| download: | index.html |
| Full analysis: | https://app.any.run/tasks/504dd033-fd9d-4cdc-9e9f-aafc2f5e1892 |
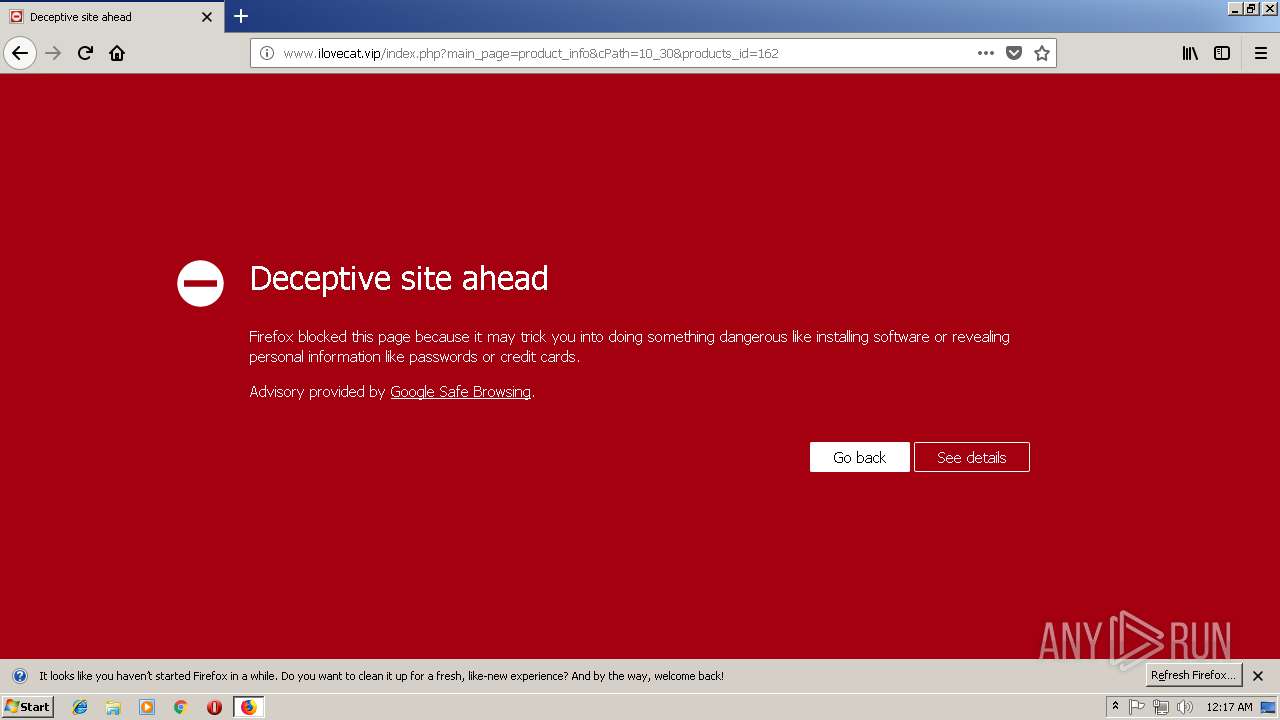
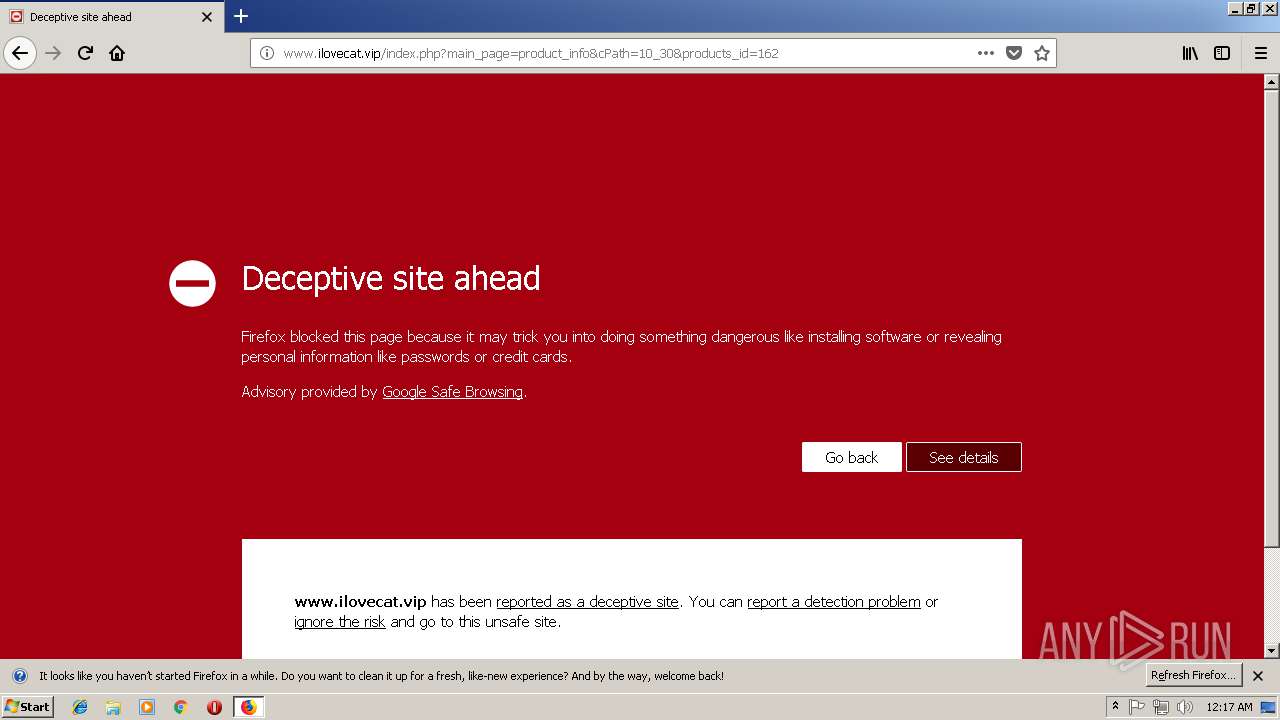
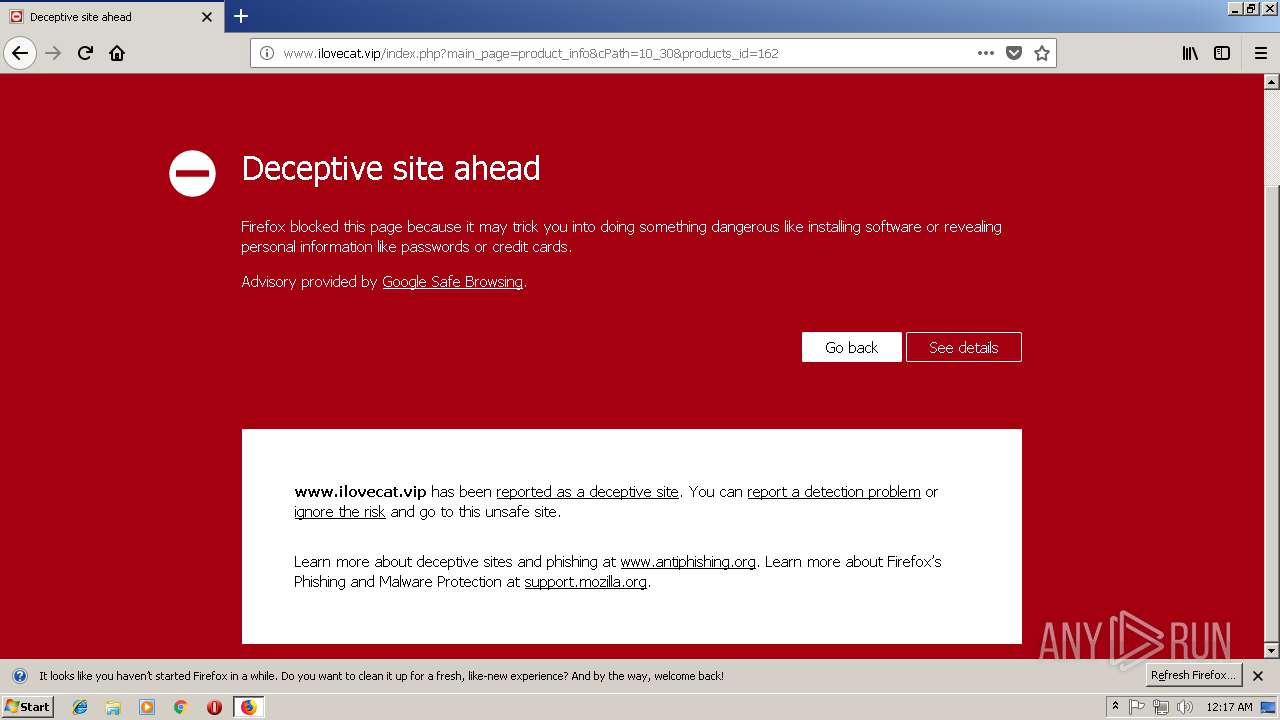
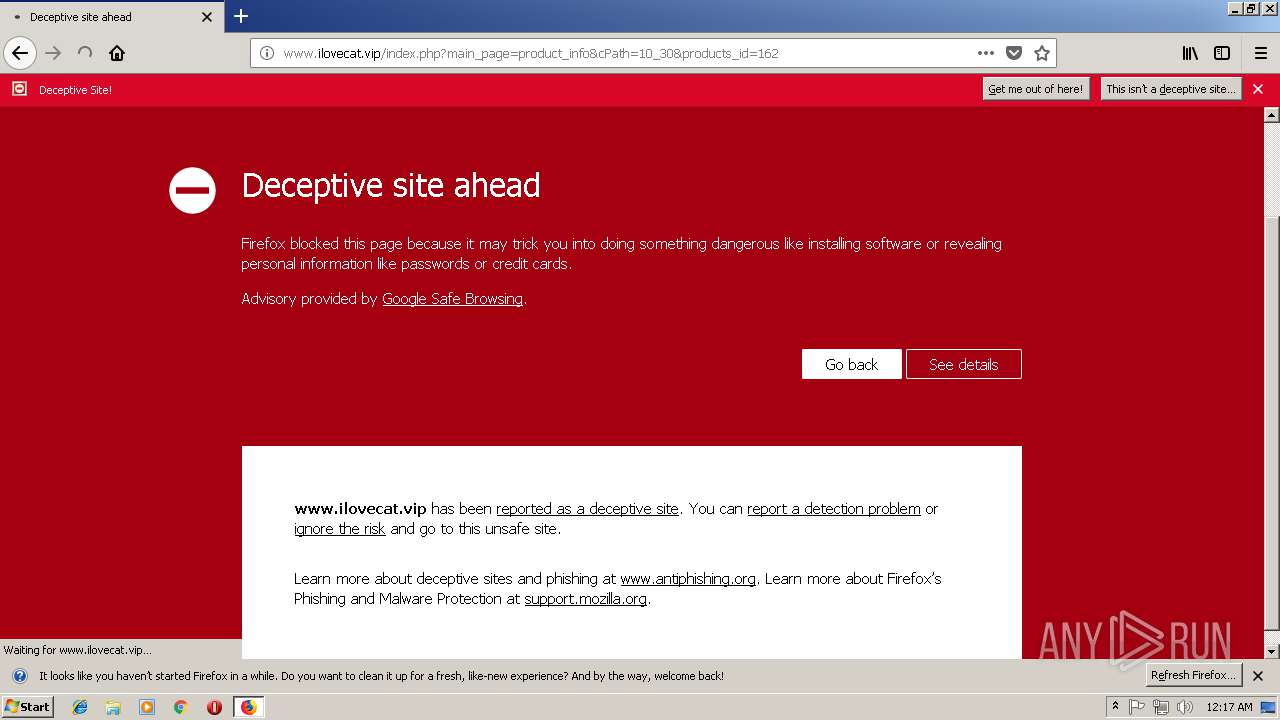
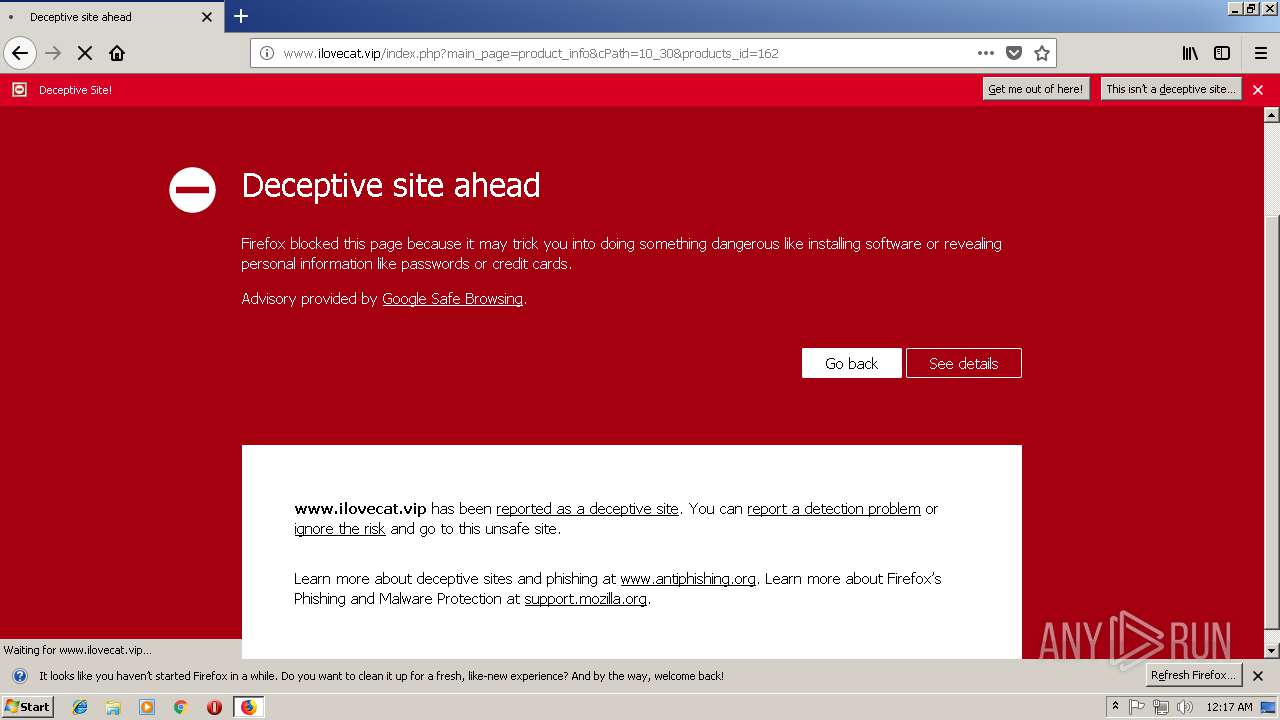
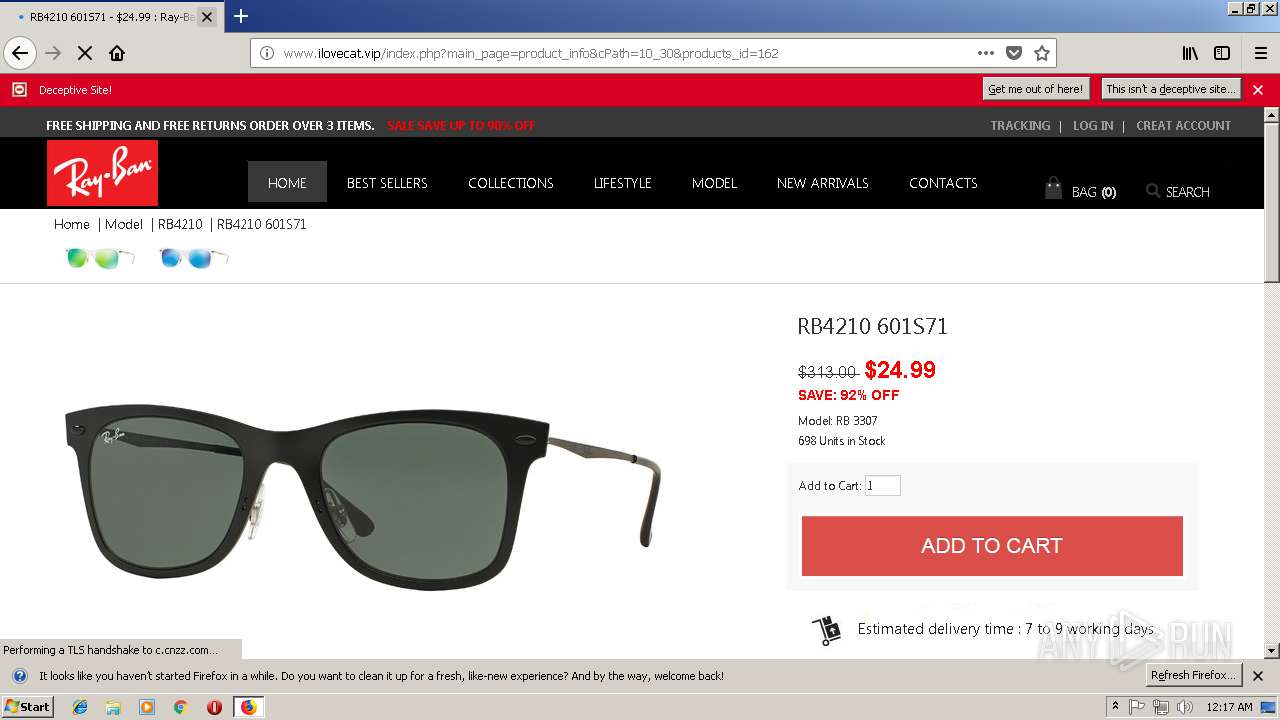
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2018, 00:14:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 522DB3CC98D6A181982C3BEE4CD41AE6 |
| SHA1: | 58C7AB3D589ADEF23FA603644AB0981A7876893E |
| SHA256: | 99668F14D146A3AADAA5B9FCABB0DAC3024E5E54B00C74C5A505871EB2A945E4 |
| SSDEEP: | 384:SSWFHHzF10D4m3PfV3l+78Q4QKDNpvfJwndyvubFx+z/Ymg9iyie72AW:SrHHzAD7/NpKdD+TYmTbe72AW |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
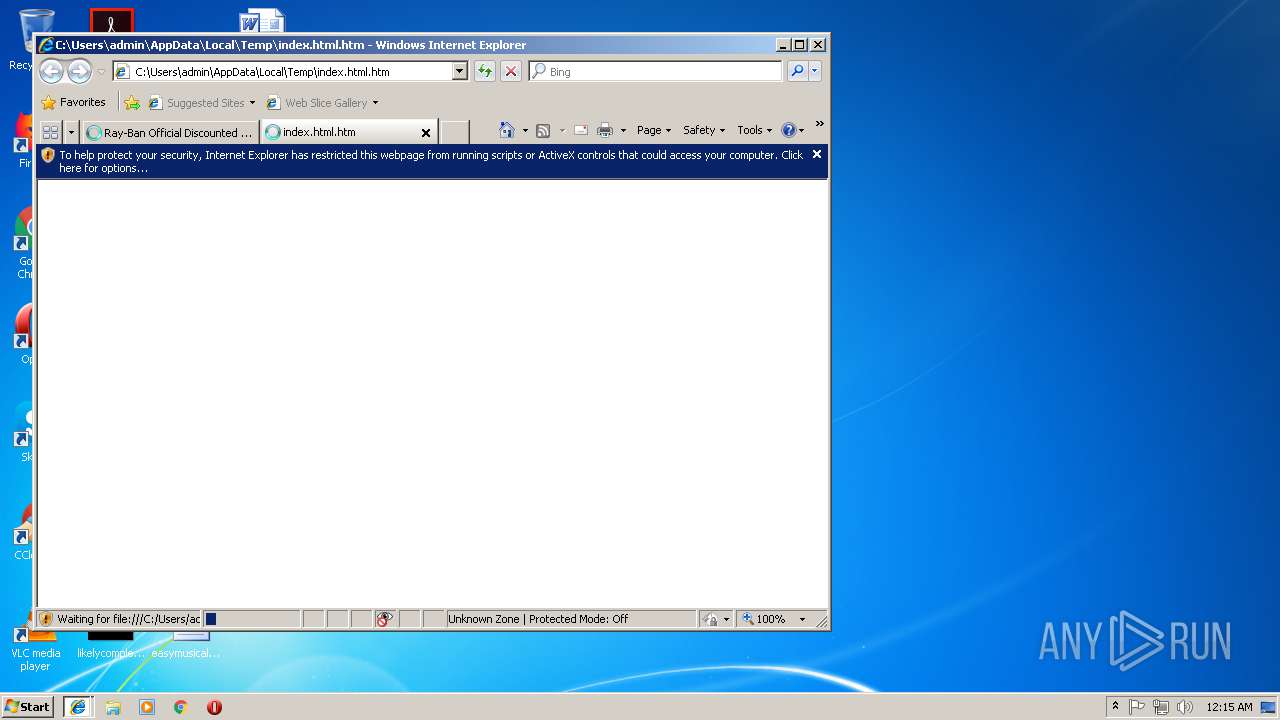
Changes internet zones settings
- iexplore.exe (PID: 920)
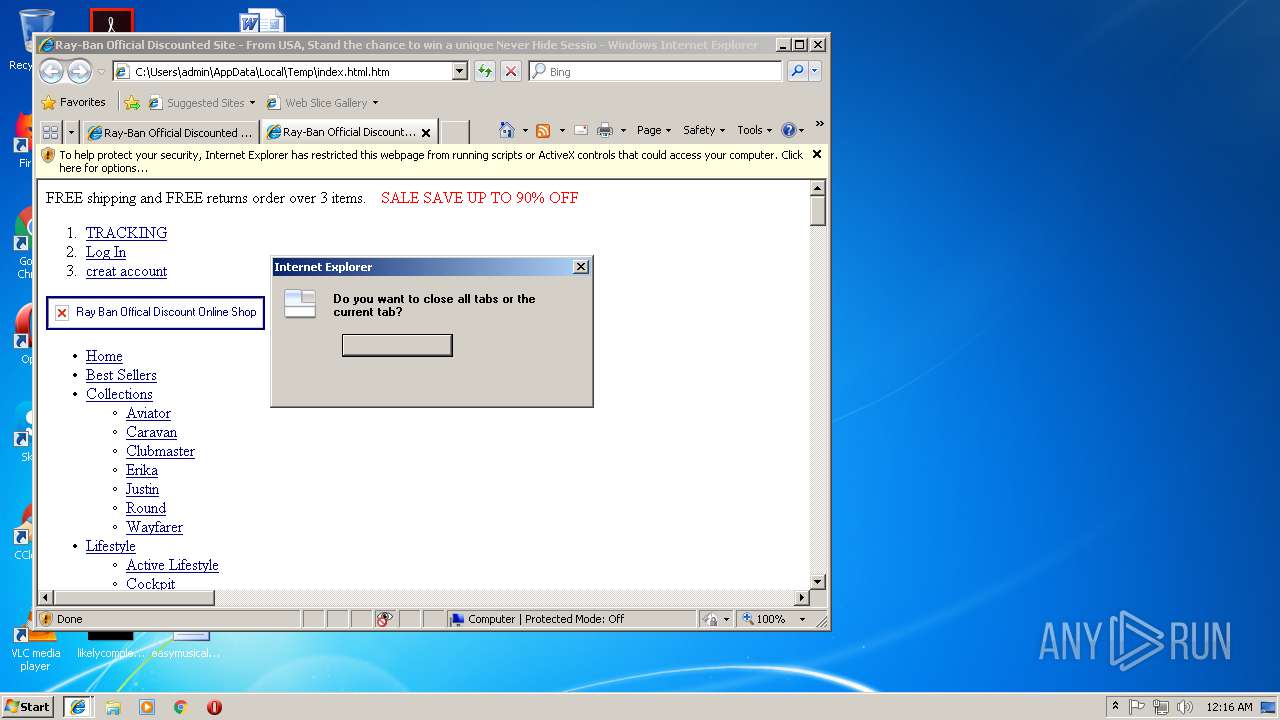
Application launched itself
- iexplore.exe (PID: 920)
- firefox.exe (PID: 1600)
Reads internet explorer settings
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 3596)
Reads Internet Cache Settings
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 3596)
Creates files in the user directory
- iexplore.exe (PID: 920)
- firefox.exe (PID: 1600)
Reads CPU info
- firefox.exe (PID: 1600)
- firefox.exe (PID: 3768)
- firefox.exe (PID: 280)
- firefox.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
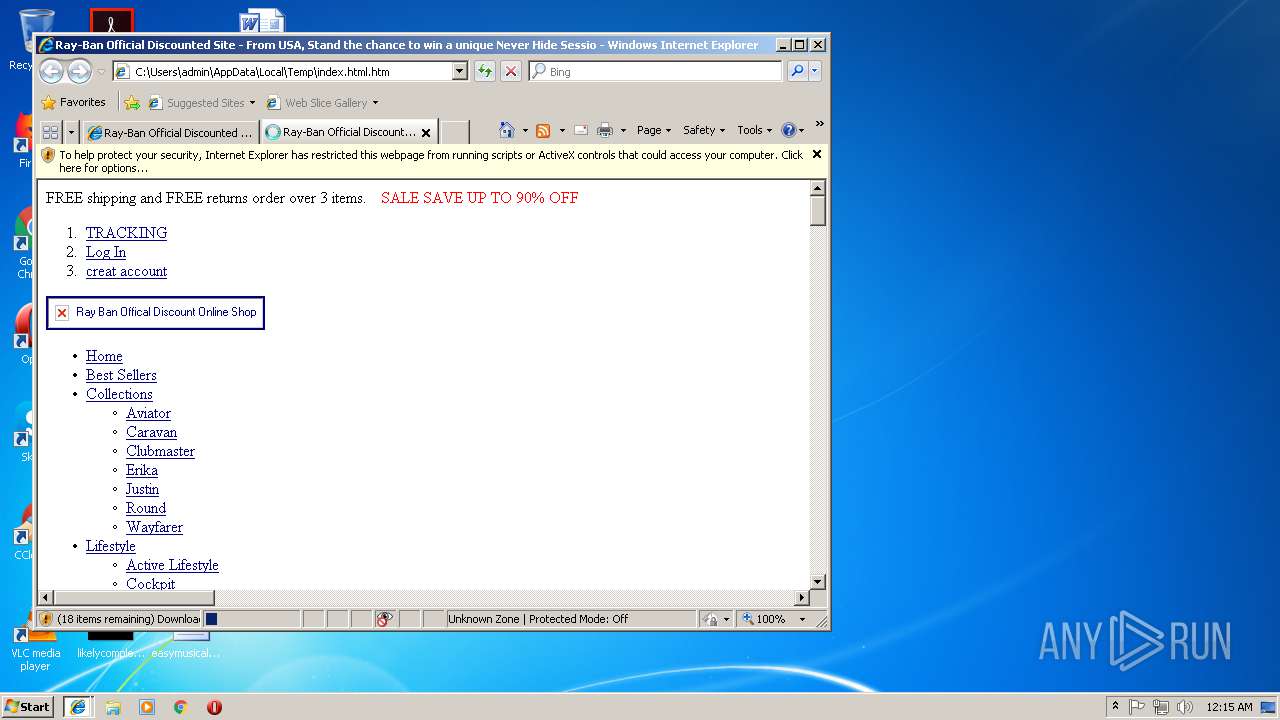
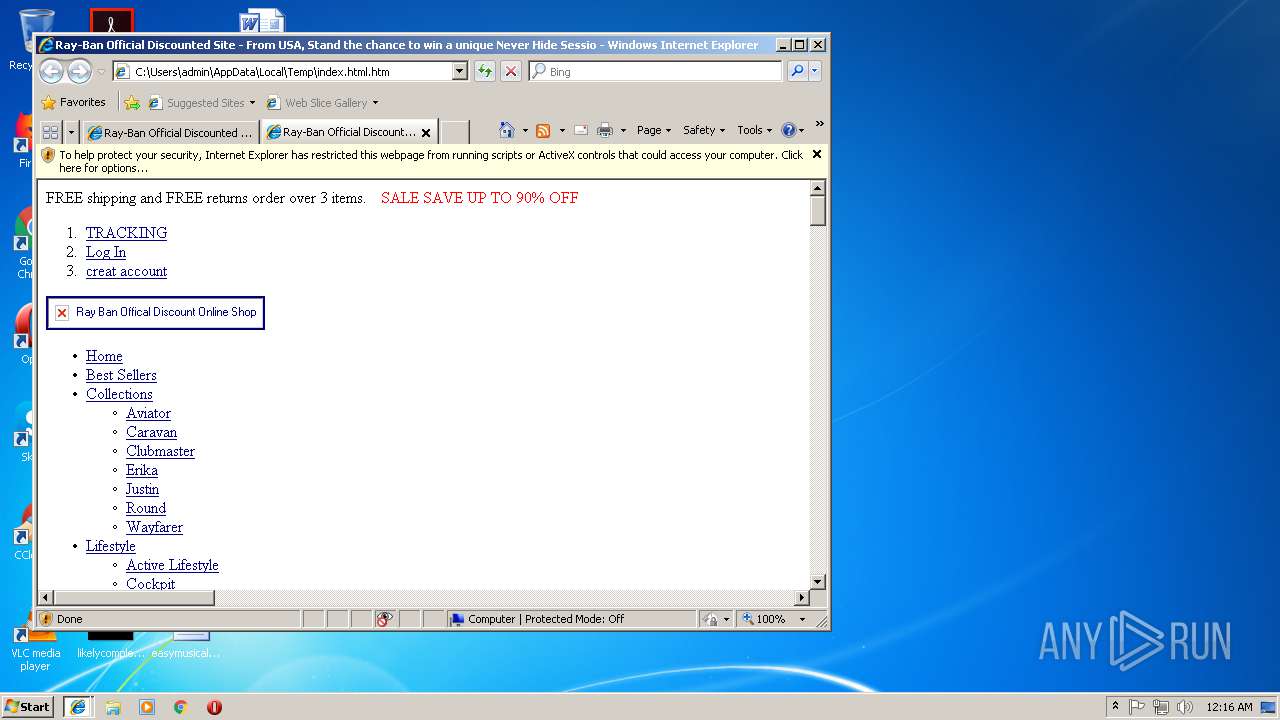
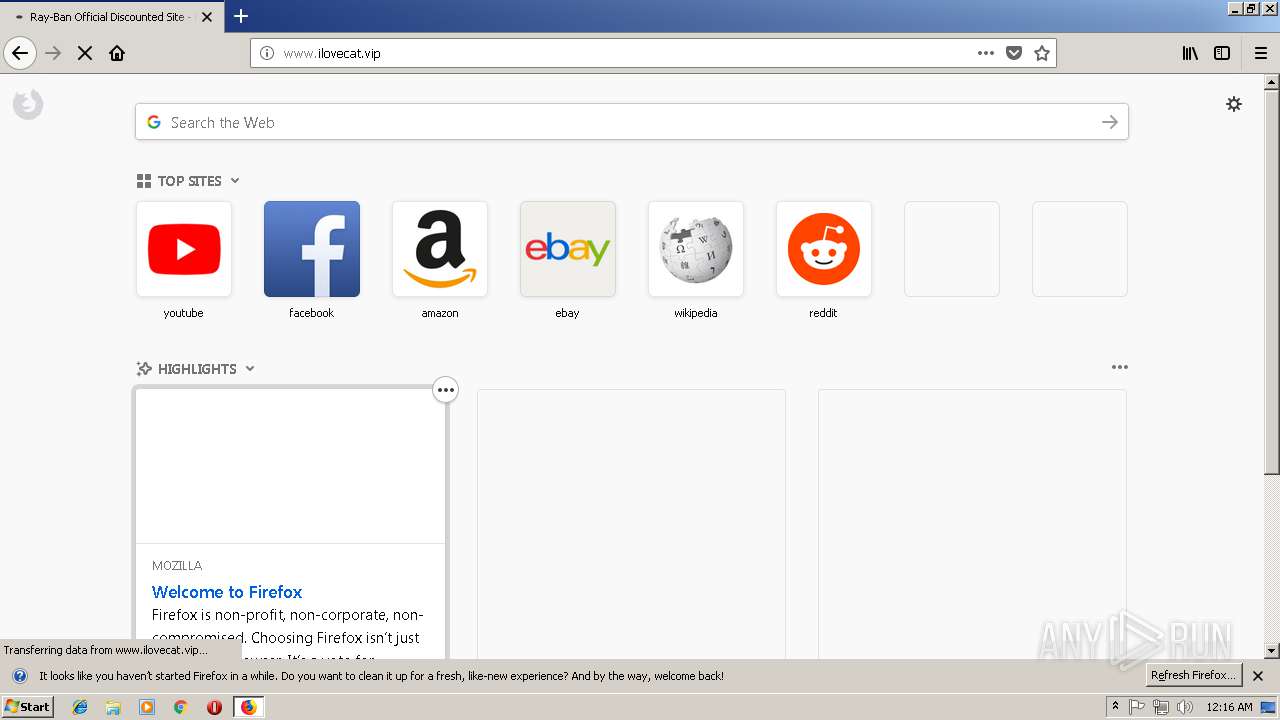
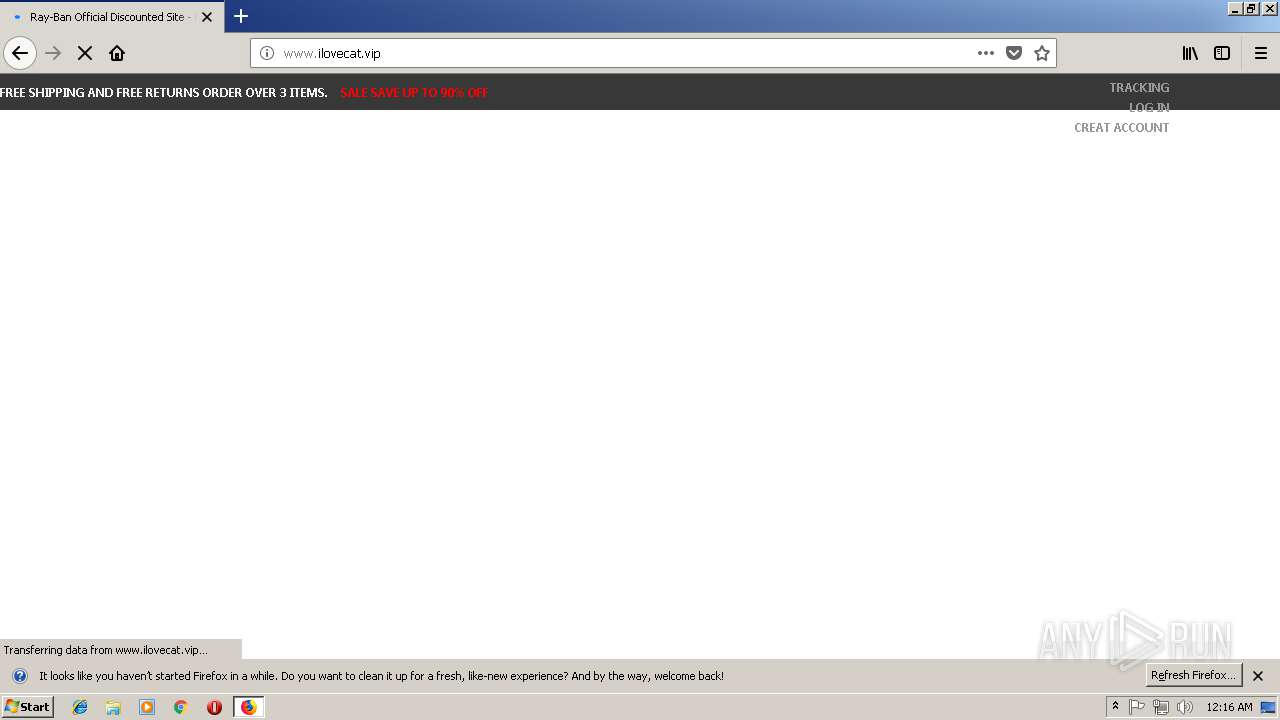
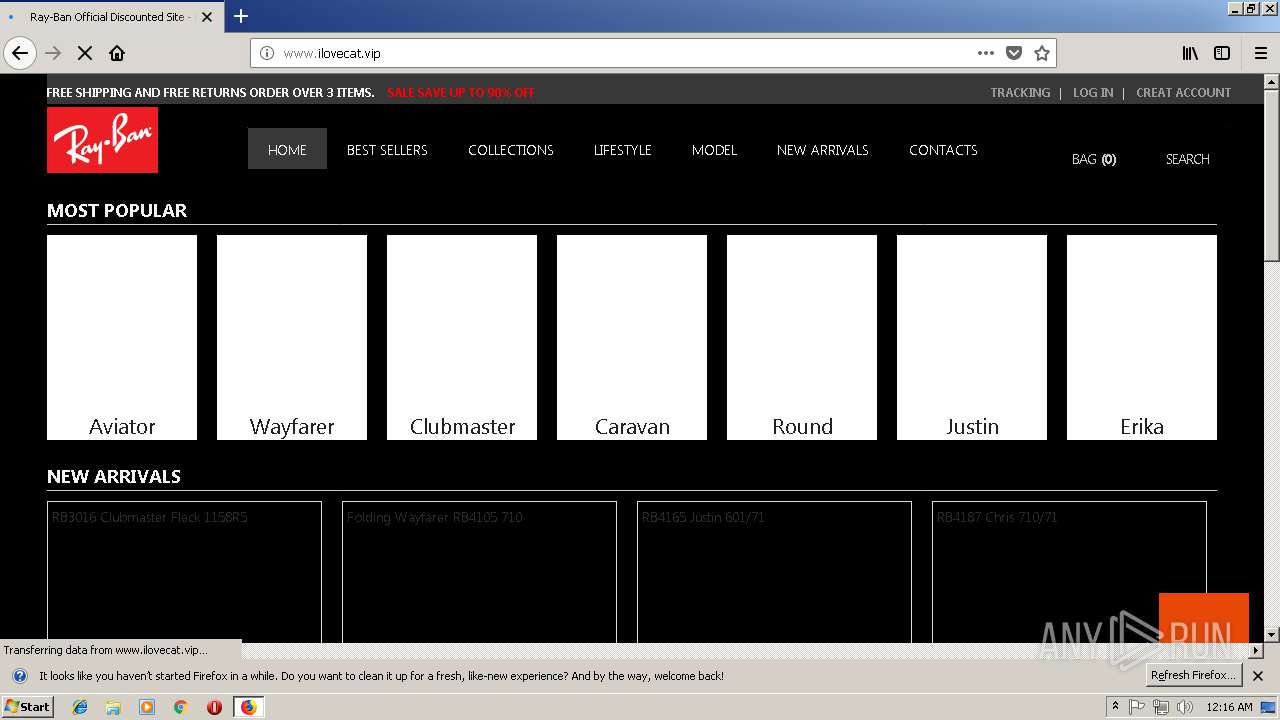
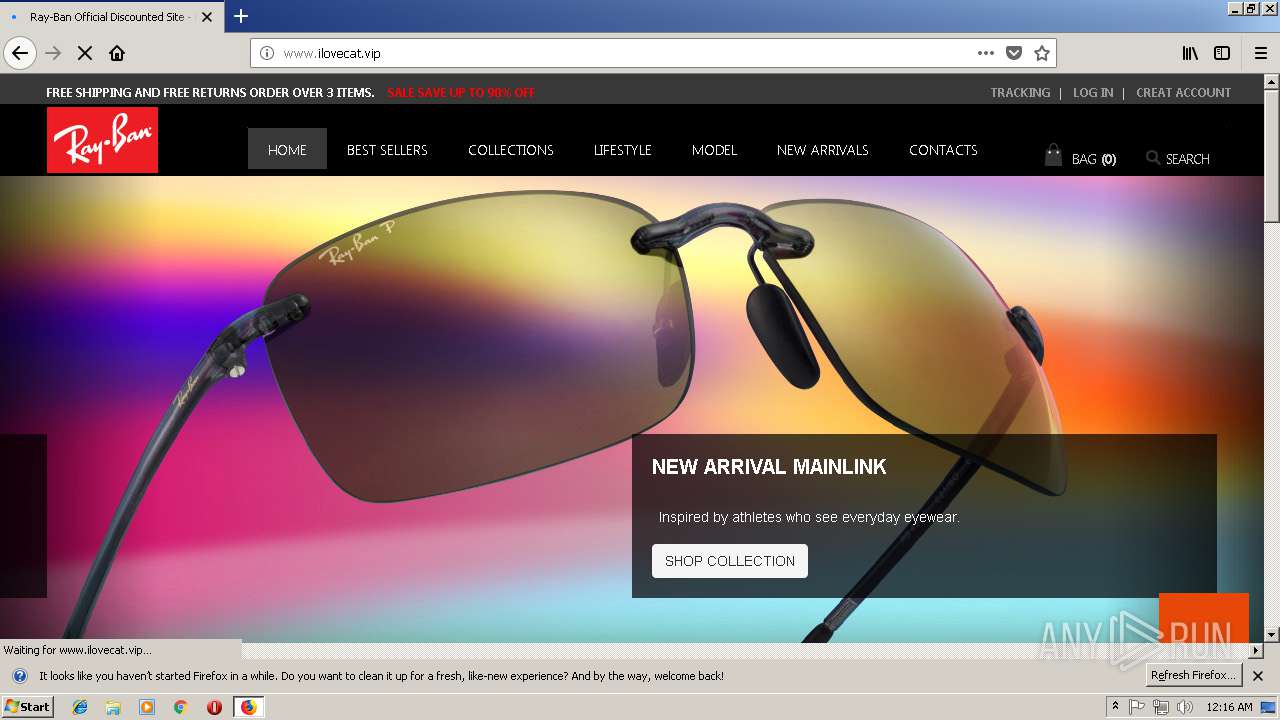
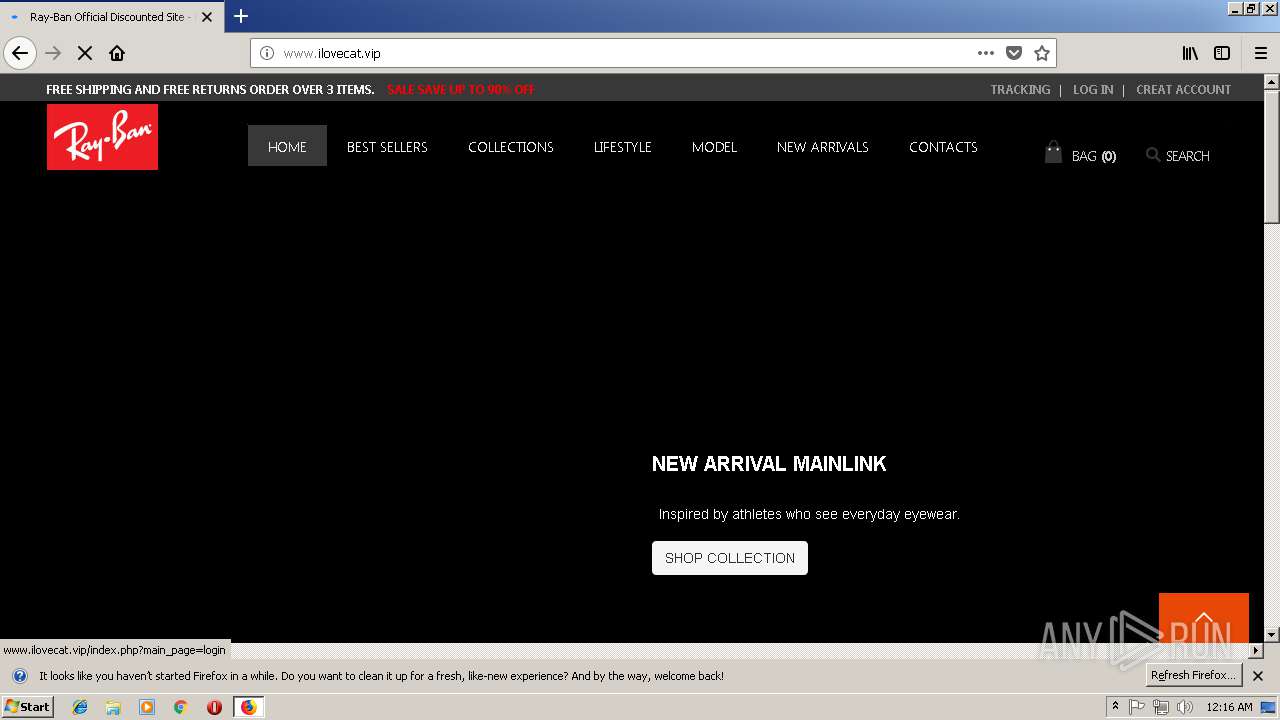
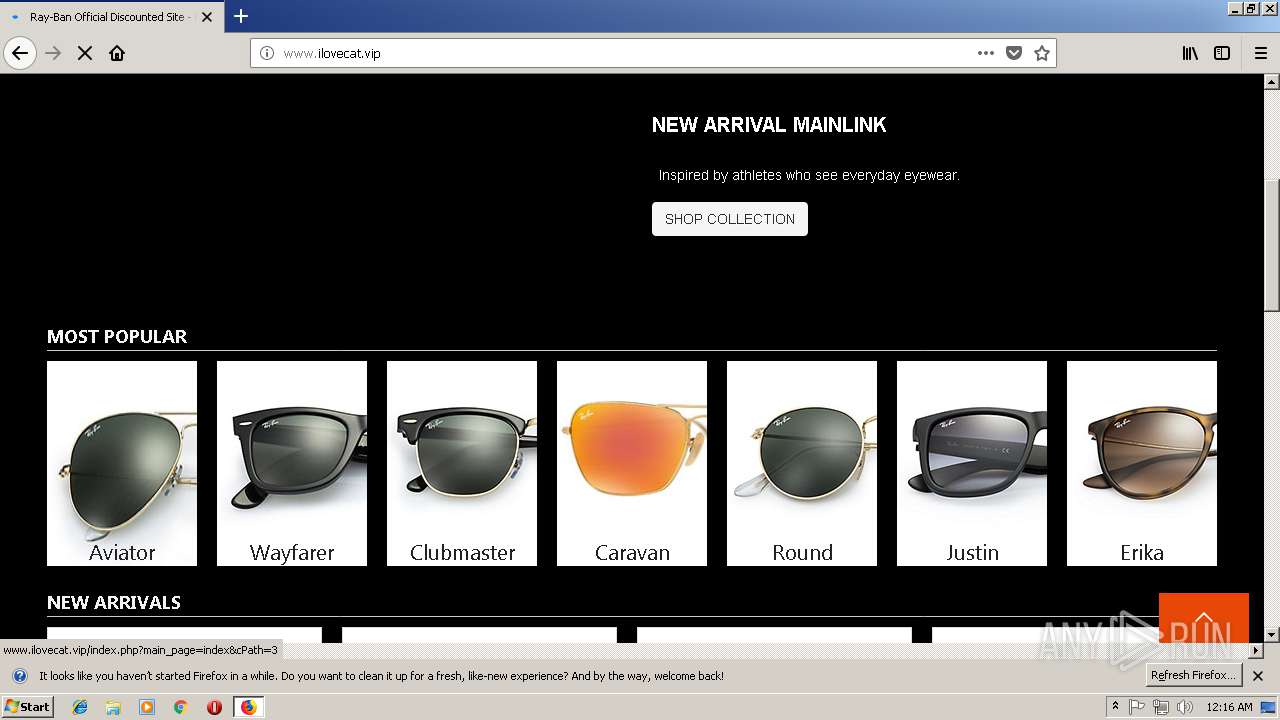
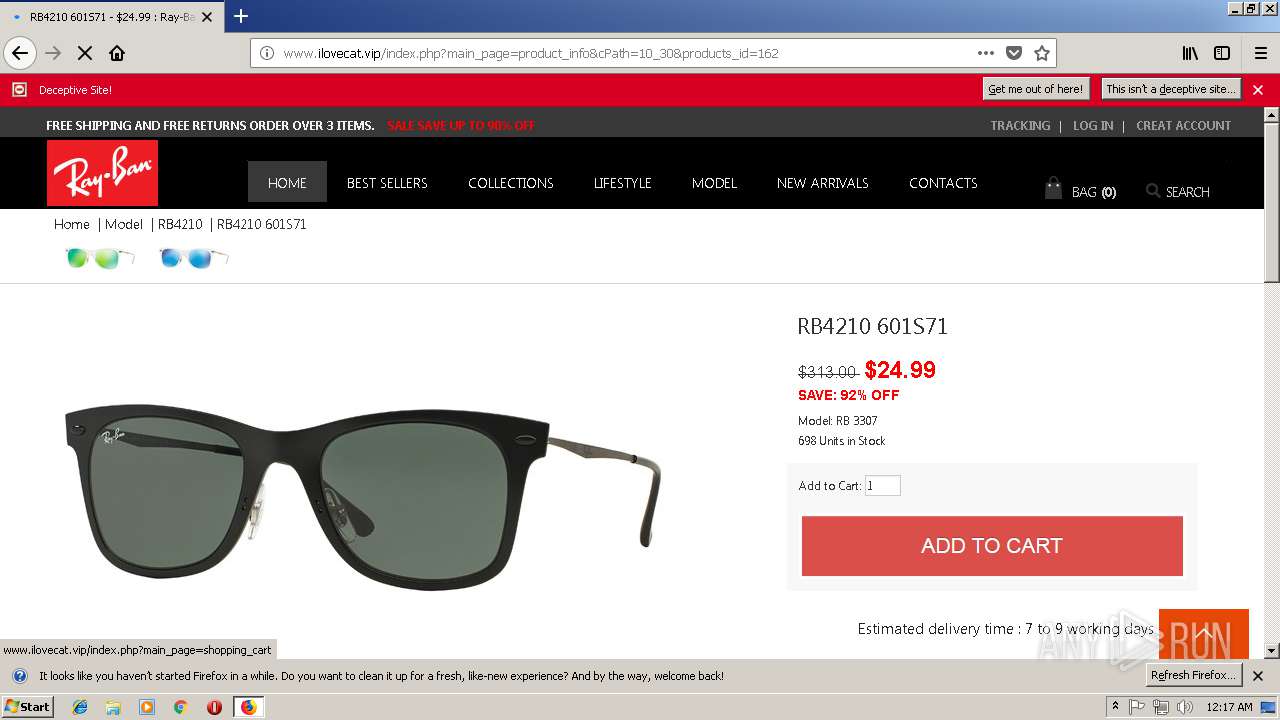
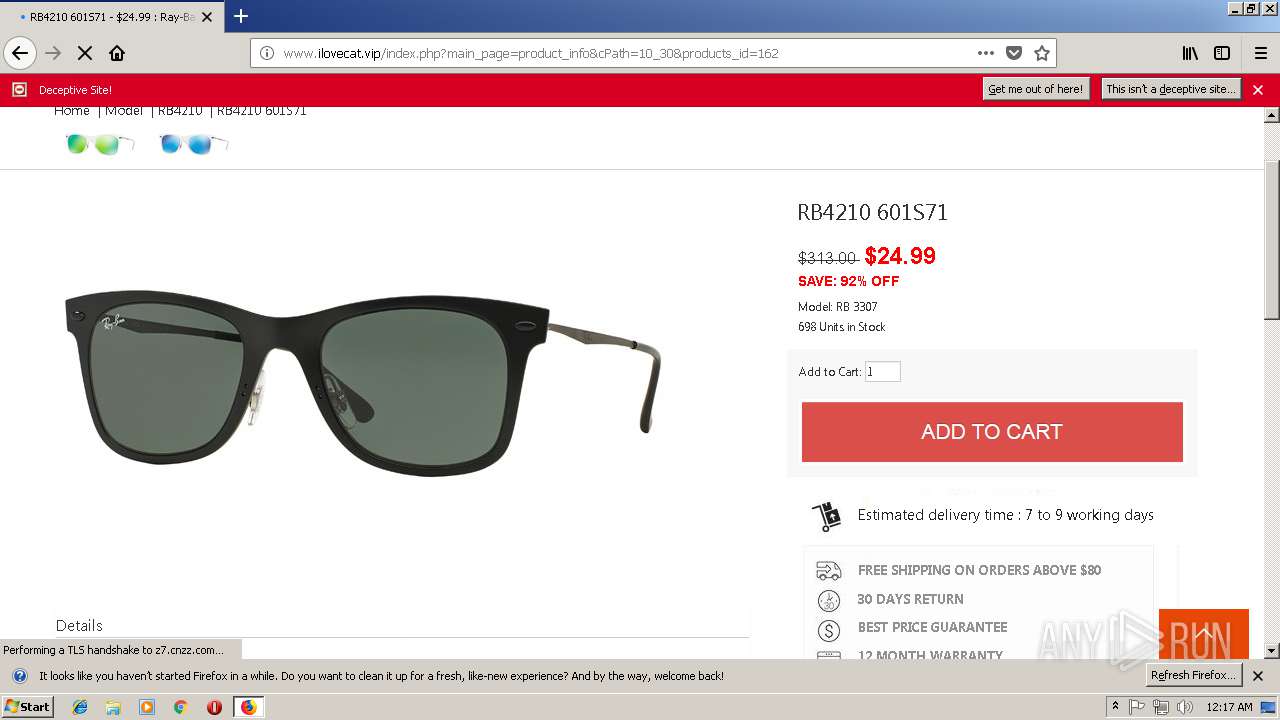
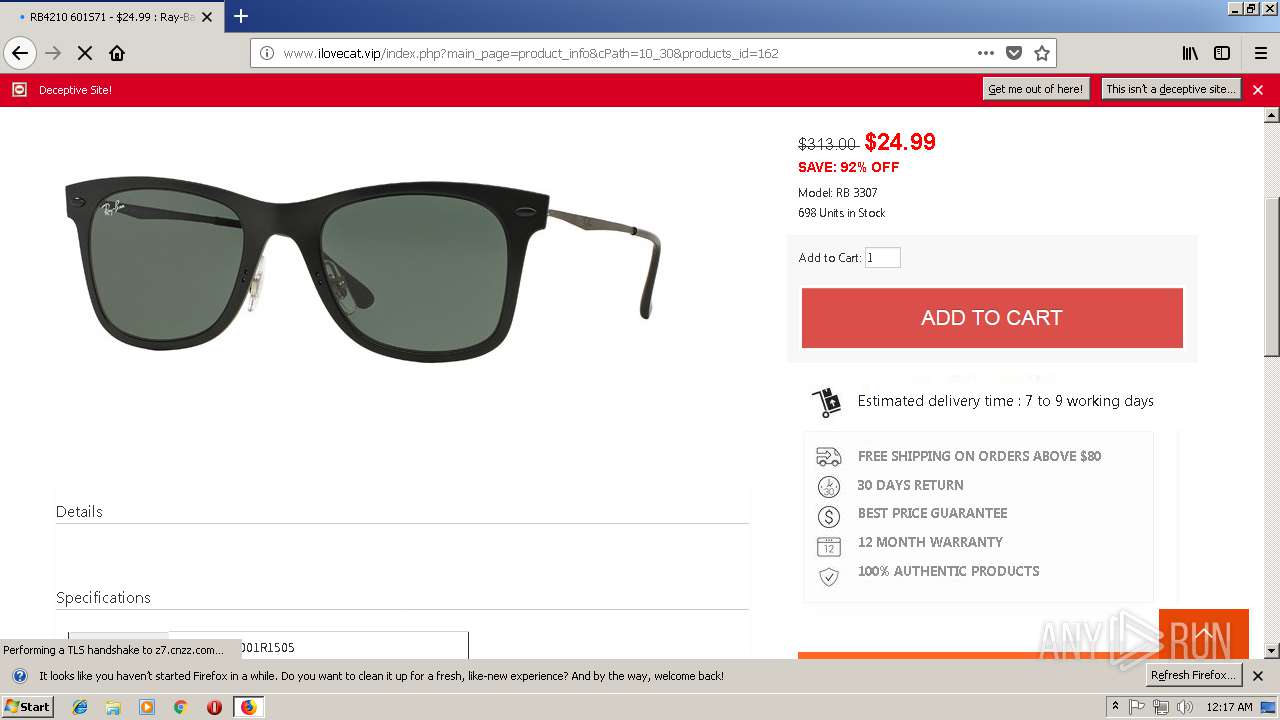
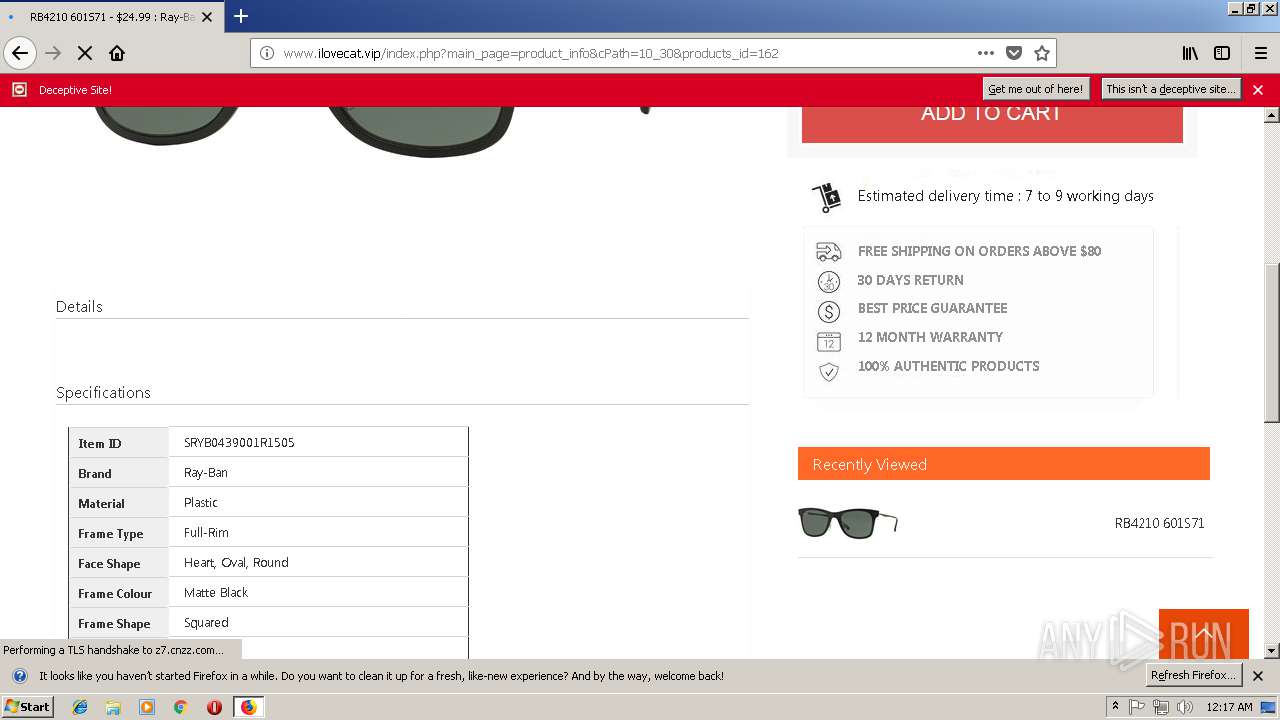
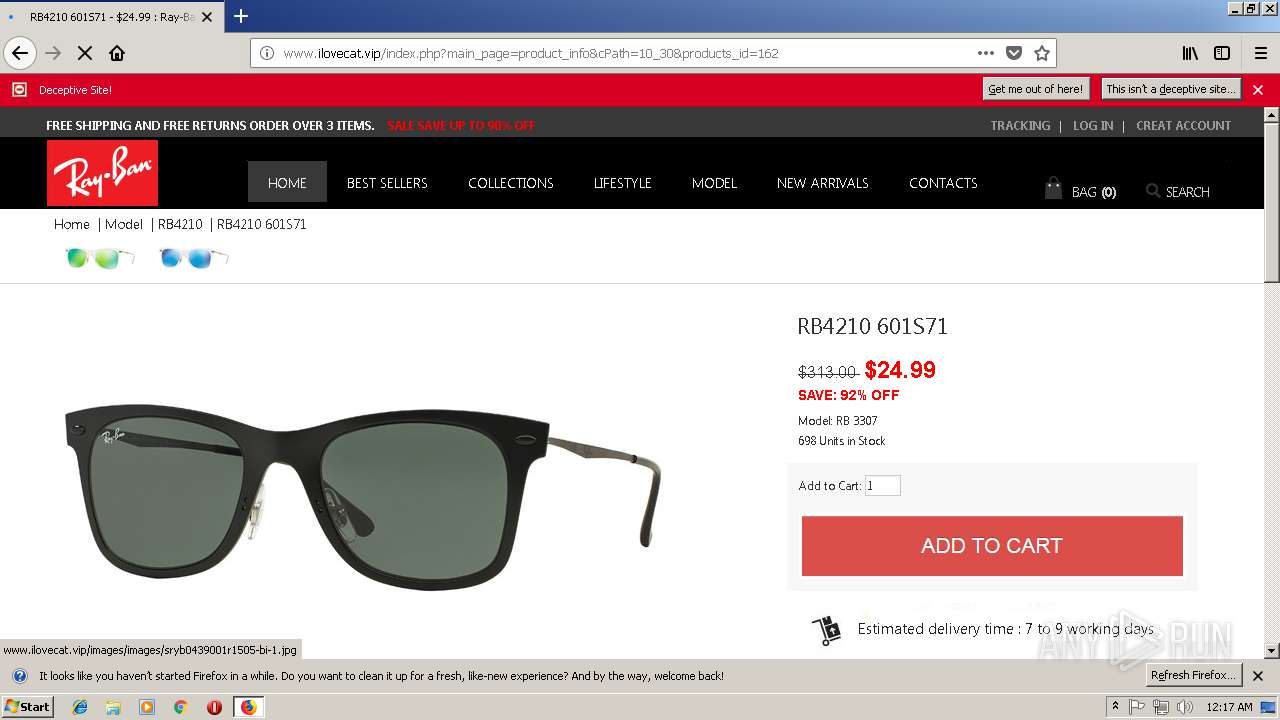
| Title: | Ray-Ban Official Discounted Site - From USA, Stand the chance to win a unique Never Hide Sessions at your home with some of the iconic Ray-Ban artists. Discover the contest! |
|---|---|
| ContentType: | text/html; charset=UTF-8 |
| Keywords: | Ray-Ban is the global leader in premium eyewear market and by far the best-selling eyewear brand in the world |
| Description: | Stand the chance to win a unique Never Hide Sessions at your home with some of the iconic Ray-Ban artists. Discover the contest! |
| ImageToolbar: | no |
| Author: | META_TAG_AUTHOR |
| Generator: | META_TAG_GENERATOR |
Total processes
42
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1600.6.401636895\324174135" -childID 2 -isForBrowser -prefsHandle 2408 -prefsLen 11442 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1600 "\\.\pipe\gecko-crash-server-pipe.1600" 2056 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
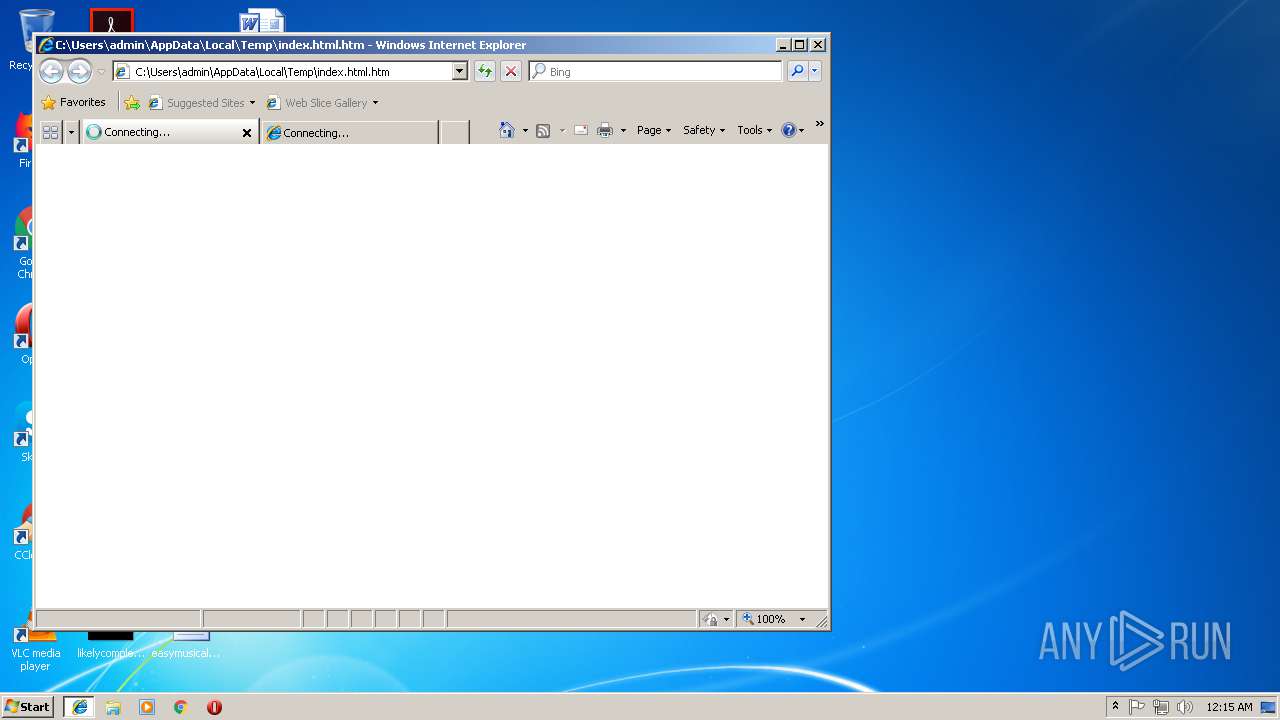
| 920 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/9090c48b-f4f2-43a2-a3a8-55df0e8d4d16/main/Firefox/61.0.2/release/20180807170231?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\9090c48b-f4f2-43a2-a3a8-55df0e8d4d16 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3448 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:920 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3596 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:920 CREDAT:14339 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3600 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1600.12.197571471\282377254" -childID 3 -isForBrowser -prefsHandle 3056 -prefsLen 11808 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1600 "\\.\pipe\gecko-crash-server-pipe.1600" 3068 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3768 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1600.0.1380760279\36771158" -childID 1 -isForBrowser -prefsHandle 784 -prefsLen 8309 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1600 "\\.\pipe\gecko-crash-server-pipe.1600" 772 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
Total events
1 009
Read events
909
Write events
97
Delete events
3
Modification events
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8B72AA2D-E3B4-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B000500090000000F0016007C00 | |||
Executable files
0
Suspicious files
166
Text files
69
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF90E0569451DF0737.TMP | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFACA43C00E25C249F.TMP | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF306CDAC9C3AAF087.TMP | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5887E2A4DFFE3361.TMP | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF92A64BB7CB48A565.TMP | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{8B72AA2F-E3B4-11E8-BFAB-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QWU8GDUAVLT4ADUSS9G4.temp | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBE5585BE0F48523B.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
160
TCP/UDP connections
118
DNS requests
77
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3448 | iexplore.exe | GET | — | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/css/stylesheet_css_buttons.css | US | — | — | shared |
3448 | iexplore.exe | GET | — | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/jscript/dist/js/jquery.min.js | US | — | — | shared |
3448 | iexplore.exe | GET | — | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/jscript/jscript_imagehover.js | US | — | — | shared |
3596 | iexplore.exe | GET | — | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/jscript/jscript_imagehover.js | US | — | — | shared |
3448 | iexplore.exe | GET | 403 | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/css/print_stylesheet.css | US | html | 1.93 Kb | shared |
3448 | iexplore.exe | GET | 403 | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/css/stylesheet.css | US | html | 1.93 Kb | shared |
3596 | iexplore.exe | GET | 403 | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/css/stylesheet_css_buttons.css | US | html | 1.91 Kb | shared |
3448 | iexplore.exe | GET | 403 | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/css/stylesheet_topmenu.css | US | html | 1.93 Kb | shared |
3596 | iexplore.exe | GET | 403 | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/css/style_imagehover.css | US | html | 1.91 Kb | shared |
3596 | iexplore.exe | GET | 403 | 104.28.22.22:80 | http://www.ilovecat.vip/includes/templates/pure_black_free/css/stylesheet_topmenu.css | US | html | 1.91 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3448 | iexplore.exe | 104.28.22.22:80 | www.ilovecat.vip | Cloudflare Inc | US | shared |
920 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3596 | iexplore.exe | 104.28.22.22:80 | www.ilovecat.vip | Cloudflare Inc | US | shared |
3596 | iexplore.exe | 111.3.87.105:443 | s13.cnzz.com | China Mobile communications corporation | CN | unknown |
1600 | firefox.exe | 34.208.206.25:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1600 | firefox.exe | 2.21.89.57:80 | detectportal.firefox.com | Akamai International B.V. | AT | whitelisted |
1600 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1600 | firefox.exe | 52.10.130.148:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1600 | firefox.exe | 104.28.22.22:80 | www.ilovecat.vip | Cloudflare Inc | US | shared |
1600 | firefox.exe | 172.217.16.46:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ilovecat.vip |
| unknown |
www.bing.com |
| whitelisted |
s13.cnzz.com |
| suspicious |
detectportal.firefox.com |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |