| File name: | hack_761_34644.exe |
| Full analysis: | https://app.any.run/tasks/575659ba-9038-4a3b-8ae3-be88c6e9b1d2 |
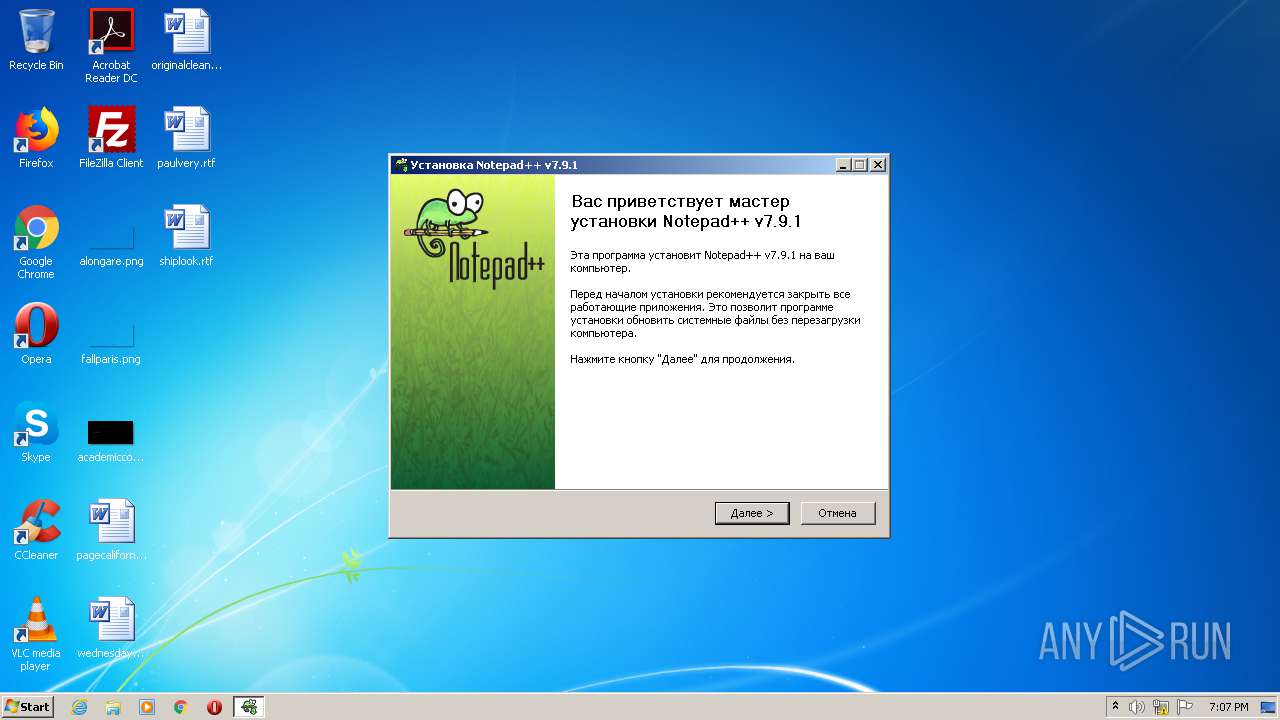
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 19:07:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C393E1863063EE6546C7108C73CCAE6D |
| SHA1: | 5F43FC499E2FC18EC0E556DD204567DDF0E5A542 |
| SHA256: | 9941D688B5F73420891C87D90A6D6B7C59355A7A964AD1DE7519E7E01BED9392 |
| SSDEEP: | 24576:kOFo4F2qsze+XMhQatYNTfDfVtykR3CGpRJmuaL:ySEzzMhQaSNDDtQcyGrJmX |
MALICIOUS
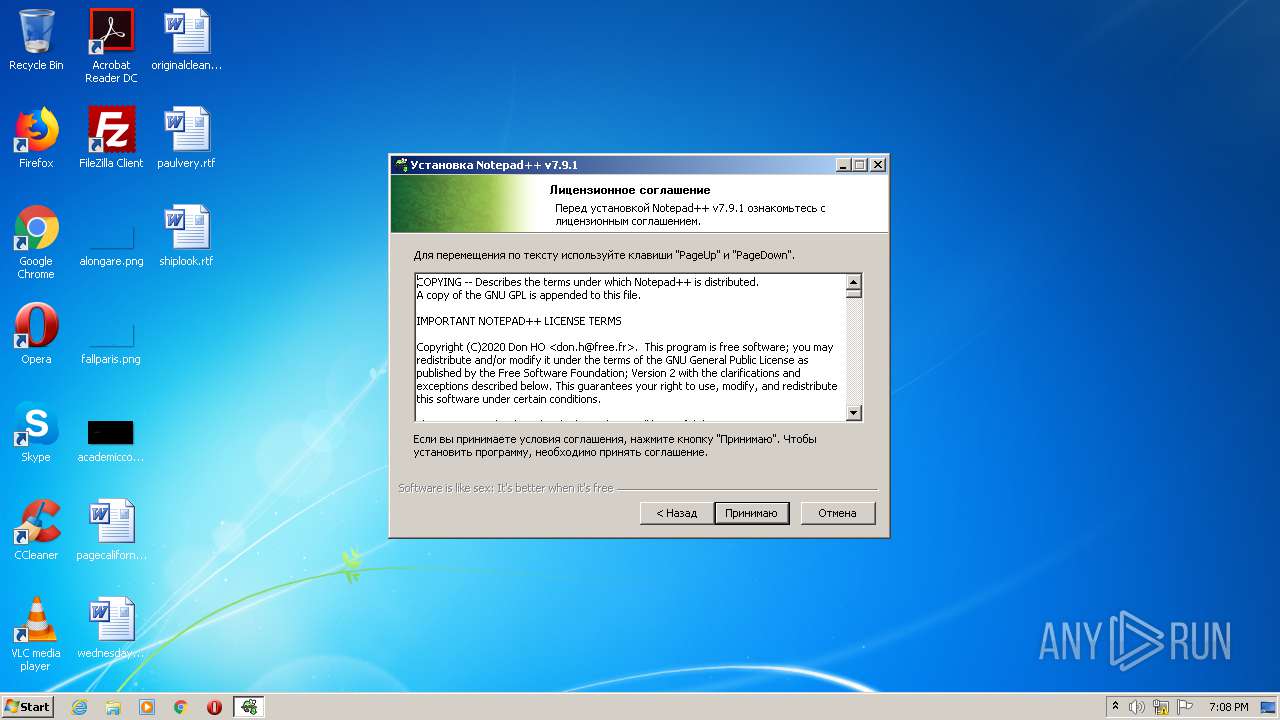
Loads dropped or rewritten executable
- hack_761_34644.exe (PID: 1768)
- gup.exe (PID: 3288)
- regsvr32.exe (PID: 960)
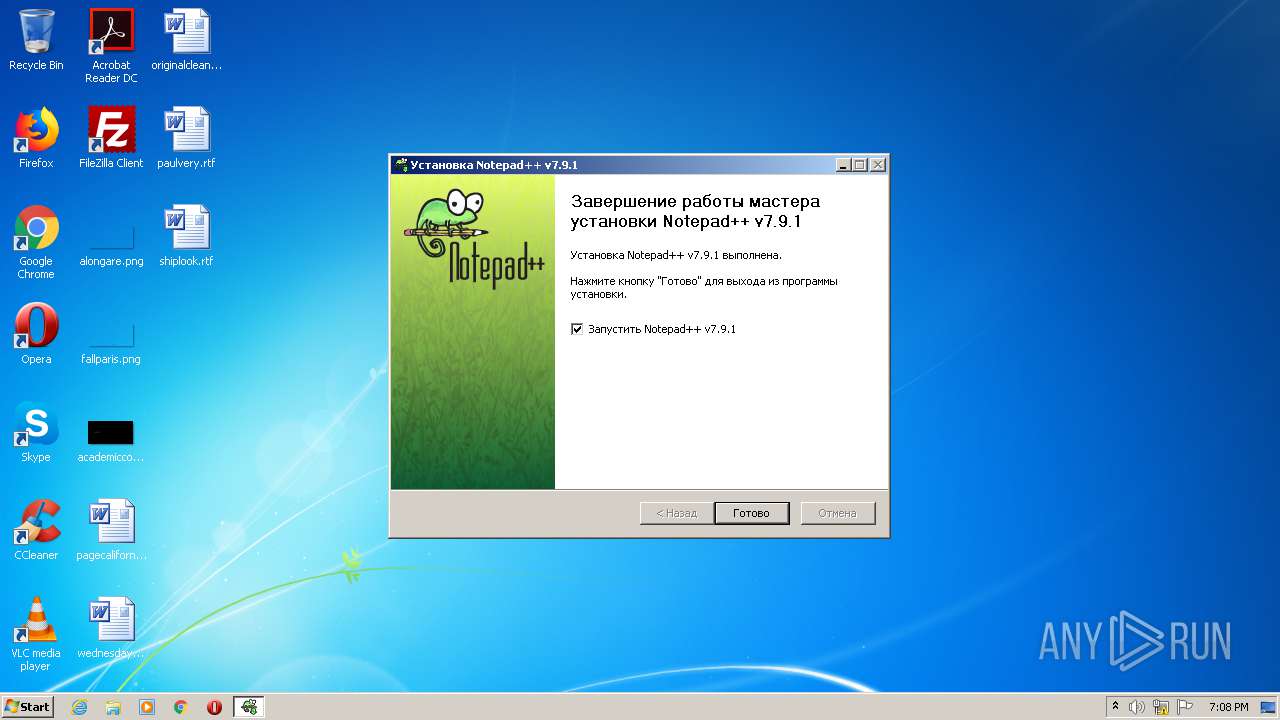
- notepad++.exe (PID: 3460)
Registers / Runs the DLL via REGSVR32.EXE
- hack_761_34644.exe (PID: 1768)
Application was dropped or rewritten from another process
- hack_761_34644.exe (PID: 1768)
- notepad++.exe (PID: 3460)
- notepad++.exe (PID: 2100)
- gup.exe (PID: 3288)
SUSPICIOUS
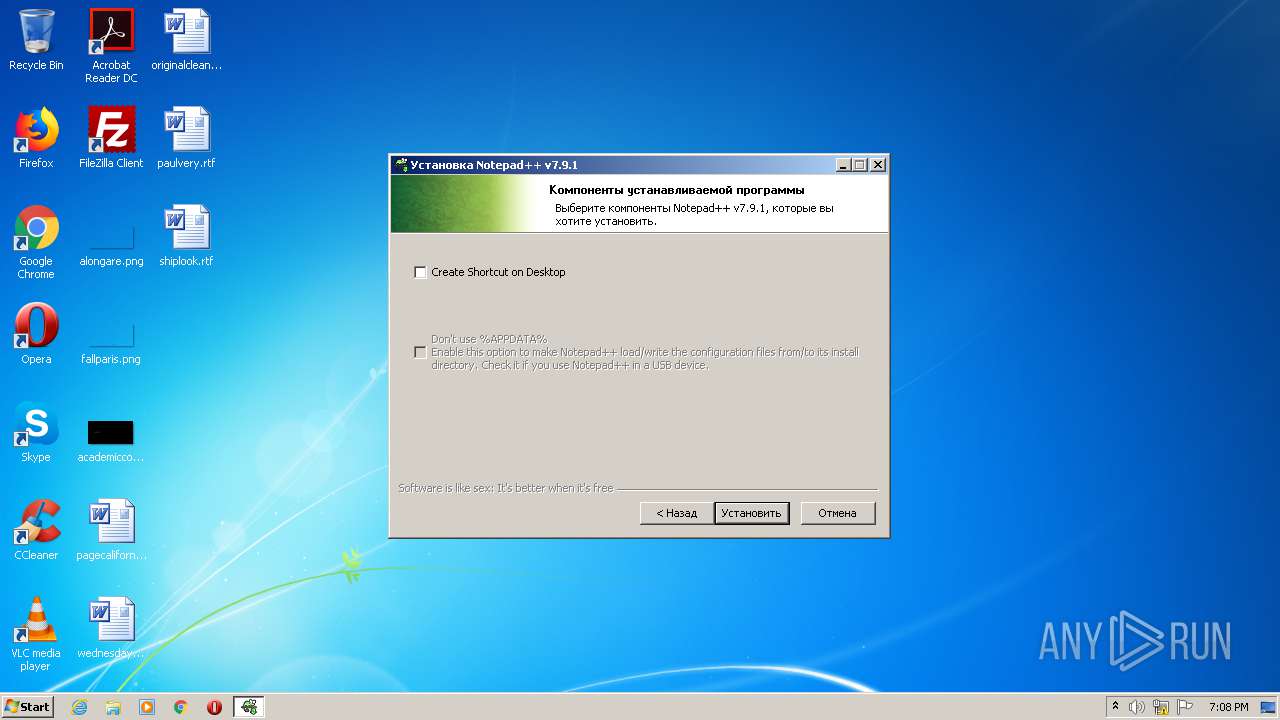
Creates files in the program directory
- hack_761_34644.exe (PID: 2680)
- hack_761_34644.exe (PID: 1340)
- hack_761_34644.exe (PID: 1768)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 976)
- cmd.exe (PID: 2012)
- hack_761_34644.exe (PID: 1340)
Executable content was dropped or overwritten
- hack_761_34644.exe (PID: 1768)
- hack_761_34644.exe (PID: 1340)
Application launched itself
- cmd.exe (PID: 2012)
- cmd.exe (PID: 976)
- hack_761_34644.exe (PID: 2680)
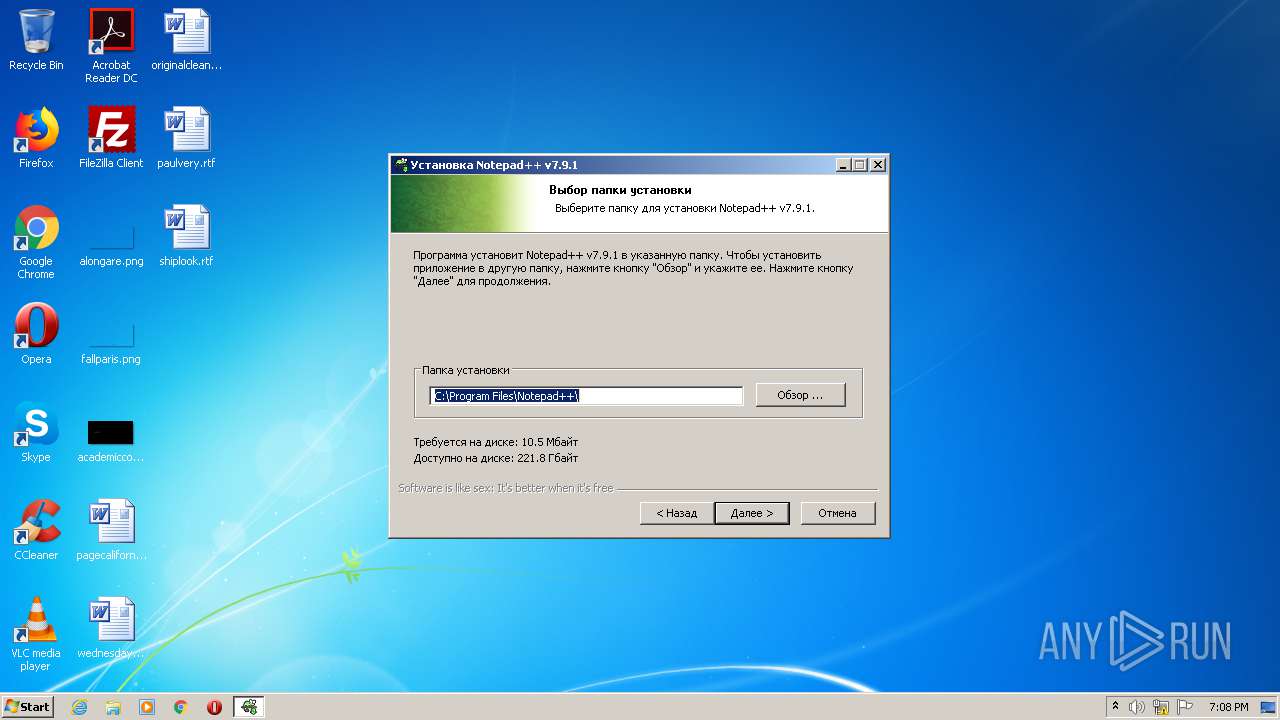
Creates a directory in Program Files
- hack_761_34644.exe (PID: 1340)
- hack_761_34644.exe (PID: 1768)
Creates files in the user directory
- hack_761_34644.exe (PID: 1768)
- notepad++.exe (PID: 3460)
- hack_761_34644.exe (PID: 1340)
- hack_761_34644.exe (PID: 2680)
Drops a file with a compile date too recent
- hack_761_34644.exe (PID: 1768)
Drops a file that was compiled in debug mode
- hack_761_34644.exe (PID: 1768)
Creates COM task schedule object
- regsvr32.exe (PID: 960)
Executed via COM
- explorer.exe (PID: 444)
Creates a software uninstall entry
- hack_761_34644.exe (PID: 1768)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:20 18:33:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 543744 |
| InitializedDataSize: | 944640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5d794 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.7.1 |
| ProductVersionNumber: | 1.7.7.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
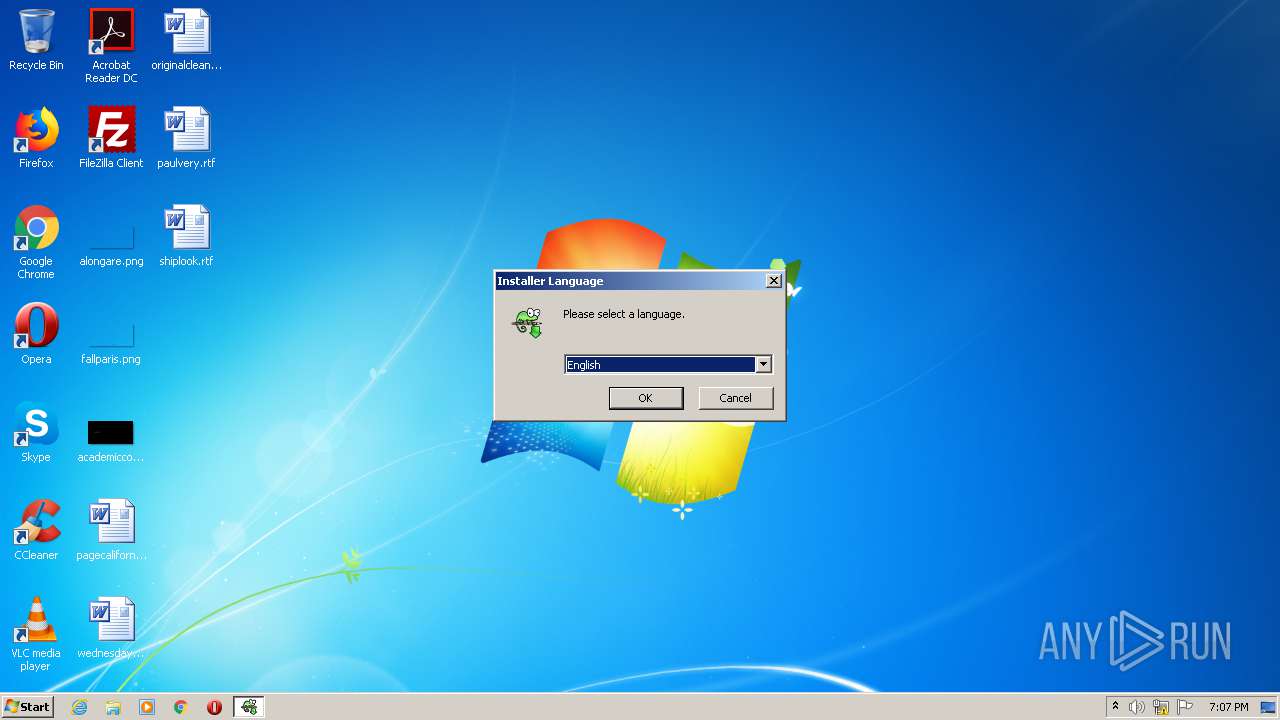
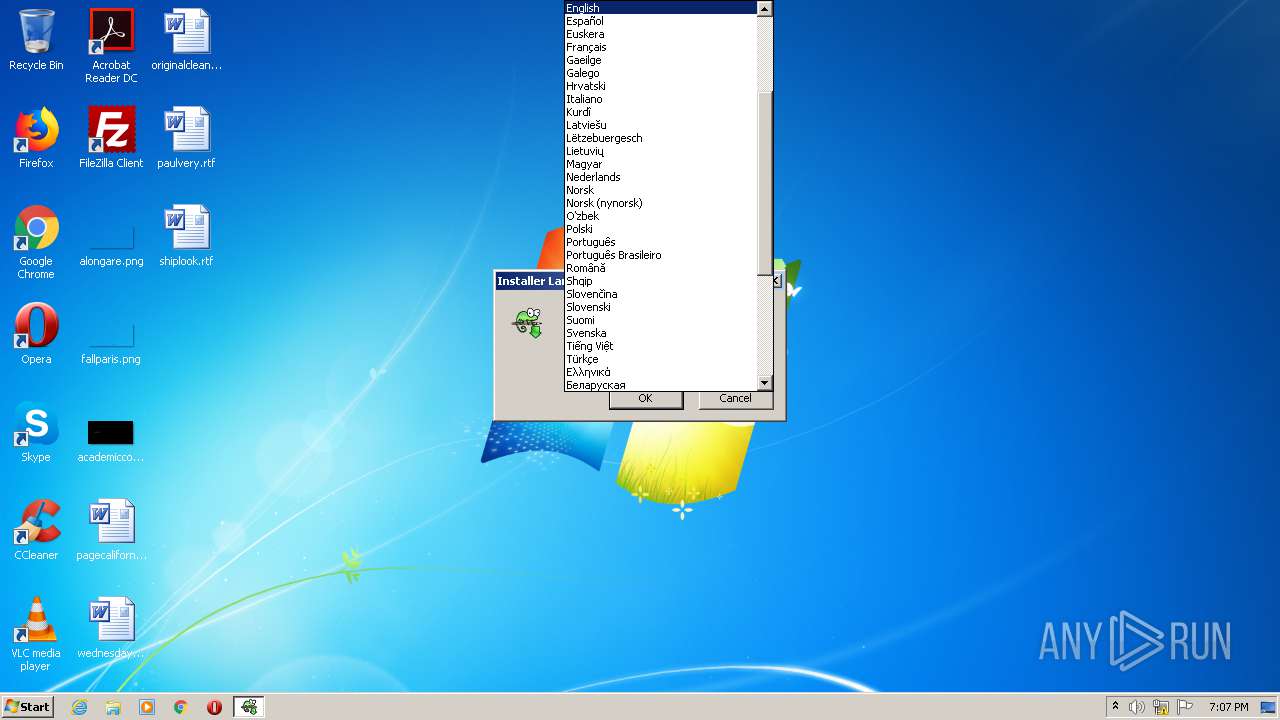
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
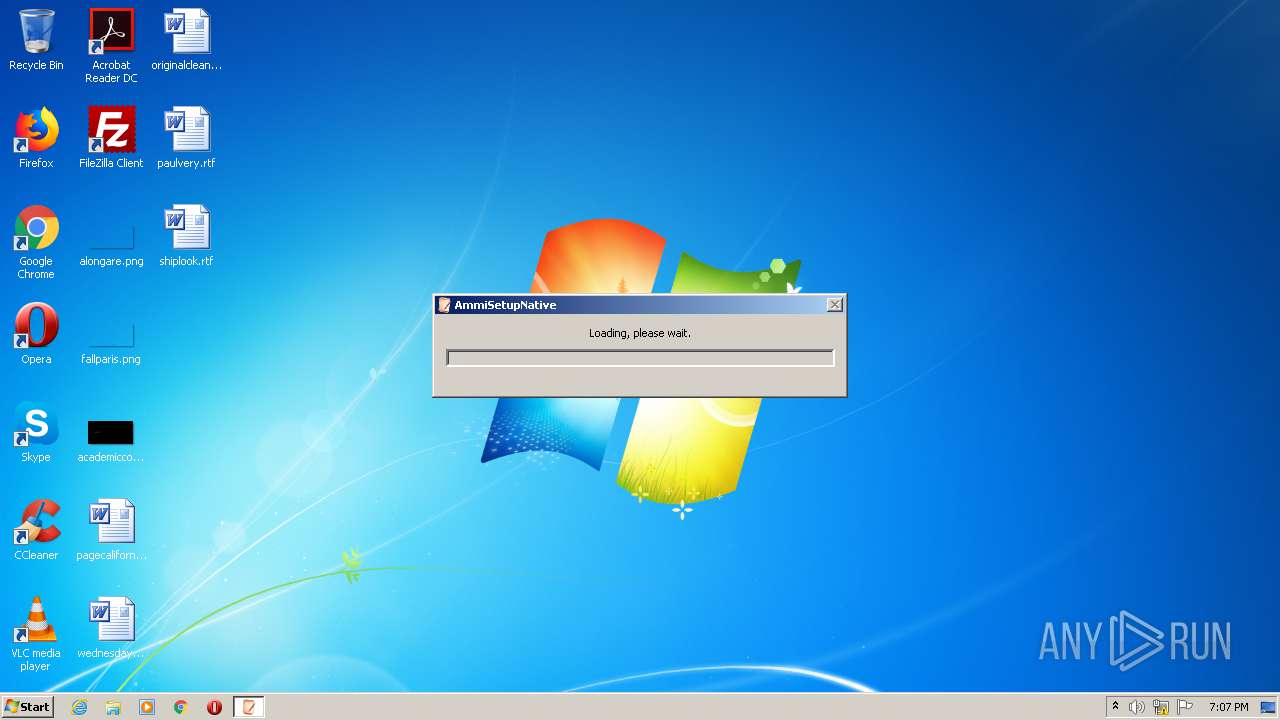
| FileDescription: | Ammi Setup Native |
| FileVersion: | 1.7.7.1 |
| InternalName: | AmmiSetupNative.exe |
| LegalCopyright: | Copyright 2020 |
| OriginalFileName: | AmmiSetupNative.exe |
| ProductName: | AmmiSetupNative |
| ProductVersion: | 1.7.7.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-May-2020 16:33:43 |
| Detected languages: |
|
| FileDescription: | Ammi Setup Native |
| FileVersion: | 1.7.7.1 |
| InternalName: | AmmiSetupNative.exe |
| LegalCopyright: | Copyright 2020 |
| OriginalFilename: | AmmiSetupNative.exe |
| ProductName: | AmmiSetupNative |
| ProductVersion: | 1.7.7.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 20-May-2020 16:33:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00084722 | 0x00084800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62054 |
.gfp4 | 0x00086000 | 0x000002F0 | 0x00000400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.81358 |
.rdata | 0x00087000 | 0x0001794E | 0x00017A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.39998 |
.data | 0x0009F000 | 0x00003E78 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.62769 |
.rsrc | 0x000A3000 | 0x000BF1D0 | 0x000BF200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.76376 |
.reloc | 0x00163000 | 0x0000BC4A | 0x0000BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.18269 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3298 | 822 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47539 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.01654 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 5.48554 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.94421 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 4.38883 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 7.99566 | 104079 | UNKNOWN | English - United States | RT_ICON |
8 | 4.69967 | 67624 | UNKNOWN | English - United States | RT_ICON |
9 | 4.88299 | 16936 | UNKNOWN | English - United States | RT_ICON |
10 | 5.04599 | 9640 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WLDAP32.dll |
WS2_32.dll |
WTSAPI32.dll |
Total processes
49
Monitored processes
12
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | regsvr32 /s "C:\Program Files\Notepad++\NppShell_06.dll" | C:\Windows\system32\regsvr32.exe | — | hack_761_34644.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 976 | C:\Windows\system32\cmd.exe /d /c cmd /d /c cmd /d /c start "" "C:\Program Files\AmmiSetupuhbNative\hack_761_34644.exe" 71369044212613 SUGpvf1zy1iDln4arUlHHFQ0O5QXOonFG0dmKtg33jZoYXgVjXgI3llP4/cIGxu/RTlKKagTDqzdukum8uk+lBBnrebyQ4IdS+EyWlcRnBEKPWceZo9h46yzlfxPfOlxPIUGXVZxJQAIMTMRvLyqhYHn0DL/HB3A9IEwW667GGxTyzEjGFZunB4RrBWEg9ZD | C:\Windows\system32\cmd.exe | — | hack_761_34644.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1340 | "C:\Users\admin\AppData\Local\Temp\hack_761_34644.exe" -uac | C:\Users\admin\AppData\Local\Temp\hack_761_34644.exe | hack_761_34644.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Ammi Setup Native Exit code: 0 Version: 1.7.7.1 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\AmmiSetupuhbNative\hack_761_34644.exe" 71369044212613 SUGpvf1zy1iDln4arUlHHFQ0O5QXOonFG0dmKtg33jZoYXgVjXgI3llP4/cIGxu/RTlKKagTDqzdukum8uk+lBBnrebyQ4IdS+EyWlcRnBEKPWceZo9h46yzlfxPfOlxPIUGXVZxJQAIMTMRvLyqhYHn0DL/HB3A9IEwW667GGxTyzEjGFZunB4RrBWEg9ZD | C:\Program Files\AmmiSetupuhbNative\hack_761_34644.exe | cmd.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: HIGH Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.9.1.0 Modules
| |||||||||||||||
| 2012 | cmd /d /c cmd /d /c start "" "C:\Program Files\AmmiSetupuhbNative\hack_761_34644.exe" 71369044212613 SUGpvf1zy1iDln4arUlHHFQ0O5QXOonFG0dmKtg33jZoYXgVjXgI3llP4/cIGxu/RTlKKagTDqzdukum8uk+lBBnrebyQ4IdS+EyWlcRnBEKPWceZo9h46yzlfxPfOlxPIUGXVZxJQAIMTMRvLyqhYHn0DL/HB3A9IEwW667GGxTyzEjGFZunB4RrBWEg9ZD | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
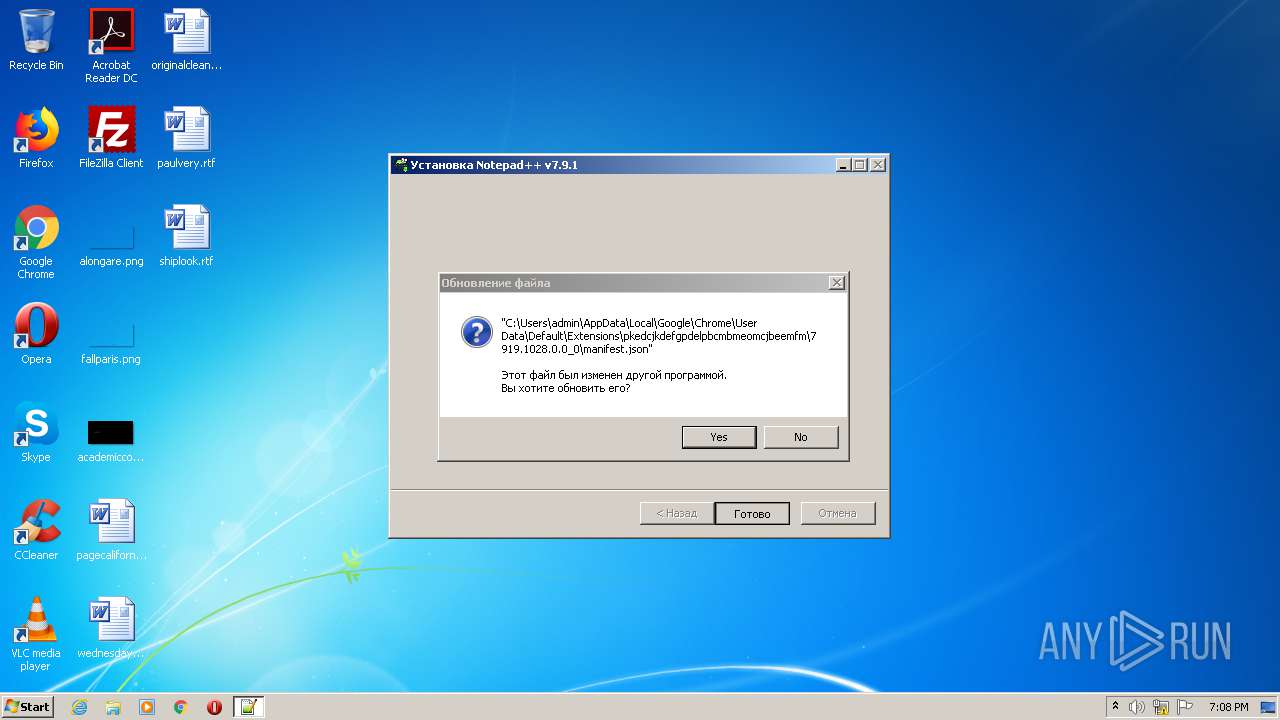
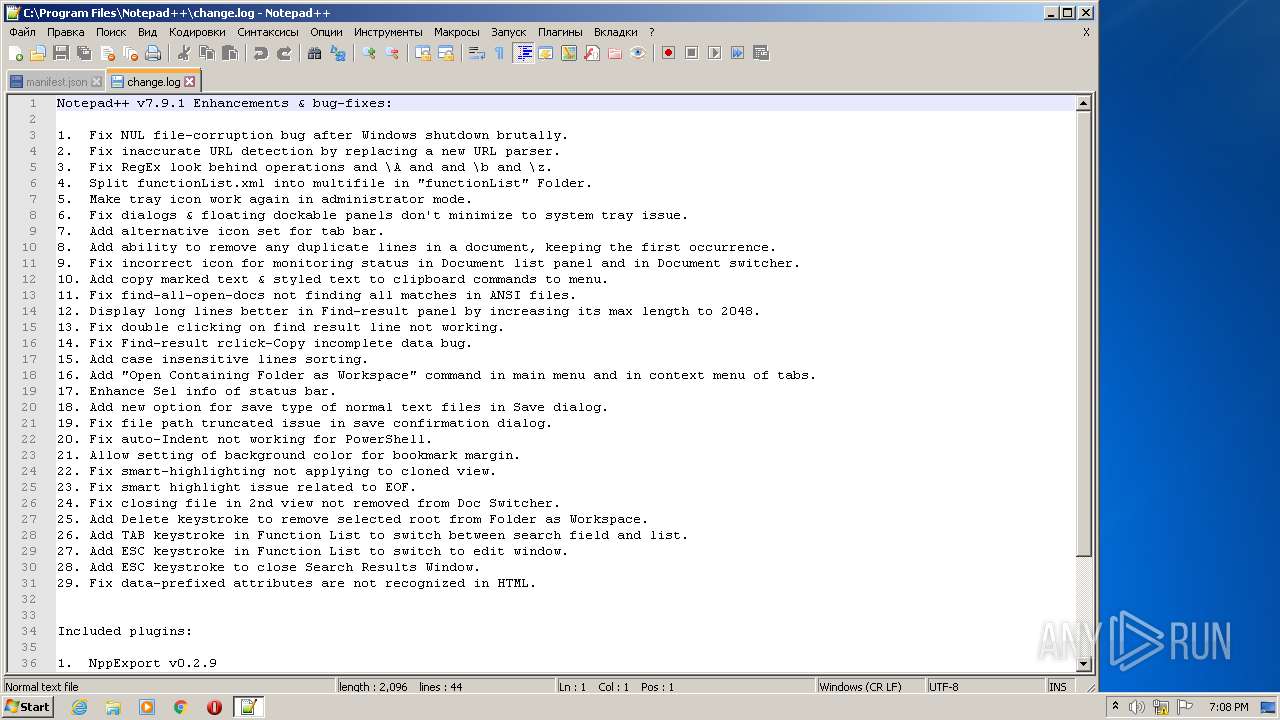
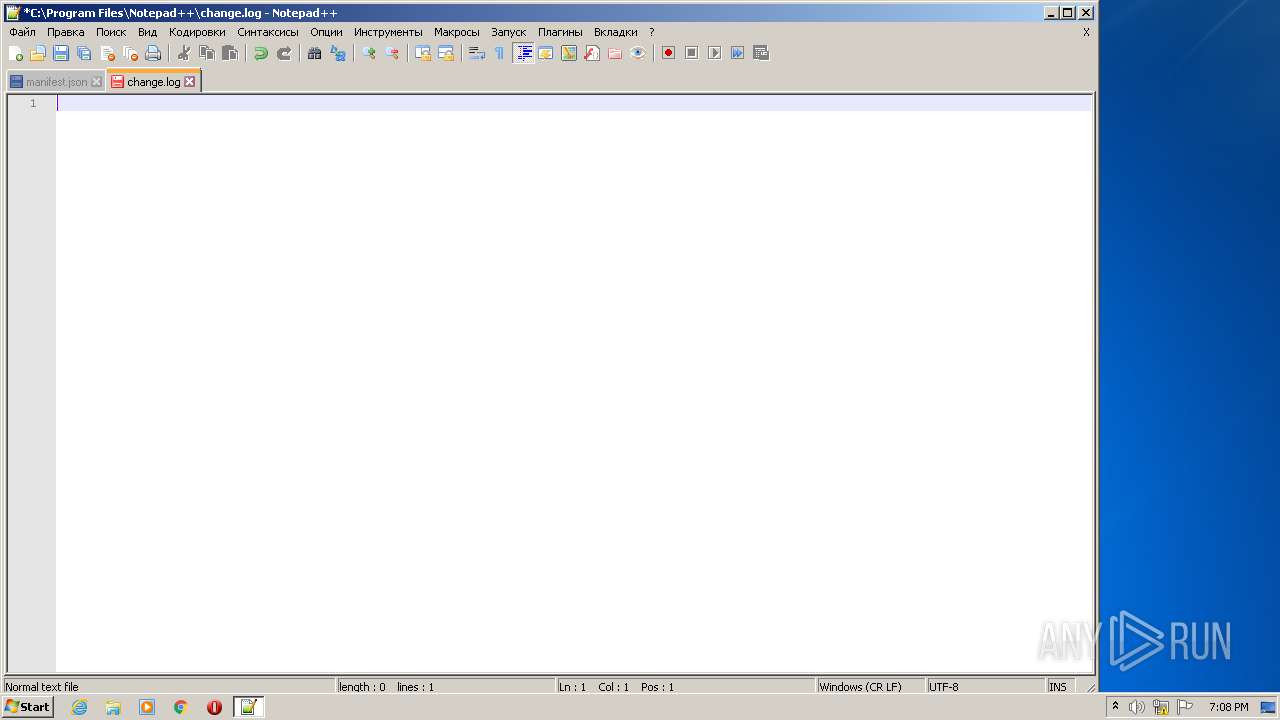
| 2100 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Program Files\Notepad++\change.log" | C:\Program Files\Notepad++\notepad++.exe | hack_761_34644.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: HIGH Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 2584 | "C:\Windows\explorer.exe" "C:\Program Files\Notepad++\notepad++.exe" | C:\Windows\explorer.exe | — | hack_761_34644.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2680 | "C:\Users\admin\AppData\Local\Temp\hack_761_34644.exe" | C:\Users\admin\AppData\Local\Temp\hack_761_34644.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Ammi Setup Native Exit code: 0 Version: 1.7.7.1 Modules
| |||||||||||||||
| 3288 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.91 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: WinGup for Notepad++ Exit code: 0 Version: 5.11 Modules
| |||||||||||||||
Total events
1 113
Read events
879
Write events
230
Delete events
4
Modification events
| (PID) Process: | (2680) hack_761_34644.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2680) hack_761_34644.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (960) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\*\shellex\ContextMenuHandlers\ANotepad++ |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (960) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00F3C2EC-A6EE-11DE-A03A-EF8F55D89593}\InprocServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (960) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00F3C2EC-A6EE-11DE-A03A-EF8F55D89593}\Settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (960) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00F3C2EC-A6EE-11DE-A03A-EF8F55D89593} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (960) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00F3C2EC-A6EE-11DE-A03A-EF8F55D89593} |
| Operation: | write | Name: | (default) |
Value: ANotepad++ | |||
| (PID) Process: | (960) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00F3C2EC-A6EE-11DE-A03A-EF8F55D89593}\InprocServer32 |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Notepad++\NppShell_06.dll | |||
| (PID) Process: | (960) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00F3C2EC-A6EE-11DE-A03A-EF8F55D89593}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (960) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00F3C2EC-A6EE-11DE-A03A-EF8F55D89593}\Settings |
| Operation: | write | Name: | Title |
Value: Edit with &Notepad++ | |||
Executable files
16
Suspicious files
4
Text files
184
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1340 | hack_761_34644.exe | C:\Program Files\AmmiSetupuhbNative\hack_761_34644.exe | executable | |
MD5:— | SHA256:— | |||
| 1340 | hack_761_34644.exe | C:\ProgramData\folder\Buffertemppho | binary | |
MD5:00A5033694B6E94D8078EF2535036E09 | SHA256:4DD388E61295C6B3F52937C142468B736B18D46EB878C28D15E202E84FD81C6F | |||
| 1768 | hack_761_34644.exe | C:\Users\admin\AppData\Local\Temp\nsqB456.tmp\LangDLL.dll | executable | |
MD5:AB1DB56369412FE8476FEFFFD11E4CC0 | SHA256:6F14C8F01F50A30743DAC68C5AC813451463DFB427EB4E35FCDFE2410E1A913B | |||
| 1768 | hack_761_34644.exe | C:\Users\admin\AppData\Local\Temp\nsqB456.tmp\nsDialogs.dll | executable | |
MD5:466179E1C8EE8A1FF5E4427DBB6C4A01 | SHA256:1E40211AF65923C2F4FD02CE021458A7745D28E2F383835E3015E96575632172 | |||
| 1768 | hack_761_34644.exe | C:\Users\admin\AppData\Local\Temp\nsqB456.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 1768 | hack_761_34644.exe | C:\Users\admin\AppData\Local\Temp\nsqB456.tmp\InstallOptions.dll | executable | |
MD5:05BF02DA51E717F79F6B5CBEA7BC0710 | SHA256:CA092BA7F275B0C9000098CDD1A9876FE8DC050FCB40A0E8A1AB8335236E9DC5 | |||
| 1340 | hack_761_34644.exe | C:\Users\admin\AppData\Roaming\folder\Buffertemppho | binary | |
MD5:00A5033694B6E94D8078EF2535036E09 | SHA256:4DD388E61295C6B3F52937C142468B736B18D46EB878C28D15E202E84FD81C6F | |||
| 1768 | hack_761_34644.exe | C:\Users\admin\AppData\Local\Temp\nsqB456.tmp\modern-wizard.bmp | image | |
MD5:C2CF6928A3AB574A5548B4DC1C38B6C0 | SHA256:2125550C12FA512782F2016E802D70BC51F4A06017CFBD4176B4A994EB2542F0 | |||
| 1768 | hack_761_34644.exe | C:\Program Files\Notepad++\autoCompletion\cs.xml | xml | |
MD5:ABDBF3E6817274A26EF82FEBB0E814F0 | SHA256:13844C2D59E409C2A7B62839BA04E9272649BFE179CF8315CE10260912260EDE | |||
| 1768 | hack_761_34644.exe | C:\Users\admin\AppData\Local\Temp\nsqB456.tmp\modern-header.bmp | image | |
MD5:56DA15FDB8D96F8F5C649DCB5E79D775 | SHA256:BB90D4338D2474138473E6B16E94B0237EE847BEA45019ED0DD4439C71BD233E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1340 | hack_761_34644.exe | 104.26.6.32:443 | allstandardsoftware.com | Cloudflare Inc | US | malicious |
3288 | gup.exe | 172.67.218.84:443 | notepad-plus-plus.org | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
allstandardsoftware.com |
| malicious |
notepad-plus-plus.org |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|