| File name: | PeatEXV4.2.0(FIX).exe |
| Full analysis: | https://app.any.run/tasks/cf501f47-8084-43a4-8192-a104f17f6d73 |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2024, 05:00:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | CF97A2ED811EA0D1960BE7DF22C6C200 |
| SHA1: | 8767A91E0CE6C2F12539701AC3FD1BA17C2538B8 |
| SHA256: | 99352B1EC00BC4A17B79769A352404B78193749FC374BE3404198429B15CC261 |
| SSDEEP: | 49152:Q1zz8adlvGV8cONwWDwlOQoLrbU/7dlRJfn232l1fiJ0xZ2MRexnOm4kVSeVvzdB:Q1zYso8BMqLP0lH2GlFug2dxnOSVSk7P |
MALICIOUS
No malicious indicators.SUSPICIOUS
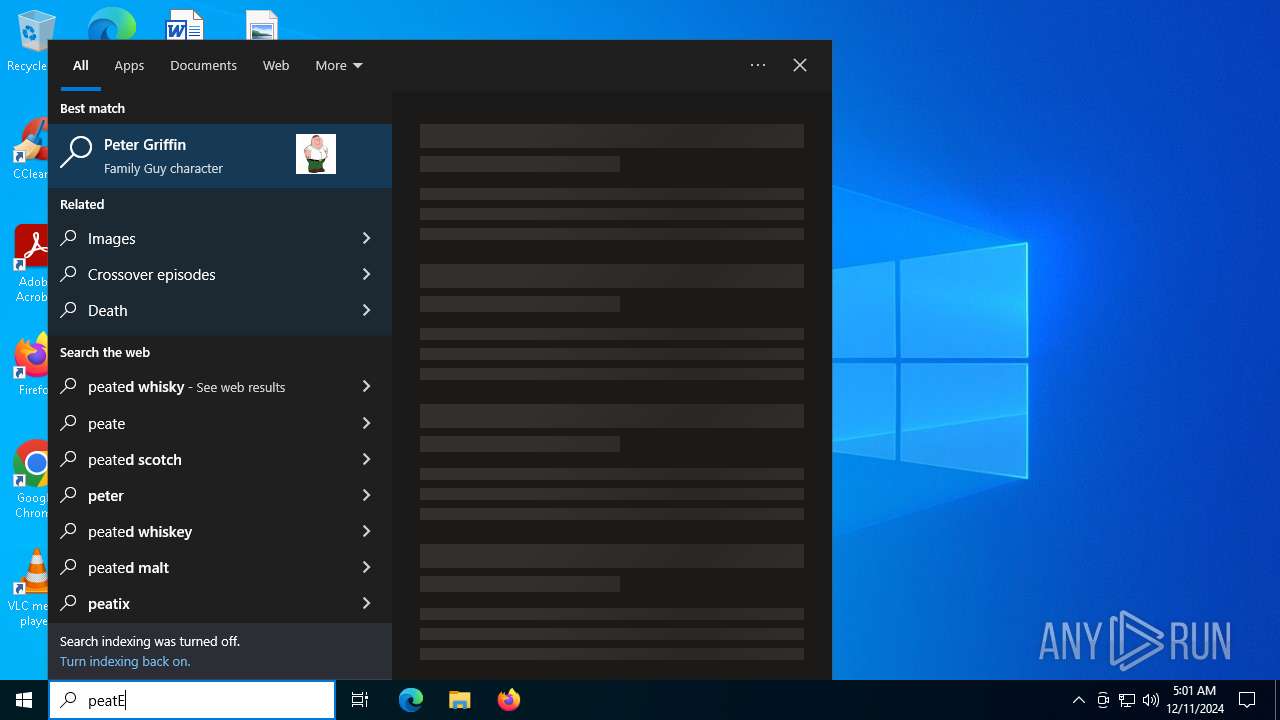
Reads security settings of Internet Explorer
- PeatEXV4.2.0(FIX).exe (PID: 6352)
Reads Internet Explorer settings
- PeatEXV4.2.0(FIX).exe (PID: 6352)
Reads Microsoft Outlook installation path
- PeatEXV4.2.0(FIX).exe (PID: 6352)
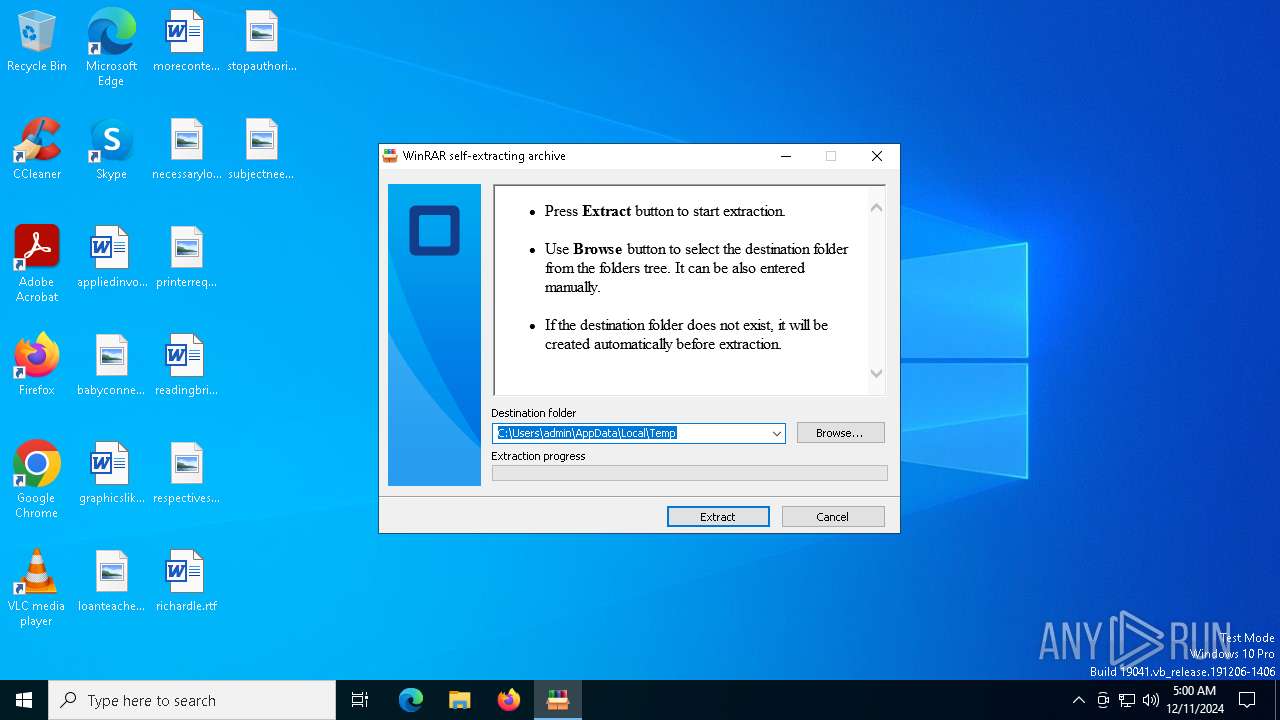
Executable content was dropped or overwritten
- PeatEXV4.2.0(FIX).exe (PID: 6352)
INFO
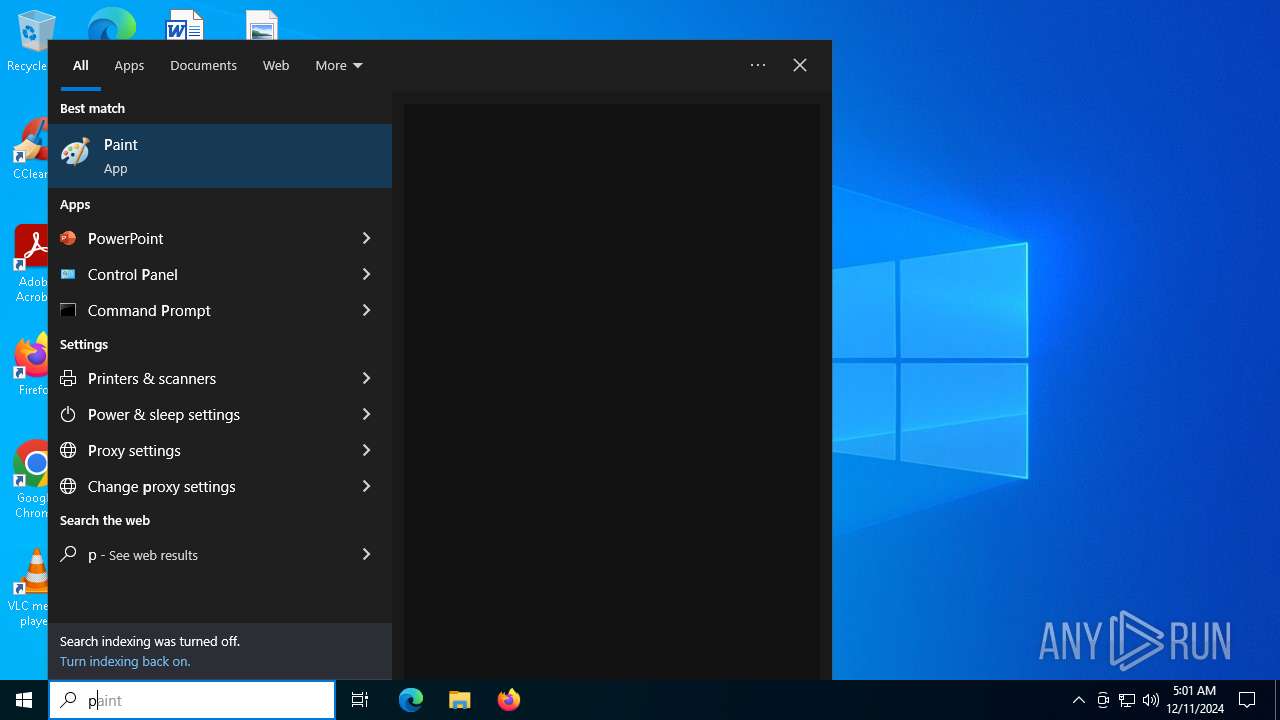
Checks proxy server information
- PeatEXV4.2.0(FIX).exe (PID: 6352)
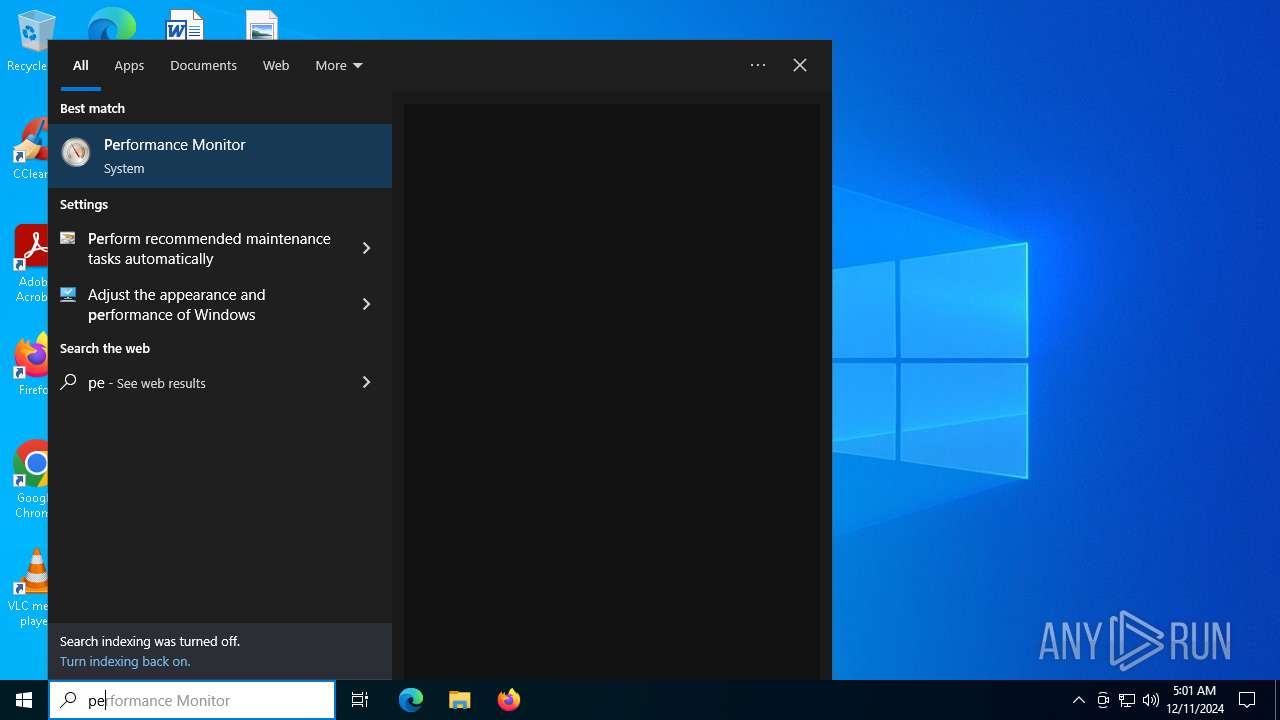
Reads the computer name
- PeatEXV4.2.0(FIX).exe (PID: 6352)
Checks supported languages
- PeatEXV4.2.0(FIX).exe (PID: 6352)
Create files in a temporary directory
- PeatEXV4.2.0(FIX).exe (PID: 6352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:07 15:07:25+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 200704 |
| InitializedDataSize: | 254976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ea80 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
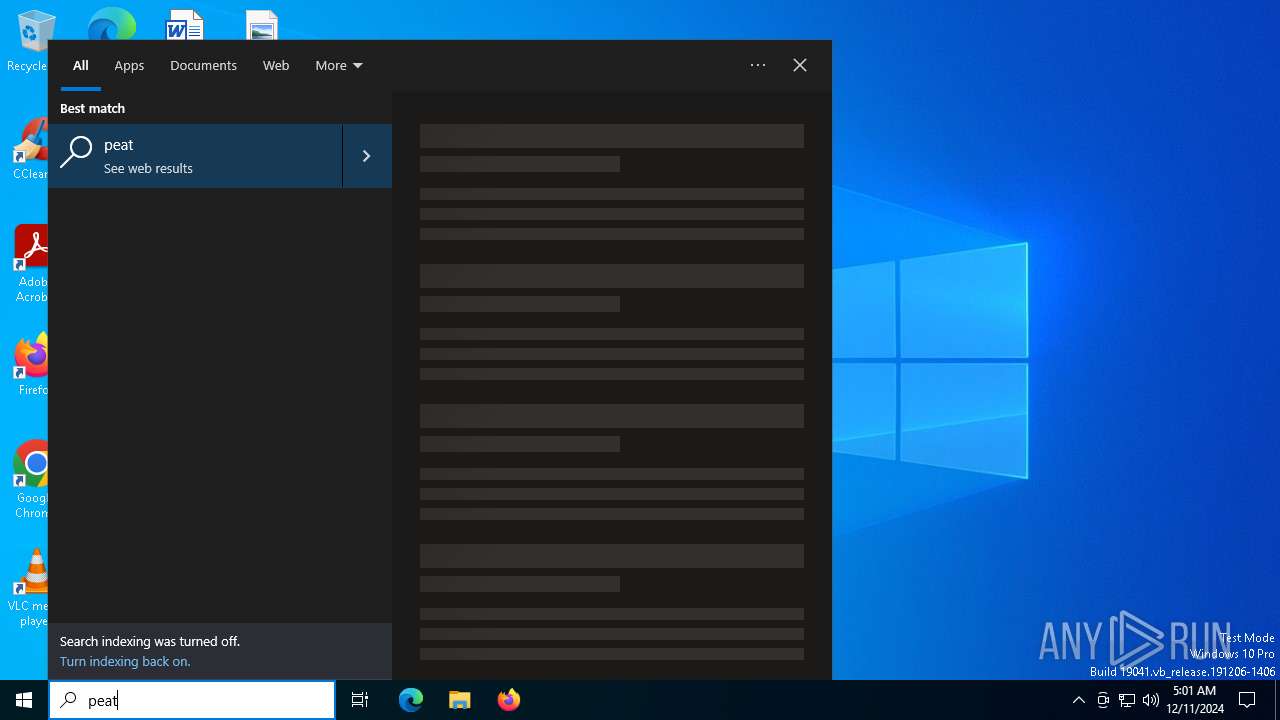
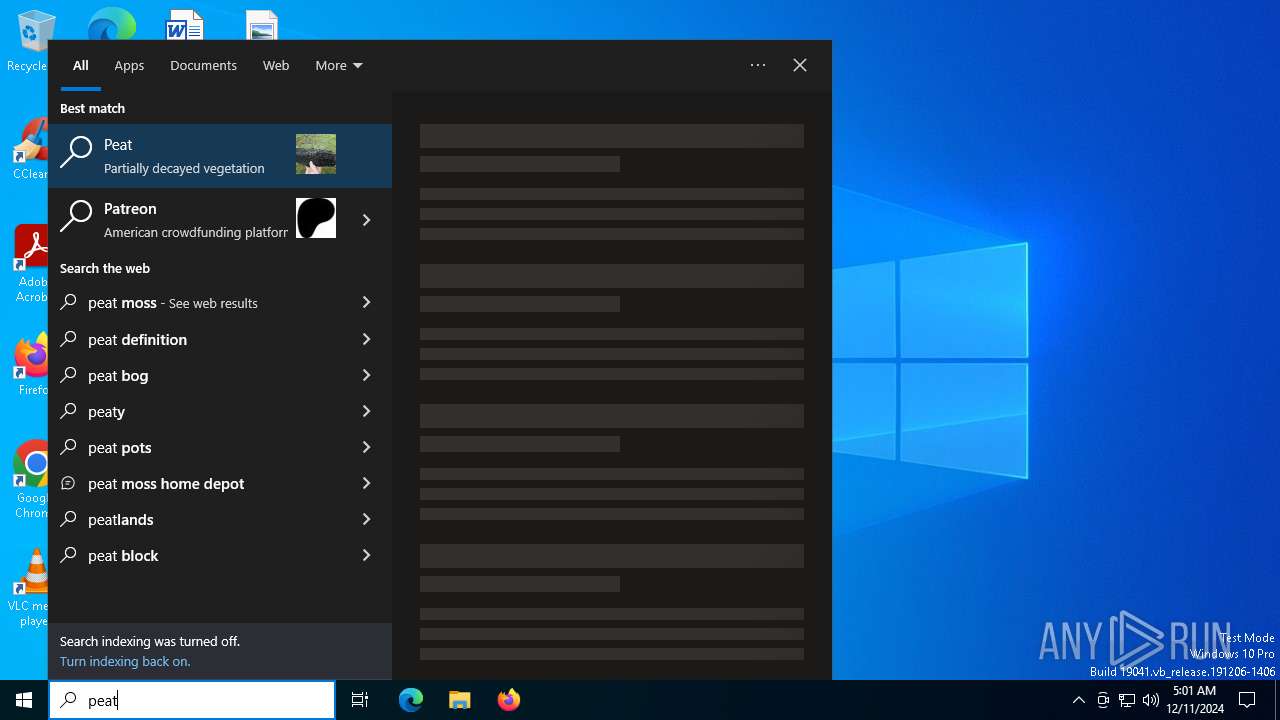
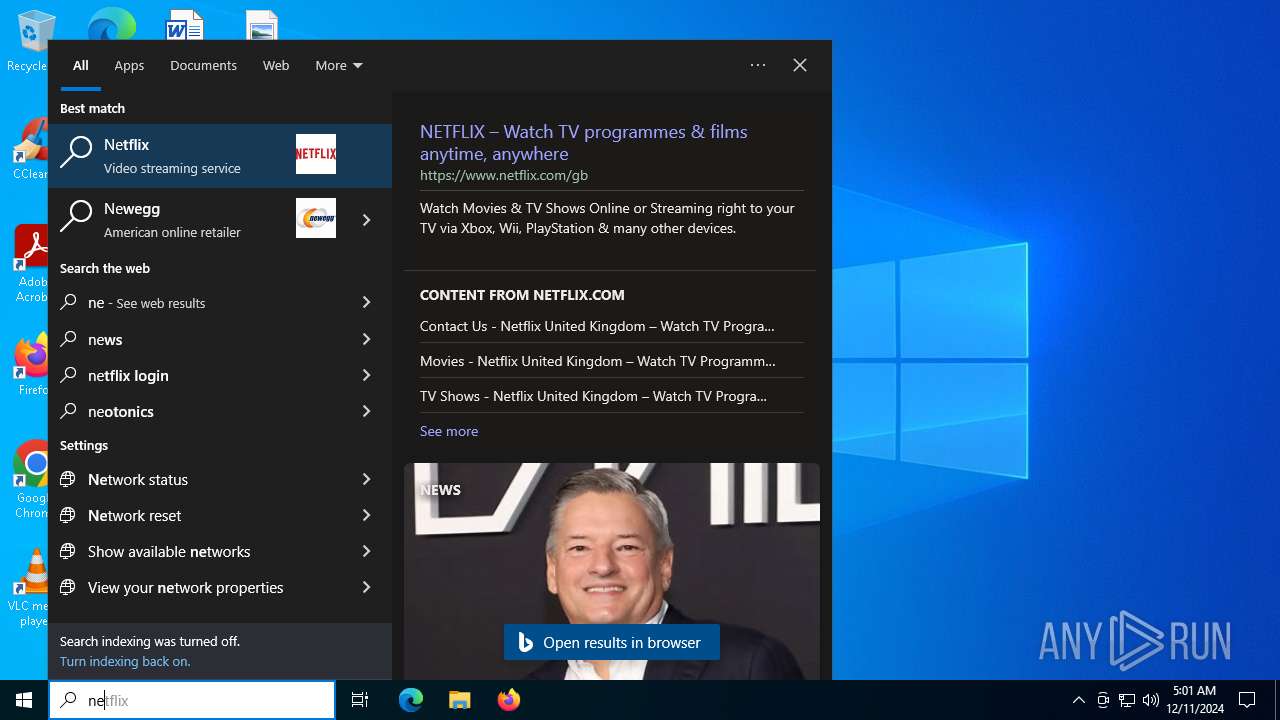
Total processes
137
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1356 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 2076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6352 | "C:\Users\admin\AppData\Local\Temp\PeatEXV4.2.0(FIX).exe" | C:\Users\admin\AppData\Local\Temp\PeatEXV4.2.0(FIX).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
650
Read events
645
Write events
3
Delete events
2
Modification events
| (PID) Process: | (6352) PeatEXV4.2.0(FIX).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6352) PeatEXV4.2.0(FIX).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6352) PeatEXV4.2.0(FIX).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6352) PeatEXV4.2.0(FIX).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (6352) PeatEXV4.2.0(FIX).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
Executable files
5
Suspicious files
18
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\data\api.txt | text | |
MD5:C1A0C7F060FF3901D883D659E0AF6D20 | SHA256:BCC9ACB96323B975BDD17434E3A14C91ABB9060BC4C23F8C17BFD9DF2D689352 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\data\lite.txt | text | |
MD5:3262D48DF5D75E3452F0F16B313B7808 | SHA256:B4DC66DDE806261BDDA8607D8707AA727D308CD80272381A5583F63899918467 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\PeatEXV4.exe | executable | |
MD5:30E44C14D4DA2BD40E91F3C000D504B5 | SHA256:BE00A4812812EC44B9647EE603ED49ED27BF8FA946A3DB0E4AF3344C3D68E507 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\Bunifu_UI_v1.5.3.dll | executable | |
MD5:E0EF2817EE5A7C8CD1EB837195768BD2 | SHA256:76E1D3EC95FDEF74ABAF90392DD6F4AA5E344922ABF11E572707287D467F2930 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\Scripts\Auratus.lua | binary | |
MD5:3ACC1EEE1948DBA0288C751A5AF70D38 | SHA256:4DAFF79506C071721FE238F7269E4B2A1E2537E3FCB806B8EA11EF2A32E3C0E9 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\PeatEXV4.exe.config | xml | |
MD5:B51C130A957051BA9FB2245BF76FB6F6 | SHA256:7921098E47E894412FDFD0CAFE0F88CC68497740998EAC17C68C00129069D803 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\Scripts\Arosia FE Gui.txt | text | |
MD5:35D63FAD061BED4BB0BB1A67200D39BA | SHA256:E5E7034610E718A61556611A1C456A8392029AF5FABCC27E1CD89D1CF3183DD6 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\EasyExploits.dll | executable | |
MD5:ED3AD22271171D1E3DD759E154FB1C6A | SHA256:75D699BAFEA25CEA37DABB82BACBEA3D0E7FE336C1DA6D63A4DB09CE448F1D67 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\Scripts\Epic Script Hub.txt | text | |
MD5:AC0B40852AF2EED51E768DE8D9F18029 | SHA256:46BF0C9E31AF1B32BB7E033EAD4C938E8A6195B460FB4D8F105B8E942CC81220 | |||
| 6352 | PeatEXV4.2.0(FIX).exe | C:\Users\admin\AppData\Local\Temp\PeatEX\PeatEXV4.pdb | binary | |
MD5:EC361017A5DFBD8CCF879D3DC6CDEDEA | SHA256:DEEB1392B0A943036CB7F56B64582A5017417EB32D1CD10D1B994D553E2DD539 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
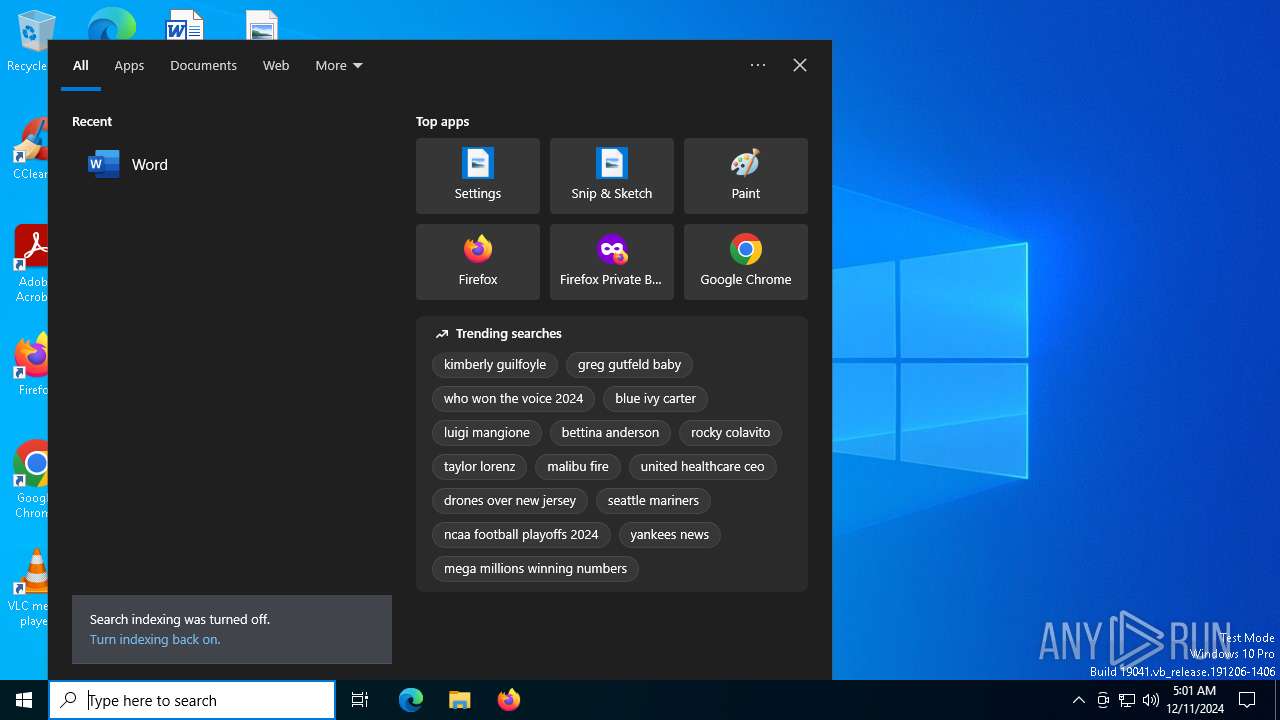
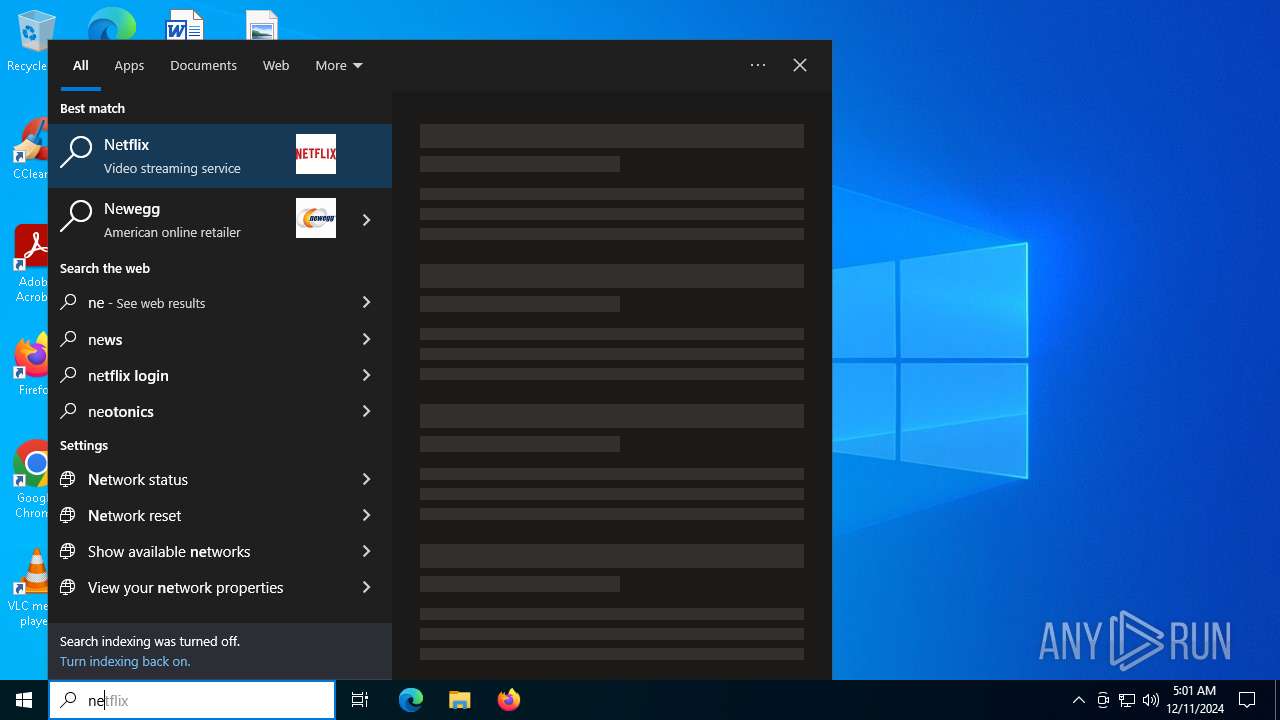
HTTP(S) requests
12
TCP/UDP connections
55
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3220 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3220 | svchost.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7068 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7068 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6228 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3220 | svchost.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3220 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.136:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 184.30.17.189:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
r.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |