| File name: | UltraUXThemePatcher_4.4.4.exe |
| Full analysis: | https://app.any.run/tasks/86c3c787-426a-4510-b01b-cdcac65de0ca |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 15:50:54 |
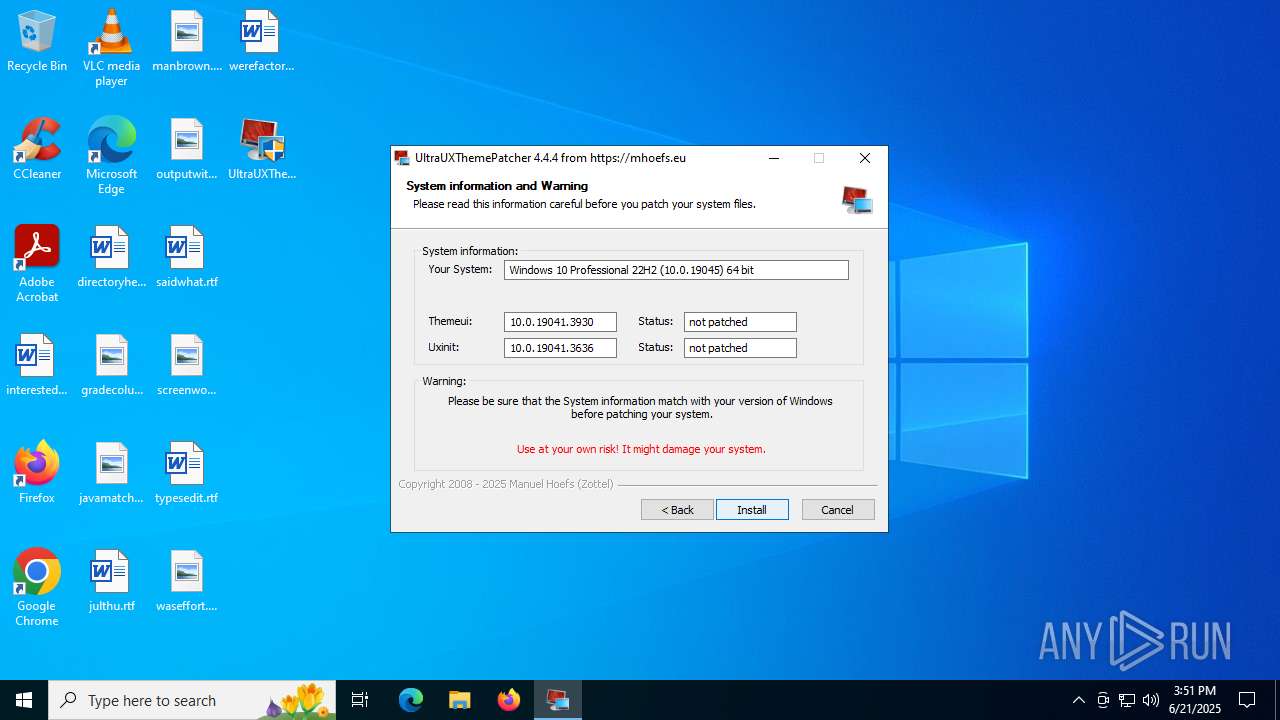
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 3276BF178249904F4E9AC0958F32D906 |
| SHA1: | 8C8421055DE59718EFF8C535F3B447132B5322F1 |
| SHA256: | 9945195D54509CA4E8A41E468851137A56F711163D4FCBE4A8692ED24023A739 |
| SSDEEP: | 3072:89Y63Sq4u9dC3Sn1aJnys0Qgnio9XL9F3SbdCvzNCv5HhQDem17tP1q/:HKSyASn1GneQgniYDSxCpMZhQDV17Jk/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Executable content was dropped or overwritten
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Searches for installed software
- dllhost.exe (PID: 5780)
The process creates files with name similar to system file names
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
There is functionality for taking screenshot (YARA)
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Reads security settings of Internet Explorer
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
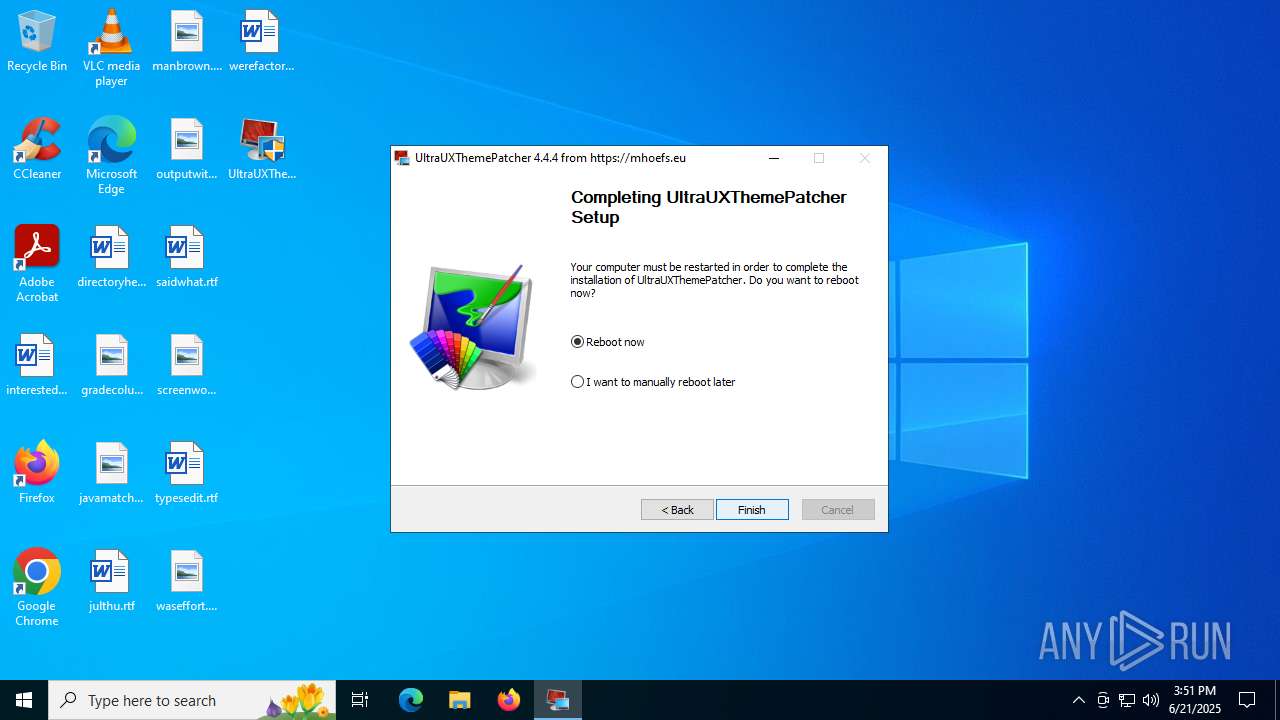
Executes as Windows Service
- VSSVC.exe (PID: 6796)
Uses ICACLS.EXE to modify access control lists
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Takes ownership (TAKEOWN.EXE)
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Creates a software uninstall entry
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Process drops legitimate windows executable
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4148)
- updater.exe (PID: 4132)
Application launched itself
- updater.exe (PID: 4132)
INFO
The sample compiled with english language support
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Checks supported languages
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
- PLUGScheduler.exe (PID: 4148)
- updater.exe (PID: 4132)
- updater.exe (PID: 5052)
Create files in a temporary directory
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Reads Environment values
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Reads the computer name
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
- PLUGScheduler.exe (PID: 4148)
- updater.exe (PID: 4132)
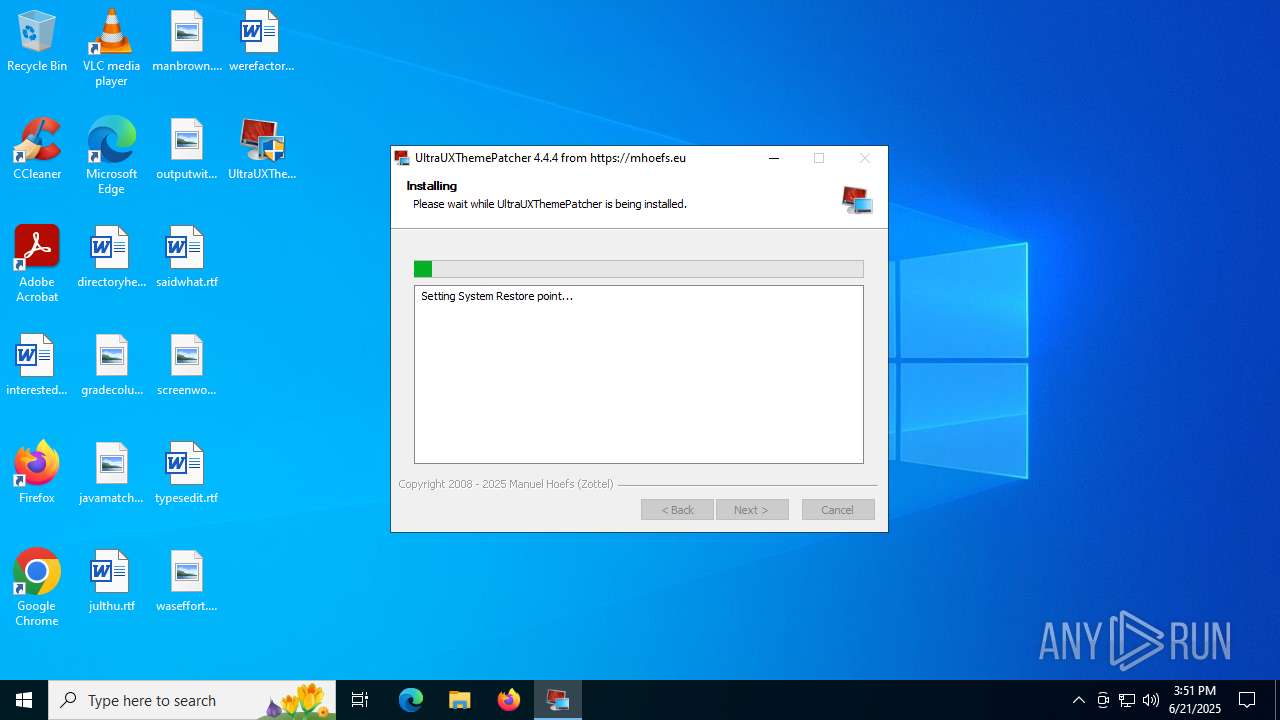
Manages system restore points
- SrTasks.exe (PID: 2532)
Creates files in the program directory
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
- PLUGScheduler.exe (PID: 4148)
Creates files or folders in the user directory
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Process checks computer location settings
- UltraUXThemePatcher_4.4.4.exe (PID: 1644)
Process checks whether UAC notifications are on
- updater.exe (PID: 4132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:08 23:05:20+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x369f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.4.4.0 |
| ProductVersionNumber: | 4.4.4.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | UltraUXThemePatcher modifies your system file(s) to use 3rd party themes |
| CompanyName: | Manuel Hoefs (Zottel) |
| FileDescription: | Windows UltraUXThemePatcher |
| FileVersion: | 4.4.4.0 |
| InternalName: | UltraUXThemePatcher_4.4.4 |
| LegalCopyright: | 2008 - 2025 Manuel Hoefs (Zottel) |
| LegalTrademarks: | UltraUXThemePatcher created by Manuel Hoefs (Zottel) |
| OriginalFileName: | UltraUXThemePatcher_4.4.4.exe |
| ProductName: | UltraUXThemePatcher |
| ProductVersion: | 4.4.4.0 |
| Website: | https://mhoefs.eu |
Total processes
278
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1568 | "C:\Users\admin\Desktop\UltraUXThemePatcher_4.4.4.exe" | C:\Users\admin\Desktop\UltraUXThemePatcher_4.4.4.exe | — | explorer.exe | |||||||||||
User: admin Company: Manuel Hoefs (Zottel) Integrity Level: MEDIUM Description: Windows UltraUXThemePatcher Exit code: 3221226540 Version: 4.4.4.0 Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\Desktop\UltraUXThemePatcher_4.4.4.exe" | C:\Users\admin\Desktop\UltraUXThemePatcher_4.4.4.exe | explorer.exe | ||||||||||||
User: admin Company: Manuel Hoefs (Zottel) Integrity Level: HIGH Description: Windows UltraUXThemePatcher Exit code: 0 Version: 4.4.4.0 Modules
| |||||||||||||||
| 1688 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | takeown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1816 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | takeown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2532 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | "C:\WINDOWS\system32\takeown.exe" /f "C:\WINDOWS\system32\uxinit.dll" | C:\Windows\System32\takeown.exe | — | UltraUXThemePatcher_4.4.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3844 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3964 | "C:\WINDOWS\system32\icacls.exe" "C:\WINDOWS\system32\uxinit.dll" /grant admin:F | C:\Windows\System32\icacls.exe | — | UltraUXThemePatcher_4.4.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | takeown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 303
Read events
2 103
Write events
182
Delete events
18
Modification events
| (PID) Process: | (1644) UltraUXThemePatcher_4.4.4.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000606E2958C4E2DB016C0600006C040000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5780) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000D0DA8858C4E2DB0194160000AC0F0000E803000001000000000000000000000089FBC472363F5245AFF00FC79F05918500000000000000000000000000000000 | |||
| (PID) Process: | (6796) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000D1BA9458C4E2DB018C1A0000AC080000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6796) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009E1E9758C4E2DB018C1A0000FC0E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6796) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009E1E9758C4E2DB018C1A000080170000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6796) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009E1E9758C4E2DB018C1A0000C0040000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6796) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6796) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (6796) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6796) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
Executable files
13
Suspicious files
45
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5780 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Users\admin\AppData\Local\Temp\nsp736D.tmp\modern-wizard.bmp | image | |
MD5:5F728E4E6B970DB76C64BE8CA3CAFC87 | SHA256:AEA40659BDB08337064640EA8B4F171881D37456B37B3E2899349AC04F0889C5 | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Windows\System32\themeui.dll.backup | executable | |
MD5:DD04F37E7E19F9BCBCCE3119D2B30D2F | SHA256:69B401FF2CF6762E18B5665B40CFE2DDC143DCF7DA1C635036844A745918E67D | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Users\admin\AppData\Local\Temp\nsp736D.tmp\nsDialogs.dll | executable | |
MD5:8F0E7415F33843431DF308BB8E06AF81 | SHA256:BB49F15FA83452370047A7801E39FC7F64E70C7545B8999BB85AA4749EAA048B | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Windows\System32\themeui.dll.new | executable | |
MD5:DD04F37E7E19F9BCBCCE3119D2B30D2F | SHA256:69B401FF2CF6762E18B5665B40CFE2DDC143DCF7DA1C635036844A745918E67D | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Users\admin\AppData\Local\Temp\nsp736D.tmp\nsisFile.dll | executable | |
MD5:B7D0D765C151D235165823B48554E442 | SHA256:A820A32E5CE89E3E336AFC71AA1BF42A357EC542C2BC6E50C6255C1333812587 | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Windows\System32\themeui.dll | executable | |
MD5:4F35DDBD4DC36620C3EA7D06E72E03A8 | SHA256:11BD7A8181475226BBB5F094E5B8D5B84501FEA74500CC04D05959DA1D689F94 | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Windows\System32\uxinit.dll.backup | executable | |
MD5:F125A0876D8684A04F4BABD010DAF904 | SHA256:D45894E386AA667220EA8B5397A82449EDC8E977EE1EA8CB2B78FFEE2A64A73B | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Windows\System32\uxinit.dll | executable | |
MD5:40C064486D8D485BCCB0020EE33CCF8A | SHA256:F5D9874C6FF19307DA15FEFF354C7CD755945B7BACA6F3B6022B8347EB34CEFC | |||
| 1644 | UltraUXThemePatcher_4.4.4.exe | C:\Windows\System32\uxinit.dll.old | executable | |
MD5:F125A0876D8684A04F4BABD010DAF904 | SHA256:D45894E386AA667220EA8B5397A82449EDC8E977EE1EA8CB2B78FFEE2A64A73B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
25
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.227.208:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | binary | 21.3 Kb | whitelisted |
4960 | RUXIMICS.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 204 | 2.23.227.208:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rb/19/cir3,ortl,cc,nc/FgBbpIj0thGWZOh_xFnM9i4O7ek.css?bu=C8YL-ASFBpYM_wrpCt0IaWlpaQ&or=w | unknown | text | 19.8 Kb | whitelisted |
— | — | GET | 200 | 2.23.227.208:443 | https://www.bing.com/rb/6i/cir3,ortl,cc,nc/LJVpDXTkWDgGwVlLgxLZkLutWKw.css?bu=Me8K6Ar1CugK2wvoCuEL6ArsC-gK8wvoCvkL6Ar_C-gKhQzoCocL6AqNC-gKgQvoCugK0gvoCpwL6AqiC-gKlgvoCugKsQu0C-gK6ArPC70L6ArDC8YL6AqxDOgKiwzoCuoM&or=w | unknown | text | 479 Kb | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rb/3D/ortl,cc,nc/AptopUBu7_oVDubJxwvaIprW-lI.css?bu=A4gCjAKPAg&or=w | unknown | text | 15.5 Kb | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rb/6i/ortl,cc,nc/NajusmjIqB4kdLn9FmVxeS4xi2o.css?bu=CdcM6AroCugK6AroCugK6AroCg&or=w | unknown | text | 44.7 Kb | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rp/-iNIzuEypRdgRJ6xnyVHizZ3bpM.br.js | unknown | binary | 17.0 Kb | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rp/3-X3h7uDMtfcne46mFDSZyqDAWs.br.js | unknown | binary | 407 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4960 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
4960 | RUXIMICS.exe | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4960 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |