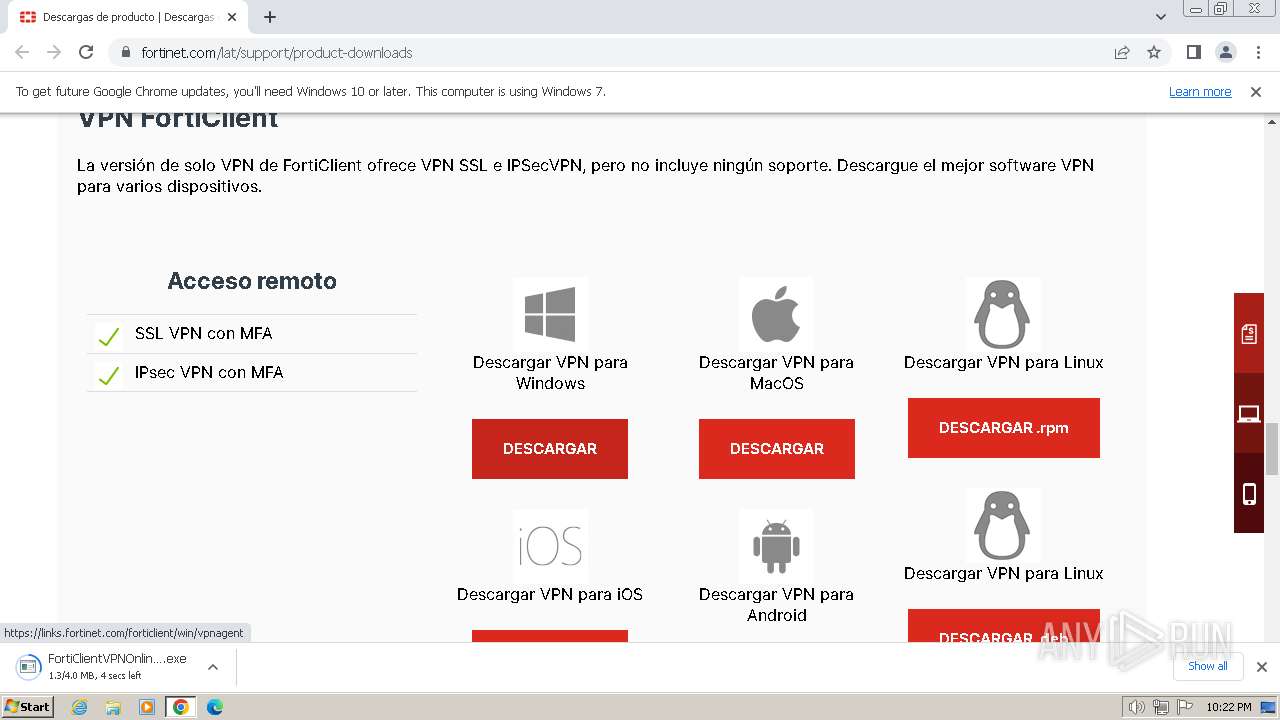
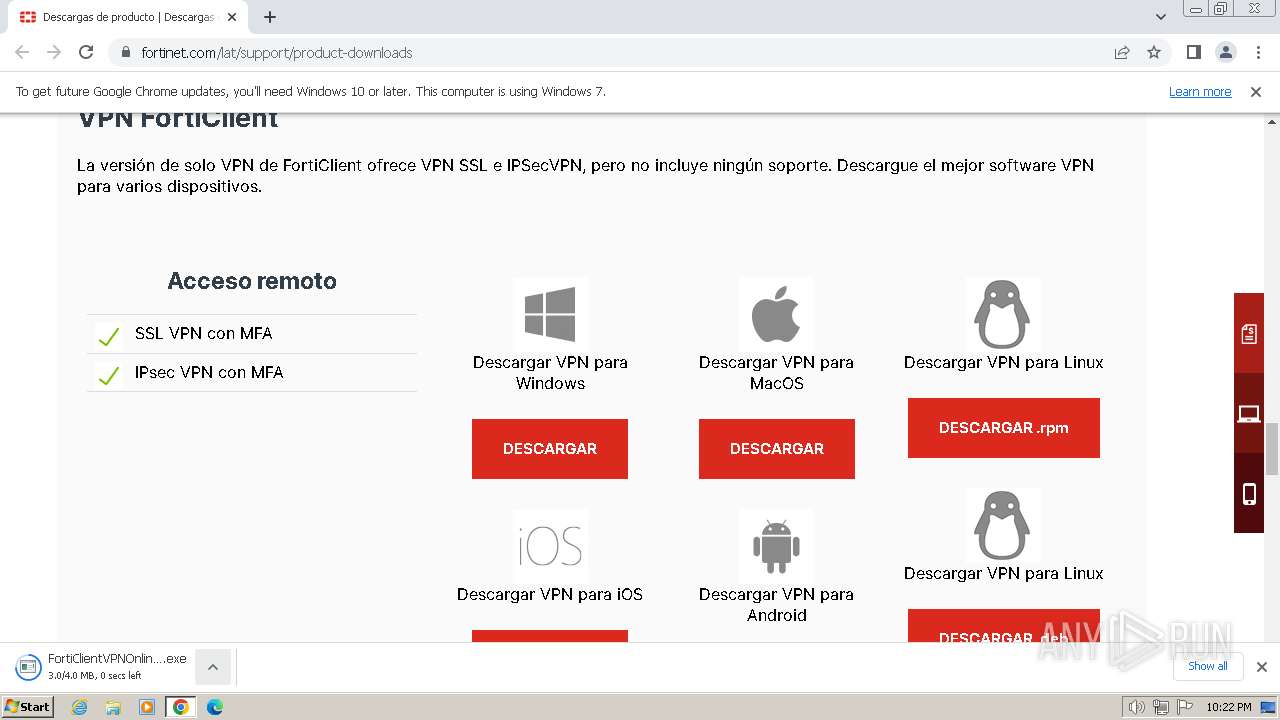
| URL: | https://www.fortinet.com/lat/support/product-downloads |
| Full analysis: | https://app.any.run/tasks/529b557e-6f99-4e90-91a5-02fd342f04da |
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2024, 22:21:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3963FE453284D95D405786A26F3B8681 |
| SHA1: | 2BD6D90BEEF05311496792D59677DA8C65F973A7 |
| SHA256: | 995A0C355376F089981E306ED12FEE39156EA2B8DED43463A44DB8DA16B16F6E |
| SSDEEP: | 3:N8DSLWXVI3g/QK9bGRIZ4n:2OLWy3AQ4iRIq |
MALICIOUS
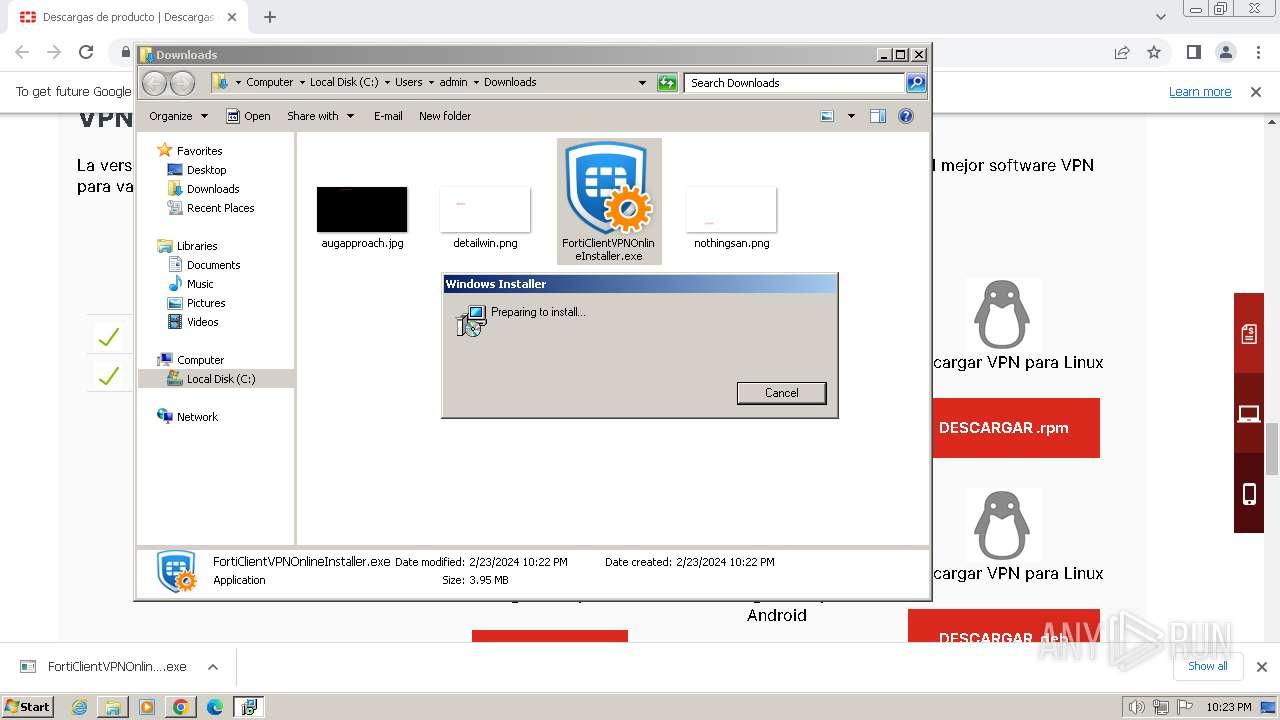
Drops the executable file immediately after the start
- FortiClientVPN.exe (PID: 3376)
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 2584)
- drvinst.exe (PID: 3224)
Creates a writable file in the system directory
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 2584)
Registers / Runs the DLL via REGSVR32.EXE
- scheduler.exe (PID: 3804)
Starts NET.EXE for service management
- FortiSSLVPNdaemon.exe (PID: 3768)
- net.exe (PID: 3624)
Changes the autorun value in the registry
- drvinst.exe (PID: 2620)
SUSPICIOUS
Reads security settings of Internet Explorer
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- FortiClientVPN.exe (PID: 3376)
- scheduler.exe (PID: 3804)
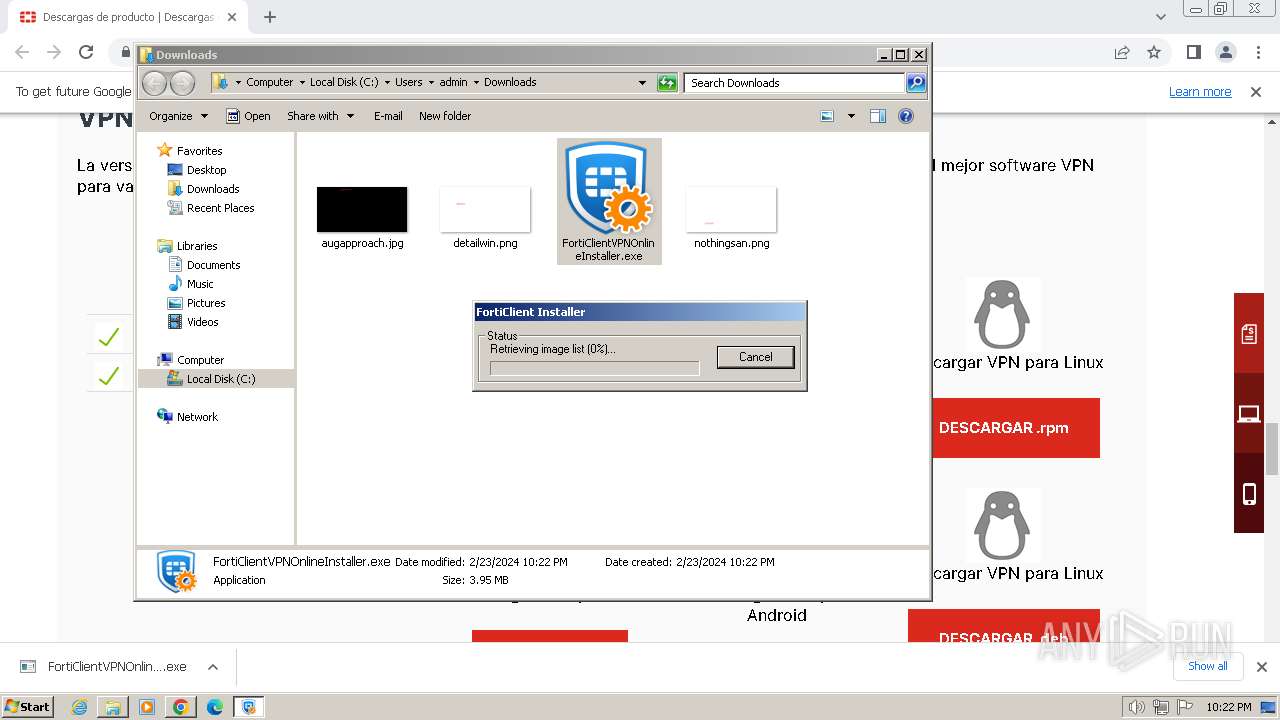
Application launched itself
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
Creates/Modifies COM task schedule object
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- regsvr32.exe (PID: 2524)
Reads the Internet Settings
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
Connects to the server without a host name
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
Checks Windows Trust Settings
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- FortiClientVPN.exe (PID: 3376)
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 2620)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 2584)
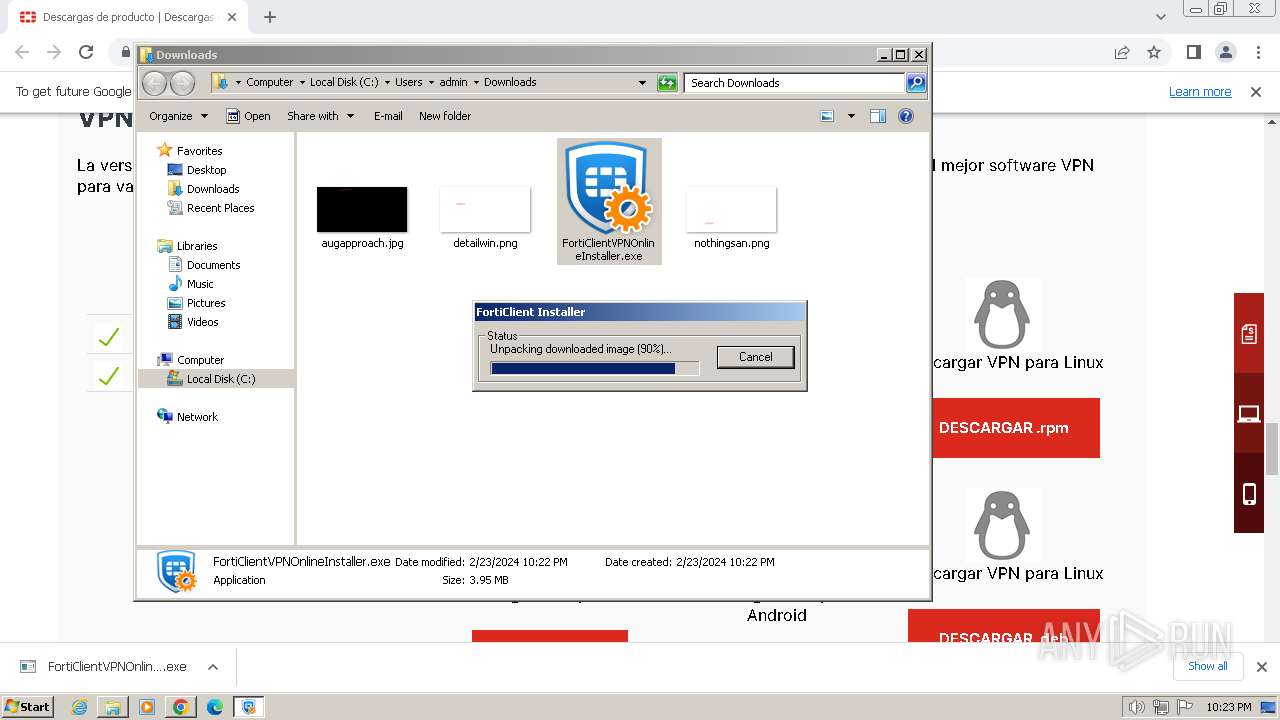
Adds/modifies Windows certificates
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
Reads settings of System Certificates
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- FortiClientVPN.exe (PID: 3376)
Executable content was dropped or overwritten
- FortiClientVPN.exe (PID: 3376)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 2584)
Creates files in the driver directory
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 2584)
Drops a system driver (possible attempt to evade defenses)
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 2584)
Reads the Windows owner or organization settings
- FortiClientVPN.exe (PID: 3376)
Executes as Windows Service
- scheduler.exe (PID: 3804)
INFO
Application launched itself
- chrome.exe (PID: 2472)
Checks supported languages
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- FortiClientVPN.exe (PID: 3376)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 2620)
- drvinst.exe (PID: 2584)
- FortiScand.exe (PID: 1376)
- scheduler.exe (PID: 3804)
- FCCOMInt.exe (PID: 2916)
- FCDBLog.exe (PID: 2924)
- FortiSSLVPNdaemon.exe (PID: 3768)
- FortiSettings.exe (PID: 3852)
- FortiVPN.exe (PID: 3840)
- FortiTray.exe (PID: 1852)
Reads the computer name
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- FortiClientVPN.exe (PID: 3376)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 2620)
- drvinst.exe (PID: 2584)
- scheduler.exe (PID: 3804)
- FCDBLog.exe (PID: 2924)
- FortiScand.exe (PID: 1376)
- FortiSSLVPNdaemon.exe (PID: 3768)
- FCCOMInt.exe (PID: 2916)
- FortiVPN.exe (PID: 3840)
- FortiTray.exe (PID: 1852)
- FortiSettings.exe (PID: 3852)
Create files in a temporary directory
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- FortiClientVPN.exe (PID: 3376)
- rundll32.exe (PID: 3504)
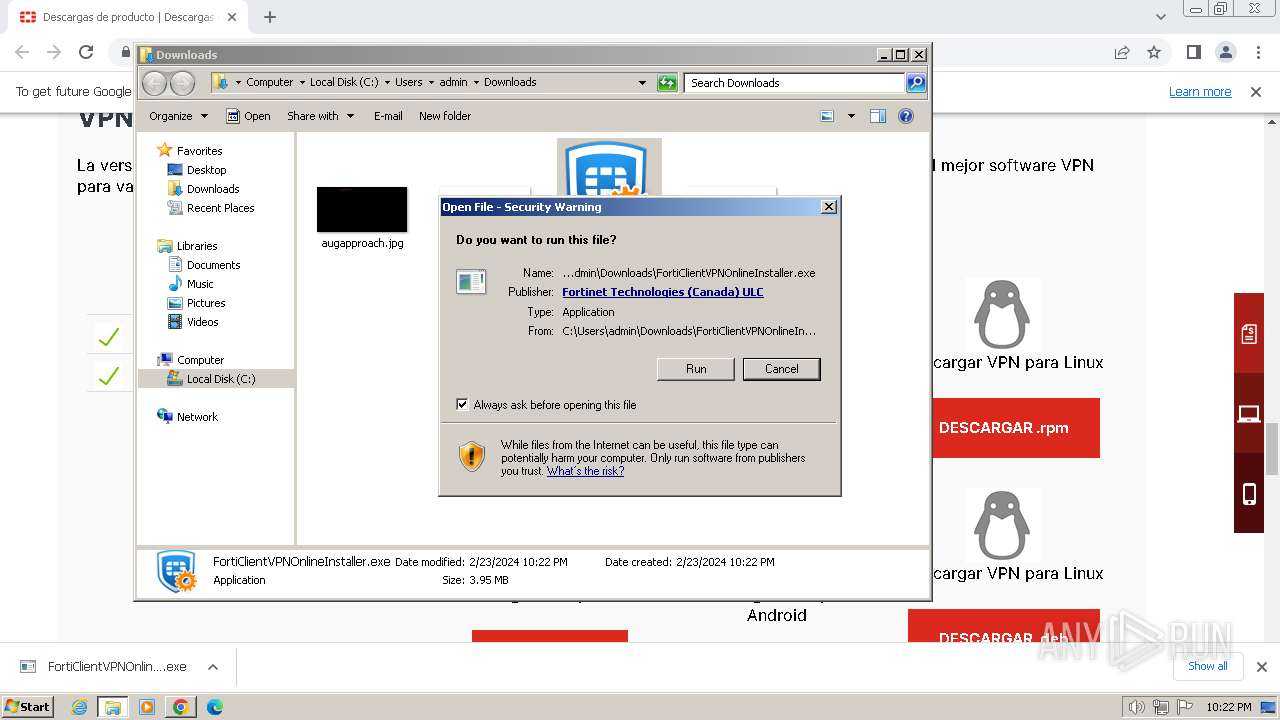
Process checks whether UAC notifications are on
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
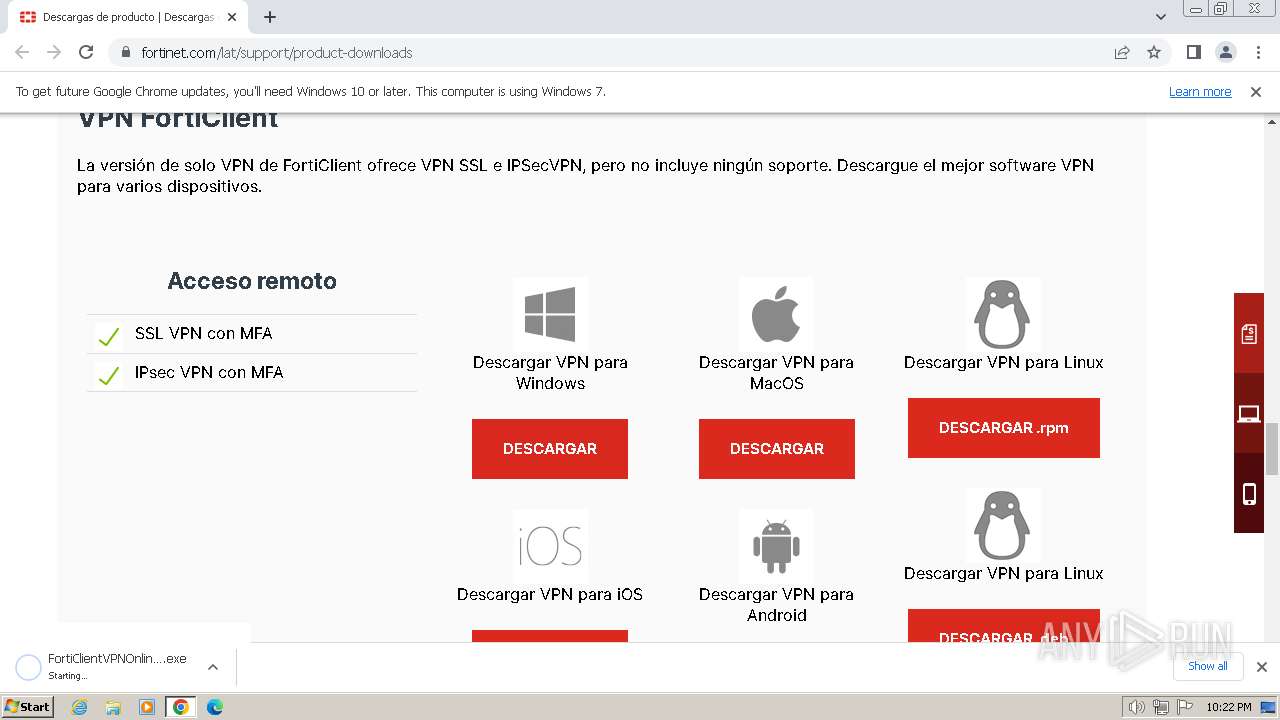
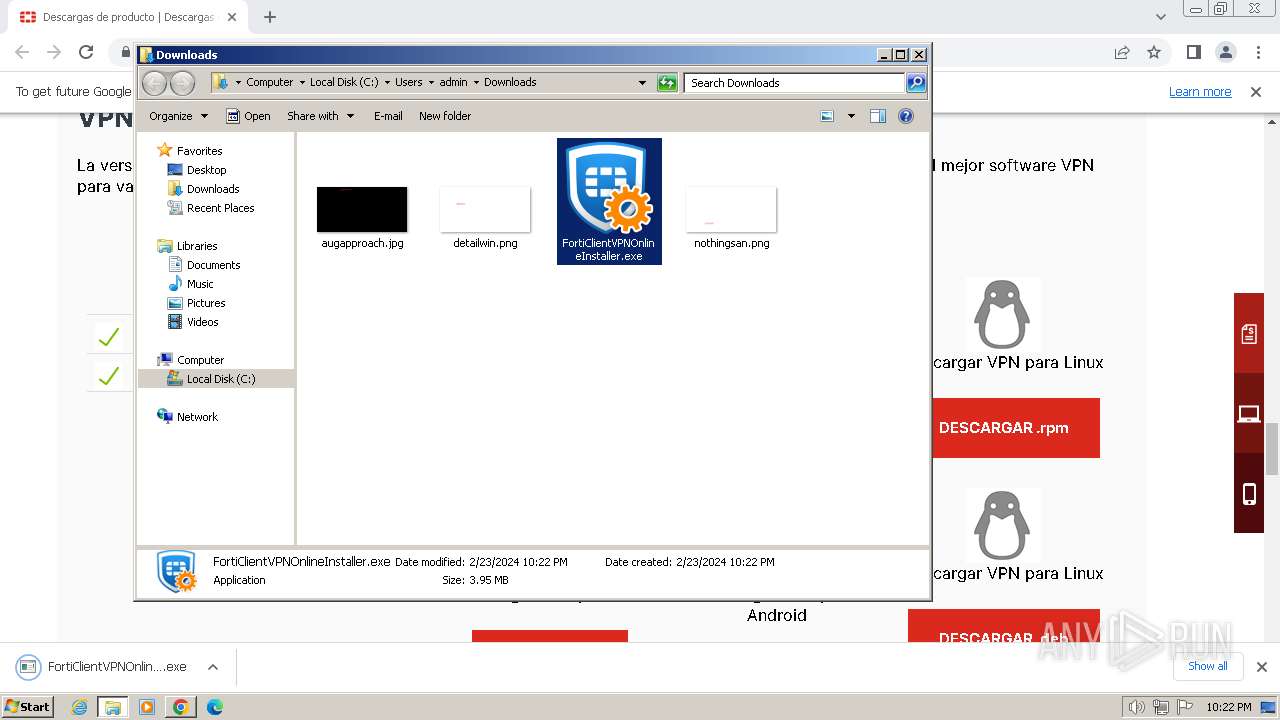
The process uses the downloaded file
- chrome.exe (PID: 1892)
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
Executable content was dropped or overwritten
- chrome.exe (PID: 2472)
Drops the executable file immediately after the start
- chrome.exe (PID: 2472)
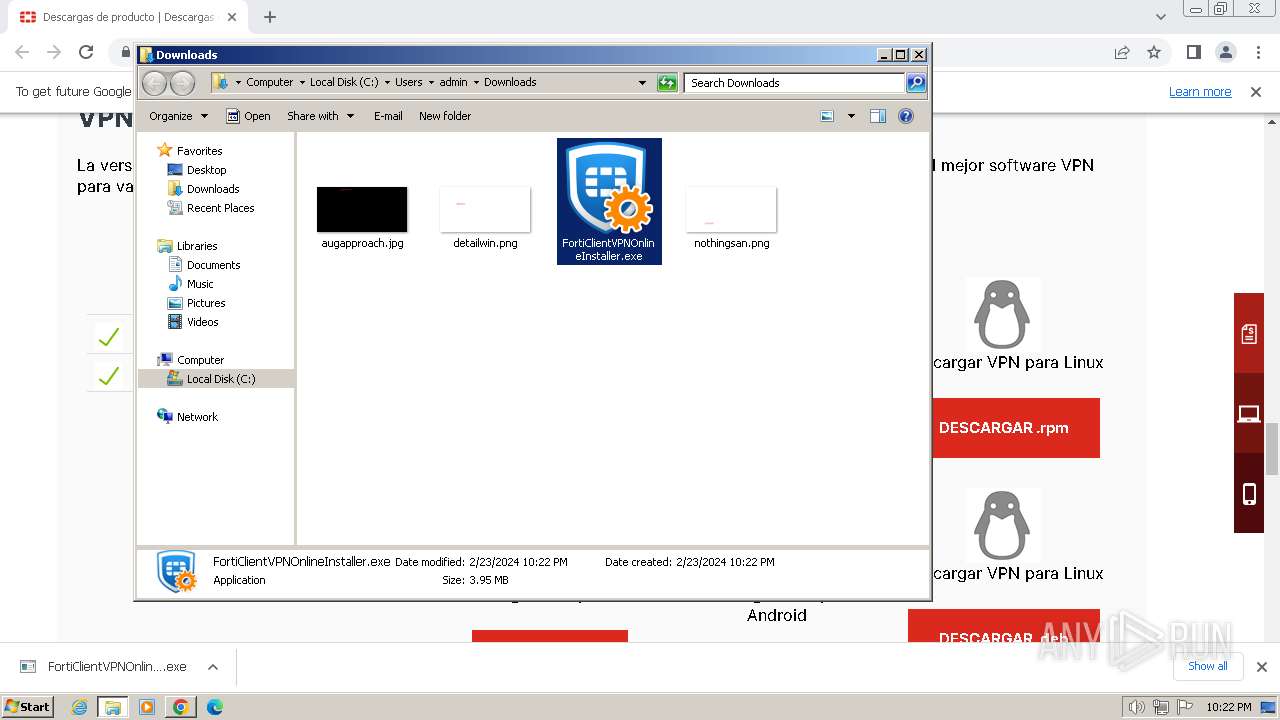
Manual execution by a user
- FortiClientVPNOnlineInstaller.exe (PID: 2808)
Reads the machine GUID from the registry
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- FortiClientVPN.exe (PID: 3376)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 2620)
- drvinst.exe (PID: 2584)
- FortiVPN.exe (PID: 3840)
Creates files or folders in the user directory
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- rundll32.exe (PID: 3504)
- FortiTray.exe (PID: 1852)
Reads the software policy settings
- FortiClientVPNOnlineInstaller.exe (PID: 2616)
- FortiClientVPN.exe (PID: 3376)
- drvinst.exe (PID: 1808)
- drvinst.exe (PID: 3224)
- drvinst.exe (PID: 2620)
- drvinst.exe (PID: 2584)
Creates files in the program directory
- FortiClientVPN.exe (PID: 3376)
- FCDBLog.exe (PID: 2924)
- FortiSSLVPNdaemon.exe (PID: 3768)
- FortiVPN.exe (PID: 3840)
Reads Environment values
- drvinst.exe (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
38
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3328 --field-trial-handle=1168,i,10539022663150268233,1156693020508993024,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1428 --field-trial-handle=1168,i,10539022663150268233,1156693020508993024,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Fortinet\FortiClient\FortiScand.exe" /regserver | C:\Program Files\Fortinet\FortiClient\FortiScand.exe | — | scheduler.exe | |||||||||||
User: SYSTEM Company: Fortinet Inc. Integrity Level: SYSTEM Description: FortiClient Scan Server Exit code: 0 Version: 7.2.3.0929 Modules
| |||||||||||||||
| 1728 | C:\Windows\system32\net1 start dnscache | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3932 --field-trial-handle=1168,i,10539022663150268233,1156693020508993024,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1808 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{6c9b9078-8041-2409-3adc-746444d70f5d}\ft_vnic.inf" "0" "66ea89307" "000004D4" "WinSta0\Default" "00000330" "208" "C:\Windows\system32\DRVSTORE\ft_vnic_C8FF177157AC1AF16135BAE14B45CCBD96F5A688" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | -s FC_{73EFB30F-1CAD-4a7a-AE2E-150282B6CE25}_000008 | C:\Program Files\Fortinet\FortiClient\FortiTray.exe | — | scheduler.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient System Tray Controller Exit code: 0 Version: 7.2.3.0929 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3852 --field-trial-handle=1168,i,10539022663150268233,1156693020508993024,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3352 --field-trial-handle=1168,i,10539022663150268233,1156693020508993024,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3844 --field-trial-handle=1168,i,10539022663150268233,1156693020508993024,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
41 640
Read events
40 903
Write events
653
Delete events
84
Modification events
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
15
Suspicious files
67
Text files
57
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f6f2.TMP | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f6e3.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\de6e24c2-aa41-4325-9817-1ab13fa726cc.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17fd7a.TMP | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF17f7cd.TMP | text | |
MD5:C383FD120B14BB0E98E99C1BCC9B43F6 | SHA256:56A3A5EACBD28BEE1CF8C1D0052321A5C27EE858BEF7B2FA1DE20806A0823CC1 | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF180d59.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
57
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2616 | FortiClientVPNOnlineInstaller.exe | POST | 200 | 173.243.138.76:80 | http://173.243.138.76/fdsupdate | unknown | binary | 684 b | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
2616 | FortiClientVPNOnlineInstaller.exe | POST | 200 | 208.184.237.75:80 | http://208.184.237.75/fdsupdate | unknown | binary | 108 Mb | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
2616 | FortiClientVPNOnlineInstaller.exe | POST | 200 | 208.184.237.75:80 | http://208.184.237.75/fdsupdate | unknown | binary | 108 Kb | unknown |
2616 | FortiClientVPNOnlineInstaller.exe | GET | 200 | 192.229.221.95:80 | http://cacerts.digicert.com/DigiCertTrustedG4CodeSigningRSA4096SHA3842021CA1.crt | unknown | binary | 1.68 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2472 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3848 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3848 | chrome.exe | 18.156.16.255:443 | www.fortinet.com | AMAZON-02 | DE | unknown |
3848 | chrome.exe | 104.18.131.236:443 | cdn.cookielaw.org | CLOUDFLARENET | — | unknown |
3848 | chrome.exe | 172.64.155.119:443 | geolocation.onetrust.com | CLOUDFLARENET | US | unknown |
3848 | chrome.exe | 142.250.185.170:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
3848 | chrome.exe | 147.154.54.13:443 | s3049749.t.eloqua.com | ORACLE-BMC-31898 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.fortinet.com |
| unknown |
cdn.cookielaw.org |
| whitelisted |
geolocation.onetrust.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
s3049749.t.eloqua.com |
| unknown |
site.fortinet.com |
| unknown |
assets.adobedtm.com |
| whitelisted |
j.6sc.co |
| shared |
c.6sc.co |
| shared |