| File name: | letspro-5.2.9.exe |
| Full analysis: | https://app.any.run/tasks/f550df59-df37-477b-860d-d2724beb67fb |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 14:30:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | D1B9E63EC11EF1D387F790F5DCEE468E |
| SHA1: | 653675A8C2D6E276B13C8691ACDFEAAC71564A24 |
| SHA256: | 9918750033EE2A71828E910DC5BCF0963FFC735A7B3077BC2F0366D6BBEE5F20 |
| SSDEEP: | 196608:T7yPfVmKbOkOisgbxI1VfVOuWIzU1K2zZawE:T7yPftbOkOPgb6dOXSUFZDE |
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- powershell.exe (PID: 5720)
- powershell.exe (PID: 1116)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 1280)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 4172)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 7684)
SUSPICIOUS
Executable content was dropped or overwritten
- letspro-5.2.9.exe (PID: 2136)
- irsetup.exe (PID: 5864)
Reads the date of Windows installation
- letspro-5.2.9.exe (PID: 2136)
Get information on the list of running processes
- irsetup.exe (PID: 5864)
Reads security settings of Internet Explorer
- letspro-5.2.9.exe (PID: 2136)
- irsetup.exe (PID: 5864)
Process drops legitimate windows executable
- irsetup.exe (PID: 5864)
The process drops C-runtime libraries
- irsetup.exe (PID: 5864)
Manipulates environment variables
- powershell.exe (PID: 5384)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 1348)
Removes files via Powershell
- powershell.exe (PID: 3300)
- powershell.exe (PID: 1348)
- powershell.exe (PID: 5384)
Starts POWERSHELL.EXE for commands execution
- irsetup.exe (PID: 5864)
- iusb3mon.exe (PID: 4152)
Base64-obfuscated command line is found
- iusb3mon.exe (PID: 4152)
The process bypasses the loading of PowerShell profile settings
- iusb3mon.exe (PID: 4152)
Connects to unusual port
- iusb3mon.exe (PID: 4152)
Starts CMD.EXE for commands execution
- iusb3mon.exe (PID: 4152)
INFO
The sample compiled with english language support
- letspro-5.2.9.exe (PID: 2136)
- irsetup.exe (PID: 5864)
Create files in a temporary directory
- letspro-5.2.9.exe (PID: 2136)
Reads the computer name
- letspro-5.2.9.exe (PID: 2136)
- iusb3mon.exe (PID: 4152)
Process checks computer location settings
- letspro-5.2.9.exe (PID: 2136)
- irsetup.exe (PID: 5864)
Checks supported languages
- letspro-5.2.9.exe (PID: 2136)
- iusb3mon.exe (PID: 4152)
- irsetup.exe (PID: 5864)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 664)
- powershell.exe (PID: 5720)
- powershell.exe (PID: 736)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 1116)
- powershell.exe (PID: 4180)
- powershell.exe (PID: 5164)
- powershell.exe (PID: 1240)
- powershell.exe (PID: 6744)
- powershell.exe (PID: 680)
- powershell.exe (PID: 1452)
The sample compiled with chinese language support
- irsetup.exe (PID: 5864)
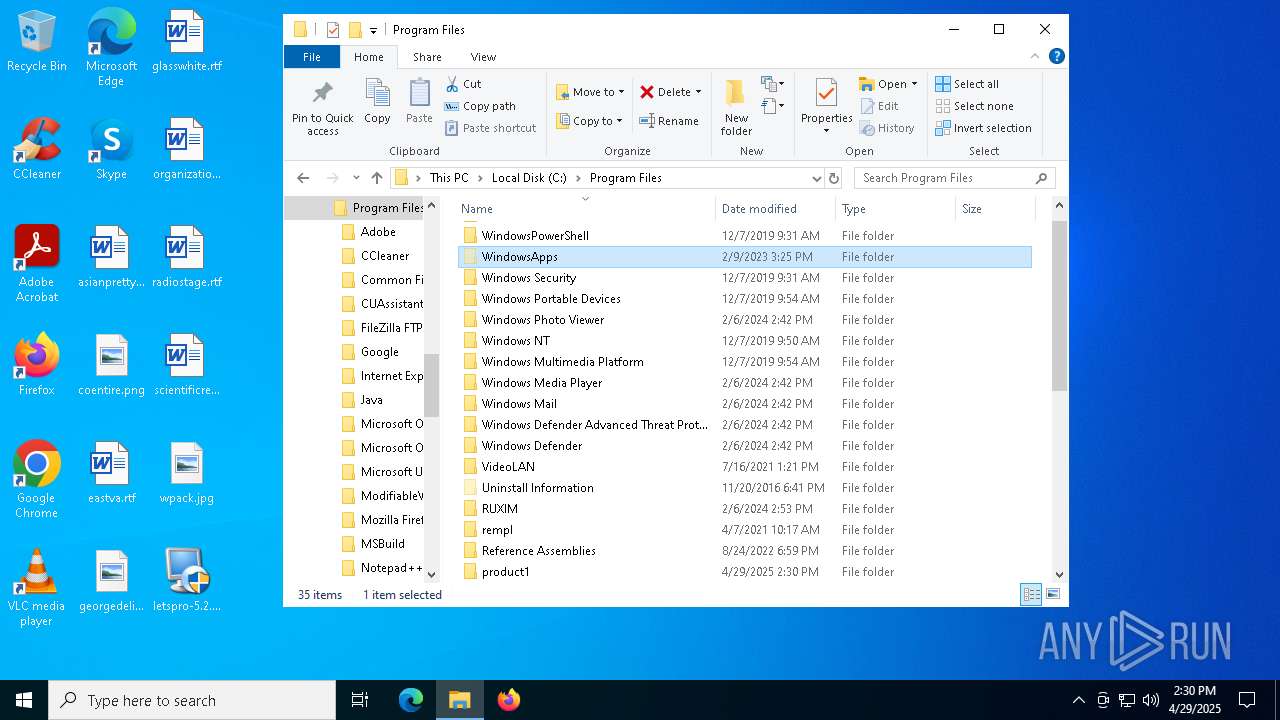
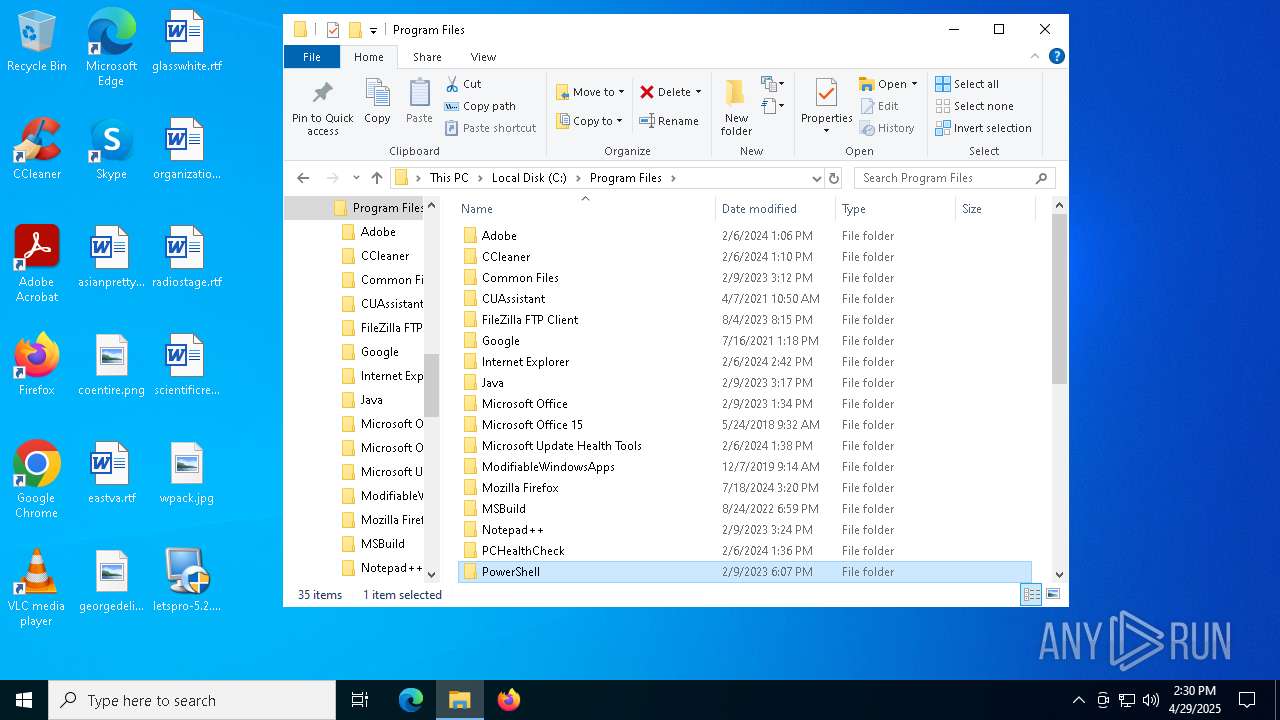
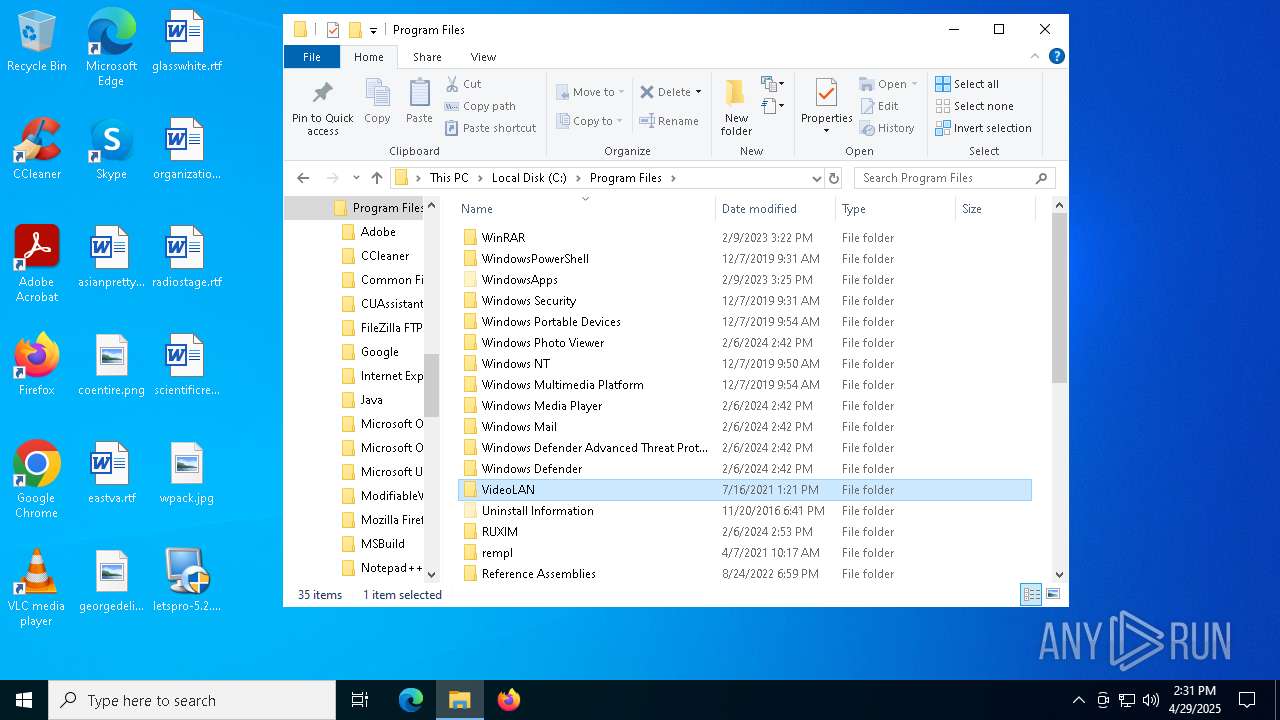
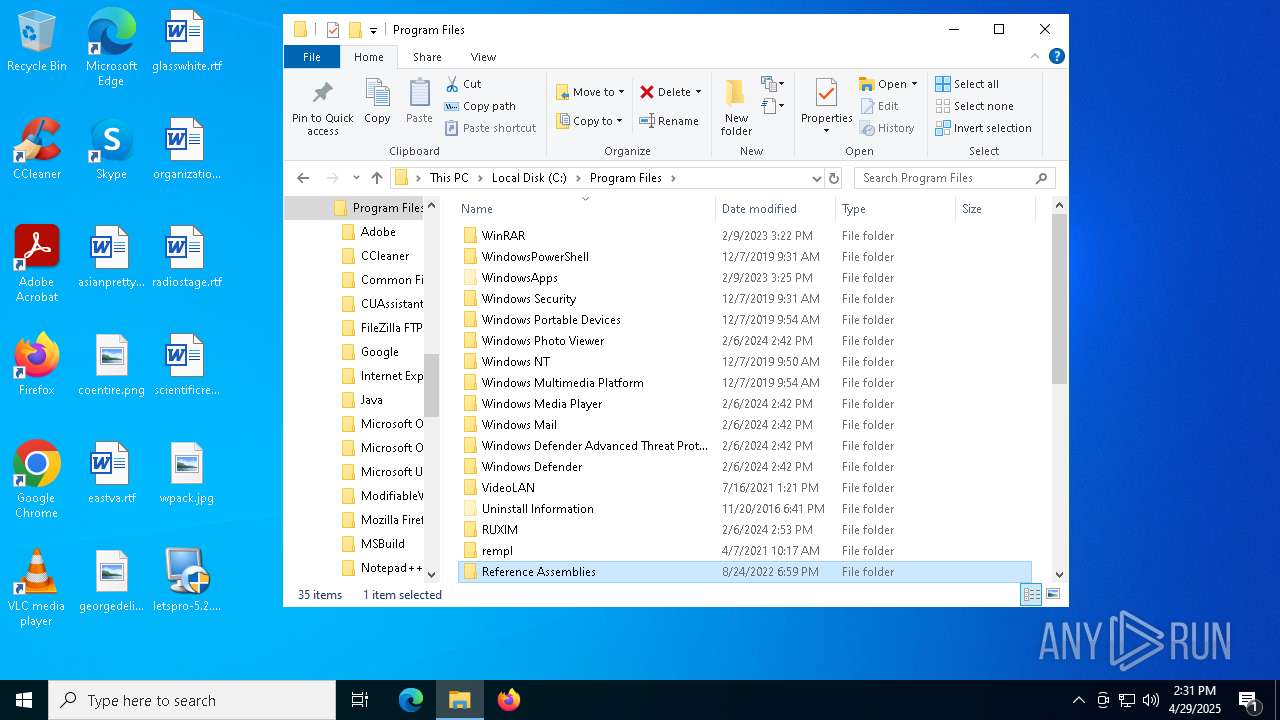
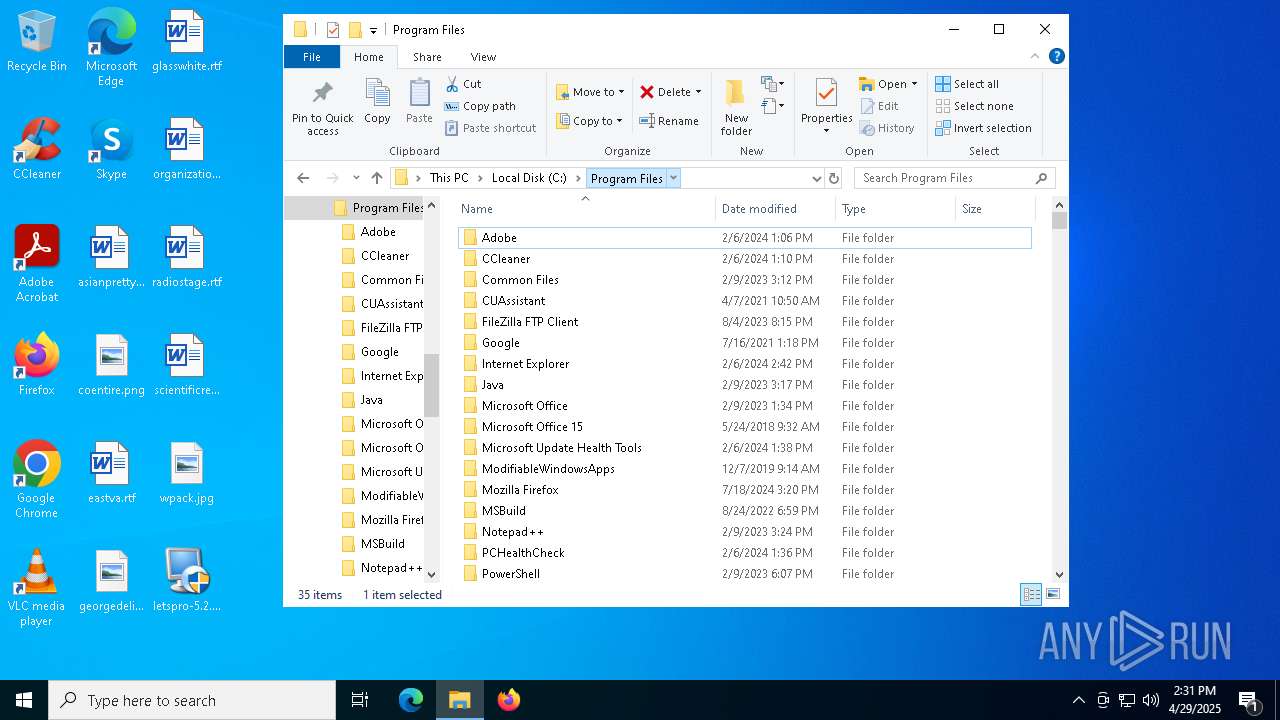
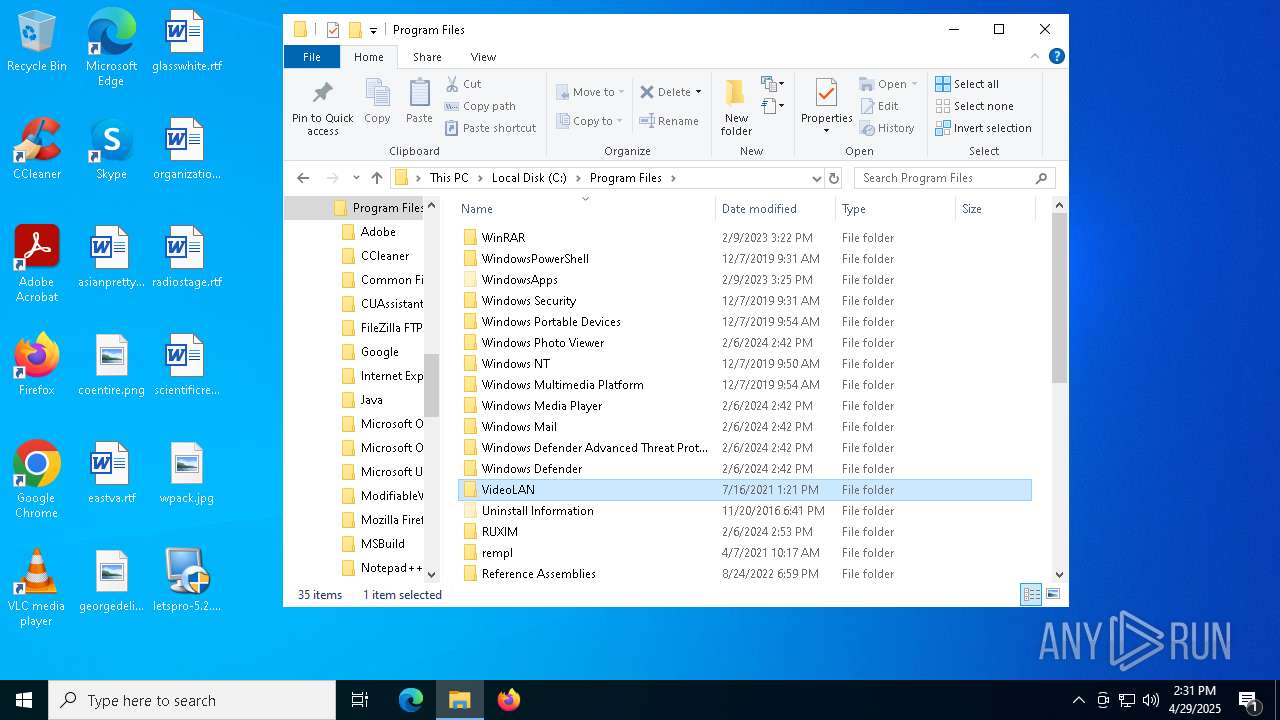
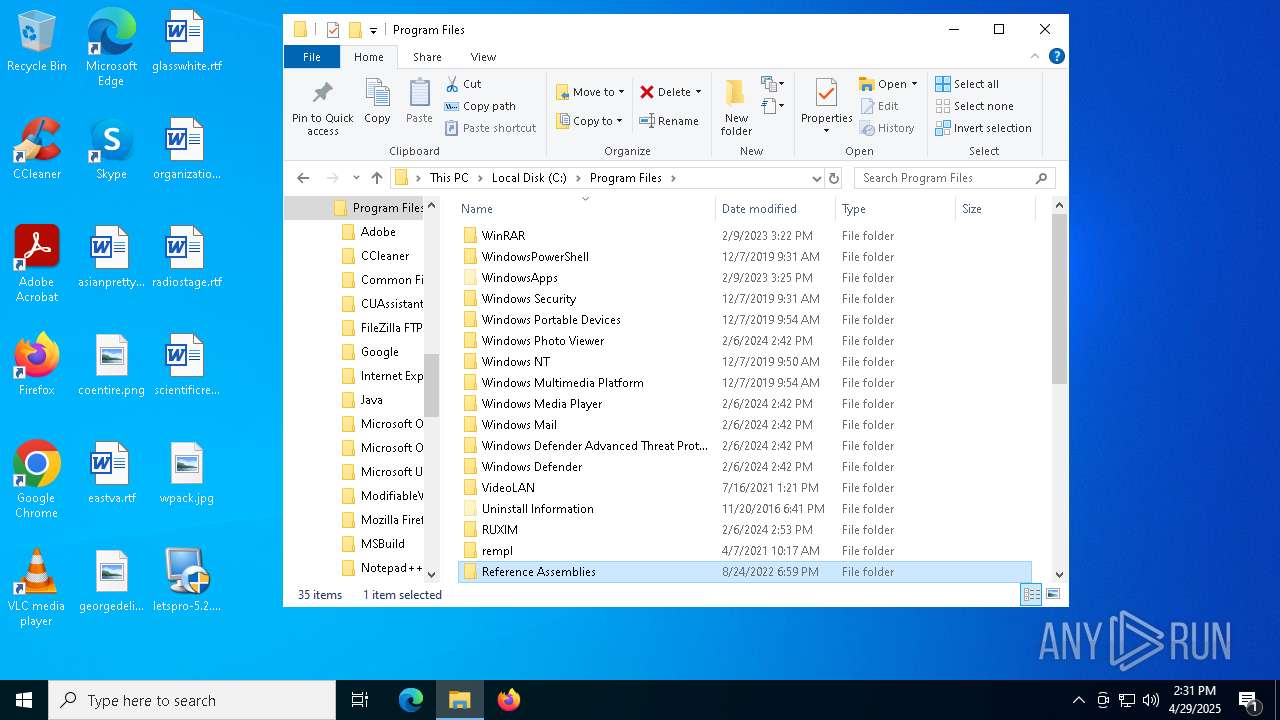
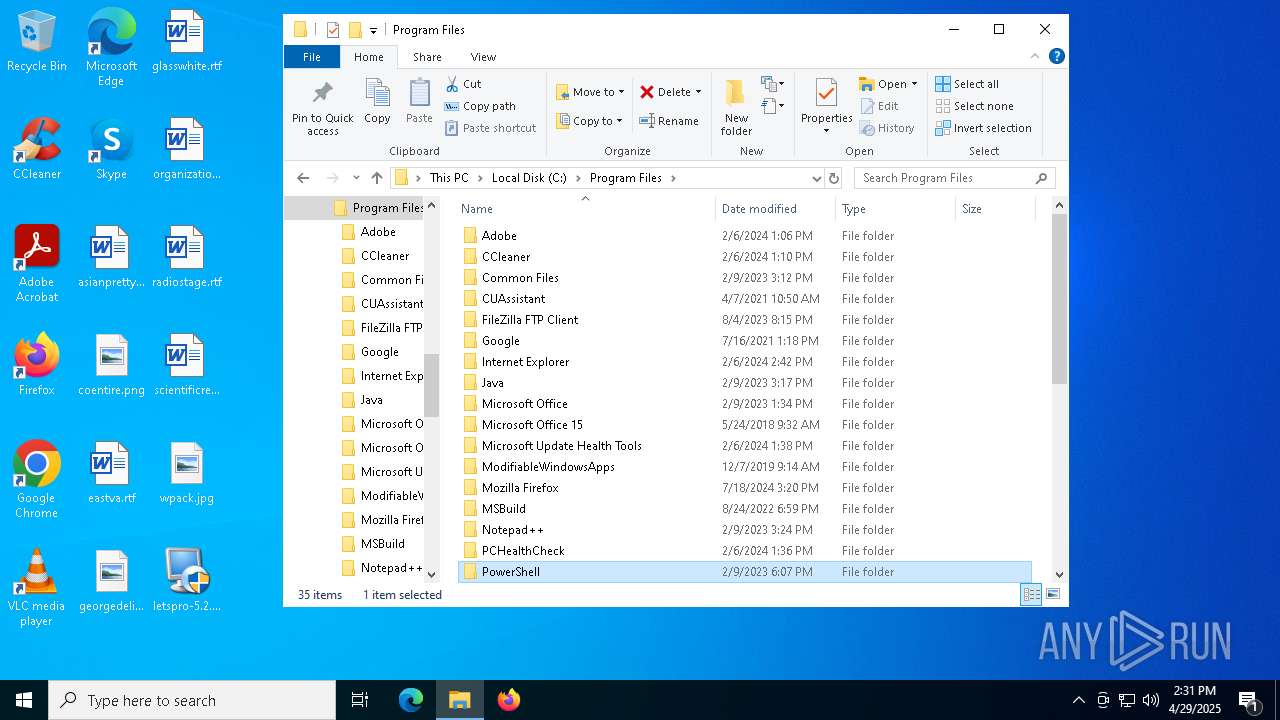
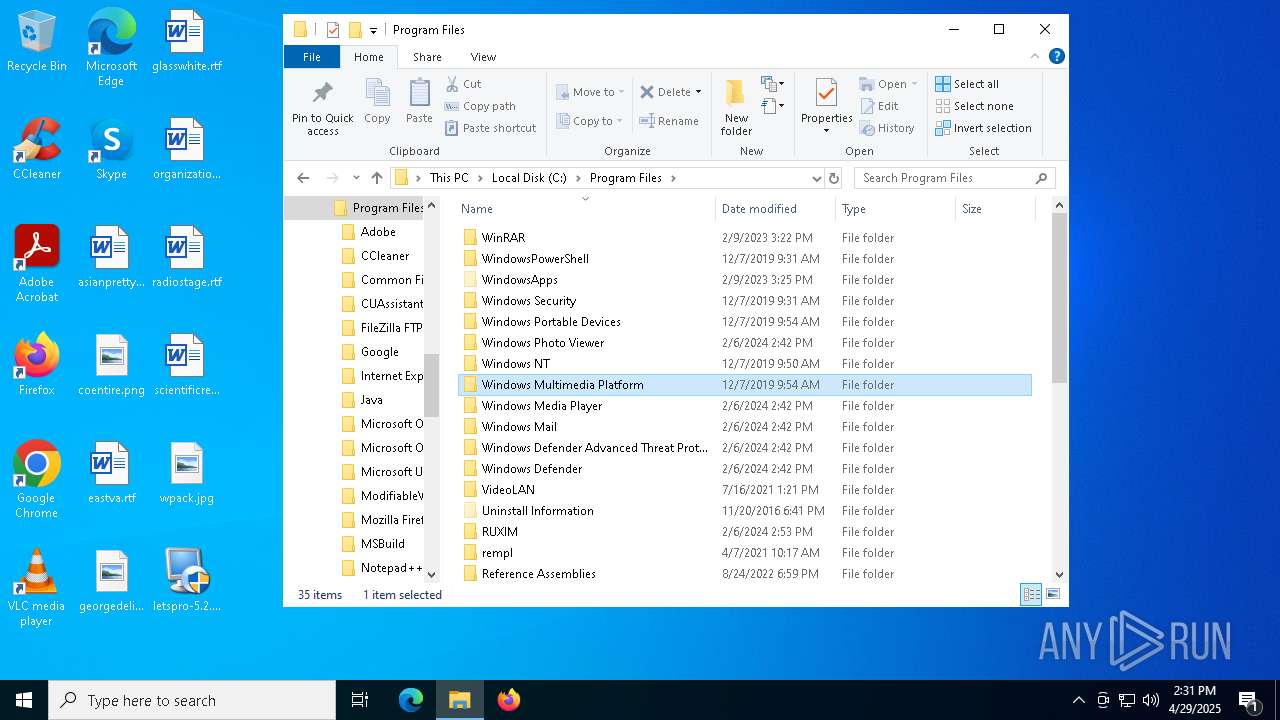
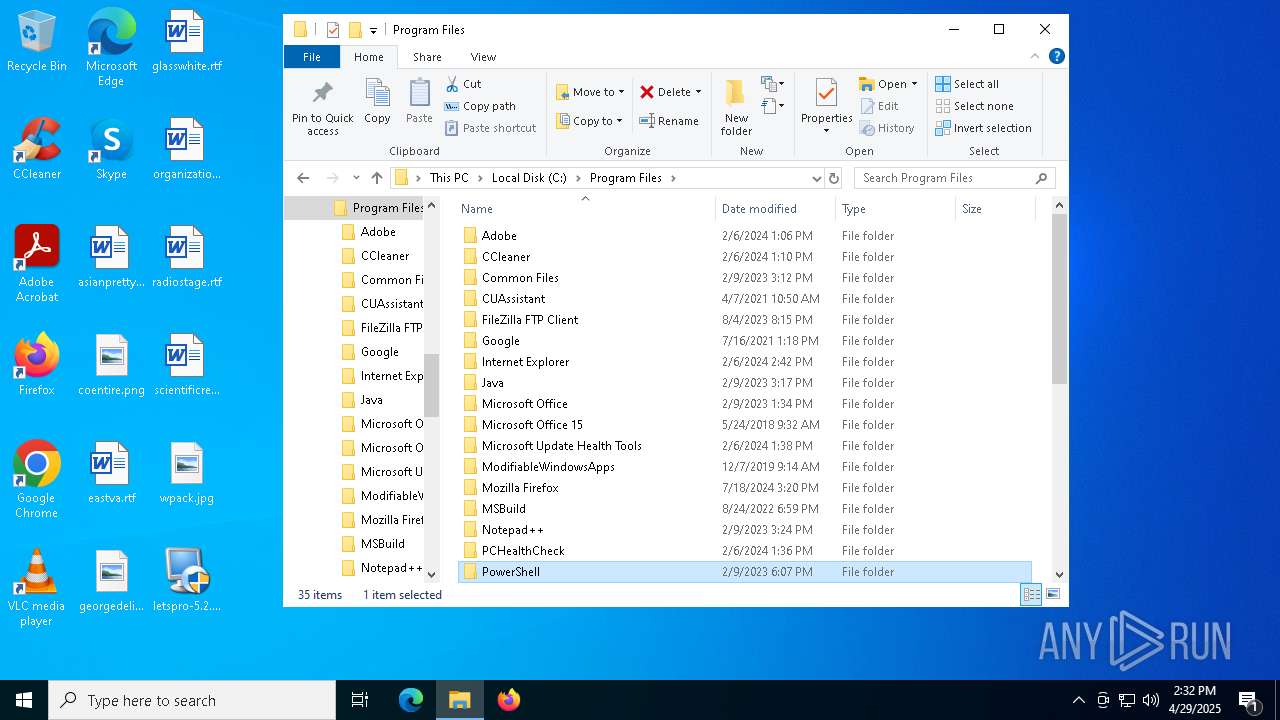
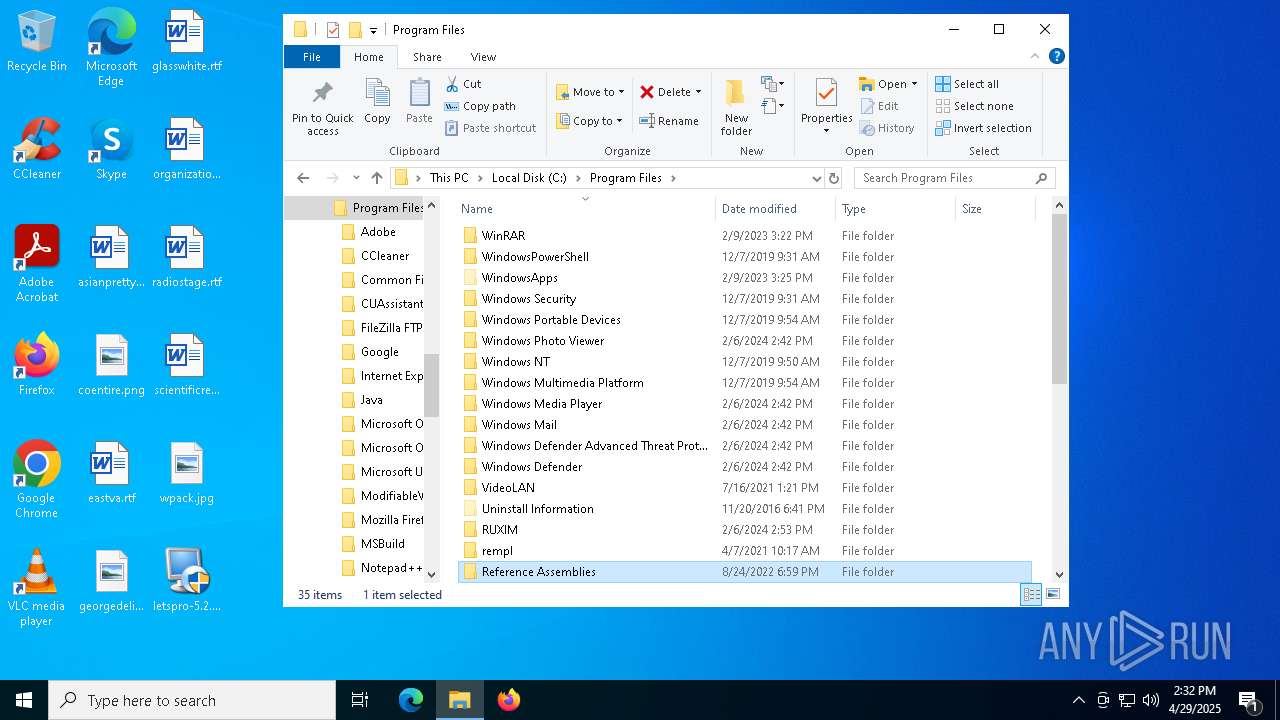
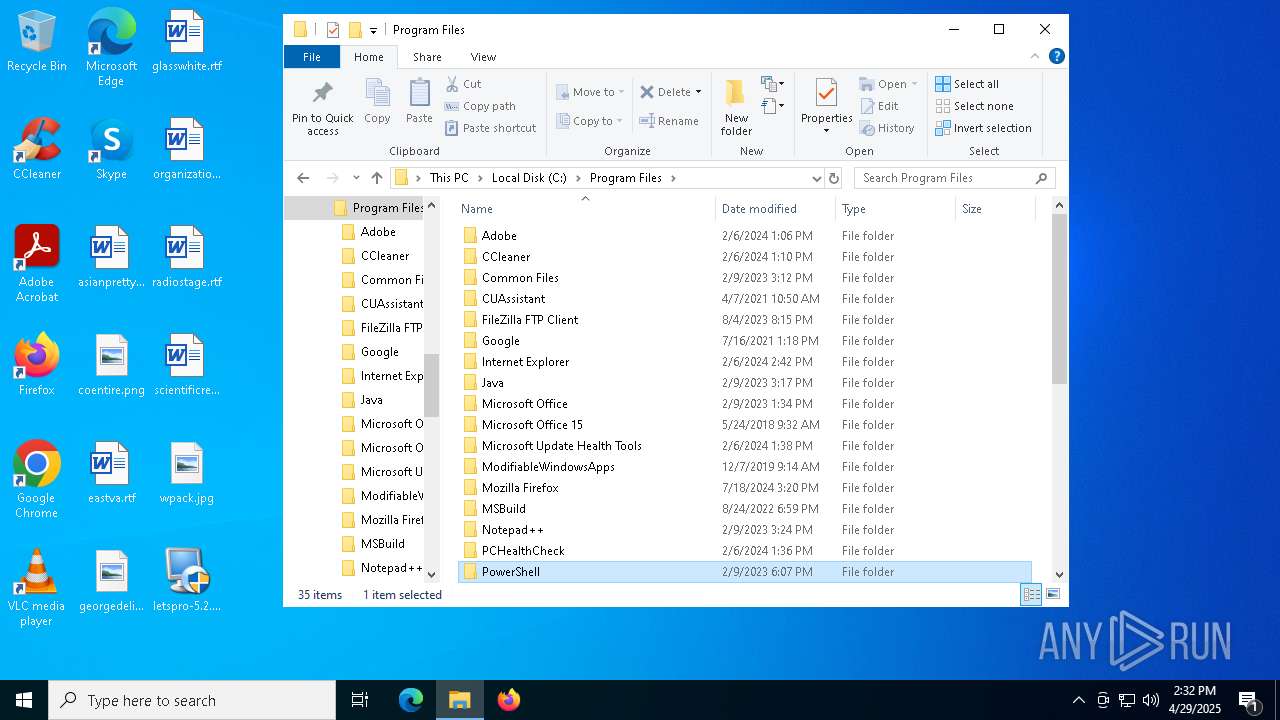
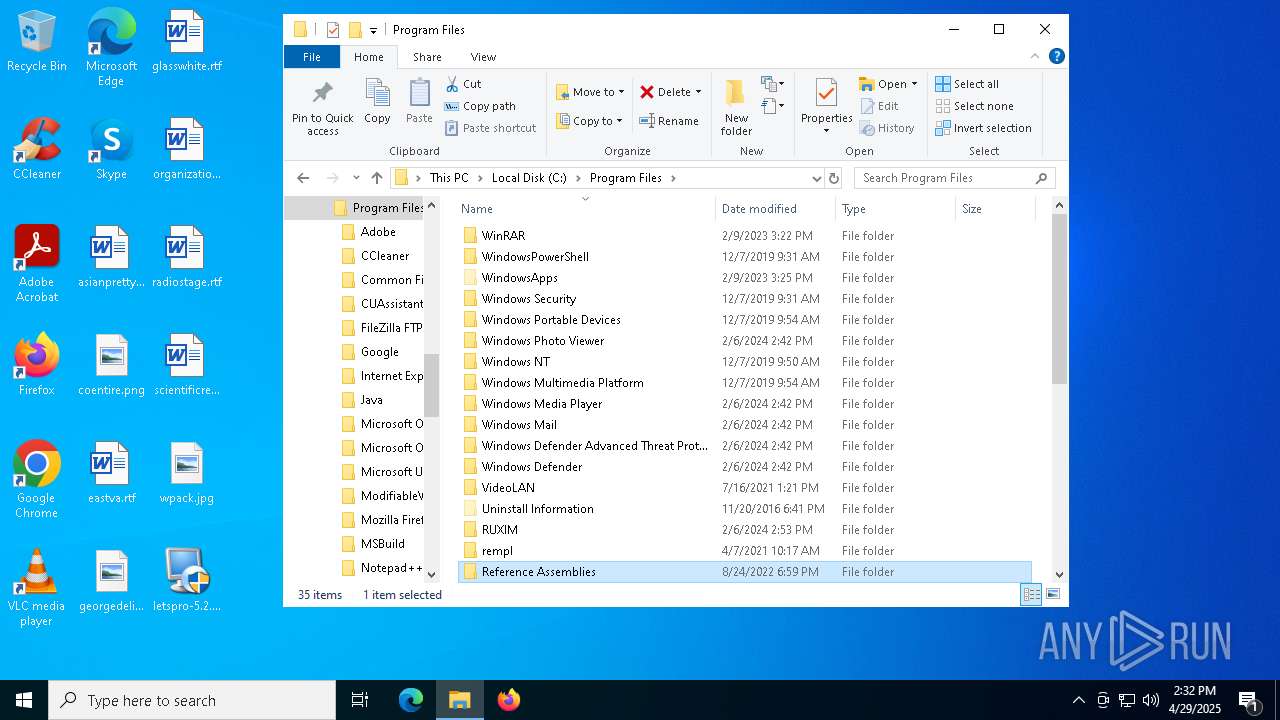
Creates files in the program directory
- irsetup.exe (PID: 5864)
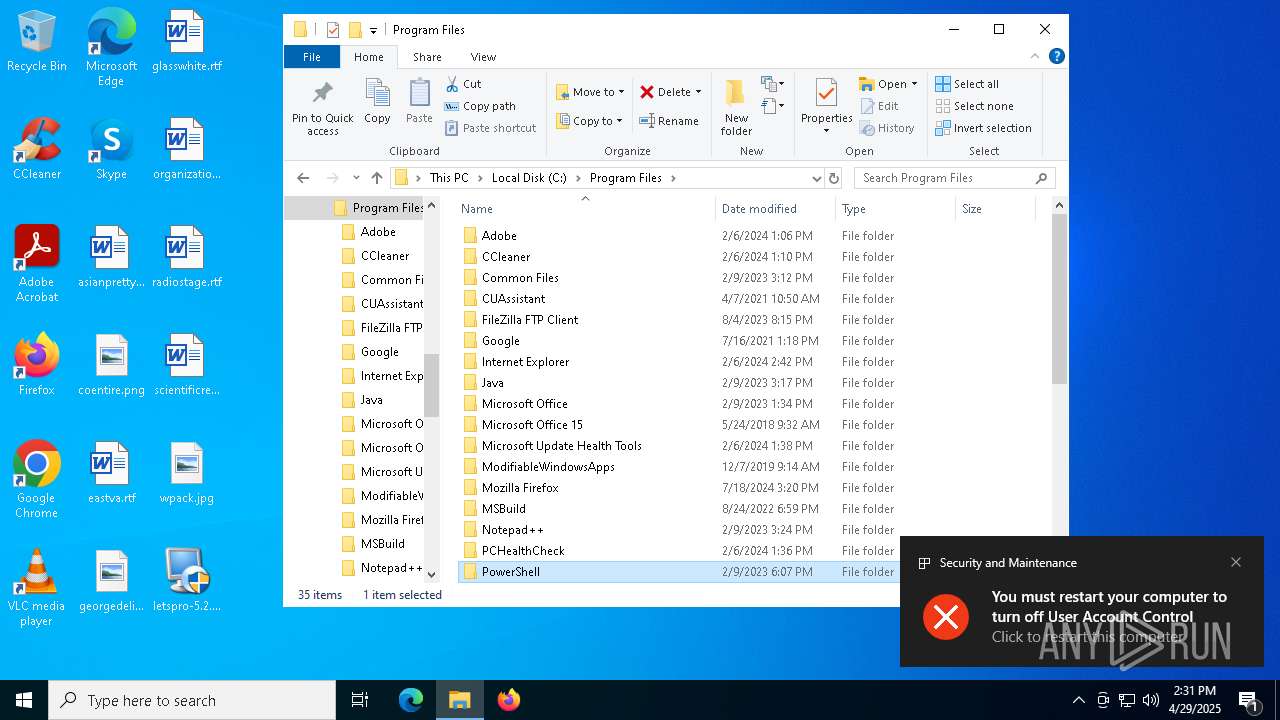
Process checks whether UAC notifications are on
- iusb3mon.exe (PID: 4152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (22.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (19.6) |
| .exe | | | UPX compressed Win32 Executable (19.2) |
| .exe | | | Win32 EXE Yoda's Crypter (18.8) |
| .scr | | | Windows screen saver (9.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:18 16:06:45+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 26112 |
| InitializedDataSize: | 50688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x301c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.7.0.0 |
| ProductVersionNumber: | 9.7.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Created with Setup Factory |
| FileDescription: | Setup Application |
| FileVersion: | 9.7.0.0 |
| InternalName: | suf_launch |
| LegalCopyright: | Setup Engine Copyright © 2004-2024 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | suf_launch.exe |
| ProductName: | Setup Factory Runtime |
| ProductVersion: | 9.7.0.0 |
Total processes
228
Monitored processes
100
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | schtasks.exe /create /tn "Windows Audio Endpoint Builder(ϵͳÒôƵ·þÎñ)" /xml "C:\ProgramData\Microsoft\MicrosoftNetFramework.xml | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Get-Process ([IO.Path]::GetFileNameWithoutExtension(\"360Tray.exe\")); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Get-Process ([IO.Path]::GetFileNameWithoutExtension(\"mpcopyaccelerator.exe\")); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Get-Process ([IO.Path]::GetFileNameWithoutExtension(\"MpDefenderCoreService.exe\")); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Get-Process ([IO.Path]::GetFileNameWithoutExtension(\"msmpeng.exe\")); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Get-Process ([IO.Path]::GetFileNameWithoutExtension(\"mpcopyaccelerator.exe\")); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
64 803
Read events
64 790
Write events
10
Delete events
3
Modification events
| (PID) Process: | (4152) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableLockWorkstation |
Value: 0 | |||
| (PID) Process: | (4152) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (4152) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (4152) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (5164) ShellExperienceHost.exe | Key: | \REGISTRY\A\{b3d03480-7dda-40f4-ffd4-63a9ecc9b1d1}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D000000E8C69E5713B9DB01 | |||
| (PID) Process: | (7392) SecEdit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\SecEdit |
| Operation: | delete value | Name: | LastWinlogonConfig |
Value: | |||
| (PID) Process: | (5332) SecEdit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\SecEdit |
| Operation: | delete value | Name: | LastWinlogonConfig |
Value: | |||
| (PID) Process: | (7384) SecEdit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\SecEdit |
| Operation: | delete value | Name: | LastWinlogonConfig |
Value: | |||
| (PID) Process: | (4152) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft |
Value: C:\ProgramData\Program\iusb3mon.exe | |||
| (PID) Process: | (4152) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft |
Value: C:\ProgramData\Program\iusb3mon.exe | |||
Executable files
7
Suspicious files
6
Text files
34
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | letspro-5.2.9.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\lua5.1.dll | executable | |
MD5:8EE9B911236013B55C120DD608C128D0 | SHA256:9D4B518D4E7EBFA578C653E321EBE2D6E066F4AA023DB1CF2F9B471F08E94CF5 | |||
| 664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jcbc2jcd.unm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sgv3btji.kdi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5720 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_220apn5r.1od.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 680 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c3tjfp31.eri.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5720 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z55mfmjf.0mu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qjma5vxn.nxl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5864 | irsetup.exe | C:\ProgramData\Microsoft\Program\ziliao.jpg | binary | |
MD5:195DBA6CDAA4C3BF23CDD407EF7521D1 | SHA256:2DD158C2D7733708352AD91DD2A8C4A60BBA7C86EECA01AC7AE4C1A4BF013FDE | |||
| 5864 | irsetup.exe | C:\ProgramData\Program\EduWebContainer.dll | executable | |
MD5:7728C745A25AD9F528D91449A0A56352 | SHA256:4975C17C193EE821A0F97D40EF3CD2517A79164541007CE56CAEFACFCF6FEFFD | |||
| 736 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a4cncs3d.bip.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
50
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2908 | SIHClient.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 304 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
2908 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2908 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2908 | SIHClient.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
2908 | SIHClient.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
2908 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
2908 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2908 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2908 | SIHClient.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2908 | SIHClient.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
jjiiee.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |