| File name: | msi.ps1 |
| Full analysis: | https://app.any.run/tasks/a9973e9e-6ac8-49c7-a87c-85befd669673 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 20:23:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 83FC8DF117245DAF855B6C4AA314114F |
| SHA1: | 1102365A2ED7449B799C05DC8EA91A34CC4CD6E5 |
| SHA256: | 99102E61A37335362F89FEDB03FB56DED94101C1C484CAF63009821105D713DE |
| SSDEEP: | 1536:ma4c4pO08JzlpCCXMizXH6ooz1xnjAzMNWgs/oe9K+oiIRiXHku1Dv9OIDQeRfh9:BDMMkjAsu1v3qA7L3qA7L3qA7h4WuX0j |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- powershell.exe (PID: 2956)
- aspnet_compiler.exe (PID: 3764)
Reads the computer name
- aspnet_compiler.exe (PID: 3764)
- powershell.exe (PID: 2956)
Reads the date of Windows installation
- powershell.exe (PID: 2956)
Executes PowerShell scripts
- powershell.exe (PID: 2956)
Creates files in the user directory
- powershell.exe (PID: 2956)
INFO
Checks Windows Trust Settings
- powershell.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
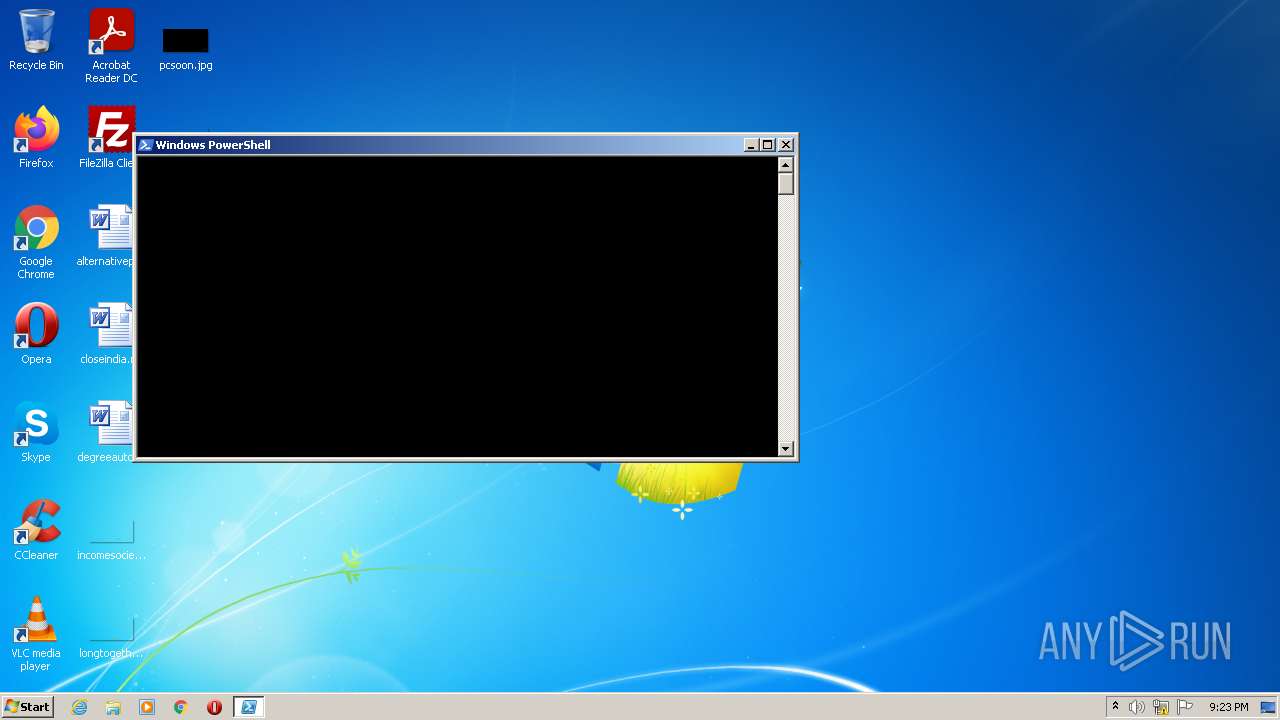
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2956 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\msi.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3764 | #cmd | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
Total events
1 534
Read events
1 470
Write events
64
Delete events
0
Modification events
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3764) aspnet_compiler.exe | Key: | HKEY_CURRENT_USER |
| Operation: | write | Name: | di |
Value: ! | |||
| (PID) Process: | (3764) aspnet_compiler.exe | Key: | HKEY_CURRENT_USER\Software\07b2b3a4d4544765 |
| Operation: | write | Name: | [kl] |
Value: | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFda048.TMP | binary | |
MD5:— | SHA256:— | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Local\Temp\eeywr3px.tu0.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UAKN8063LCYV8BNRUHQ2.temp | binary | |
MD5:— | SHA256:— | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Local\Temp\2hkkxgz2.o5h.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
23
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | aspnet_compiler.exe | 81.171.25.103:5555 | us-microsoft.linkpc.net | LeaseWeb Netherlands B.V. | NL | unknown |
— | — | 81.171.25.103:5555 | us-microsoft.linkpc.net | LeaseWeb Netherlands B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
us-microsoft.linkpc.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to DynDNS Domain (linkpc .net) |