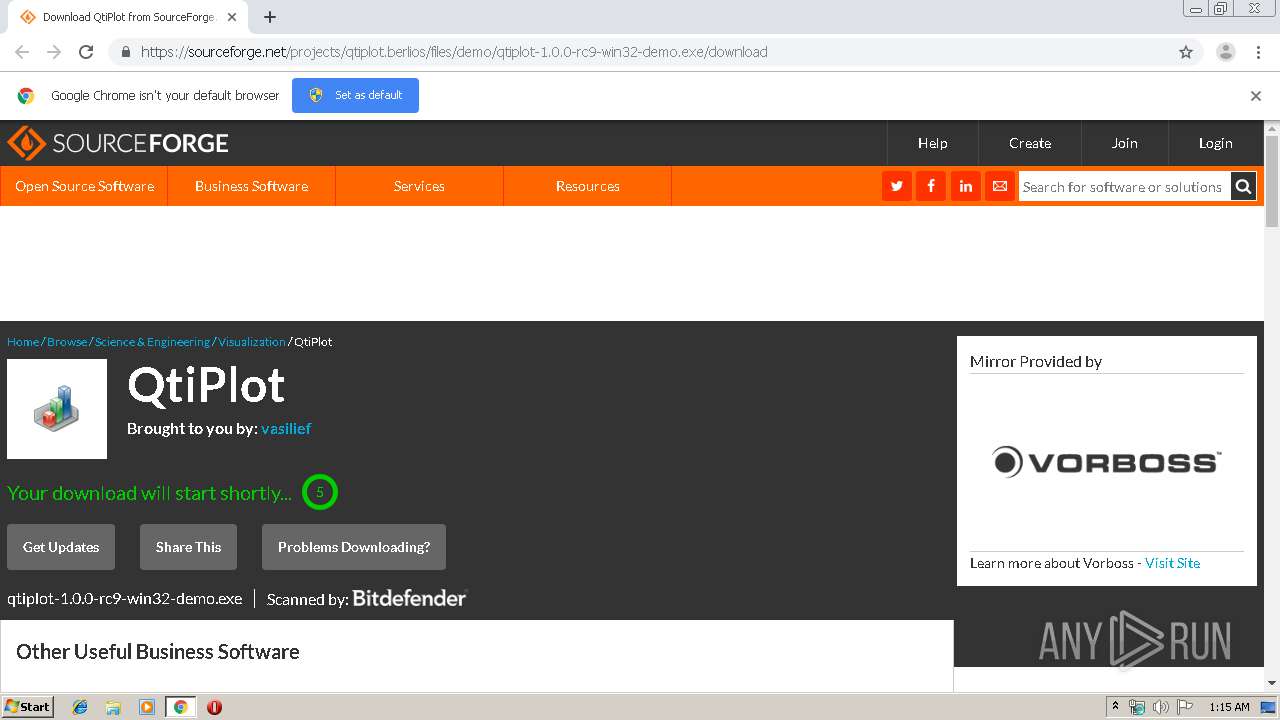
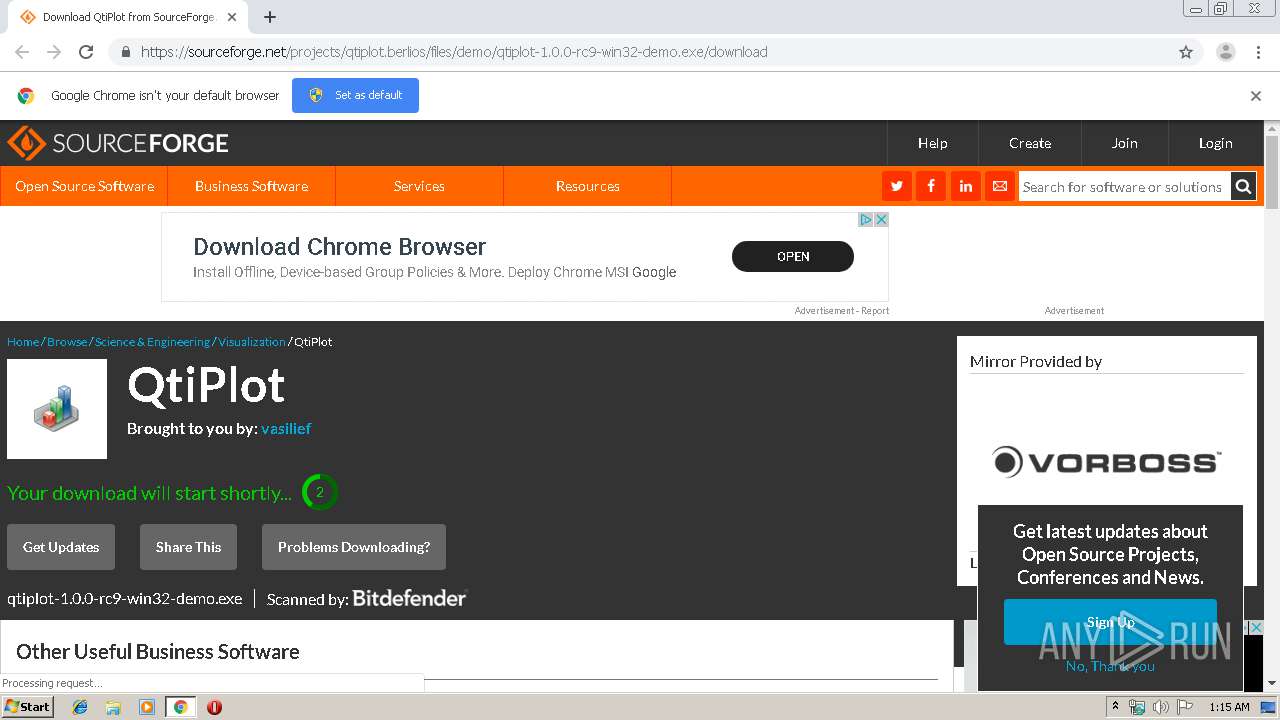
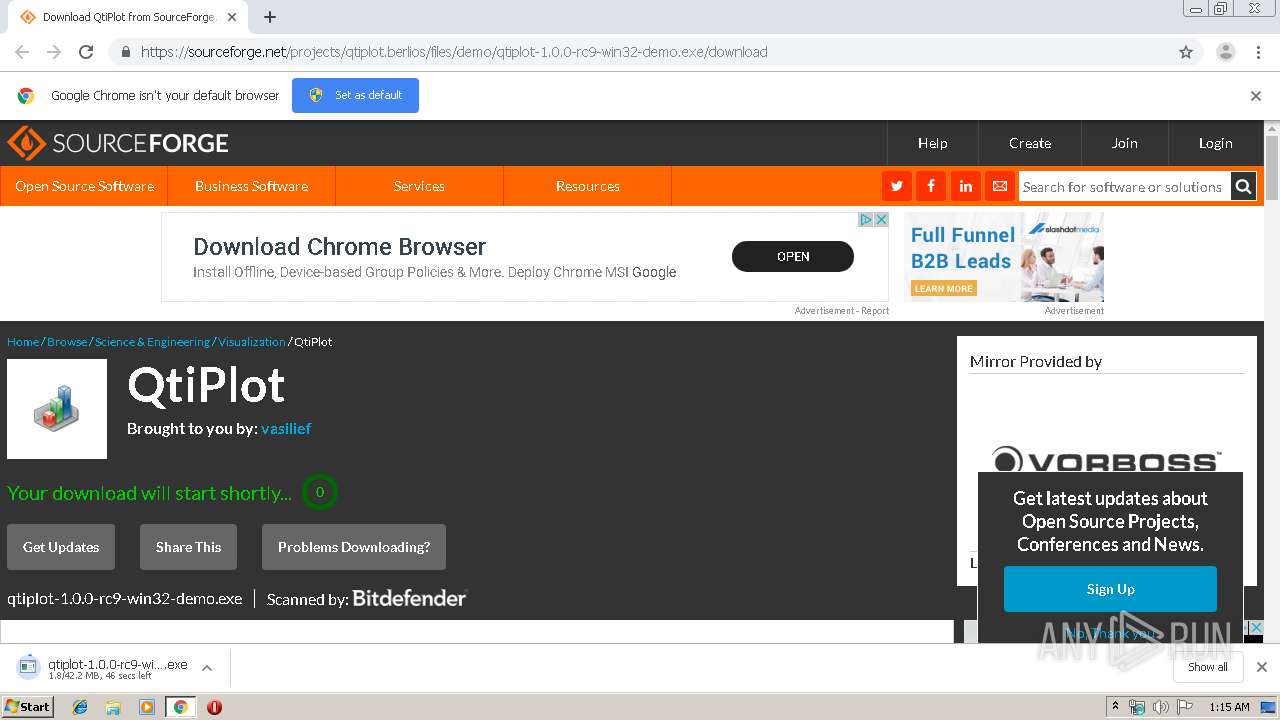
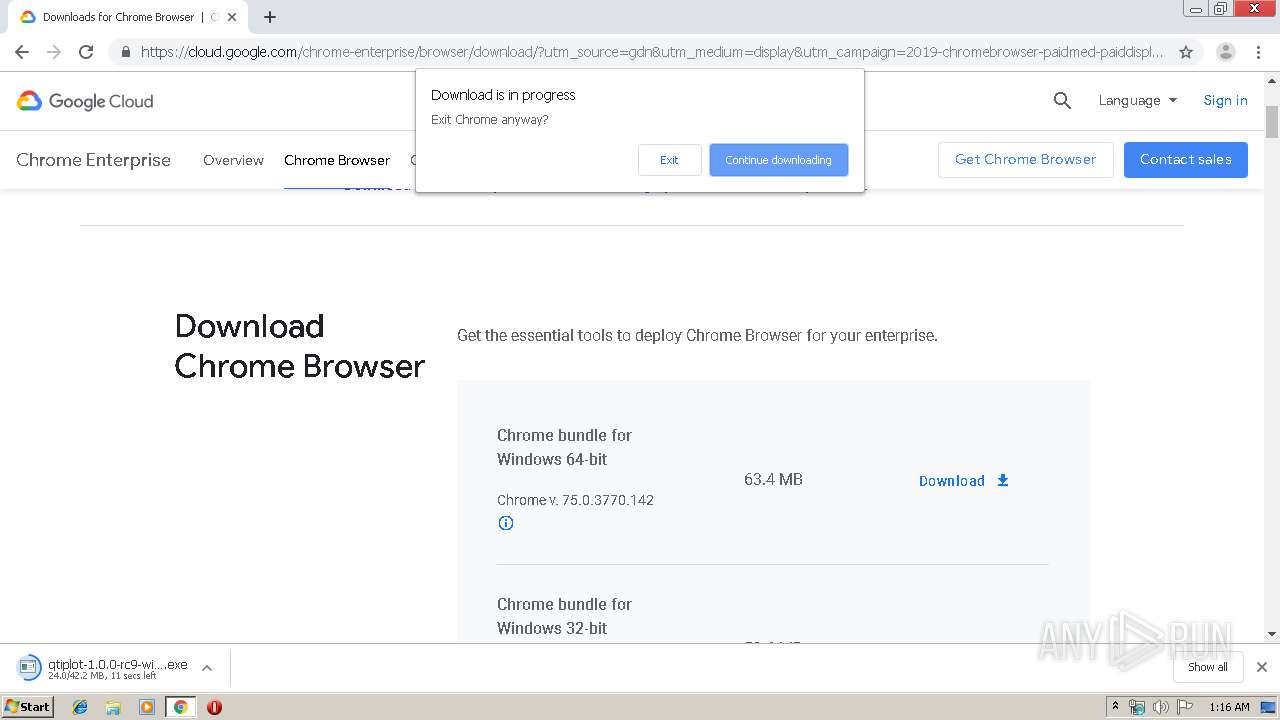
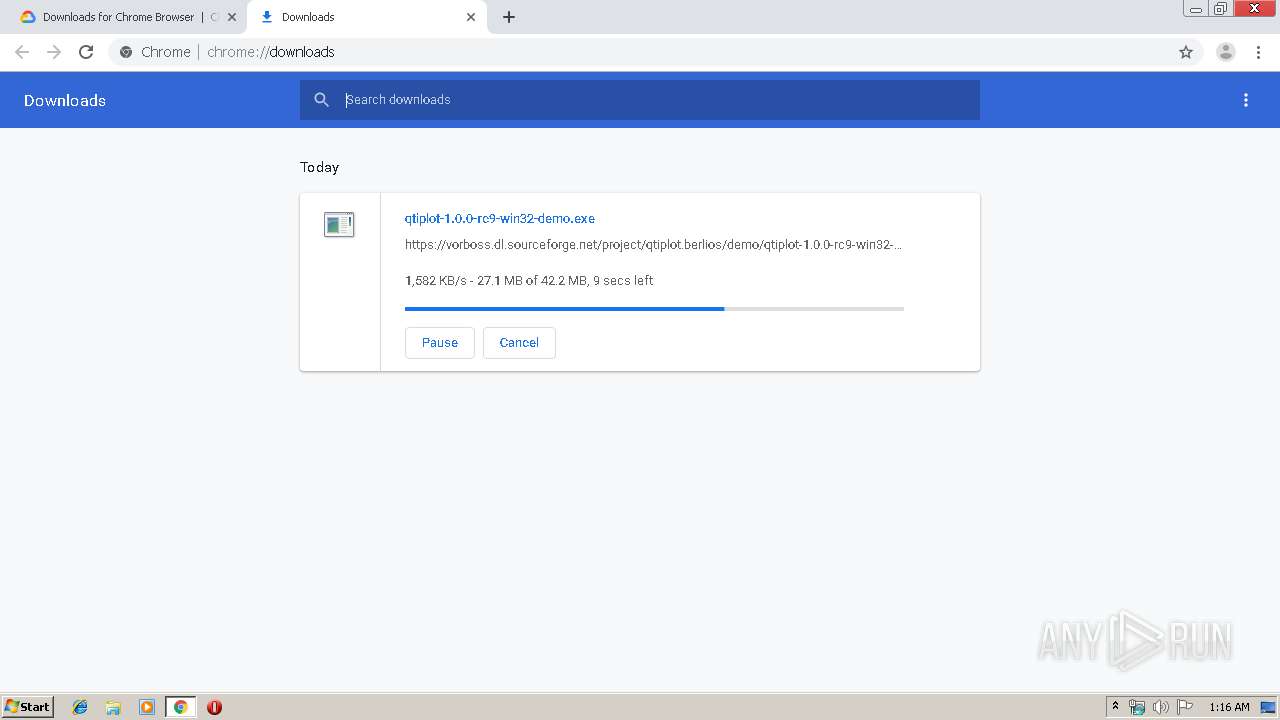
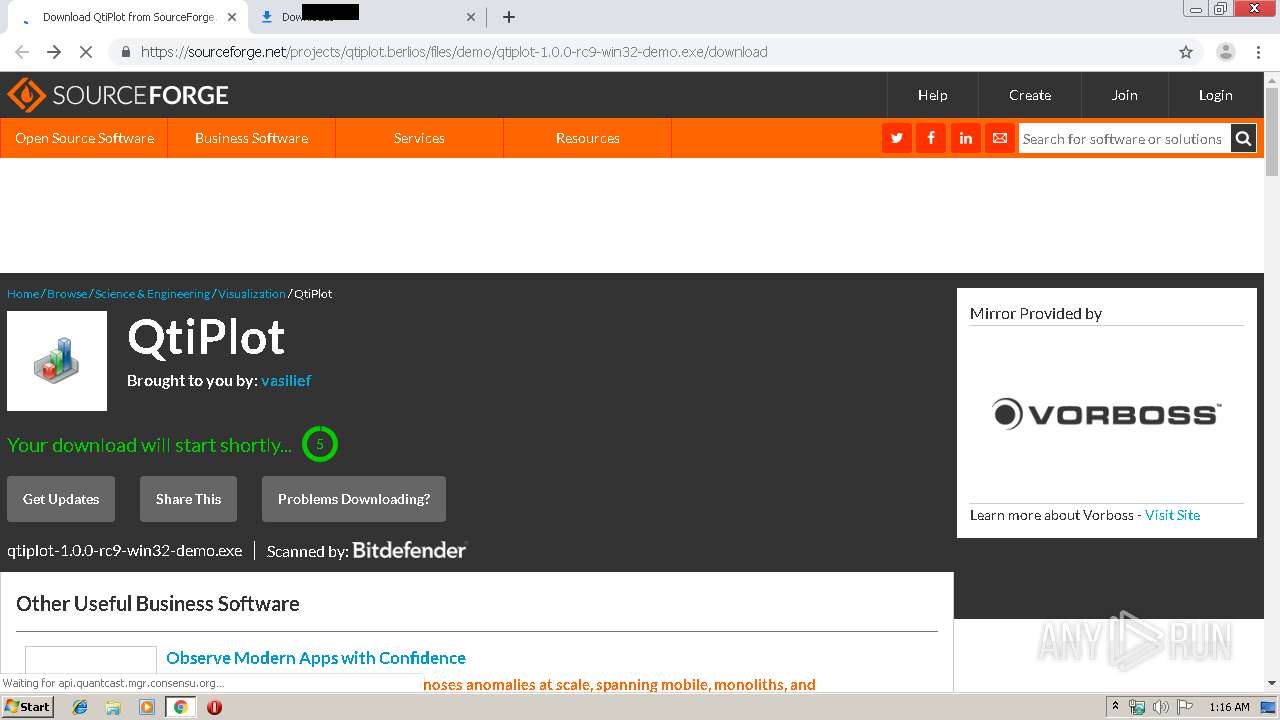
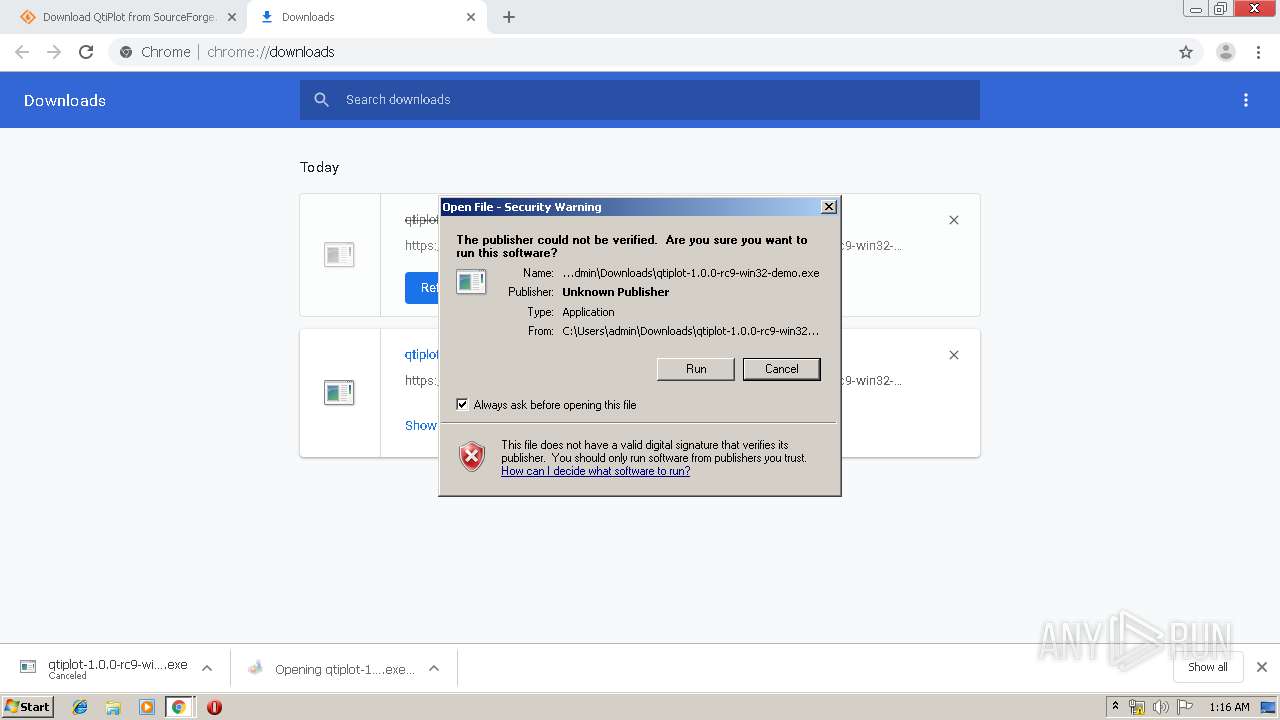
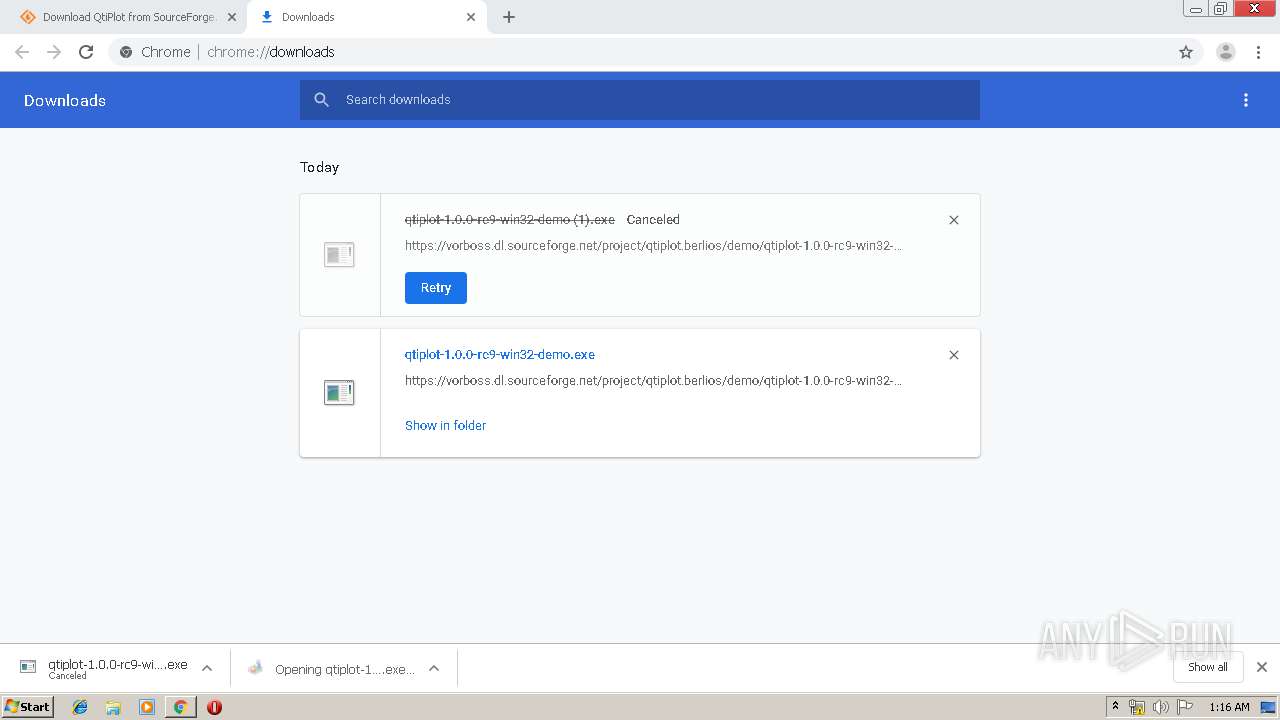
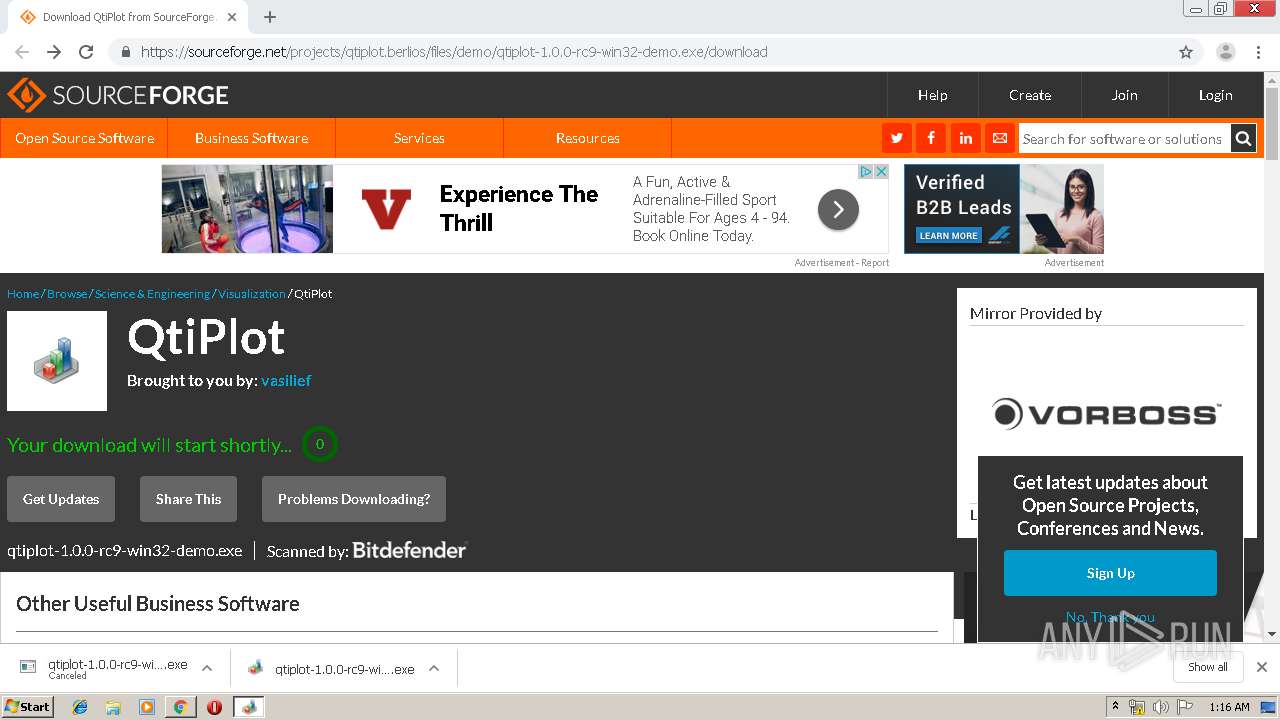
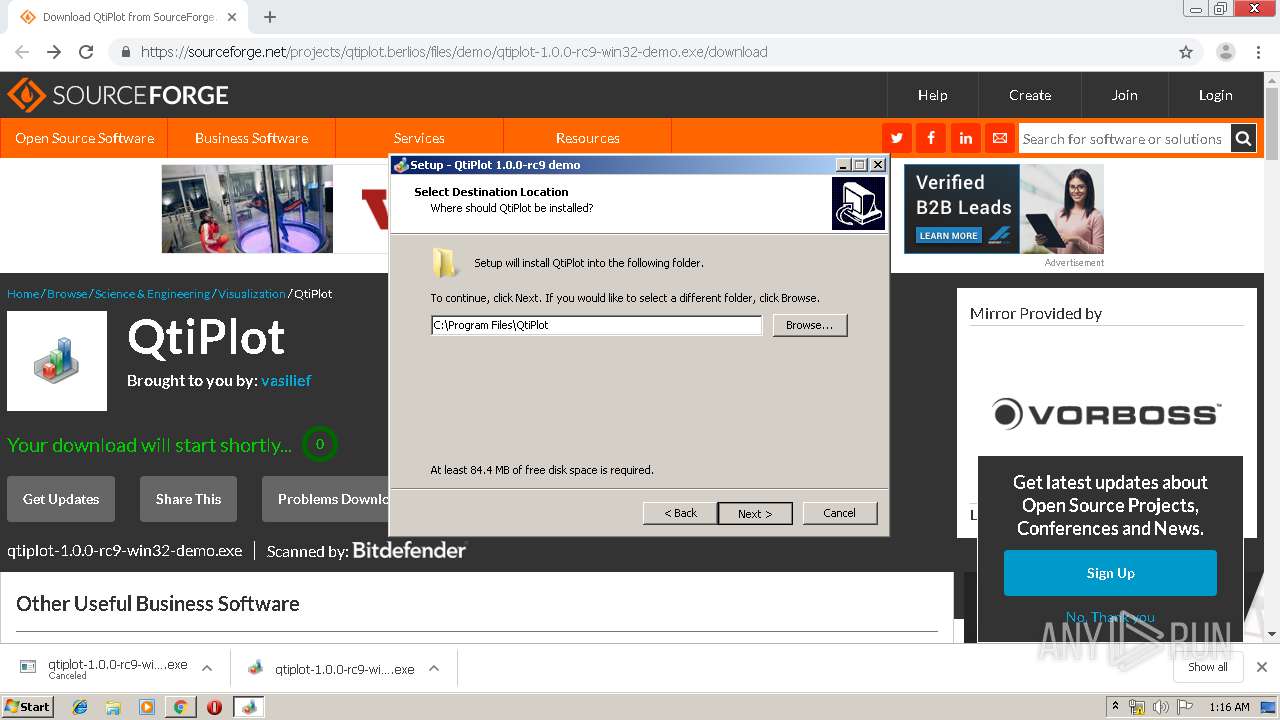
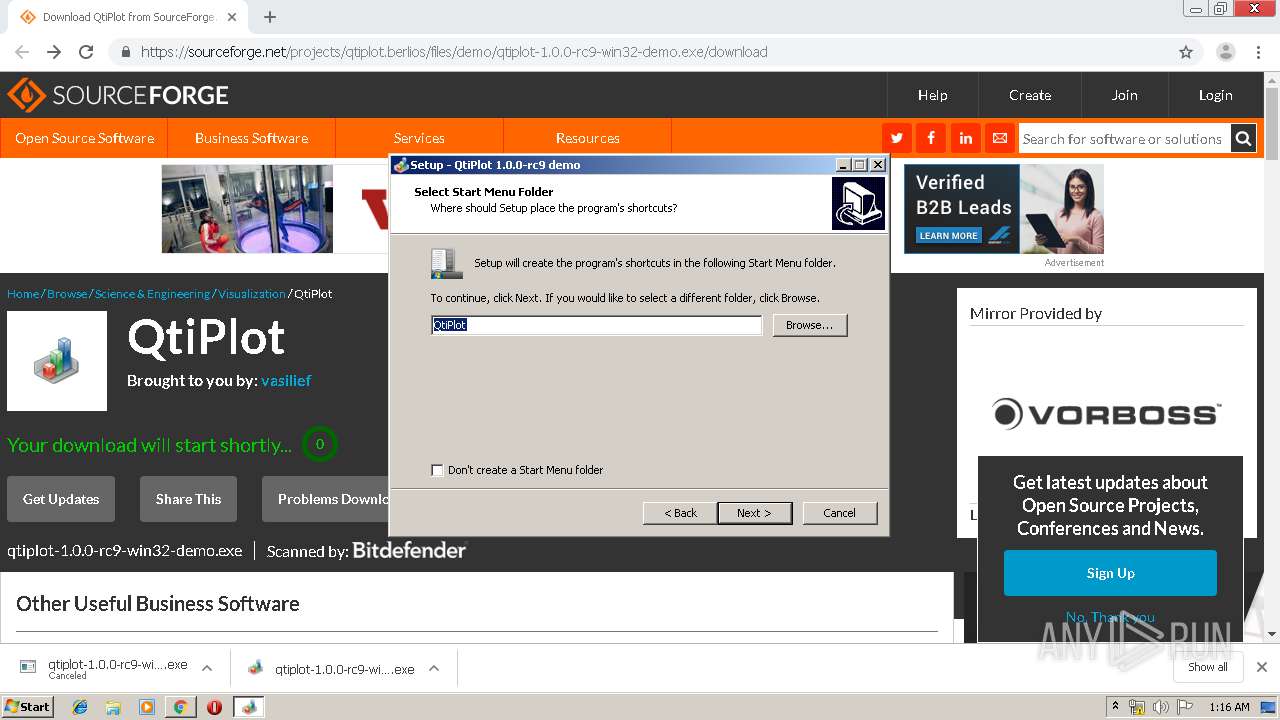
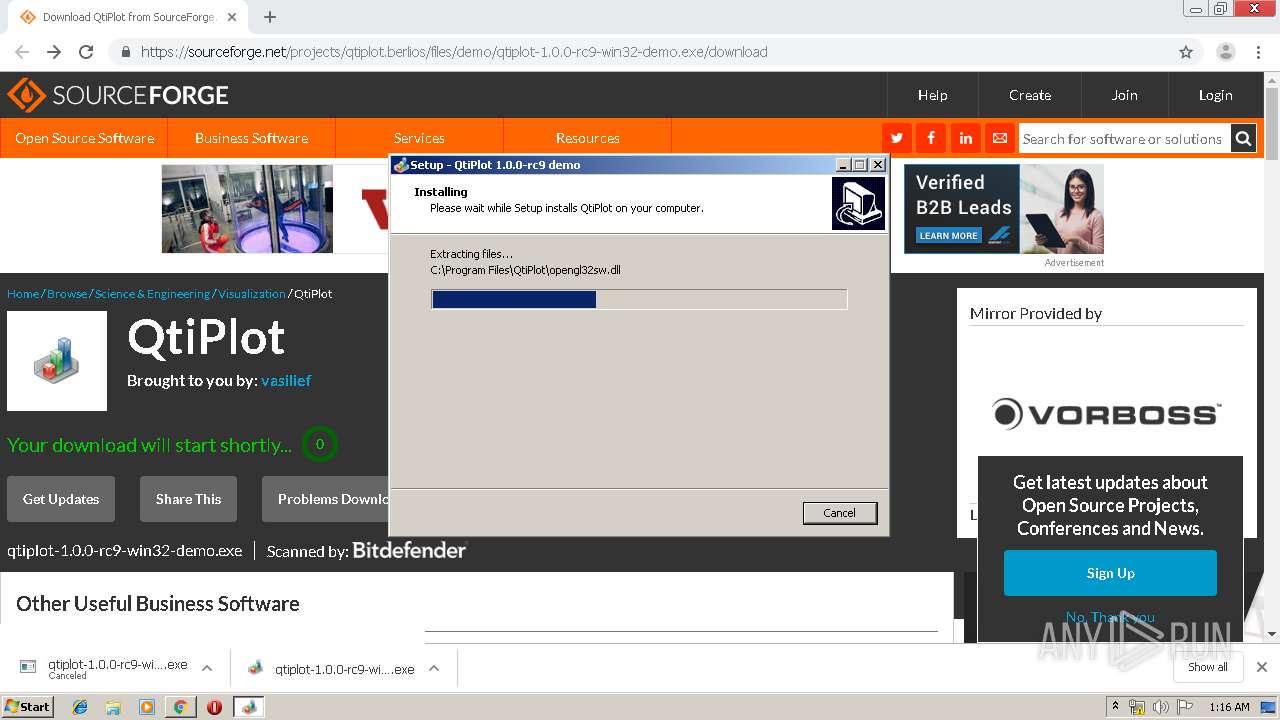
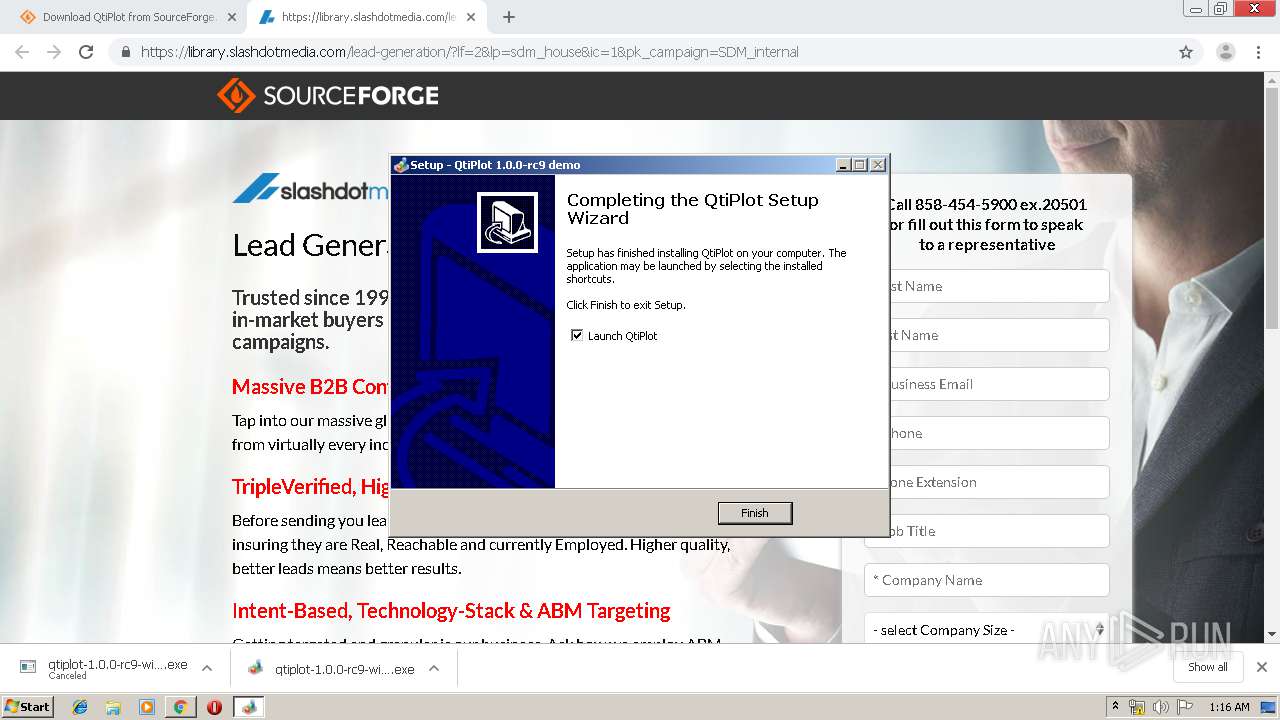
| URL: | https://sourceforge.net/projects/qtiplot.berlios/files/demo/qtiplot-1.0.0-rc9-win32-demo.exe/download |
| Full analysis: | https://app.any.run/tasks/755a1c3c-20c5-43a1-b945-1ebb18e97b23 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 00:15:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1A10CCFA28F314EA82482B1CE3B205FE |
| SHA1: | C2D2196703F2EBF6168AA6FAB22671E8AC7370FF |
| SHA256: | 9972192FFE940BD21683F8E6E5618BAADA0E6ED82CFA332C4A7F6AC0CC12A31C |
| SSDEEP: | 3:N8HCGSuLAuUtGUEtgoKQJmvKKIfuUh7cNuVBLz:2iGnCtGUEtgoKQJ3pfbtcNI/ |
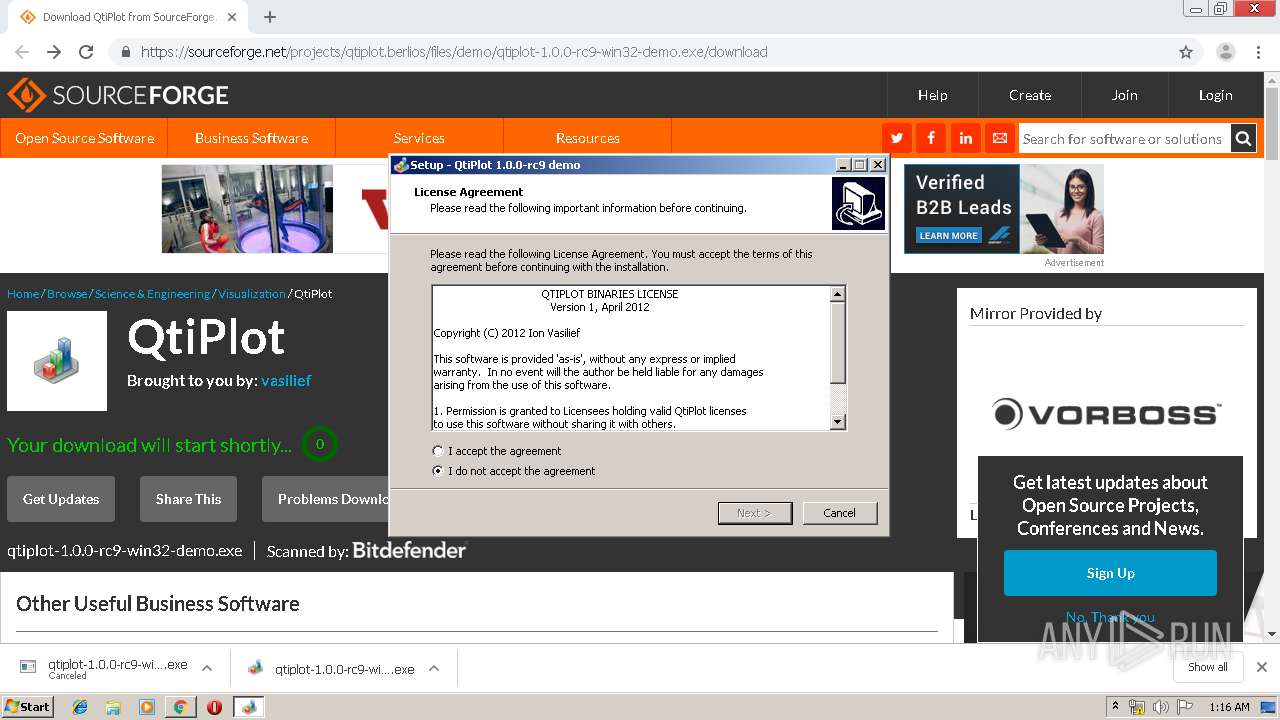
MALICIOUS
Application was dropped or rewritten from another process
- qtiplot-1.0.0-rc9-win32-demo.exe (PID: 2736)
- qtiplot.exe (PID: 1784)
- qtiplot-1.0.0-rc9-win32-demo.exe (PID: 3800)
Loads dropped or rewritten executable
- qtiplot.exe (PID: 1784)
SUSPICIOUS
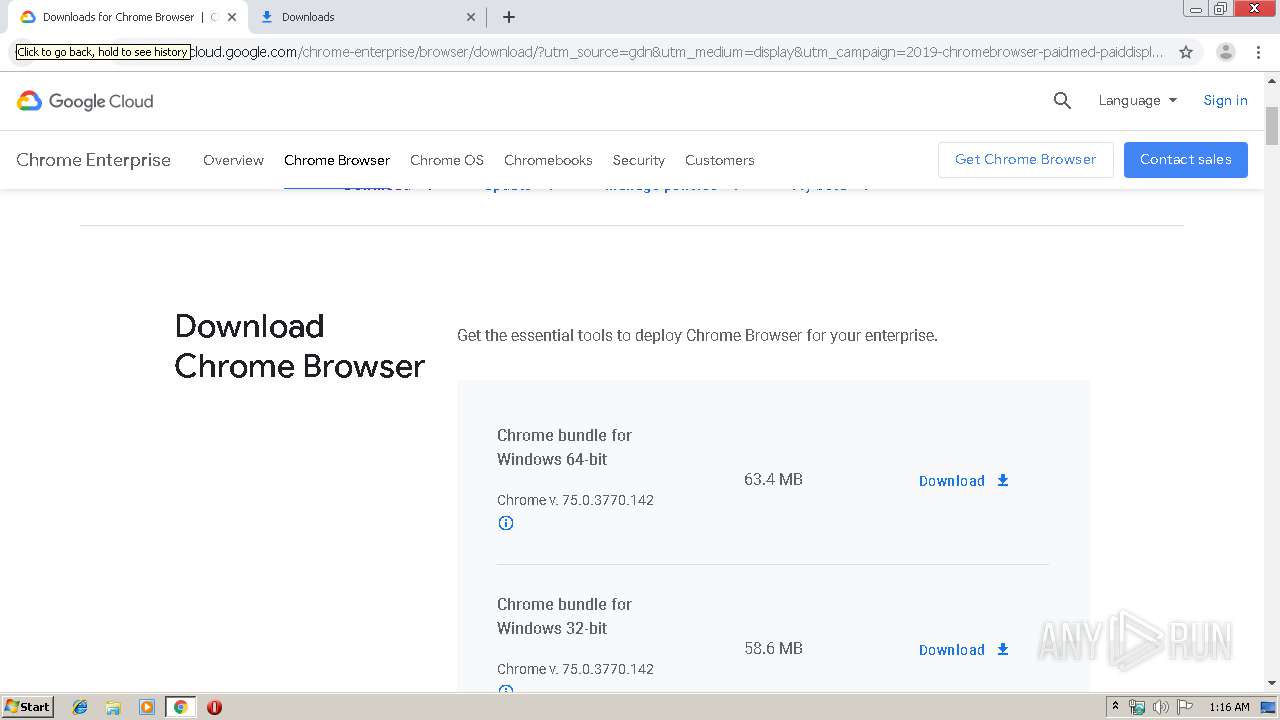
Executable content was dropped or overwritten
- chrome.exe (PID: 3020)
- chrome.exe (PID: 2376)
- qtiplot-1.0.0-rc9-win32-demo.exe (PID: 3800)
- qtiplot-1.0.0-rc9-win32-demo.exe (PID: 2736)
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3432)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3020)
Modifies the open verb of a shell class
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3432)
Reads Windows owner or organization settings
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3432)
Reads the Windows organization settings
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3432)
Creates files in the program directory
- qtiplot.exe (PID: 1784)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3020)
Application launched itself
- chrome.exe (PID: 3020)
Application was dropped or rewritten from another process
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3432)
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3980)
Creates files in the program directory
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3432)
Creates a software uninstall entry
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3432)
Dropped object may contain Bitcoin addresses
- qtiplot-1.0.0-rc9-win32-demo.tmp (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
39
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12135251056427190879 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\QtiPlot\qtiplot.exe" | C:\Program Files\QtiPlot\qtiplot.exe | — | qtiplot-1.0.0-rc9-win32-demo.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4463873799472763094 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13082895797114835807 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8986378528956973500 --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1664899139747820829 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6656197080953361959 --mojo-platform-channel-handle=3484 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12908043258814756400 --mojo-platform-channel-handle=2244 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1304340929053962766 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,15290051461686486591,7189447969613444879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13472228909722862804 --mojo-platform-channel-handle=3440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 611
Read events
1 453
Write events
147
Delete events
11
Modification events
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3020-13207882528858625 |
Value: 259 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
56
Suspicious files
162
Text files
219
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\091242b6-4ff8-46ed-aecc-76c8e9f35182.tmp | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17ae12.TMP | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17ae03.TMP | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF17aedd.TMP | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
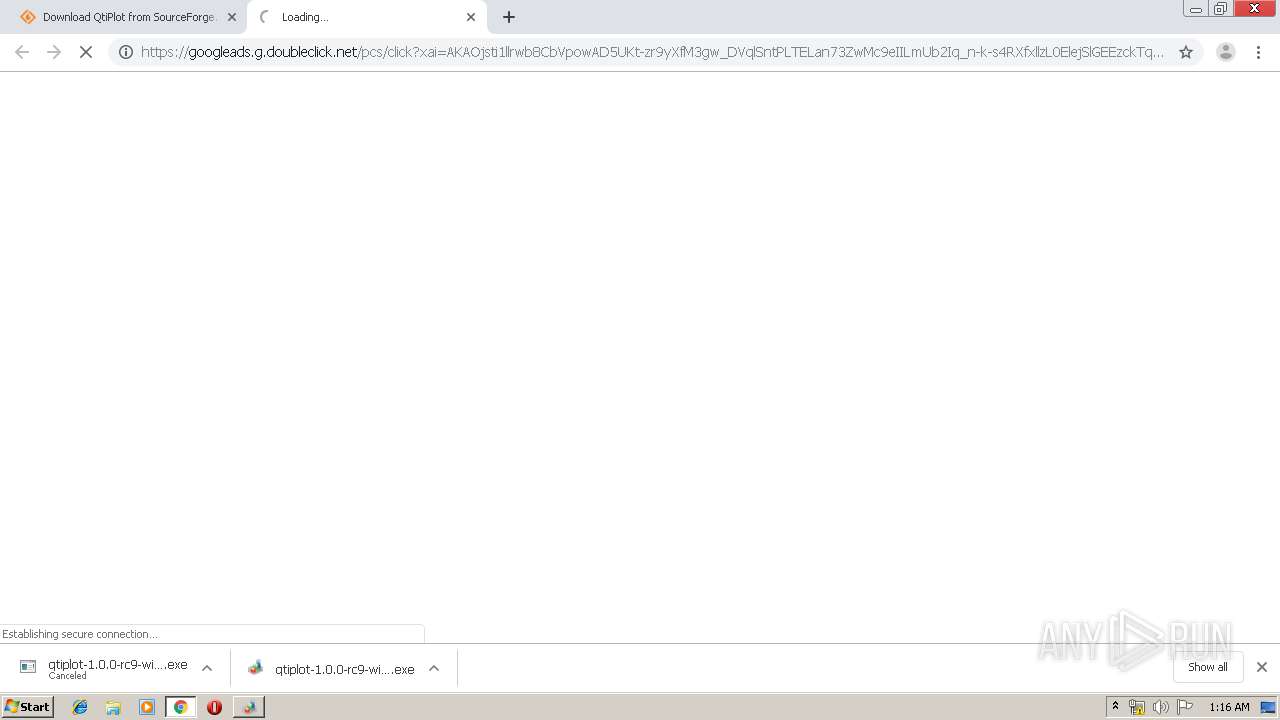
HTTP(S) requests
5
TCP/UDP connections
118
DNS requests
83
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
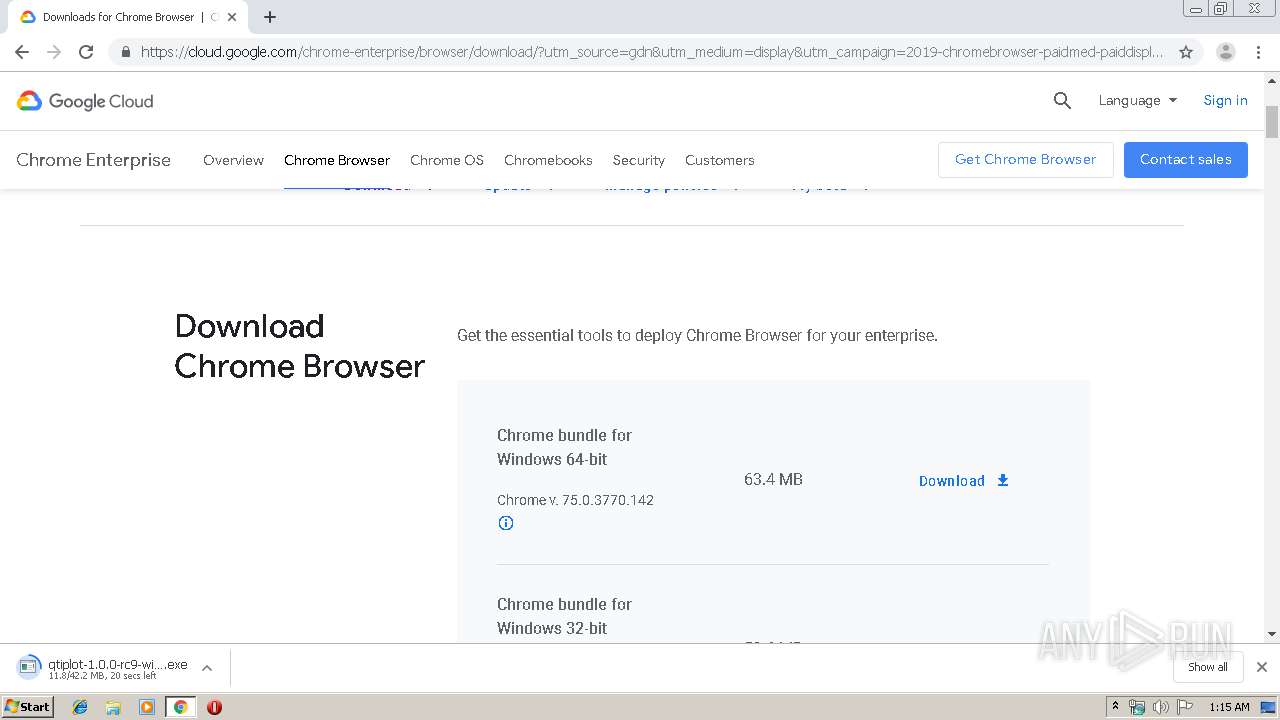
2376 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
2376 | chrome.exe | GET | 200 | 52.85.188.163:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2376 | chrome.exe | GET | 200 | 173.194.129.233:80 | http://r4---sn-q0c7rn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.153.204.5&mm=28&mn=sn-q0c7rn76&ms=nvh&mt=1563408392&mv=u&mvi=3&pl=21&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2376 | chrome.exe | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.3 Kb | whitelisted |
2376 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2376 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 104.20.116.11:443 | a.fsdn.com | Cloudflare Inc | US | shared |
2376 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 216.105.38.13:443 | sourceforge.net | American Internet Services, LLC. | US | malicious |
2376 | chrome.exe | 151.101.2.2:443 | cdn.taboola.com | Fastly | US | shared |
2376 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 2.19.43.224:443 | sb.scorecardresearch.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
sourceforge.net |
| whitelisted |
accounts.google.com |
| shared |
a.fsdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
quantcast.mgr.consensu.org |
| whitelisted |
www.google.com |
| malicious |
cdn.taboola.com |
| whitelisted |
x.ss2.us |
| whitelisted |