| URL: | http://download1424.mediafire.com/vgum1shaocug/c3kk08tv25nb666/FreeFileSync_10.9_macOS.zip |
| Full analysis: | https://app.any.run/tasks/99ecb19c-30b7-4d2d-a62c-6837ee27bea5 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 23:07:36 |
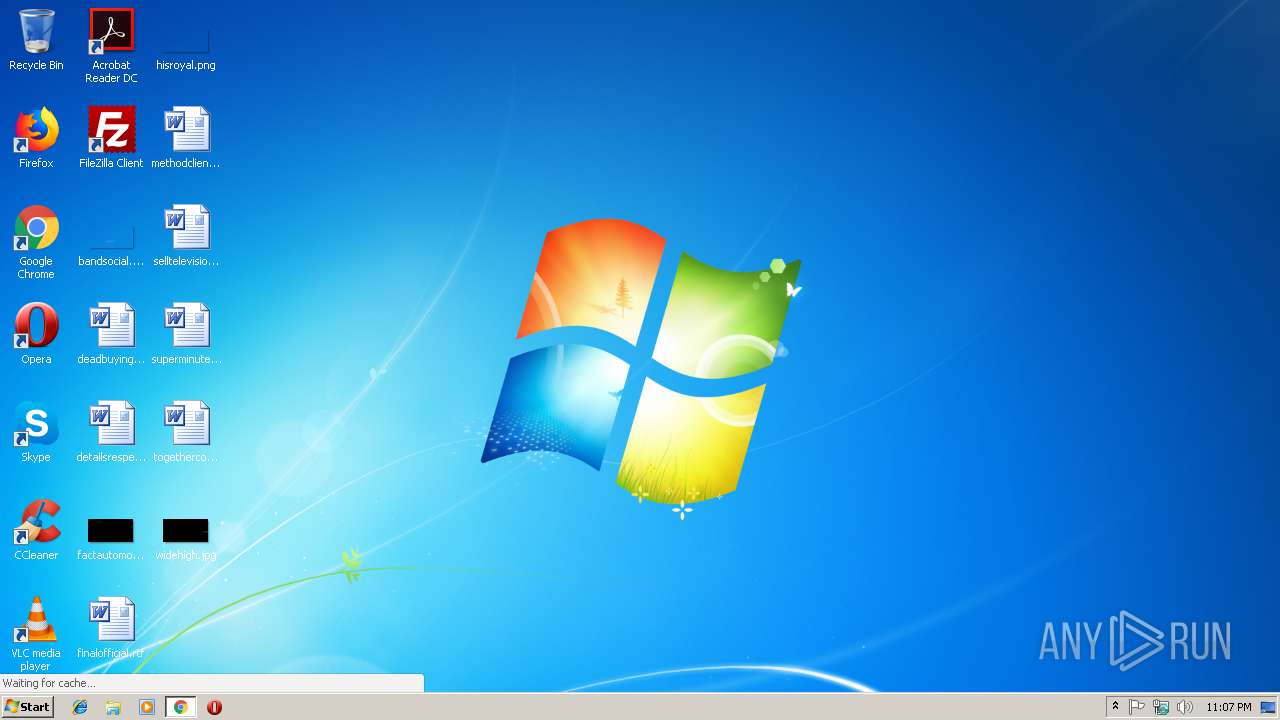
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2BD2CEBC02668F8F65E838F4CB2317A0 |
| SHA1: | DC2E6BA5C2CAC278D0B2448FC407DB7D327B2650 |
| SHA256: | 997CF9580C85F7CF8E074777B9BD677A468665DAA45ECAF74663E5B04FE4917C |
| SSDEEP: | 3:N1KaKE6RFSeGETAEKGXKGWO21XyalR7LGdLcLq2LkV:CaoSeGnEdXEXyIiLcLZkV |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2972)
Reads settings of System Certificates
- chrome.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=852,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D047695F52D4E5A856185BA6D38AF85B --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=852,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=6594FA022F0CF9BA49D6BA57F21202F0 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6594FA022F0CF9BA49D6BA57F21202F0 --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2976 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://download1424.mediafire.com/vgum1shaocug/c3kk08tv25nb666/FreeFileSync_10.9_macOS.zip | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=852,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=1C9CF2F27D76A879A500118763E4F912 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1C9CF2F27D76A879A500118763E4F912 --renderer-client-id=3 --mojo-platform-channel-handle=2108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=852,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2A08C6C1DA2F2C58A6B862CAD8059F91 --mojo-platform-channel-handle=2380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f3d00b0,0x6f3d00c0,0x6f3d00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=852,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4BBBD5C03D5C924048C9EC7616E10DFB --mojo-platform-channel-handle=3812 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
511
Read events
467
Write events
41
Delete events
3
Modification events
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2972-13195004872409000 |
Value: 259 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2972-13195004872409000 |
Value: 259 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
19
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d694553e-e257-48d2-9413-691be3b33ca8.tmp | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\256b2eaf-6052-4b31-94d4-7ee009f6b494.tmp | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2469a7.TMP | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF246a24.TMP | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF2469b7.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
30
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
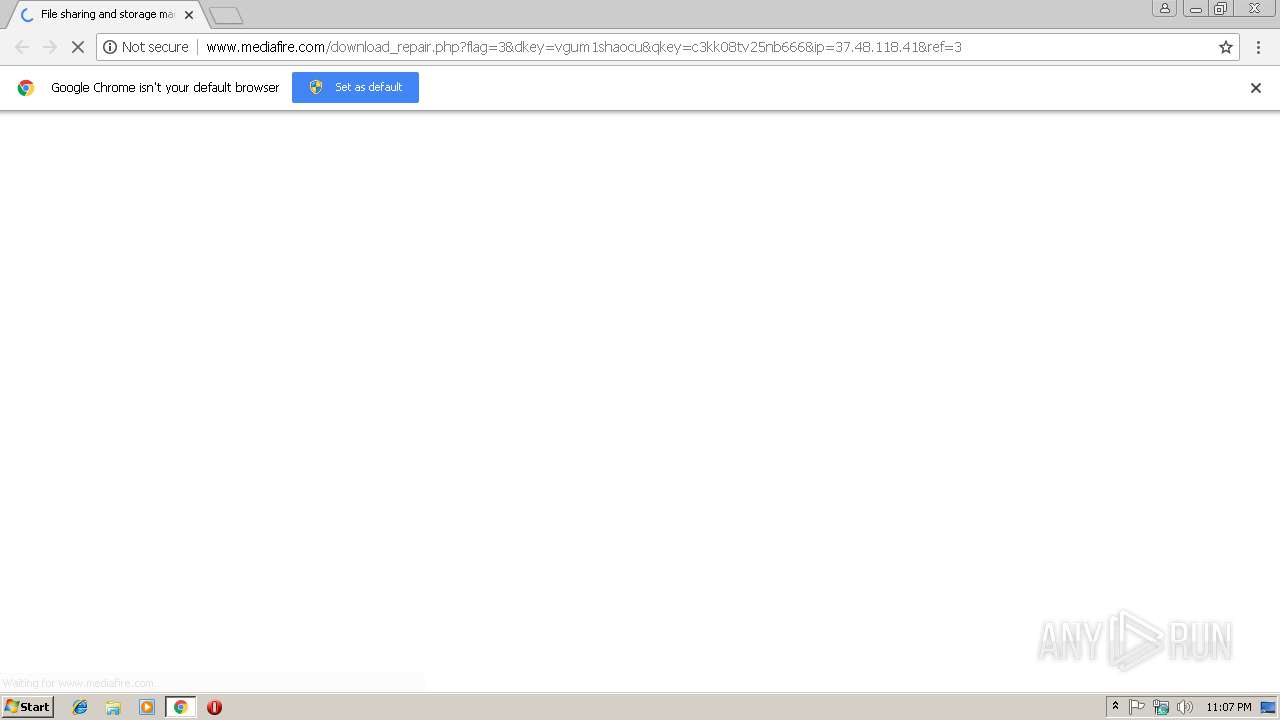
2972 | chrome.exe | GET | 302 | 205.196.123.112:80 | http://download1424.mediafire.com/vgum1shaocug/c3kk08tv25nb666/FreeFileSync_10.9_macOS.zip | US | — | — | malicious |
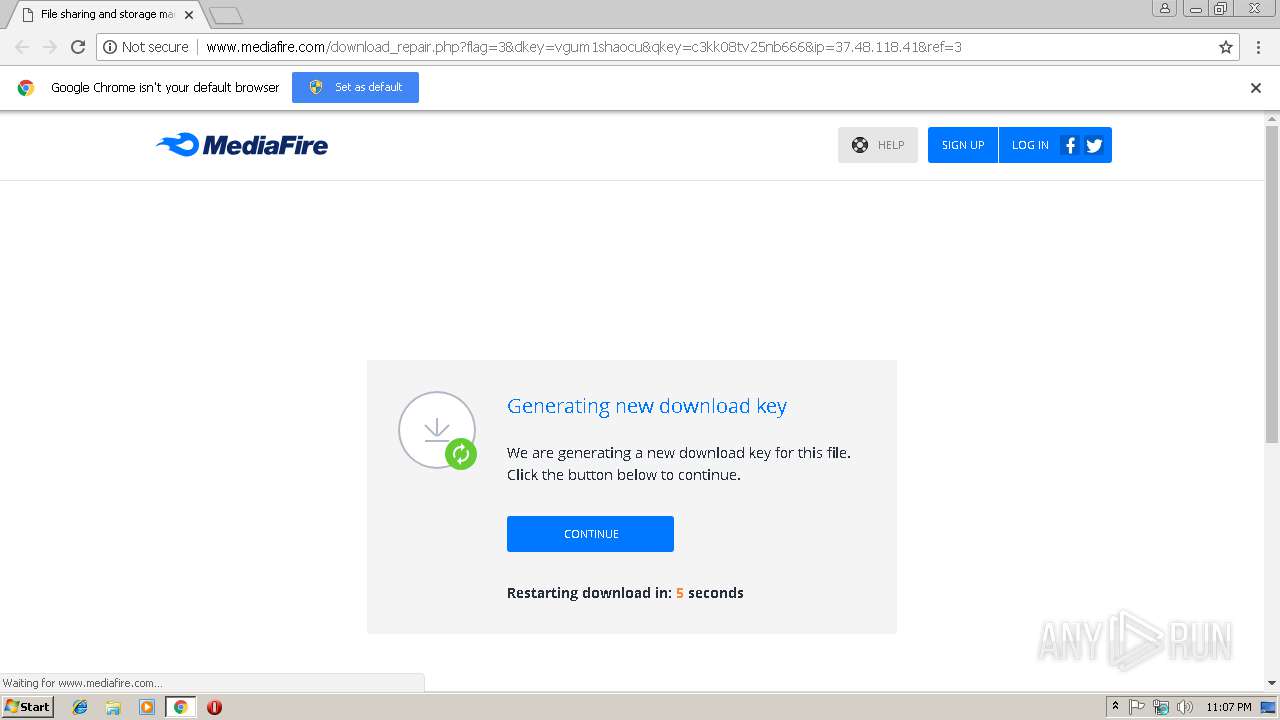
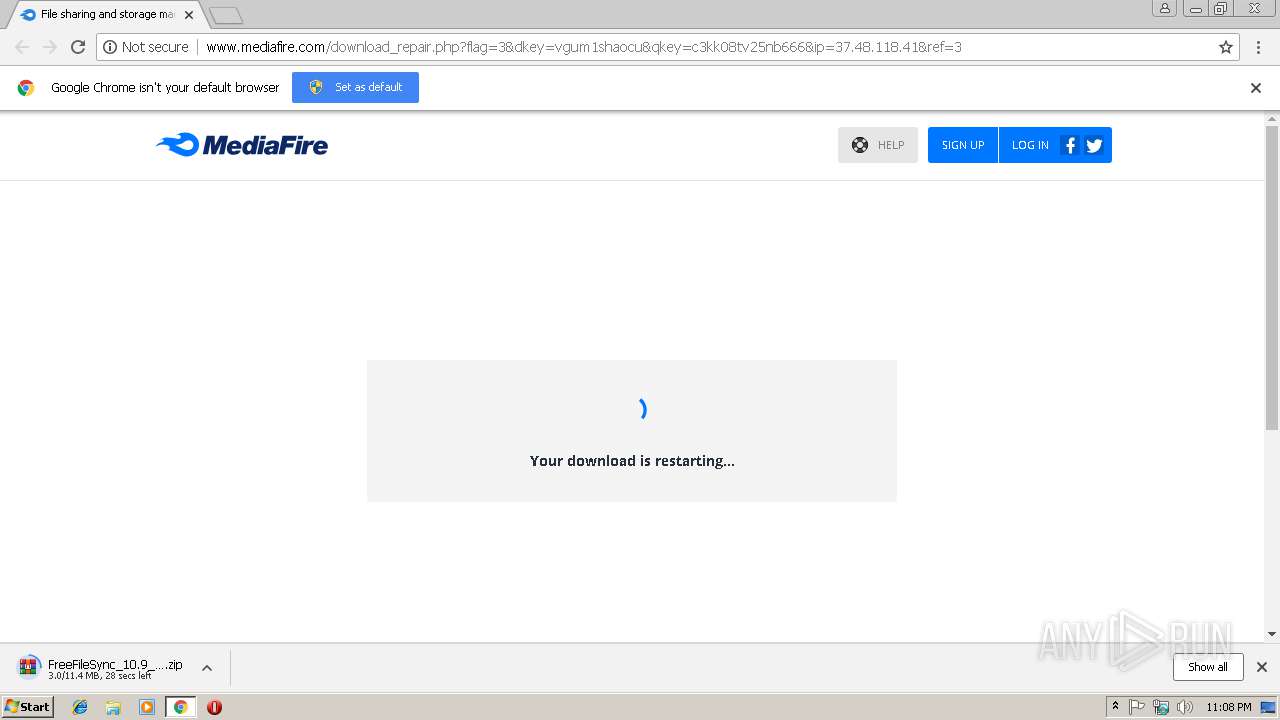
2972 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/download_repair.php?flag=3&dkey=vgum1shaocu&qkey=c3kk08tv25nb666&ip=37.48.118.41&ref=3 | US | html | 9.20 Kb | shared |
2972 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/images/icons/myfiles/default.png | US | image | 424 b | shared |
2972 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://static.mediafire.com/css/mfv3_121064.php?ver=nonssl | US | text | 61.9 Kb | shared |
2972 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://static.mediafire.com/css/mfv4_121064.php?ver=nonssl&date=2019-02-18 | US | text | 66.1 Kb | shared |
2972 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://static.mediafire.com/js/master_121064.js | US | text | 153 Kb | shared |
2972 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://static.mediafire.com/images/icons/dropdown-arrow-left-white.png | US | image | 123 b | shared |
2972 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/blank.html | US | html | 157 b | shared |
2972 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://www.google-analytics.com/r/collect?v=1&_v=j73&a=7488389&t=pageview&_s=1&dl=http%3A%2F%2Fwww.mediafire.com%2Fdownload_repair.php%3Fflag%3D3%26dkey%3Dvgum1shaocu%26qkey%3Dc3kk08tv25nb666%26ip%3D37.48.118.41%26ref%3D3&ul=en-us&de=UTF-8&dt=File%20sharing%20and%20storage%20made%20simple&sd=24-bit&sr=1280x720&vp=1264x582&je=0&_u=YEBAAEAB~&jid=1538503078&gjid=1148742362&cid=276438147.1550531275&tid=UA-829541-1&_gid=1417918299.1550531275&_r=1&cd1=unregistered&cd7=legacy&cd8=%2F10%2F20%2F50%2F100%2F&z=1714183483 | US | html | 417 b | whitelisted |
2972 | chrome.exe | GET | 200 | 172.217.21.238:80 | http://translate.google.com/translate_a/element.js?cb=googleTranslateElementInit | US | text | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 205.196.123.112:80 | download1424.mediafire.com | MediaFire, LLC | US | suspicious |
2972 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 104.19.194.29:80 | www.mediafire.com | Cloudflare Inc | US | shared |
2972 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 216.58.208.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 172.217.21.238:80 | translate.google.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 64.233.167.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
download1424.mediafire.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
static.mediafire.com |
| shared |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |