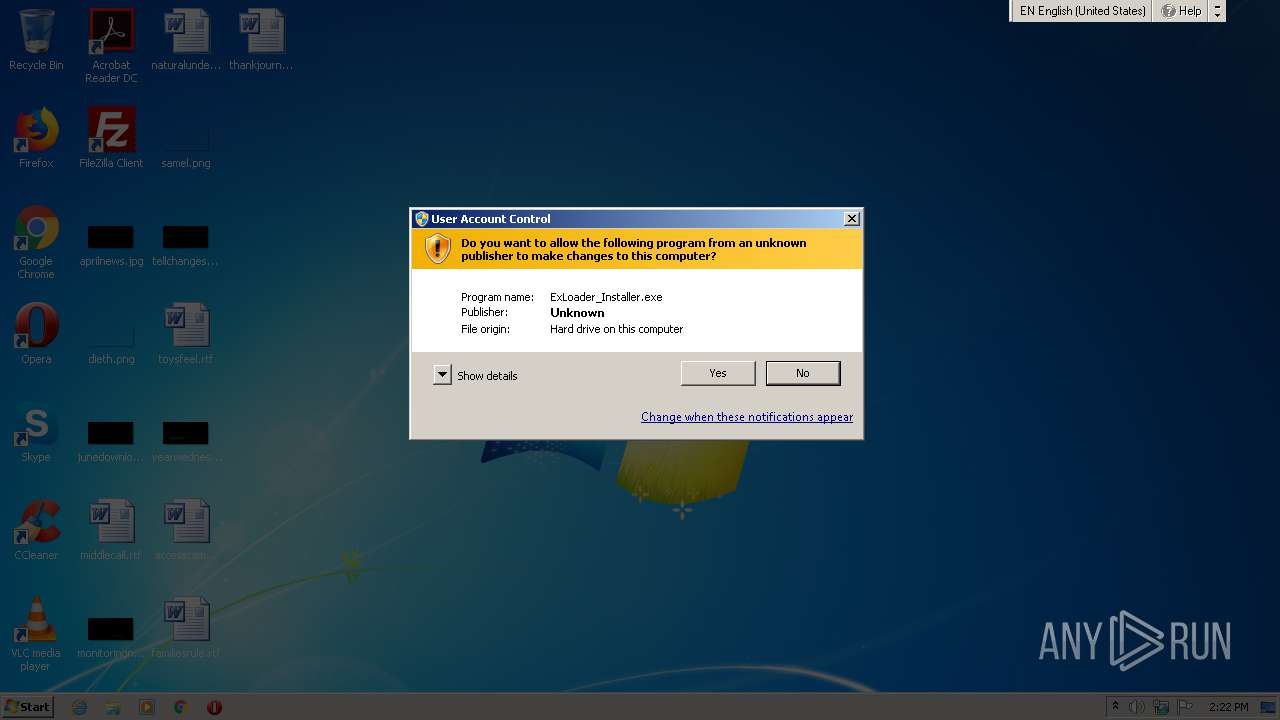
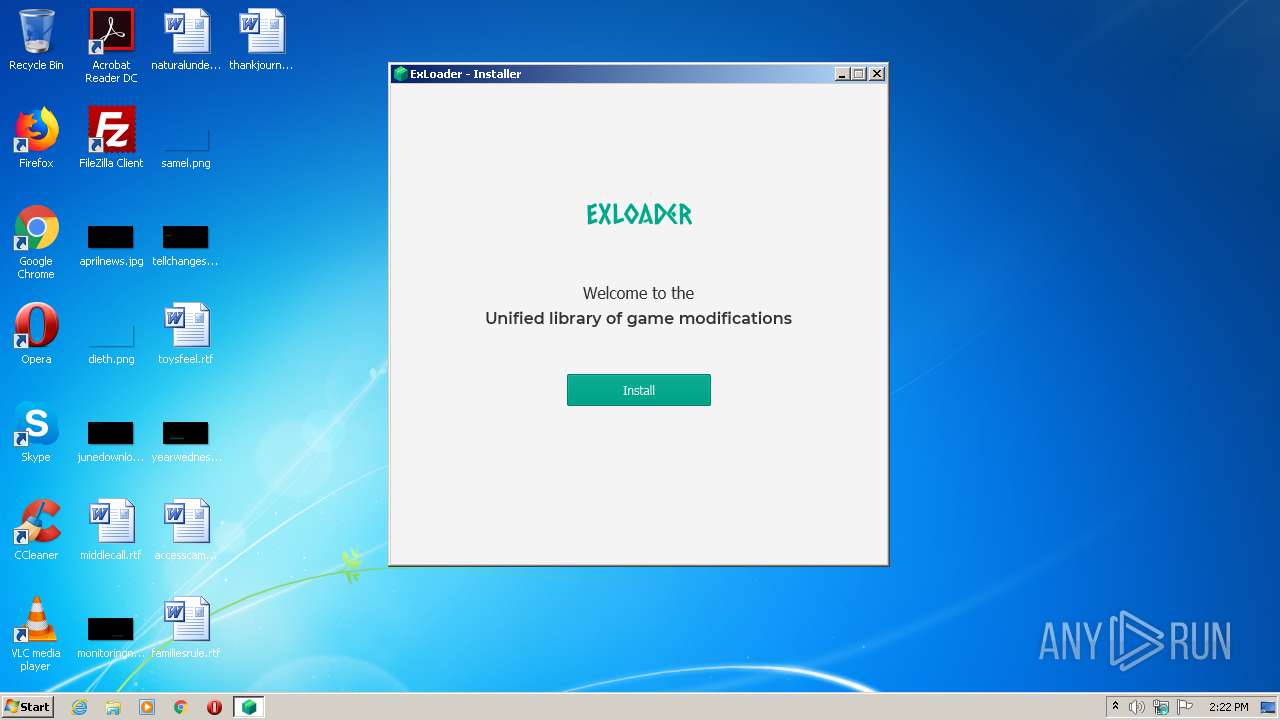
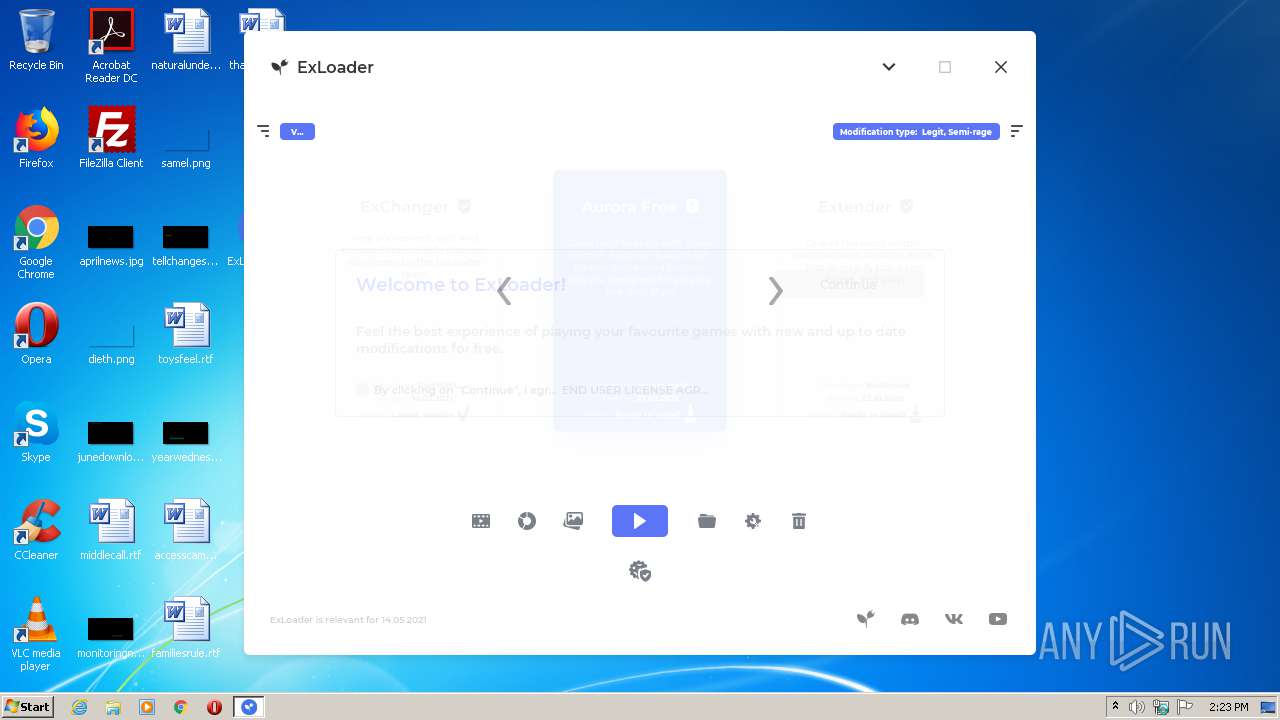
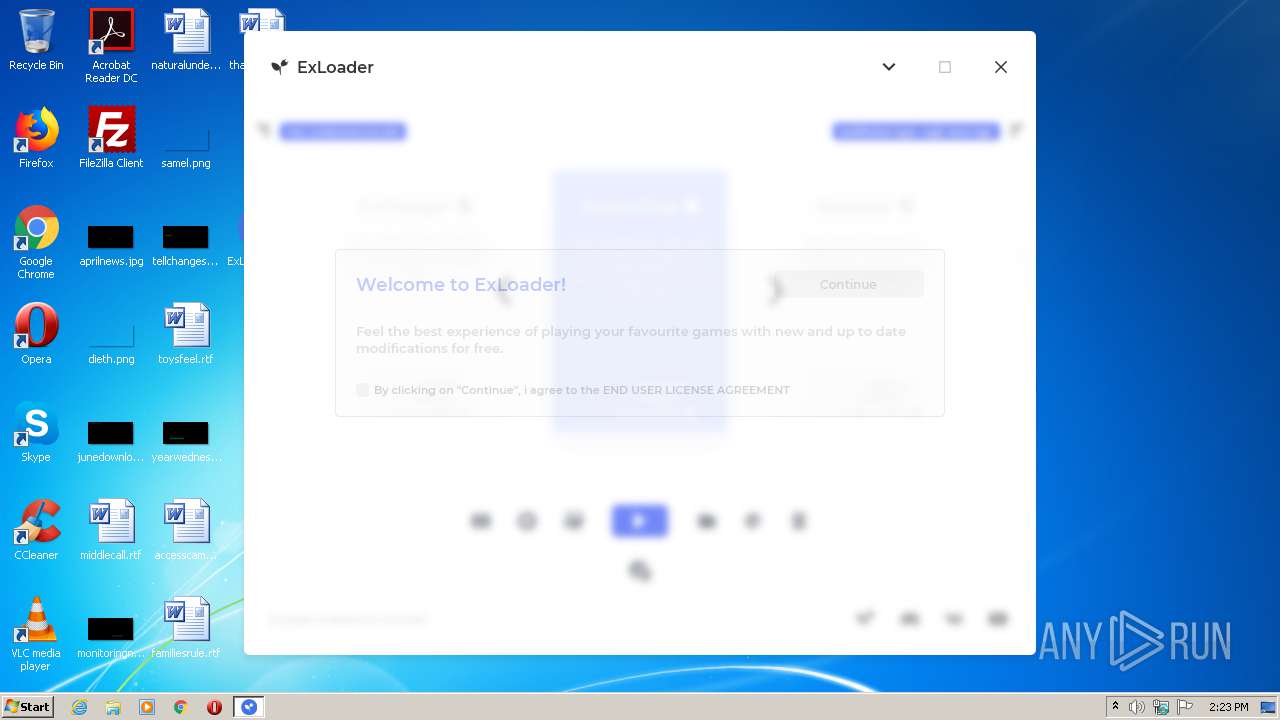
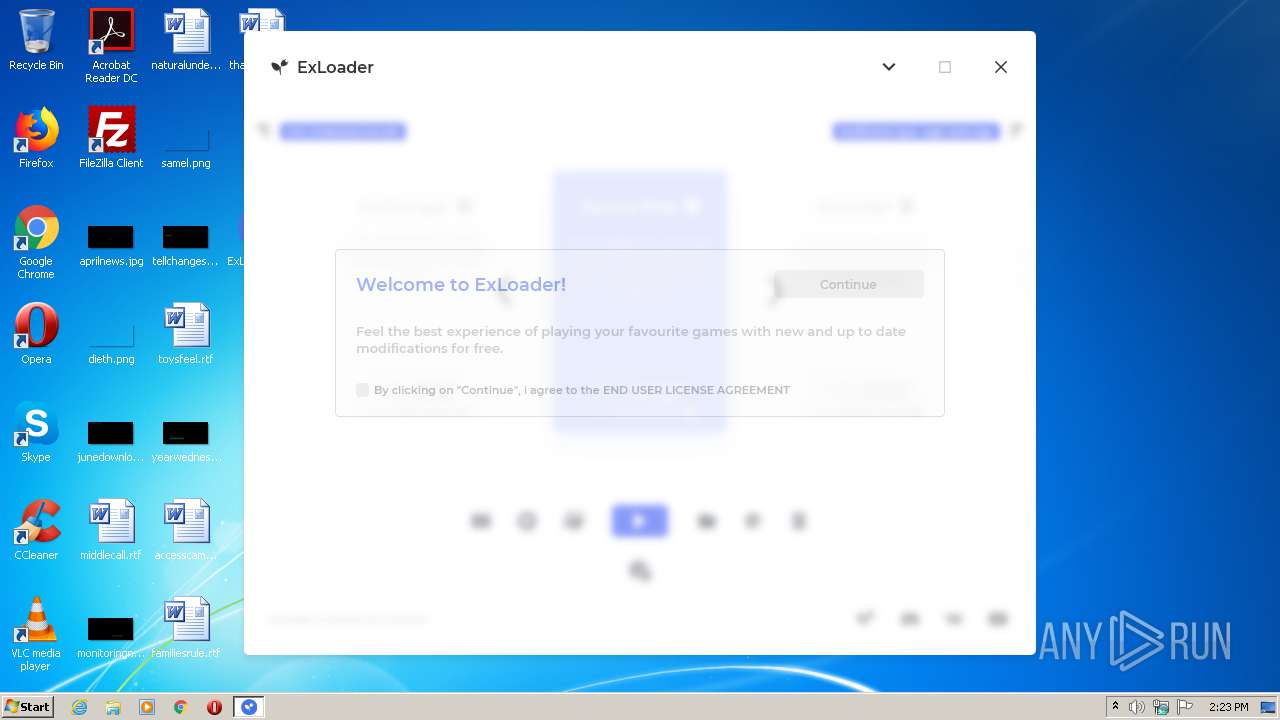
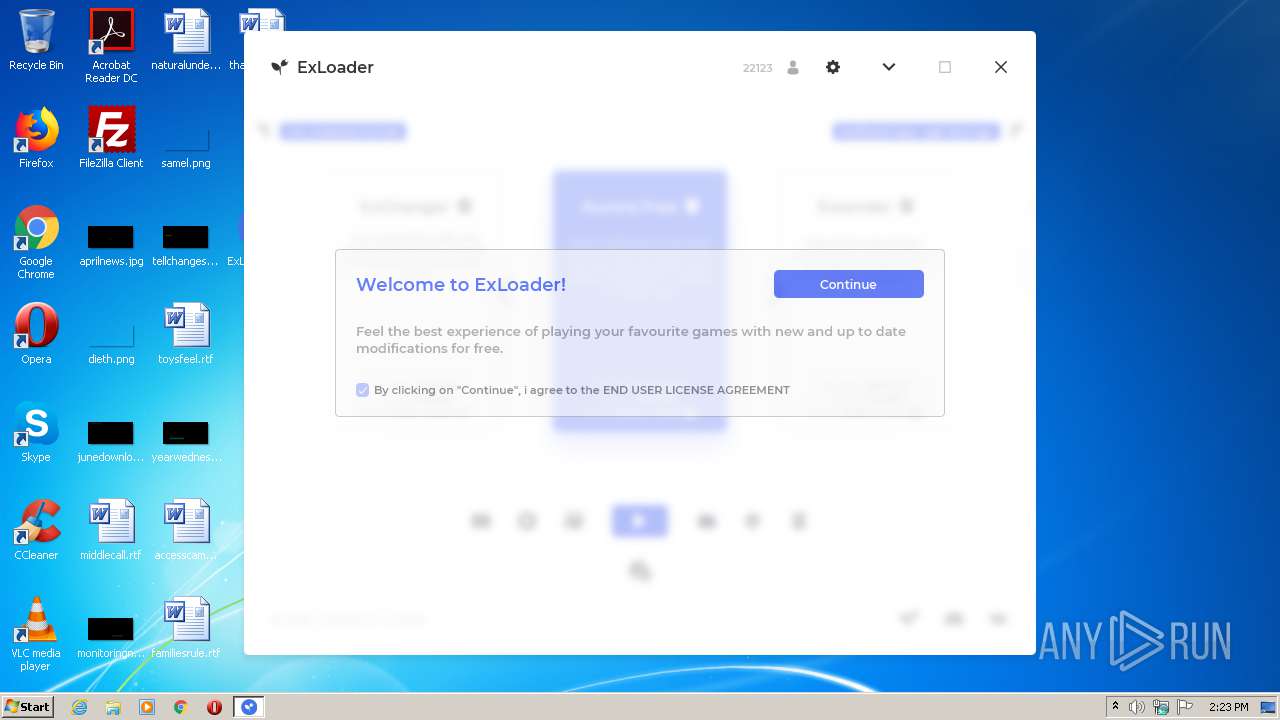
| File name: | ExLoader_Installer.exe |
| Full analysis: | https://app.any.run/tasks/a9ff0591-f298-4ceb-b2fc-5c8a47ae17ba |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2021, 13:22:17 |
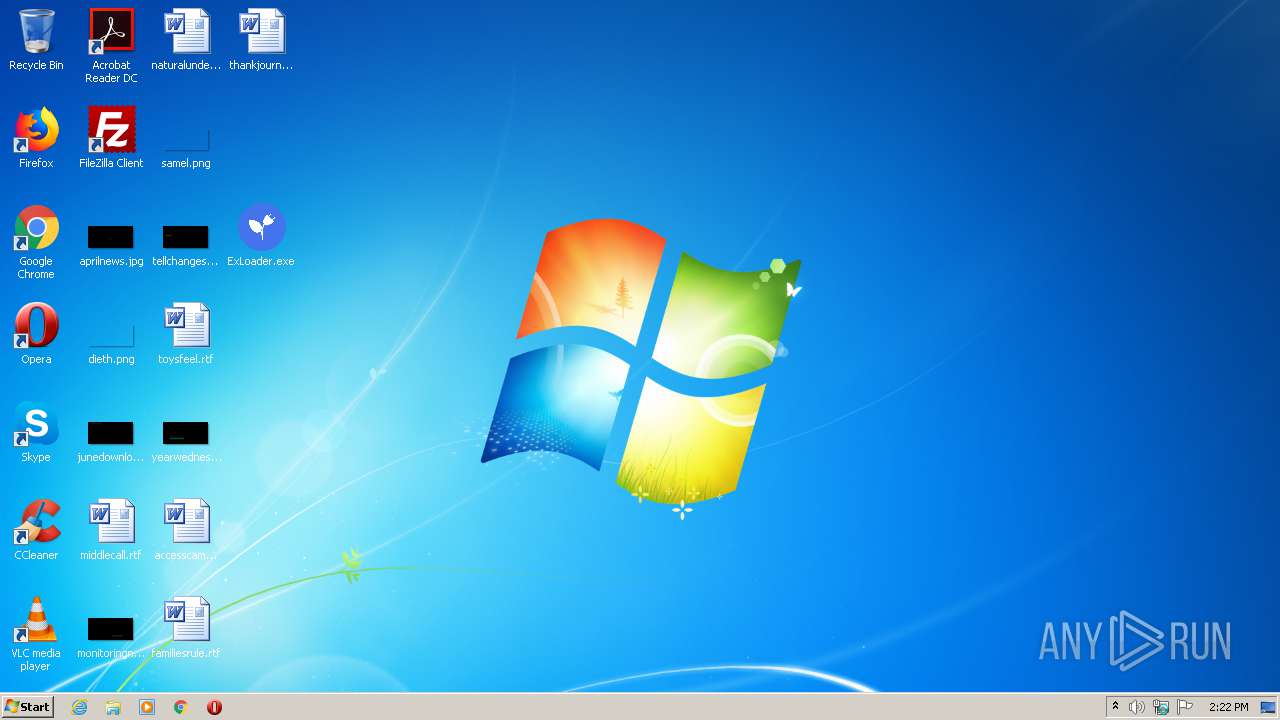
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | CD5E102EC9C6DF3577F63CC96474F977 |
| SHA1: | 98CFDD0BB3F942AB8639A93136018491F2638BA6 |
| SHA256: | 99100F11F3E157F6B994DE9A2D4C0472ED9DF394C6BFEDED686C65D504537236 |
| SSDEEP: | 98304:imZsKg4Ucz1nHmAETG5w74Uu2TBrHJWGs2NyqeoNE/7SRYYGo:i09JnHYK5wHTVHJack+co |
MALICIOUS
Application was dropped or rewritten from another process
- ExLoader.exe (PID: 2284)
SUSPICIOUS
Creates files in the user directory
- javaw.exe (PID: 1864)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 1864)
- javaw.exe (PID: 1720)
Executes JAVA applets
- ExLoader_Installer.exe (PID: 3564)
- ExLoader.exe (PID: 2284)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3732)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 3812)
- cmd.exe (PID: 2480)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 1160)
- cmd.exe (PID: 2488)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 352)
- cmd.exe (PID: 3708)
- cmd.exe (PID: 2848)
- cmd.exe (PID: 2816)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 2784)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 3424)
- cmd.exe (PID: 3380)
- cmd.exe (PID: 1828)
- cmd.exe (PID: 2060)
- cmd.exe (PID: 2696)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 2020)
Starts application with an unusual extension
- cmd.exe (PID: 3464)
- cmd.exe (PID: 3812)
- cmd.exe (PID: 2480)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 2488)
- cmd.exe (PID: 1160)
- cmd.exe (PID: 352)
- cmd.exe (PID: 3708)
- cmd.exe (PID: 2848)
- cmd.exe (PID: 2784)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 2816)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 3424)
- cmd.exe (PID: 3380)
- cmd.exe (PID: 1828)
- cmd.exe (PID: 2060)
- cmd.exe (PID: 2696)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 2020)
- cmd.exe (PID: 3732)
Checks Windows language
- reg.exe (PID: 864)
- reg.exe (PID: 1232)
Executable content was dropped or overwritten
- javaw.exe (PID: 1864)
Drops a file with a compile date too recent
- javaw.exe (PID: 1864)
Creates files in the program directory
- javaw.exe (PID: 1720)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 832)
Uses WMIC.EXE to obtain a list of AntiViruses
- cmd.exe (PID: 3364)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2576)
INFO
Checks supported languages
- reg.exe (PID: 2612)
- reg.exe (PID: 2156)
- reg.exe (PID: 864)
- reg.exe (PID: 1232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1290 |
| UninitializedDataSize: | 36864 |
| InitializedDataSize: | 379392 |
| CodeSize: | 25088 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| TimeStamp: | 2021:05:12 13:35:08+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-May-2021 11:35:08 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 12-May-2021 11:35:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006080 | 0x00006200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.98243 |
.data | 0x00008000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00009000 | 0x00000510 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01355 |
.bss | 0x0000A000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00013000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65264 |
.rsrc | 0x00014000 | 0x0005B59C | 0x0005B600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.00741 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.89003 | 104 | UNKNOWN | Process Default Language | RT_GROUP_ICON |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 3.34315 | 16936 | UNKNOWN | Process Default Language | RT_ICON |
4 | 3.49595 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
5 | 3.79136 | 4264 | UNKNOWN | Process Default Language | RT_ICON |
6 | 3.94447 | 2440 | UNKNOWN | Process Default Language | RT_ICON |
7 | 4.26631 | 1128 | UNKNOWN | Process Default Language | RT_ICON |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
12 | 4.0958 | 22 | UNKNOWN | Process Default Language | RT_RCDATA |
15 | 4.21782 | 41 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
165
Monitored processes
92
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\System32\cmd.exe /c "C:\Windows\System32\chcp.com 65001>nul & C:\Windows\System32\reg.exe query "HKU\S-1-5-19"" | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 444 | reg query "HKEY_CURRENT_USER\Control Panel\International\Geo" /v "Name" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | C:\Windows\System32\chcp.com 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 580 | C:\Windows\System32\chcp.com 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 760 | C:\Windows\System32\chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 832 | cmd /c taskkill /f /im pid 1864 | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 860 | C:\Windows\System32\chcp.com 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | reg query "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Nls\Language" /v "InstallLanguage" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 924 | reg query "HKU\S-1-5-19" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | C:\Windows\System32\cmd.exe /c "C:\Windows\System32\chcp 65001>nul & reg query "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Nls\Language" /v "InstallLanguage"" | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
242
Read events
240
Write events
2
Delete events
0
Modification events
| (PID) Process: | (1864) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (1720) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
1
Suspicious files
0
Text files
11
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1864 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF8356371702120121603.tmp | otf | |
MD5:— | SHA256:— | |||
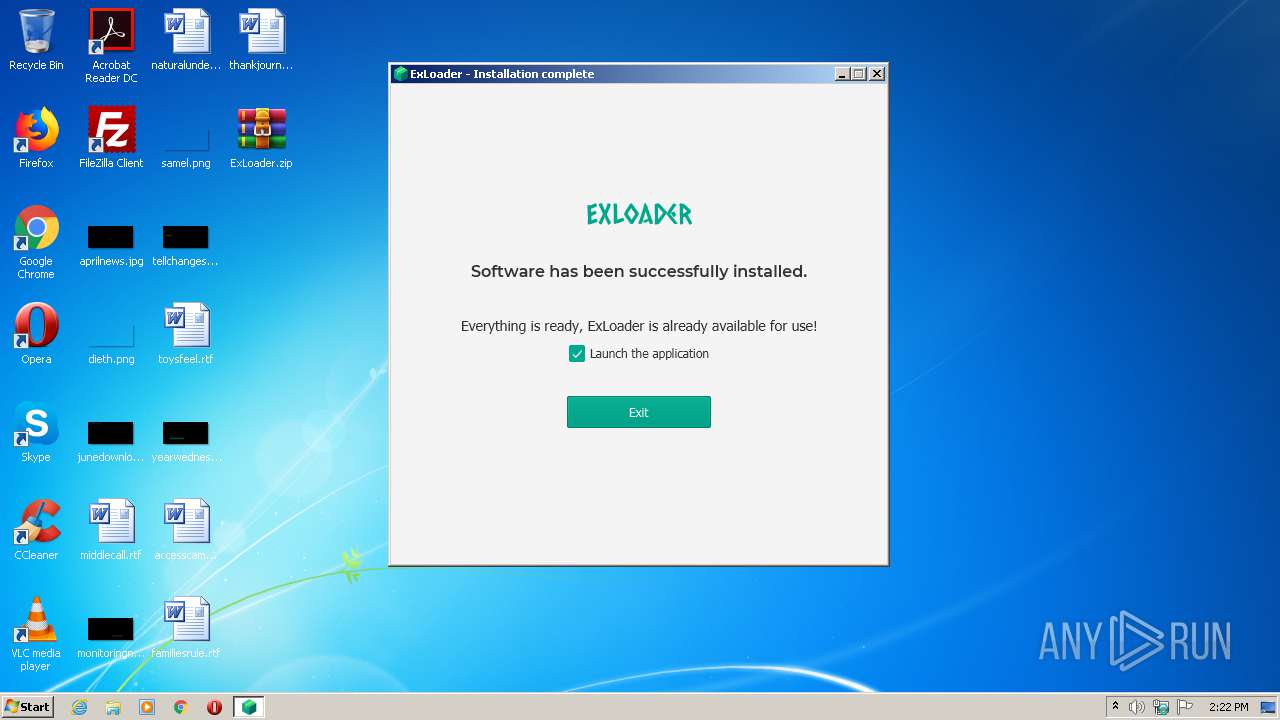
| 1864 | javaw.exe | C:\Users\admin\Desktop\ExLoader.zip | — | |
MD5:— | SHA256:— | |||
| 1864 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 1864 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF6787606109879465278.tmp | ttf | |
MD5:A98626E1AEF6CEBA5DFC1EE7112E235A | SHA256:92B3D3C6E135EB1DC95F88E6CA75BD6113D9EB3261A95CA39F733E3897E53675 | |||
| 1864 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 1864 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF7425964120613288458.tmp | ttf | |
MD5:C88CECBFFAD6D8E731FD95DE49561EBD | SHA256:BAB583D38D105DAC9141B287FB2B7763B6D8B0BAE97E745FAACCEDB40A579C29 | |||
| 1864 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF3195588506488392853.tmp | ttf | |
MD5:9BC77C3BCA968C7490DE95D1532D0E87 | SHA256:257AF9A05DE6371E1F7B345D02A93AF5C2E0AB9B9224418A45189B8CC86049CD | |||
| 1864 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF315852283372096516.tmp | otf | |
MD5:— | SHA256:— | |||
| 1864 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF2569271888922045869.tmp | otf | |
MD5:— | SHA256:— | |||
| 1864 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF8284375993227103330.tmp | ttf | |
MD5:9BC77C3BCA968C7490DE95D1532D0E87 | SHA256:257AF9A05DE6371E1F7B345D02A93AF5C2E0AB9B9224418A45189B8CC86049CD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1864 | javaw.exe | 172.67.130.125:443 | exloader.app | — | US | unknown |
1720 | javaw.exe | 104.21.66.57:443 | exloader.net | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
exloader.app |
| unknown |
exloader.net |
| unknown |