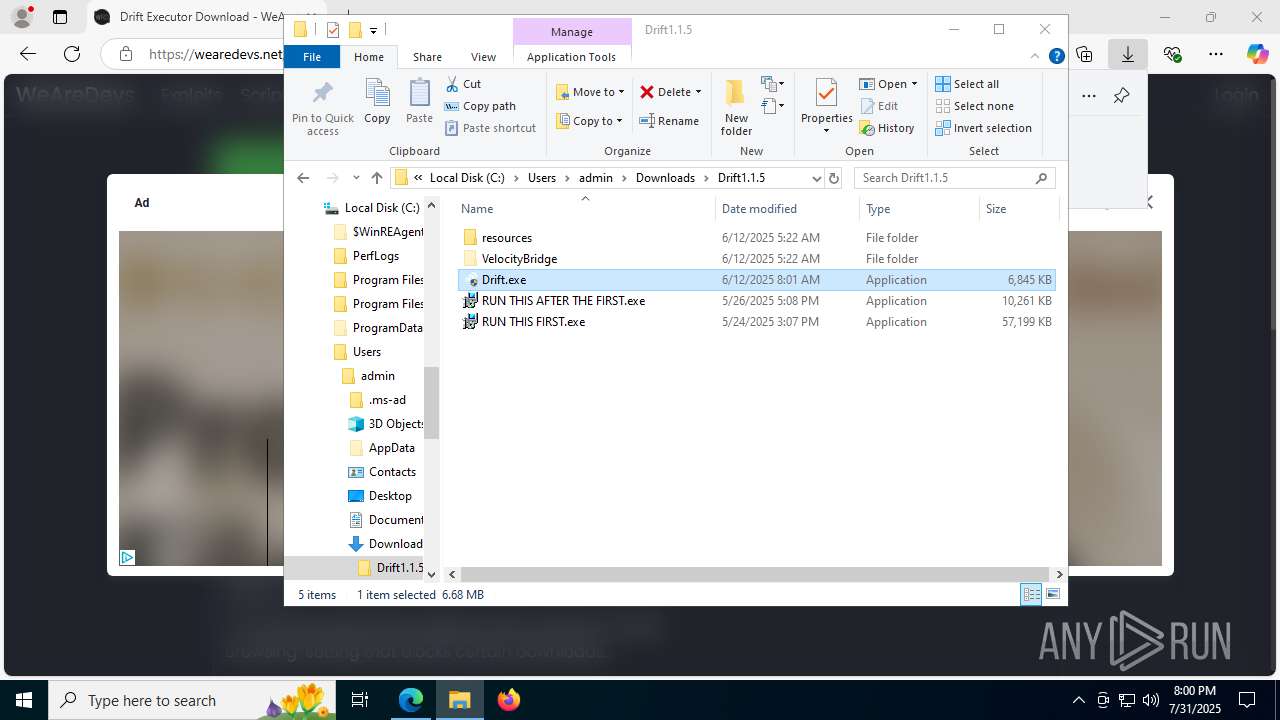
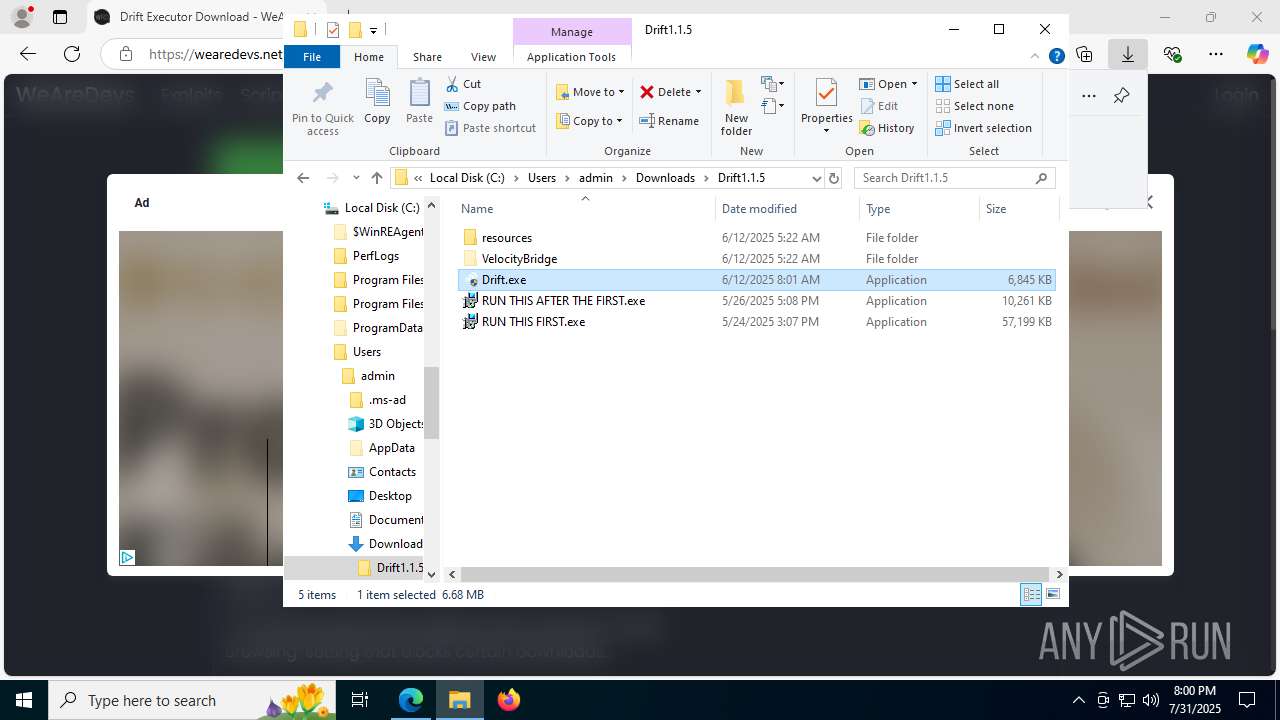
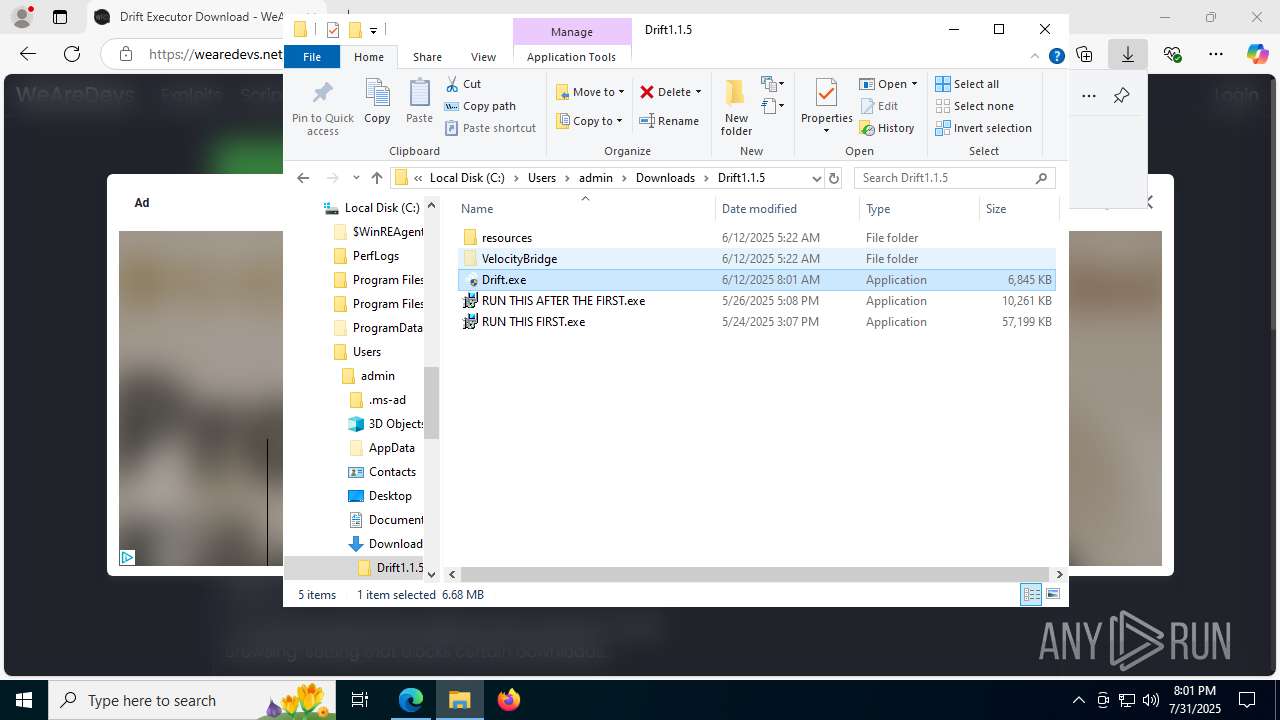
| URL: | https://wearedevs.net/d/Drift |
| Full analysis: | https://app.any.run/tasks/d8faeb26-d05c-4427-b7df-5aa44dff63ae |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2025, 19:58:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1DCA9C11408D7B92CFB618A26A081FD0 |
| SHA1: | E07FCF2394ADF825FFABA1EE04C73AA43318405B |
| SHA256: | 994DC829349B5FEC400688D90B4B6F553DCFB0B7942D4F445CE765D128A5A4C0 |
| SSDEEP: | 3:N8R/BApK8Mn:25BuBMn |
MALICIOUS
Changes the autorun value in the registry
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
Changes powershell execution policy (Bypass)
- Drift.exe (PID: 1864)
Bypass execution policy to execute commands
- powershell.exe (PID: 7244)
SUSPICIOUS
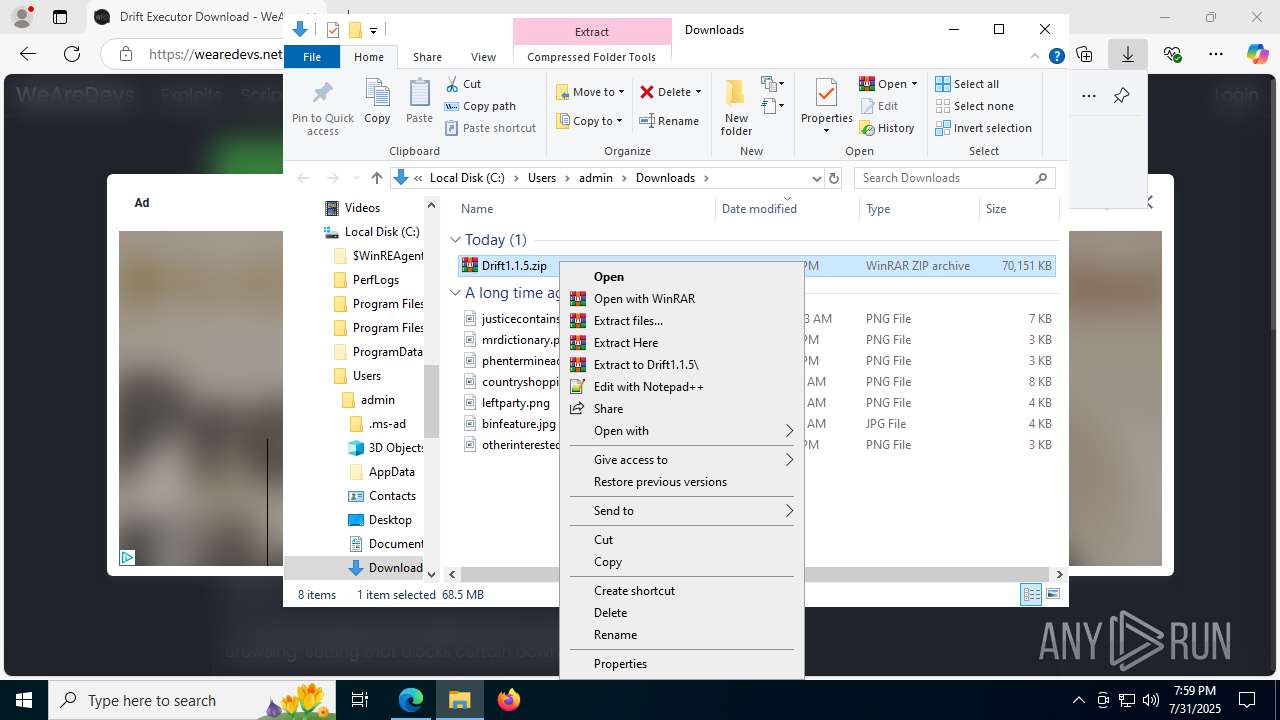
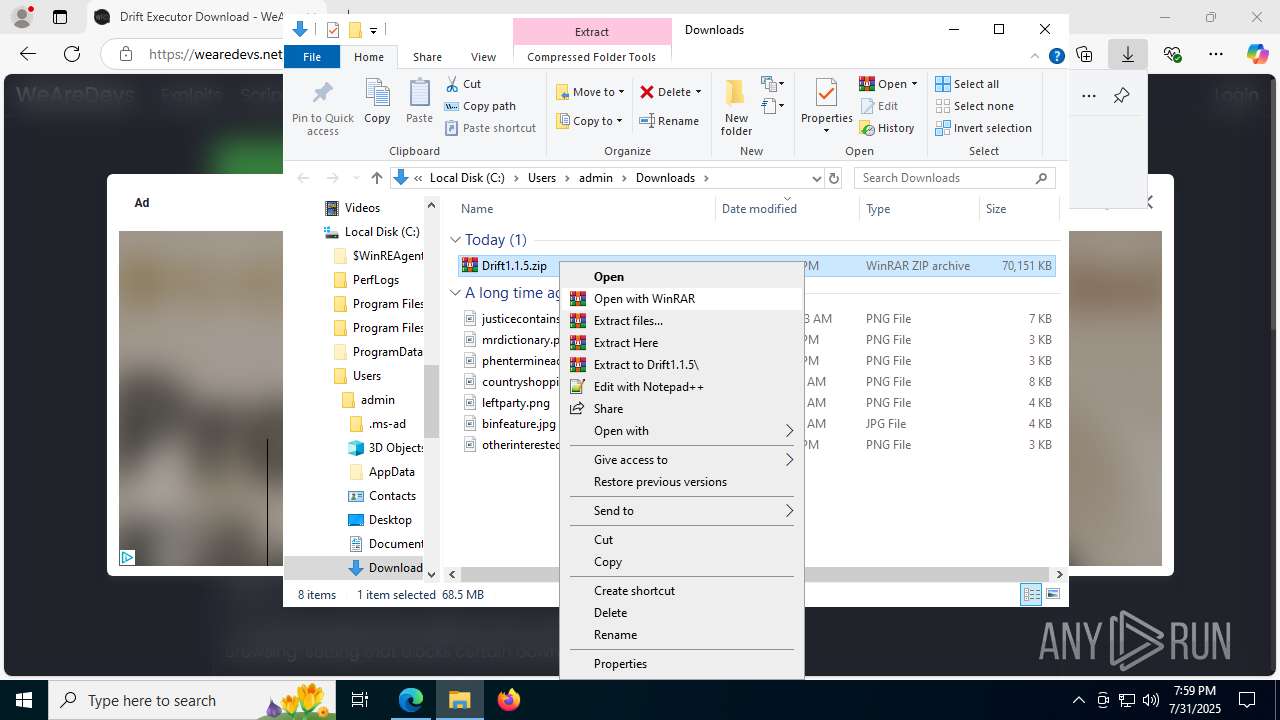
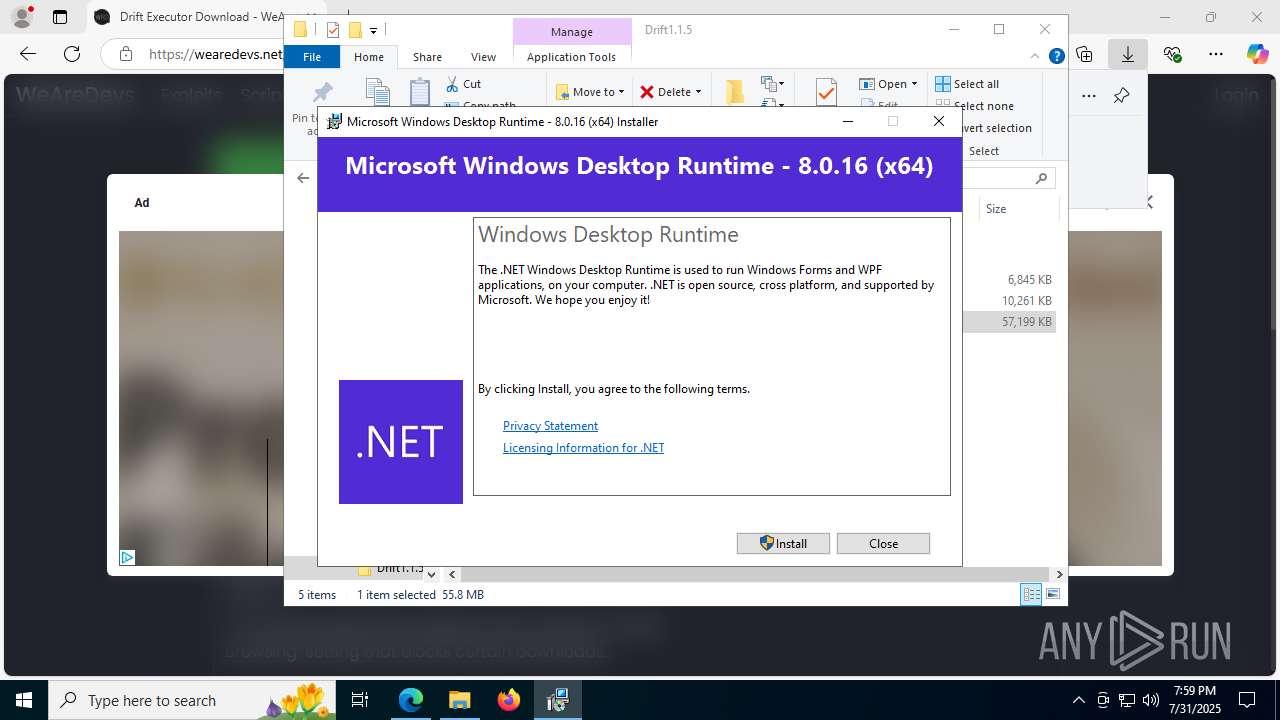
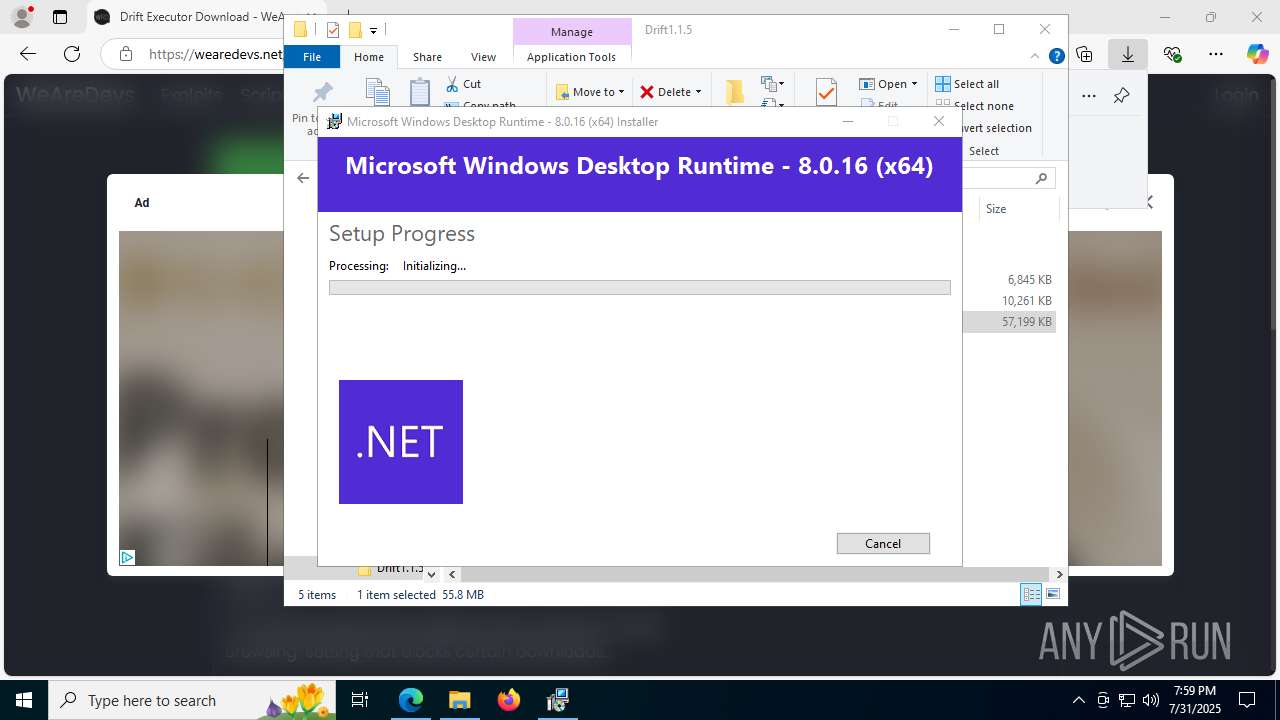
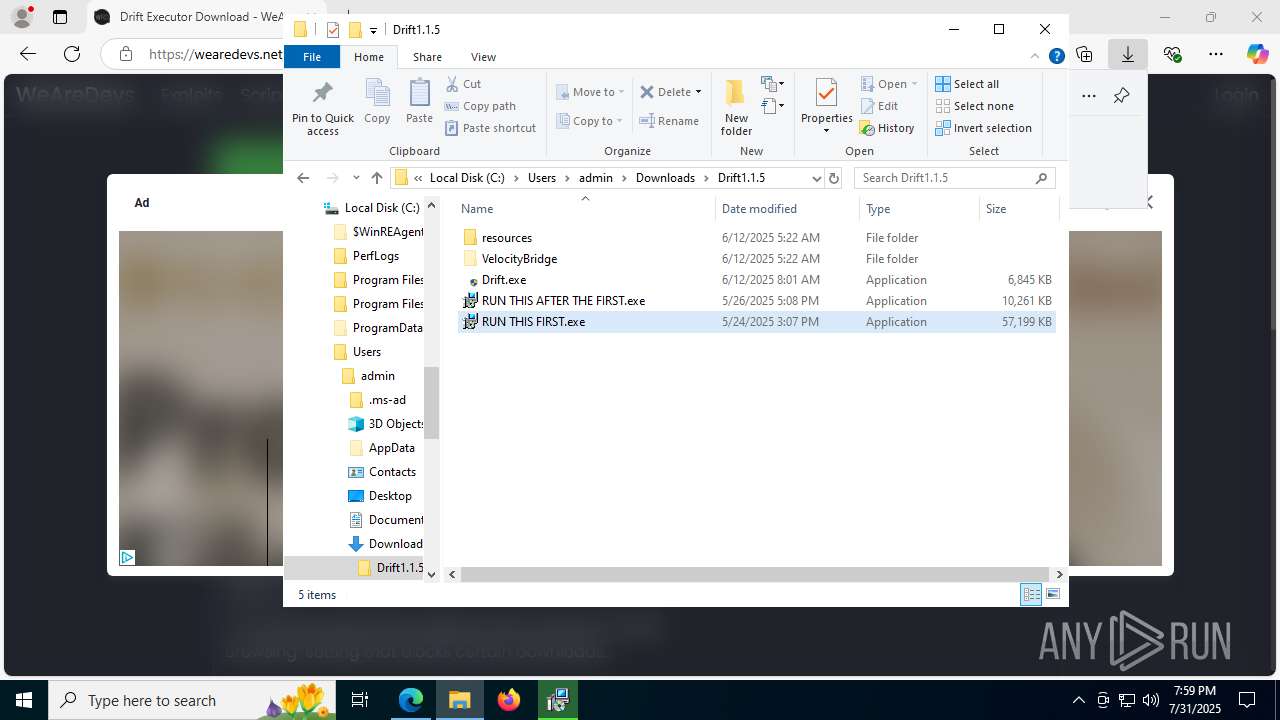
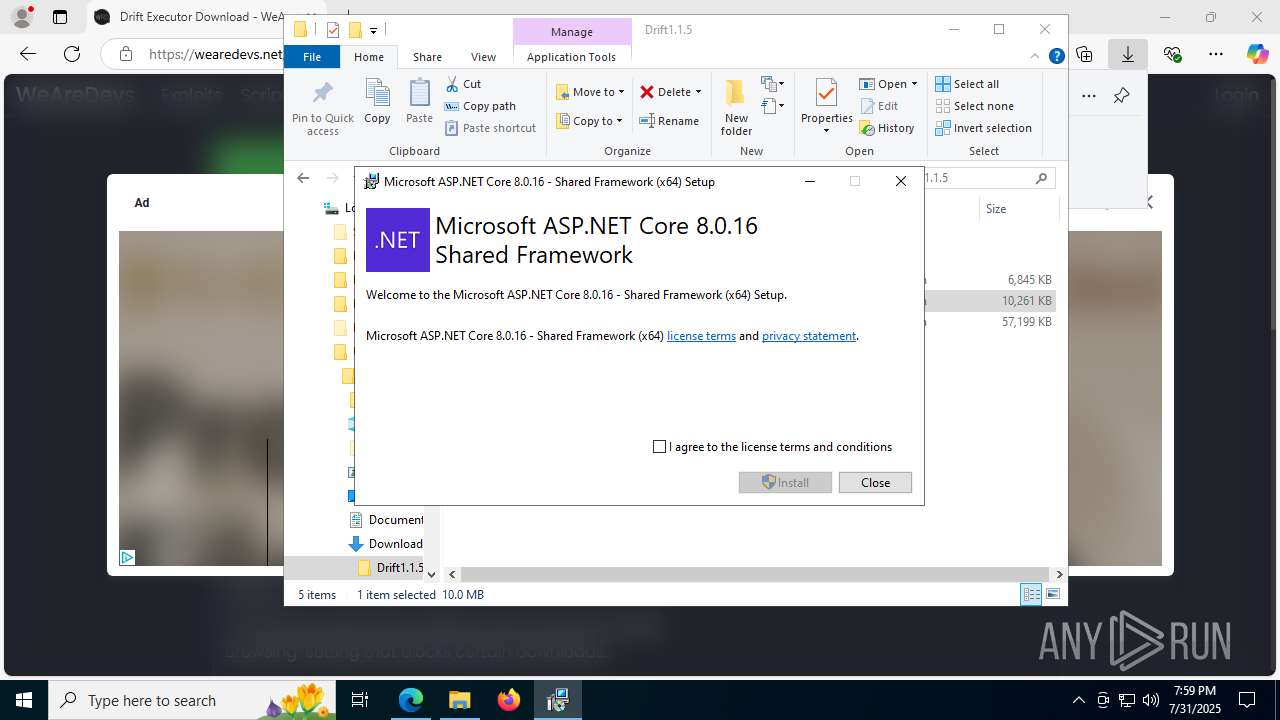
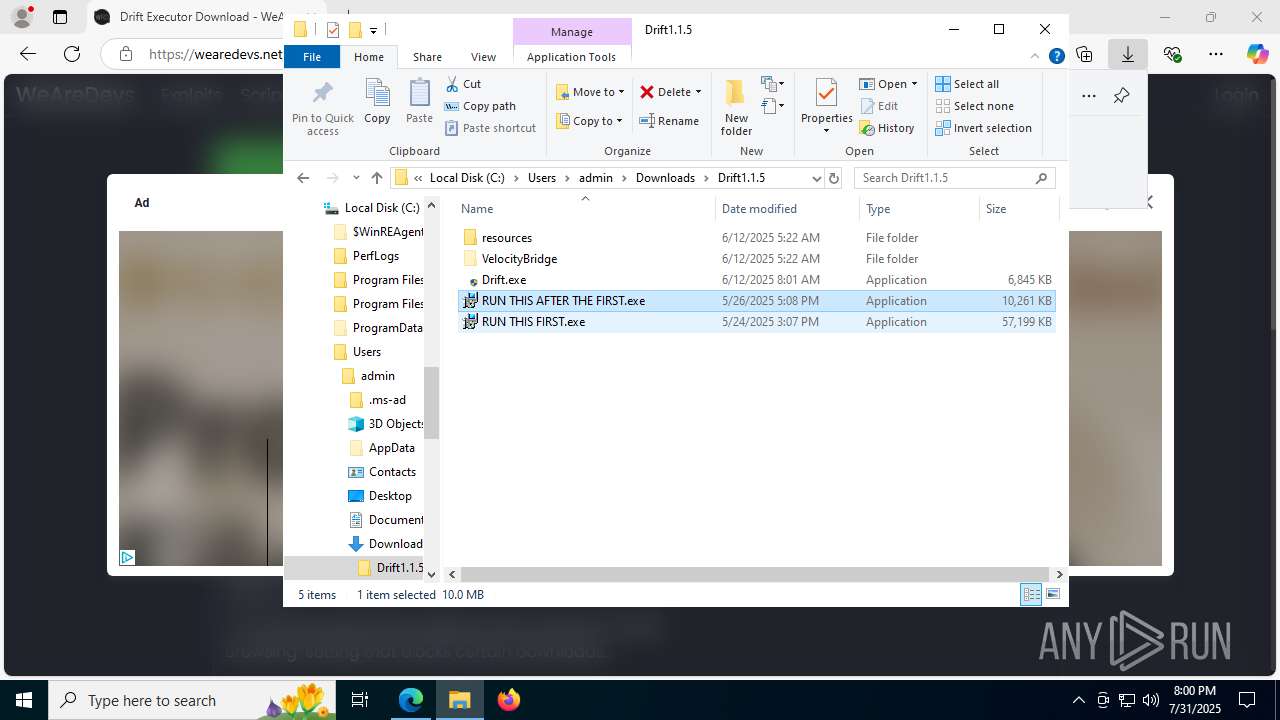
Process drops legitimate windows executable
- WinRAR.exe (PID: 7516)
- RUN THIS FIRST.exe (PID: 7904)
- msiexec.exe (PID: 5060)
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- RUN THIS AFTER THE FIRST.exe (PID: 7604)
- RUN THIS FIRST.exe (PID: 7748)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
Starts a Microsoft application from unusual location
- RUN THIS FIRST.exe (PID: 7748)
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
Executable content was dropped or overwritten
- RUN THIS FIRST.exe (PID: 7748)
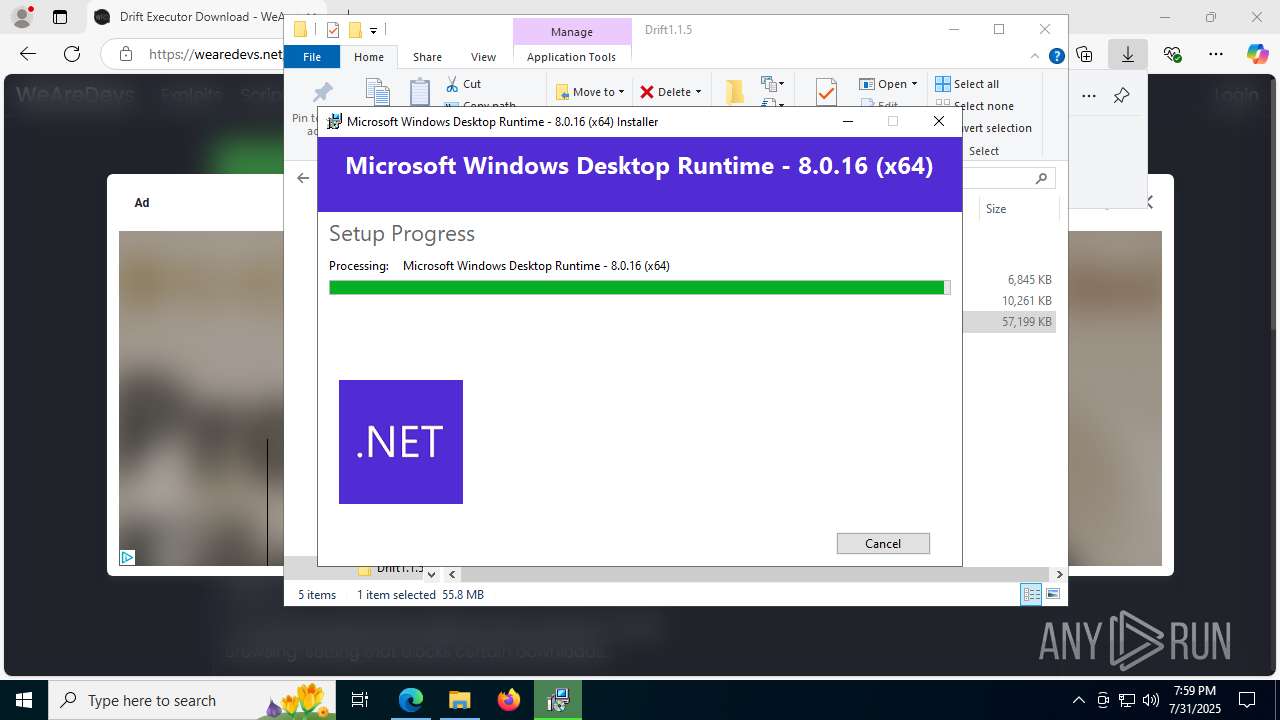
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- RUN THIS AFTER THE FIRST.exe (PID: 7604)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
- Drift.exe (PID: 1864)
- RUN THIS FIRST.exe (PID: 7904)
- VelocityBridge.exe (PID: 2124)
Reads security settings of Internet Explorer
- RUN THIS FIRST.exe (PID: 7748)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
Searches for installed software
- RUN THIS FIRST.exe (PID: 7748)
- dllhost.exe (PID: 7472)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5060)
The process creates files with name similar to system file names
- msiexec.exe (PID: 5060)
The process drops C-runtime libraries
- msiexec.exe (PID: 5060)
Starts itself from another location
- RUN THIS FIRST.exe (PID: 7748)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
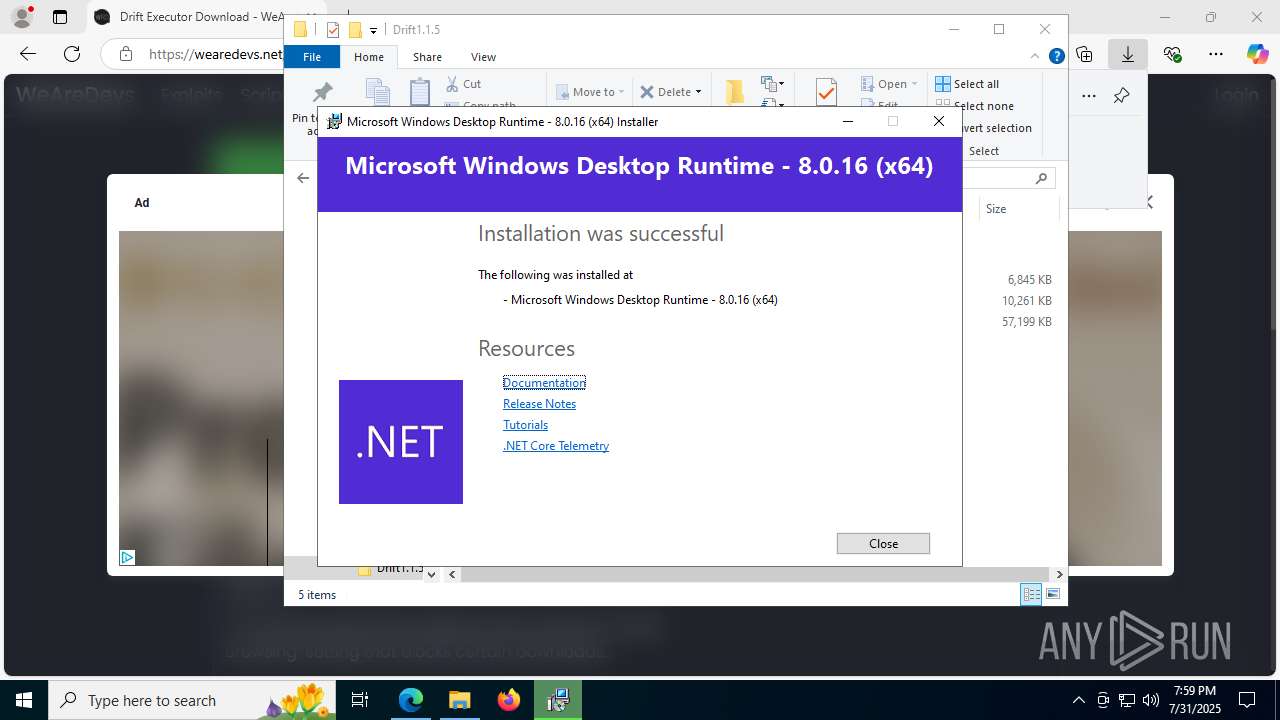
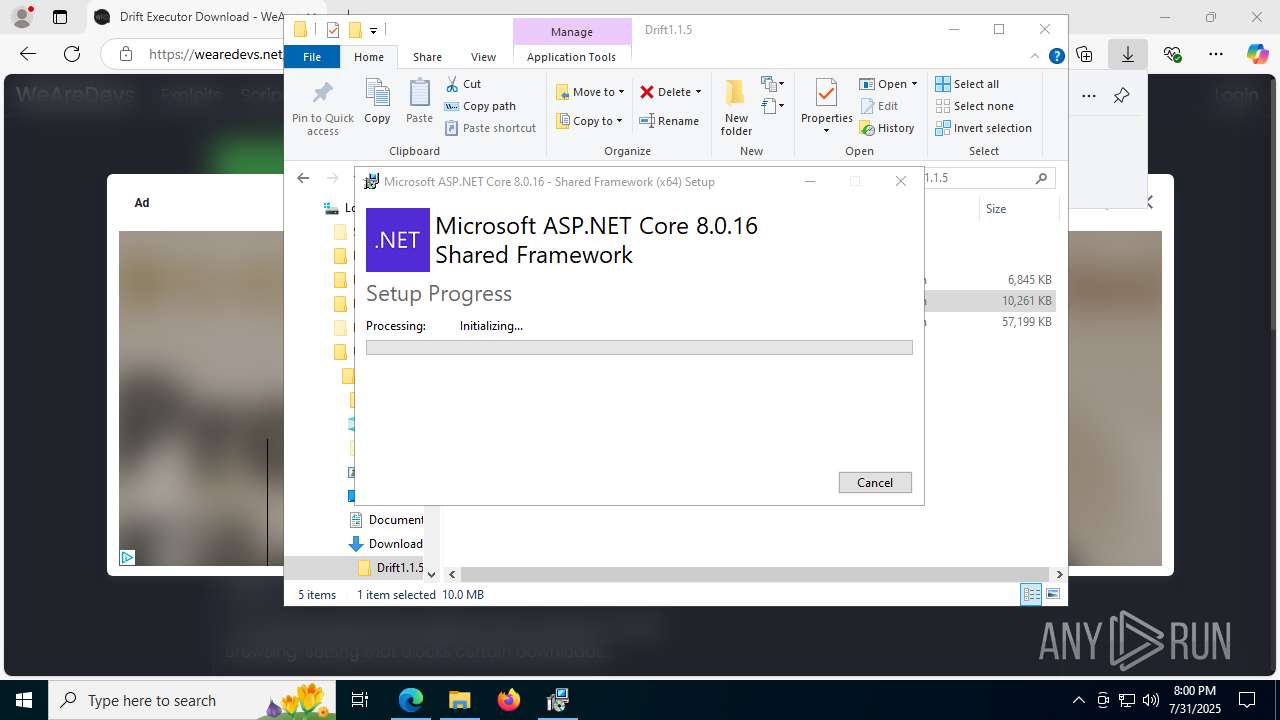
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
The process executes Powershell scripts
- Drift.exe (PID: 1864)
Executes as Windows Service
- VSSVC.exe (PID: 7200)
Starts POWERSHELL.EXE for commands execution
- Drift.exe (PID: 1864)
Executing commands from a ".bat" file
- powershell.exe (PID: 7244)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7244)
The executable file from the user directory is run by the CMD process
- VelocityBridge.exe (PID: 2124)
INFO
Reads Environment values
- identity_helper.exe (PID: 7720)
Reads the computer name
- identity_helper.exe (PID: 7720)
- RUN THIS FIRST.exe (PID: 7748)
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- msiexec.exe (PID: 5060)
- msiexec.exe (PID: 1980)
- msiexec.exe (PID: 7512)
- msiexec.exe (PID: 4084)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
- msiexec.exe (PID: 7496)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
- Drift.exe (PID: 1864)
- msiexec.exe (PID: 5500)
- Drift.exe (PID: 4676)
- VelocityBridge.exe (PID: 2124)
- Drift.exe (PID: 8144)
Application launched itself
- msedge.exe (PID: 6788)
The sample compiled with english language support
- RUN THIS FIRST.exe (PID: 7904)
- RUN THIS FIRST.exe (PID: 7748)
- WinRAR.exe (PID: 7516)
- msiexec.exe (PID: 5060)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
- RUN THIS AFTER THE FIRST.exe (PID: 7604)
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
Checks supported languages
- identity_helper.exe (PID: 7720)
- RUN THIS FIRST.exe (PID: 7904)
- RUN THIS FIRST.exe (PID: 7748)
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- msiexec.exe (PID: 7496)
- msiexec.exe (PID: 7512)
- msiexec.exe (PID: 4084)
- RUN THIS AFTER THE FIRST.exe (PID: 7604)
- msiexec.exe (PID: 5060)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
- msiexec.exe (PID: 1980)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
- msiexec.exe (PID: 5500)
- Drift.exe (PID: 1864)
- Drift.exe (PID: 4676)
- VelocityBridge.exe (PID: 2124)
- Drift.exe (PID: 8144)
- Decompiler.exe (PID: 420)
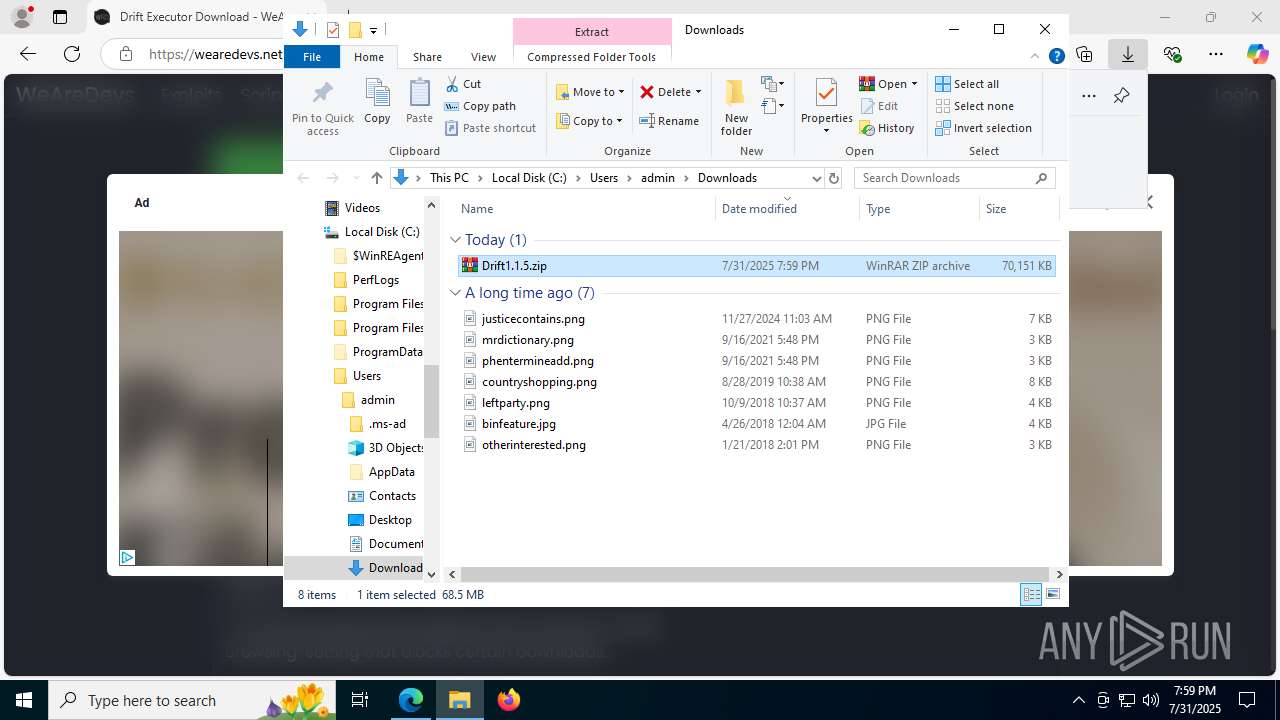
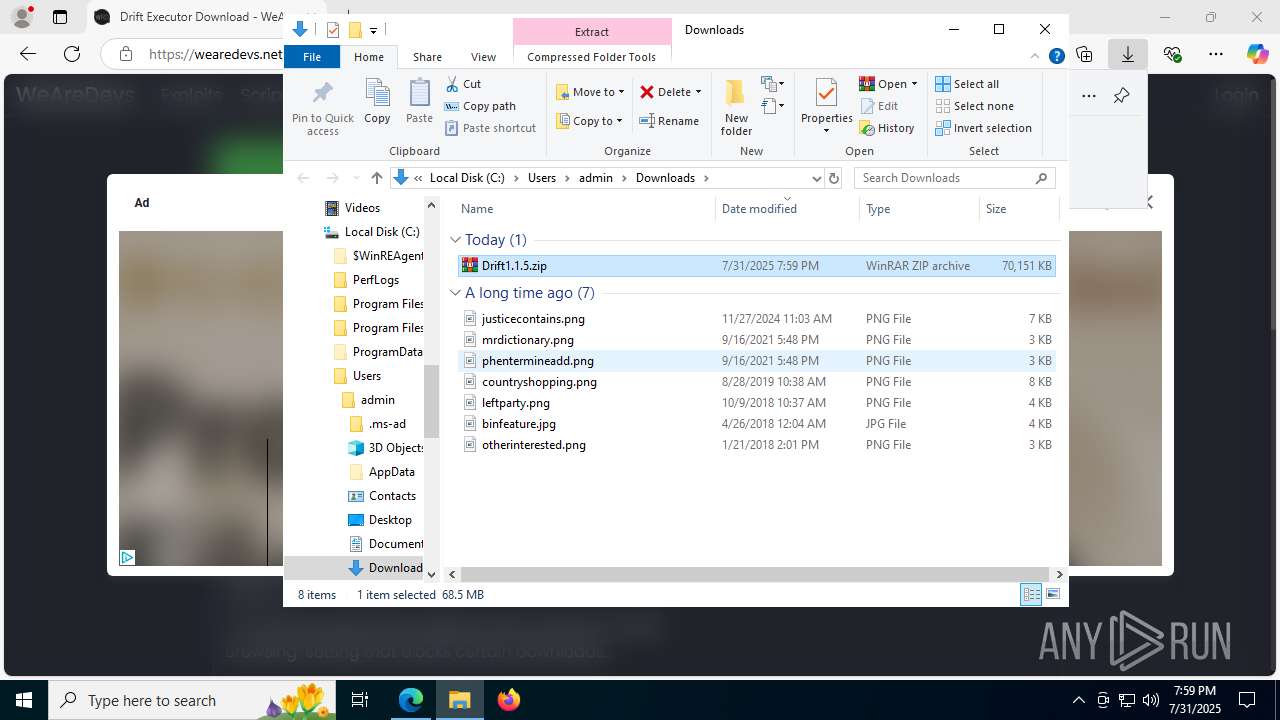
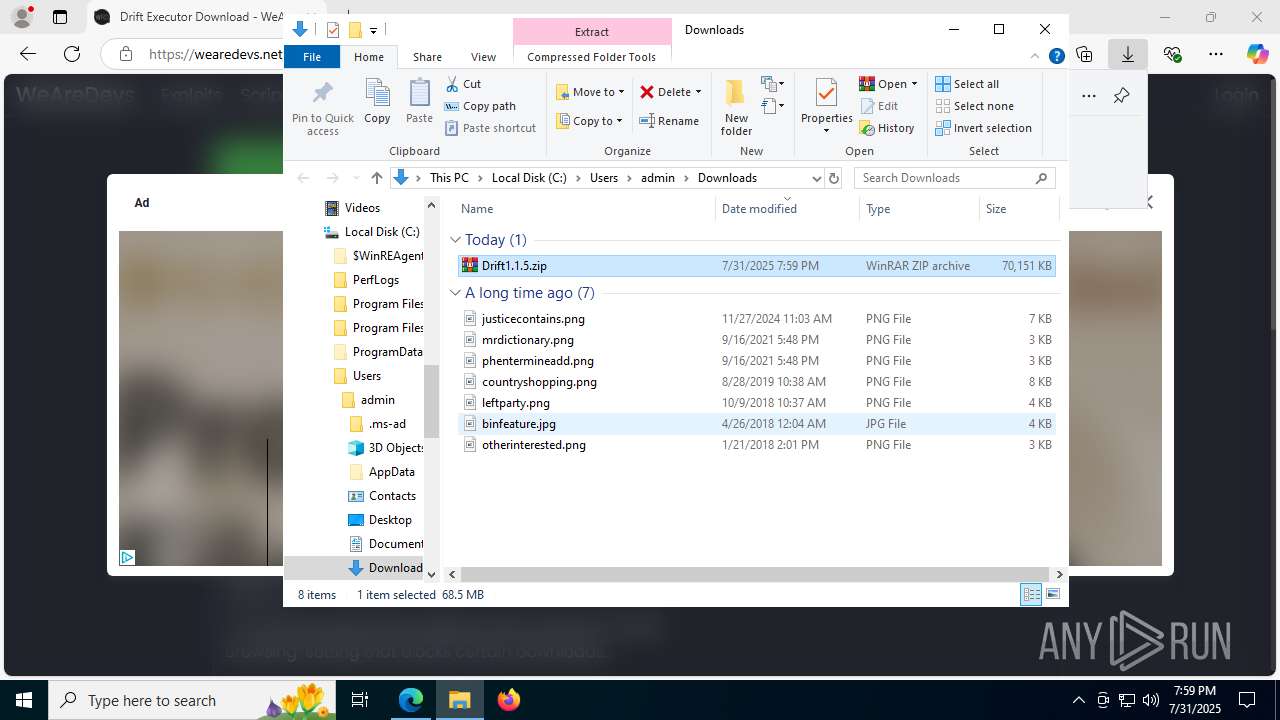
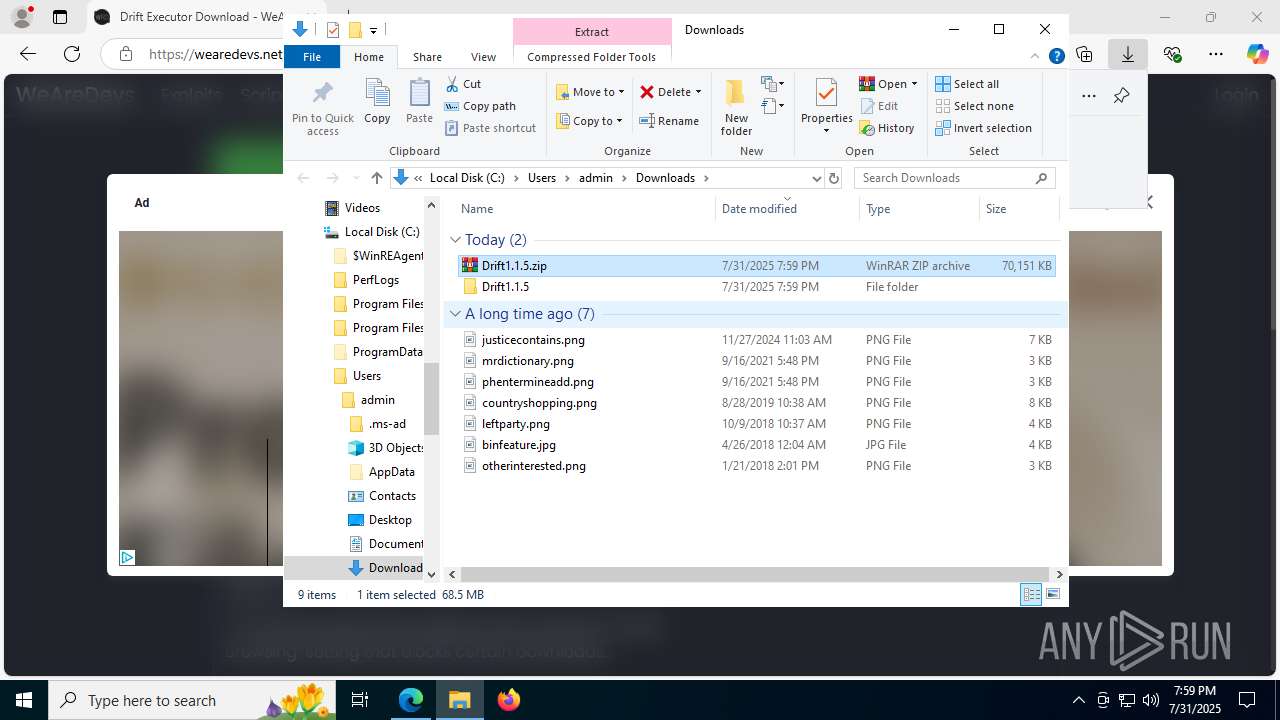
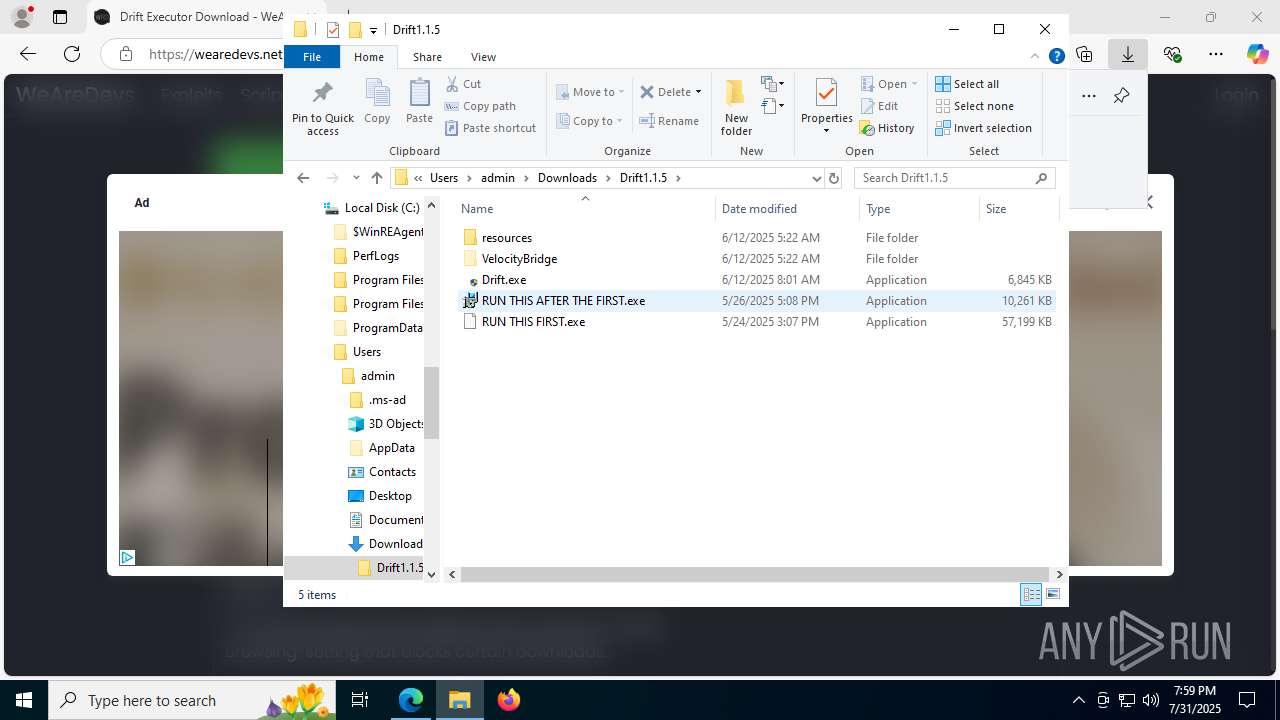
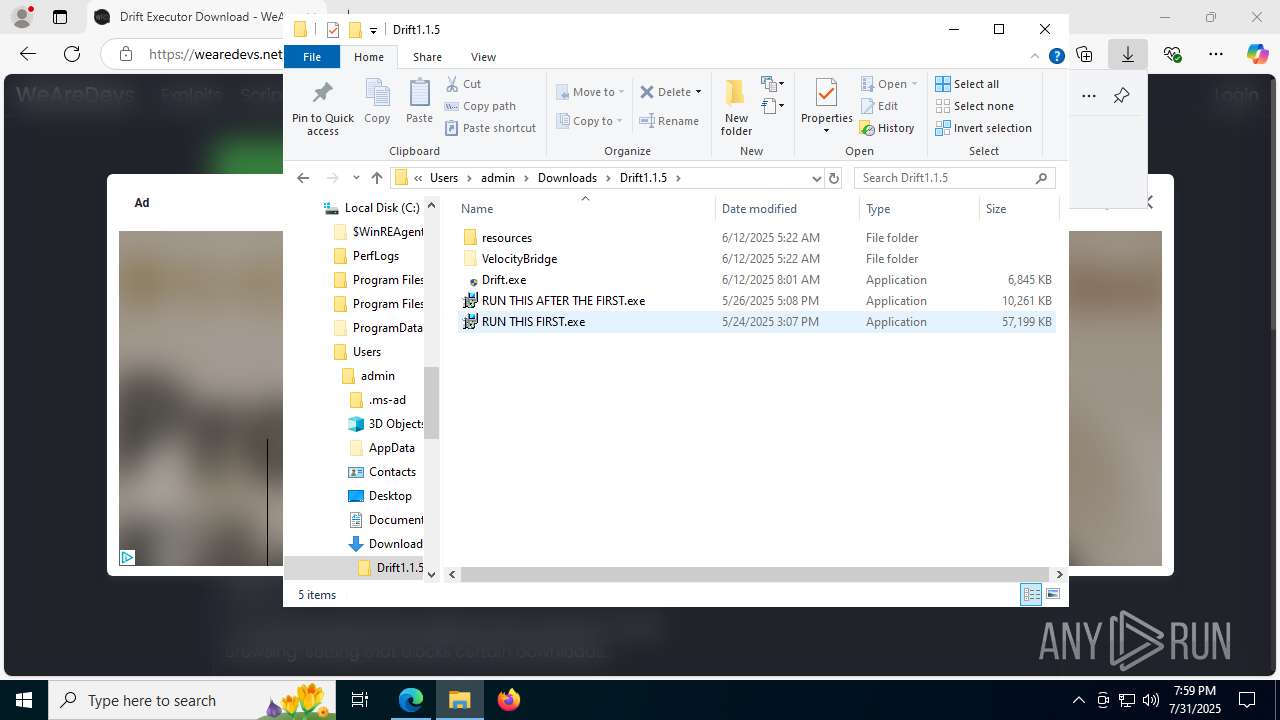
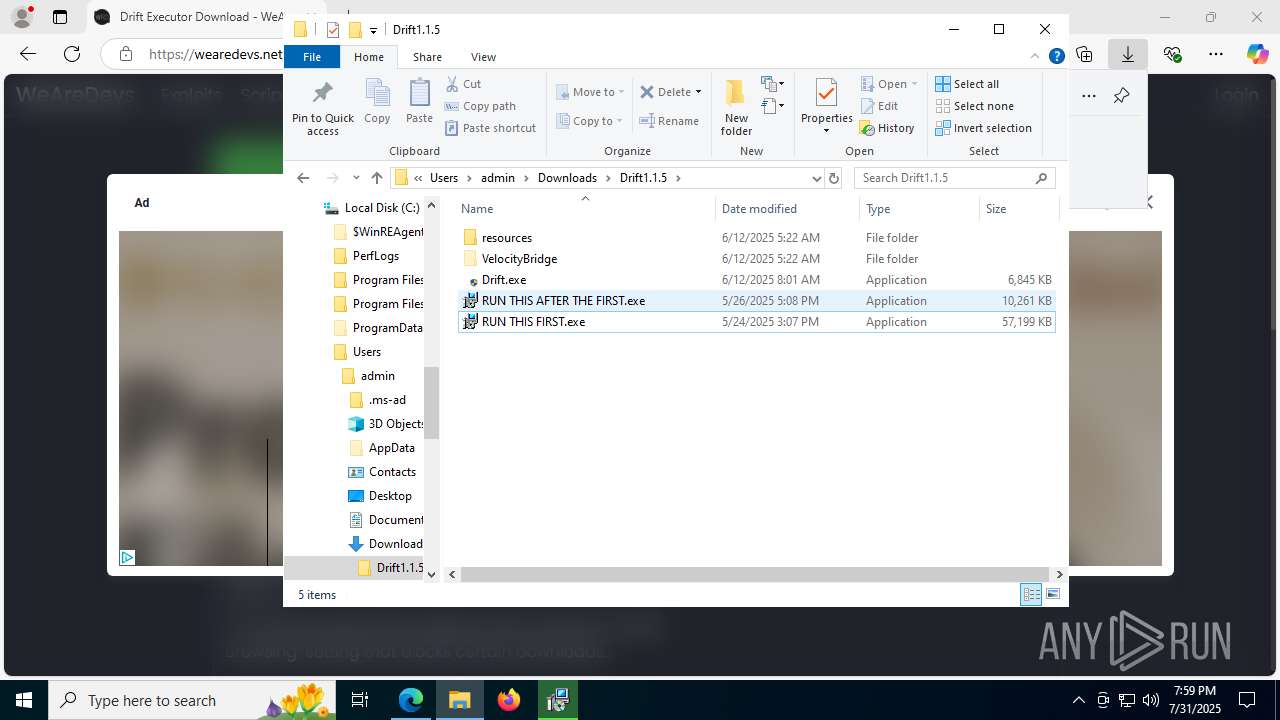
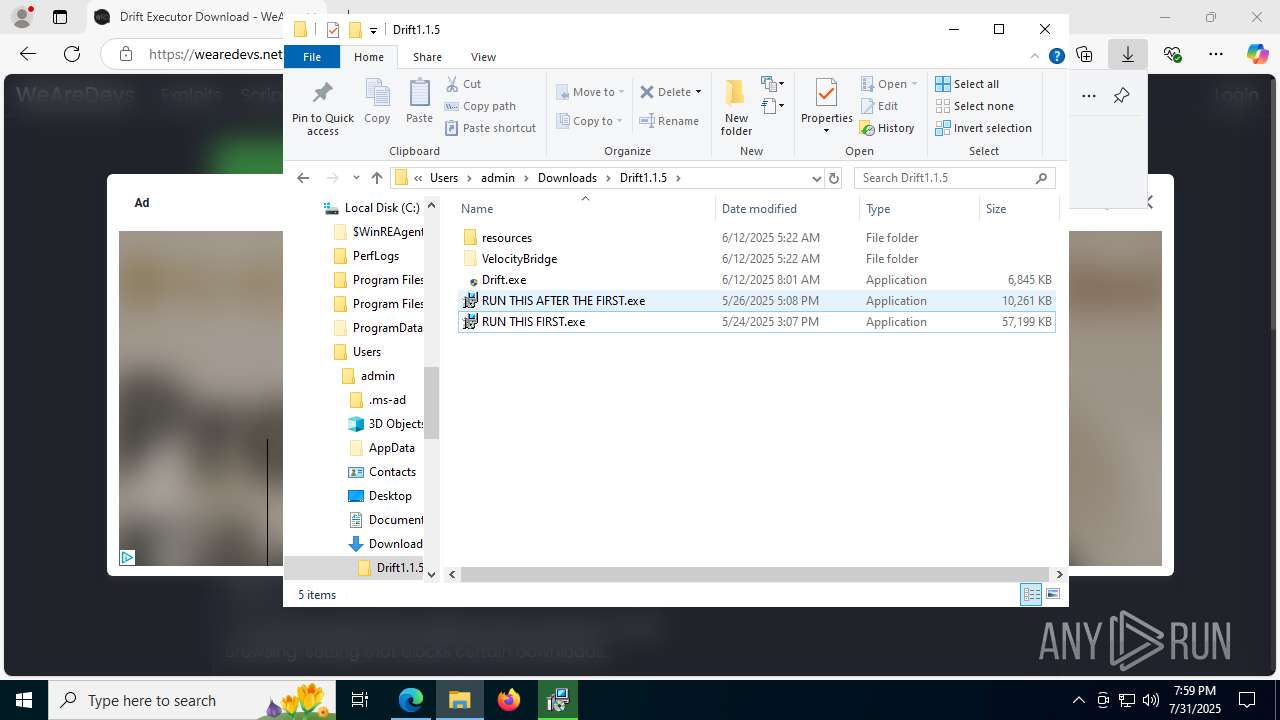
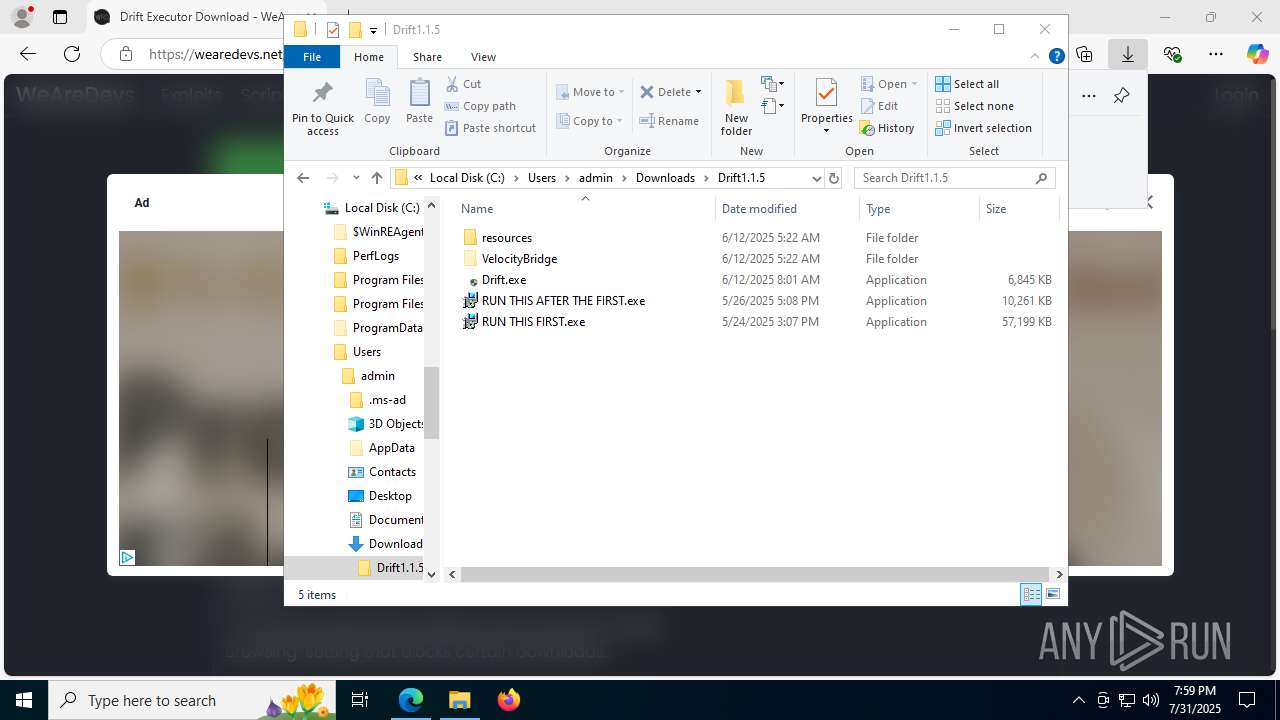
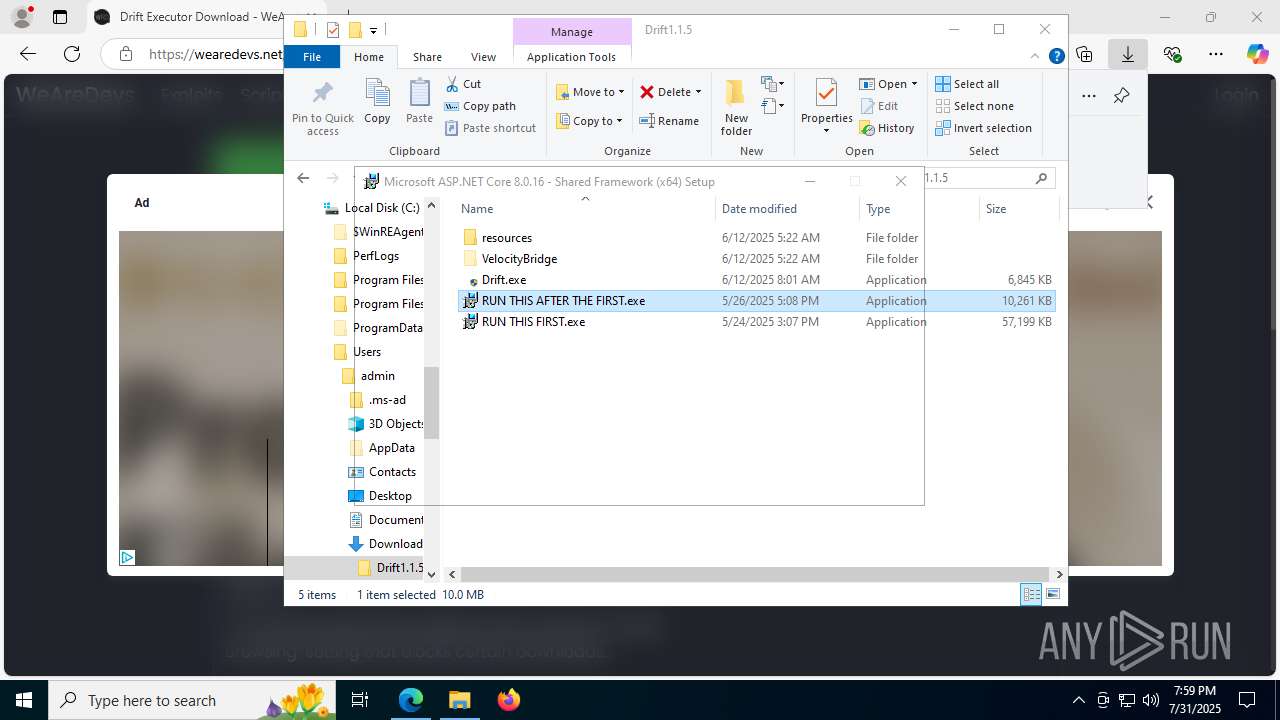
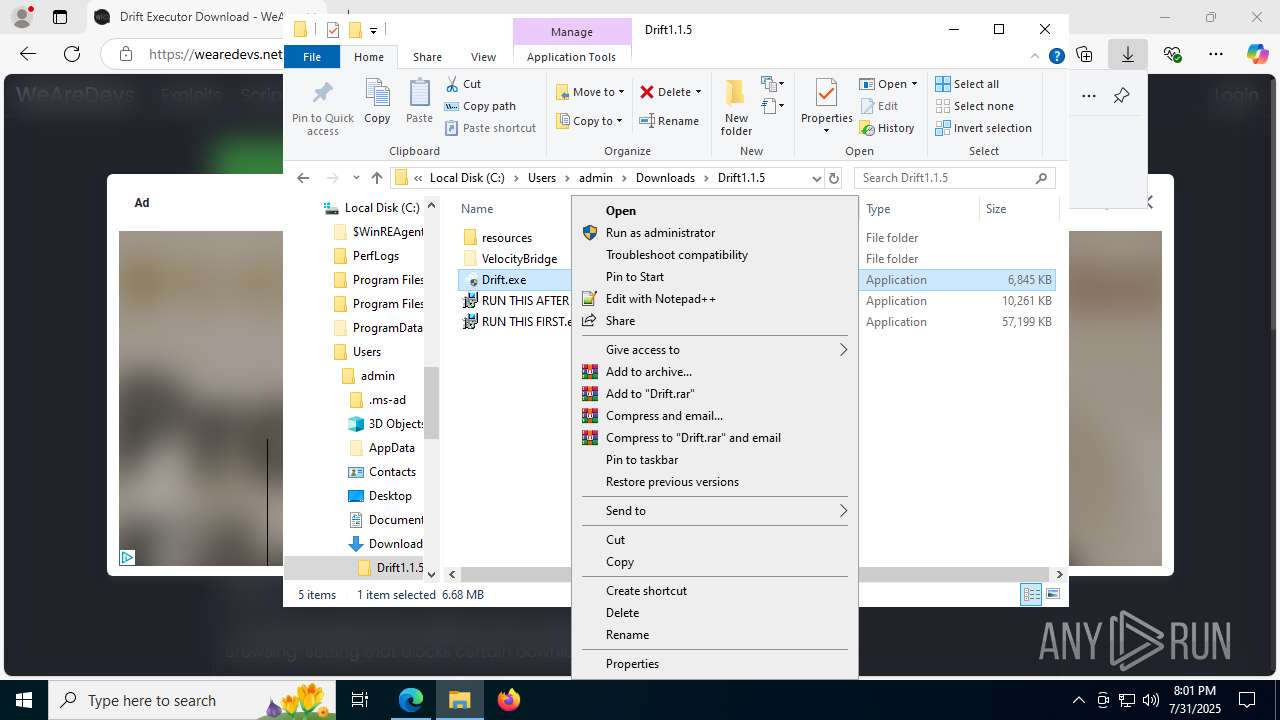
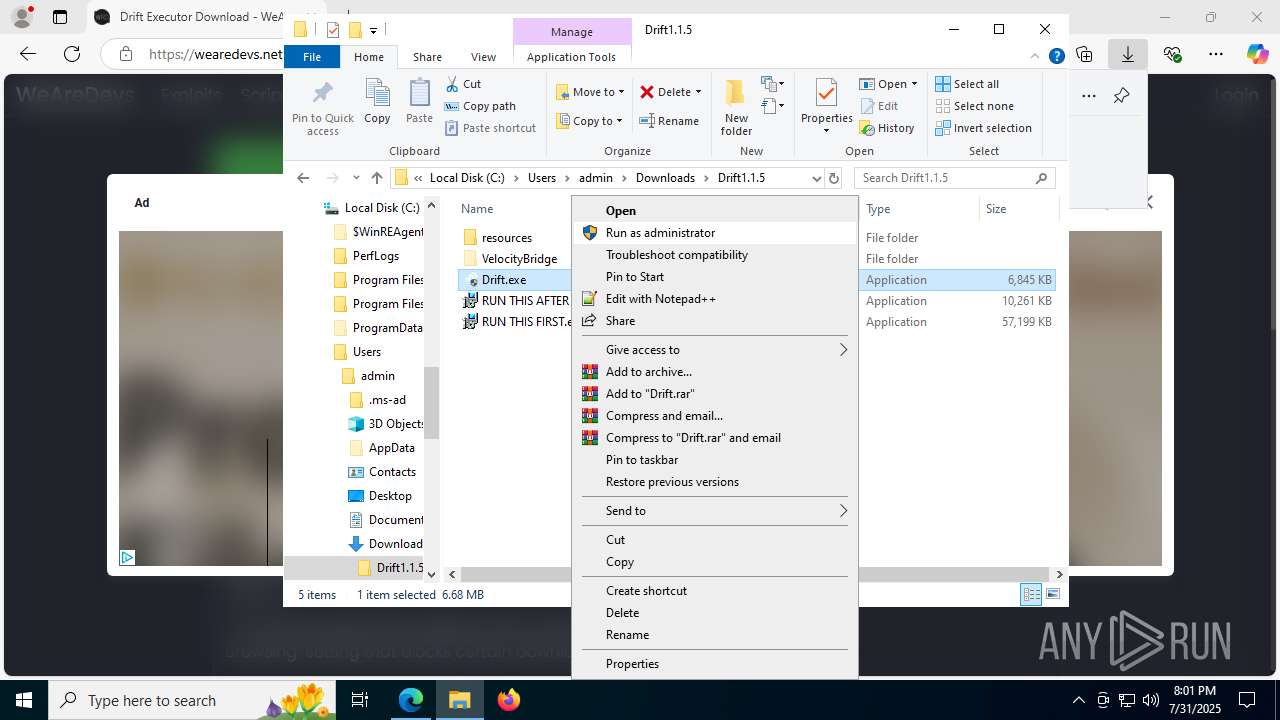
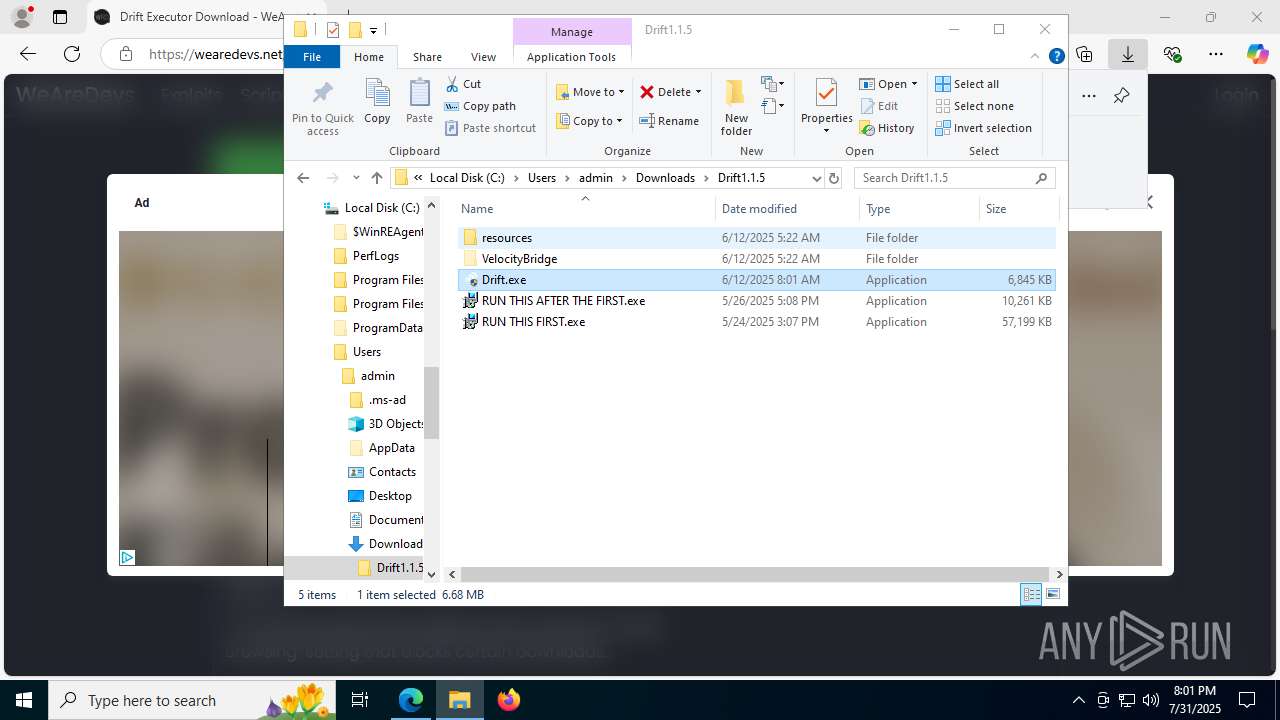
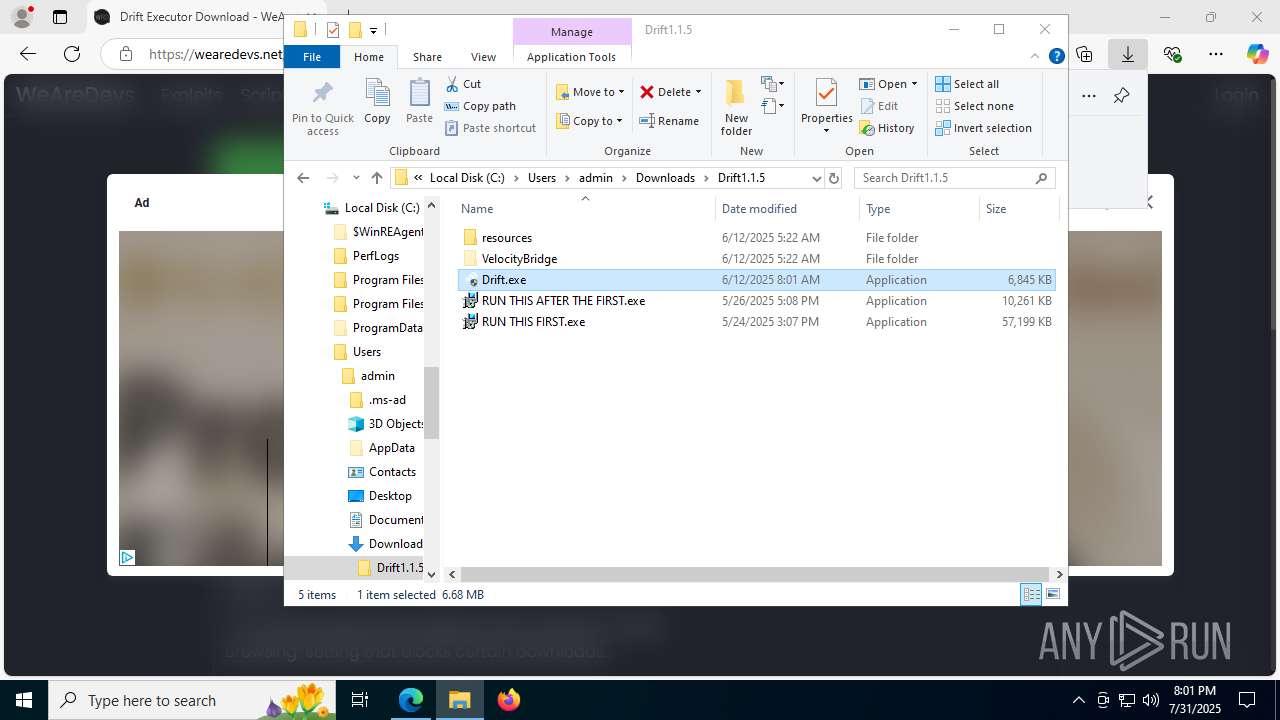
Manual execution by a user
- WinRAR.exe (PID: 7516)
- RUN THIS FIRST.exe (PID: 7904)
- RUN THIS AFTER THE FIRST.exe (PID: 7604)
- Drift.exe (PID: 1864)
- Drift.exe (PID: 7828)
- Drift.exe (PID: 6372)
- Drift.exe (PID: 4676)
- Drift.exe (PID: 8144)
Create files in a temporary directory
- RUN THIS FIRST.exe (PID: 7748)
- RUN THIS FIRST.exe (PID: 7904)
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- RUN THIS AFTER THE FIRST.exe (PID: 7604)
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
Reads the machine GUID from the registry
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- msiexec.exe (PID: 5060)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
Launching a file from a Registry key
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
Creates files in the program directory
- windowsdesktop-runtime-8.0.16-win-x64.exe (PID: 7680)
- AspNetCoreSharedFrameworkBundle-x64.exe (PID: 7968)
- VelocityBridge.exe (PID: 2124)
Reads the software policy settings
- msiexec.exe (PID: 5060)
- VelocityBridge.exe (PID: 2124)
- slui.exe (PID: 868)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5060)
- WinRAR.exe (PID: 7516)
Creates a software uninstall entry
- msiexec.exe (PID: 5060)
Process checks computer location settings
- RUN THIS AFTER THE FIRST.exe (PID: 7628)
- RUN THIS FIRST.exe (PID: 7748)
Manages system restore points
- SrTasks.exe (PID: 7416)
Checks proxy server information
- Drift.exe (PID: 1864)
- Drift.exe (PID: 4676)
- Drift.exe (PID: 8144)
- VelocityBridge.exe (PID: 2124)
- slui.exe (PID: 868)
Creates files or folders in the user directory
- Drift.exe (PID: 1864)
- VelocityBridge.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
215
Monitored processes
65
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "Bin\Decompiler.exe" | C:\Users\admin\AppData\Roaming\Drift\Bridge\Bin\Bin\Decompiler.exe | — | VelocityBridge.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 868 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5656,i,13662469101712084448,4173237981940730210,262144 --variations-seed-version --mojo-platform-channel-handle=1608 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3636,i,13662469101712084448,4173237981940730210,262144 --variations-seed-version --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4344,i,13662469101712084448,4173237981940730210,262144 --variations-seed-version --mojo-platform-channel-handle=3456 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\Downloads\Drift1.1.5\Drift.exe" | C:\Users\admin\Downloads\Drift1.1.5\Drift.exe | explorer.exe | ||||||||||||
User: admin Company: drift Integrity Level: HIGH Description: Drift Version: 0.1.0 Modules
| |||||||||||||||
| 1980 | C:\Windows\syswow64\MsiExec.exe -Embedding 63D5BF1DEB5BE0F0554492E0BA254E60 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3948,i,13662469101712084448,4173237981940730210,262144 --variations-seed-version --mojo-platform-channel-handle=6716 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4976,i,13662469101712084448,4173237981940730210,262144 --variations-seed-version --mojo-platform-channel-handle=7780 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2124 | "C:\\Users\\admin\\AppData\\Roaming\\Drift\\Bridge\\VelocityBridge.exe" 18123 | C:\Users\admin\AppData\Roaming\Drift\Bridge\VelocityBridge.exe | cmd.exe | ||||||||||||
User: admin Company: VelocityBridge Integrity Level: HIGH Description: VelocityBridge Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
26 225
Read events
24 808
Write events
1 338
Delete events
79
Modification events
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DC5F8D5AD5992F00 | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1835042 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A31A9274-FD2F-4366-AA06-8CF7B2F29F25} | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1835042 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {90E6A548-9DF1-44FD-AC23-4C5F71AA870A} | |||
| (PID) Process: | (6788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1835042 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D159B9FC-62D4-4C44-AEA8-DF4AF545CFC3} | |||
Executable files
641
Suspicious files
343
Text files
124
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d7dd.TMP | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d7ec.TMP | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d7ec.TMP | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d7ec.TMP | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d7fc.TMP | — | |
MD5:— | SHA256:— | |||
| 6788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
134
DNS requests
131
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7924 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3876 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1754372421&P2=404&P3=2&P4=UXUUaGFuLi29Oe6u%2bXIbs%2bSxAfpEFlDvHyLZKJK9%2bDI8ZwBWFoSAIVXmawVlbjUC%2b63zzcxogMQ8byctu8EMgw%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.31:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3876 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754372419&P2=404&P3=2&P4=GG8WZLCO3TaSGdL9e9rTAlEONDXL8rxamFff3Xk0llpmtl8s6Jnek2Hku4Xr7WVWhTaWNxOzW%2bFl9x96u9mbpA%3d%3d | unknown | — | — | whitelisted |
3876 | svchost.exe | GET | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6b853aed-57d0-44a7-b8d5-4cdd01a61f64?P1=1754372421&P2=404&P3=2&P4=fRBcFbUz2TtsGzIceDE47s9O178bmw888oxp1E%2f2lJpw7vko%2b36IabBOSxnfXC4VpPR%2bDZ6BrETdEAmLdUthpg%3d%3d | unknown | — | — | whitelisted |
3876 | svchost.exe | GET | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1754372422&P2=404&P3=2&P4=E8980E7v%2f0nEO8V8AraaFA97F906zcO1BfdyPOELKY%2fK4MUplGz0jsuE%2f%2bteqXIbyzSXFBWwD69w0crhpwpijA%3d%3d | unknown | — | — | whitelisted |
3876 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1754376021&P2=404&P3=2&P4=lygHUlz974piv4V%2fBA%2fF%2b81%2fC1A4yLwt9MBFGR4PML16IciyhuAfOuEpZXYjjuXx26LjVllX6QLWp24YrGoM1Q%3d%3d | unknown | — | — | whitelisted |
3876 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6b853aed-57d0-44a7-b8d5-4cdd01a61f64?P1=1754372421&P2=404&P3=2&P4=fRBcFbUz2TtsGzIceDE47s9O178bmw888oxp1E%2f2lJpw7vko%2b36IabBOSxnfXC4VpPR%2bDZ6BrETdEAmLdUthpg%3d%3d | unknown | — | — | whitelisted |
3460 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:uoyxzk6Zk10R4XiAQAmndLau6u0UVkN7B-2kLRAVRXE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1380 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3460 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3460 | msedge.exe | 142.250.186.40:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
3460 | msedge.exe | 142.250.185.131:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3460 | msedge.exe | 142.250.185.130:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
3460 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
wearedevs.net |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
unpkg.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3460 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
3460 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3460 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3460 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3460 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3460 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
Process | Message |
|---|---|
Drift.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Drift.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Drift.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Drift.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Drift.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Drift.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|