| File name: | skpc.dll |
| Full analysis: | https://app.any.run/tasks/37d5b6a4-9fb9-449e-9605-e987e91470ec |
| Verdict: | No threats detected |
| Analysis date: | July 16, 2020, 05:20:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | D312336FD46972A544929D0DC4E07B83 |
| SHA1: | 560C0AFF12106B09CC1EF6CF94772B7D33FBAE40 |
| SHA256: | 99244E4186047A6531177FD189B3C299EFA7DB869DB7ED307E3AFA372913F306 |
| SSDEEP: | 49152:HAz7U68JSVdzU3nXSJbf0TneirrkrKoFBDRbeWaIQXx15KaG9Dsnie2cE1SH7efD:Huz4nmf0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
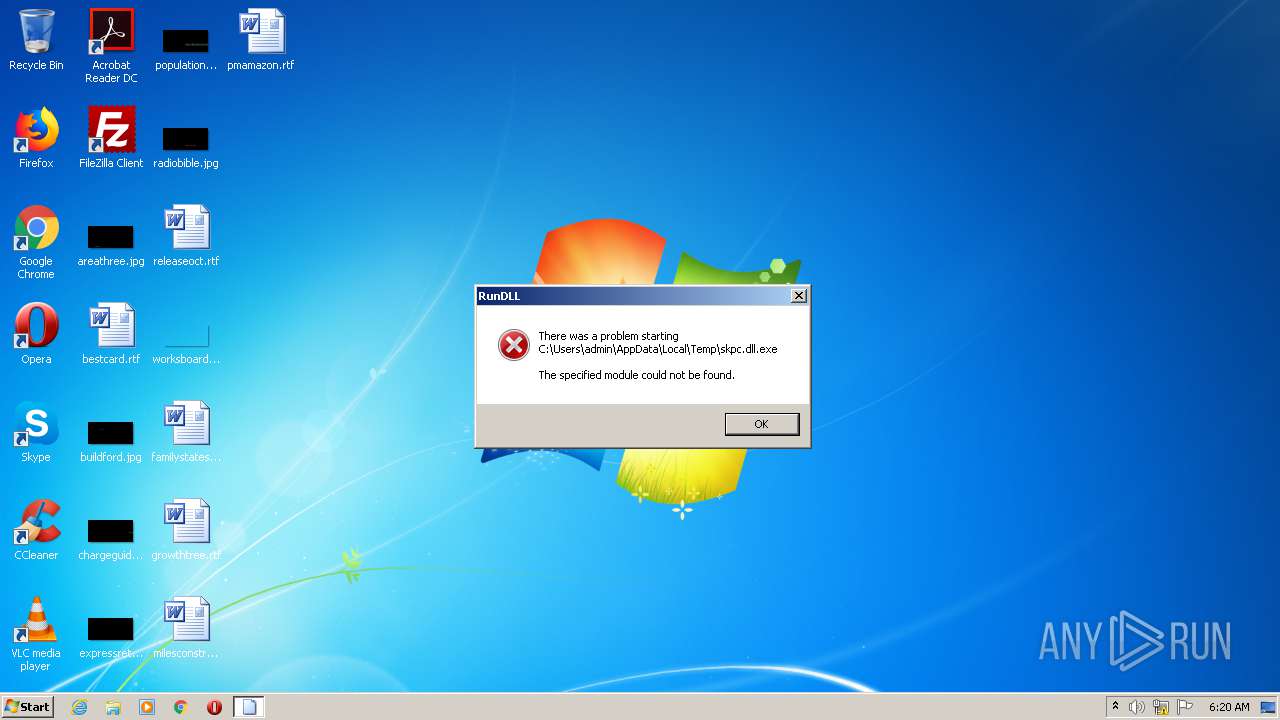
Loads main object executable
- rundll32.exe (PID: 580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (46.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (41) |
| .exe | | | Win32 Executable (generic) (6.6) |
| .exe | | | Generic Win/DOS Executable (2.9) |
| .exe | | | DOS Executable Generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:15 10:53:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1454080 |
| InitializedDataSize: | 765952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xfcc1c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.0.13 |
| ProductVersionNumber: | 2.1.0.13 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | 税率调整 |
| FileVersion: | 2, 1, 0, 13 |
| InternalName: | skp |
| LegalCopyright: | 版权所有 (C) 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | skpc.DLL |
| PrivateBuild: | - |
| ProductName: | skpc Dynamic Link Library |
| ProductVersion: | 2, 1, 0, 13 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Mar-2019 09:53:30 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | 税率调整 |
| FileVersion: | 2, 1, 0, 13 |
| InternalName: | skp |
| LegalCopyright: | 版权所有 (C) 2018 |
| LegalTrademarks: | - |
| OriginalFilename: | skpc.DLL |
| PrivateBuild: | - |
| ProductName: | skpc Dynamic Link Library |
| ProductVersion: | 2, 1, 0, 13 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Mar-2019 09:53:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001620AA | 0x00163000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31119 |
.rdata | 0x00164000 | 0x0003D310 | 0x0003E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12674 |
.data | 0x001A2000 | 0x00061AEF | 0x0005E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.28168 |
.rsrc | 0x00204000 | 0x00001CD0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.65497 |
.reloc | 0x00206000 | 0x0001880A | 0x00019000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.66002 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.48393 | 796 | UNKNOWN | Chinese - PRC | RT_VERSION |
2 | 2.74274 | 180 | UNKNOWN | Chinese - PRC | RT_CURSOR |
3841 | 3.68399 | 80 | UNKNOWN | Chinese - PRC | RT_STRING |
3842 | 1.37932 | 44 | UNKNOWN | Chinese - PRC | RT_STRING |
3843 | 5.07447 | 120 | UNKNOWN | Chinese - PRC | RT_STRING |
3857 | 6.10651 | 452 | UNKNOWN | Chinese - PRC | RT_STRING |
3858 | 5.07121 | 298 | UNKNOWN | Chinese - PRC | RT_STRING |
3859 | 5.85681 | 326 | UNKNOWN | Chinese - PRC | RT_STRING |
3865 | 3.16865 | 64 | UNKNOWN | Chinese - PRC | RT_STRING |
3866 | 4.15663 | 100 | UNKNOWN | Chinese - PRC | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
NISEC_SKP.dll |
OLEAUT32.dll |
USER32.dll |
VERSION.dll |
WINSPOOL.DRV |
ZLib_Tools.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
Asc2Hex | 1 | 0x00005260 |
DBDecrypt | 2 | 0x000039F0 |
DBEncrypt | 3 | 0x000039D0 |
ExportEncrypt | 4 | 0x00003A10 |
Hex2Asc | 5 | 0x00005360 |
InitClient | 6 | 0x000033B0 |
OperateDisk | 7 | 0x00005430 |
OperateDiskF | 8 | 0x000054C0 |
SetVerifyFlagX | 9 | 0x00005420 |
UploadDecrypt | 10 | 0x00003C20 |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\skpc.dll.exe", Asc2Hex | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report