| File name: | WattpadDownloader.exe |
| Full analysis: | https://app.any.run/tasks/d631e67a-fca7-472d-9268-dfc4256c3a84 |
| Verdict: | No threats detected |
| Analysis date: | March 29, 2018, 21:21:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 97876B1D374B715204D71528E4D7712E |
| SHA1: | 41CDC05462EFFABB856FD3810ED285EC7433CF55 |
| SHA256: | 99166C46612F4422D20CB9F56351A507CBEF066DB898D87AF4DA8DA7C8A3ABE7 |
| SSDEEP: | 49152:IZSXTvvQzmvfwlwXdaSjogI3IGgtyqU8jItS0vG55XL5uIR23c9GAYb3kzTw2PjH:iAvQzyfwlwXdawmD8j |
MALICIOUS
No malicious indicators.SUSPICIOUS
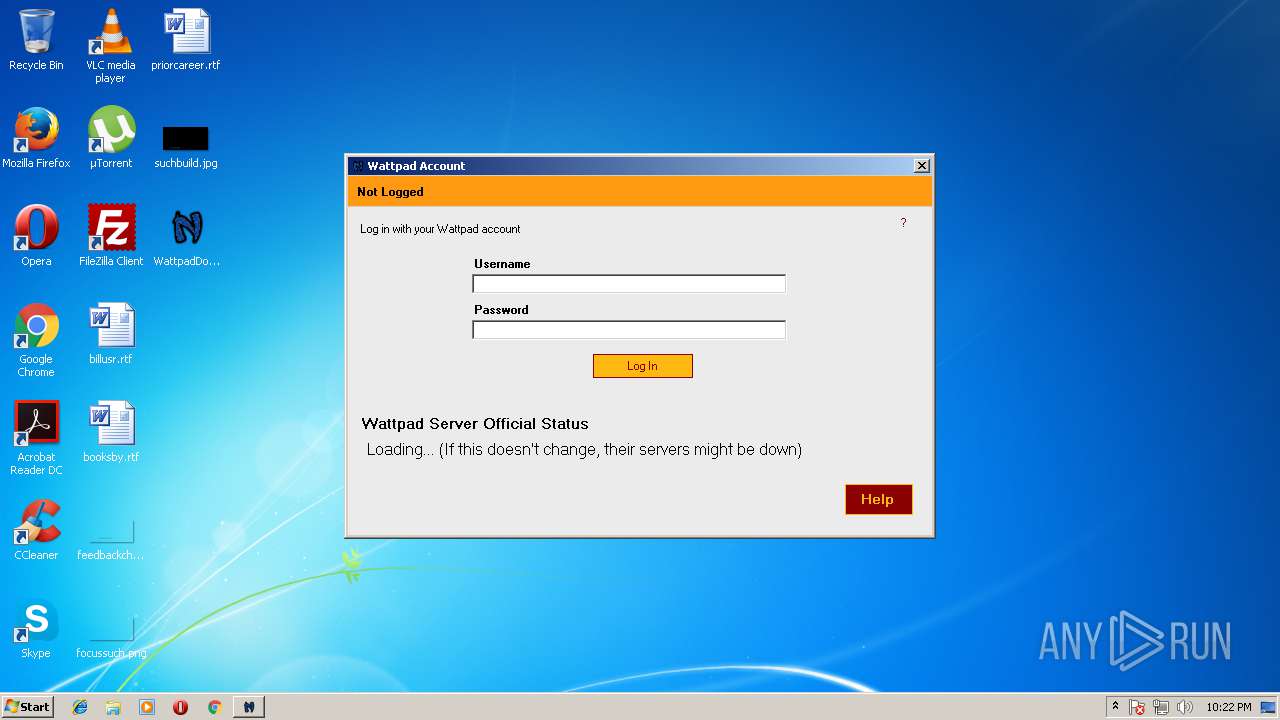
Starts Internet Explorer
- WattpadDownloader.exe (PID: 3276)
Creates files in the user directory
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 2504)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2636)
Loads the .NET runtime environment
- WattpadDownloader.exe (PID: 3276)
Changes internet zones settings
- iexplore.exe (PID: 4036)
Dropped object may contain URL's
- iexplore.exe (PID: 2636)
Creates files in the user directory
- iexplore.exe (PID: 2636)
Loads rich edit control libraries
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 2504)
- WattpadDownloader.exe (PID: 3276)
Reads settings of System Certificates
- iexplore.exe (PID: 2636)
Application launched itself
- iexplore.exe (PID: 4036)
Reads internet explorer settings
- iexplore.exe (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:08 04:34:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 5027328 |
| InitializedDataSize: | 44032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4cd41e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.8.0.0 |
| ProductVersionNumber: | 3.8.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
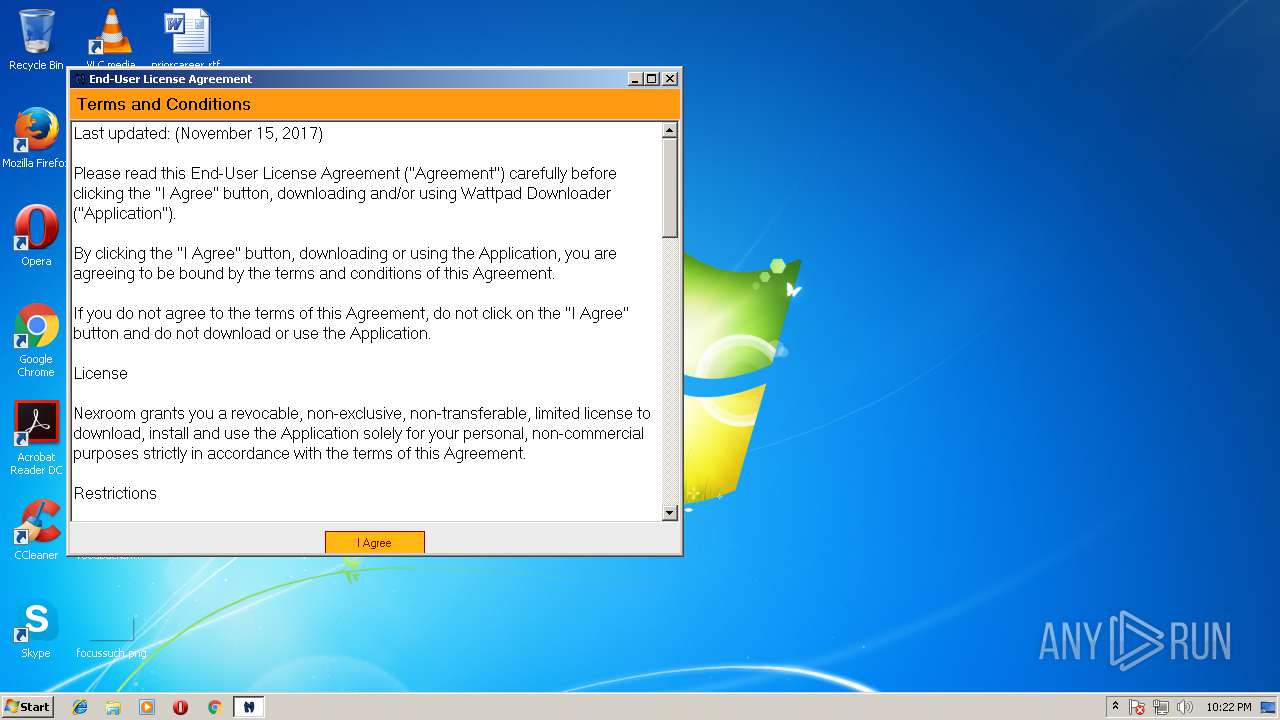
| Comments: | Wattpad Stories Downloader |
| CompanyName: | Nexroom |
| FileDescription: | WattpadDownloader |
| FileVersion: | 3.8.0.0 |
| InternalName: | WattpadDownloader.exe |
| LegalCopyright: | Copyright © Nexroom 2009 - 2018 |
| LegalTrademarks: | Nexroom |
| OriginalFileName: | WattpadDownloader.exe |
| ProductName: | Wattpad Downloader |
| ProductVersion: | 3.8.0.0 |
| AssemblyVersion: | 3.8.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Mar-2018 03:34:04 |
| Debug artifacts: |
|
| Comments: | Wattpad Stories Downloader |
| CompanyName: | Nexroom |
| FileDescription: | WattpadDownloader |
| FileVersion: | 3.8.0.0 |
| InternalName: | WattpadDownloader.exe |
| LegalCopyright: | Copyright © Nexroom 2009 - 2018 |
| LegalTrademarks: | Nexroom |
| OriginalFilename: | WattpadDownloader.exe |
| ProductName: | Wattpad Downloader |
| ProductVersion: | 3.8.0.0 |
| Assembly Version: | 3.8.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Mar-2018 03:34:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x004CB424 | 0x004CB600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.98784 |
.rsrc | 0x004CE000 | 0x0000AA00 | 0x0000AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.22002 |
.reloc | 0x004DA000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
34
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2504 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,137 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4036 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\Desktop\WattpadDownloader.exe" | C:\Users\admin\Desktop\WattpadDownloader.exe | — | explorer.exe | |||||||||||
User: admin Company: Nexroom Integrity Level: MEDIUM Description: WattpadDownloader Exit code: 0 Version: 3.8.0.0 Modules
| |||||||||||||||
| 4036 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | — | WattpadDownloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
465
Read events
392
Write events
73
Delete events
0
Modification events
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3276) WattpadDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WattpadDownloader_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
25
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4036 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3276 | WattpadDownloader.exe | C:\Wpd\cf | text | |
MD5:— | SHA256:— | |||
| 2636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
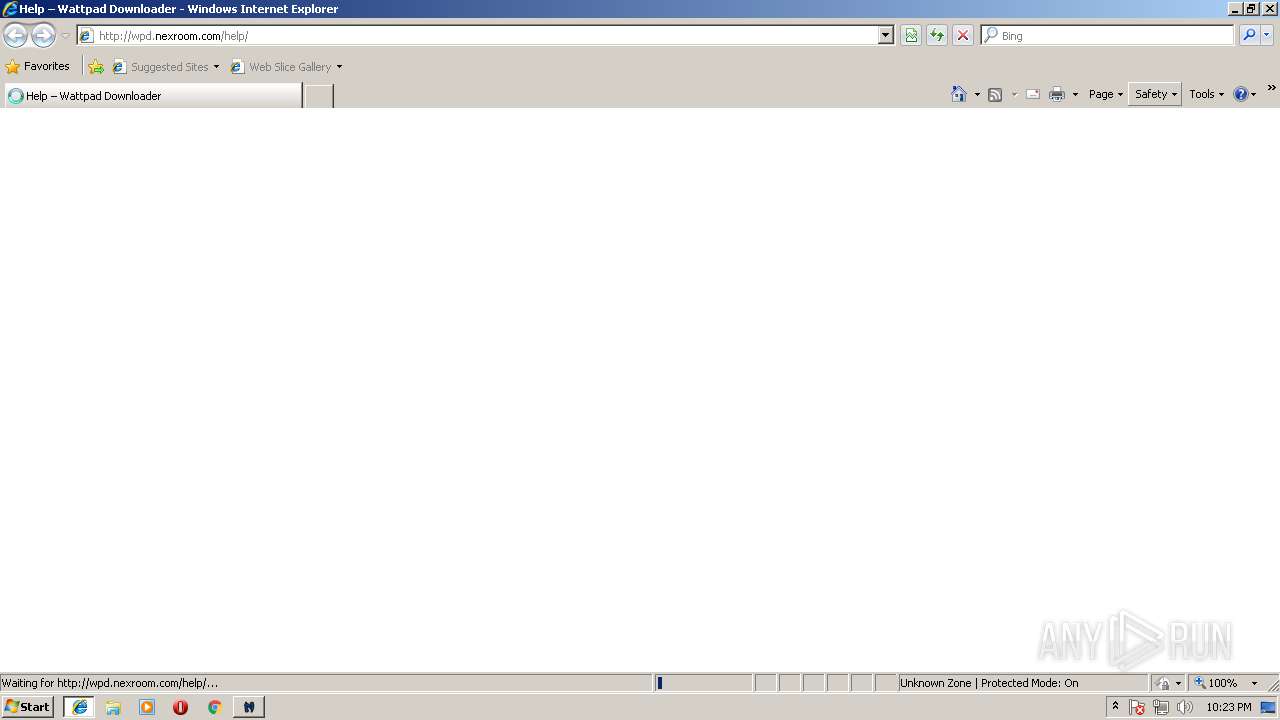
| 2636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\3CF29ENZ\help[1].htm | html | |
MD5:— | SHA256:— | |||
| 2636 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@wpd.nexroom[1].txt | text | |
MD5:— | SHA256:— | |||
| 2636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2636 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF83VWXP\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2636 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@nexroom[2].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
20
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 301 | 50.87.144.239:80 | http://wpd.nexroom.com/en/help/ | US | — | — | unknown |
— | — | GET | — | 50.87.144.239:80 | http://wpd.nexroom.com/wp-content/plugins/ultimate-faqs/css/ewd-ufaq-styles.css?ver=4.9.4 | US | — | — | unknown |
— | — | GET | — | 50.87.144.239:80 | http://wpd.nexroom.com/wp-content/themes/newsbuzz/style.css?ver=4.9.4 | US | — | — | unknown |
— | — | GET | — | 50.87.144.239:80 | http://wpd.nexroom.com/wp-content/themes/newsbuzz/font-awesome/css/font-awesome.min.css?ver=4.9.4 | US | — | — | unknown |
— | — | GET | — | 50.87.144.239:80 | http://wpd.nexroom.com/wp-content/plugins/wpglobus/includes/css/wpglobus.min.css?ver=1.9.9 | US | — | — | unknown |
— | — | GET | — | 50.87.144.239:80 | http://wpd.nexroom.com/wp-content/plugins/google-analytics-for-wordpress/assets/js/frontend.min.js?ver=6.2.8 | US | — | — | unknown |
— | — | GET | 200 | 185.166.140.32:80 | http://status.wattpad.com/ | DE | html | 48.4 Kb | suspicious |
— | — | GET | 200 | 50.87.144.239:80 | http://wpd.nexroom.com/help/ | US | html | 10.7 Kb | unknown |
— | — | GET | 200 | 50.87.144.239:80 | http://nra.nexroom.com/wpd/ccv.php?vns=rJ6unZDCiMMO8wW1EaUj8kC2YkejMPnraRfP35my0nraTelAXKbhQkKnE12iumnfI8Anra69d8eGE1nranra69d8eGE1nra | US | text | 1.13 Kb | unknown |
— | — | GET | — | 50.87.144.239:80 | http://wpd.nexroom.com/wp-content/plugins/ultimate-faqs/css/rrssb-min.css?ver=4.9.4 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 50.87.144.239:80 | nra.nexroom.com | Unified Layer | US | unknown |
— | — | 185.166.140.32:80 | status.wattpad.com | ATLASSIAN PTY LTD | DE | unknown |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 216.58.206.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 216.58.206.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 216.58.206.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 64.233.166.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 216.58.206.227:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nra.nexroom.com |
| unknown |
status.wattpad.com |
| suspicious |
www.bing.com |
| whitelisted |
wpd.nexroom.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
support.wattpaddownloader.com |
| malicious |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |