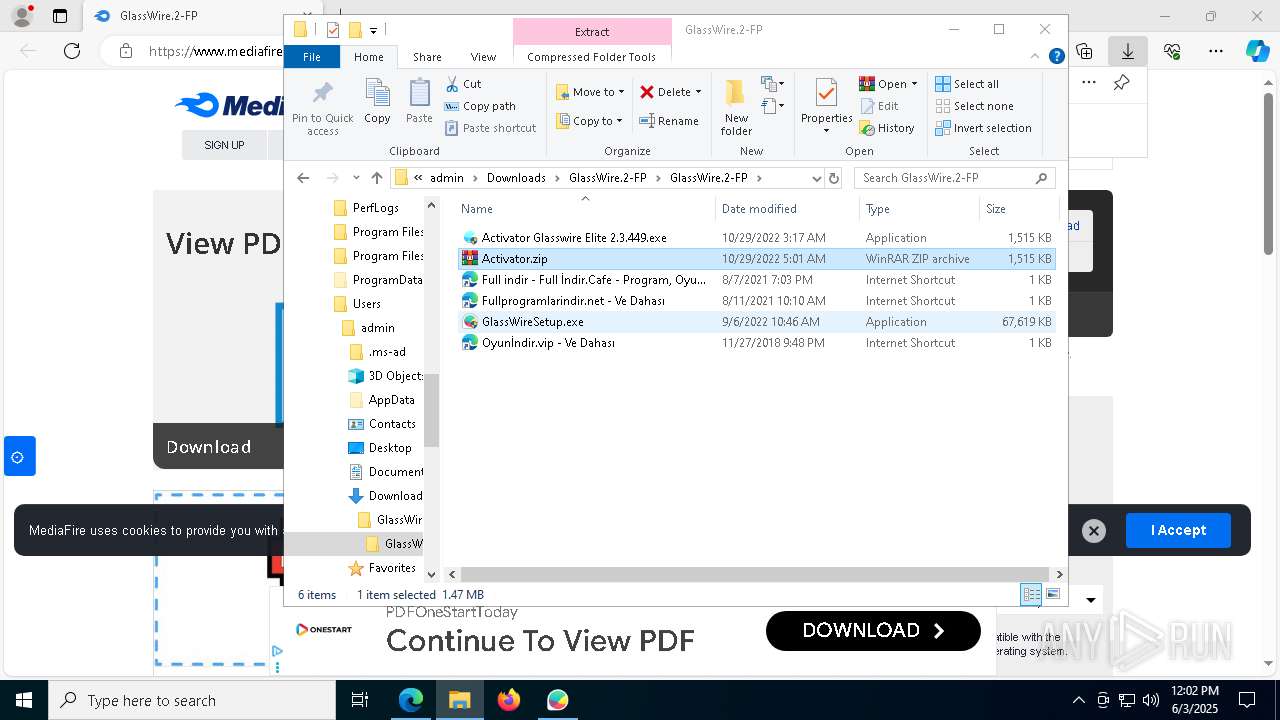
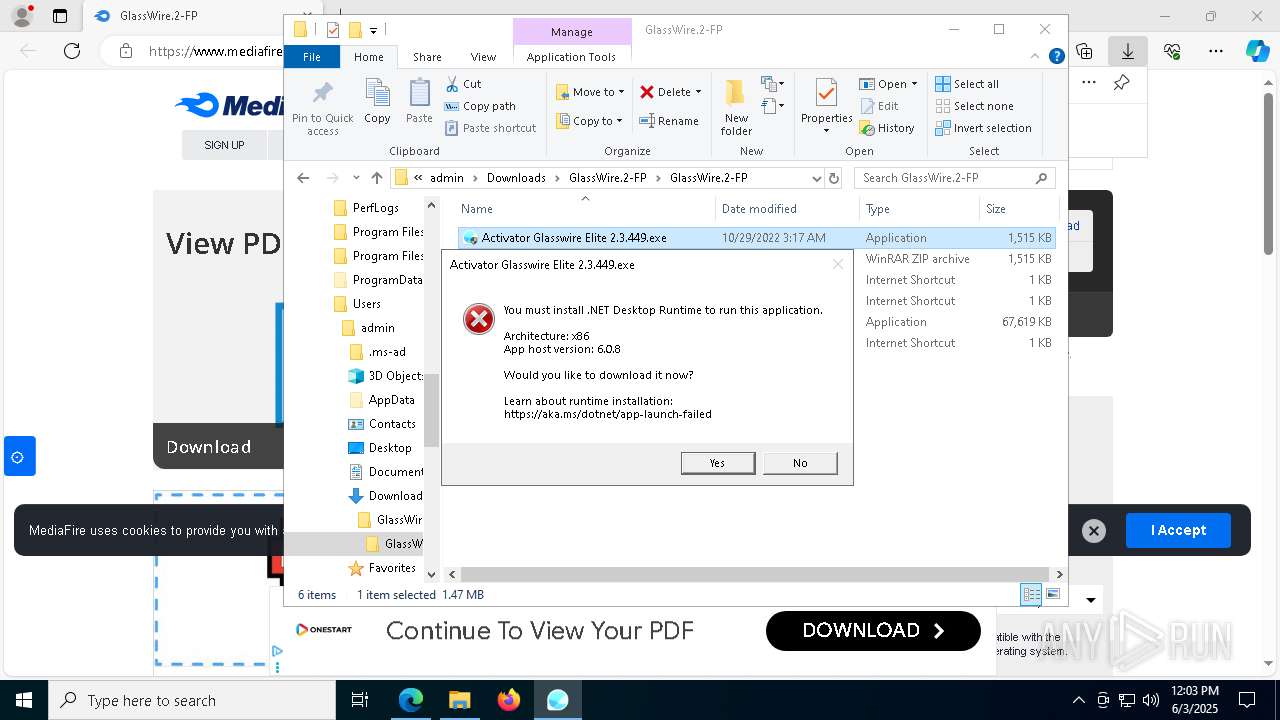
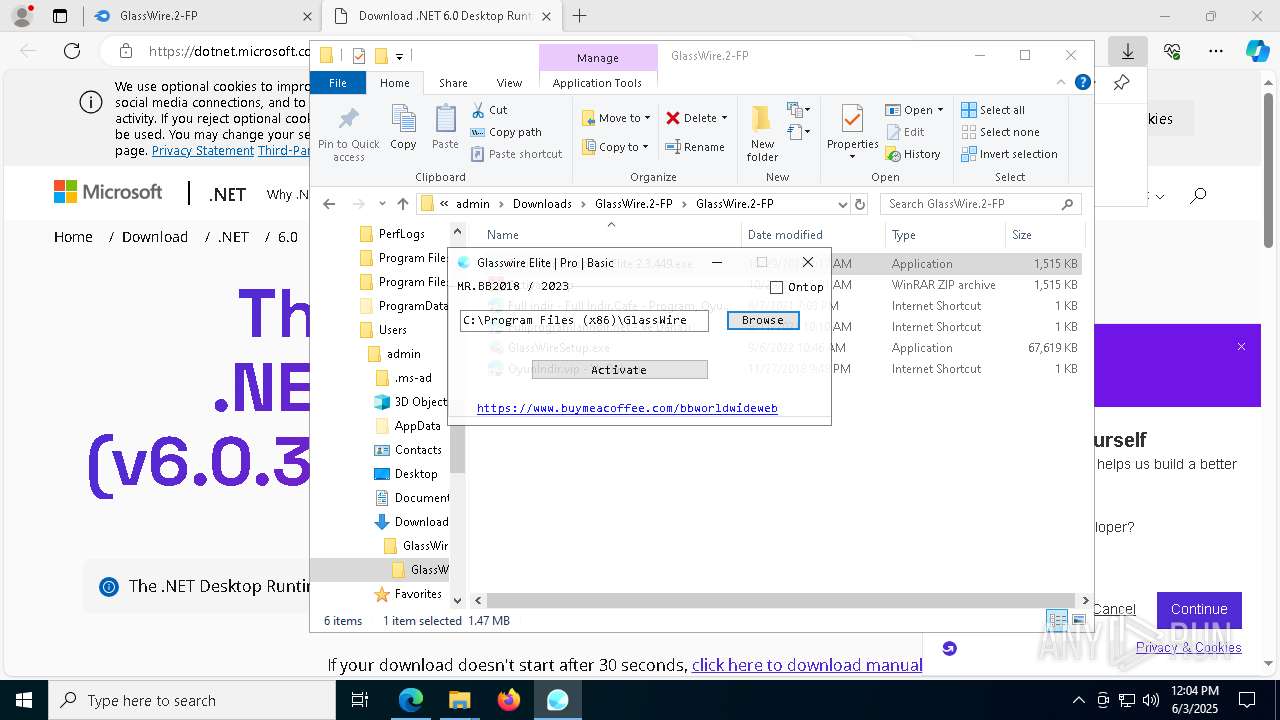
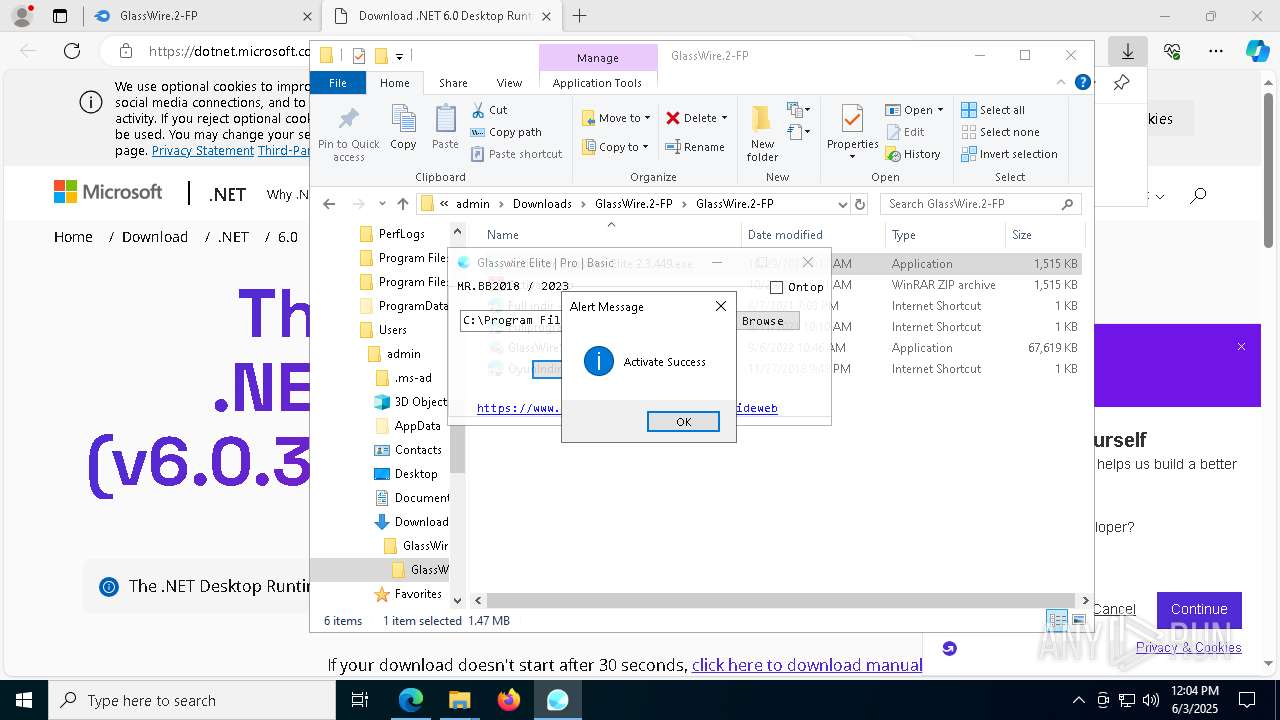
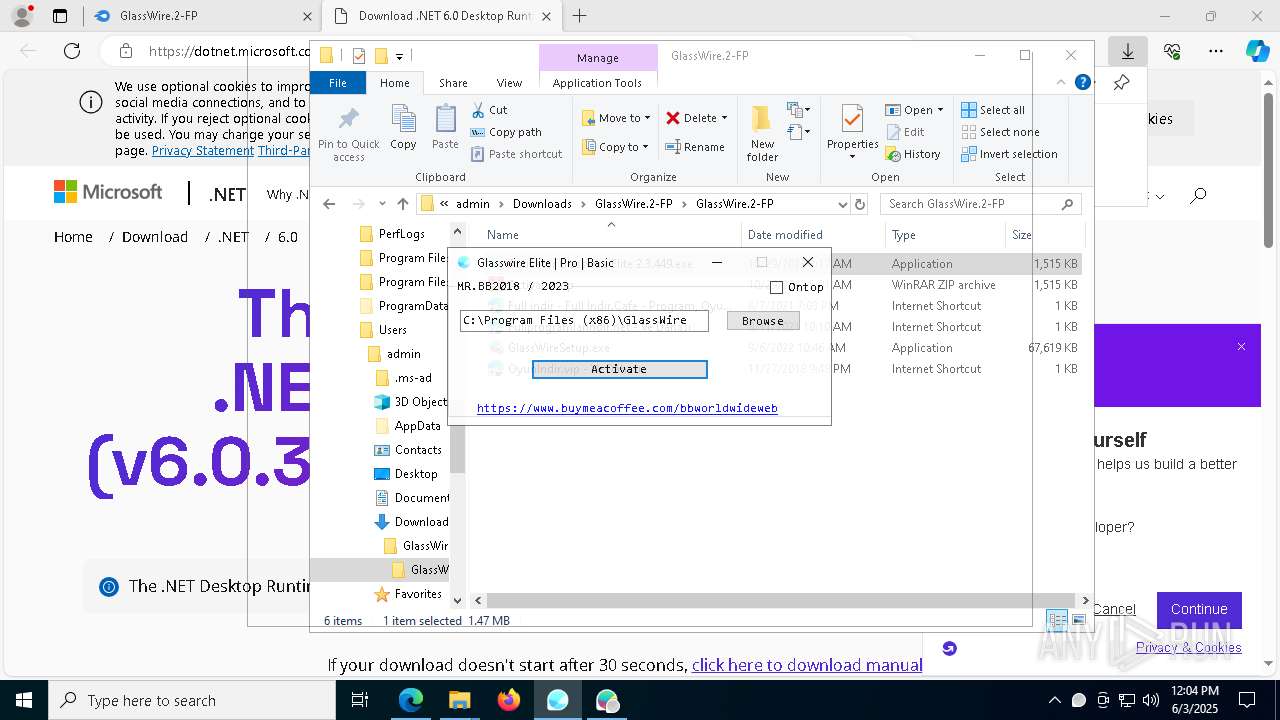
- Activator Glasswire Elite 2.3.449.exe (PID: 3744)
- net.exe (PID: 8236)
- net.exe (PID: 7872)
Changes the autorun value in the registry
- rundll32.exe (PID: 132)
SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 5492)
Malware-specific behavior (creating "System.dll" in Temp)
- GlassWireSetup.exe (PID: 5376)
The process creates files with name similar to system file names
- GlassWireSetup.exe (PID: 5376)
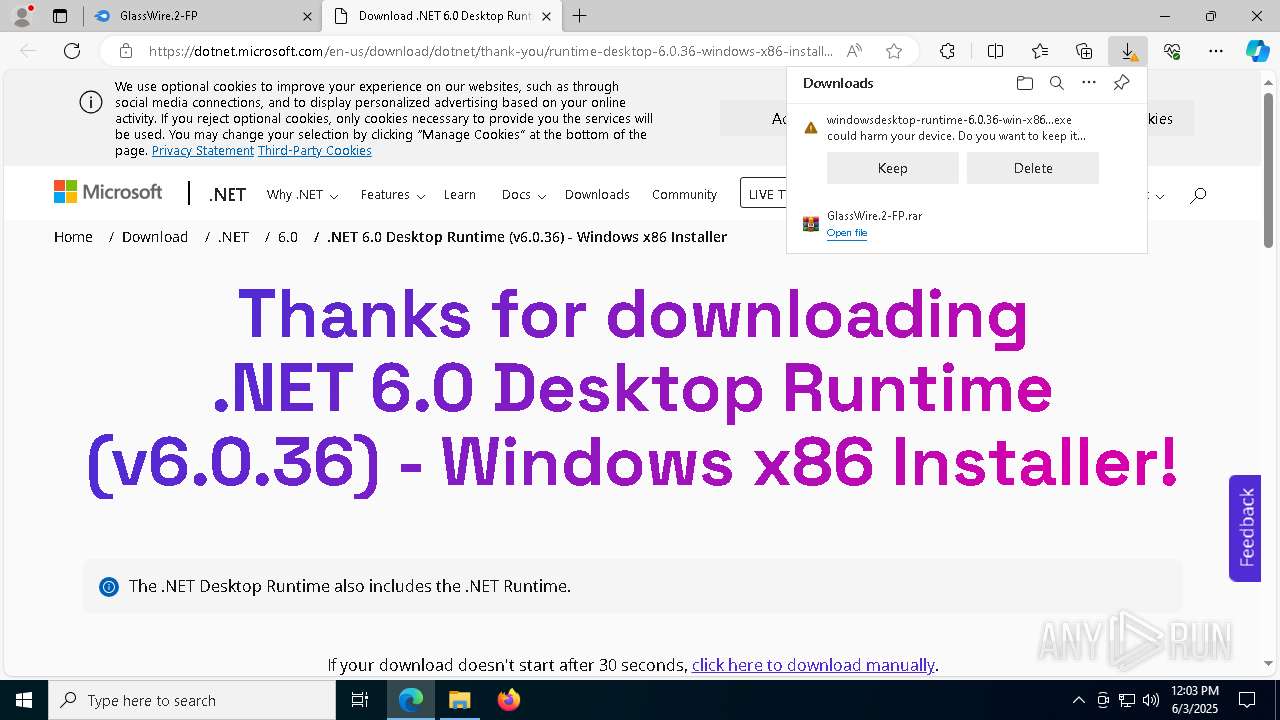
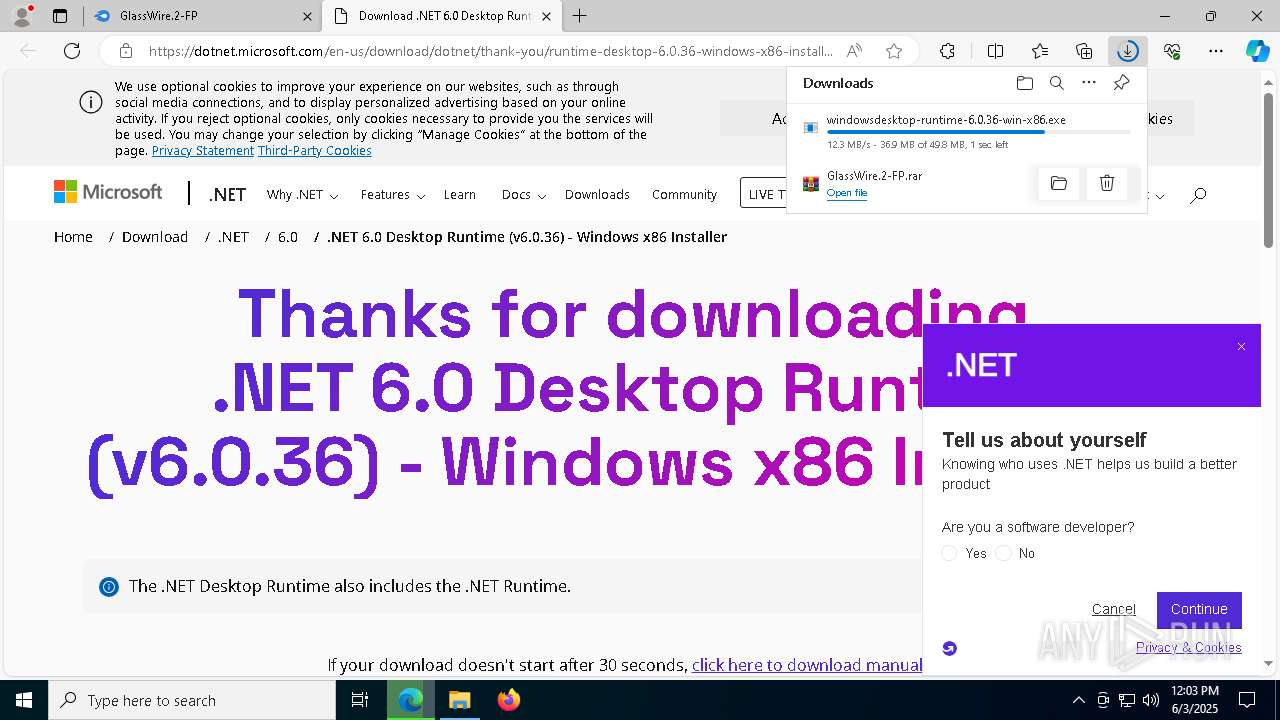
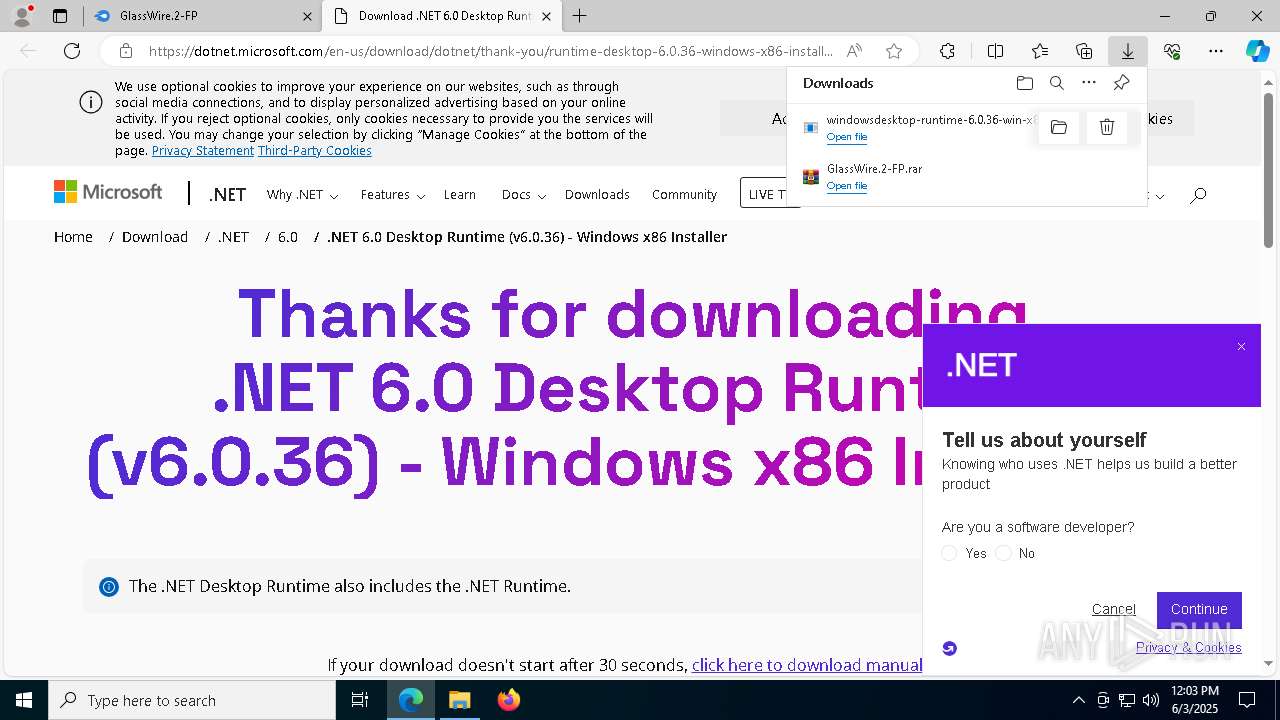
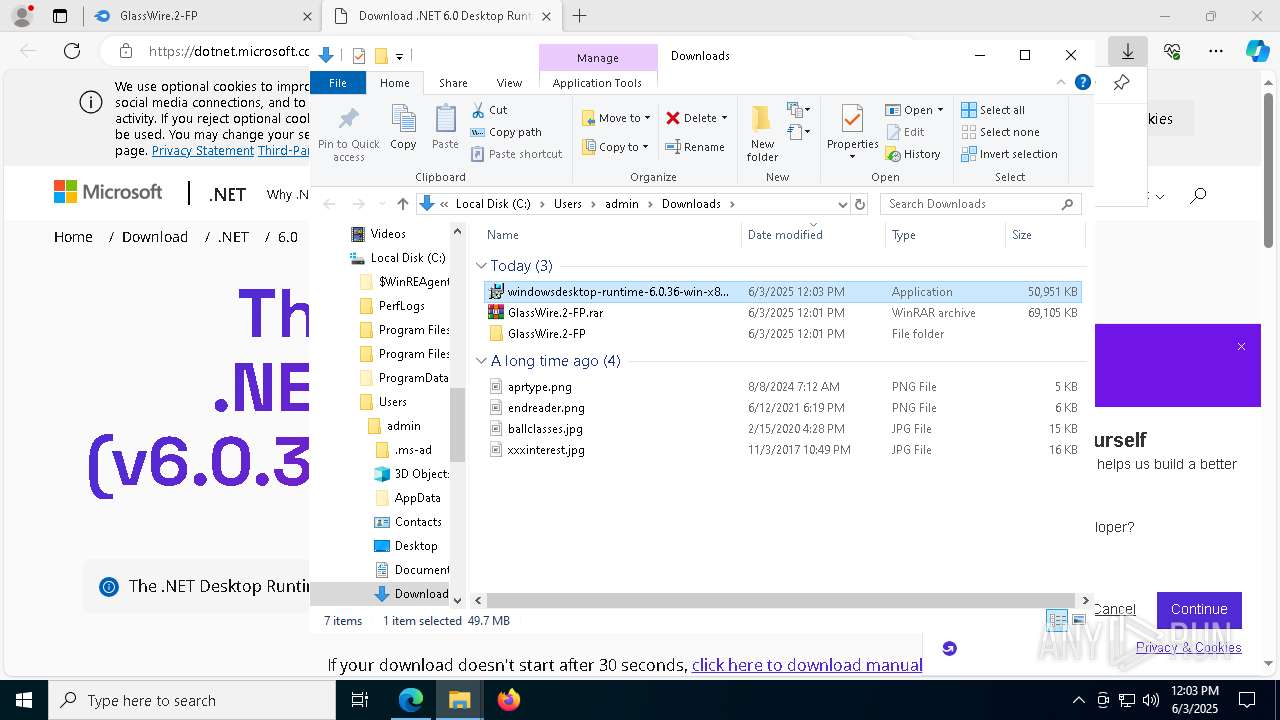
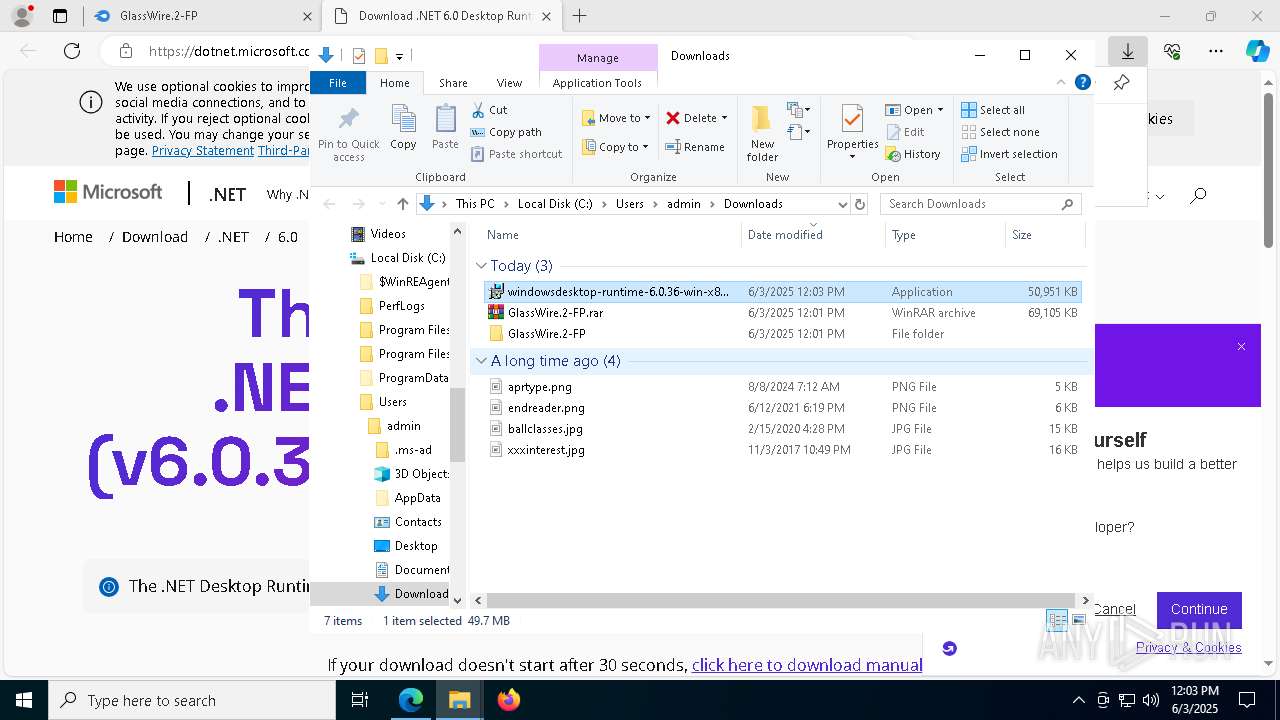
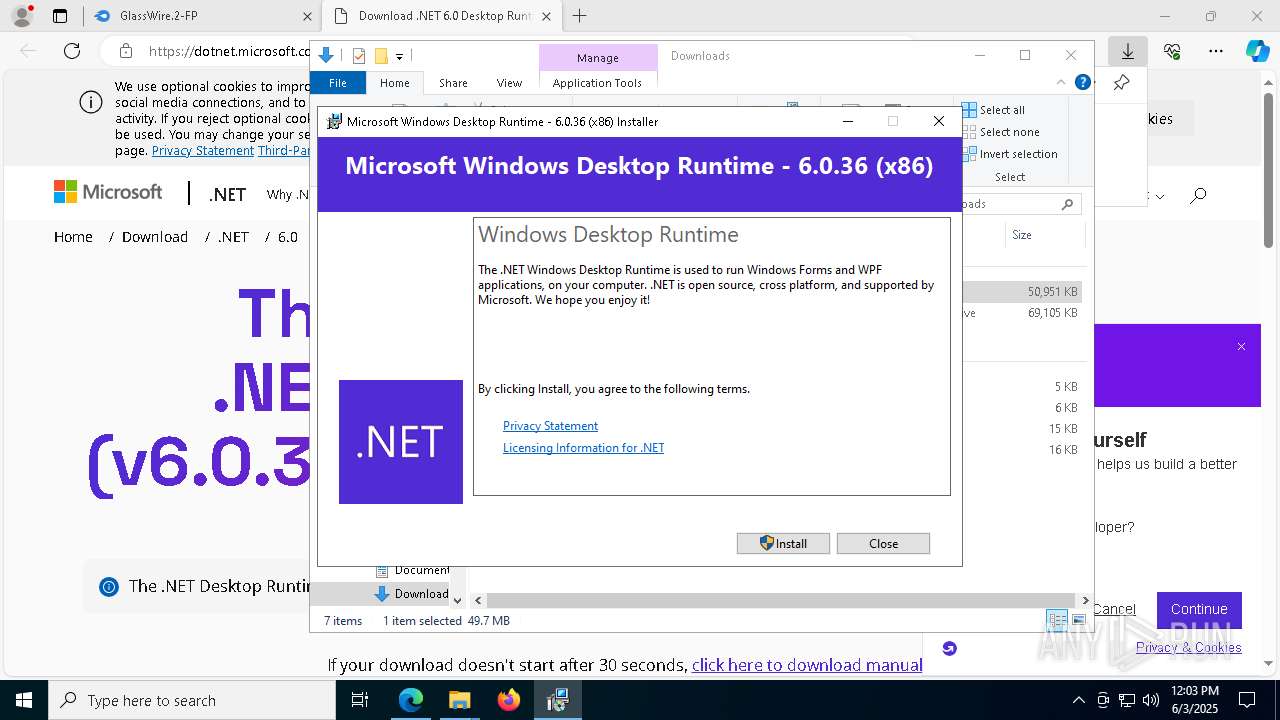
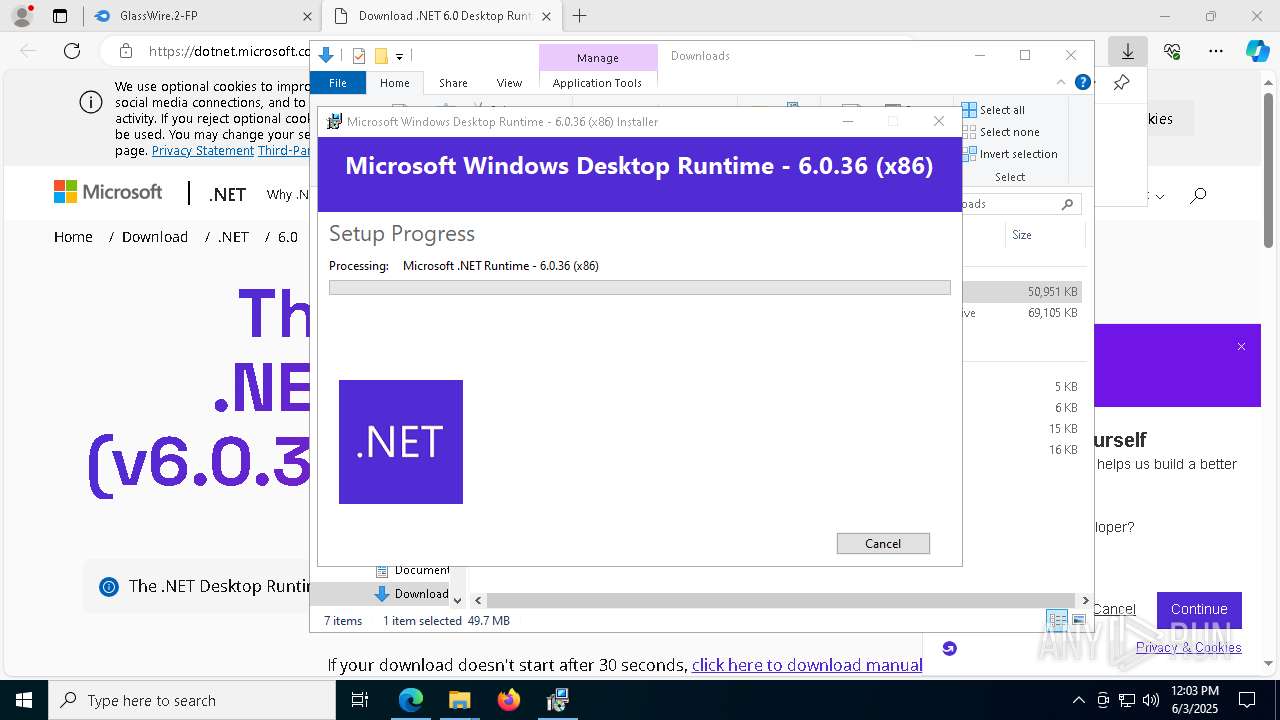
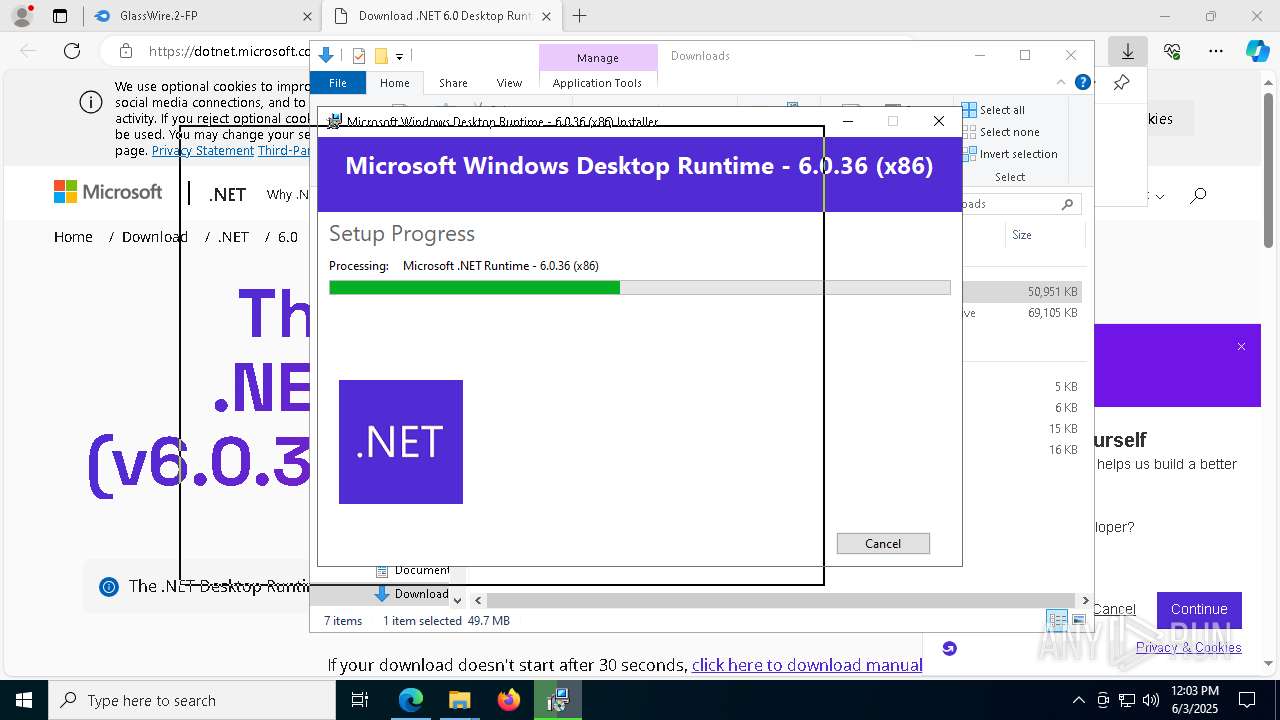
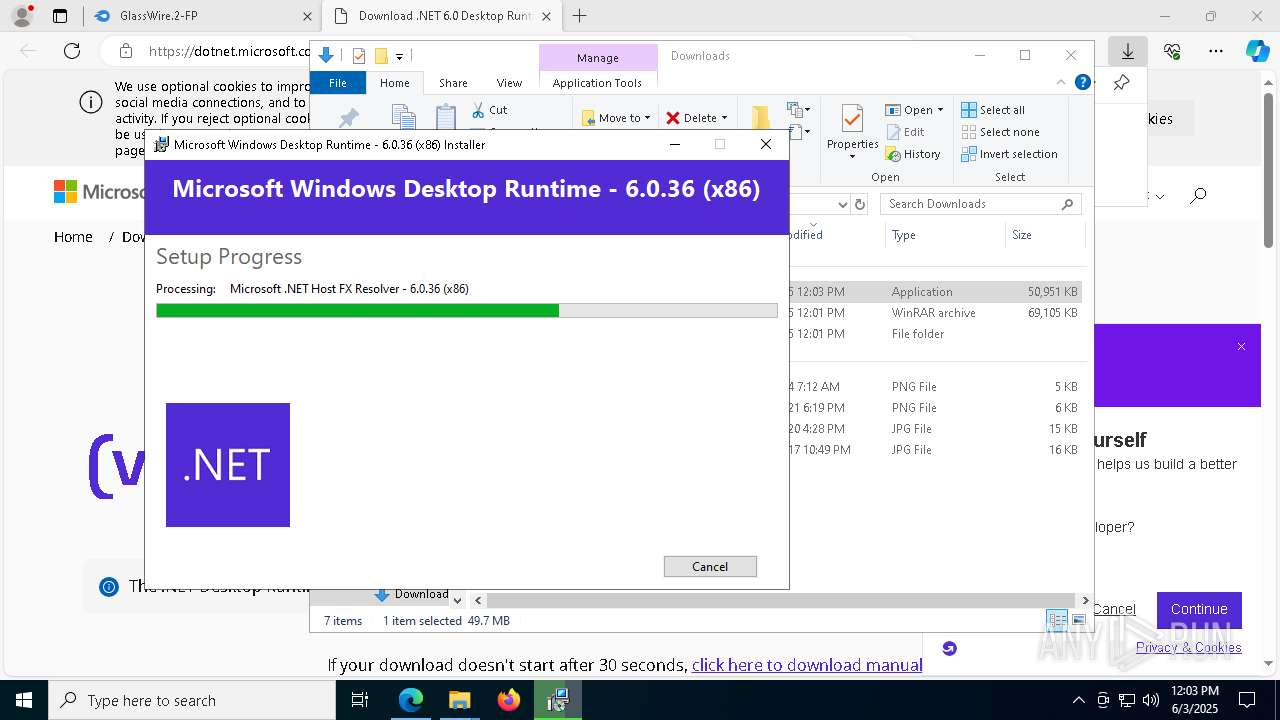
Process drops legitimate windows executable
- GlassWireSetup.exe (PID: 5376)
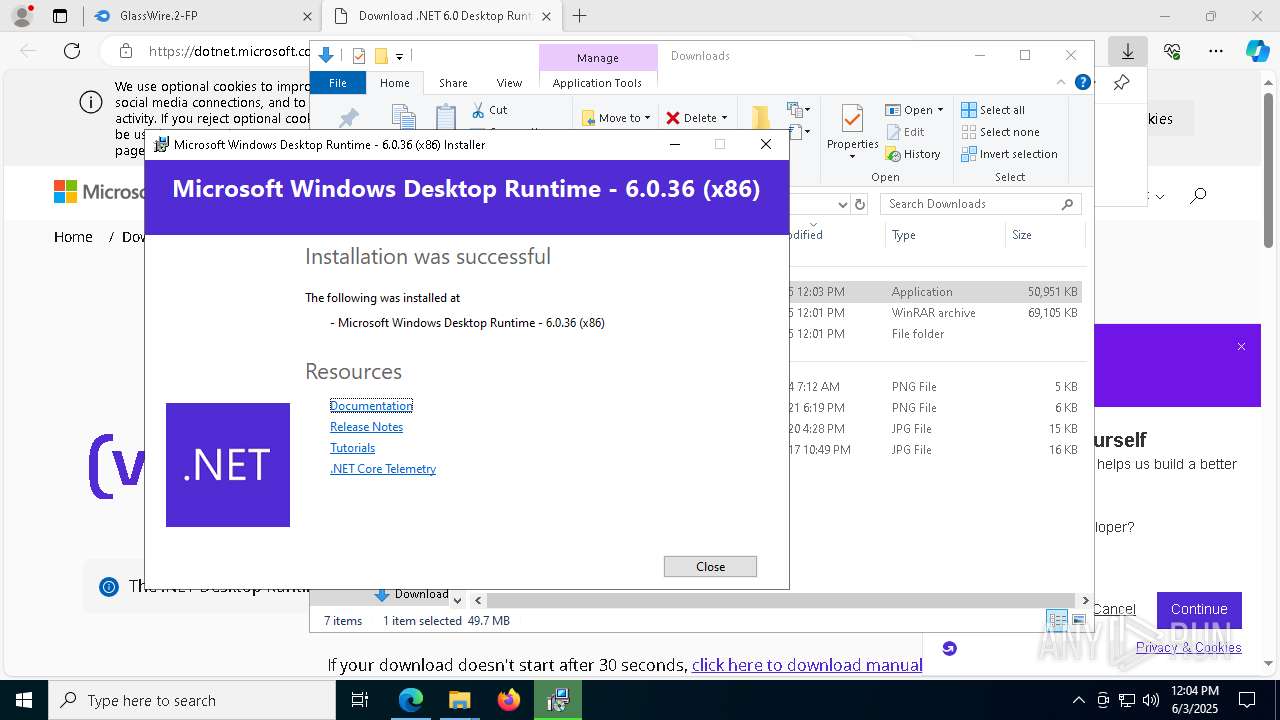
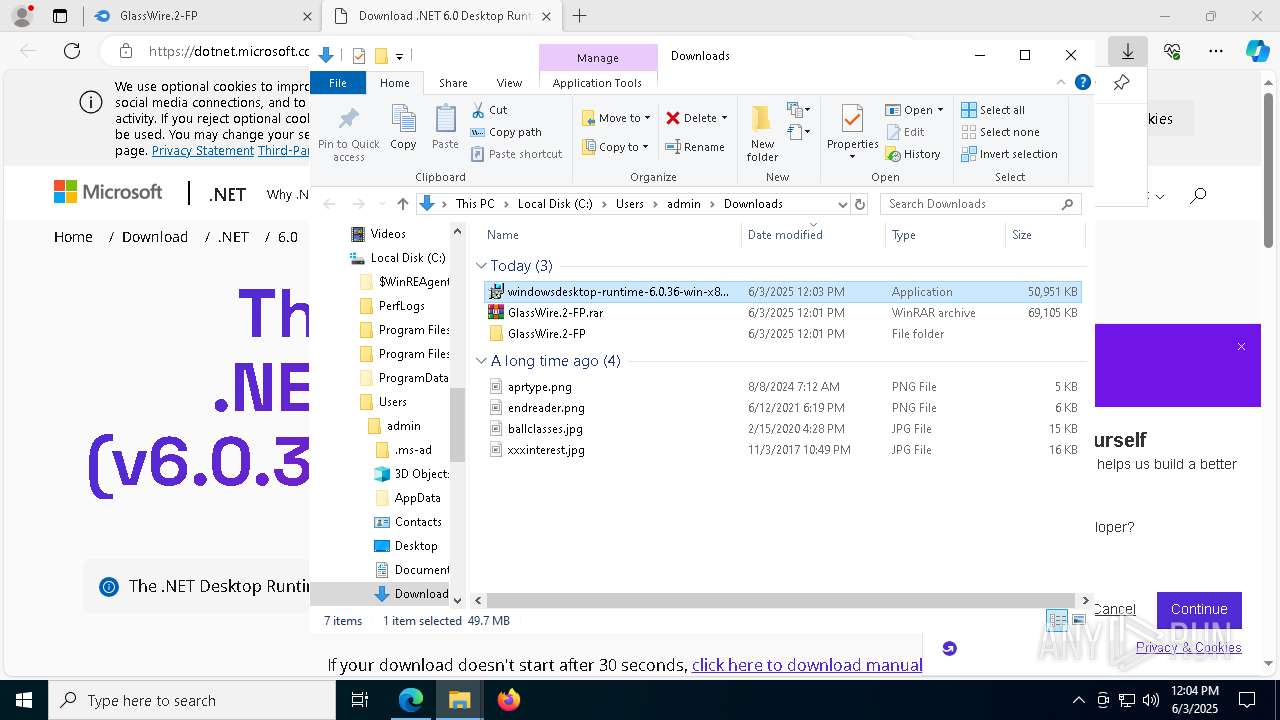
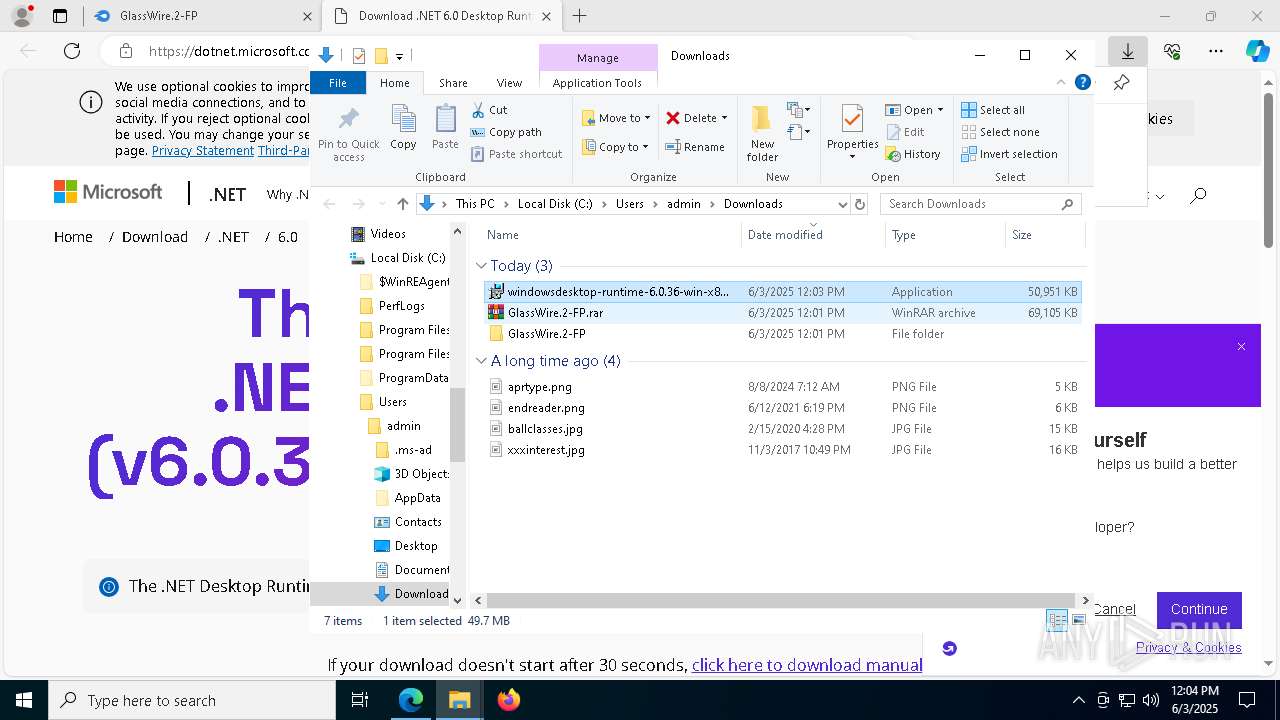
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 6180)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 9052)
- msiexec.exe (PID: 4932)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 2524)
Searches for installed software
- vc_redist.x86.exe (PID: 8500)
Executable content was dropped or overwritten
- vc_redist.x86.exe (PID: 8500)
- vc_redist.x86.exe (PID: 8648)
- GlassWireSetup.exe (PID: 5376)
- cmd.exe (PID: 7288)
- rundll32.exe (PID: 132)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 6180)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 9052)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 2524)
- Activator Glasswire Elite 2.3.449.exe (PID: 3744)
Reads security settings of Internet Explorer
- GWInstSt.exe (PID: 3760)
Reads the BIOS version
- GlassWireSetup.exe (PID: 5376)
Drops a system driver (possible attempt to evade defenses)
- GlassWireSetup.exe (PID: 5376)
- cmd.exe (PID: 7288)
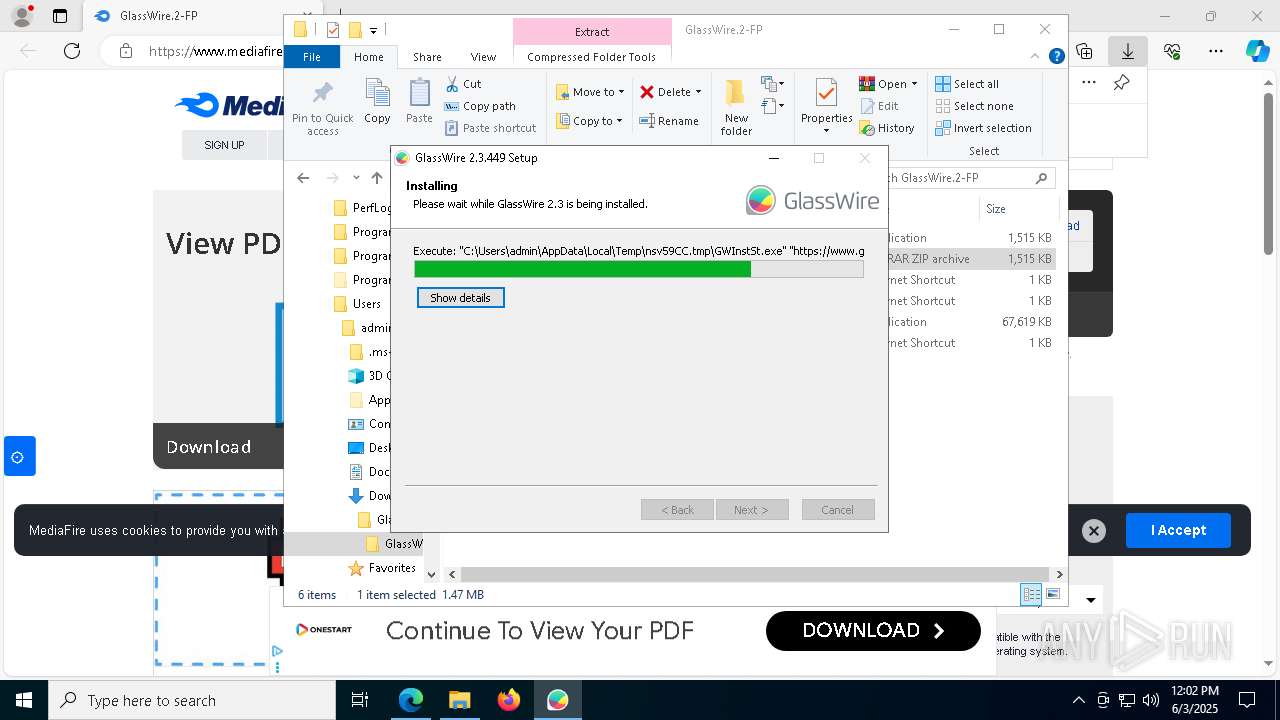
Executing commands from ".cmd" file
- GlassWireSetup.exe (PID: 5376)
Starts CMD.EXE for commands execution
- GlassWireSetup.exe (PID: 5376)
There is functionality for taking screenshot (YARA)
- GlassWireSetup.exe (PID: 5376)
- GWCtlSrv.exe (PID: 2140)
- GlassWire.exe (PID: 8708)
- GWCtlSrv.exe (PID: 7524)
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 8648)
- vc_redist.x86.exe (PID: 8500)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 9052)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 2524)
Creates files in the driver directory
- cmd.exe (PID: 7288)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 7288)
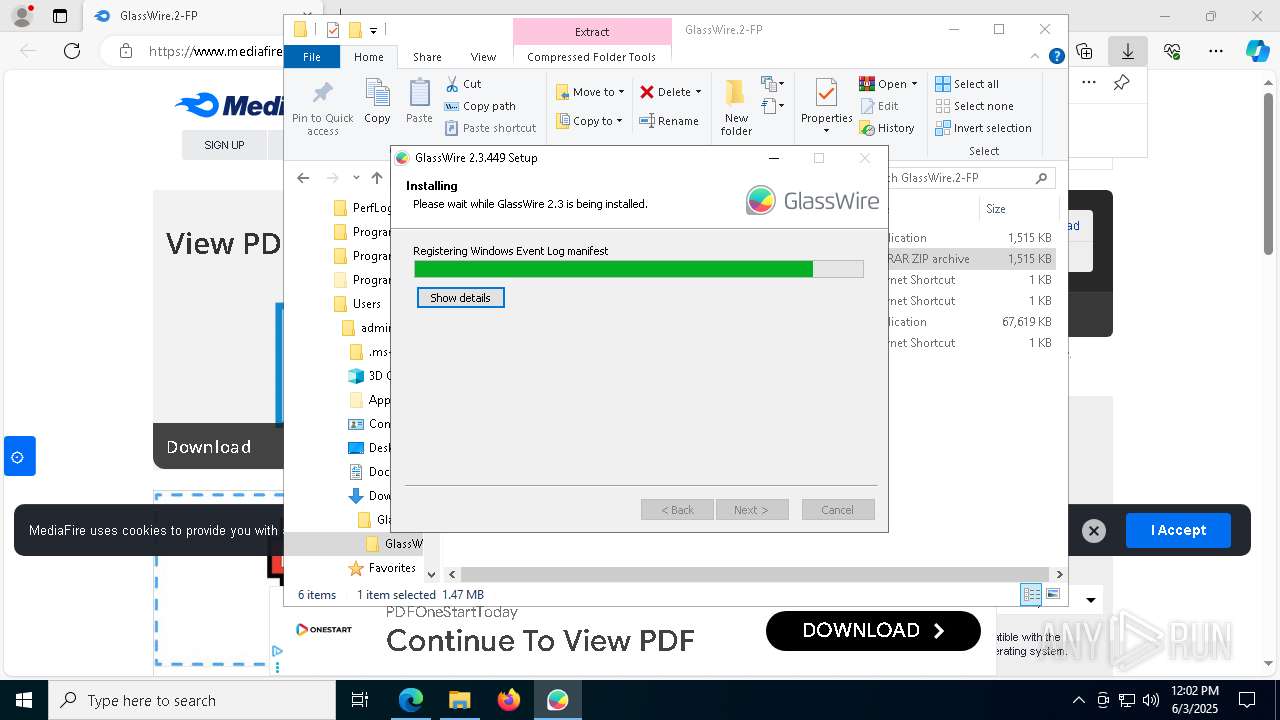
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- GlassWireSetup.exe (PID: 5376)
- wevtutil.exe (PID: 8816)
Executes as Windows Service
- GWCtlSrv.exe (PID: 2140)
- GWCtlSrv.exe (PID: 7524)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 8332)
Starts itself from another location
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 9052)
The process drops C-runtime libraries
- msiexec.exe (PID: 4932)
INFO
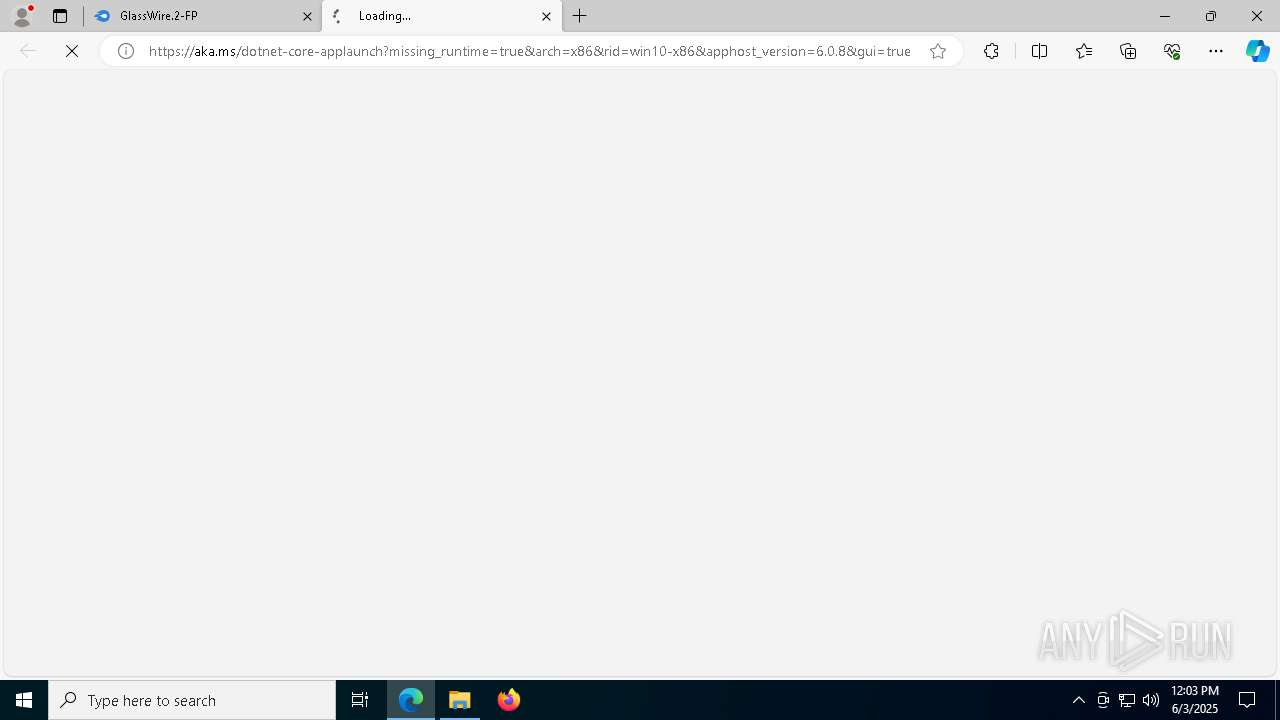
Application launched itself
- msedge.exe (PID: 5956)
Reads the computer name
- identity_helper.exe (PID: 8444)
- GlassWireSetup.exe (PID: 5376)
- vc_redist.x86.exe (PID: 8500)
- GWInstSt.exe (PID: 3760)
Reads Environment values
- identity_helper.exe (PID: 8444)
Checks supported languages
- identity_helper.exe (PID: 8444)
- GlassWireSetup.exe (PID: 5376)
- GWInstSt.exe (PID: 3760)
- vc_redist.x86.exe (PID: 8648)
- vc_redist.x86.exe (PID: 8500)
Reads Microsoft Office registry keys
- explorer.exe (PID: 5492)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
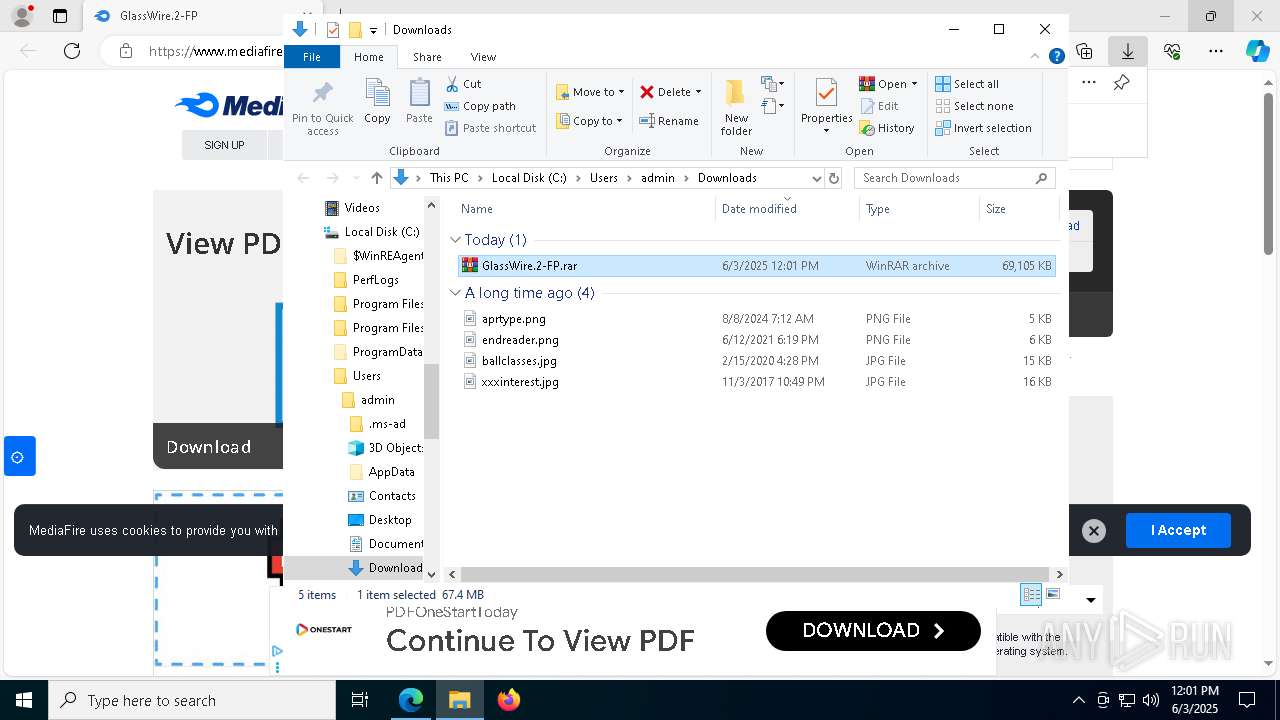
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7000)
- msedge.exe (PID: 8804)
- msedge.exe (PID: 5956)
- msiexec.exe (PID: 4932)
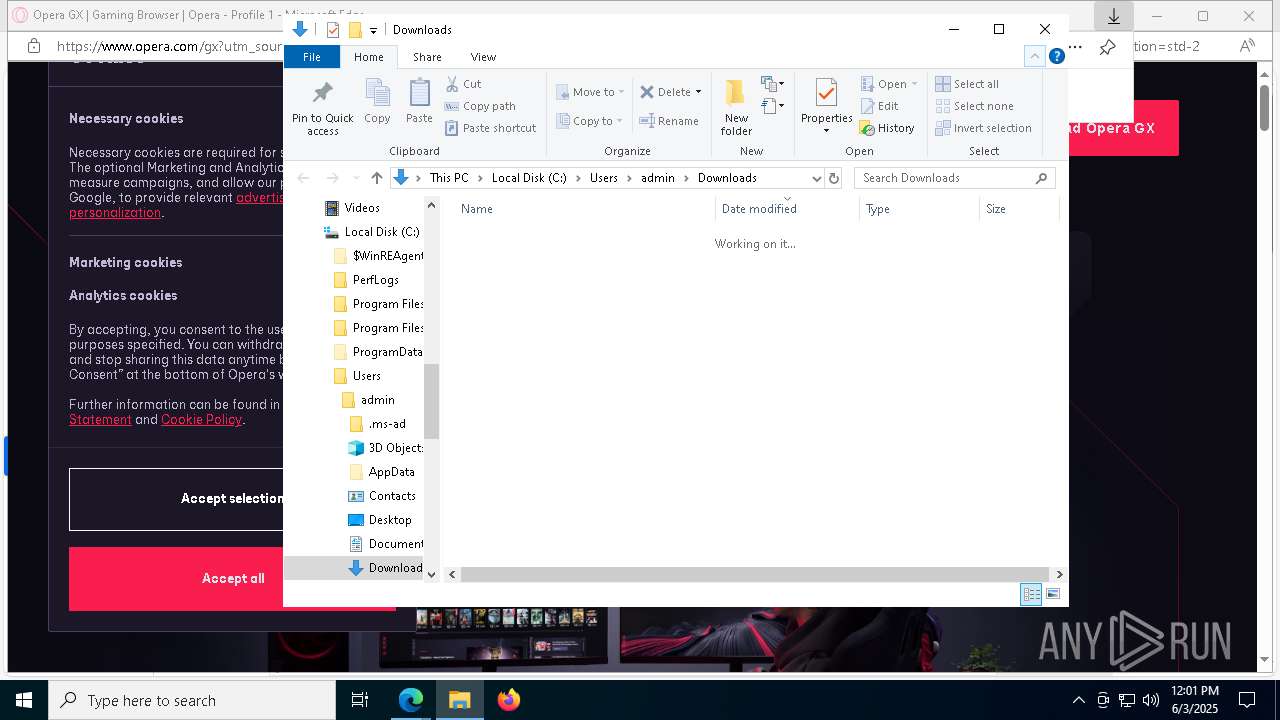
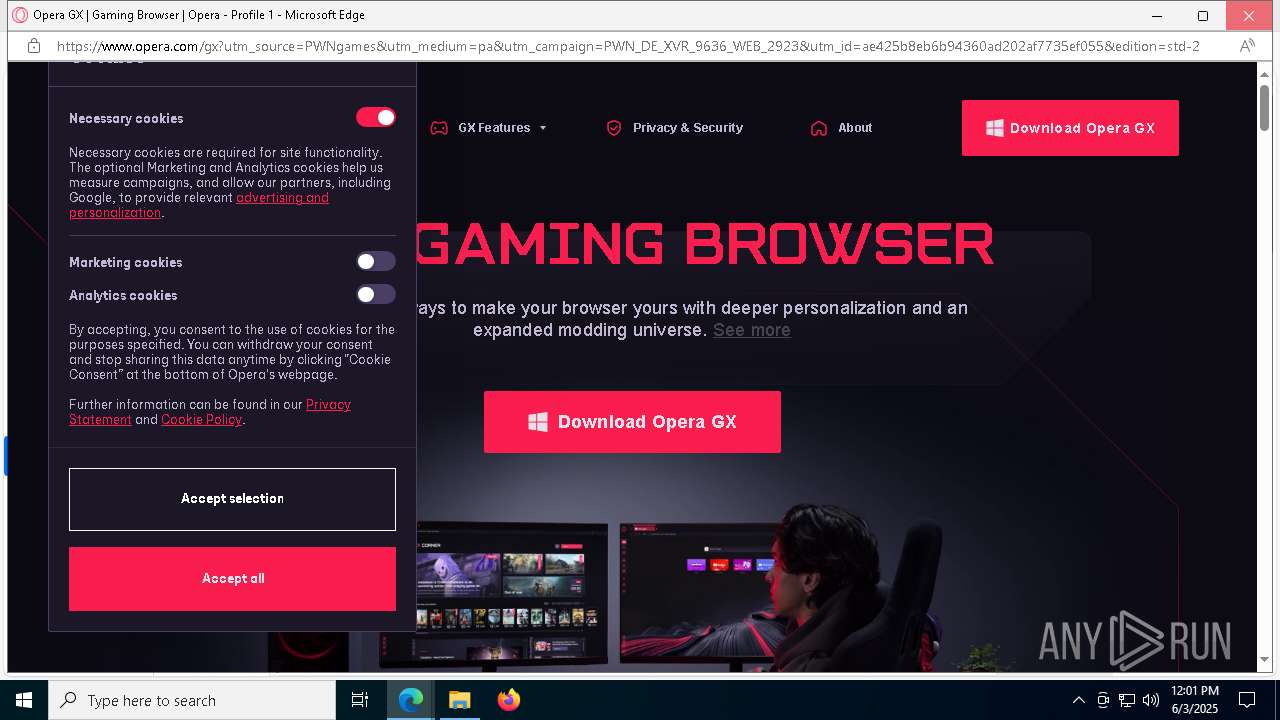
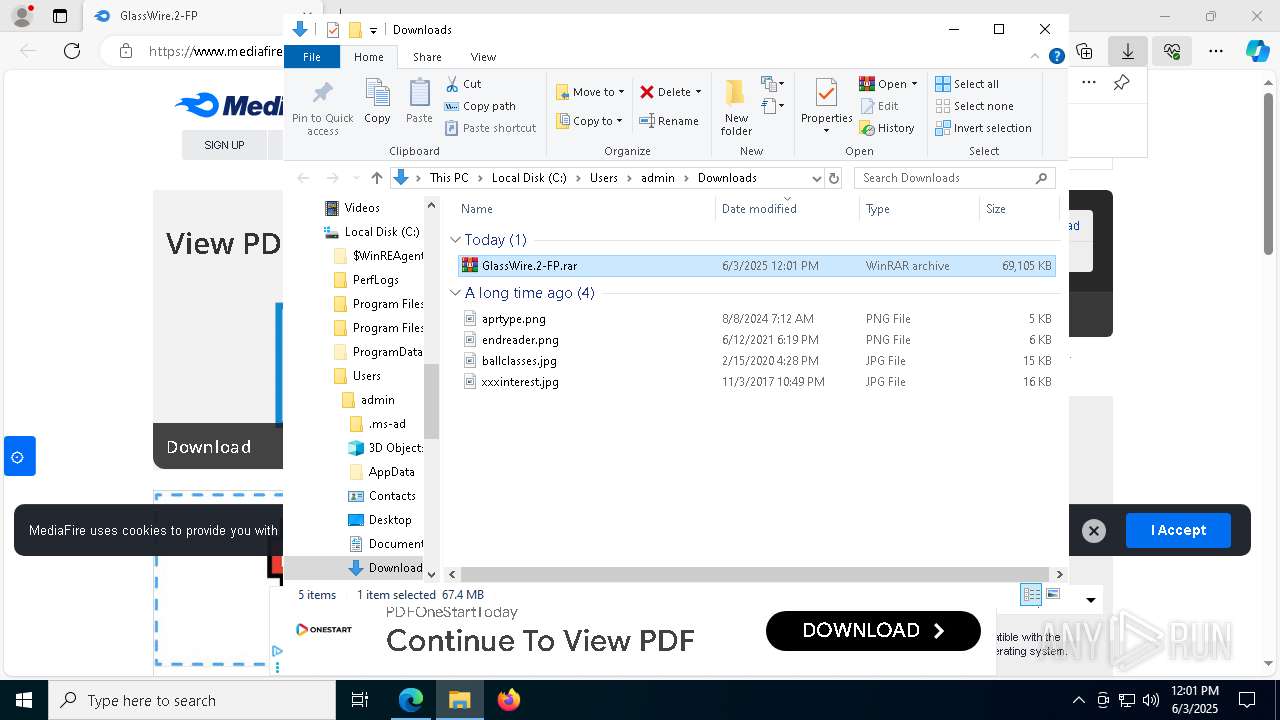
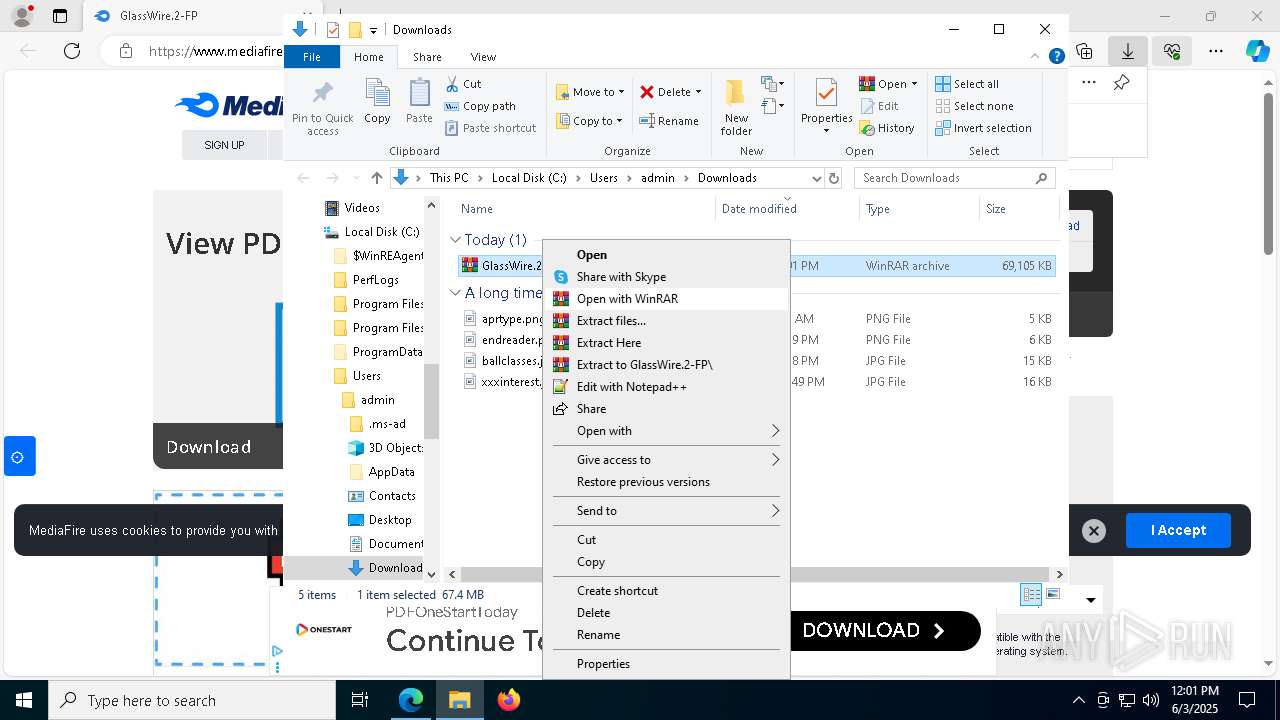
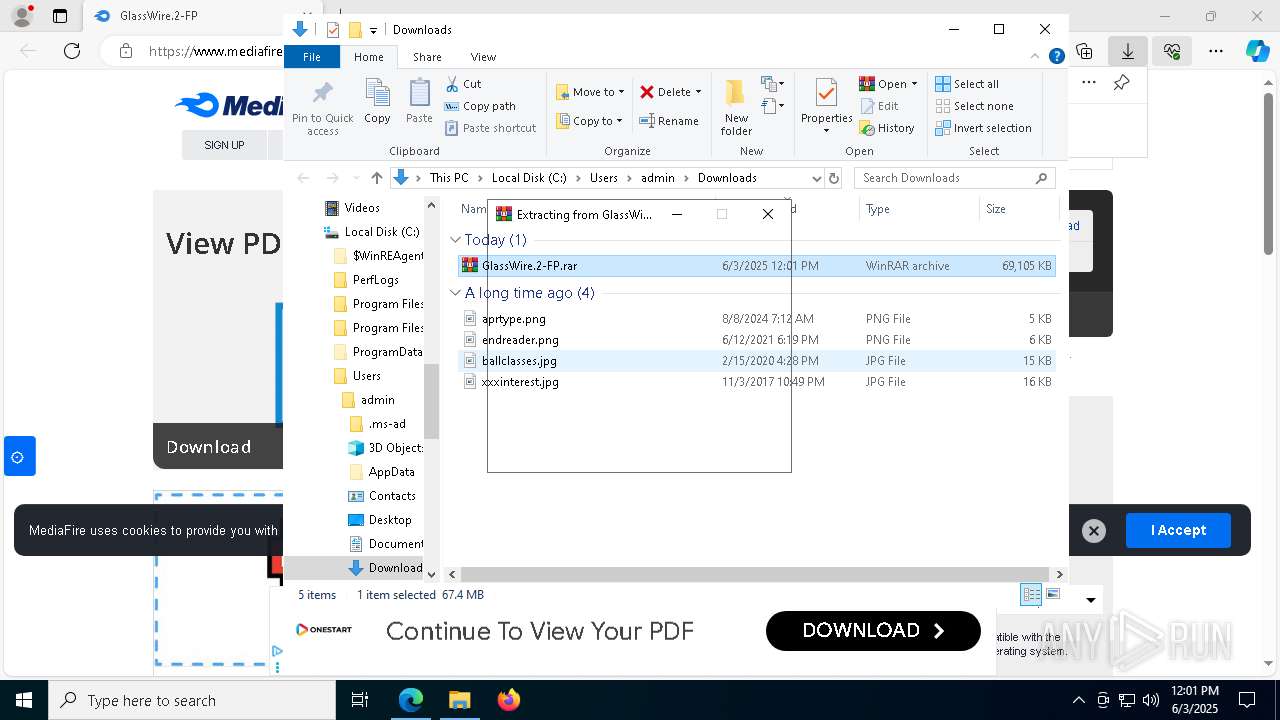
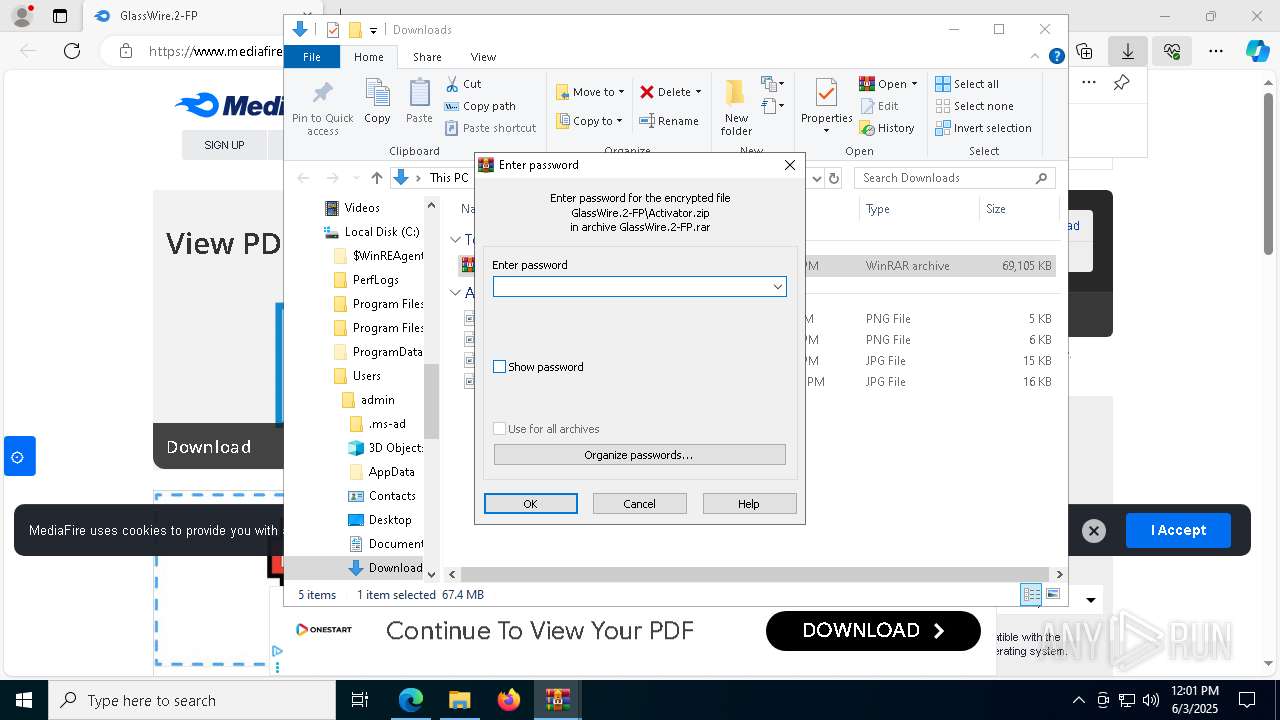
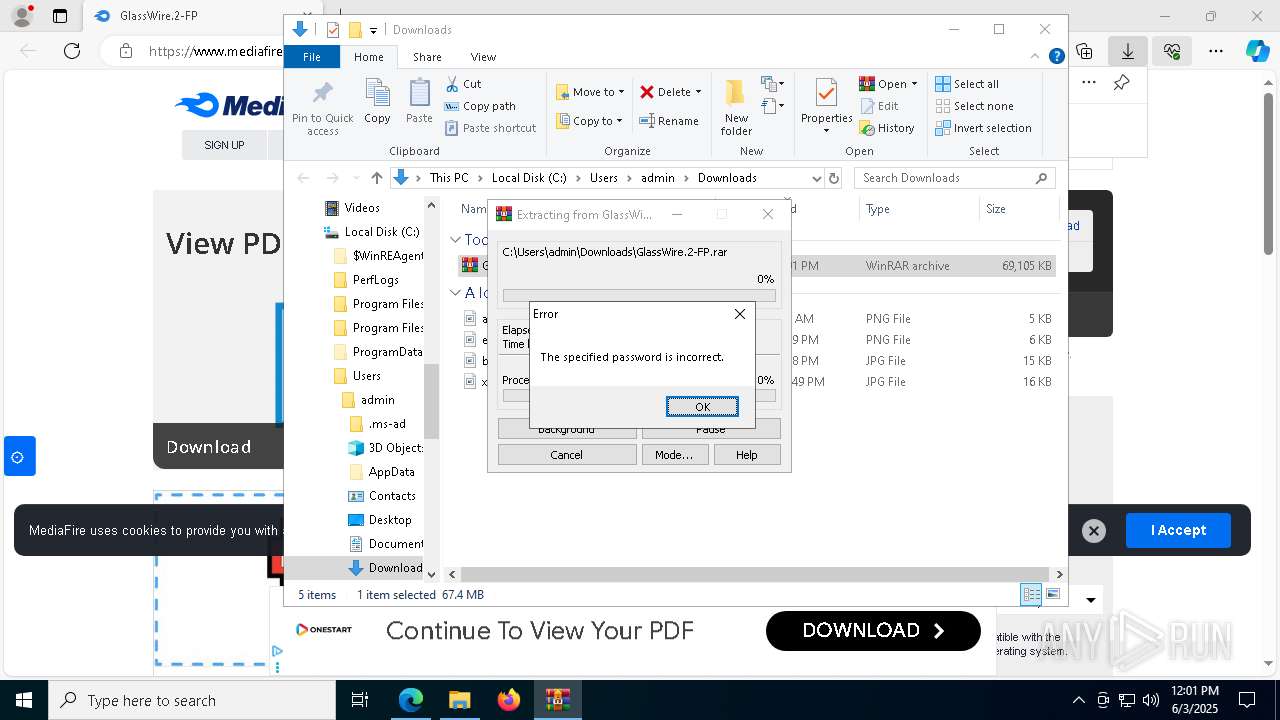
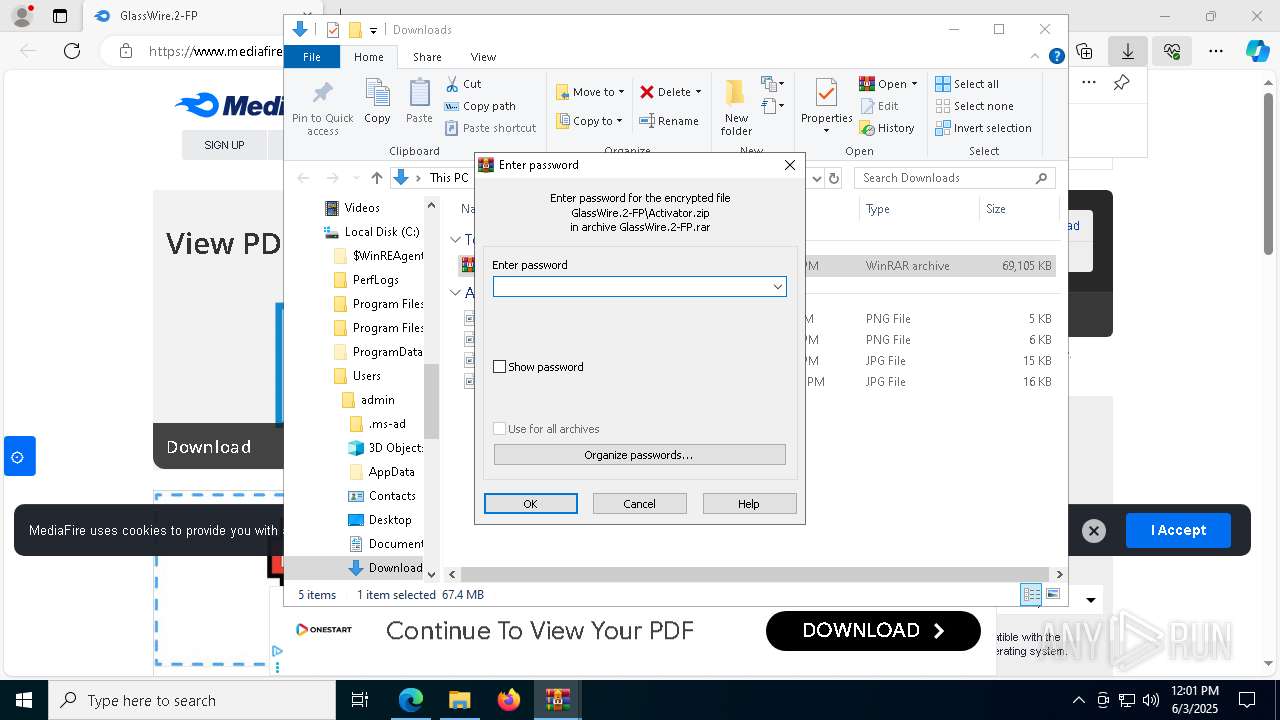
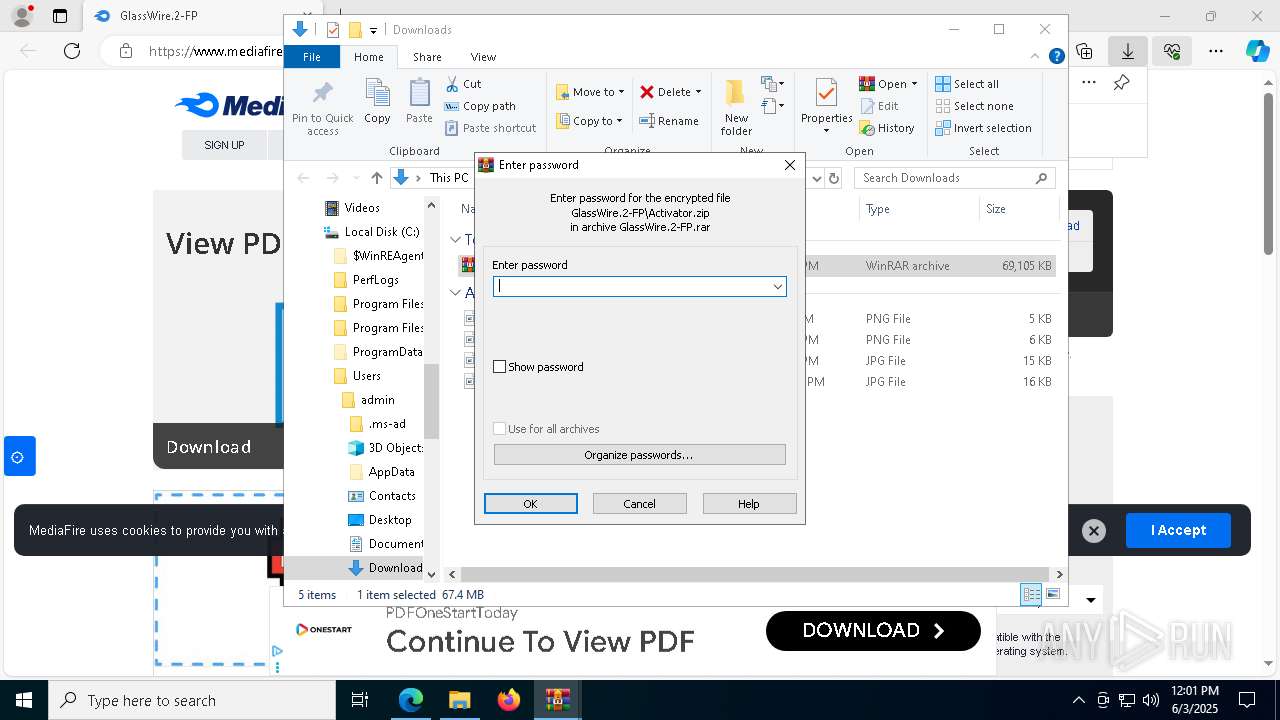
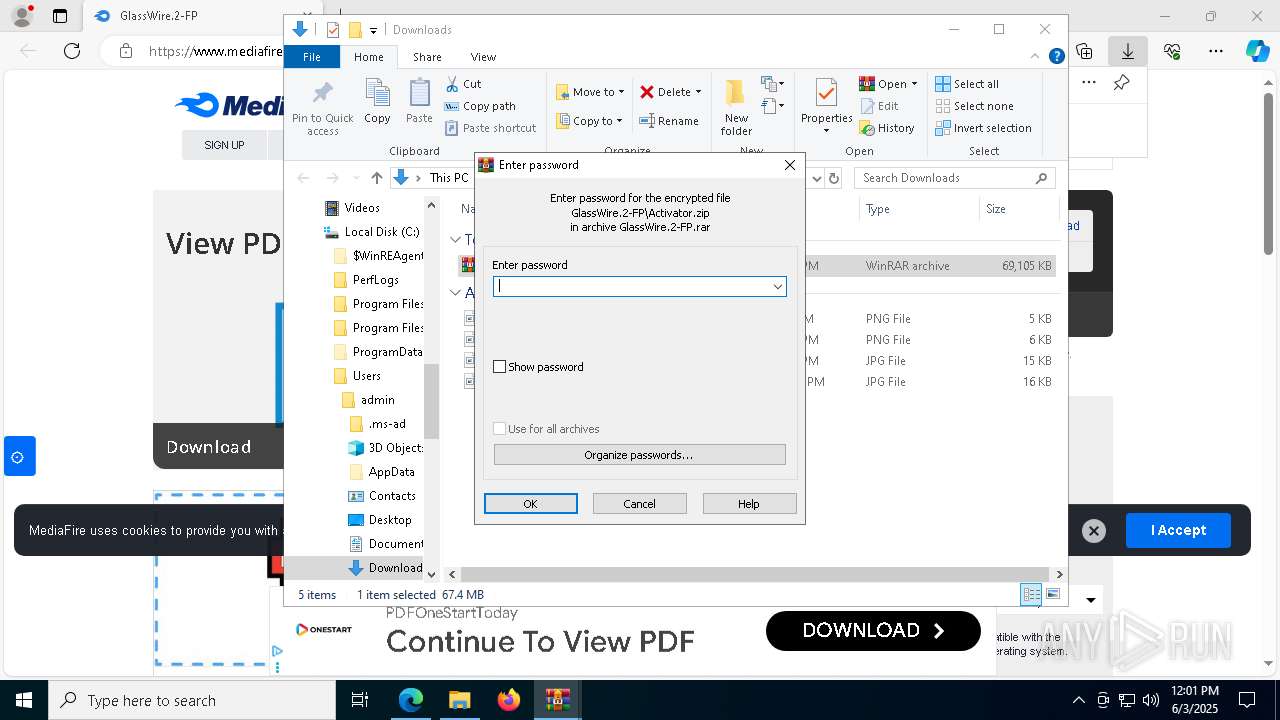
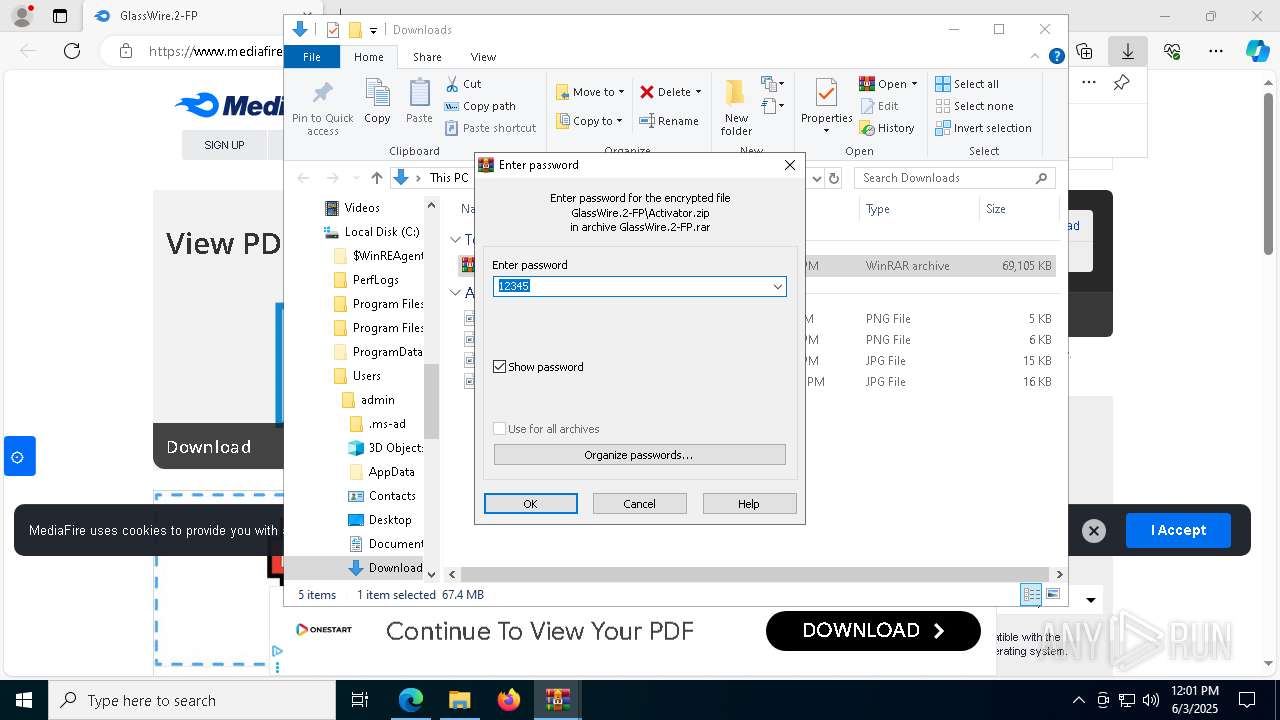
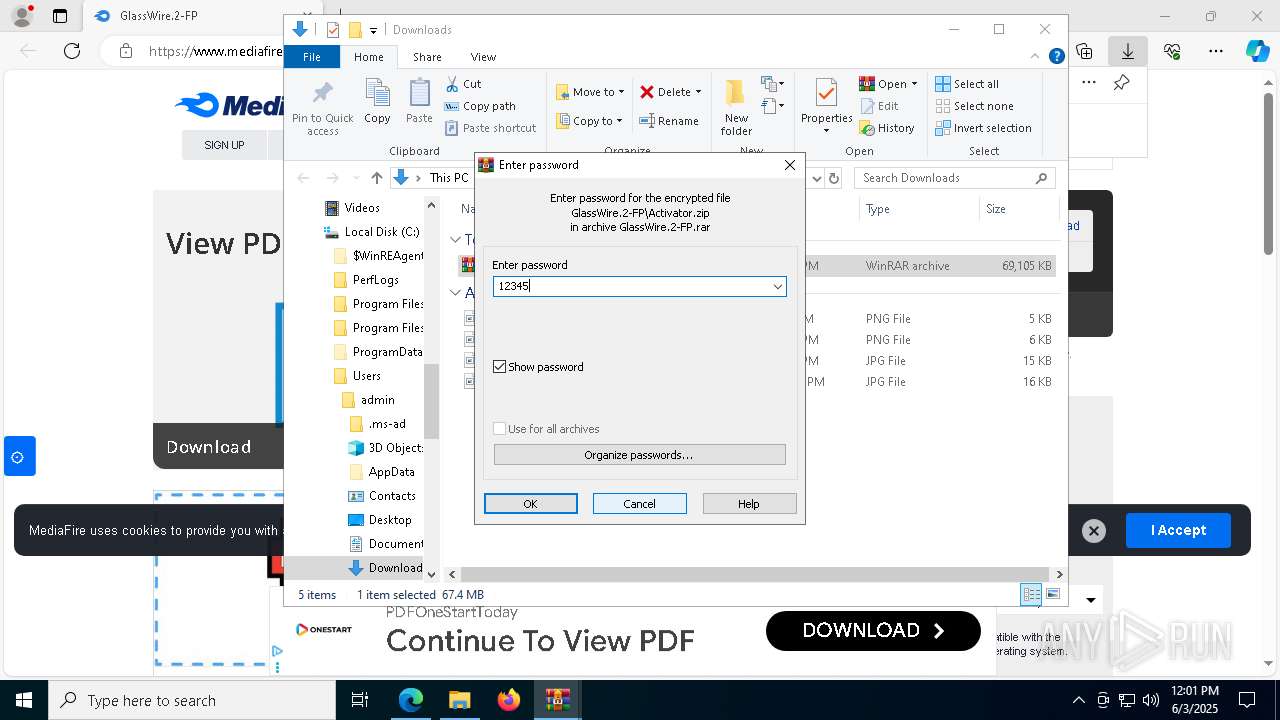
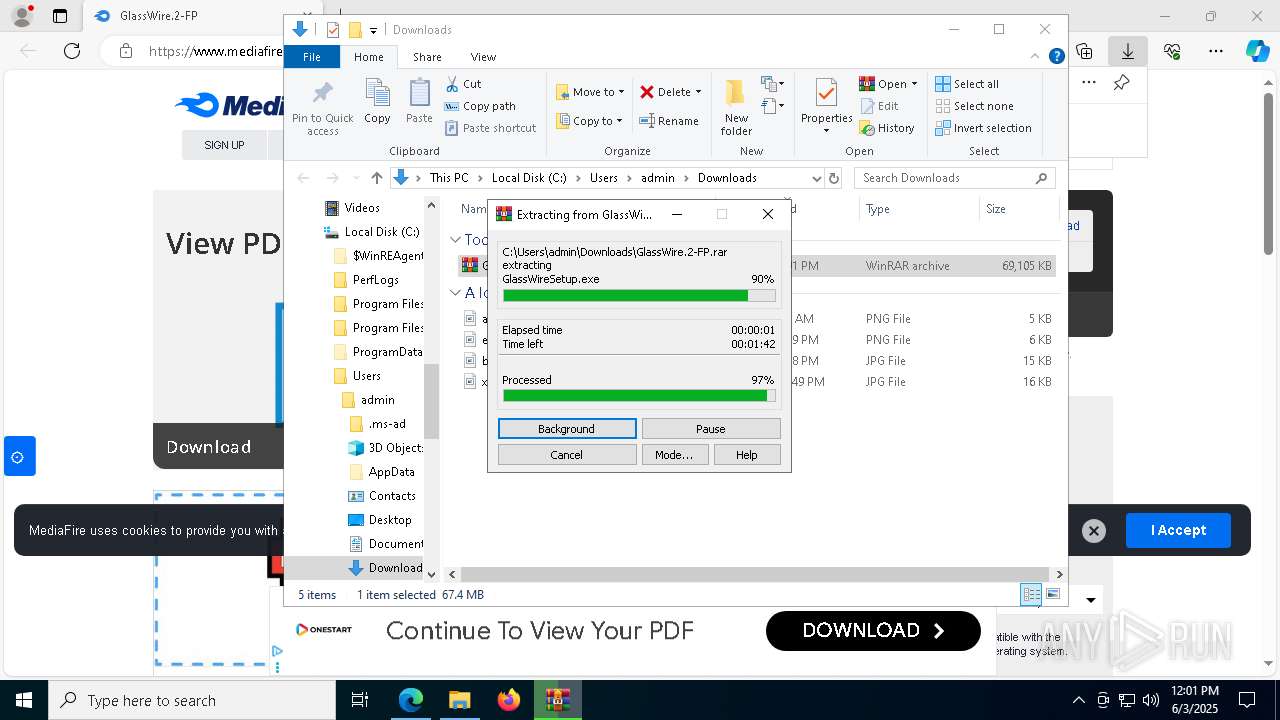
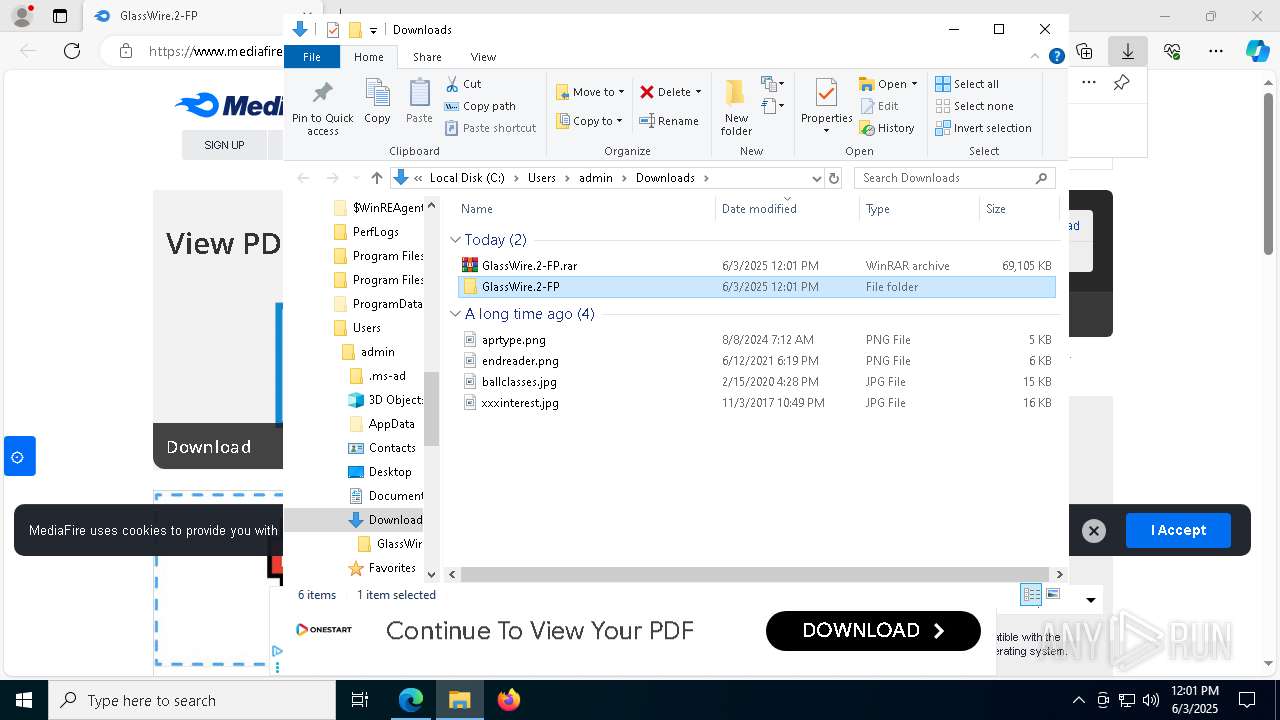
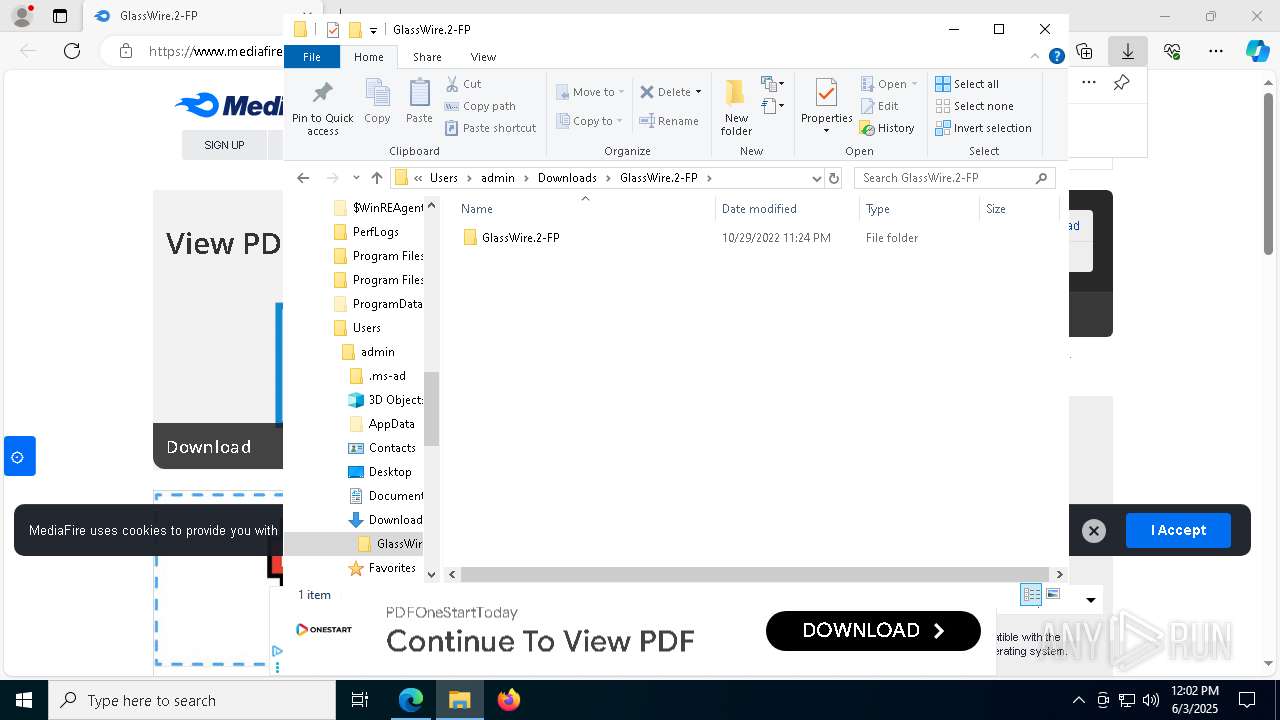
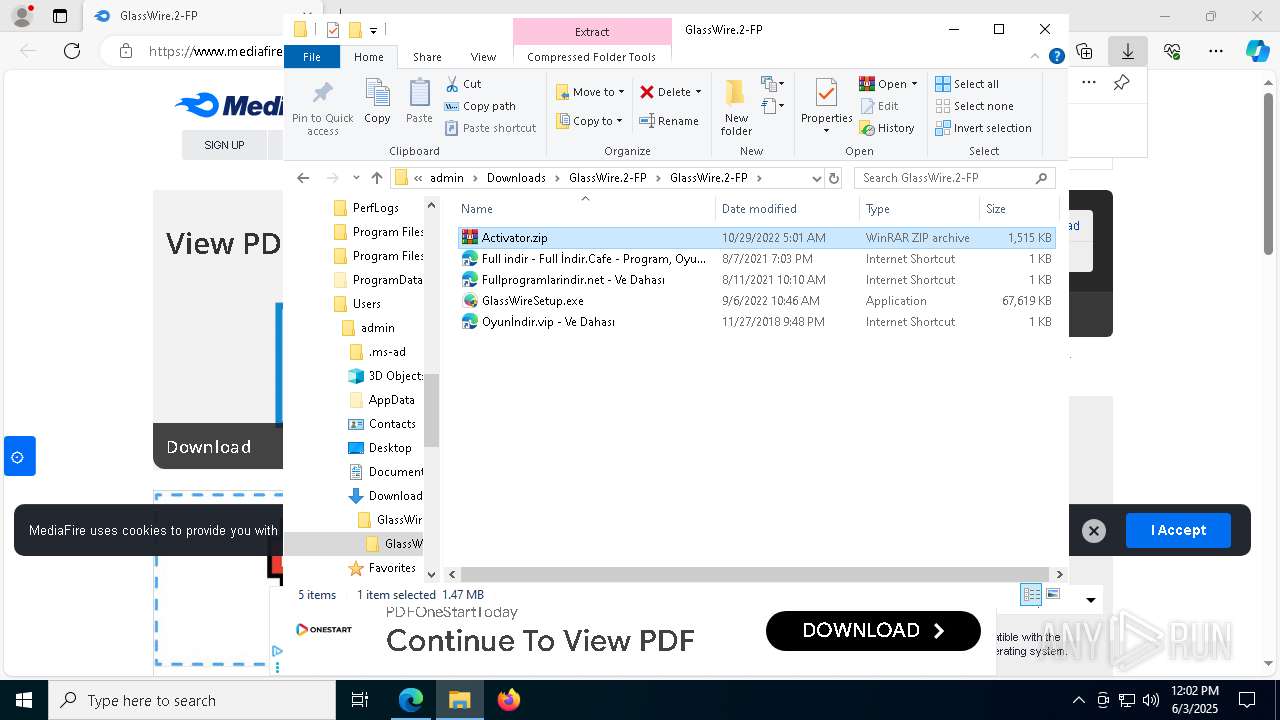
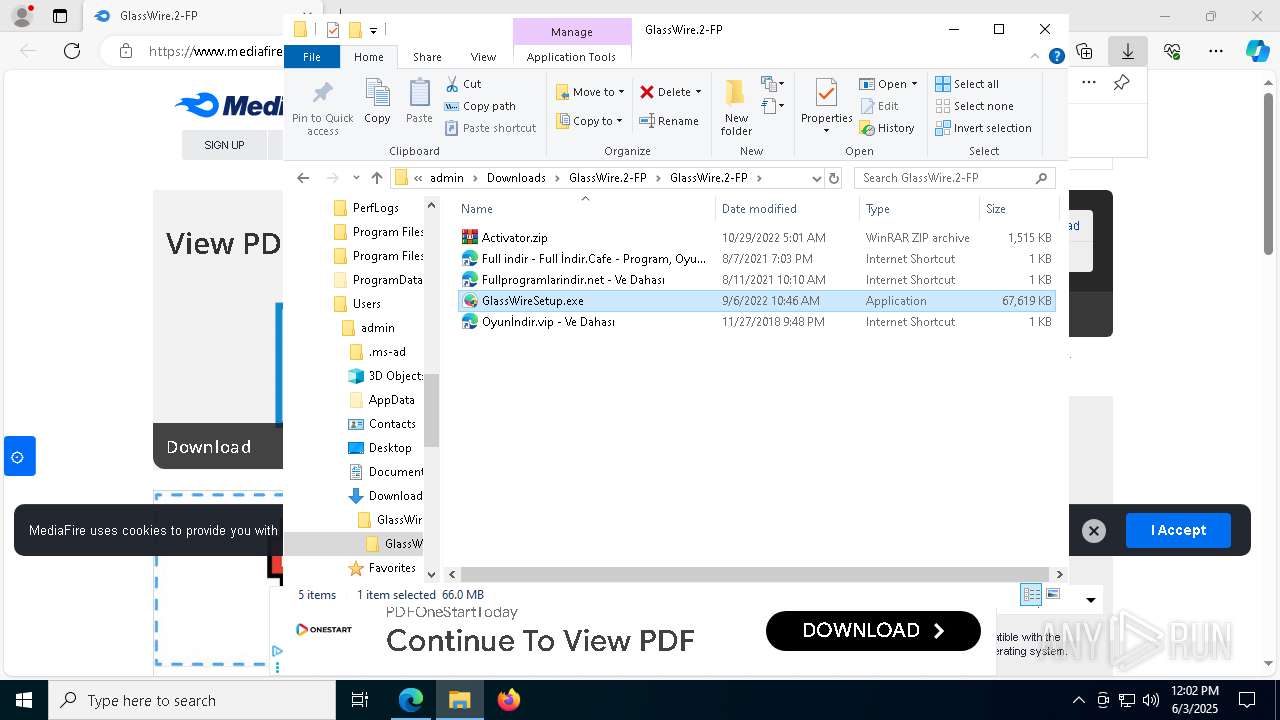
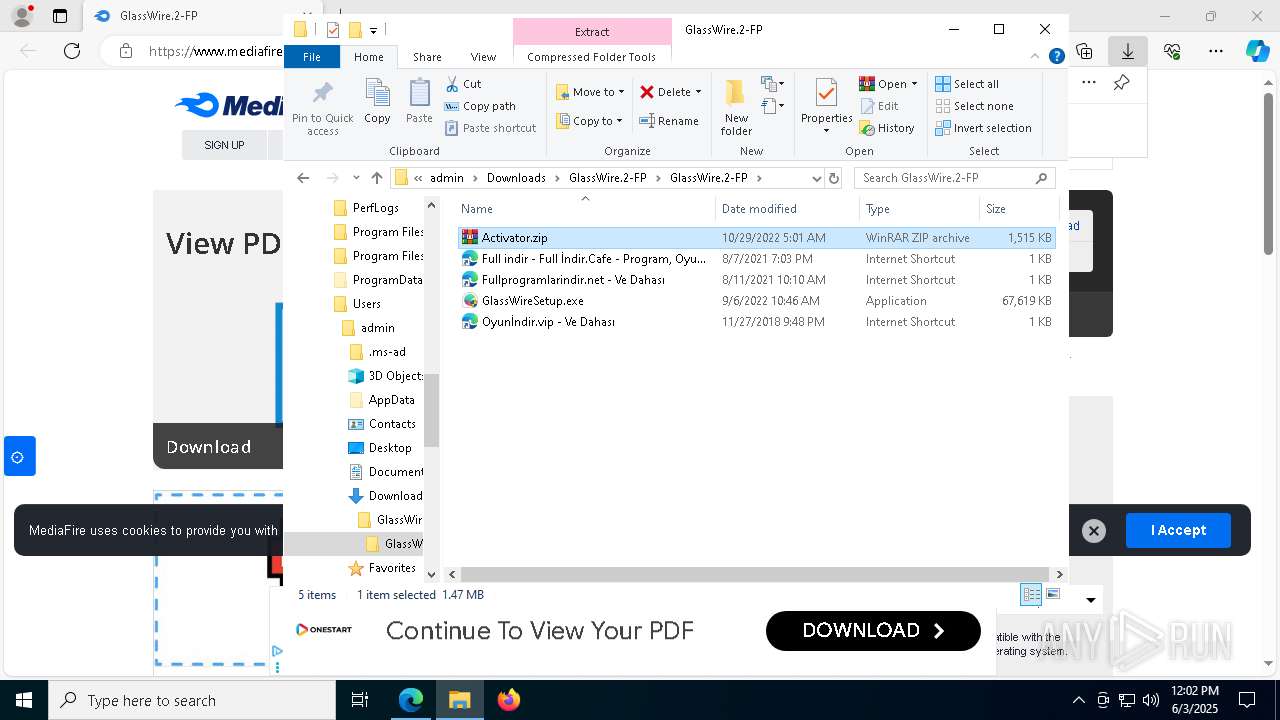
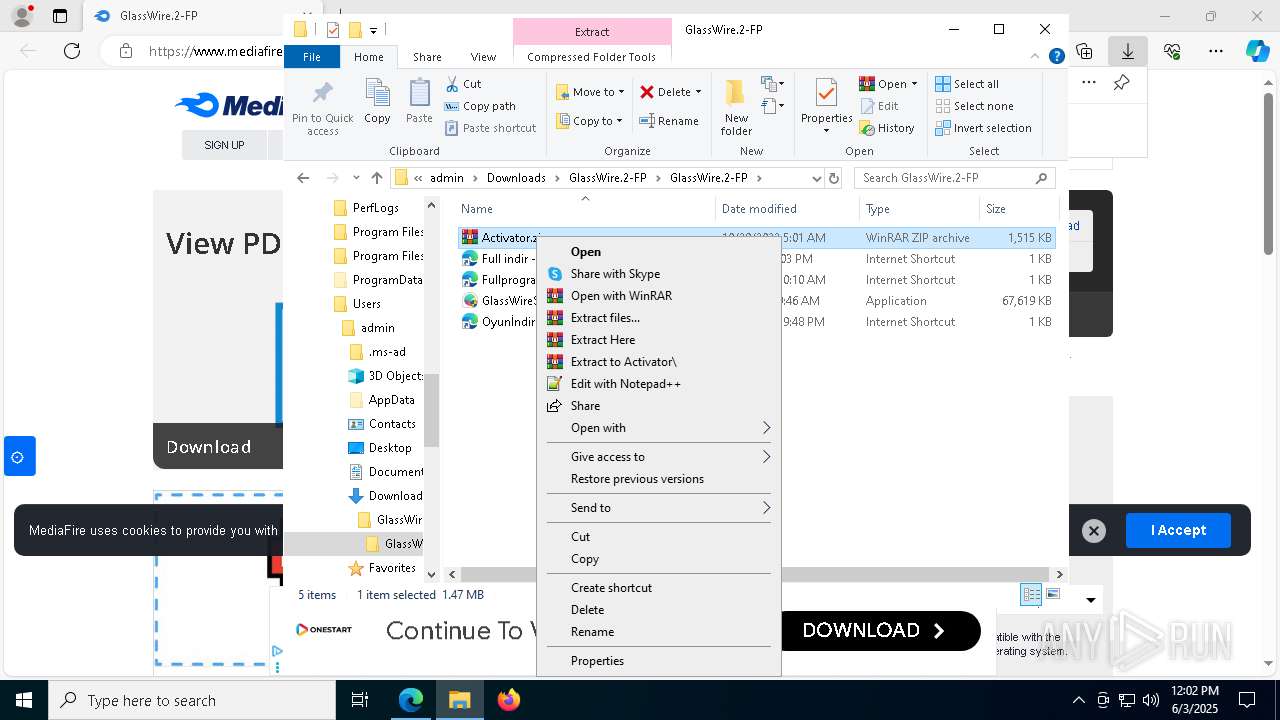
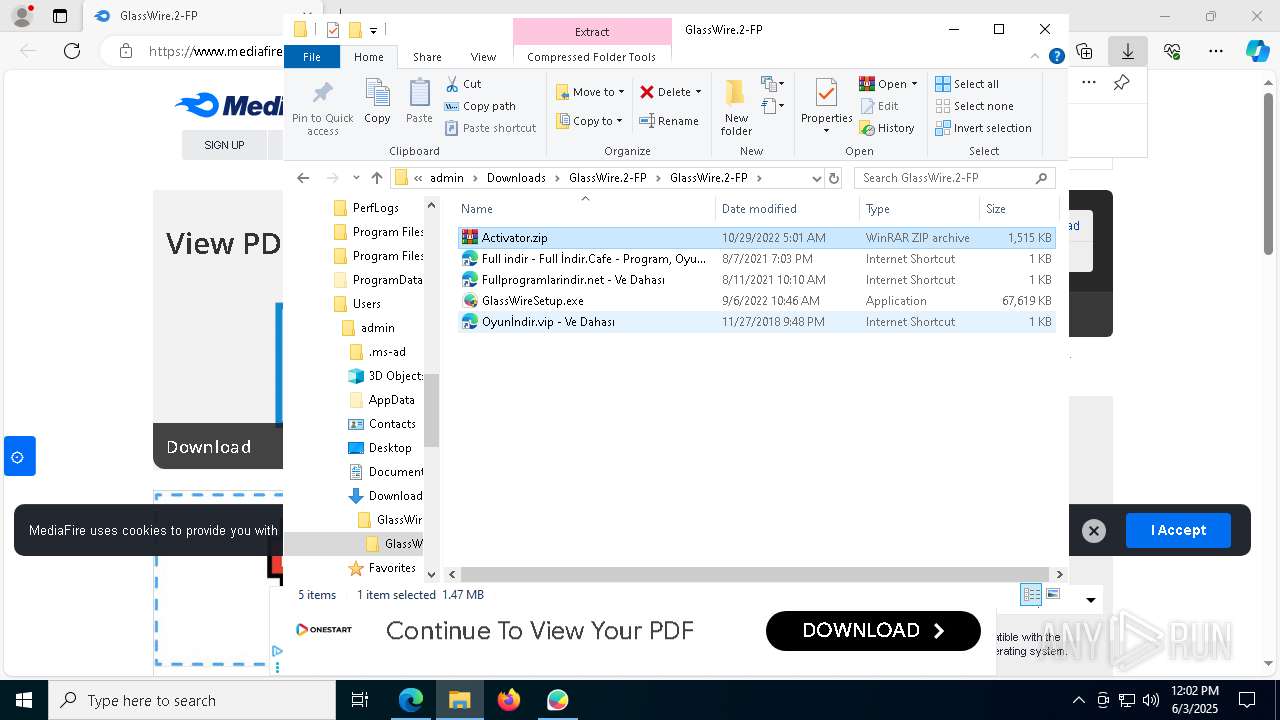
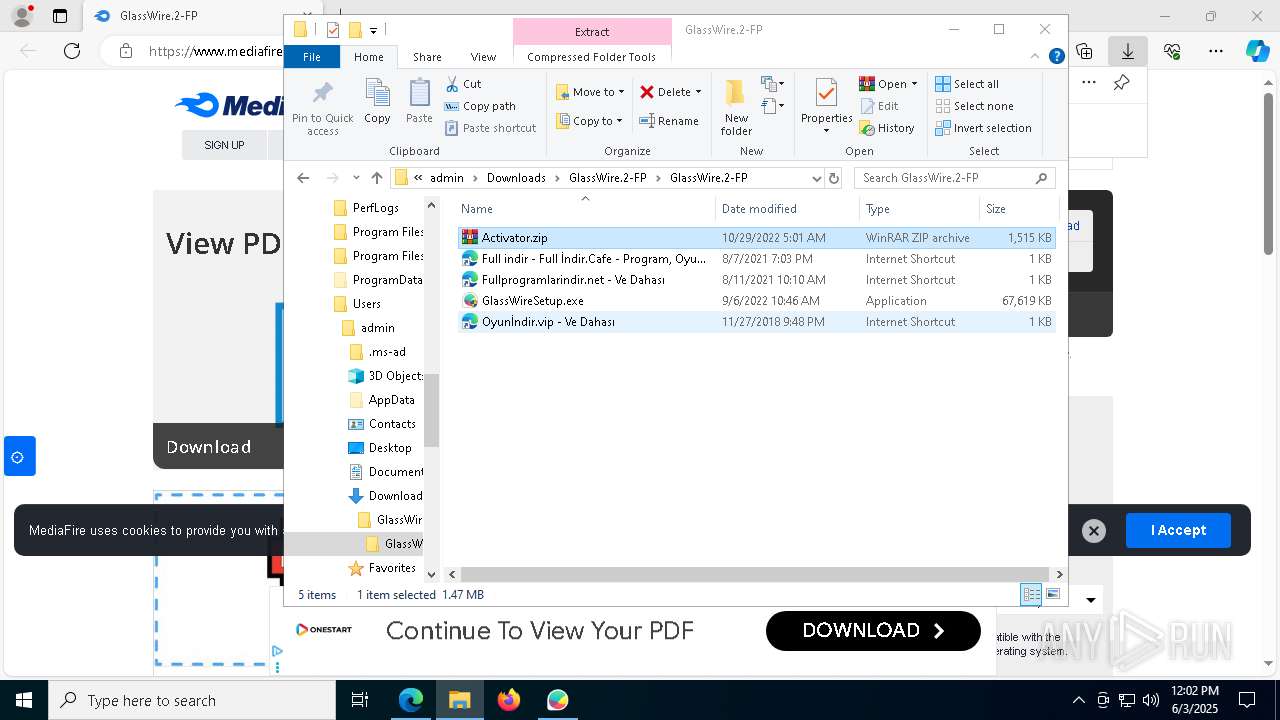
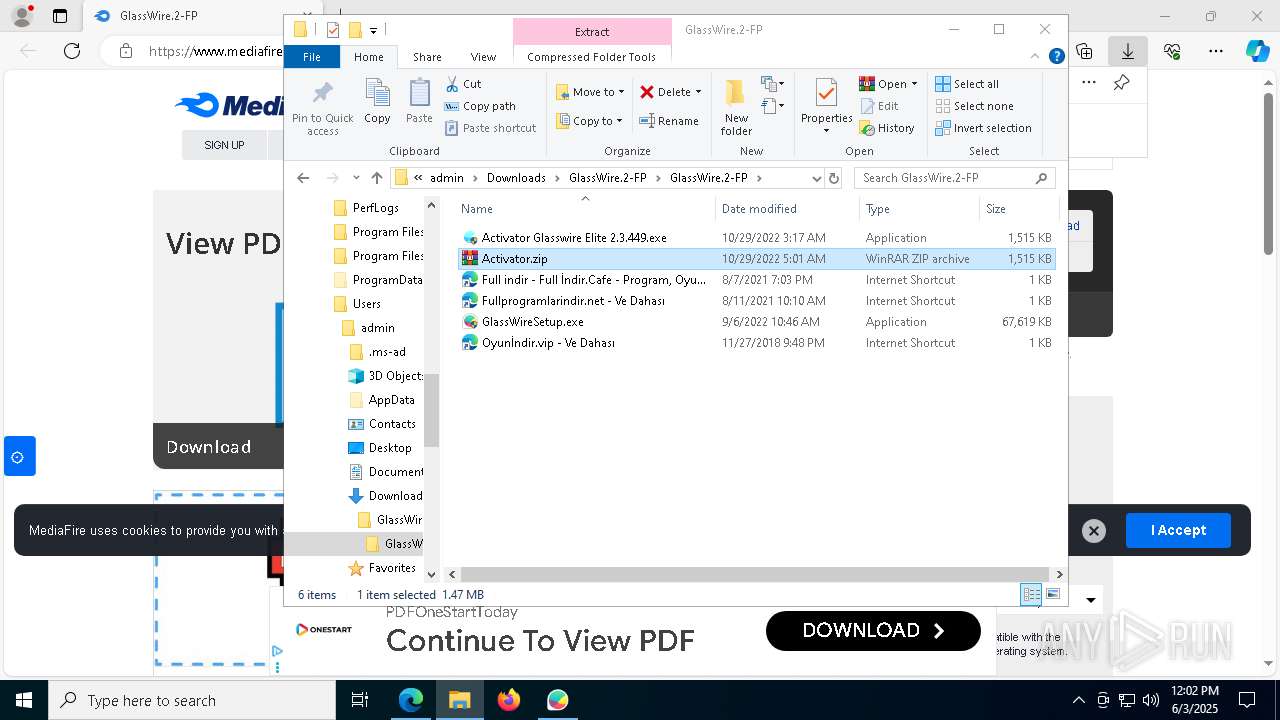
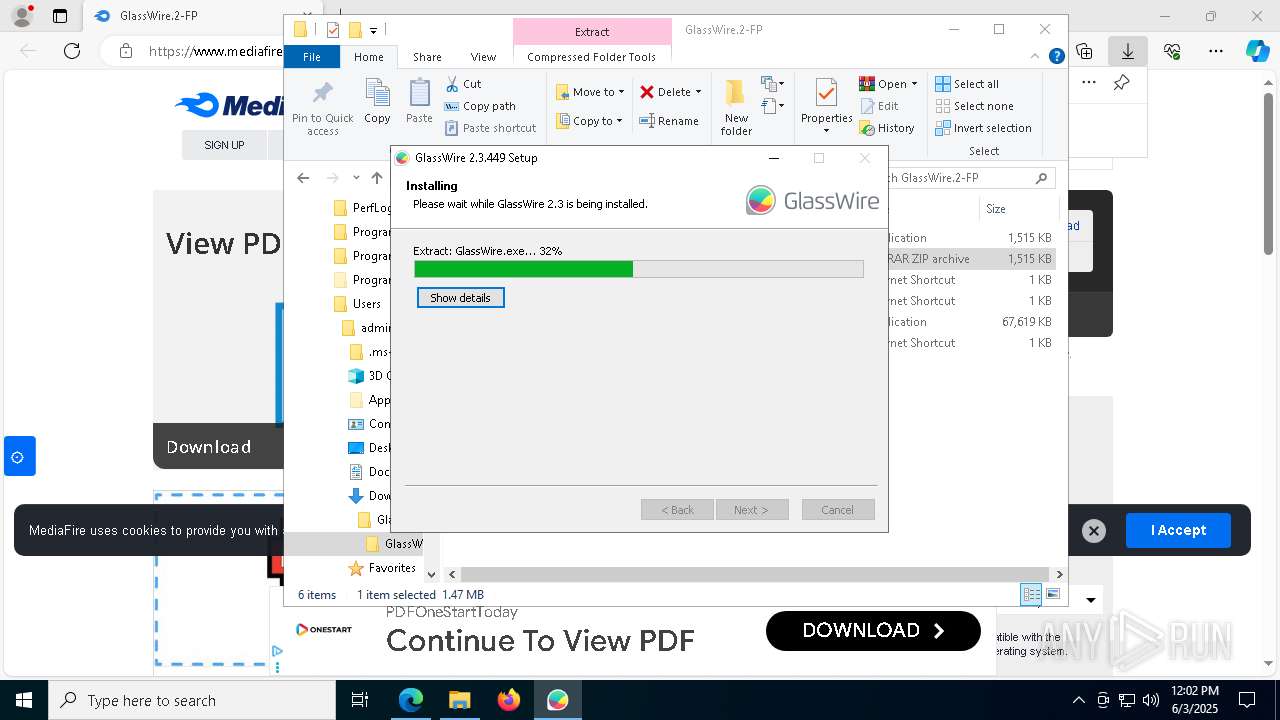
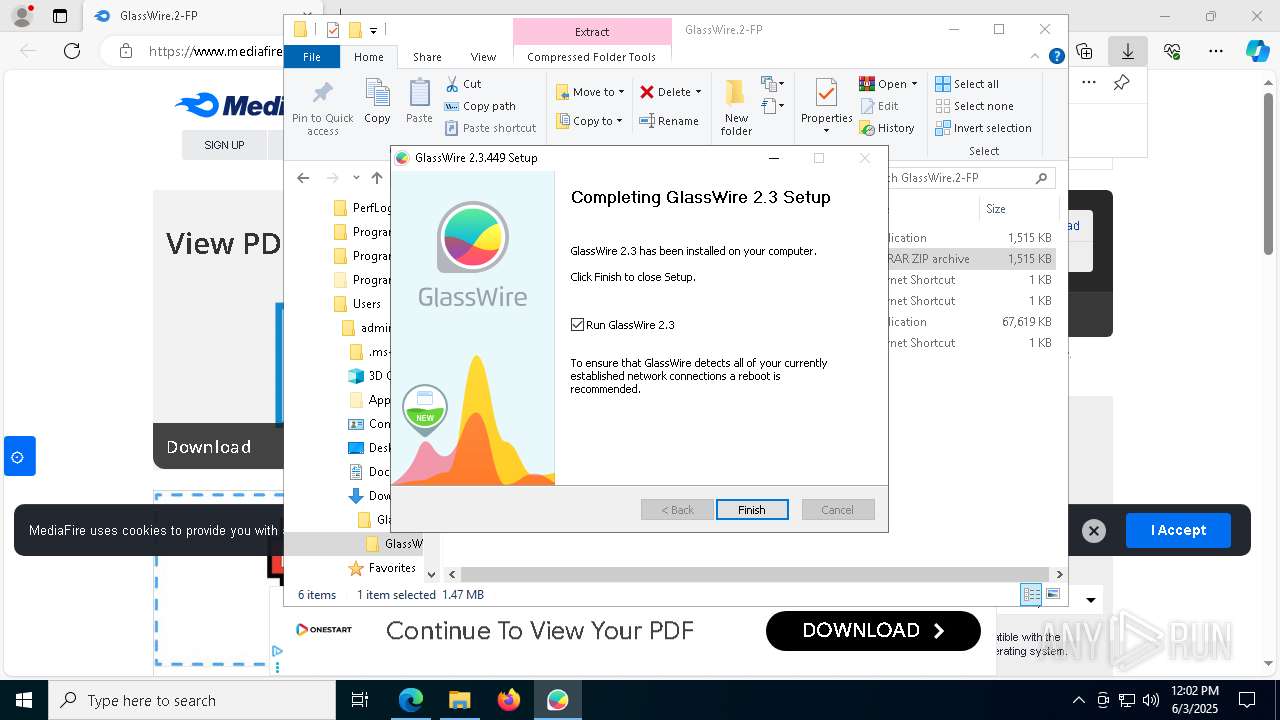
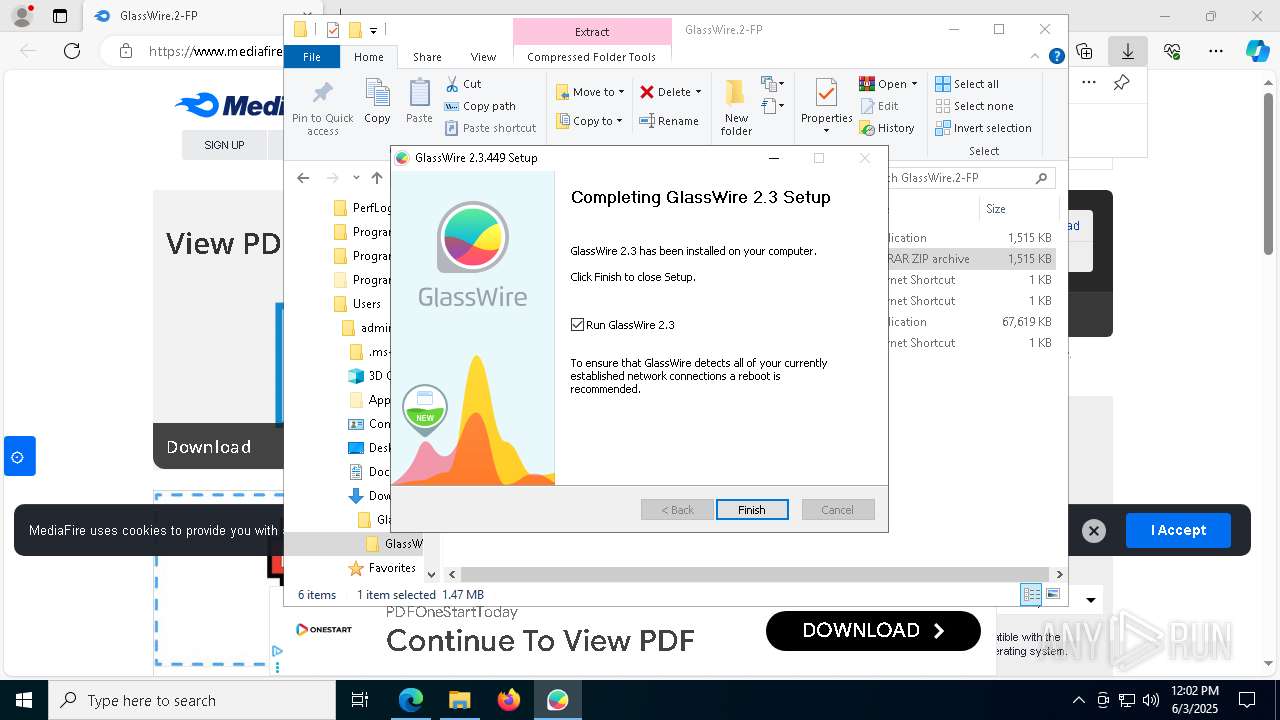
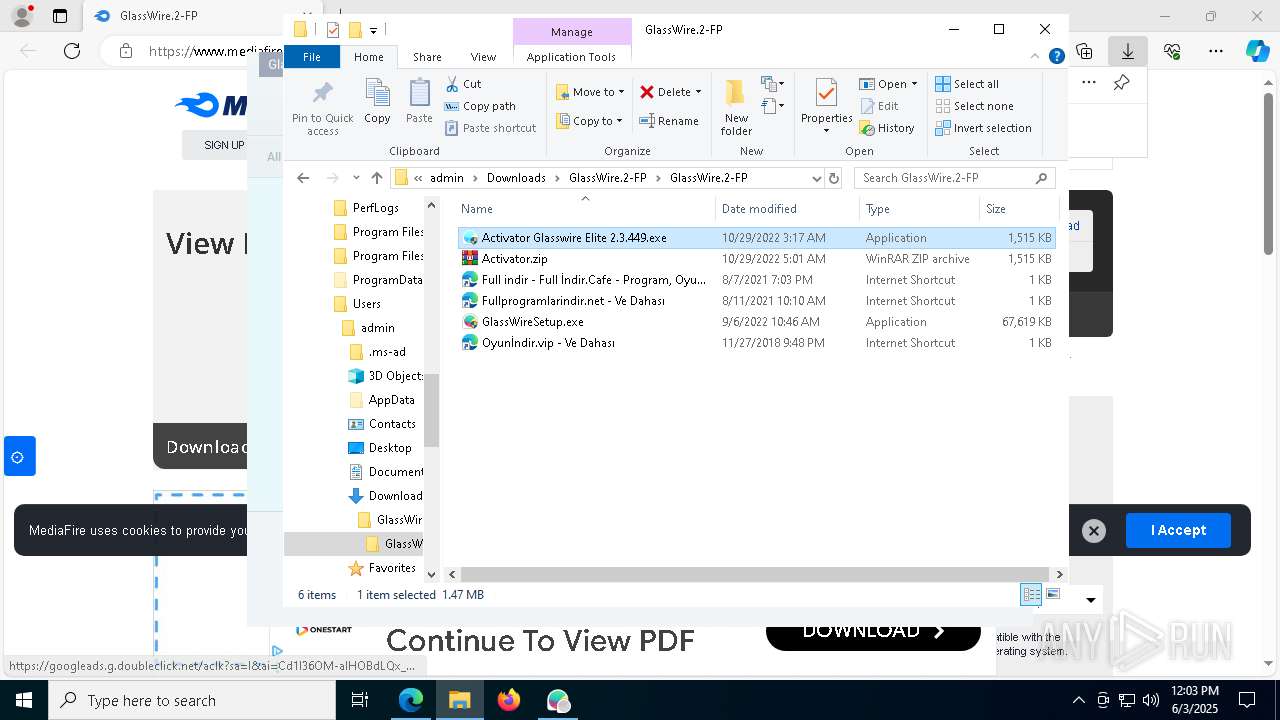
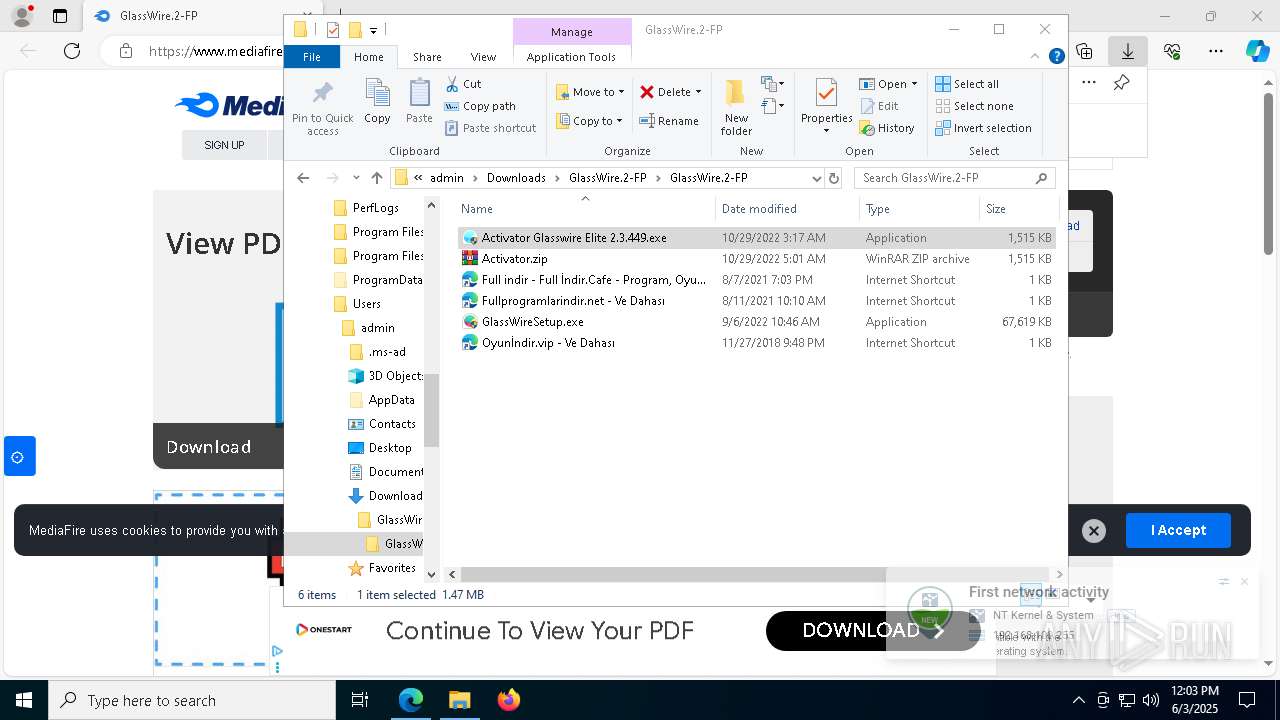
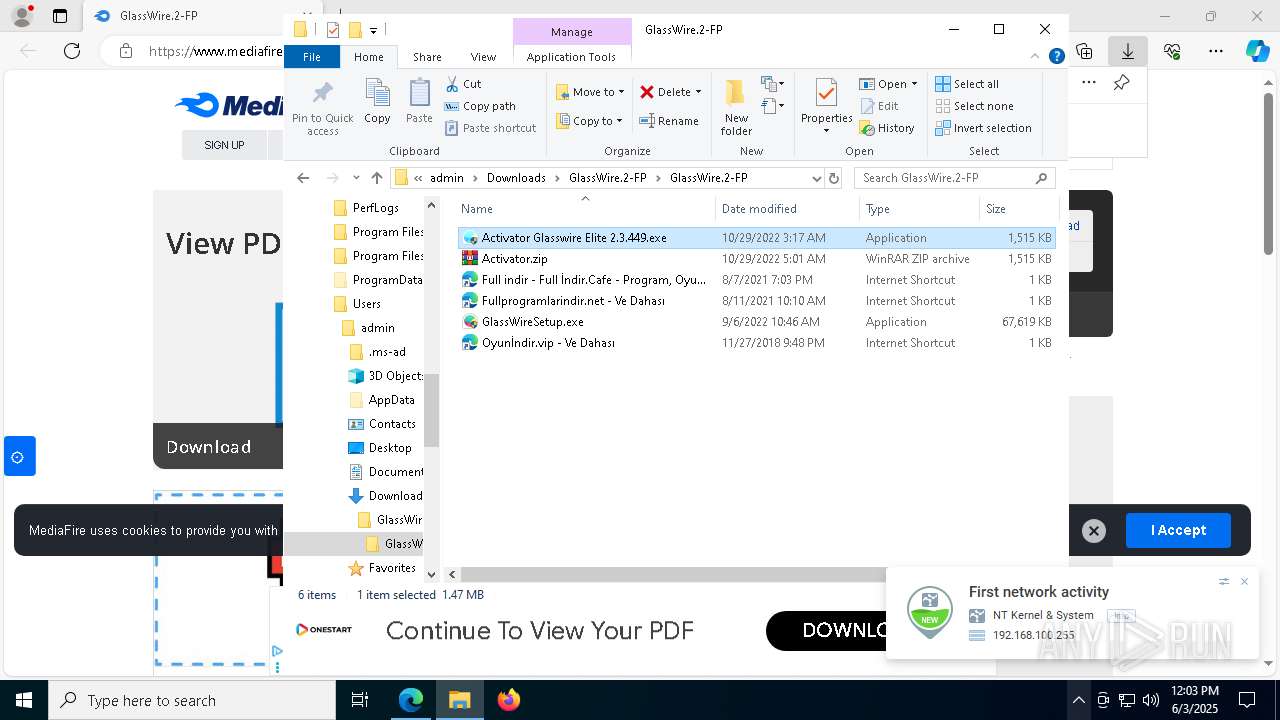
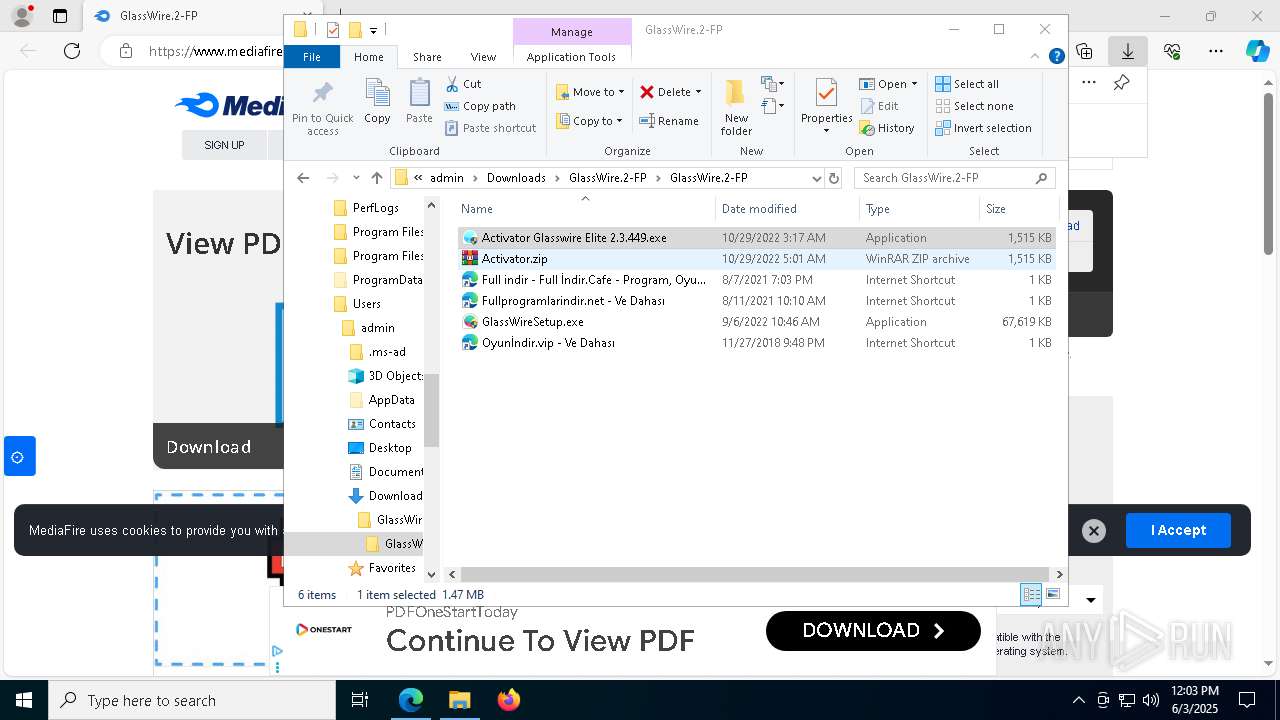
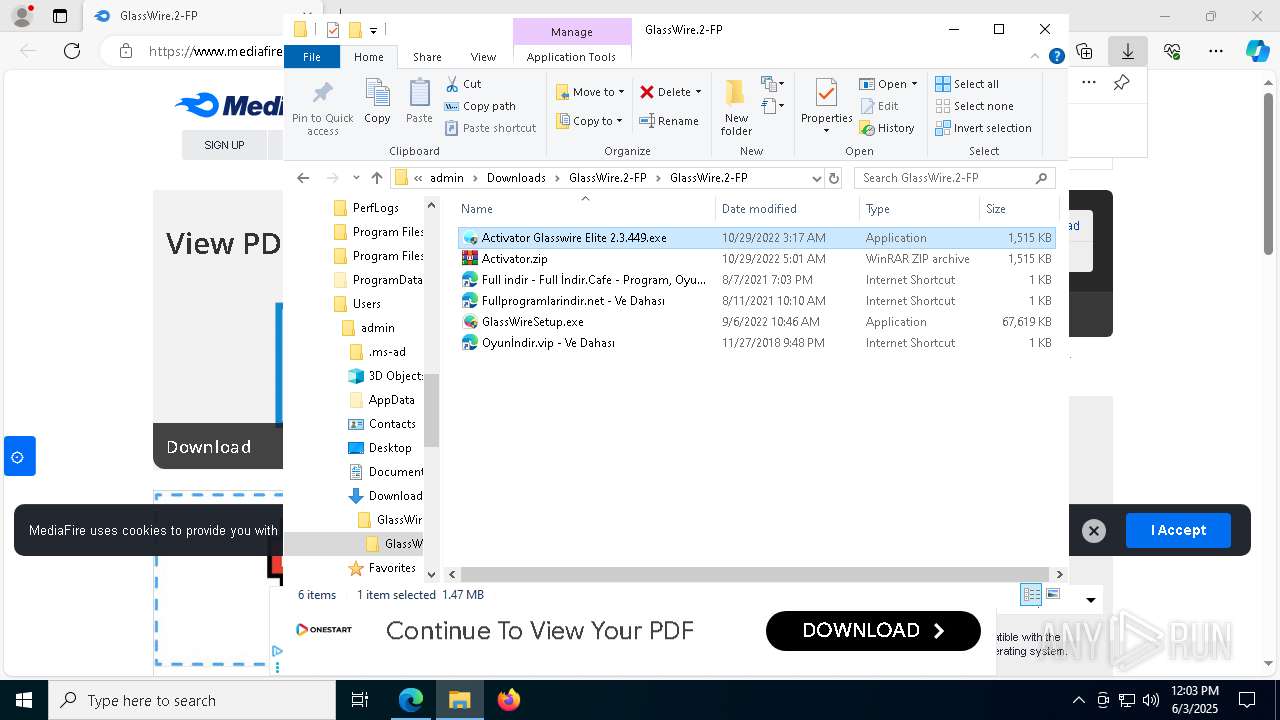
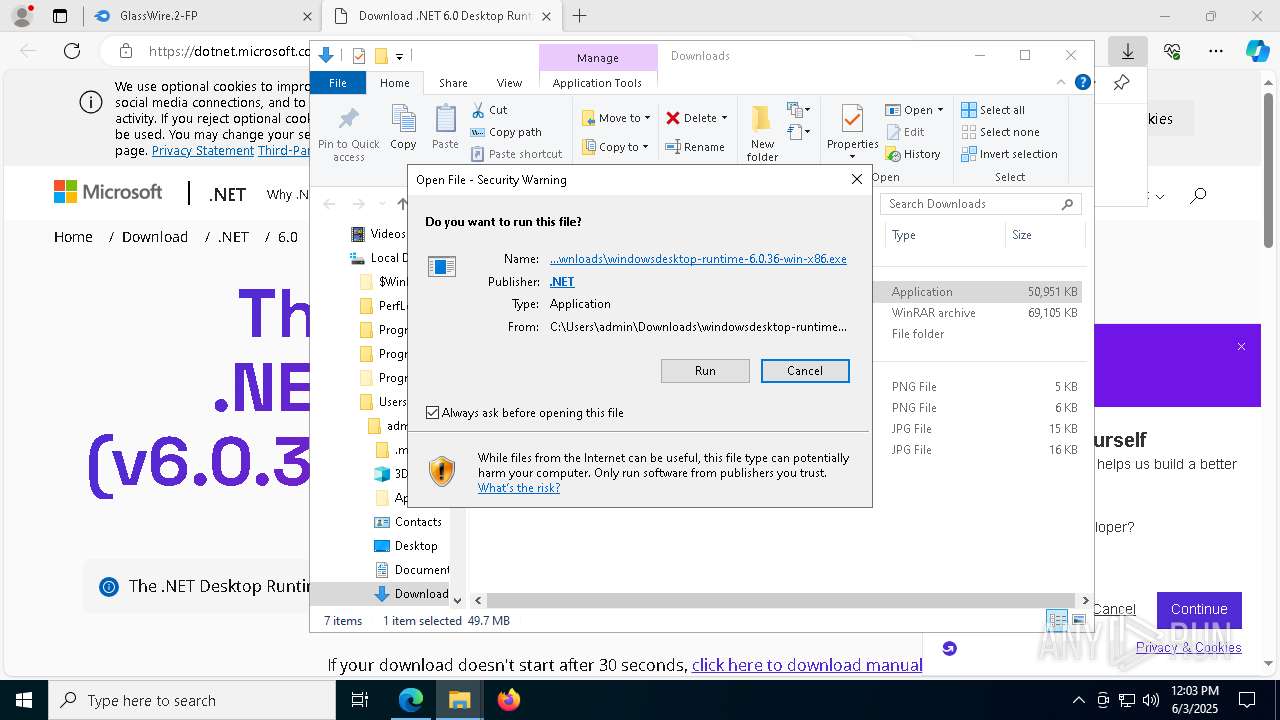
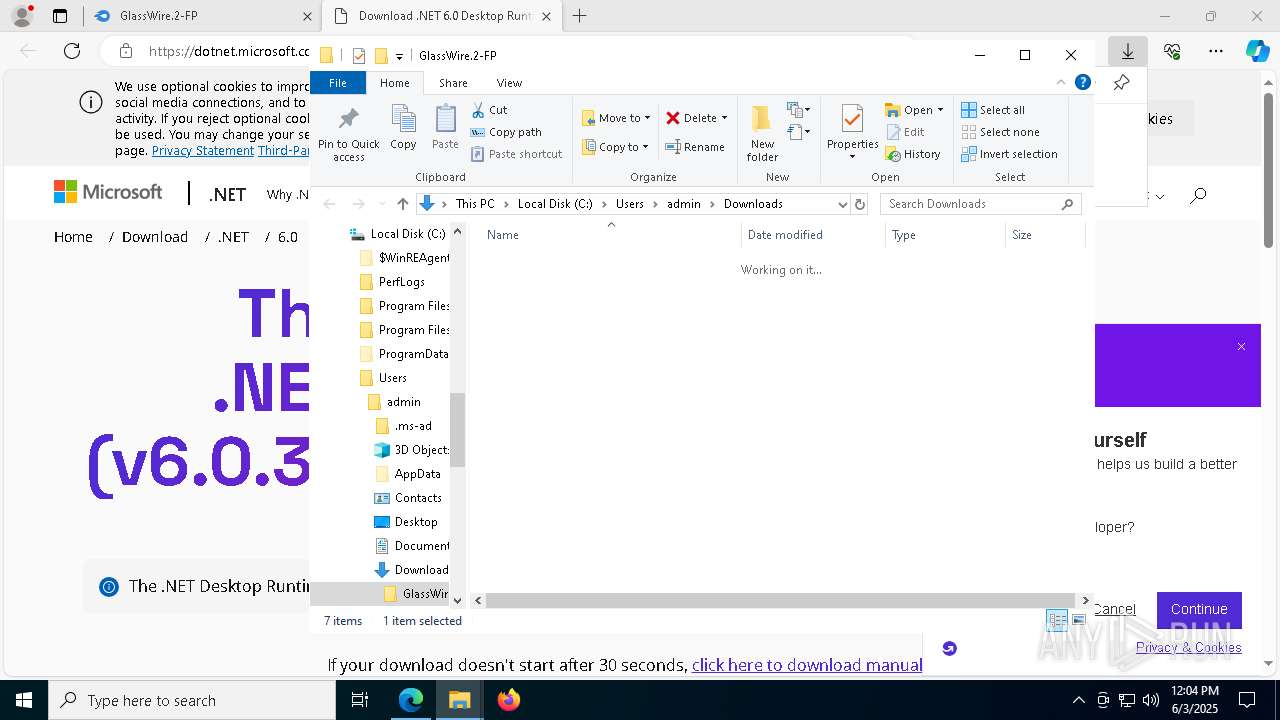
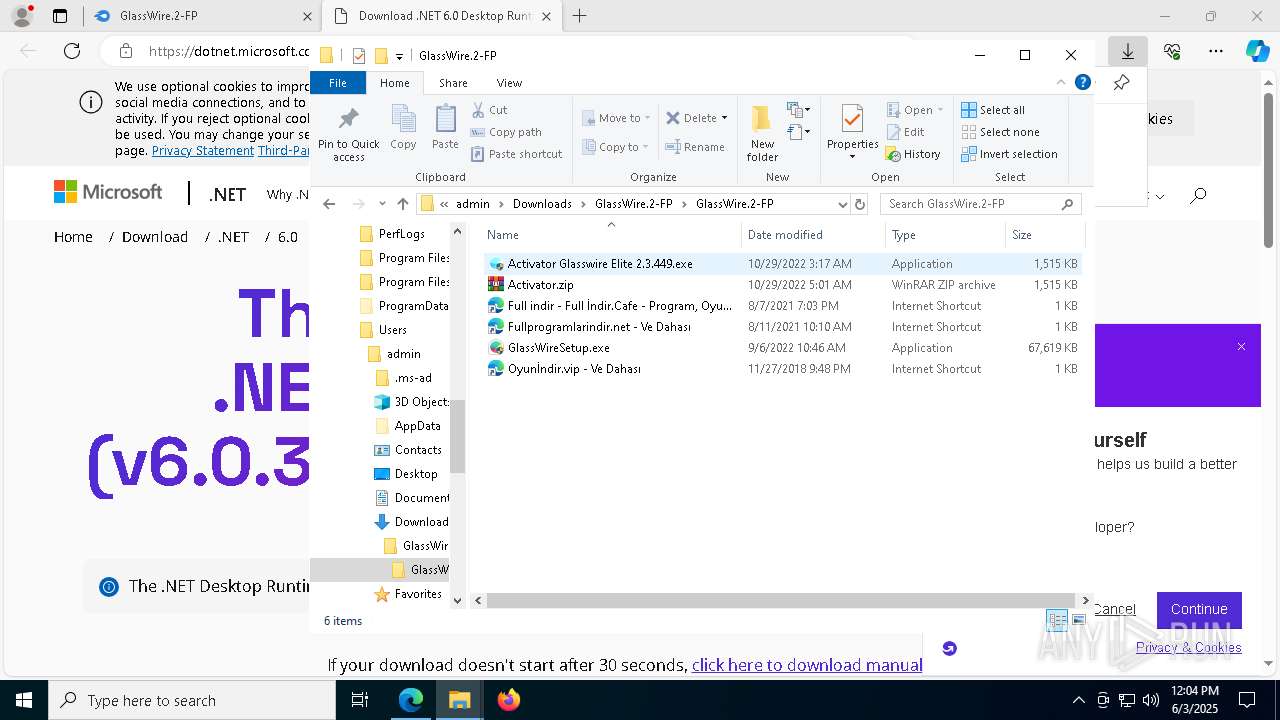
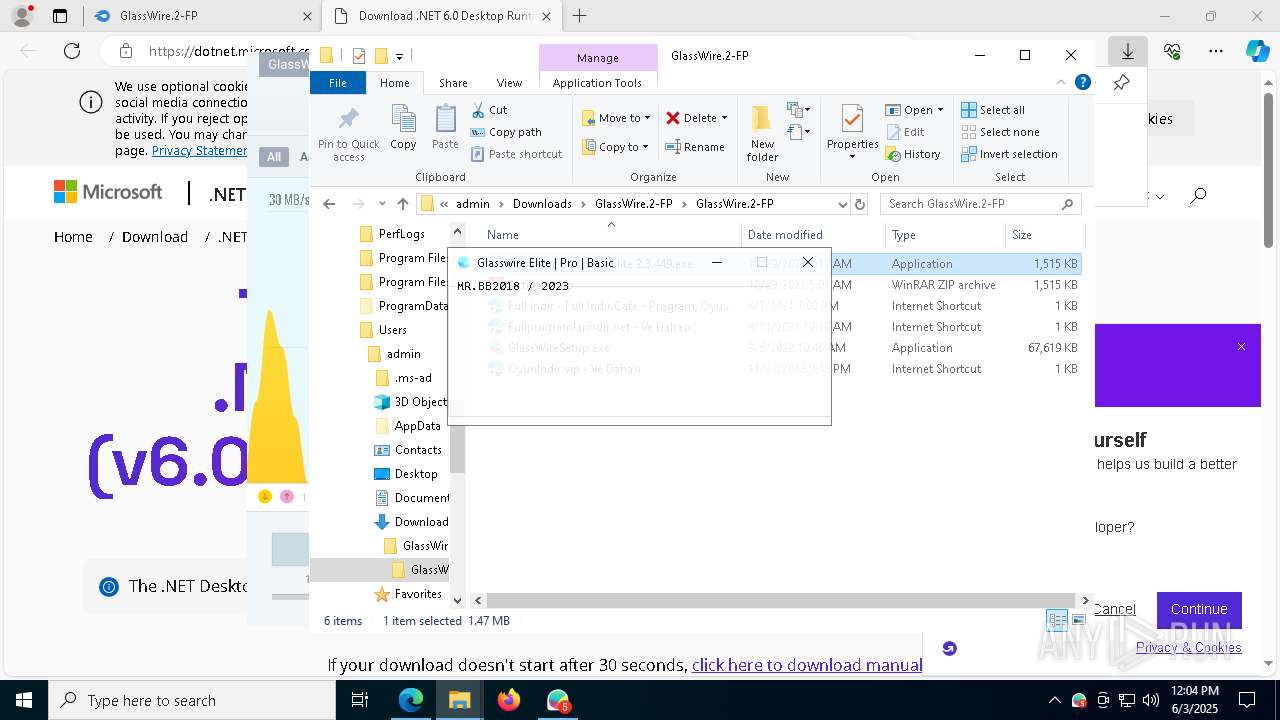
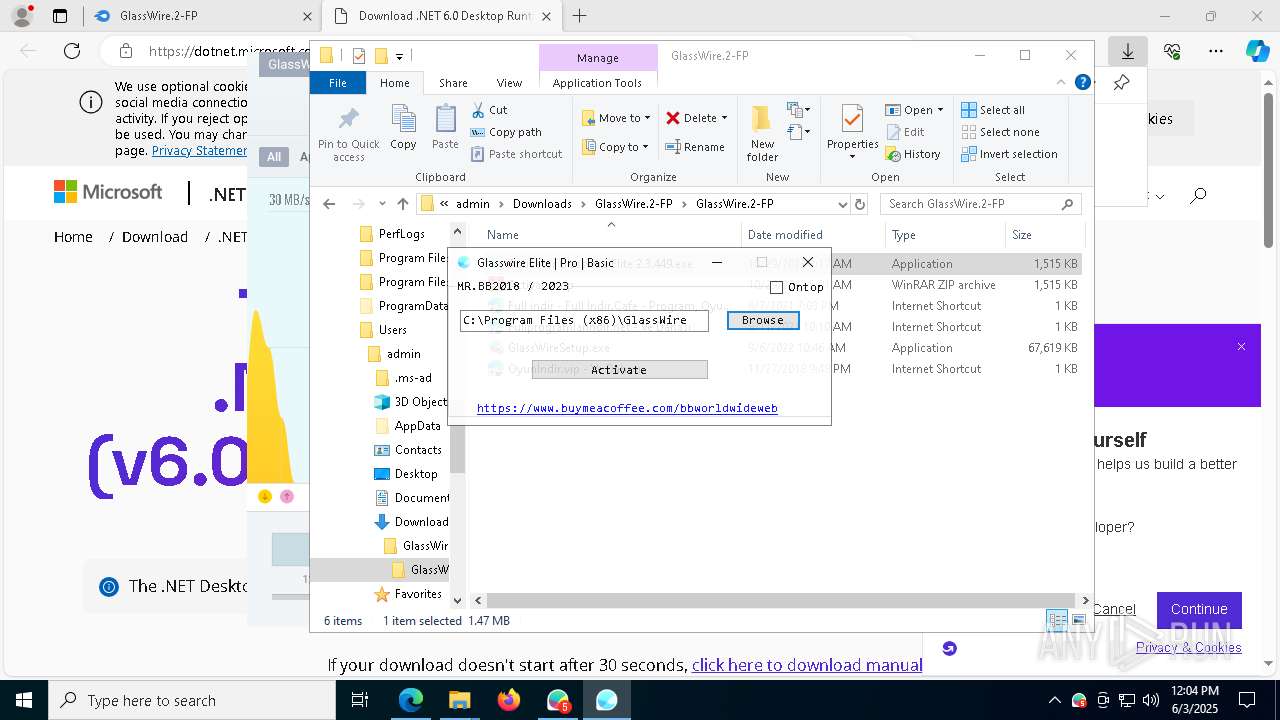
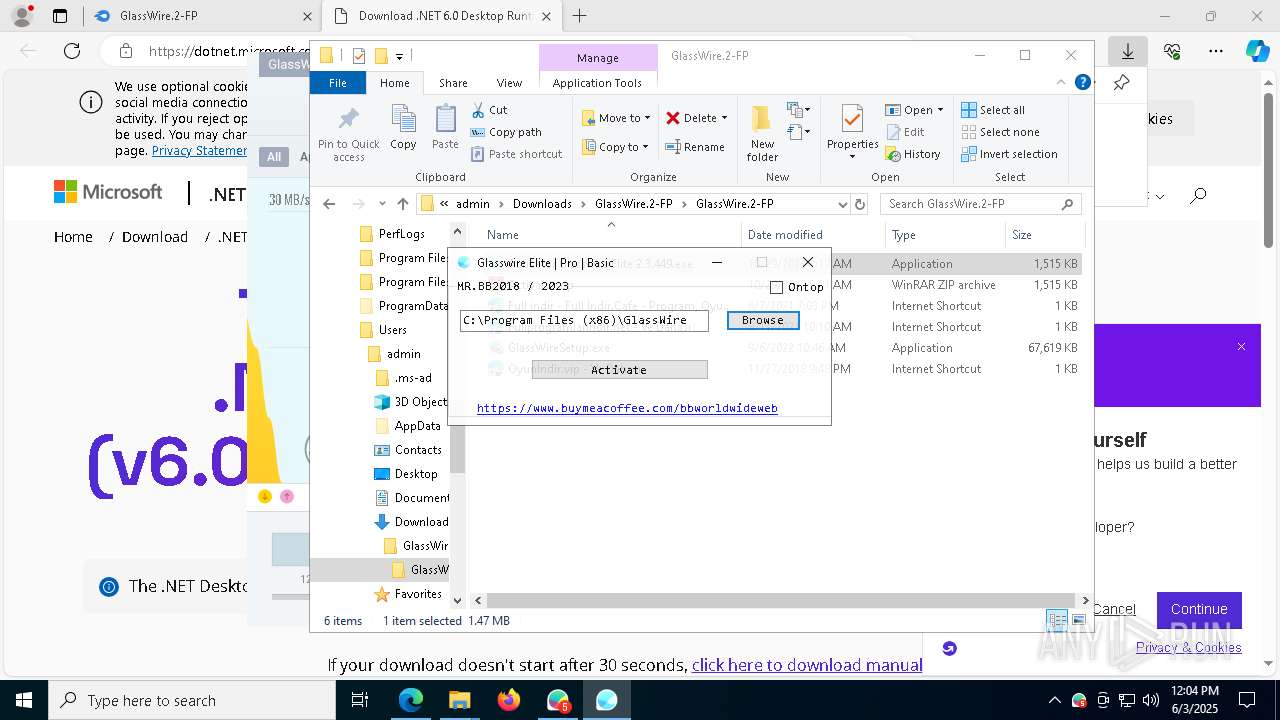
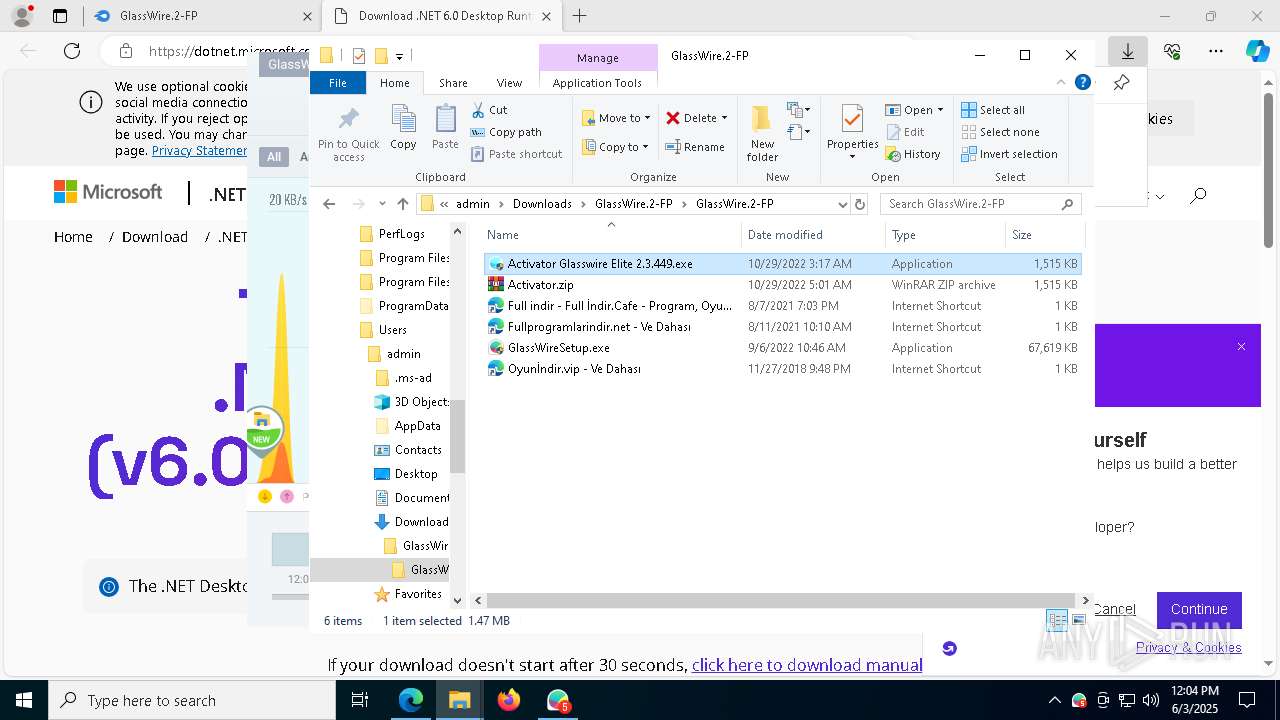
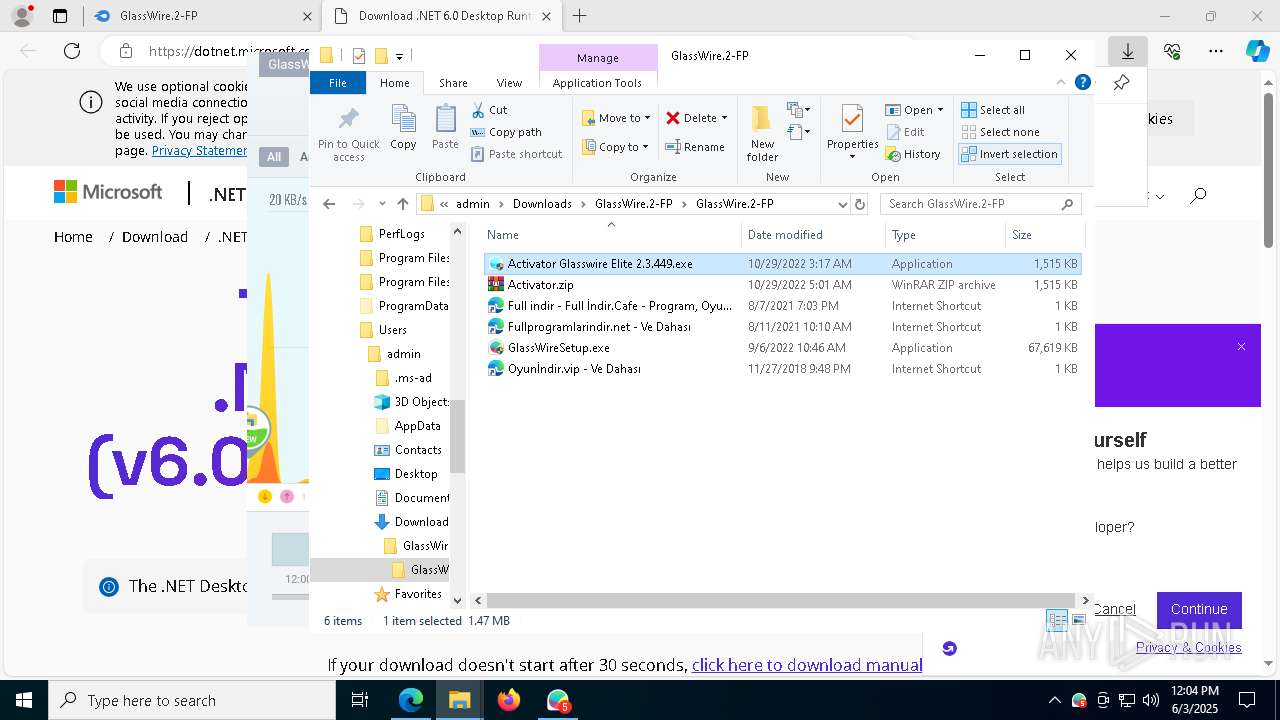
Manual execution by a user
- WinRAR.exe (PID: 7000)
- WinRAR.exe (PID: 1764)
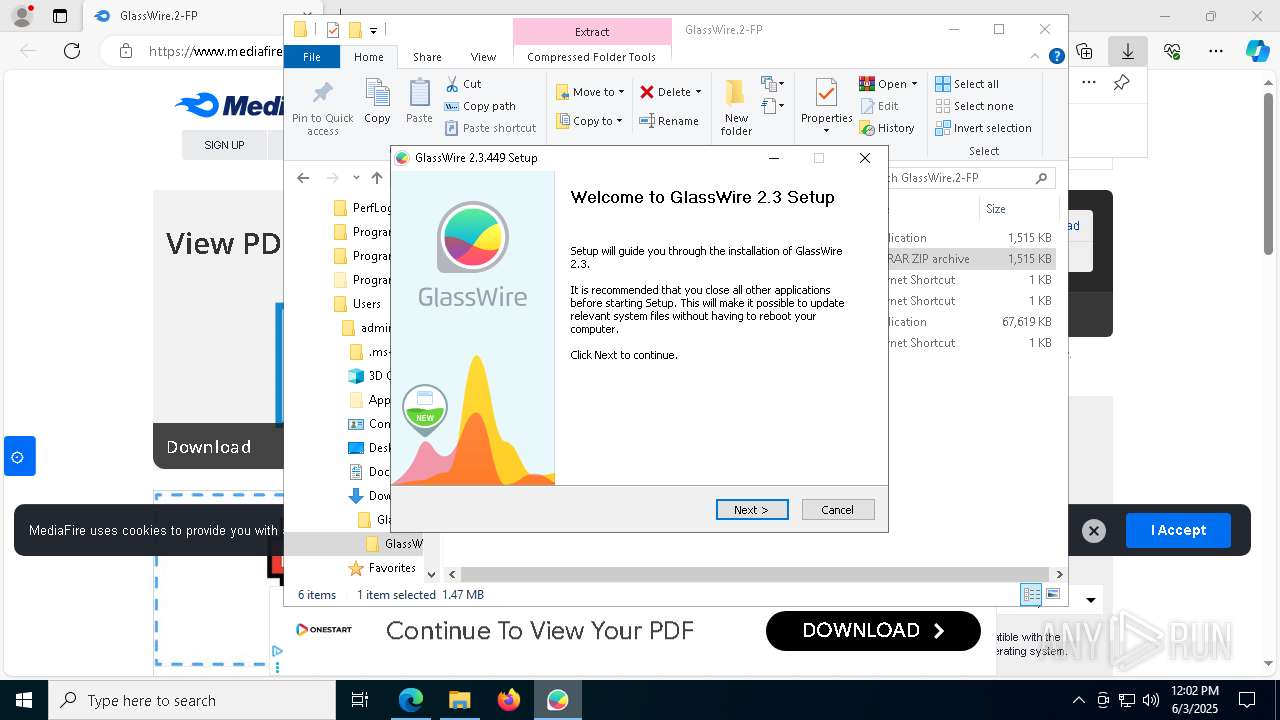
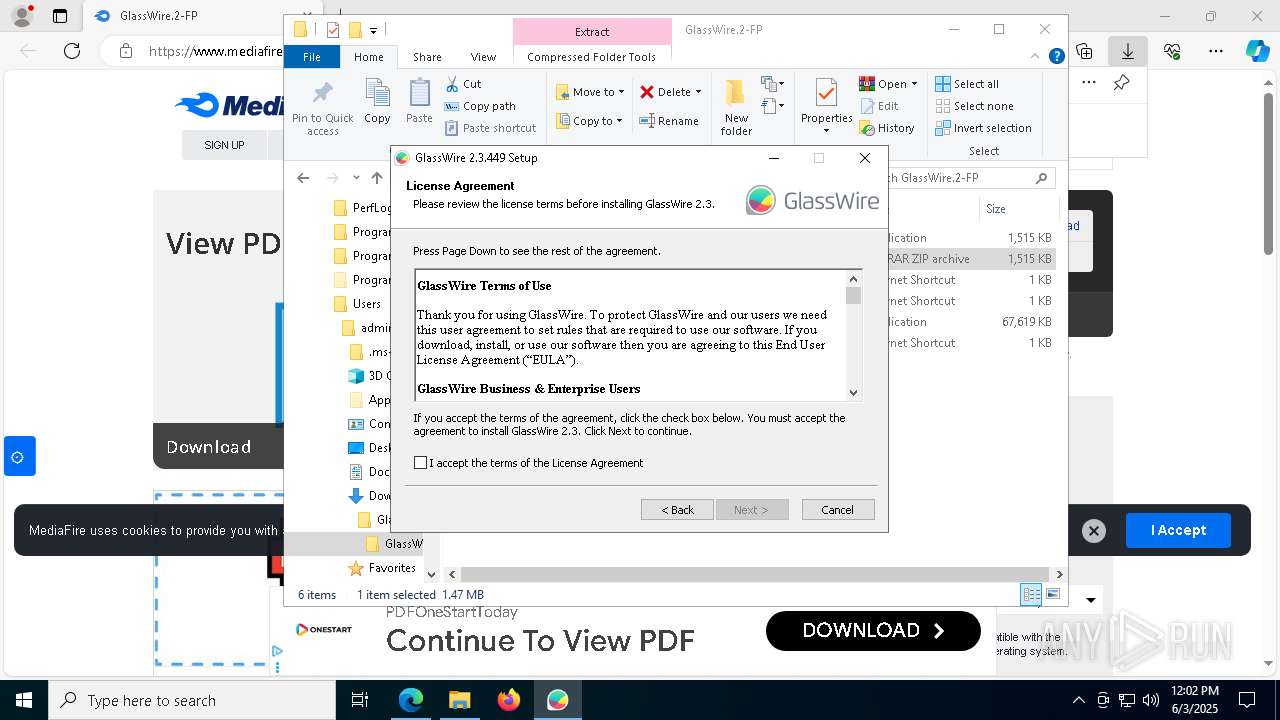
- GlassWireSetup.exe (PID: 5604)
- GlassWireSetup.exe (PID: 5376)
- Activator Glasswire Elite 2.3.449.exe (PID: 8668)
- Activator Glasswire Elite 2.3.449.exe (PID: 8660)
Reads the software policy settings
- slui.exe (PID: 7304)
- GWInstSt.exe (PID: 3760)
Process checks whether UAC notifications are on
- GlassWireSetup.exe (PID: 5376)
The sample compiled with english language support
- GlassWireSetup.exe (PID: 5376)
- vc_redist.x86.exe (PID: 8500)
- msedge.exe (PID: 8804)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 6180)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 9052)
- msiexec.exe (PID: 4932)
- Activator Glasswire Elite 2.3.449.exe (PID: 3744)
- windowsdesktop-runtime-6.0.36-win-x86.exe (PID: 2524)
Create files in a temporary directory
- GlassWireSetup.exe (PID: 5376)
- vc_redist.x86.exe (PID: 8500)
Process checks computer location settings
- GlassWireSetup.exe (PID: 5376)
Creates files in the program directory
- GlassWireSetup.exe (PID: 5376)
Reads the machine GUID from the registry
- GWInstSt.exe (PID: 3760)
Creates files or folders in the user directory
- GWInstSt.exe (PID: 3760)
Launching a file from a Registry key
- rundll32.exe (PID: 132)
Reads the time zone
- runonce.exe (PID: 7292)
Checks proxy server information
- GWInstSt.exe (PID: 3760)
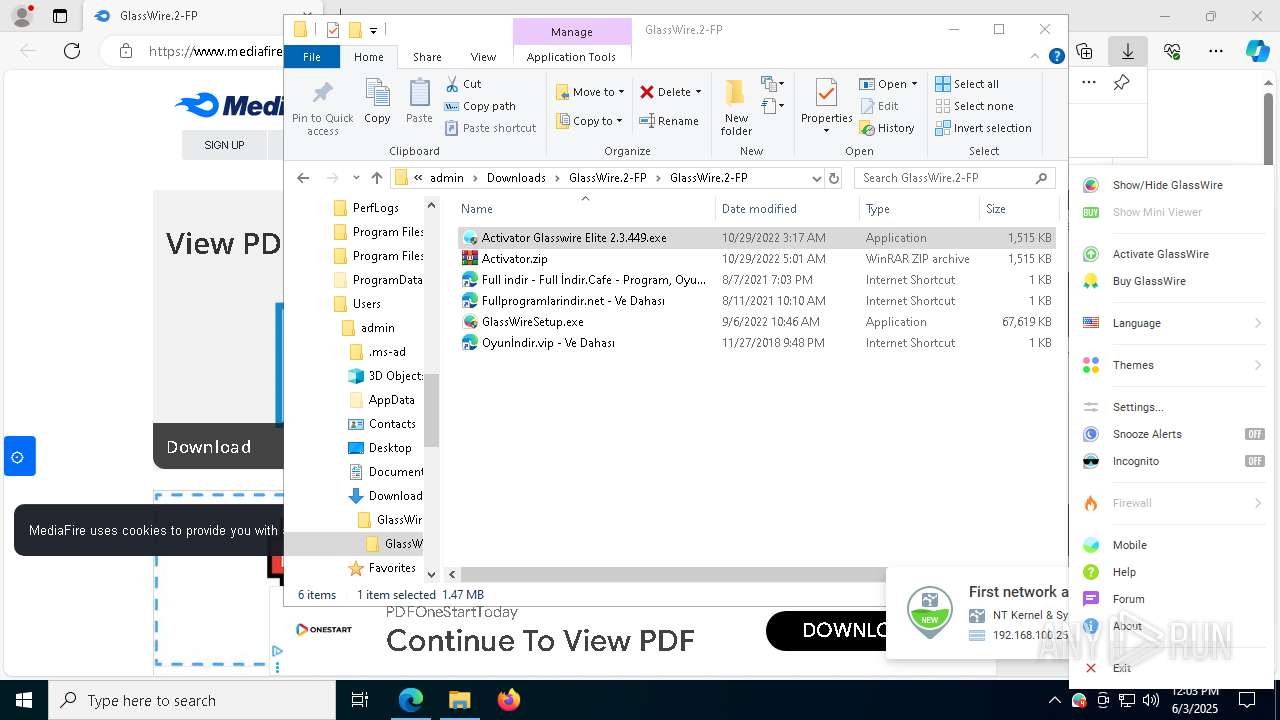
Themida protector has been detected
- GWIdlMon.exe (PID: 5156)
- GWCtlSrv.exe (PID: 2140)
- GlassWire.exe (PID: 8708)
- GWCtlSrv.exe (PID: 7524)
- GlassWire.exe (PID: 1388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
287
Monitored processes
146
Malicious processes
7
Suspicious processes
3
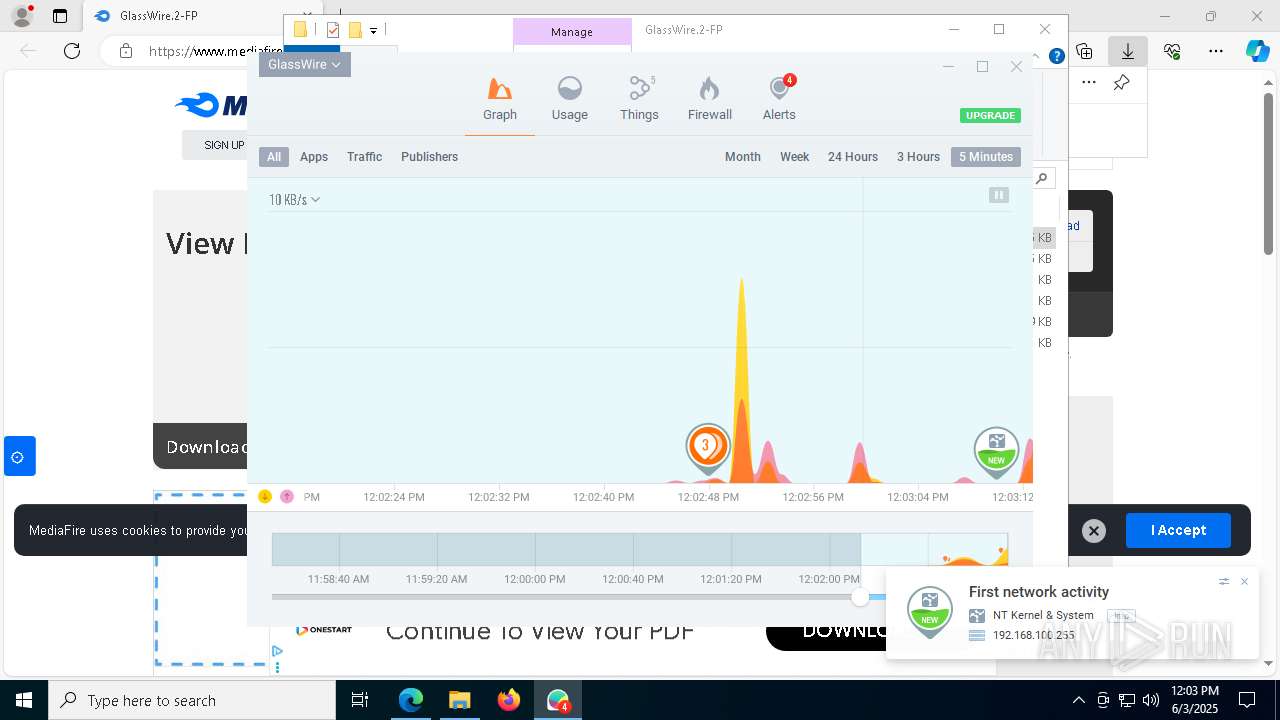
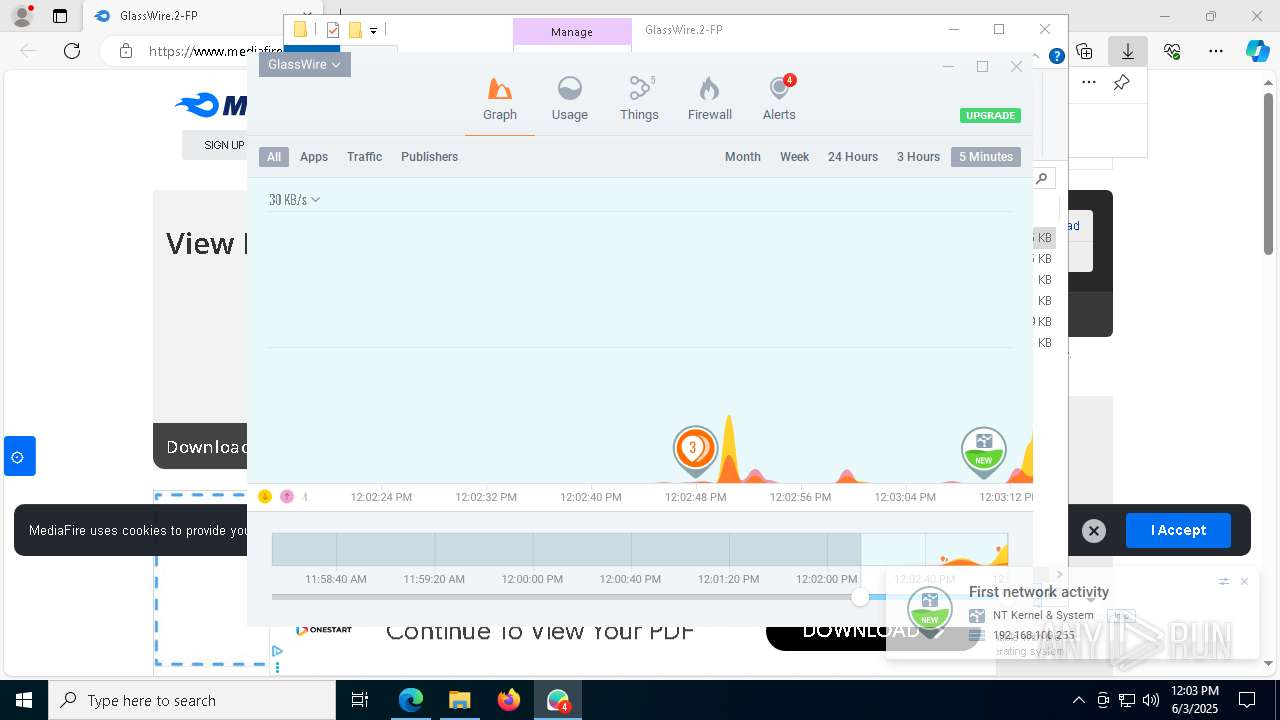
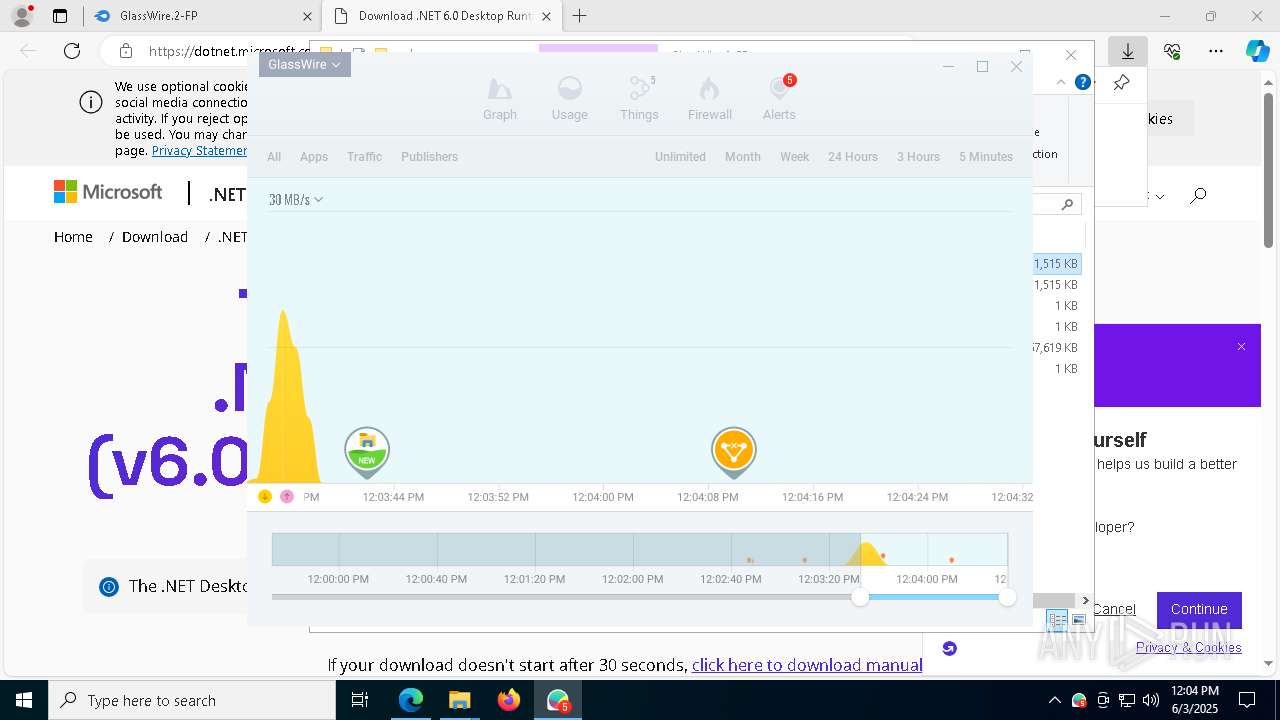
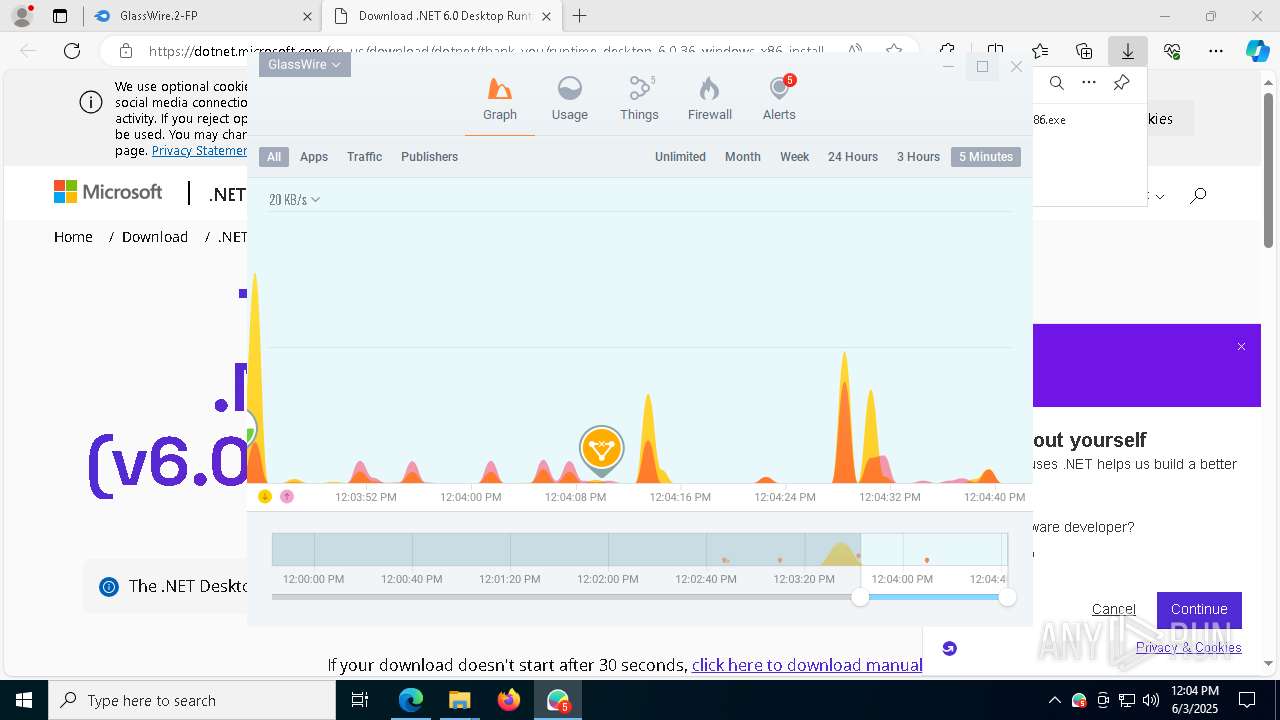
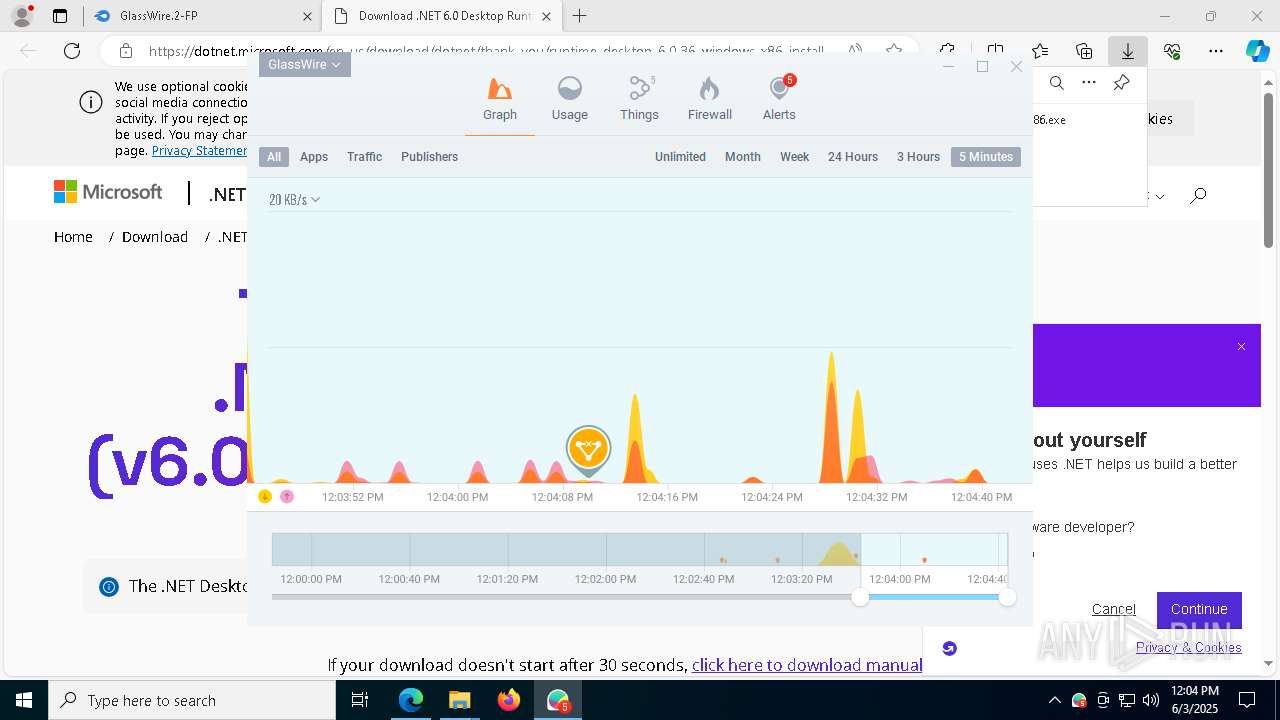
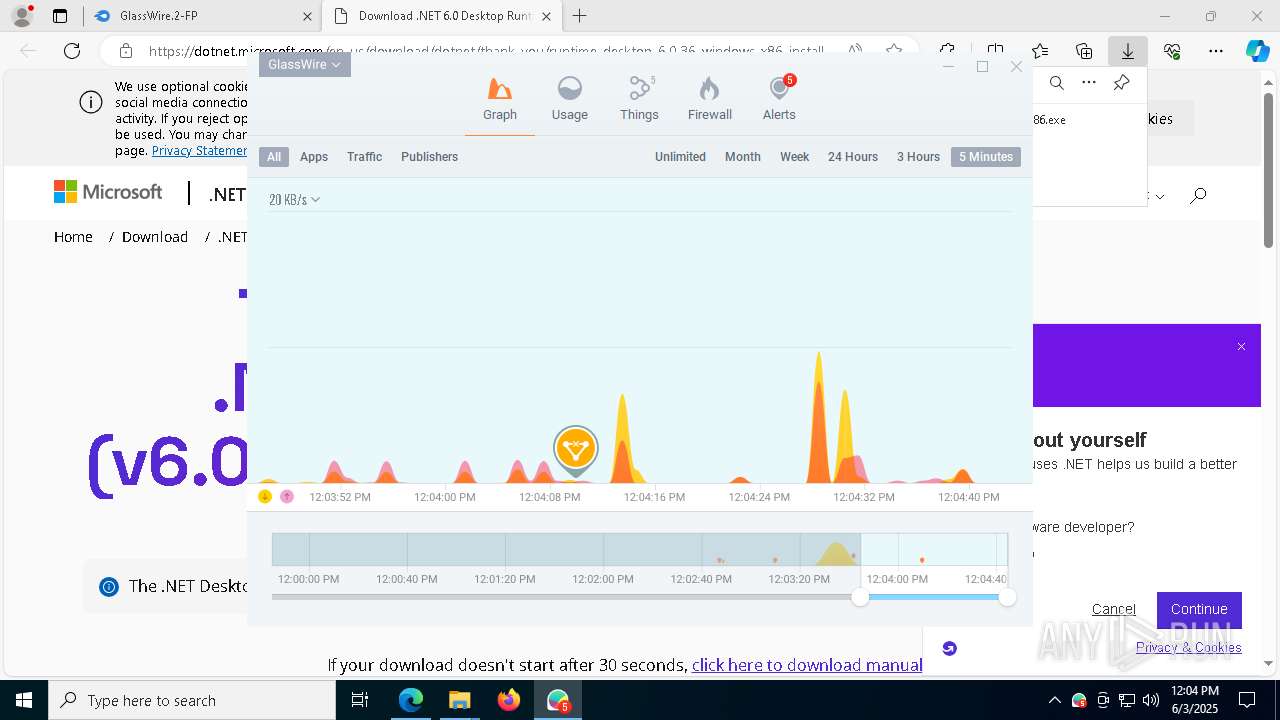
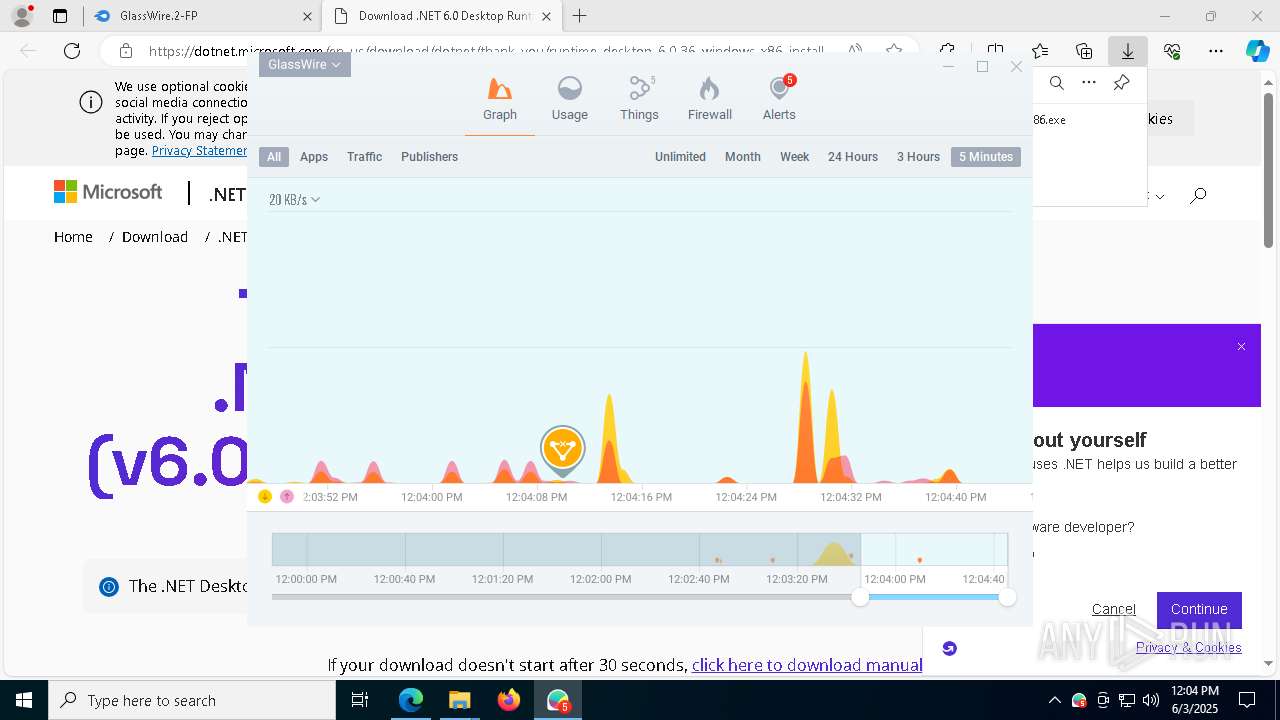
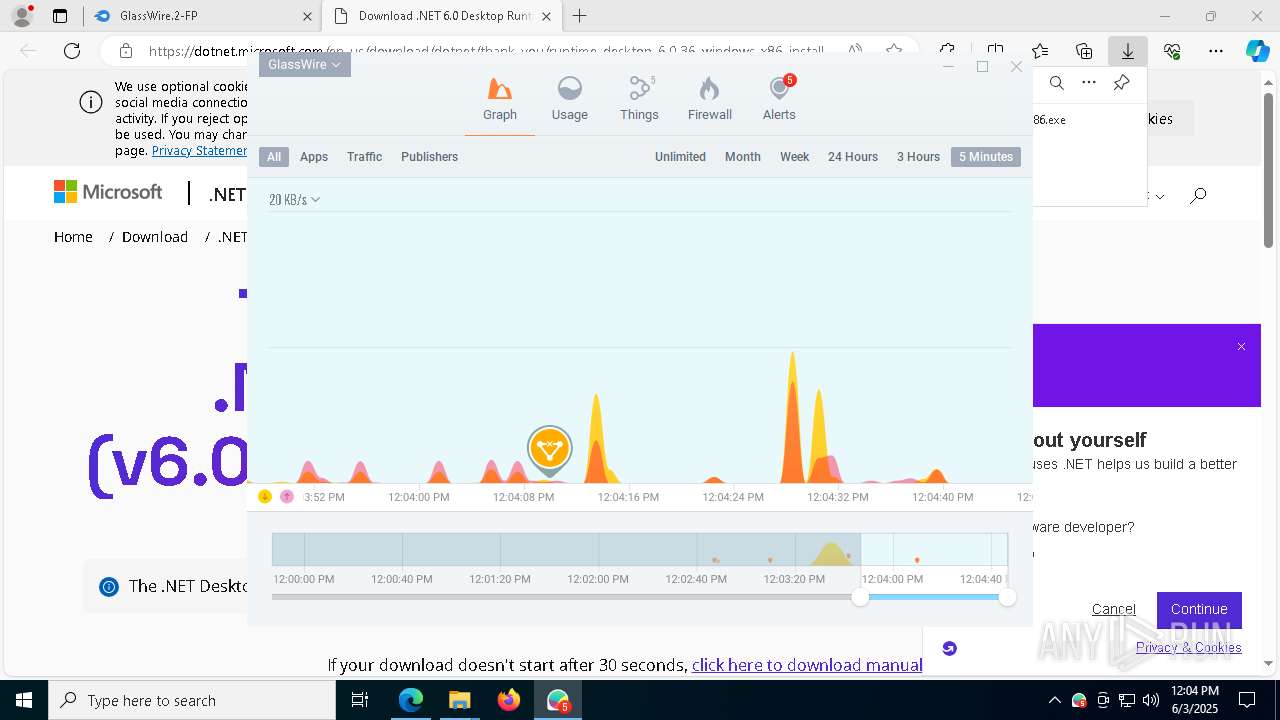
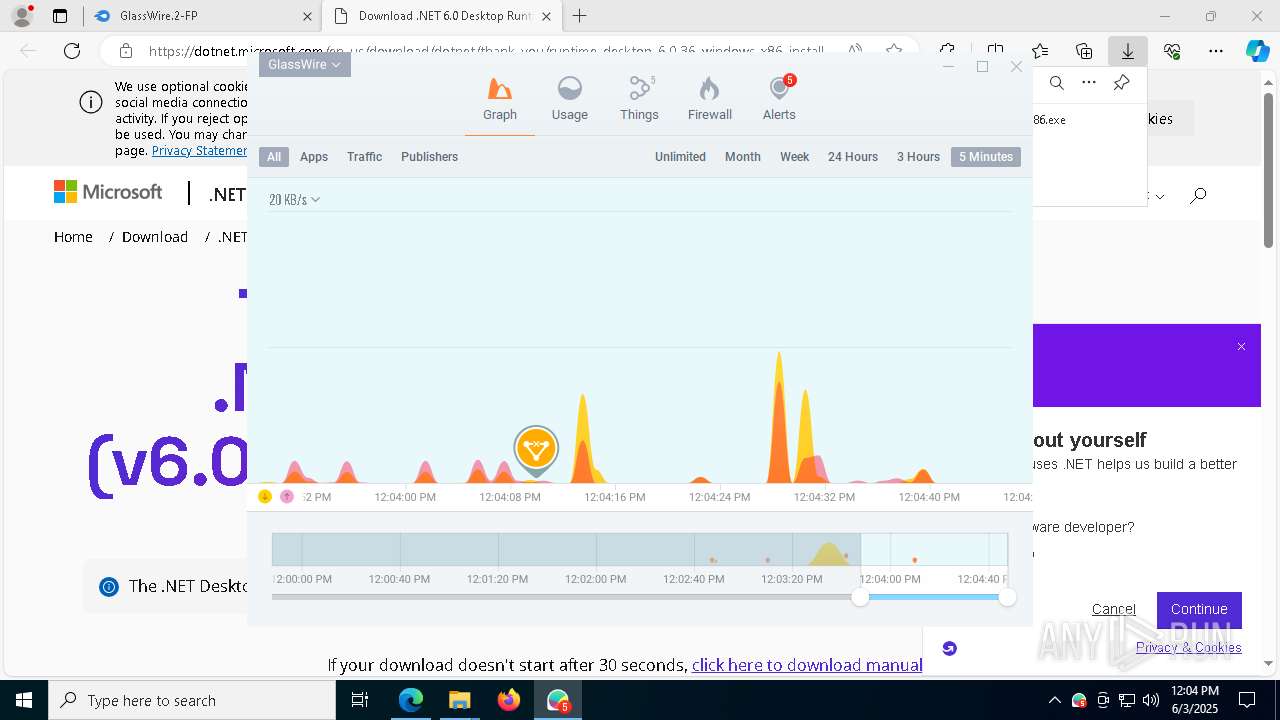
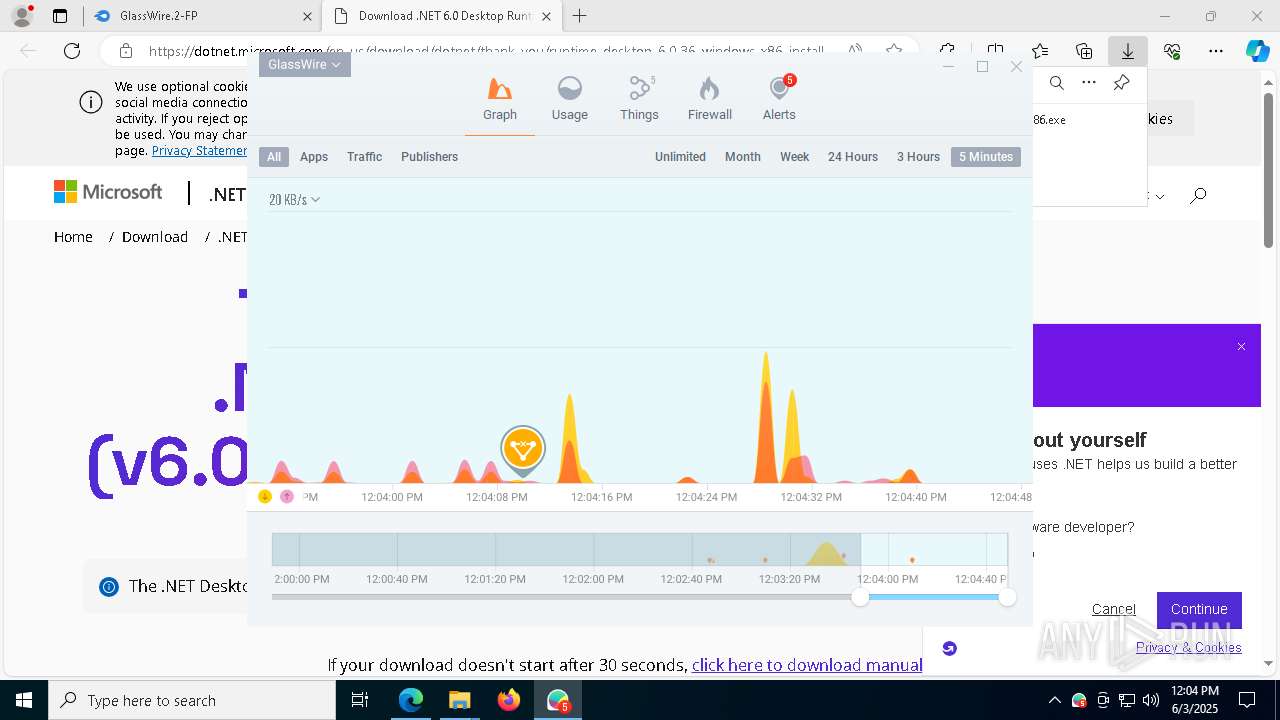
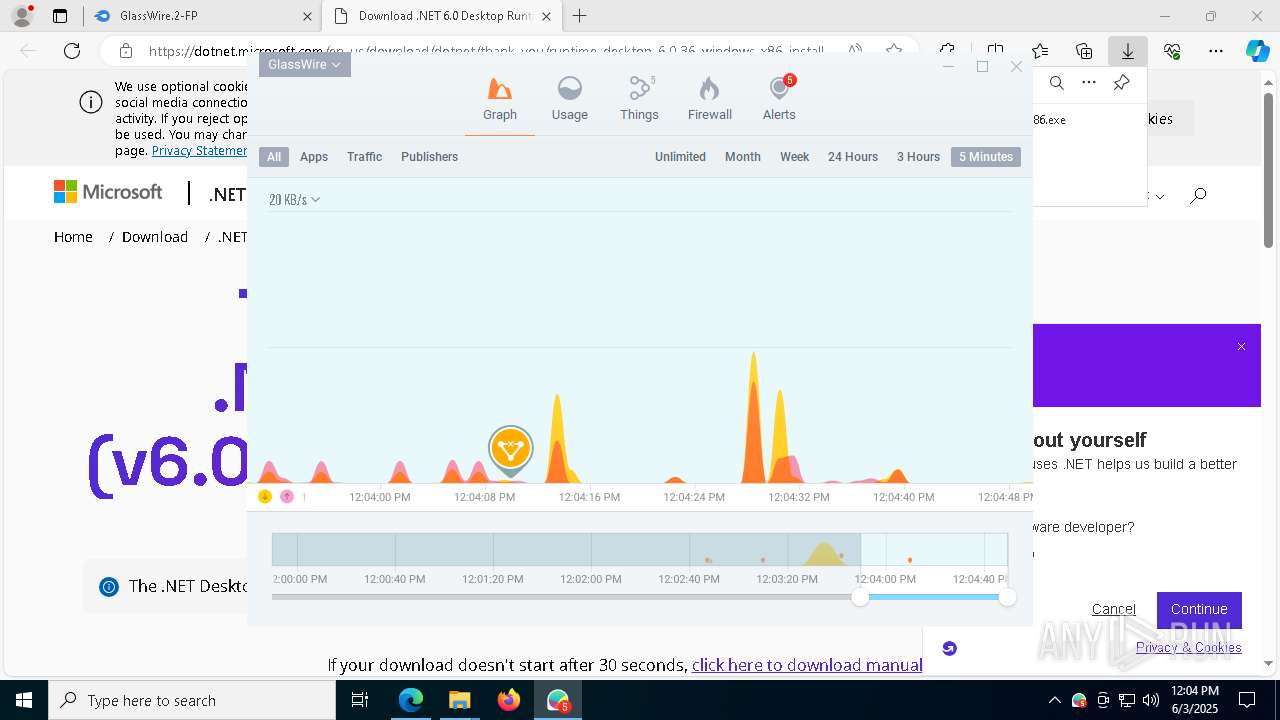
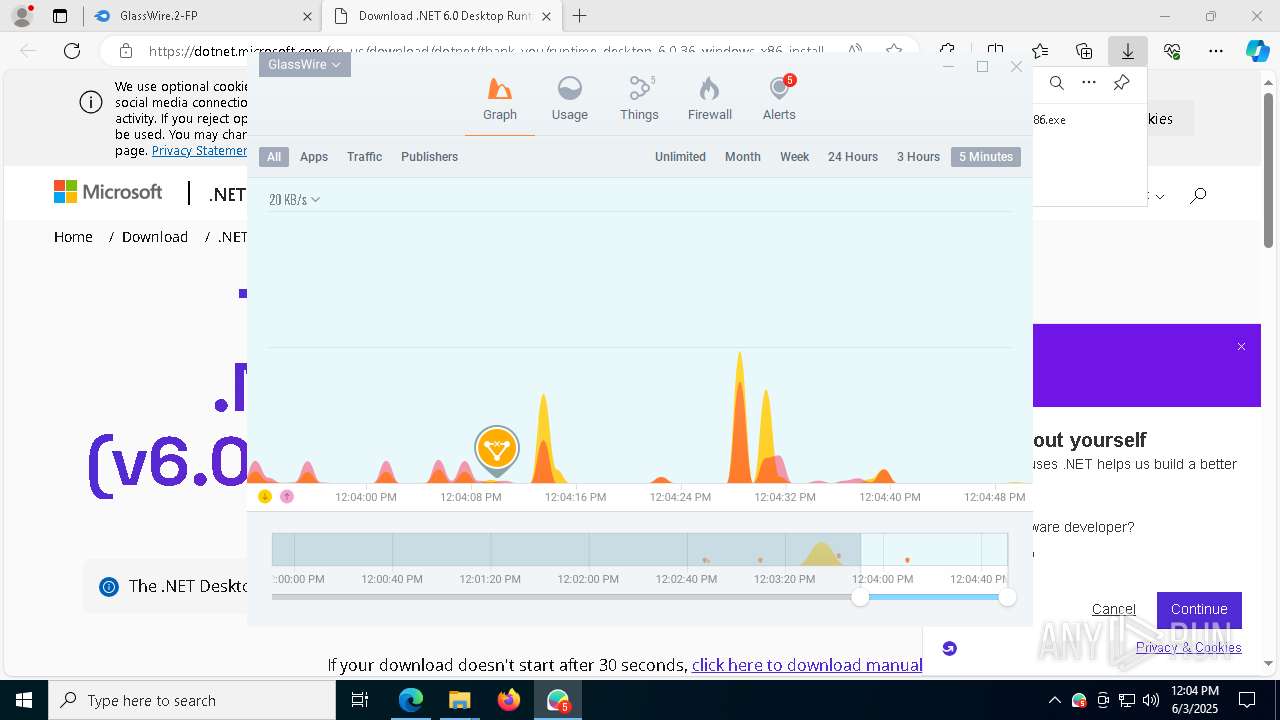
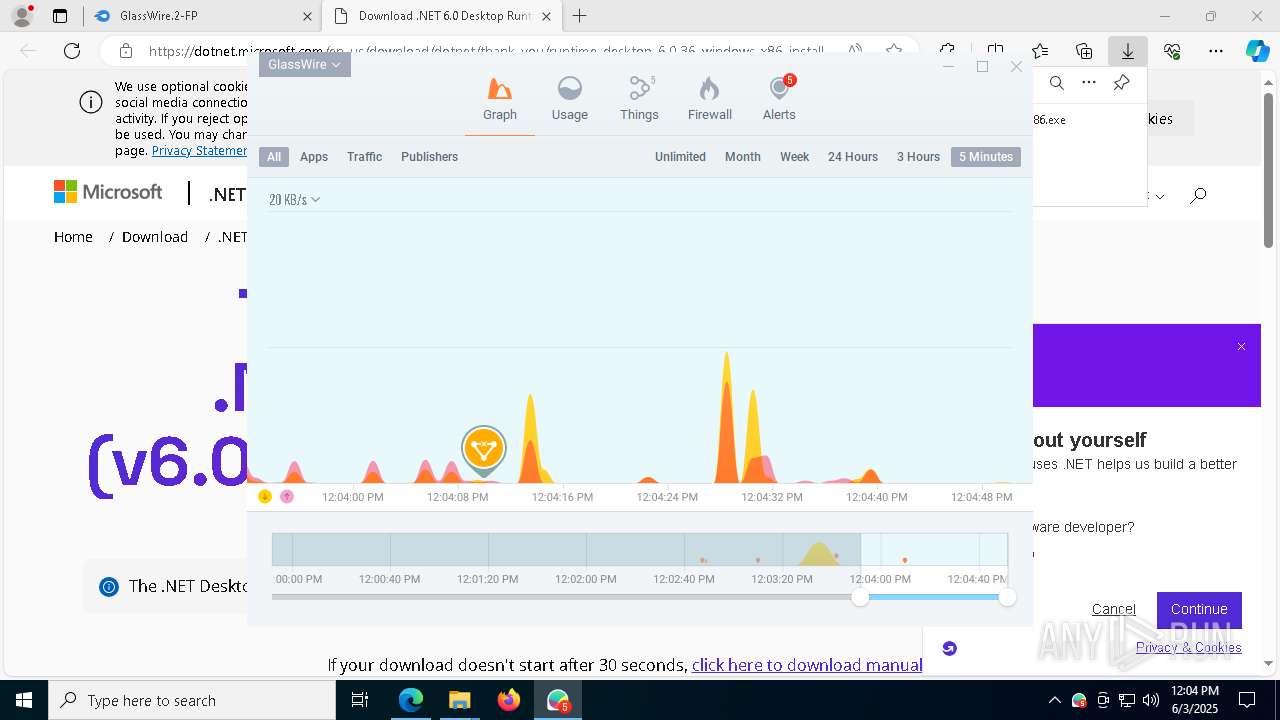
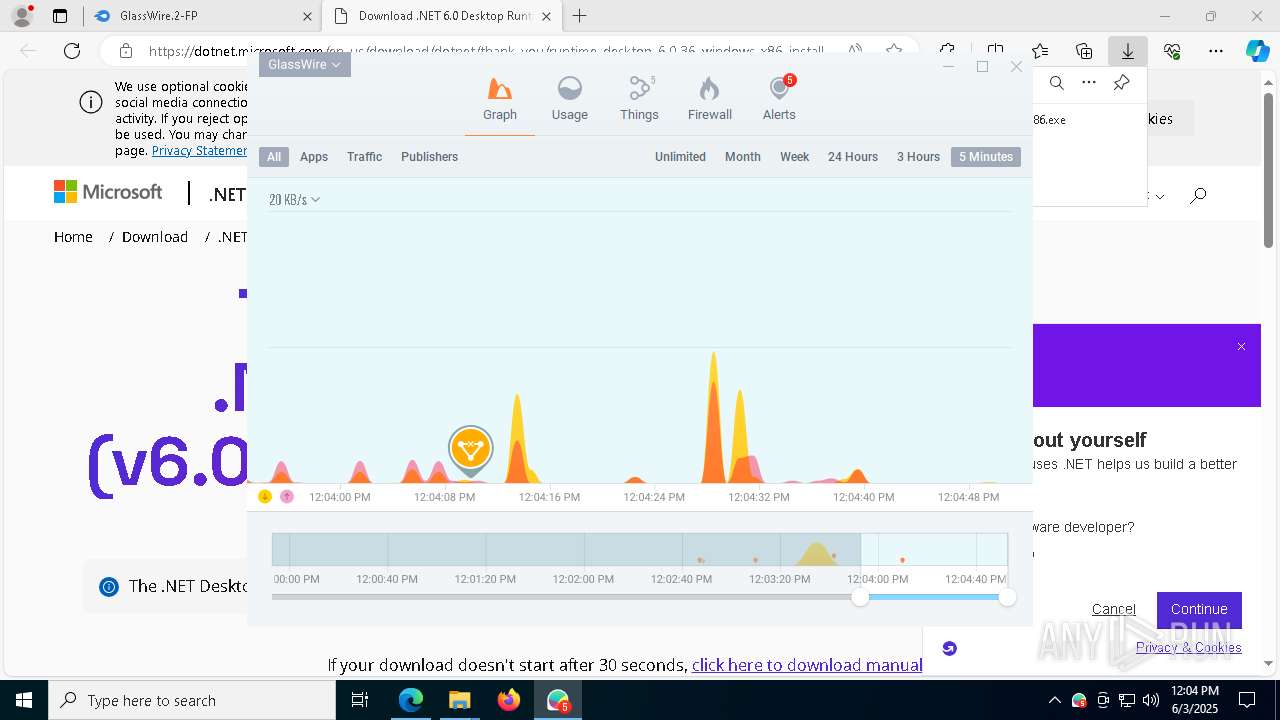
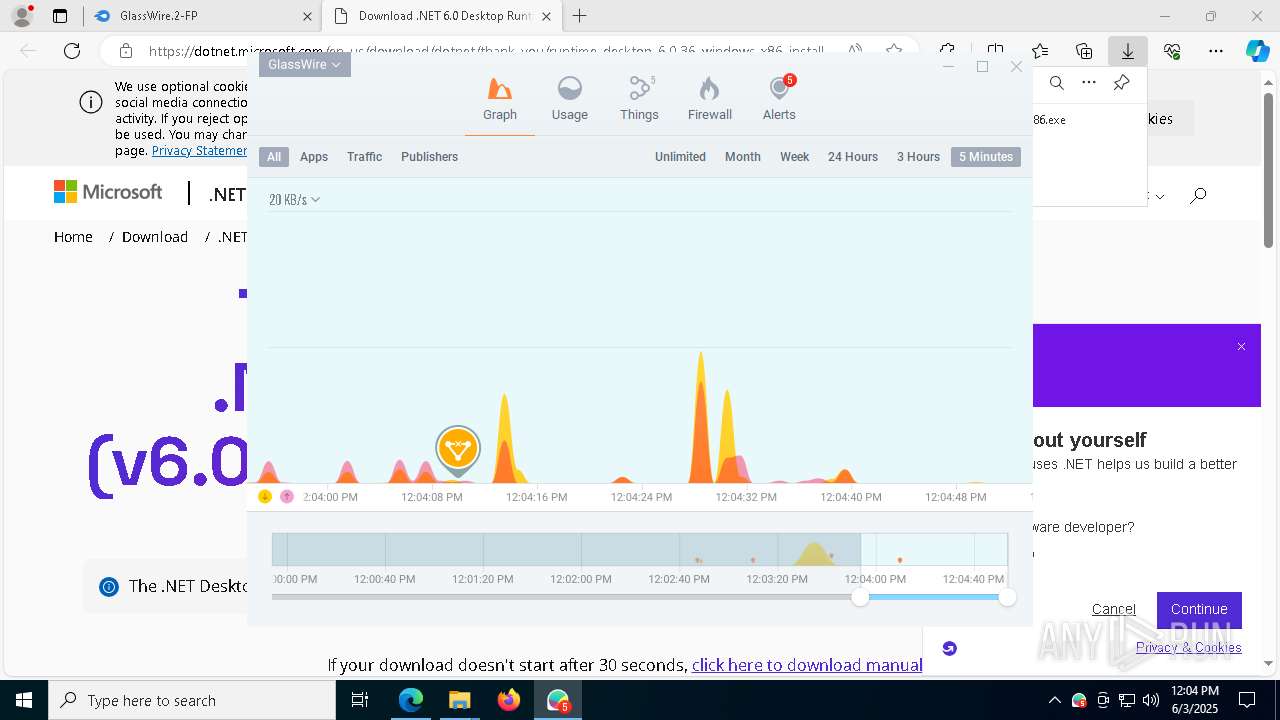
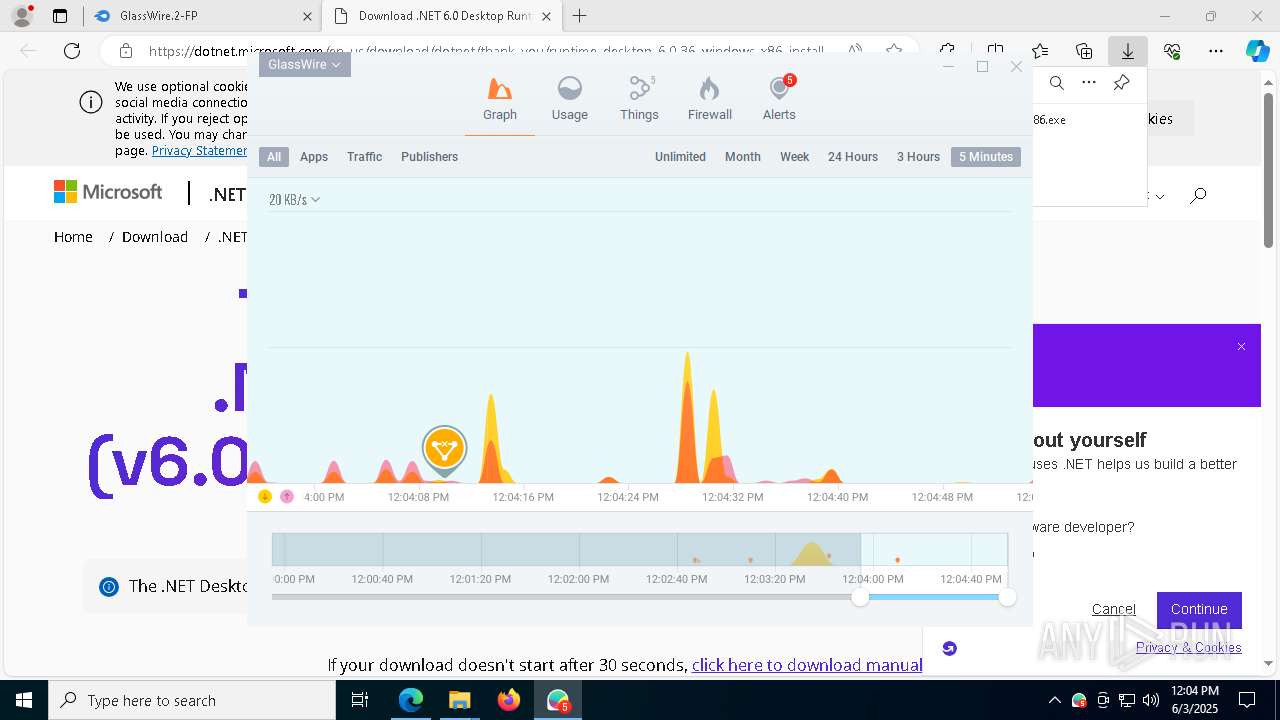
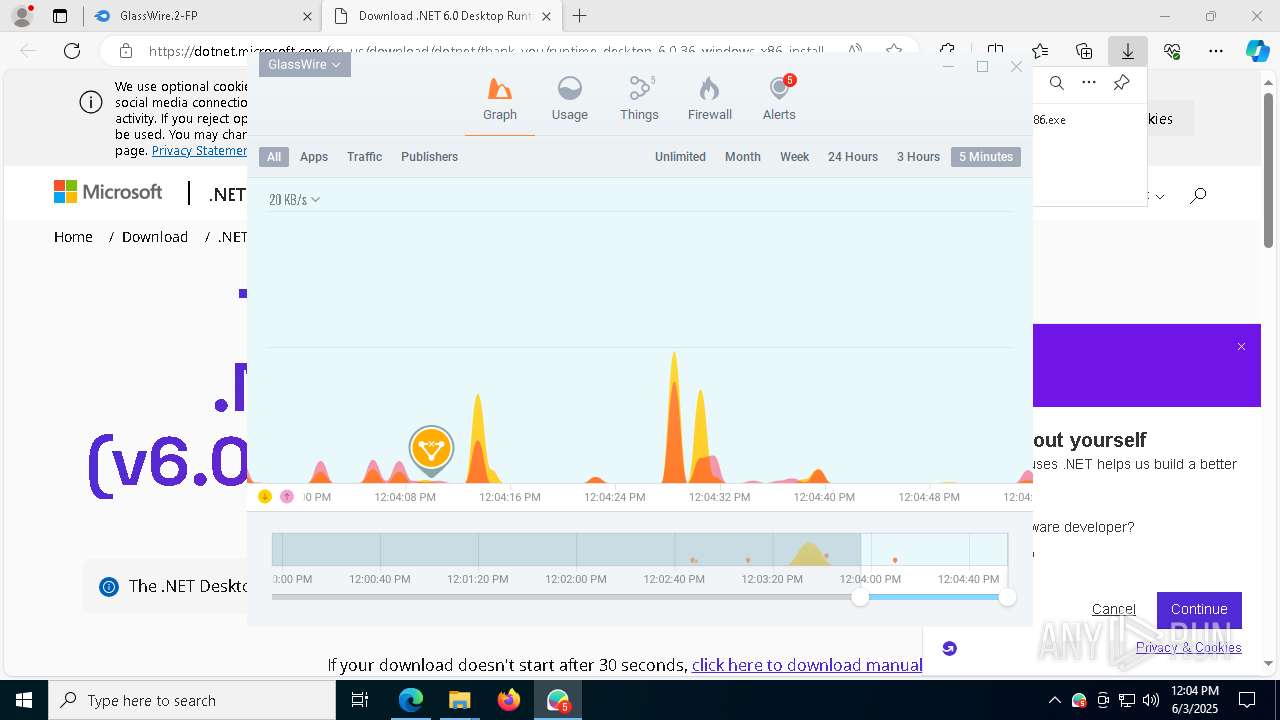
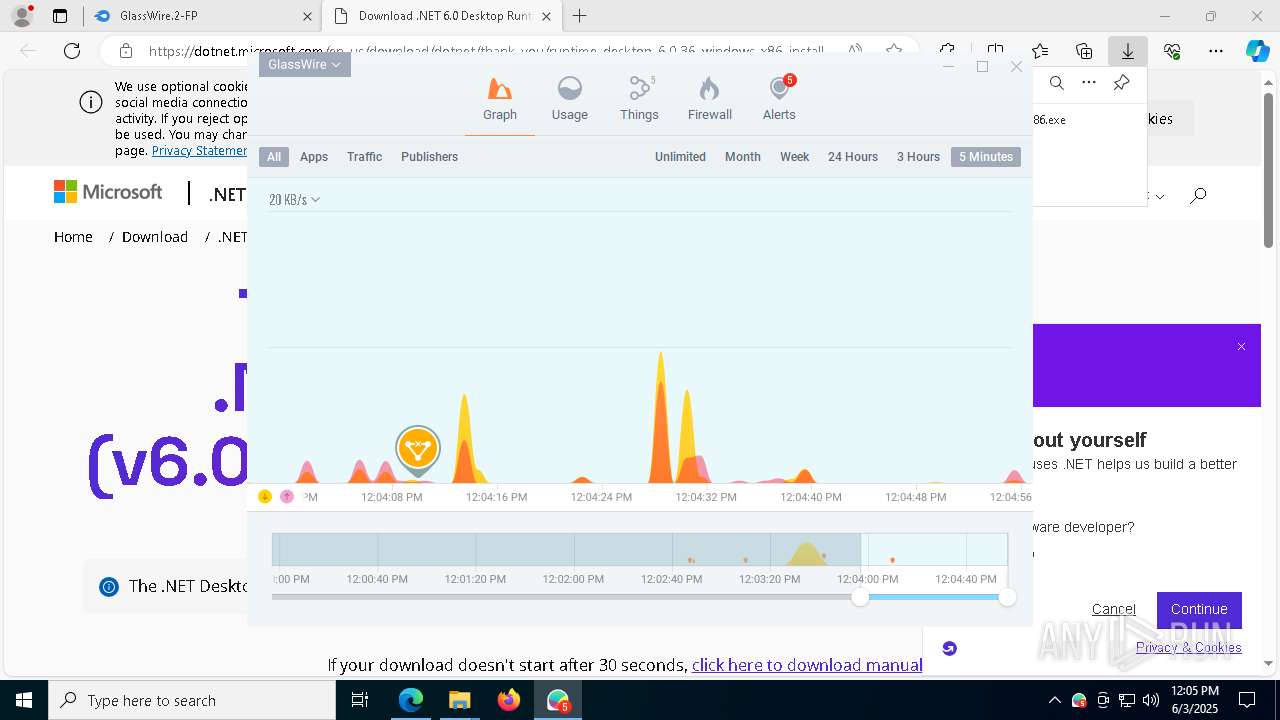
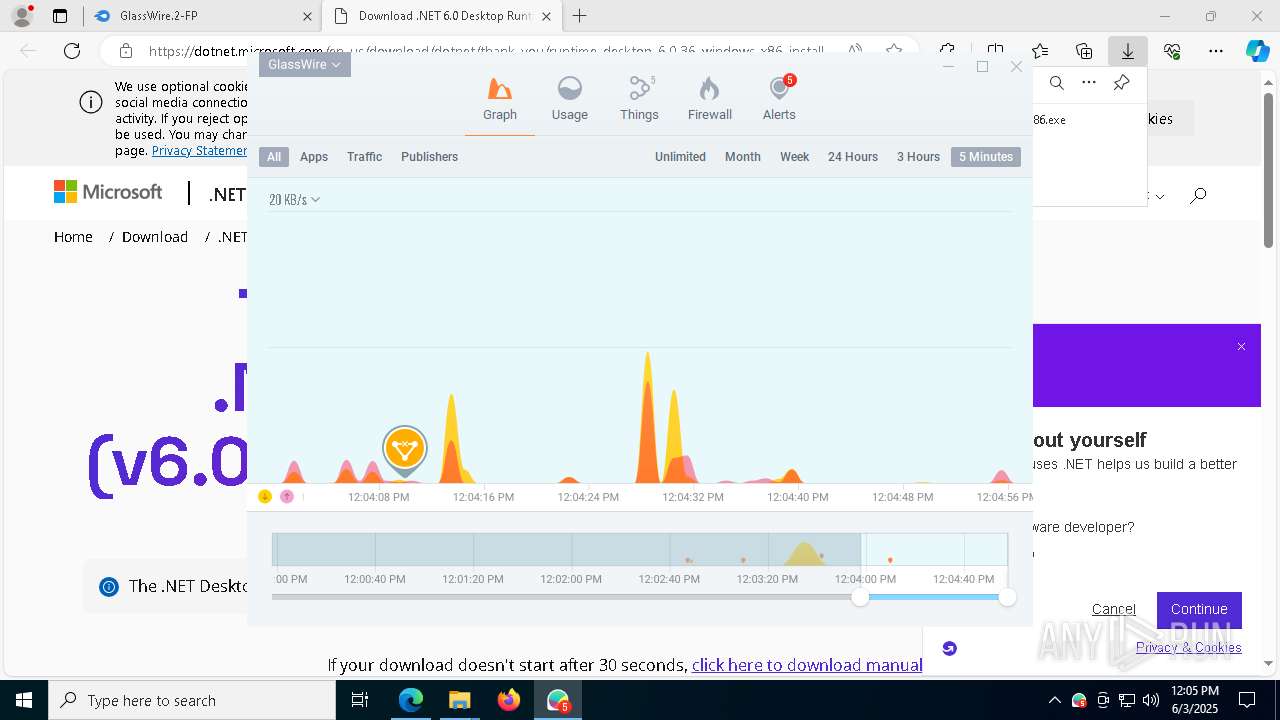
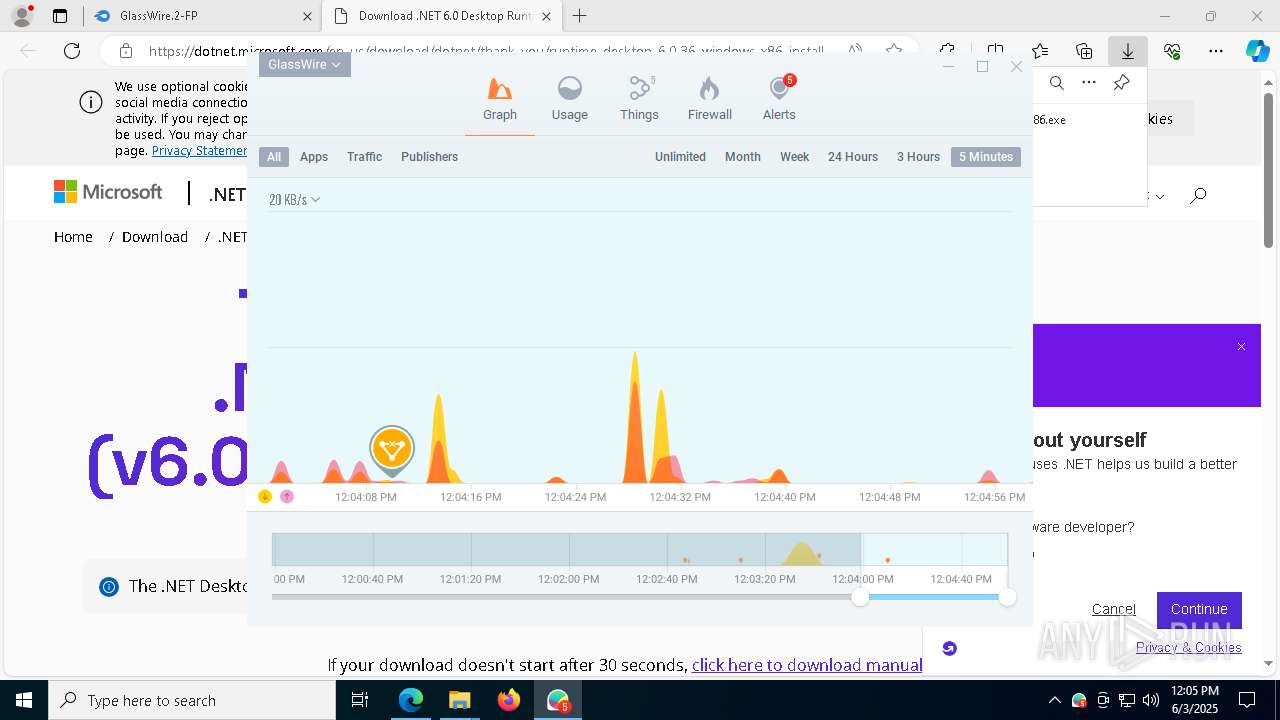
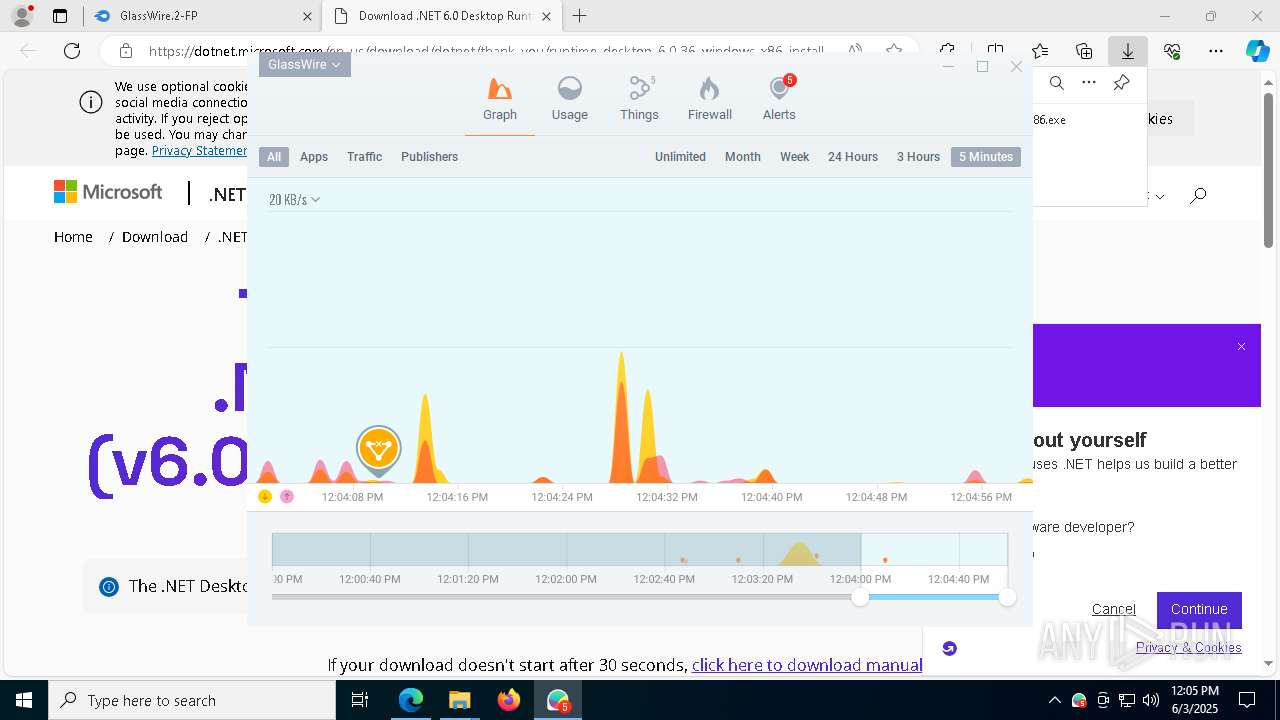
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\System32\RunDLL32.Exe syssetup,SetupInfObjectInstallAction DefaultInstall 128 C:\WINDOWS\System32\Drivers\gwdrv.inf | C:\Windows\System32\rundll32.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3572 --field-trial-handle=2268,i,7298105277169875438,14017825894590759128,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=6292 --field-trial-handle=2268,i,7298105277169875438,14017825894590759128,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 472 | C:\WINDOWS\System32\net.exe start gwdrv | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5524 --field-trial-handle=2268,i,7298105277169875438,14017825894590759128,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=8800 --field-trial-handle=2268,i,7298105277169875438,14017825894590759128,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=63 --mojo-platform-channel-handle=7148 --field-trial-handle=2268,i,7298105277169875438,14017825894590759128,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 808 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5748 --field-trial-handle=2268,i,7298105277169875438,14017825894590759128,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=9536 --field-trial-handle=2268,i,7298105277169875438,14017825894590759128,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=8668 --field-trial-handle=2268,i,7298105277169875438,14017825894590759128,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
86 912
Read events
85 389
Write events
1 433
Delete events
90
Modification events
| (PID) Process: | (5956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5956) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C9CD43E93F952F00 | |||
| (PID) Process: | (5956) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9F894BE93F952F00 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000040328 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:00000000000C031A |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262952 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {95250E9D-6D0C-4F46-906C-321D65B95C27} | |||
| (PID) Process: | (5956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262952 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0809D19F-1F1E-4B1C-920A-4F2E0DADB646} | |||
Executable files
558
Suspicious files
742
Text files
202
Unknown types
118
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f605.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f615.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f625.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f615.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f634.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f663.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
304
DNS requests
387
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | svchost.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8772 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748971709&P2=404&P3=2&P4=WU1Uzi9b5uKHDk06j1nu5jC1xUWV%2fCAlU0fVkPGrle0rpnZSH8pymhsS3UzH1rSxU%2fK%2fYG5WNtyq%2fAFKEdZJhg%3d%3d | unknown | — | — | whitelisted |
8772 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748971709&P2=404&P3=2&P4=WU1Uzi9b5uKHDk06j1nu5jC1xUWV%2fCAlU0fVkPGrle0rpnZSH8pymhsS3UzH1rSxU%2fK%2fYG5WNtyq%2fAFKEdZJhg%3d%3d | unknown | — | — | whitelisted |
8772 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748971709&P2=404&P3=2&P4=WU1Uzi9b5uKHDk06j1nu5jC1xUWV%2fCAlU0fVkPGrle0rpnZSH8pymhsS3UzH1rSxU%2fK%2fYG5WNtyq%2fAFKEdZJhg%3d%3d | unknown | — | — | whitelisted |
8772 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1748971710&P2=404&P3=2&P4=FWR4yhS5Nm9RxZ0HDCYsmrU5fr88rDL%2fogQs23gQbM%2bupjiuLRT6JM8rVjD0lz9j2T5WAhPIzM620BrOrHnjZg%3d%3d | unknown | — | — | whitelisted |
8772 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1748971710&P2=404&P3=2&P4=FWR4yhS5Nm9RxZ0HDCYsmrU5fr88rDL%2fogQs23gQbM%2bupjiuLRT6JM8rVjD0lz9j2T5WAhPIzM620BrOrHnjZg%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8772 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b96d4ca8-86b5-4bcc-9b2f-8200e97368c2?P1=1749216525&P2=404&P3=2&P4=luT1tcr3Wklf7%2bBHooDPrdAr066VpH45F%2fLzuKRxsbrWgchKw8wjjFuPBSpQz90cd7SDKbhGlQVW3RlaUaZNKQ%3d%3d | unknown | — | — | whitelisted |
8772 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b96d4ca8-86b5-4bcc-9b2f-8200e97368c2?P1=1749216525&P2=404&P3=2&P4=luT1tcr3Wklf7%2bBHooDPrdAr066VpH45F%2fLzuKRxsbrWgchKw8wjjFuPBSpQz90cd7SDKbhGlQVW3RlaUaZNKQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
864 | svchost.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
864 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5576 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5956 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6920 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6920 | msedge.exe | 104.17.151.117:443 | www.mediafire.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
static.mediafire.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |