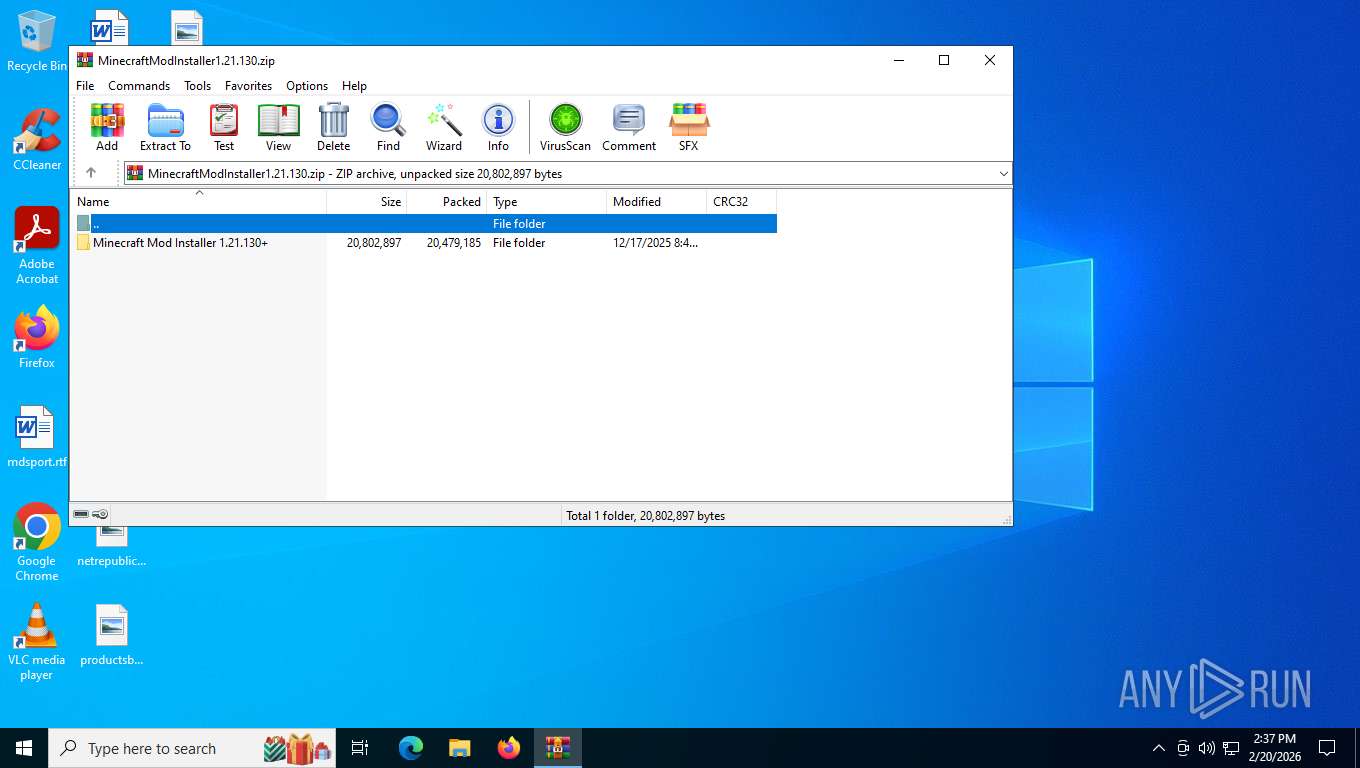
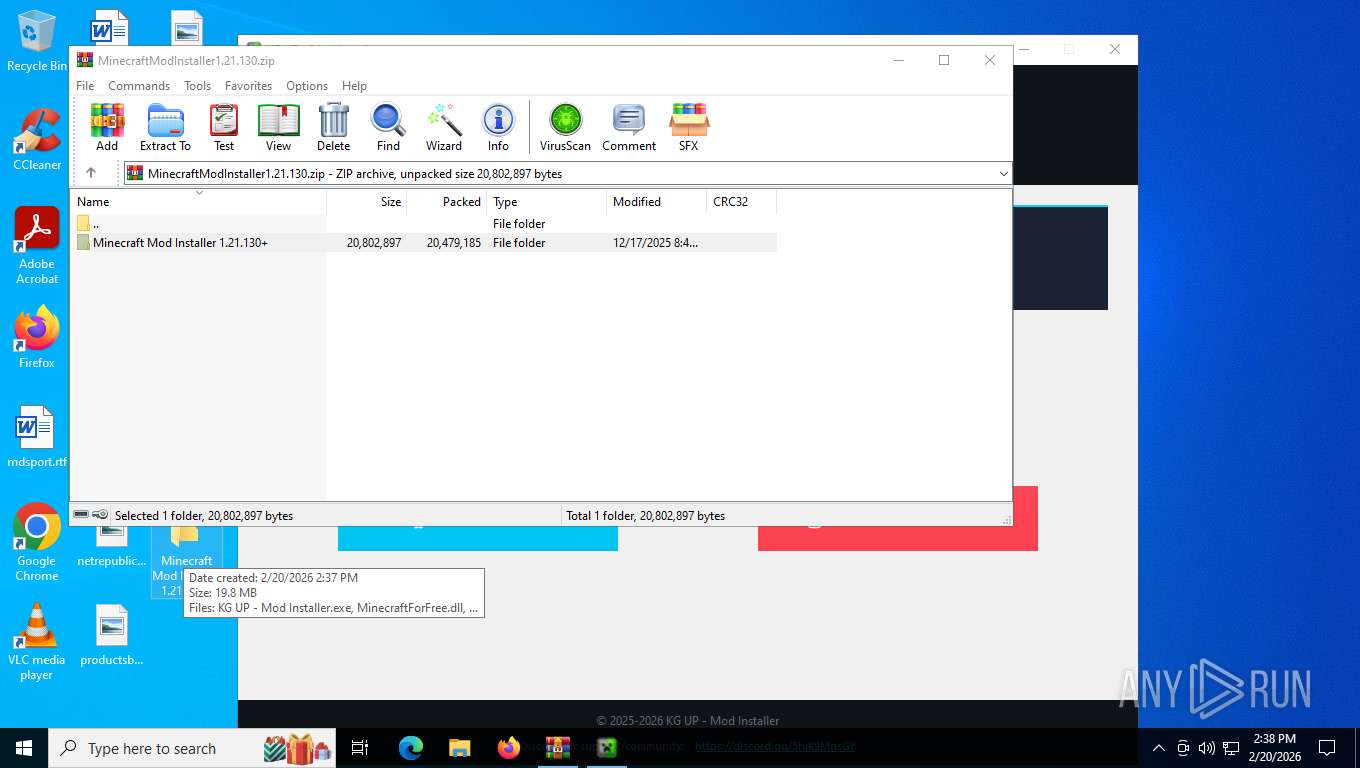
| File name: | MinecraftModInstaller1.21.130.zip |
| Full analysis: | https://app.any.run/tasks/7f0a338b-28c3-4c32-a04a-5b3d2963e7ce |
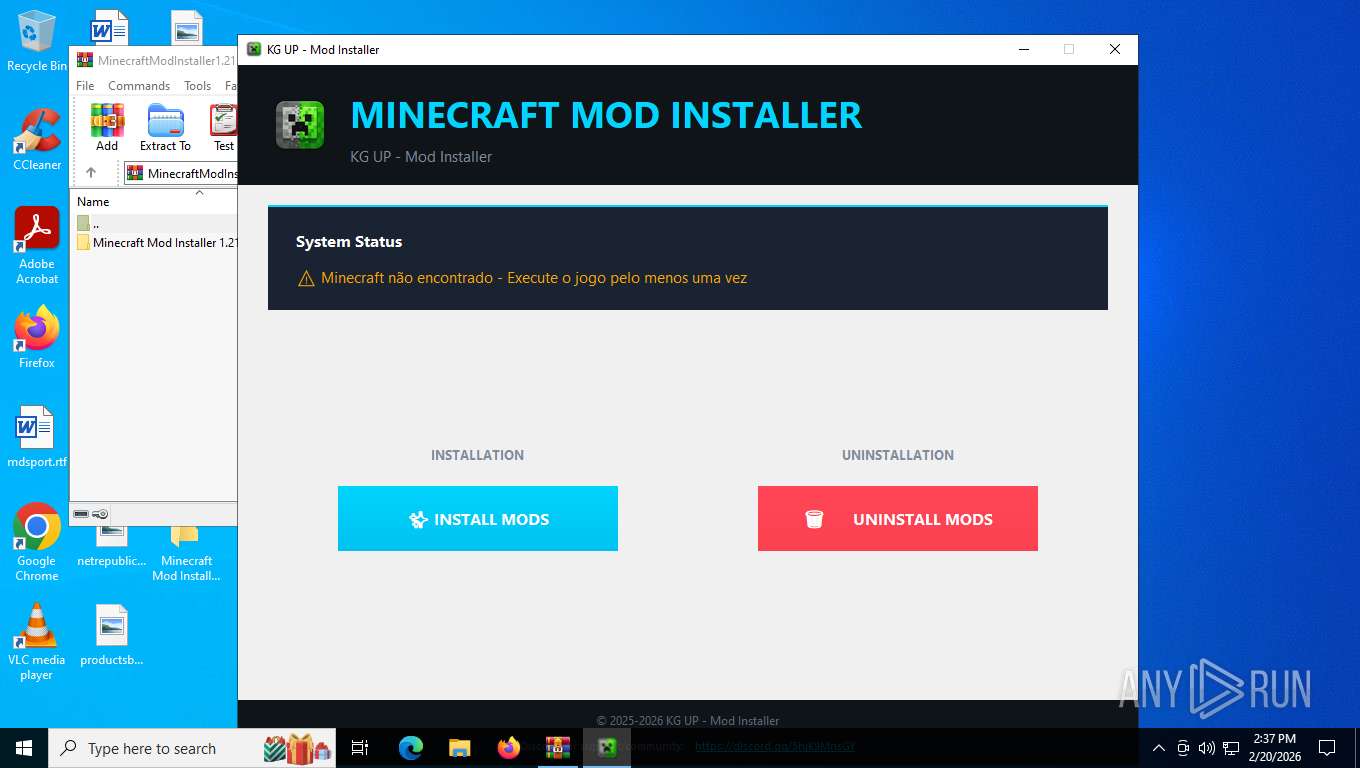
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2026, 19:36:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 572B9FFE1D22CD60C44C03E1B3C9B80C |
| SHA1: | 0A9E8458B39344D29E9D3CA7392B68D581388CAD |
| SHA256: | 99196BB2B86CA56B995C16C4268635CFE3DFAD3BF760A1E6D76CB8AF5330E9B4 |
| SSDEEP: | 196608:/7n2gc+MvK2mEUQoJVGHCb1Yyuq01carA+1YmFLNnj0:/7n2gczK2TJoJVGHCb1N/QcUA+msLZw |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 8248)
SUSPICIOUS
Loads Python modules
- KG UP - Mod Installer.exe (PID: 7680)
Process drops python dynamic module
- KG UP - Mod Installer.exe (PID: 5608)
Executable content was dropped or overwritten
- KG UP - Mod Installer.exe (PID: 5608)
Application launched itself
- KG UP - Mod Installer.exe (PID: 5608)
The process drops C-runtime libraries
- KG UP - Mod Installer.exe (PID: 5608)
INFO
Reads the computer name
- KG UP - Mod Installer.exe (PID: 7680)
- KG UP - Mod Installer.exe (PID: 5608)
There is functionality for taking screenshot (YARA)
- KG UP - Mod Installer.exe (PID: 7680)
- KG UP - Mod Installer.exe (PID: 5608)
Checks proxy server information
- slui.exe (PID: 5628)
- KG UP - Mod Installer.exe (PID: 7680)
Manual execution by a user
- KG UP - Mod Installer.exe (PID: 7644)
- KG UP - Mod Installer.exe (PID: 5608)
Checks supported languages
- KG UP - Mod Installer.exe (PID: 5608)
- KG UP - Mod Installer.exe (PID: 7680)
Create files in a temporary directory
- KG UP - Mod Installer.exe (PID: 5608)
The sample compiled with english language support
- KG UP - Mod Installer.exe (PID: 5608)
PyInstaller has been detected (YARA)
- KG UP - Mod Installer.exe (PID: 5608)
- KG UP - Mod Installer.exe (PID: 7680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:12:17 22:49:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Minecraft Mod Installer 1.21.130+/ |
Total processes
145
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5608 | "C:\Users\admin\Desktop\Minecraft Mod Installer 1.21.130+\KG UP - Mod Installer.exe" | C:\Users\admin\Desktop\Minecraft Mod Installer 1.21.130+\KG UP - Mod Installer.exe | explorer.exe | ||||||||||||
User: admin Company: KG UP Integrity Level: HIGH Description: Minecraft Mod Installer - Instalador de mods para Minecraft Bedrock Edition Version: 2.0.0.0 Modules
| |||||||||||||||
| 5628 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7644 | "C:\Users\admin\Desktop\Minecraft Mod Installer 1.21.130+\KG UP - Mod Installer.exe" | C:\Users\admin\Desktop\Minecraft Mod Installer 1.21.130+\KG UP - Mod Installer.exe | — | explorer.exe | |||||||||||
User: admin Company: KG UP Integrity Level: MEDIUM Description: Minecraft Mod Installer - Instalador de mods para Minecraft Bedrock Edition Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
| 7680 | "C:\Users\admin\Desktop\Minecraft Mod Installer 1.21.130+\KG UP - Mod Installer.exe" | C:\Users\admin\Desktop\Minecraft Mod Installer 1.21.130+\KG UP - Mod Installer.exe | — | KG UP - Mod Installer.exe | |||||||||||
User: admin Company: KG UP Integrity Level: HIGH Description: Minecraft Mod Installer - Instalador de mods para Minecraft Bedrock Edition Version: 2.0.0.0 Modules
| |||||||||||||||
| 8248 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\MinecraftModInstaller1.21.130.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
12 553
Read events
12 542
Write events
11
Delete events
0
Modification events
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\MinecraftModInstaller1.21.130.zip | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
60
Suspicious files
3
Text files
897
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\PIL\_imaging.cp314-win_amd64.pyd | binary | |
MD5:D91B4E7D46109B2B0B8225192BB4873D | SHA256:82AE998248C6785A4101E98B8C85A598D51DF8F951CE3759AC27EDE43B763467 | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\PIL\_imagingft.cp314-win_amd64.pyd | binary | |
MD5:6EA2ED9BCA90019EE27528EF7712EFD1 | SHA256:EB309945F9C9C500E37548DA1E0058E4496BEB7AC8906E1F31F4E68448DA358B | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\PIL\_webp.cp314-win_amd64.pyd | binary | |
MD5:D03B8F7B0B2FBDD765BC848CE02BF626 | SHA256:3A60CF8F8E5535C11C192A34130E1C0EB7092AF9A96C02D2AEBA91462E2C158E | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\VCRUNTIME140.dll | binary | |
MD5:32DA96115C9D783A0769312C0482A62D | SHA256:8B10C53241726B0ACC9F513157E67FCB01C166FEC69E5E38CA6AADA8F9A3619F | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\PIL\_imagingmath.cp314-win_amd64.pyd | binary | |
MD5:3FA2E09807837C16E3808B40D98A5FF4 | SHA256:BB3F5FBD4ECF24F5745BB0DA820CB1058635DF1D3F07A85F710E8635C8342BC3 | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\PIL\_imagingtk.cp314-win_amd64.pyd | binary | |
MD5:76BBFB9F30A11AEF2F0BA7A3E3F2F6A4 | SHA256:D78C6E8DF5314FDB13AB01F745069A00AFC90FE137960541DB99DDAF07DC8B89 | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\_ctypes.pyd | binary | |
MD5:5860D45269A360D830807497FDA7DD50 | SHA256:F761AAD10818806531AA431143B30F0D90A0A402B60F6F1C6E406FCC08F4E6B8 | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\_lzma.pyd | binary | |
MD5:47BFBDCB4B88B6D9E6FB7CA72F7929CA | SHA256:3A0C632BA1B9BEF724E87E42011942BA90B0DEE1B47BCD563728899E95DCB723 | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\_bz2.pyd | executable | |
MD5:94FD94A3194EF83BE4437755A14CB810 | SHA256:F0643F805A011EFC704DF472BB431BA231E6AE31FB7BA71328DF1B6F1A9E1AA2 | |||
| 5608 | KG UP - Mod Installer.exe | C:\Users\admin\AppData\Local\Temp\_MEI56082\PIL\_avif.cp314-win_amd64.pyd | binary | |
MD5:7D931C01642EEAB5F5DB6453D0644D70 | SHA256:26B61C89A7783CF6054CEEE03A3D6C50200D45306021EBC4E356E8CD064CD0BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
25
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
1584 | RUXIMICS.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/RUXIM?os=Windows&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3623&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&FlightRing=Retail&AttrDataVer=186&App=RUXIM&AppVer=&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
1324 | svchost.exe | GET | 200 | 184.24.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
1584 | RUXIMICS.exe | GET | 200 | 184.24.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5208 | slui.exe | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | binary | 512 b | whitelisted |
1324 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
3292 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 401 b | whitelisted |
— | — | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | binary | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1324 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1584 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.146:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
1324 | svchost.exe | 184.24.77.16:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 184.24.77.16:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
1584 | RUXIMICS.exe | 184.24.77.16:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
1324 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.kgup.shop |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1324 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |