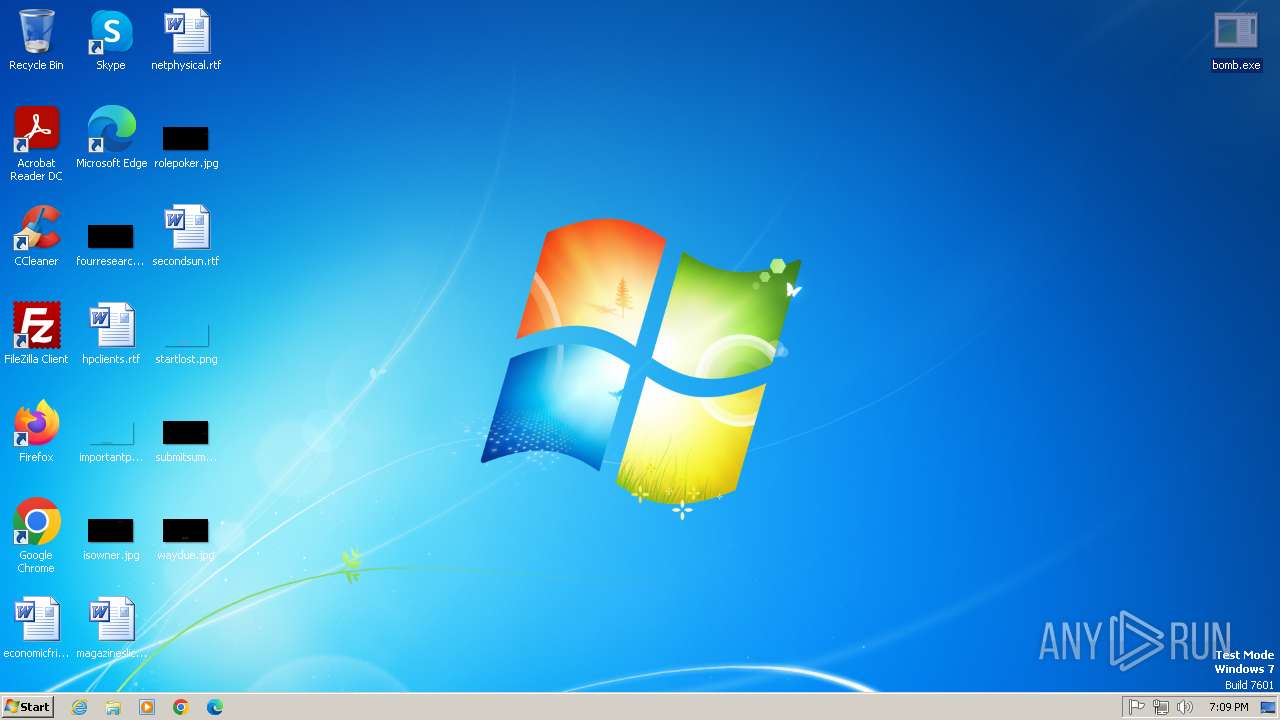
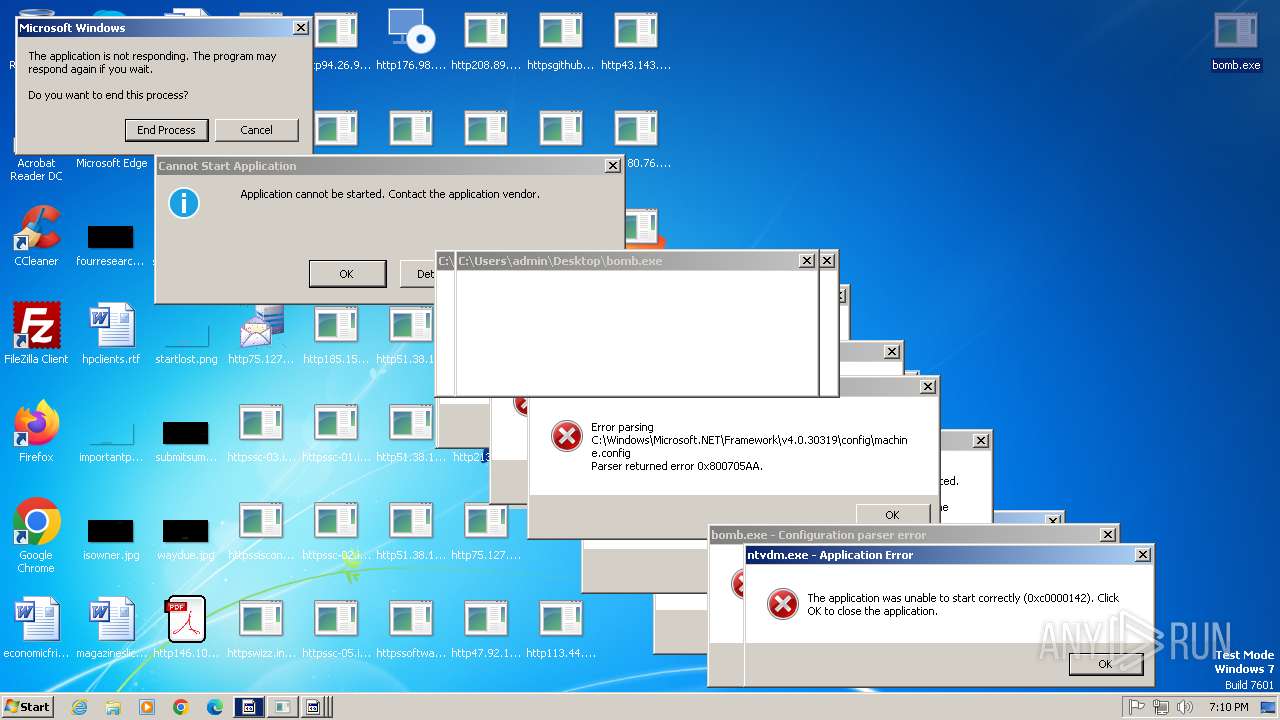
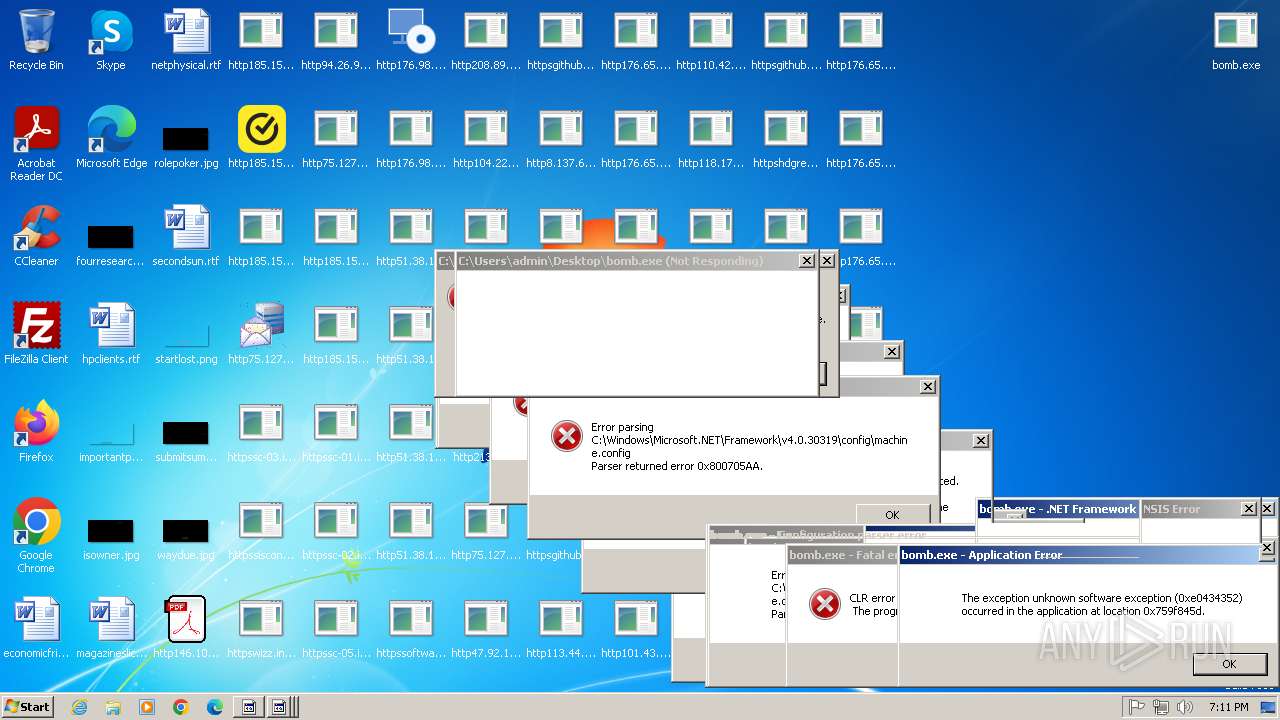
| File name: | bomb.exe |
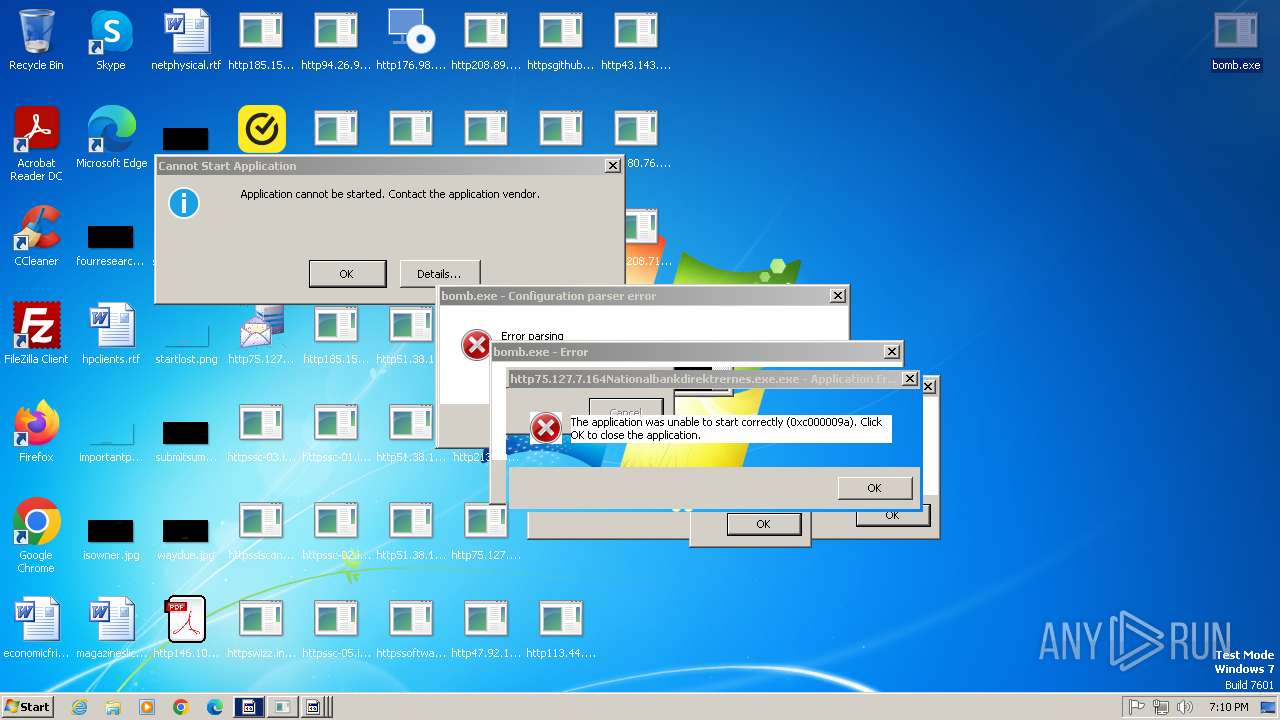
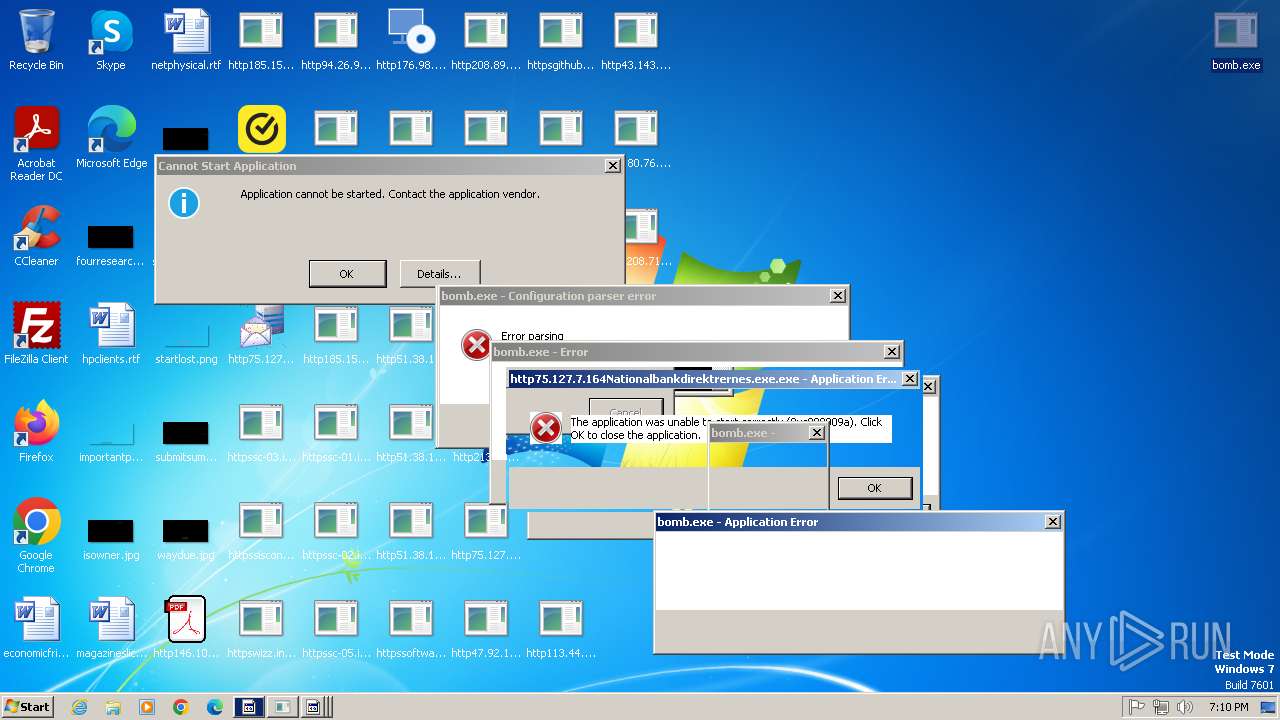
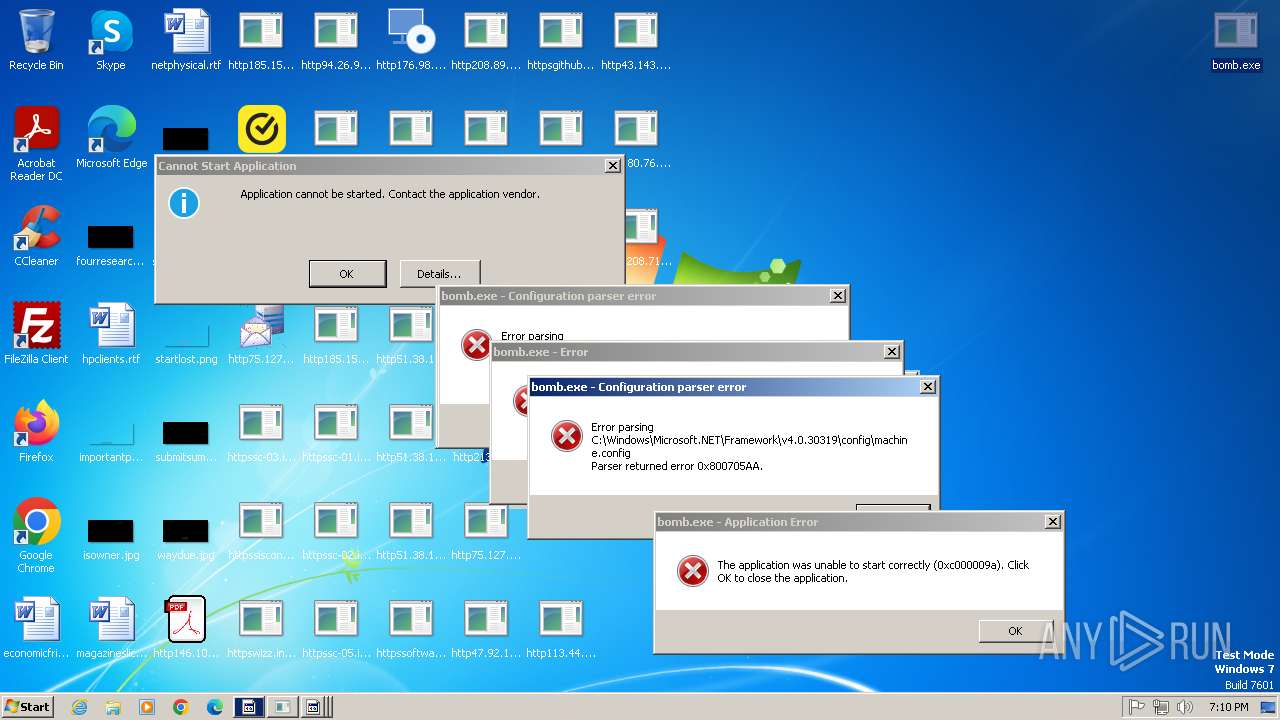
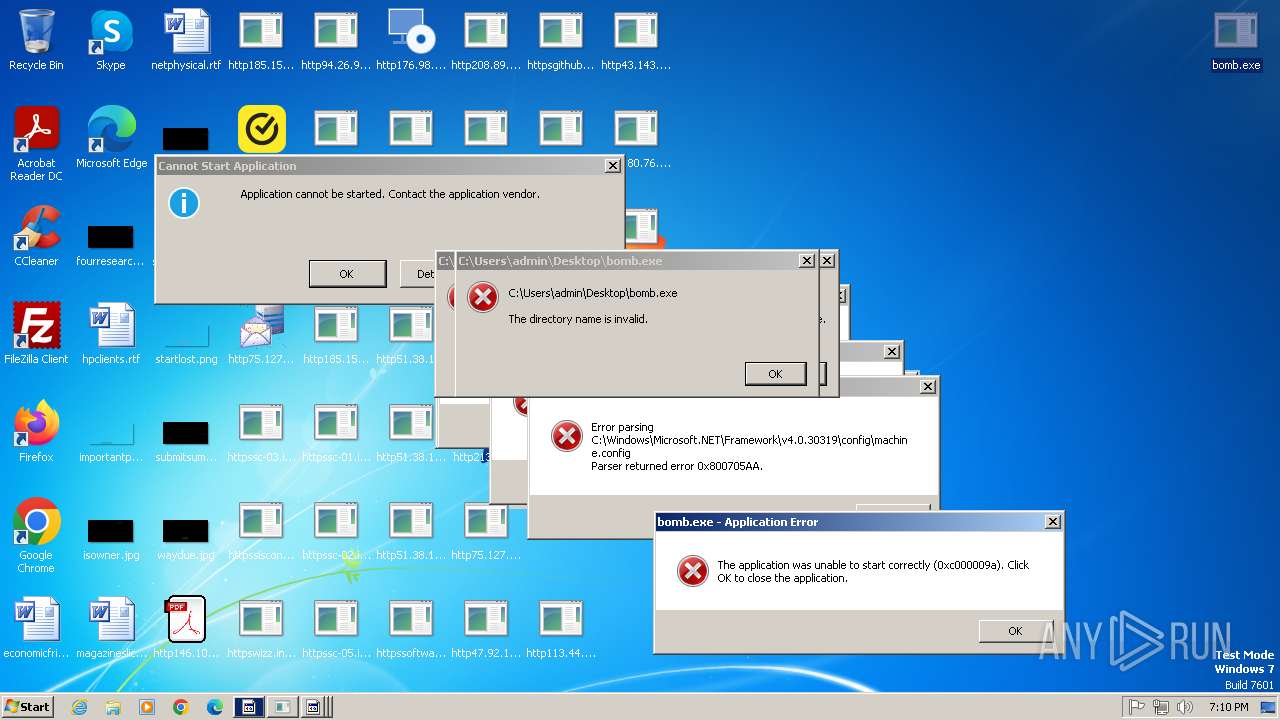
| Full analysis: | https://app.any.run/tasks/5e4e4b0c-7a9a-4036-ba00-8ebb35bc93f6 |
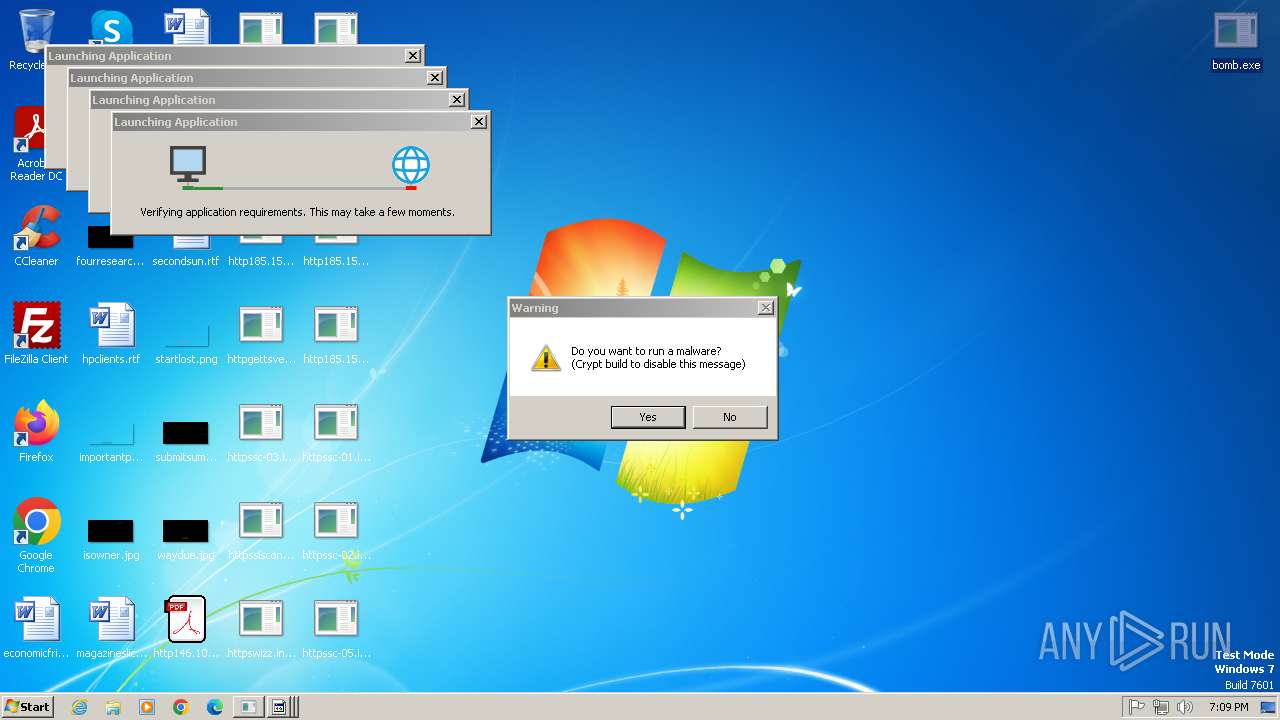
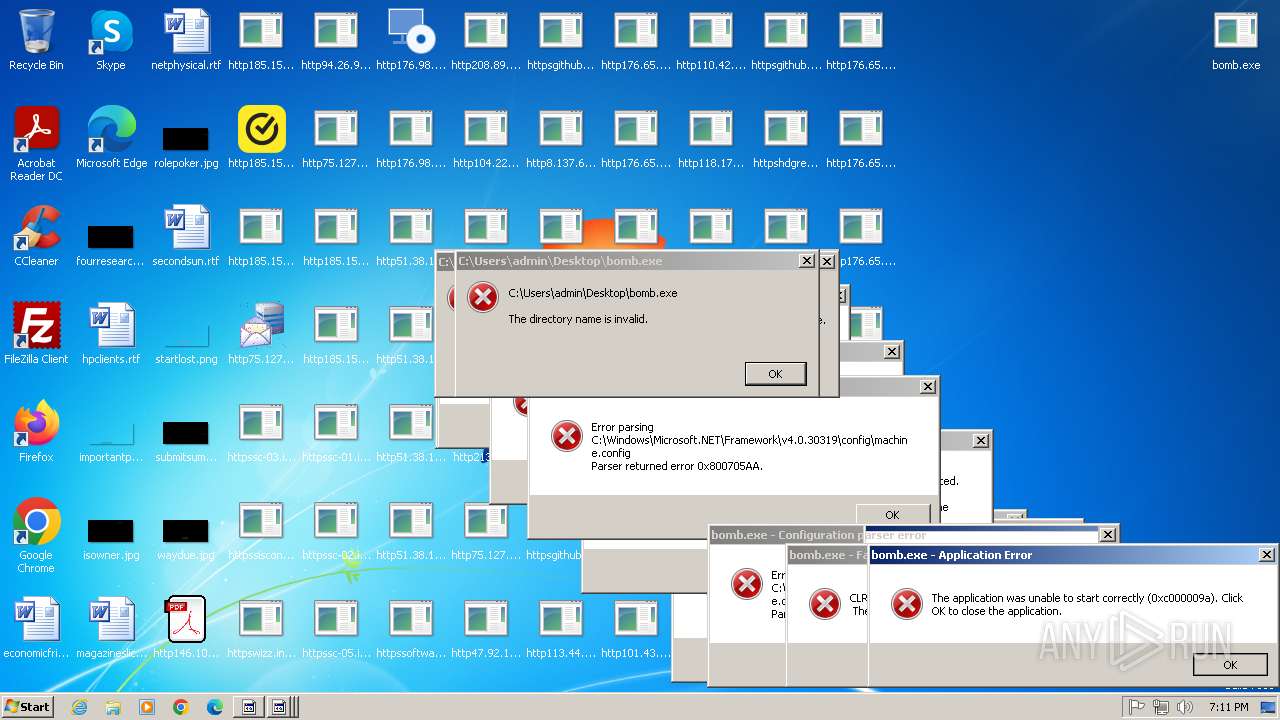
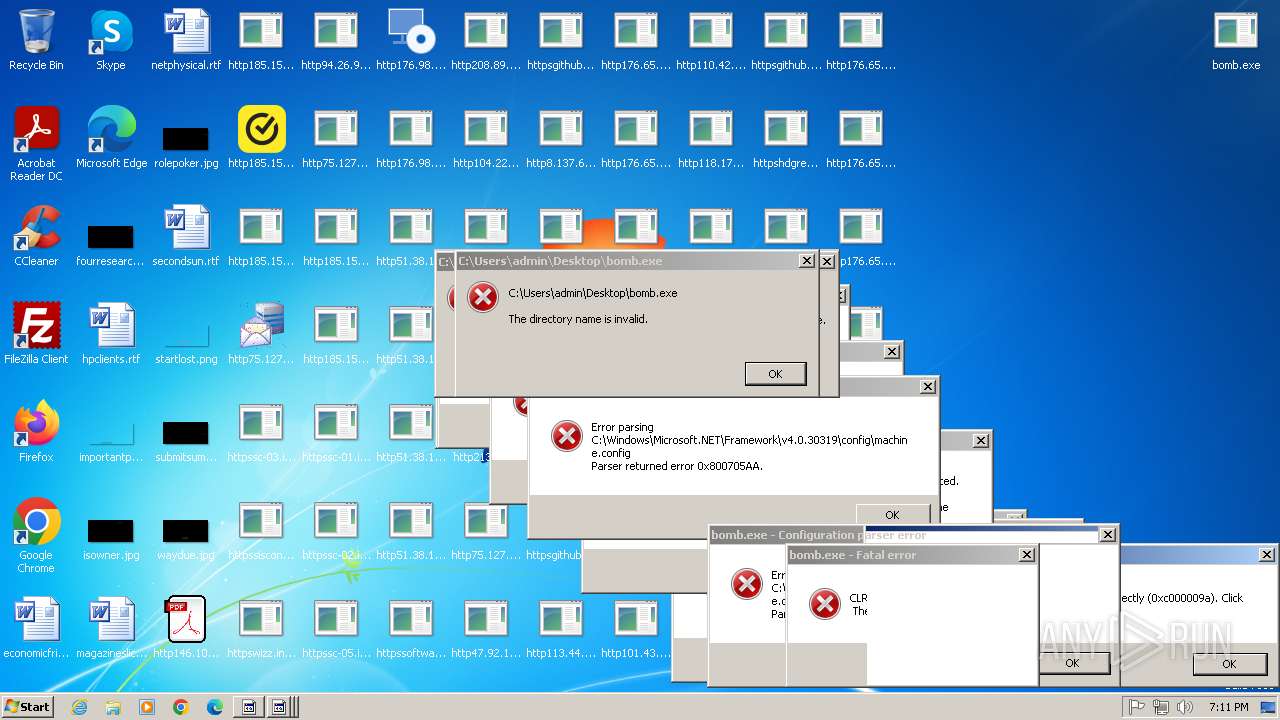
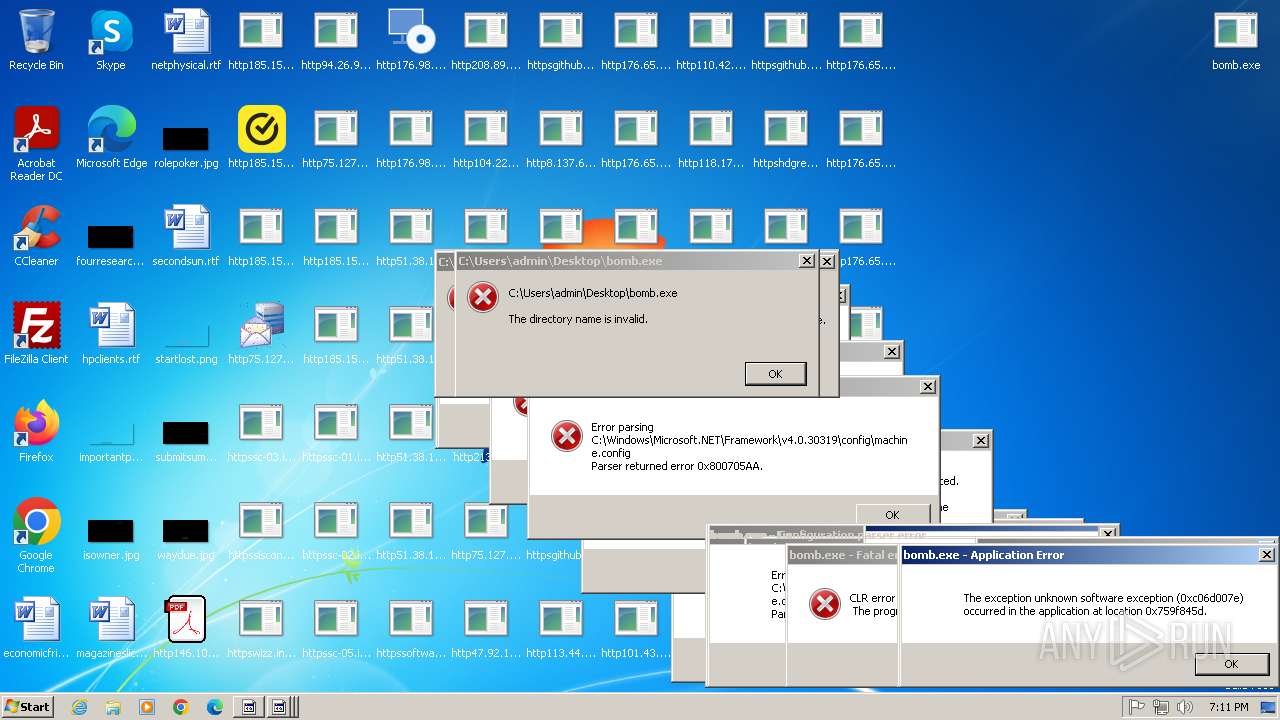
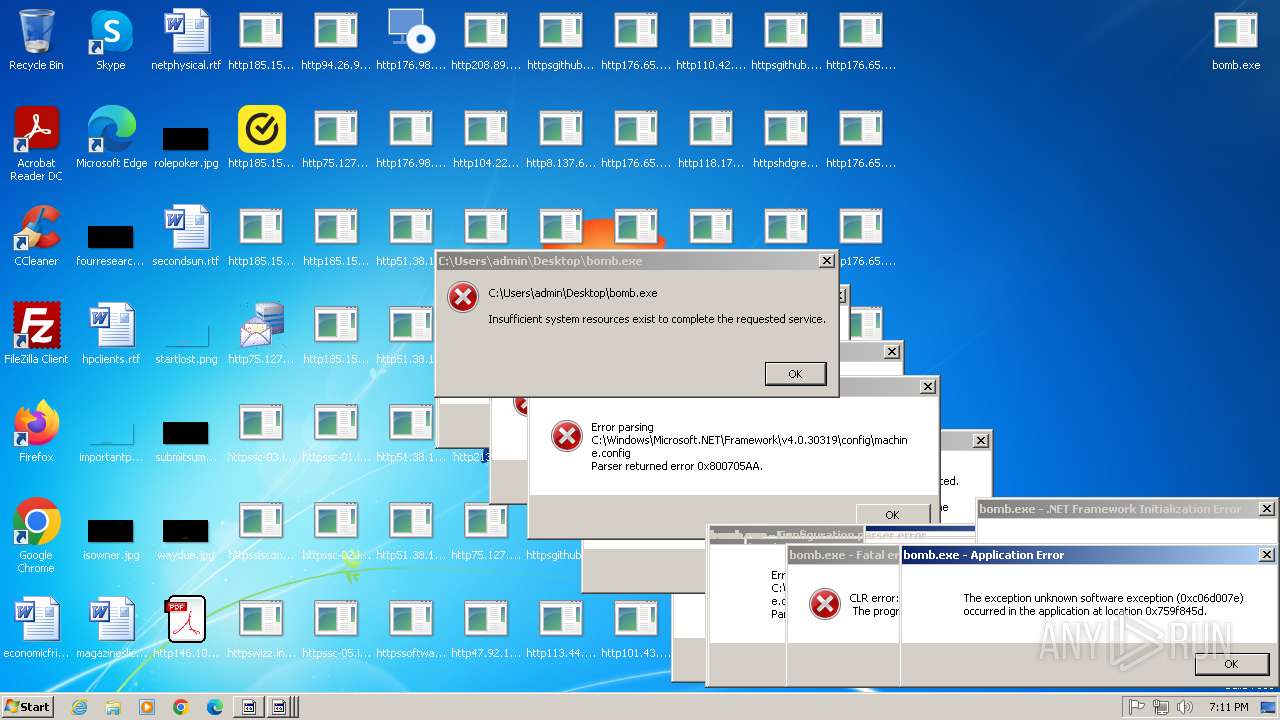
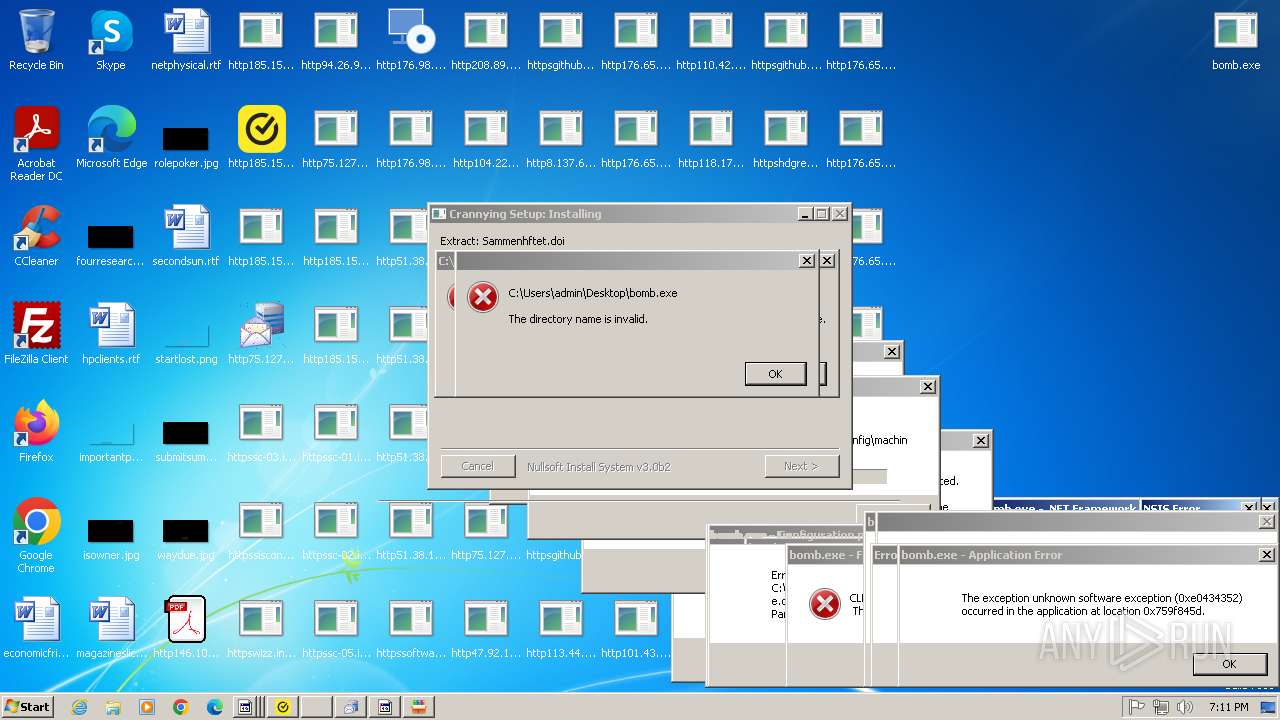
| Verdict: | Malicious activity |
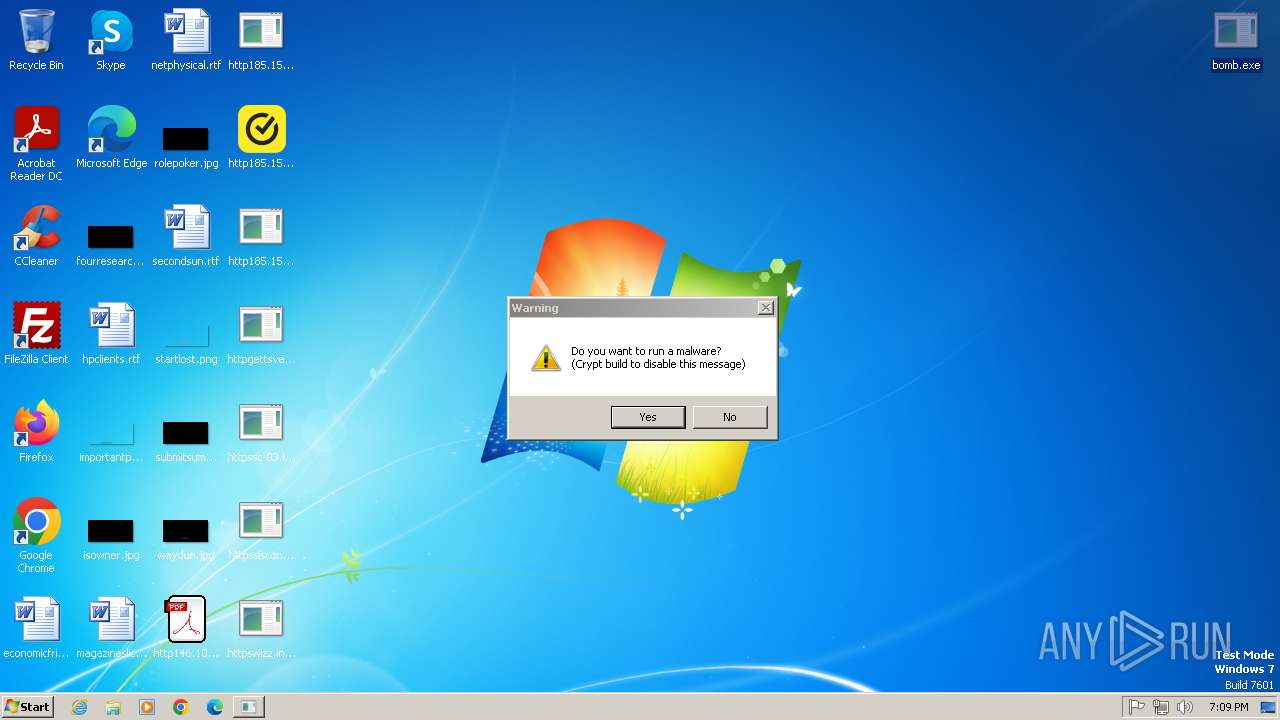
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 17, 2025, 18:09:20 |
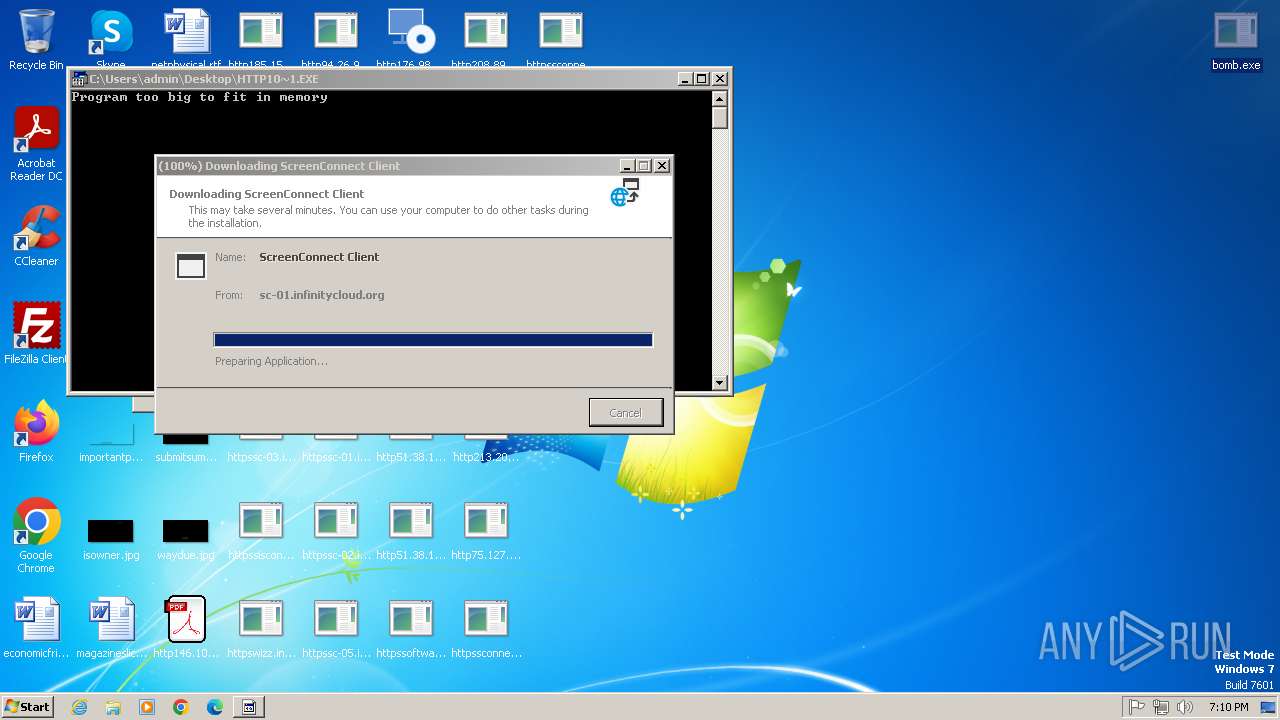
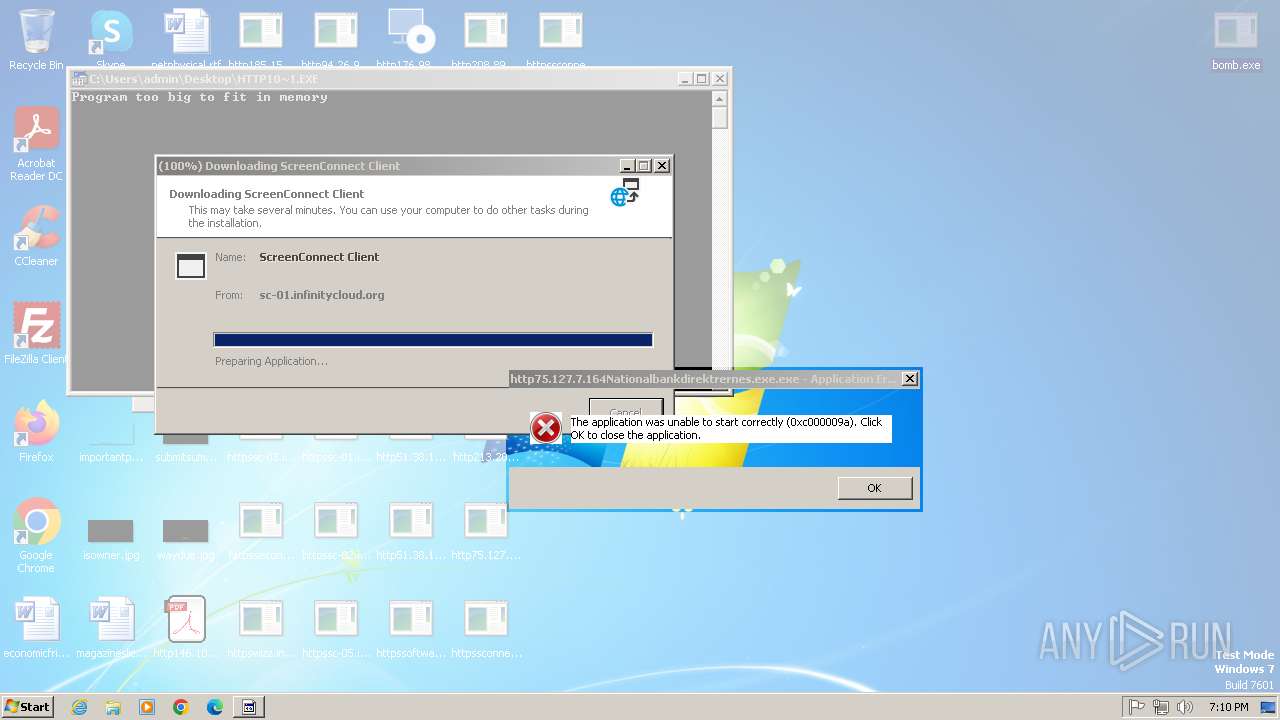
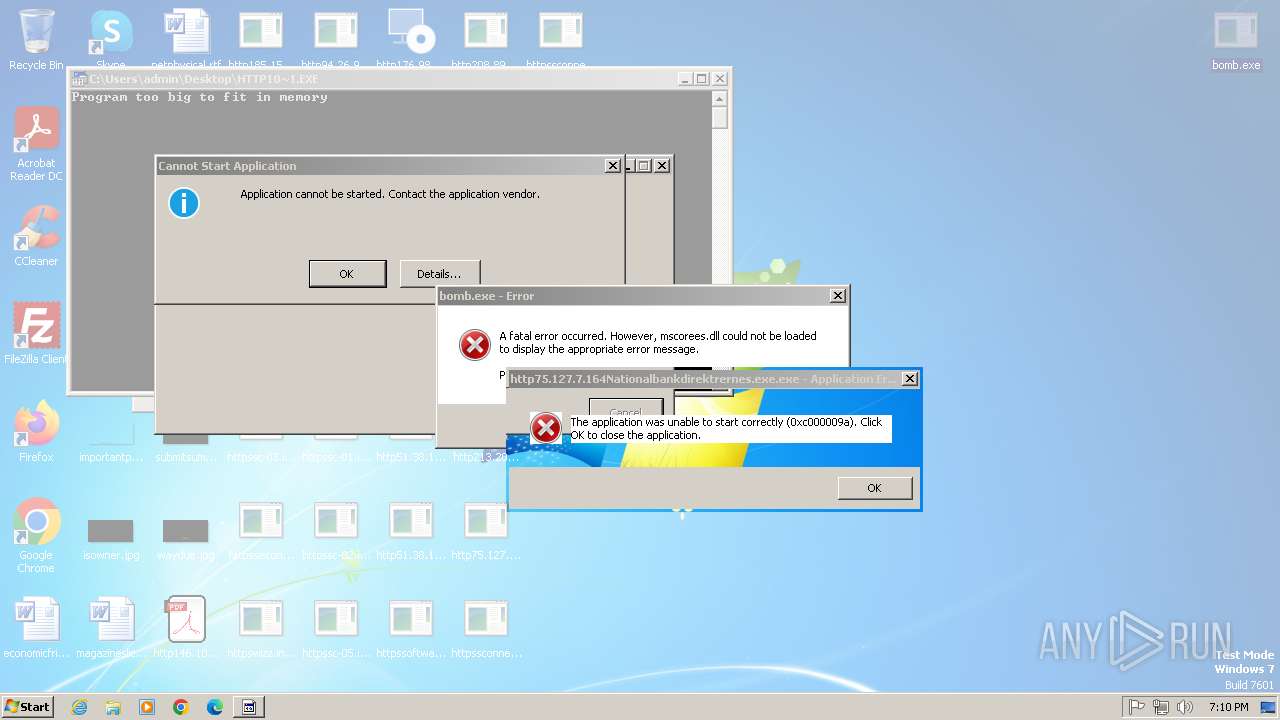
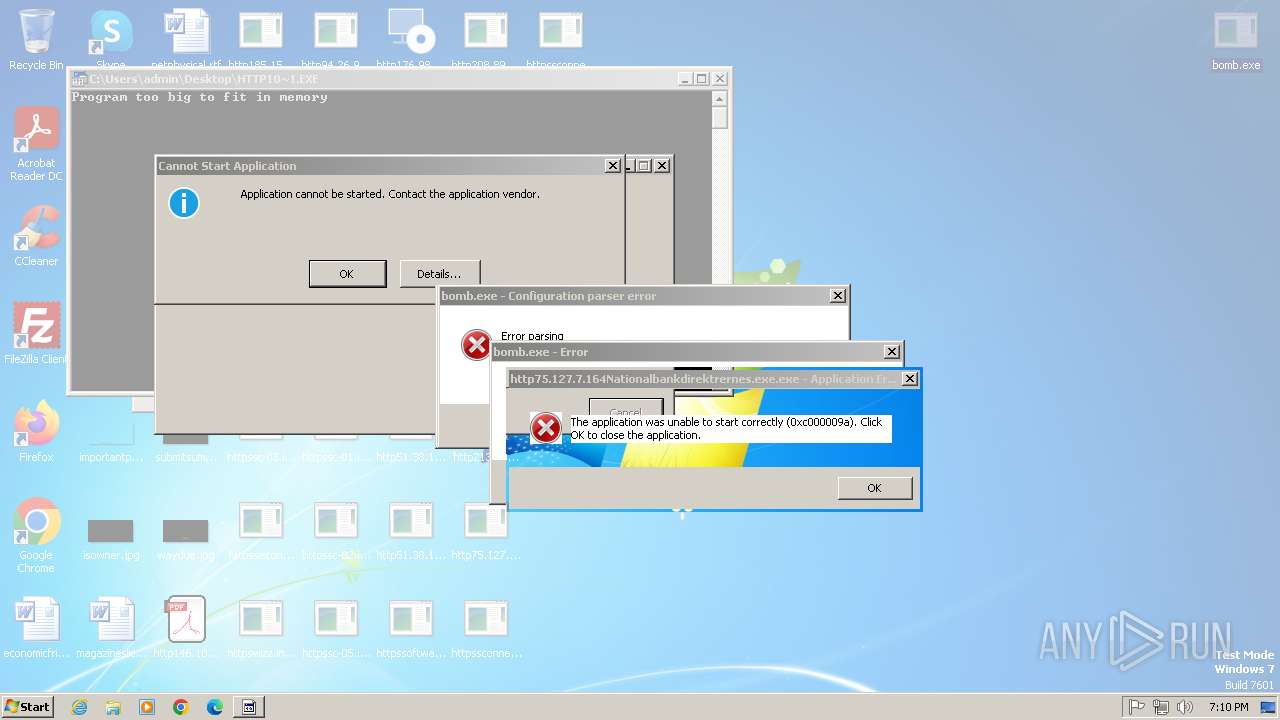
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 0E2AD53C884E25F969B3A575F4BB90BB |
| SHA1: | 81E774FE109DDC9185AD3FB68995A069CE9045E0 |
| SHA256: | 990D1FF1AB883A9BACBBB6ABCF975139D9AB359B74FFBA16F1FA7A66A30E935D |
| SSDEEP: | 192:OJa0tZMoQszhl4AKd+QHzdPbwPz1OLU87glpp/bI6J4YlTtoIw:OLJQjd+qzZ0OLU870NJDoI |
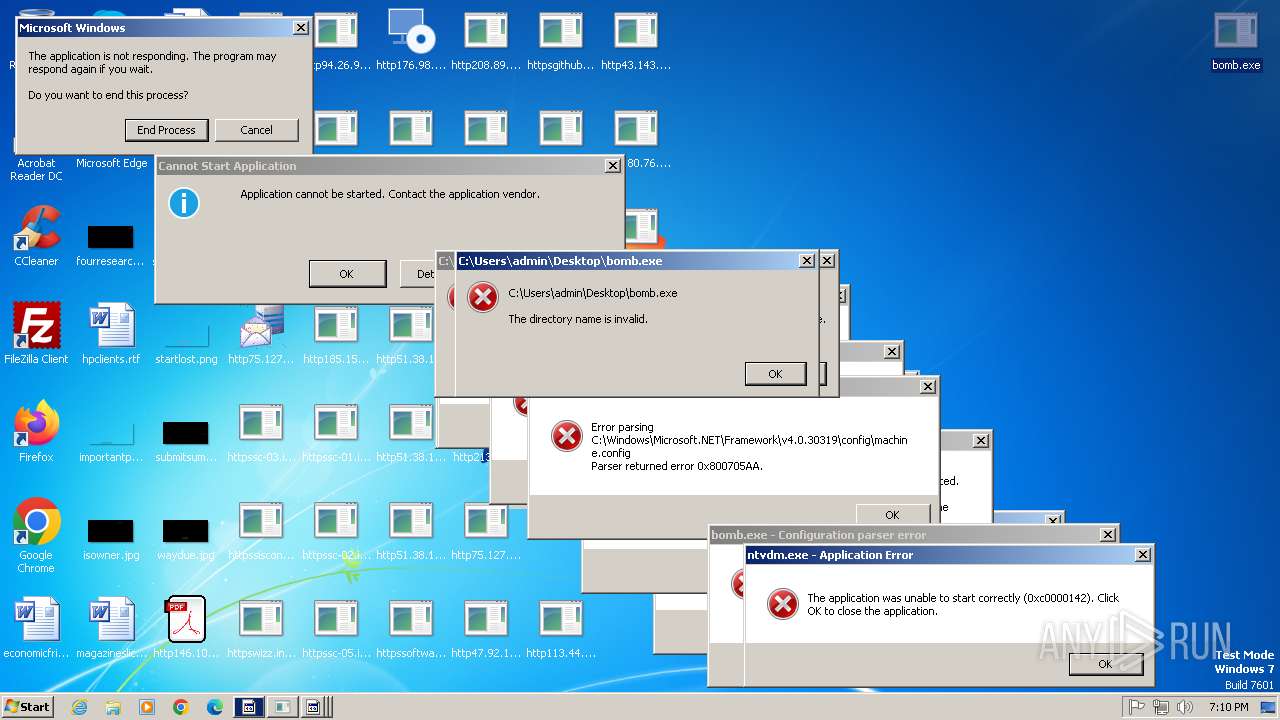
MALICIOUS
HAUSBOMBER has been detected (YARA)
- bomb.exe (PID: 1224)
- bomb.exe (PID: 2332)
- bomb.exe (PID: 268)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 148)
- bomb.exe (PID: 2728)
- bomb.exe (PID: 3820)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 3044)
- bomb.exe (PID: 3004)
Registers / Runs the DLL via REGSVR32.EXE
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
GHOSTSOCKS has been found (auto)
- bomb.exe (PID: 1224)
LUMMA mutex has been found
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
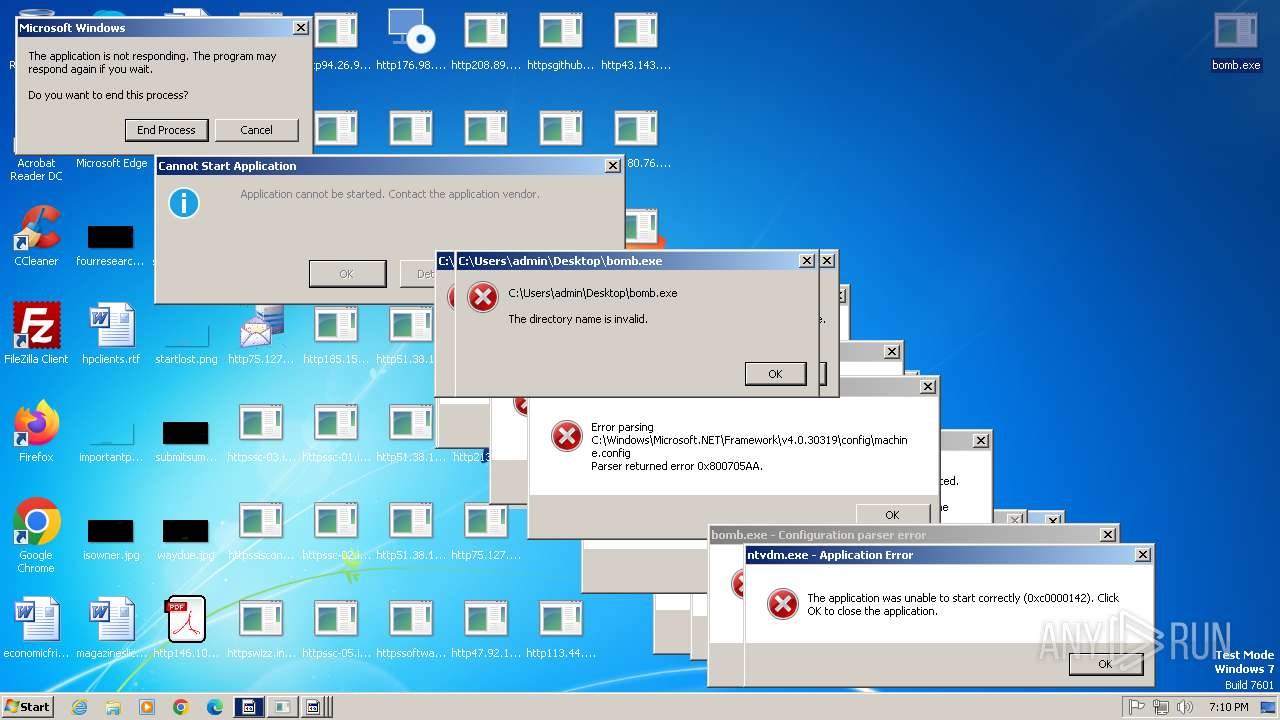
Actions looks like stealing of personal data
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
Steals credentials from Web Browsers
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
Antivirus name has been found in the command line (generic signature)
- sfc.exe (PID: 7364)
LUMMA has been detected (YARA)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
SUSPICIOUS
Reads the Internet Settings
- bomb.exe (PID: 1224)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- dfsvc.exe (PID: 3284)
- bomb.exe (PID: 268)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 3316)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 3004)
- bomb.exe (PID: 148)
- bomb.exe (PID: 2728)
- bomb.exe (PID: 3820)
Reads settings of System Certificates
- bomb.exe (PID: 1224)
- httpswizz.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3096)
- httpssisconnect-01.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2724)
- httpssc-02.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3088)
- httpssc-05.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2720)
- httpssc-01.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3176)
- dfsvc.exe (PID: 3284)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
- bomb.exe (PID: 268)
- bomb.exe (PID: 3684)
Process requests binary or script from the Internet
- bomb.exe (PID: 1224)
- bomb.exe (PID: 268)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 2952)
Potential Corporate Privacy Violation
- bomb.exe (PID: 1224)
- bomb.exe (PID: 268)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 3820)
- bomb.exe (PID: 3032)
- bomb.exe (PID: 148)
- bomb.exe (PID: 2728)
- bomb.exe (PID: 3004)
- bomb.exe (PID: 3316)
- bomb.exe (PID: 2996)
- bomb.exe (PID: 3120)
- bomb.exe (PID: 3364)
- bomb.exe (PID: 3904)
- bomb.exe (PID: 3036)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 3764)
- bomb.exe (PID: 4036)
- bomb.exe (PID: 1600)
- bomb.exe (PID: 3348)
- bomb.exe (PID: 3860)
- bomb.exe (PID: 4068)
- bomb.exe (PID: 2904)
- bomb.exe (PID: 3068)
- bomb.exe (PID: 2496)
- bomb.exe (PID: 2364)
- bomb.exe (PID: 3164)
- bomb.exe (PID: 2460)
- bomb.exe (PID: 3576)
- bomb.exe (PID: 1632)
- bomb.exe (PID: 3616)
- bomb.exe (PID: 2456)
- bomb.exe (PID: 1972)
- bomb.exe (PID: 960)
- bomb.exe (PID: 2804)
- bomb.exe (PID: 2480)
- bomb.exe (PID: 852)
- bomb.exe (PID: 3780)
- bomb.exe (PID: 1088)
- bomb.exe (PID: 2580)
- bomb.exe (PID: 3752)
- bomb.exe (PID: 4316)
- bomb.exe (PID: 4300)
- bomb.exe (PID: 3552)
- bomb.exe (PID: 4132)
- bomb.exe (PID: 4144)
- bomb.exe (PID: 4288)
- bomb.exe (PID: 2384)
- bomb.exe (PID: 4248)
- bomb.exe (PID: 4192)
- bomb.exe (PID: 4272)
- bomb.exe (PID: 4264)
- bomb.exe (PID: 4308)
- bomb.exe (PID: 4324)
Reads security settings of Internet Explorer
- bomb.exe (PID: 1224)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- dfsvc.exe (PID: 3284)
- bomb.exe (PID: 268)
Connects to the server without a host name
- bomb.exe (PID: 1224)
- bomb.exe (PID: 268)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 2952)
Executable content was dropped or overwritten
- bomb.exe (PID: 1224)
- http185.156.72.2files5795480469A2vn0Mb.exe.exe (PID: 3044)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- http185.156.72.2files5795480469A2vn0Mb.exe.exe (PID: 2532)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
- dfsvc.exe (PID: 3284)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 268)
- http185.156.72.2files5795480469A2vn0Mb.exe.exe (PID: 8144)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 8896)
Reads the Windows owner or organization settings
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
Process drops legitimate windows executable
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 268)
- bomb.exe (PID: 1224)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 8896)
- bomb.exe (PID: 3820)
Adds/modifies Windows certificates
- httpssc-03.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2388)
- dfsvc.exe (PID: 3284)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
- bomb.exe (PID: 268)
The process checks if it is being run in the virtual environment
- http185.156.72.2files6723359323FxefytI.exe.exe (PID: 2352)
Connects to unusual port
- bomb.exe (PID: 1224)
- bomb.exe (PID: 268)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
Reads Internet Explorer settings
- dfsvc.exe (PID: 3284)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 3284)
There is functionality for taking screenshot (YARA)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
INFO
Checks supported languages
- bomb.exe (PID: 1224)
- bomb.exe (PID: 268)
- http185.156.72.2files6723359323FxefytI.exe.exe (PID: 2352)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
- http146.103.7.34150TiWorker.exe.exe (PID: 3016)
- http185.156.72.2files5795480469A2vn0Mb.exe.exe (PID: 3044)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- http185.156.72.2files5795480469A2vn0Mb.exe.exe (PID: 2532)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
- httpswizz.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3096)
- bomb.exe (PID: 148)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 2728)
- httpssisconnect-01.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2724)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 3316)
- dfsvc.exe (PID: 2872)
- httpssc-02.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3088)
- httpssc-05.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2720)
- dfsvc.exe (PID: 3000)
- dfsvc.exe (PID: 3812)
- bomb.exe (PID: 3004)
- bomb.exe (PID: 3832)
- bomb.exe (PID: 3820)
- httpssc-03.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2388)
- dfsvc.exe (PID: 3284)
- dfsvc.exe (PID: 3352)
- bomb.exe (PID: 3032)
- bomb.exe (PID: 3364)
- bomb.exe (PID: 3348)
- bomb.exe (PID: 3036)
- bomb.exe (PID: 2996)
- bomb.exe (PID: 3068)
- bomb.exe (PID: 2496)
- bomb.exe (PID: 3120)
- bomb.exe (PID: 3904)
- bomb.exe (PID: 3448)
- bomb.exe (PID: 3860)
- bomb.exe (PID: 3576)
- bomb.exe (PID: 4068)
- bomb.exe (PID: 4036)
- httpssc-01.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3176)
- bomb.exe (PID: 3780)
- bomb.exe (PID: 3164)
- bomb.exe (PID: 2904)
- bomb.exe (PID: 3768)
- bomb.exe (PID: 3788)
- bomb.exe (PID: 3764)
- bomb.exe (PID: 1088)
- bomb.exe (PID: 1600)
- bomb.exe (PID: 1632)
- bomb.exe (PID: 1628)
- bomb.exe (PID: 2456)
- bomb.exe (PID: 1972)
- bomb.exe (PID: 852)
- bomb.exe (PID: 960)
- bomb.exe (PID: 2112)
- bomb.exe (PID: 3616)
- bomb.exe (PID: 2804)
- bomb.exe (PID: 2060)
- bomb.exe (PID: 2480)
- bomb.exe (PID: 2580)
- bomb.exe (PID: 2460)
- bomb.exe (PID: 1964)
- bomb.exe (PID: 2364)
- bomb.exe (PID: 2332)
- bomb.exe (PID: 2056)
- bomb.exe (PID: 2384)
- bomb.exe (PID: 1396)
- bomb.exe (PID: 3044)
- bomb.exe (PID: 4144)
- bomb.exe (PID: 3752)
- bomb.exe (PID: 4132)
- bomb.exe (PID: 4192)
- bomb.exe (PID: 4248)
- bomb.exe (PID: 4280)
- bomb.exe (PID: 4316)
- bomb.exe (PID: 4352)
- bomb.exe (PID: 4324)
- bomb.exe (PID: 4300)
- bomb.exe (PID: 4288)
- bomb.exe (PID: 4308)
- bomb.exe (PID: 4272)
- bomb.exe (PID: 4264)
- bomb.exe (PID: 4420)
- bomb.exe (PID: 4468)
- bomb.exe (PID: 4540)
- bomb.exe (PID: 4636)
- bomb.exe (PID: 4500)
- bomb.exe (PID: 4620)
- bomb.exe (PID: 4476)
- bomb.exe (PID: 4628)
- bomb.exe (PID: 4492)
- bomb.exe (PID: 4656)
- bomb.exe (PID: 4728)
- bomb.exe (PID: 4644)
- bomb.exe (PID: 4768)
- bomb.exe (PID: 4664)
- bomb.exe (PID: 4692)
- bomb.exe (PID: 4752)
- bomb.exe (PID: 4744)
- bomb.exe (PID: 4812)
- bomb.exe (PID: 4828)
- bomb.exe (PID: 4820)
- bomb.exe (PID: 4836)
- bomb.exe (PID: 4844)
- bomb.exe (PID: 3552)
- bomb.exe (PID: 4760)
- bomb.exe (PID: 5196)
- bomb.exe (PID: 5224)
- bomb.exe (PID: 5244)
- bomb.exe (PID: 5284)
- bomb.exe (PID: 5356)
- bomb.exe (PID: 5328)
- bomb.exe (PID: 5364)
- bomb.exe (PID: 5260)
- bomb.exe (PID: 5428)
- bomb.exe (PID: 5436)
- bomb.exe (PID: 5464)
- bomb.exe (PID: 5484)
- bomb.exe (PID: 5376)
- bomb.exe (PID: 5552)
- bomb.exe (PID: 5560)
- bomb.exe (PID: 5620)
- bomb.exe (PID: 5520)
- bomb.exe (PID: 5576)
- bomb.exe (PID: 5700)
- bomb.exe (PID: 5728)
- bomb.exe (PID: 5748)
- bomb.exe (PID: 5644)
- bomb.exe (PID: 5680)
- bomb.exe (PID: 5764)
- bomb.exe (PID: 5824)
- bomb.exe (PID: 5832)
- bomb.exe (PID: 5932)
- bomb.exe (PID: 5916)
- bomb.exe (PID: 5996)
- bomb.exe (PID: 5988)
- bomb.exe (PID: 5884)
- bomb.exe (PID: 5860)
- bomb.exe (PID: 6040)
- bomb.exe (PID: 6056)
- bomb.exe (PID: 6048)
- bomb.exe (PID: 6088)
- bomb.exe (PID: 6004)
- bomb.exe (PID: 4152)
- bomb.exe (PID: 2716)
- bomb.exe (PID: 4156)
- bomb.exe (PID: 2508)
- bomb.exe (PID: 6120)
- bomb.exe (PID: 3956)
- bomb.exe (PID: 3260)
- bomb.exe (PID: 3652)
- bomb.exe (PID: 3340)
- bomb.exe (PID: 4380)
- bomb.exe (PID: 2816)
- bomb.exe (PID: 5144)
- bomb.exe (PID: 4168)
- bomb.exe (PID: 2204)
- bomb.exe (PID: 1828)
- bomb.exe (PID: 4244)
- bomb.exe (PID: 6168)
- bomb.exe (PID: 6204)
- bomb.exe (PID: 4384)
- bomb.exe (PID: 4140)
- bomb.exe (PID: 6156)
- bomb.exe (PID: 6240)
- bomb.exe (PID: 6288)
- bomb.exe (PID: 6320)
- bomb.exe (PID: 6228)
- bomb.exe (PID: 6276)
- bomb.exe (PID: 6436)
- bomb.exe (PID: 6412)
- bomb.exe (PID: 6452)
- bomb.exe (PID: 6484)
- bomb.exe (PID: 6336)
- bomb.exe (PID: 6380)
- bomb.exe (PID: 6536)
- bomb.exe (PID: 6560)
- bomb.exe (PID: 6596)
- bomb.exe (PID: 6584)
- bomb.exe (PID: 6508)
- bomb.exe (PID: 6660)
- bomb.exe (PID: 6684)
- bomb.exe (PID: 6732)
- bomb.exe (PID: 6632)
- bomb.exe (PID: 6792)
- bomb.exe (PID: 6768)
- bomb.exe (PID: 6804)
- bomb.exe (PID: 6884)
- bomb.exe (PID: 6984)
- bomb.exe (PID: 6864)
- bomb.exe (PID: 7008)
- bomb.exe (PID: 7084)
- bomb.exe (PID: 7056)
- bomb.exe (PID: 7264)
- bomb.exe (PID: 7108)
- bomb.exe (PID: 7256)
- bomb.exe (PID: 6992)
- bomb.exe (PID: 6908)
Reads the machine GUID from the registry
- bomb.exe (PID: 1224)
- http185.156.72.2files6723359323FxefytI.exe.exe (PID: 2352)
- httpssc-03.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2388)
- httpswizz.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3096)
- httpssisconnect-01.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2724)
- httpssc-02.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3088)
- httpssc-05.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2720)
- httpssc-01.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3176)
- dfsvc.exe (PID: 3284)
- dfsvc.exe (PID: 3812)
- dfsvc.exe (PID: 3352)
- dfsvc.exe (PID: 3000)
- dfsvc.exe (PID: 2872)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
- bomb.exe (PID: 268)
- bomb.exe (PID: 2728)
- bomb.exe (PID: 148)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 3004)
- bomb.exe (PID: 3820)
- bomb.exe (PID: 3316)
- bomb.exe (PID: 3904)
- bomb.exe (PID: 3364)
- bomb.exe (PID: 3348)
- bomb.exe (PID: 3032)
- bomb.exe (PID: 3120)
- bomb.exe (PID: 3068)
- bomb.exe (PID: 2996)
- bomb.exe (PID: 3036)
Reads the computer name
- bomb.exe (PID: 1224)
- bomb.exe (PID: 268)
- http185.156.72.2files6723359323FxefytI.exe.exe (PID: 2352)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- httpssc-03.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2388)
- httpswizz.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3096)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
- httpssc-02.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3088)
- httpssisconnect-01.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2724)
- bomb.exe (PID: 3684)
- dfsvc.exe (PID: 2872)
- bomb.exe (PID: 2728)
- bomb.exe (PID: 148)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 3316)
- dfsvc.exe (PID: 3000)
- dfsvc.exe (PID: 3812)
- httpssc-05.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 2720)
- bomb.exe (PID: 3004)
- bomb.exe (PID: 3820)
- bomb.exe (PID: 3832)
- dfsvc.exe (PID: 3352)
- dfsvc.exe (PID: 3284)
- bomb.exe (PID: 3364)
- bomb.exe (PID: 3348)
- bomb.exe (PID: 3036)
- bomb.exe (PID: 3032)
- bomb.exe (PID: 2996)
- bomb.exe (PID: 2496)
- bomb.exe (PID: 3068)
- bomb.exe (PID: 3120)
- bomb.exe (PID: 3904)
- bomb.exe (PID: 3448)
- bomb.exe (PID: 3860)
- bomb.exe (PID: 3576)
- bomb.exe (PID: 4036)
- bomb.exe (PID: 4068)
- httpssc-01.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe (PID: 3176)
- bomb.exe (PID: 3164)
- bomb.exe (PID: 3780)
- bomb.exe (PID: 2904)
- bomb.exe (PID: 3788)
- bomb.exe (PID: 1600)
- bomb.exe (PID: 3768)
- bomb.exe (PID: 1628)
- bomb.exe (PID: 1632)
- bomb.exe (PID: 960)
- bomb.exe (PID: 852)
- bomb.exe (PID: 1972)
- bomb.exe (PID: 2456)
- bomb.exe (PID: 3616)
- bomb.exe (PID: 2112)
- bomb.exe (PID: 2804)
- bomb.exe (PID: 2060)
- bomb.exe (PID: 2480)
- bomb.exe (PID: 2364)
- bomb.exe (PID: 2580)
- bomb.exe (PID: 2460)
- bomb.exe (PID: 1964)
- bomb.exe (PID: 2332)
- bomb.exe (PID: 2384)
- bomb.exe (PID: 1396)
- bomb.exe (PID: 3044)
- bomb.exe (PID: 2056)
- bomb.exe (PID: 1088)
- bomb.exe (PID: 3764)
- bomb.exe (PID: 3552)
- bomb.exe (PID: 3752)
- bomb.exe (PID: 4132)
- bomb.exe (PID: 4144)
- bomb.exe (PID: 4192)
- bomb.exe (PID: 4280)
- bomb.exe (PID: 4316)
- bomb.exe (PID: 4248)
- bomb.exe (PID: 4300)
- bomb.exe (PID: 4324)
- bomb.exe (PID: 4288)
- bomb.exe (PID: 4352)
- bomb.exe (PID: 4308)
- bomb.exe (PID: 4272)
- bomb.exe (PID: 4264)
- bomb.exe (PID: 4540)
- bomb.exe (PID: 4476)
- bomb.exe (PID: 4468)
- bomb.exe (PID: 4420)
- bomb.exe (PID: 4500)
- bomb.exe (PID: 4636)
- bomb.exe (PID: 4628)
- bomb.exe (PID: 4620)
- bomb.exe (PID: 4492)
- bomb.exe (PID: 4656)
- bomb.exe (PID: 4644)
- bomb.exe (PID: 4728)
- bomb.exe (PID: 4692)
- bomb.exe (PID: 4768)
- bomb.exe (PID: 4752)
- bomb.exe (PID: 4744)
- bomb.exe (PID: 4664)
- bomb.exe (PID: 4760)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
- bomb.exe (PID: 4812)
- bomb.exe (PID: 4836)
- bomb.exe (PID: 4828)
- bomb.exe (PID: 5196)
- bomb.exe (PID: 5224)
- bomb.exe (PID: 5244)
- bomb.exe (PID: 4844)
- bomb.exe (PID: 4820)
- bomb.exe (PID: 5284)
- bomb.exe (PID: 5328)
- bomb.exe (PID: 5356)
- bomb.exe (PID: 5260)
- bomb.exe (PID: 5428)
- bomb.exe (PID: 5436)
- bomb.exe (PID: 5464)
- bomb.exe (PID: 5484)
- bomb.exe (PID: 5376)
- bomb.exe (PID: 5364)
- bomb.exe (PID: 5560)
- bomb.exe (PID: 5552)
- bomb.exe (PID: 5576)
- bomb.exe (PID: 5520)
- bomb.exe (PID: 5680)
- bomb.exe (PID: 5728)
- bomb.exe (PID: 5700)
- bomb.exe (PID: 5620)
- bomb.exe (PID: 5644)
- bomb.exe (PID: 5764)
- bomb.exe (PID: 5824)
- bomb.exe (PID: 5748)
- bomb.exe (PID: 5884)
- bomb.exe (PID: 5932)
- bomb.exe (PID: 5832)
- bomb.exe (PID: 5860)
- bomb.exe (PID: 5916)
- bomb.exe (PID: 5996)
- bomb.exe (PID: 6004)
- bomb.exe (PID: 6040)
- bomb.exe (PID: 5988)
- bomb.exe (PID: 4152)
- bomb.exe (PID: 6120)
- bomb.exe (PID: 6048)
- bomb.exe (PID: 6088)
- bomb.exe (PID: 6056)
- bomb.exe (PID: 4156)
- bomb.exe (PID: 3260)
- bomb.exe (PID: 3652)
- bomb.exe (PID: 3956)
- bomb.exe (PID: 4380)
- bomb.exe (PID: 2508)
- bomb.exe (PID: 2716)
- bomb.exe (PID: 1828)
- bomb.exe (PID: 2816)
- bomb.exe (PID: 4168)
- bomb.exe (PID: 2204)
- bomb.exe (PID: 3340)
- bomb.exe (PID: 5144)
- bomb.exe (PID: 4244)
- bomb.exe (PID: 4140)
- bomb.exe (PID: 6156)
- bomb.exe (PID: 4384)
- bomb.exe (PID: 6168)
- bomb.exe (PID: 6228)
- bomb.exe (PID: 6240)
- bomb.exe (PID: 6276)
- bomb.exe (PID: 6288)
- bomb.exe (PID: 6204)
- bomb.exe (PID: 6380)
- bomb.exe (PID: 6412)
- bomb.exe (PID: 6436)
- bomb.exe (PID: 6452)
- bomb.exe (PID: 6320)
- bomb.exe (PID: 6336)
- bomb.exe (PID: 6536)
- bomb.exe (PID: 6560)
- bomb.exe (PID: 6596)
- bomb.exe (PID: 6484)
- bomb.exe (PID: 6508)
- bomb.exe (PID: 6660)
- bomb.exe (PID: 6684)
- bomb.exe (PID: 6732)
- bomb.exe (PID: 6632)
- bomb.exe (PID: 6792)
- bomb.exe (PID: 6768)
- bomb.exe (PID: 6804)
- bomb.exe (PID: 6864)
- bomb.exe (PID: 6884)
- bomb.exe (PID: 6984)
- bomb.exe (PID: 7084)
- bomb.exe (PID: 7056)
- bomb.exe (PID: 6908)
- bomb.exe (PID: 6584)
Reads the software policy settings
- bomb.exe (PID: 1224)
- dfsvc.exe (PID: 3284)
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
- bomb.exe (PID: 268)
- bomb.exe (PID: 3684)
Reads Environment values
- bomb.exe (PID: 1224)
- dfsvc.exe (PID: 3284)
- bomb.exe (PID: 268)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 148)
- bomb.exe (PID: 2728)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 3316)
- bomb.exe (PID: 3004)
- bomb.exe (PID: 3820)
- bomb.exe (PID: 3120)
- bomb.exe (PID: 3364)
- bomb.exe (PID: 3032)
- bomb.exe (PID: 3904)
- bomb.exe (PID: 3036)
- bomb.exe (PID: 2996)
- bomb.exe (PID: 3068)
- bomb.exe (PID: 3348)
Disables trace logs
- bomb.exe (PID: 1224)
- dfsvc.exe (PID: 3284)
- bomb.exe (PID: 268)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 3316)
- bomb.exe (PID: 2728)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 148)
- bomb.exe (PID: 3820)
- bomb.exe (PID: 3004)
- bomb.exe (PID: 3032)
- bomb.exe (PID: 3120)
- bomb.exe (PID: 3364)
- bomb.exe (PID: 2996)
- bomb.exe (PID: 3904)
- bomb.exe (PID: 3036)
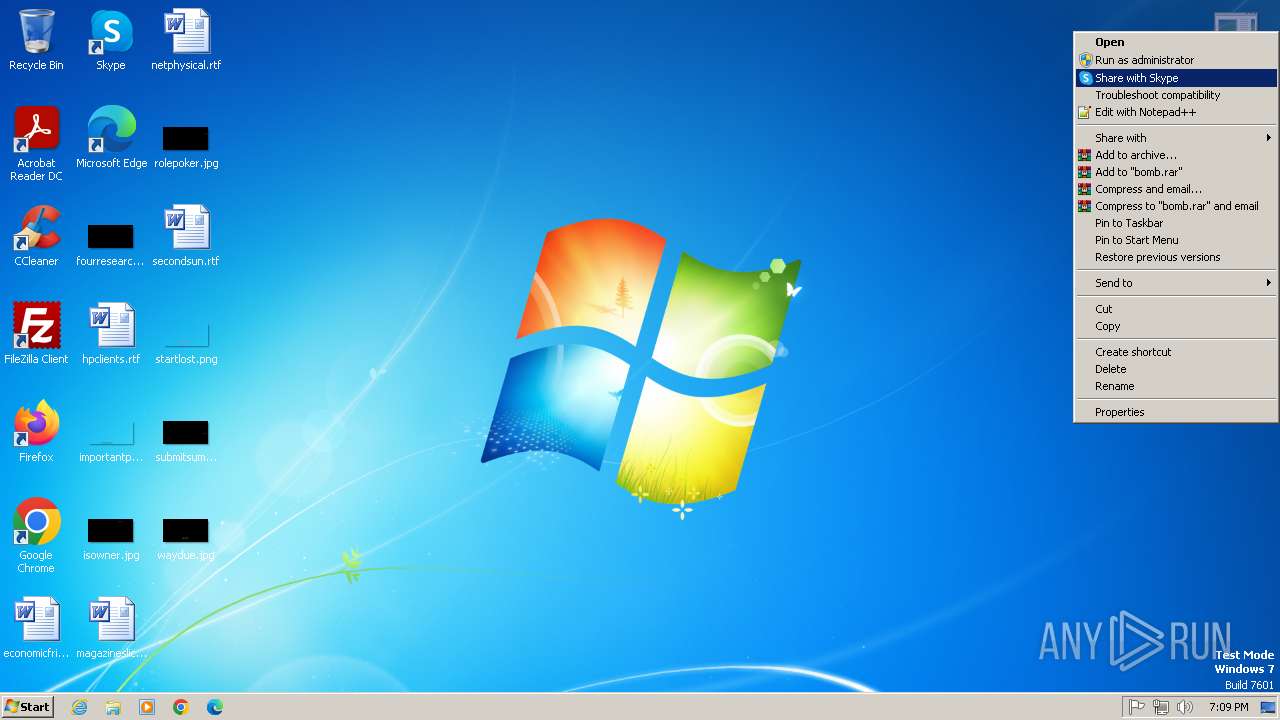
Manual execution by a user
- bomb.exe (PID: 268)
- bomb.exe (PID: 148)
- bomb.exe (PID: 2952)
- bomb.exe (PID: 2728)
- bomb.exe (PID: 3316)
- bomb.exe (PID: 3004)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 3820)
- bomb.exe (PID: 3832)
- bomb.exe (PID: 3348)
- bomb.exe (PID: 3032)
- bomb.exe (PID: 3036)
- bomb.exe (PID: 3068)
- bomb.exe (PID: 3364)
- bomb.exe (PID: 3120)
- bomb.exe (PID: 2996)
- bomb.exe (PID: 3904)
- bomb.exe (PID: 2496)
- bomb.exe (PID: 3860)
- bomb.exe (PID: 3448)
- bomb.exe (PID: 4036)
- bomb.exe (PID: 1088)
- bomb.exe (PID: 3576)
- bomb.exe (PID: 4068)
- bomb.exe (PID: 3164)
- bomb.exe (PID: 2904)
- bomb.exe (PID: 3780)
- bomb.exe (PID: 3788)
- bomb.exe (PID: 3768)
- bomb.exe (PID: 3764)
- bomb.exe (PID: 1600)
- bomb.exe (PID: 960)
- bomb.exe (PID: 1628)
- bomb.exe (PID: 2456)
- bomb.exe (PID: 2112)
- bomb.exe (PID: 852)
- bomb.exe (PID: 1972)
- bomb.exe (PID: 3616)
- bomb.exe (PID: 2460)
- bomb.exe (PID: 2060)
- bomb.exe (PID: 2804)
- bomb.exe (PID: 2480)
- bomb.exe (PID: 2580)
- bomb.exe (PID: 2364)
- bomb.exe (PID: 1964)
- bomb.exe (PID: 2332)
- bomb.exe (PID: 2384)
- bomb.exe (PID: 2056)
- bomb.exe (PID: 3044)
- bomb.exe (PID: 1396)
- bomb.exe (PID: 3552)
- bomb.exe (PID: 1632)
- bomb.exe (PID: 4144)
- bomb.exe (PID: 3752)
- bomb.exe (PID: 4132)
- bomb.exe (PID: 4192)
- bomb.exe (PID: 4272)
- bomb.exe (PID: 4248)
- bomb.exe (PID: 4264)
- bomb.exe (PID: 4288)
- bomb.exe (PID: 4280)
- bomb.exe (PID: 4300)
- bomb.exe (PID: 4324)
- bomb.exe (PID: 4316)
- bomb.exe (PID: 4308)
- bomb.exe (PID: 4420)
- bomb.exe (PID: 4352)
- bomb.exe (PID: 4468)
- bomb.exe (PID: 4476)
- bomb.exe (PID: 4492)
- bomb.exe (PID: 4500)
- bomb.exe (PID: 4540)
- bomb.exe (PID: 4620)
- bomb.exe (PID: 4636)
- bomb.exe (PID: 4628)
- bomb.exe (PID: 4644)
- bomb.exe (PID: 4656)
- bomb.exe (PID: 4692)
- bomb.exe (PID: 4664)
- bomb.exe (PID: 4728)
- bomb.exe (PID: 4744)
- bomb.exe (PID: 4752)
- bomb.exe (PID: 4760)
- bomb.exe (PID: 4768)
- bomb.exe (PID: 4820)
- bomb.exe (PID: 4828)
- bomb.exe (PID: 4812)
- bomb.exe (PID: 4836)
- bomb.exe (PID: 4844)
- bomb.exe (PID: 5196)
- bomb.exe (PID: 5224)
- bomb.exe (PID: 5244)
- bomb.exe (PID: 5260)
- bomb.exe (PID: 5328)
- bomb.exe (PID: 5364)
- bomb.exe (PID: 5356)
- bomb.exe (PID: 5376)
- bomb.exe (PID: 5284)
- bomb.exe (PID: 5464)
- bomb.exe (PID: 5484)
- bomb.exe (PID: 5520)
- bomb.exe (PID: 5428)
- bomb.exe (PID: 5436)
- bomb.exe (PID: 5576)
- bomb.exe (PID: 5644)
- bomb.exe (PID: 5560)
- bomb.exe (PID: 5552)
- bomb.exe (PID: 5620)
- bomb.exe (PID: 5700)
- bomb.exe (PID: 5748)
- bomb.exe (PID: 5680)
- bomb.exe (PID: 5728)
- bomb.exe (PID: 5824)
- bomb.exe (PID: 5832)
- bomb.exe (PID: 5860)
- bomb.exe (PID: 5764)
- bomb.exe (PID: 5996)
- bomb.exe (PID: 5988)
- bomb.exe (PID: 6004)
- bomb.exe (PID: 5884)
- bomb.exe (PID: 5916)
- bomb.exe (PID: 5932)
- bomb.exe (PID: 6048)
- bomb.exe (PID: 6056)
- bomb.exe (PID: 6040)
- bomb.exe (PID: 6088)
- bomb.exe (PID: 4156)
- bomb.exe (PID: 2716)
- bomb.exe (PID: 2508)
- bomb.exe (PID: 4380)
- bomb.exe (PID: 6120)
- bomb.exe (PID: 4152)
- bomb.exe (PID: 3260)
- bomb.exe (PID: 3956)
- bomb.exe (PID: 3340)
- bomb.exe (PID: 1828)
- bomb.exe (PID: 3652)
- bomb.exe (PID: 4384)
- bomb.exe (PID: 2816)
- bomb.exe (PID: 5144)
- bomb.exe (PID: 2204)
- bomb.exe (PID: 4168)
- bomb.exe (PID: 6156)
- bomb.exe (PID: 6168)
- bomb.exe (PID: 6204)
- bomb.exe (PID: 4244)
- bomb.exe (PID: 4140)
- bomb.exe (PID: 6276)
- bomb.exe (PID: 6288)
- bomb.exe (PID: 6336)
- bomb.exe (PID: 6228)
- bomb.exe (PID: 6240)
- bomb.exe (PID: 6320)
- bomb.exe (PID: 6436)
- bomb.exe (PID: 6452)
- bomb.exe (PID: 6484)
- bomb.exe (PID: 6380)
- bomb.exe (PID: 6412)
- bomb.exe (PID: 6536)
- bomb.exe (PID: 6560)
- bomb.exe (PID: 6584)
- bomb.exe (PID: 6632)
- bomb.exe (PID: 6508)
- bomb.exe (PID: 6596)
- bomb.exe (PID: 6684)
- bomb.exe (PID: 6660)
- bomb.exe (PID: 6732)
- bomb.exe (PID: 6804)
- bomb.exe (PID: 6768)
- bomb.exe (PID: 6792)
- bomb.exe (PID: 6864)
- bomb.exe (PID: 6884)
- bomb.exe (PID: 6908)
- bomb.exe (PID: 7056)
- bomb.exe (PID: 7084)
- bomb.exe (PID: 7108)
- bomb.exe (PID: 6992)
- bomb.exe (PID: 6984)
- bomb.exe (PID: 7008)
- bomb.exe (PID: 7100)
- bomb.exe (PID: 7128)
- bomb.exe (PID: 7256)
- bomb.exe (PID: 7264)
- bomb.exe (PID: 7240)
- bomb.exe (PID: 7632)
- bomb.exe (PID: 7656)
- bomb.exe (PID: 7608)
- bomb.exe (PID: 7648)
- bomb.exe (PID: 7640)
- bomb.exe (PID: 7688)
- bomb.exe (PID: 7380)
- bomb.exe (PID: 7600)
- bomb.exe (PID: 7616)
- bomb.exe (PID: 7924)
- bomb.exe (PID: 7868)
- bomb.exe (PID: 7892)
- bomb.exe (PID: 8004)
- bomb.exe (PID: 7724)
- bomb.exe (PID: 7752)
- bomb.exe (PID: 7768)
- bomb.exe (PID: 7992)
- bomb.exe (PID: 7716)
- bomb.exe (PID: 5348)
- bomb.exe (PID: 8216)
- bomb.exe (PID: 8012)
- bomb.exe (PID: 8060)
- bomb.exe (PID: 8052)
- bomb.exe (PID: 7664)
- bomb.exe (PID: 7848)
- bomb.exe (PID: 7808)
- bomb.exe (PID: 7744)
- bomb.exe (PID: 8044)
- bomb.exe (PID: 8076)
- bomb.exe (PID: 8020)
- bomb.exe (PID: 8428)
- bomb.exe (PID: 8436)
- bomb.exe (PID: 8420)
- bomb.exe (PID: 8324)
- bomb.exe (PID: 8412)
- bomb.exe (PID: 8536)
- bomb.exe (PID: 8576)
- bomb.exe (PID: 8688)
- bomb.exe (PID: 8660)
- bomb.exe (PID: 8668)
- bomb.exe (PID: 8500)
- bomb.exe (PID: 8520)
- bomb.exe (PID: 8508)
- bomb.exe (PID: 8876)
- bomb.exe (PID: 8828)
- bomb.exe (PID: 8816)
- bomb.exe (PID: 8932)
- bomb.exe (PID: 9144)
- bomb.exe (PID: 9024)
- bomb.exe (PID: 9036)
- bomb.exe (PID: 9120)
- bomb.exe (PID: 9136)
- bomb.exe (PID: 8712)
- bomb.exe (PID: 8736)
- bomb.exe (PID: 8728)
- bomb.exe (PID: 8772)
- bomb.exe (PID: 8792)
- bomb.exe (PID: 8884)
- bomb.exe (PID: 9176)
- bomb.exe (PID: 9160)
- bomb.exe (PID: 9168)
- bomb.exe (PID: 9200)
- bomb.exe (PID: 9236)
- bomb.exe (PID: 9248)
- bomb.exe (PID: 9372)
- bomb.exe (PID: 9264)
- bomb.exe (PID: 9256)
- bomb.exe (PID: 9352)
- bomb.exe (PID: 9380)
- bomb.exe (PID: 9388)
- bomb.exe (PID: 9360)
- bomb.exe (PID: 9224)
- bomb.exe (PID: 9776)
- bomb.exe (PID: 9724)
- bomb.exe (PID: 9716)
- bomb.exe (PID: 9684)
- bomb.exe (PID: 9800)
- bomb.exe (PID: 9828)
- bomb.exe (PID: 9852)
- bomb.exe (PID: 9456)
- bomb.exe (PID: 9500)
- bomb.exe (PID: 9508)
- bomb.exe (PID: 9516)
- bomb.exe (PID: 9532)
- bomb.exe (PID: 9652)
- bomb.exe (PID: 9644)
- bomb.exe (PID: 9664)
- bomb.exe (PID: 9976)
- bomb.exe (PID: 6728)
- bomb.exe (PID: 10148)
- bomb.exe (PID: 6744)
- bomb.exe (PID: 5892)
- bomb.exe (PID: 5980)
- bomb.exe (PID: 9876)
- bomb.exe (PID: 9924)
- bomb.exe (PID: 9940)
- bomb.exe (PID: 9948)
- bomb.exe (PID: 10088)
- bomb.exe (PID: 10116)
- bomb.exe (PID: 7760)
- bomb.exe (PID: 10328)
- bomb.exe (PID: 10556)
- bomb.exe (PID: 7596)
- bomb.exe (PID: 7440)
- bomb.exe (PID: 7304)
- bomb.exe (PID: 7228)
- bomb.exe (PID: 7452)
- bomb.exe (PID: 10860)
- bomb.exe (PID: 10964)
- bomb.exe (PID: 10948)
- bomb.exe (PID: 10908)
- bomb.exe (PID: 10956)
- bomb.exe (PID: 10932)
- bomb.exe (PID: 10940)
- bomb.exe (PID: 10916)
- bomb.exe (PID: 10768)
- bomb.exe (PID: 10828)
- bomb.exe (PID: 10924)
- bomb.exe (PID: 10900)
- bomb.exe (PID: 10992)
- bomb.exe (PID: 11040)
- bomb.exe (PID: 11024)
- bomb.exe (PID: 11092)
- bomb.exe (PID: 11068)
- bomb.exe (PID: 11056)
- bomb.exe (PID: 11076)
- bomb.exe (PID: 10984)
- bomb.exe (PID: 10976)
- bomb.exe (PID: 11016)
- bomb.exe (PID: 11032)
- bomb.exe (PID: 11008)
- bomb.exe (PID: 11000)
- bomb.exe (PID: 11048)
- bomb.exe (PID: 11084)
- bomb.exe (PID: 11284)
- bomb.exe (PID: 11232)
- bomb.exe (PID: 11248)
- bomb.exe (PID: 11276)
- bomb.exe (PID: 11224)
- bomb.exe (PID: 11292)
- bomb.exe (PID: 11240)
- bomb.exe (PID: 11216)
- bomb.exe (PID: 11108)
- bomb.exe (PID: 11100)
- bomb.exe (PID: 11120)
- bomb.exe (PID: 11260)
- bomb.exe (PID: 11268)
- bomb.exe (PID: 11400)
- bomb.exe (PID: 11460)
- bomb.exe (PID: 11500)
- bomb.exe (PID: 11484)
- bomb.exe (PID: 11492)
- bomb.exe (PID: 11476)
- bomb.exe (PID: 11564)
- bomb.exe (PID: 11572)
- bomb.exe (PID: 11552)
- bomb.exe (PID: 11384)
- bomb.exe (PID: 11392)
- bomb.exe (PID: 11612)
- bomb.exe (PID: 11688)
- bomb.exe (PID: 11672)
- bomb.exe (PID: 11696)
- bomb.exe (PID: 11724)
- bomb.exe (PID: 11716)
- bomb.exe (PID: 11740)
- bomb.exe (PID: 11752)
- bomb.exe (PID: 11592)
- bomb.exe (PID: 11600)
- bomb.exe (PID: 11620)
- bomb.exe (PID: 11680)
- bomb.exe (PID: 11904)
- bomb.exe (PID: 11896)
- bomb.exe (PID: 11920)
- bomb.exe (PID: 11912)
- bomb.exe (PID: 11928)
- bomb.exe (PID: 11944)
- bomb.exe (PID: 11936)
- bomb.exe (PID: 11952)
- bomb.exe (PID: 11960)
- bomb.exe (PID: 11968)
- bomb.exe (PID: 11760)
- bomb.exe (PID: 11784)
- bomb.exe (PID: 11808)
- bomb.exe (PID: 11800)
- bomb.exe (PID: 328)
- bomb.exe (PID: 12048)
- bomb.exe (PID: 12060)
- bomb.exe (PID: 12148)
- bomb.exe (PID: 12132)
- bomb.exe (PID: 12140)
- bomb.exe (PID: 3636)
- bomb.exe (PID: 9904)
- bomb.exe (PID: 12260)
- bomb.exe (PID: 12268)
- bomb.exe (PID: 11160)
- bomb.exe (PID: 11984)
- bomb.exe (PID: 11976)
- bomb.exe (PID: 12016)
- bomb.exe (PID: 12032)
- bomb.exe (PID: 12040)
- bomb.exe (PID: 12156)
- bomb.exe (PID: 12628)
- bomb.exe (PID: 12592)
- bomb.exe (PID: 12600)
- bomb.exe (PID: 12616)
- bomb.exe (PID: 12608)
- bomb.exe (PID: 12656)
- bomb.exe (PID: 12648)
- bomb.exe (PID: 12636)
- bomb.exe (PID: 12676)
- bomb.exe (PID: 12692)
- bomb.exe (PID: 12716)
- bomb.exe (PID: 12360)
- bomb.exe (PID: 12684)
- bomb.exe (PID: 13032)
- bomb.exe (PID: 12956)
- bomb.exe (PID: 12972)
- bomb.exe (PID: 12964)
- bomb.exe (PID: 13024)
- bomb.exe (PID: 12732)
- bomb.exe (PID: 12724)
- bomb.exe (PID: 13140)
- bomb.exe (PID: 13220)
- bomb.exe (PID: 13548)
- bomb.exe (PID: 13516)
- bomb.exe (PID: 13524)
- bomb.exe (PID: 13532)
- bomb.exe (PID: 13564)
- bomb.exe (PID: 13572)
- bomb.exe (PID: 13104)
- bomb.exe (PID: 13116)
- bomb.exe (PID: 13124)
- bomb.exe (PID: 13132)
- bomb.exe (PID: 13148)
- bomb.exe (PID: 13228)
- bomb.exe (PID: 13596)
- bomb.exe (PID: 13612)
- bomb.exe (PID: 13652)
- bomb.exe (PID: 13628)
- bomb.exe (PID: 13660)
- bomb.exe (PID: 13644)
- bomb.exe (PID: 13704)
- bomb.exe (PID: 13696)
- bomb.exe (PID: 13712)
- bomb.exe (PID: 13540)
- bomb.exe (PID: 13556)
- bomb.exe (PID: 13580)
- bomb.exe (PID: 13588)
- bomb.exe (PID: 13636)
- bomb.exe (PID: 13876)
- bomb.exe (PID: 13884)
- bomb.exe (PID: 13720)
- bomb.exe (PID: 13736)
- bomb.exe (PID: 13728)
- bomb.exe (PID: 13752)
- bomb.exe (PID: 13796)
- bomb.exe (PID: 13812)
- bomb.exe (PID: 13972)
- bomb.exe (PID: 13980)
- bomb.exe (PID: 13988)
- bomb.exe (PID: 14036)
- bomb.exe (PID: 14012)
- bomb.exe (PID: 14232)
- bomb.exe (PID: 14208)
- bomb.exe (PID: 14240)
- bomb.exe (PID: 13924)
- bomb.exe (PID: 13940)
- bomb.exe (PID: 13932)
- bomb.exe (PID: 13952)
- bomb.exe (PID: 13996)
- bomb.exe (PID: 14004)
- bomb.exe (PID: 14476)
- bomb.exe (PID: 12168)
- bomb.exe (PID: 14408)
- bomb.exe (PID: 14420)
- bomb.exe (PID: 14428)
- bomb.exe (PID: 14460)
- bomb.exe (PID: 14556)
- bomb.exe (PID: 14496)
- bomb.exe (PID: 14504)
- bomb.exe (PID: 14224)
- bomb.exe (PID: 14268)
- bomb.exe (PID: 14280)
- bomb.exe (PID: 14288)
- bomb.exe (PID: 11196)
- bomb.exe (PID: 12072)
- bomb.exe (PID: 14888)
- bomb.exe (PID: 14880)
- bomb.exe (PID: 14940)
- bomb.exe (PID: 14916)
- bomb.exe (PID: 14924)
- bomb.exe (PID: 14932)
- bomb.exe (PID: 15304)
- bomb.exe (PID: 14996)
- bomb.exe (PID: 15328)
- bomb.exe (PID: 14572)
- bomb.exe (PID: 14668)
- bomb.exe (PID: 14768)
- bomb.exe (PID: 14760)
- bomb.exe (PID: 14904)
- bomb.exe (PID: 14984)
- bomb.exe (PID: 15360)
- bomb.exe (PID: 15464)
- bomb.exe (PID: 15520)
- bomb.exe (PID: 15564)
- bomb.exe (PID: 15544)
- bomb.exe (PID: 15616)
- bomb.exe (PID: 15584)
- bomb.exe (PID: 15592)
- bomb.exe (PID: 15608)
- bomb.exe (PID: 15312)
- bomb.exe (PID: 15320)
- bomb.exe (PID: 15352)
- bomb.exe (PID: 15368)
- bomb.exe (PID: 15408)
- bomb.exe (PID: 15552)
- bomb.exe (PID: 15628)
- bomb.exe (PID: 15744)
- bomb.exe (PID: 16044)
- bomb.exe (PID: 16052)
- bomb.exe (PID: 16328)
- bomb.exe (PID: 16244)
- bomb.exe (PID: 16336)
- bomb.exe (PID: 16348)
- bomb.exe (PID: 16356)
- bomb.exe (PID: 16364)
- bomb.exe (PID: 5204)
- bomb.exe (PID: 16372)
- bomb.exe (PID: 16836)
- bomb.exe (PID: 16844)
- bomb.exe (PID: 16860)
- bomb.exe (PID: 16876)
- bomb.exe (PID: 16884)
- bomb.exe (PID: 5232)
- bomb.exe (PID: 8184)
- bomb.exe (PID: 5192)
- bomb.exe (PID: 9892)
- bomb.exe (PID: 3160)
- bomb.exe (PID: 16392)
- bomb.exe (PID: 16680)
- bomb.exe (PID: 16688)
- bomb.exe (PID: 16824)
- bomb.exe (PID: 16852)
- bomb.exe (PID: 16908)
- bomb.exe (PID: 16900)
- bomb.exe (PID: 16948)
- bomb.exe (PID: 16972)
- bomb.exe (PID: 16956)
- bomb.exe (PID: 16964)
- bomb.exe (PID: 17008)
- bomb.exe (PID: 16980)
- bomb.exe (PID: 16988)
- bomb.exe (PID: 17016)
- bomb.exe (PID: 16892)
- bomb.exe (PID: 16932)
- bomb.exe (PID: 16940)
- bomb.exe (PID: 16916)
- bomb.exe (PID: 16924)
- bomb.exe (PID: 17220)
- bomb.exe (PID: 17208)
- bomb.exe (PID: 17148)
- bomb.exe (PID: 17200)
- bomb.exe (PID: 17232)
- bomb.exe (PID: 17364)
- bomb.exe (PID: 17372)
- bomb.exe (PID: 17380)
- bomb.exe (PID: 17388)
- bomb.exe (PID: 17000)
- bomb.exe (PID: 17028)
- bomb.exe (PID: 17036)
- bomb.exe (PID: 17076)
- bomb.exe (PID: 17096)
- bomb.exe (PID: 17124)
- bomb.exe (PID: 17356)
- bomb.exe (PID: 17456)
- bomb.exe (PID: 17444)
- bomb.exe (PID: 17488)
- bomb.exe (PID: 17480)
- bomb.exe (PID: 17464)
- bomb.exe (PID: 17472)
- bomb.exe (PID: 17508)
- bomb.exe (PID: 17428)
- bomb.exe (PID: 17404)
- bomb.exe (PID: 17436)
- bomb.exe (PID: 17420)
- bomb.exe (PID: 17412)
- bomb.exe (PID: 17396)
The sample compiled with english language support
- bomb.exe (PID: 1224)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
- bomb.exe (PID: 268)
- bomb.exe (PID: 3684)
- bomb.exe (PID: 2952)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 8896)
- bomb.exe (PID: 3820)
Create files in a temporary directory
- http146.103.7.34150TiWorker.exe.exe (PID: 3016)
- http185.156.72.2files5795480469A2vn0Mb.exe.exe (PID: 3044)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2960)
- http185.156.72.2files5795480469A2vn0Mb.exe.exe (PID: 2532)
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
- dfsvc.exe (PID: 3284)
Reads mouse settings
- http146.103.7.34150TiWorker.exe.exe (PID: 3016)
Creates files or folders in the user directory
- http185.156.72.2files5795480469A2vn0Mb.exe.tmp (PID: 2732)
- dfsvc.exe (PID: 3284)
Checks proxy server information
- dfsvc.exe (PID: 3284)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 3284)
Attempting to use instant messaging service
- http185.156.72.2files5712371530E759x7N.exe.exe (PID: 2024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(2024) http185.156.72.2files5712371530E759x7N.exe.exe
C2 (11)onehunqpom.life/zpxd
featurlyin.top/pdal
overcovtcg.top/juhd
blackswmxc.top/bgry
laminaflbx.shop/twoq
racxilb.digital/ozi
posseswsnc.top/akds
https://t.me/kz_prokla1
chainsimbb.run/qgbb
jackthyfuc.run/xpas
narrathfpt.top/tekq
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2057:01:07 19:44:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 9216 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x43be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | bomb.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | bomb.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
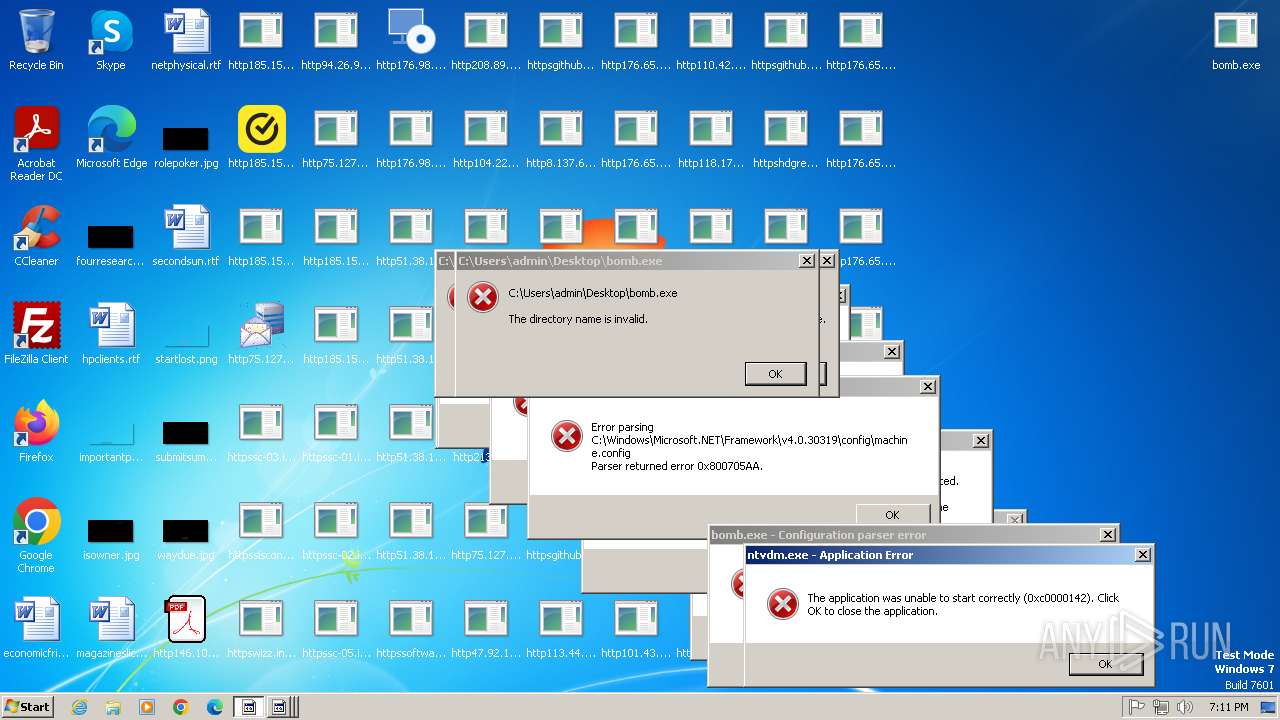
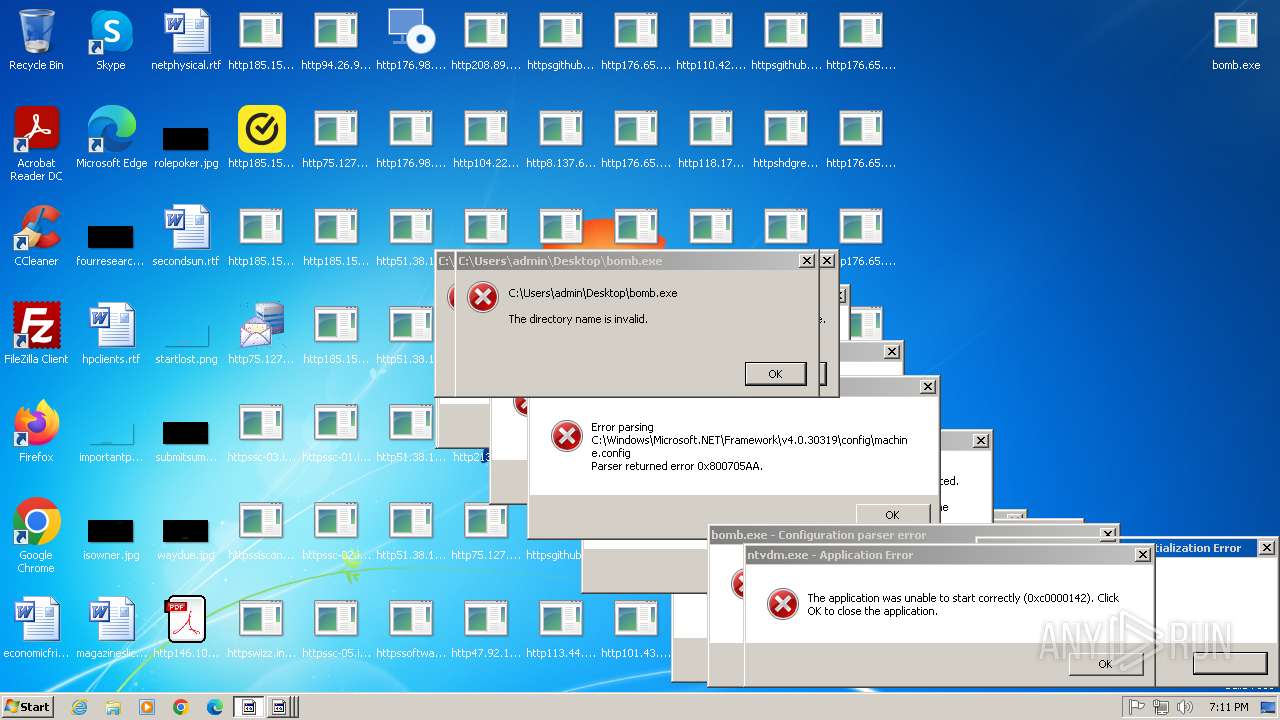
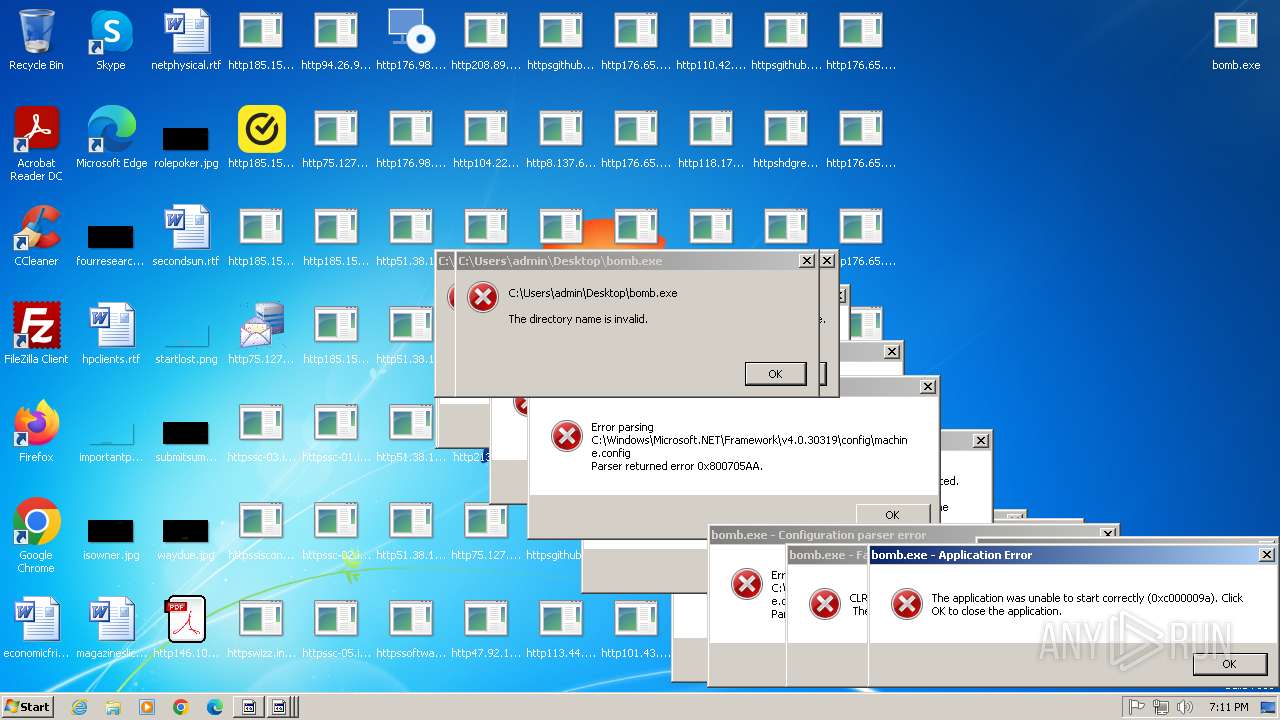
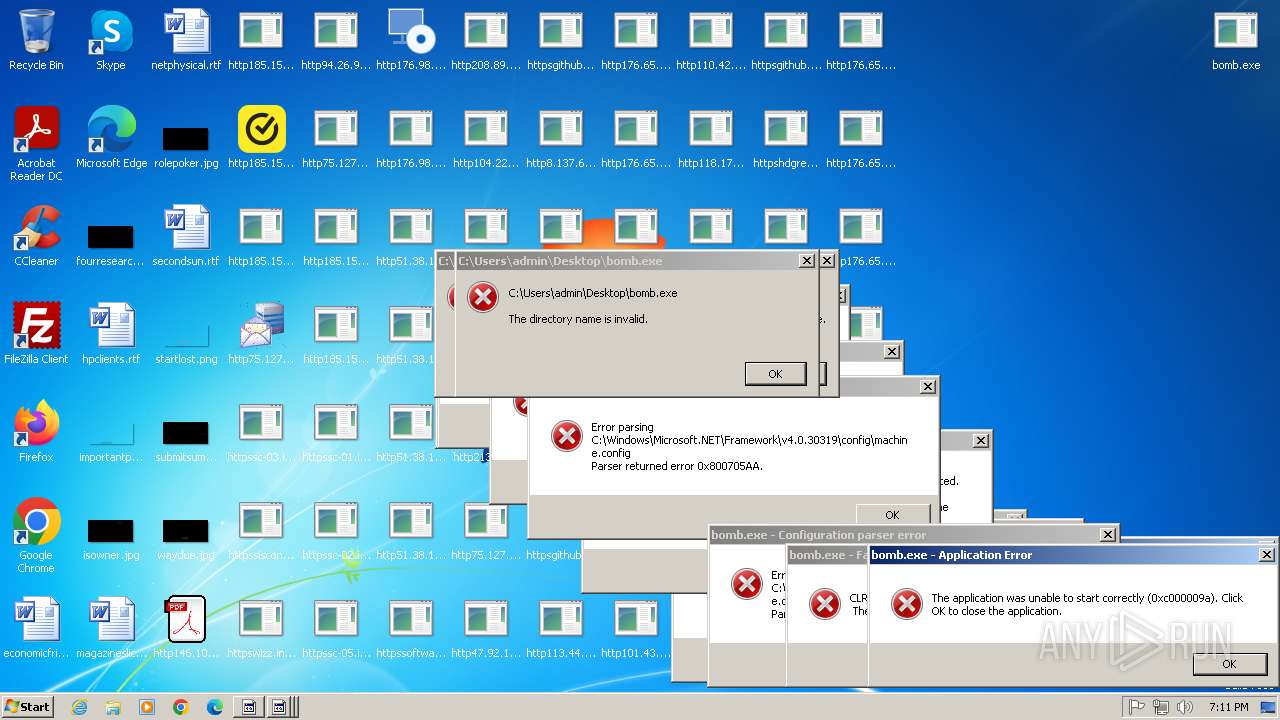
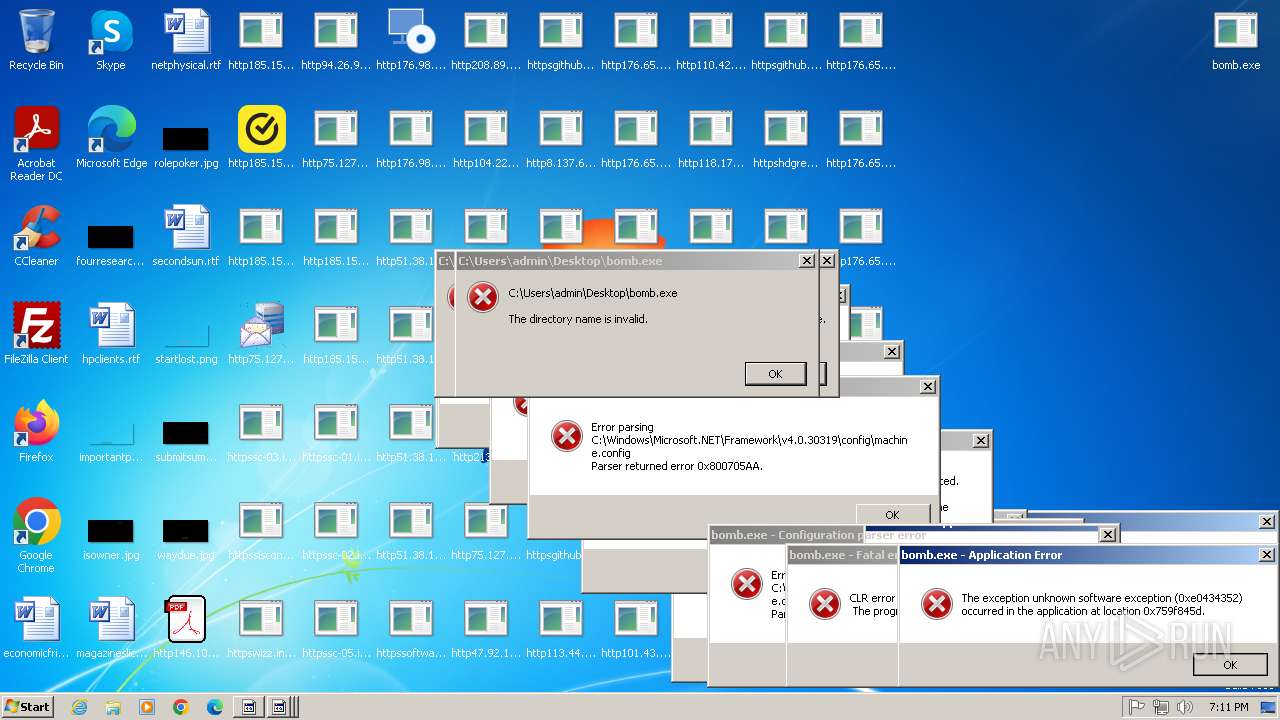
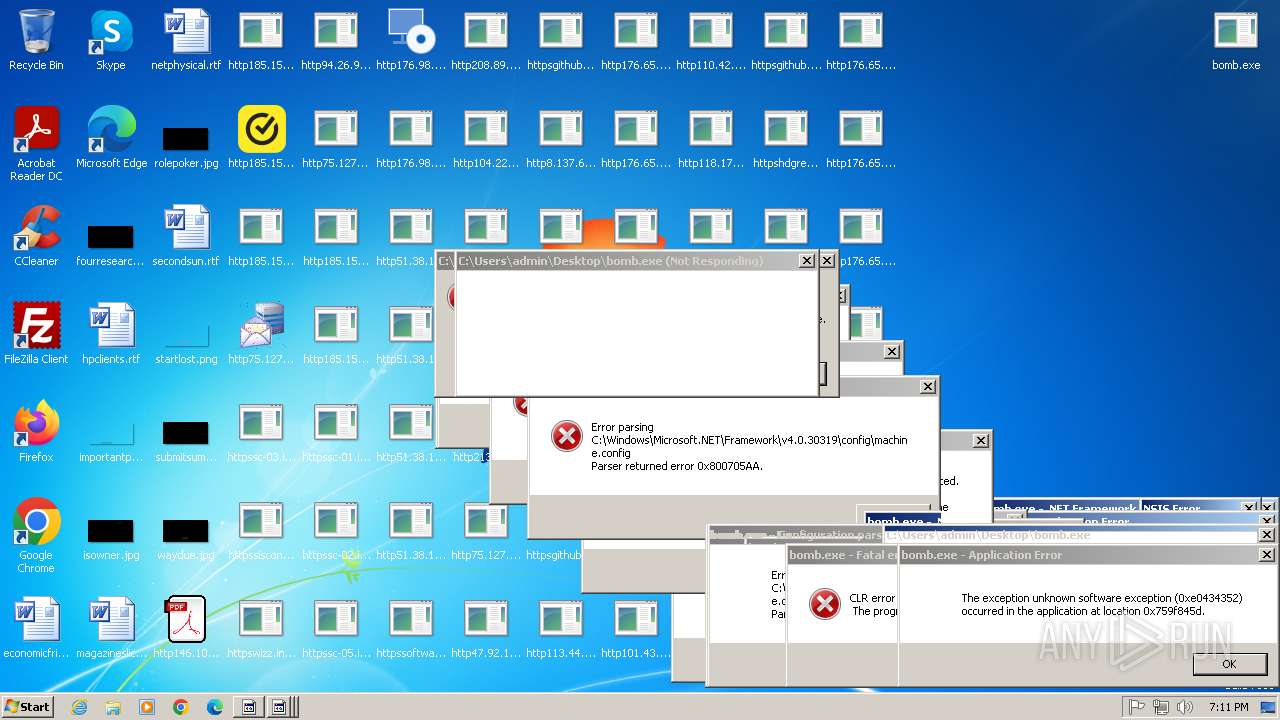
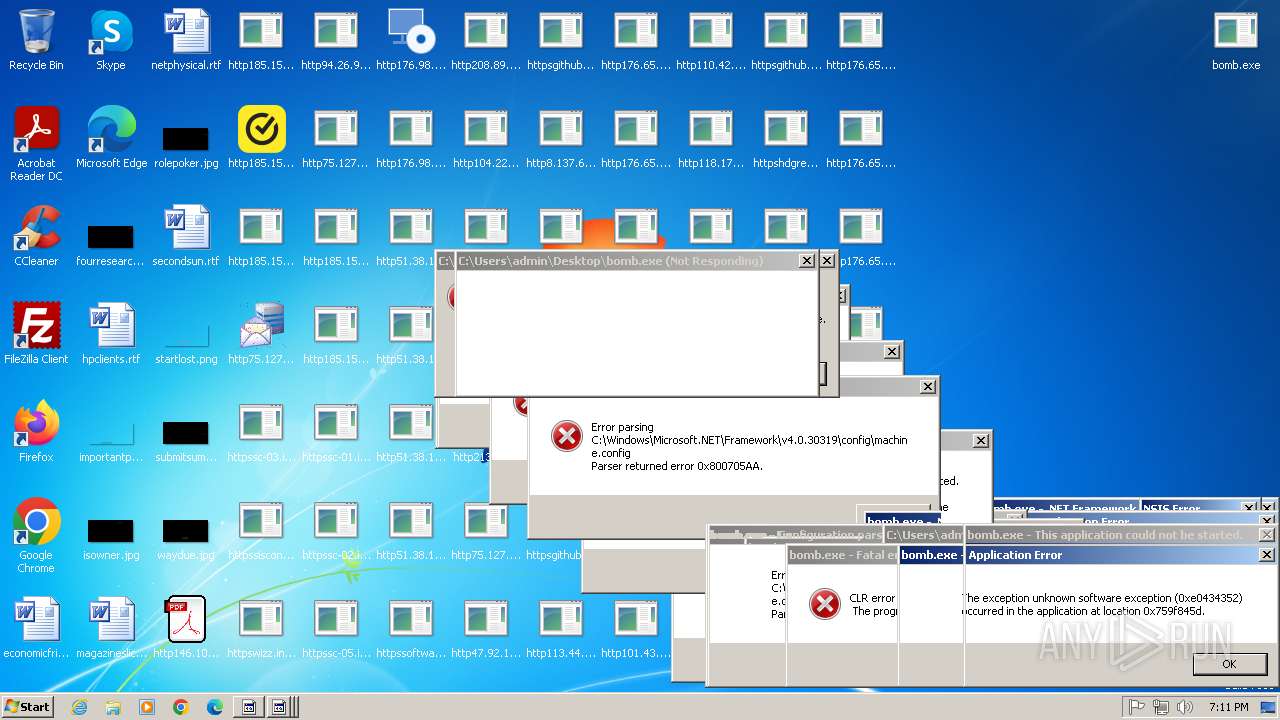
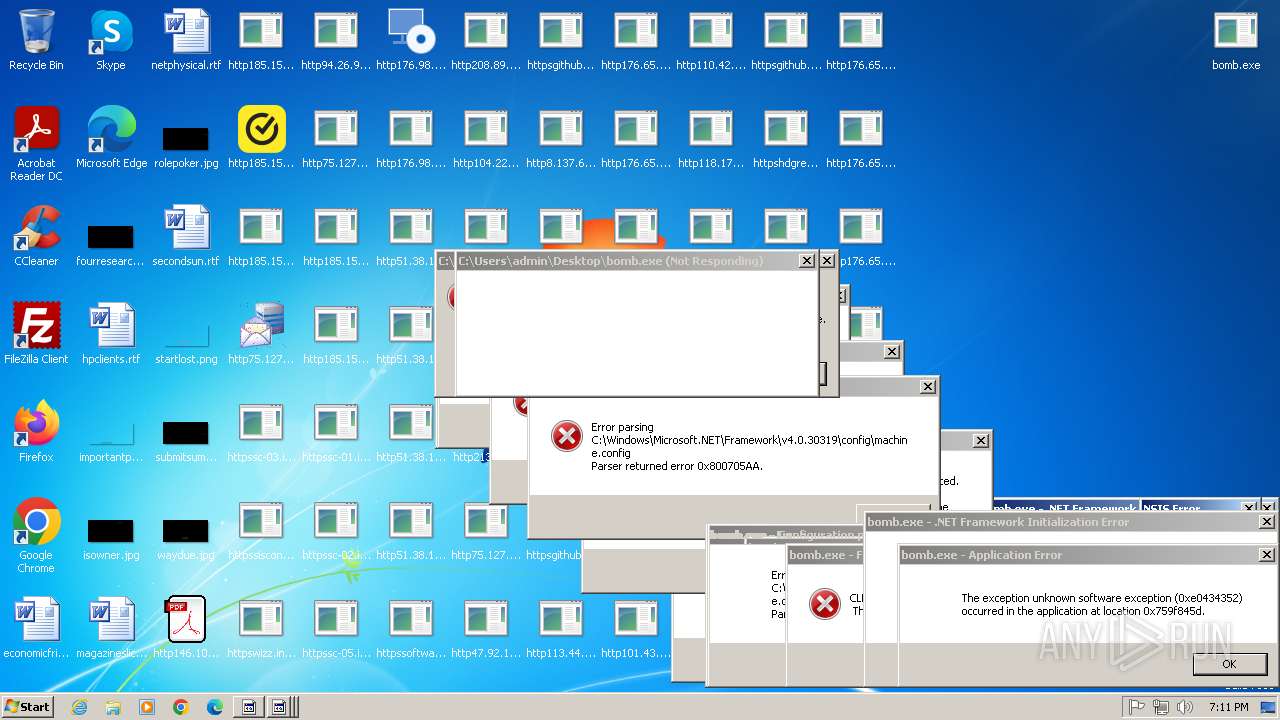
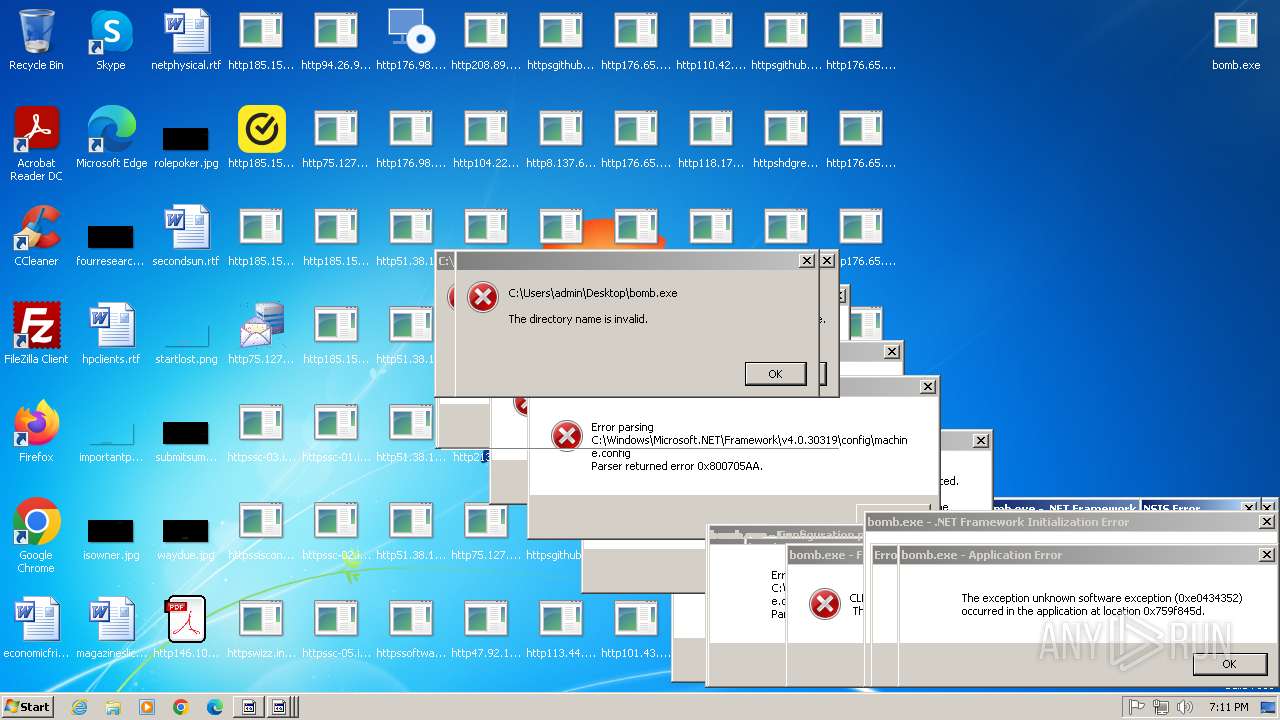
Total processes
647
Monitored processes
606
Malicious processes
15
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 268 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.0.0.0 Modules
| |||||||||||||||
| 328 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 852 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 960 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 1080 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 1224 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 1396 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 1600 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
184 788
Read events
184 391
Write events
352
Delete events
45
Modification events
| (PID) Process: | (1080) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Nla\Cache\Intranet |
| Operation: | write | Name: | {4040CF00-1B3E-486A-B407-FA14C56B6FC0} |
Value: D4DA6D3E3157 | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1224) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
79
Suspicious files
20
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | http185.156.72.2files5795480469A2vn0Mb.exe.tmp | C:\Users\admin\AppData\Local\Temp\is-QB0KG.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1224 | bomb.exe | C:\Users\admin\Desktop\http185.156.72.2files6723359323FxefytI.exe.exe | executable | |
MD5:7EF7FCFDF9938FAFA37BABC36601E7DD | SHA256:40163F7C5341BD1CB29B47552827544D75B8D9EFEAD359B292B281EAD445A3A1 | |||
| 1224 | bomb.exe | C:\Users\admin\Desktop\http185.156.72.2files5795480469A2vn0Mb.exe.exe | executable | |
MD5:4E8144068DAF97AE616160FDCC26F34F | SHA256:0C181B7D7E866BE58430F2B4EA0B8822BD1C1A5C64E63815AE9B8531134F42B4 | |||
| 1224 | bomb.exe | C:\Users\admin\Desktop\http185.156.72.2files5712371530E759x7N.exe.exe | executable | |
MD5:D14A22031323C343623D6766BA80B1ED | SHA256:BBC04EE70F769D1D57EA46968ABDD2AD2B673BACD805FE1BCBAC9E7FE8C28AE4 | |||
| 3044 | http185.156.72.2files5795480469A2vn0Mb.exe.exe | C:\Users\admin\AppData\Local\Temp\is-2420V.tmp\http185.156.72.2files5795480469A2vn0Mb.exe.tmp | executable | |
MD5:FFD4DF78AA9788CA6A3DC61077AD50ED | SHA256:5F620B954086C437DAA38012076FE6C453F28F6FD2A1459018C26CB7BDCF20E6 | |||
| 1224 | bomb.exe | C:\Users\admin\Desktop\http146.103.7.34150TiWorker.exe.exe | executable | |
MD5:AD60FC98CFA36FD229FD46AABC71B260 | SHA256:C17E8C6B860A83B92AD9426113FED857076924F0DE5D7ED0E6ECACD032DF67A8 | |||
| 3016 | http146.103.7.34150TiWorker.exe.exe | C:\Users\admin\AppData\Local\Temp\demonetising | binary | |
MD5:24466CEAA754885D3AE569EF821E7103 | SHA256:B24A39DB91A037063D1EA2D79E3170C7A5290AB14C2221C1C7B34F6682854589 | |||
| 3016 | http146.103.7.34150TiWorker.exe.exe | C:\Users\admin\AppData\Local\Temp\aut483F.tmp | binary | |
MD5:24466CEAA754885D3AE569EF821E7103 | SHA256:B24A39DB91A037063D1EA2D79E3170C7A5290AB14C2221C1C7B34F6682854589 | |||
| 2732 | http185.156.72.2files5795480469A2vn0Mb.exe.tmp | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\is-DCF3N.tmp | executable | |
MD5:E1C166179121741D0D0E7E3EB37483D7 | SHA256:042EDF9FA6AE5D48C84E66361312ADA77B419BE6D4DD0B1AA2CF538550B23AB6 | |||
| 1224 | bomb.exe | C:\Users\admin\Desktop\httpssc-03.infinitycloud.orgbinsupport.client.exei=&e=Support&y=Guest&r=.exe | executable | |
MD5:90BAE9193A83D5CF1F509ADA3CCB8608 | SHA256:67B5F6F0A1C82B52AB276D5E45E6CC73F100D2B4D1E1EB18E01E1CA47495B8A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
326
TCP/UDP connections
1 268
DNS requests
45
Threats
1 697
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
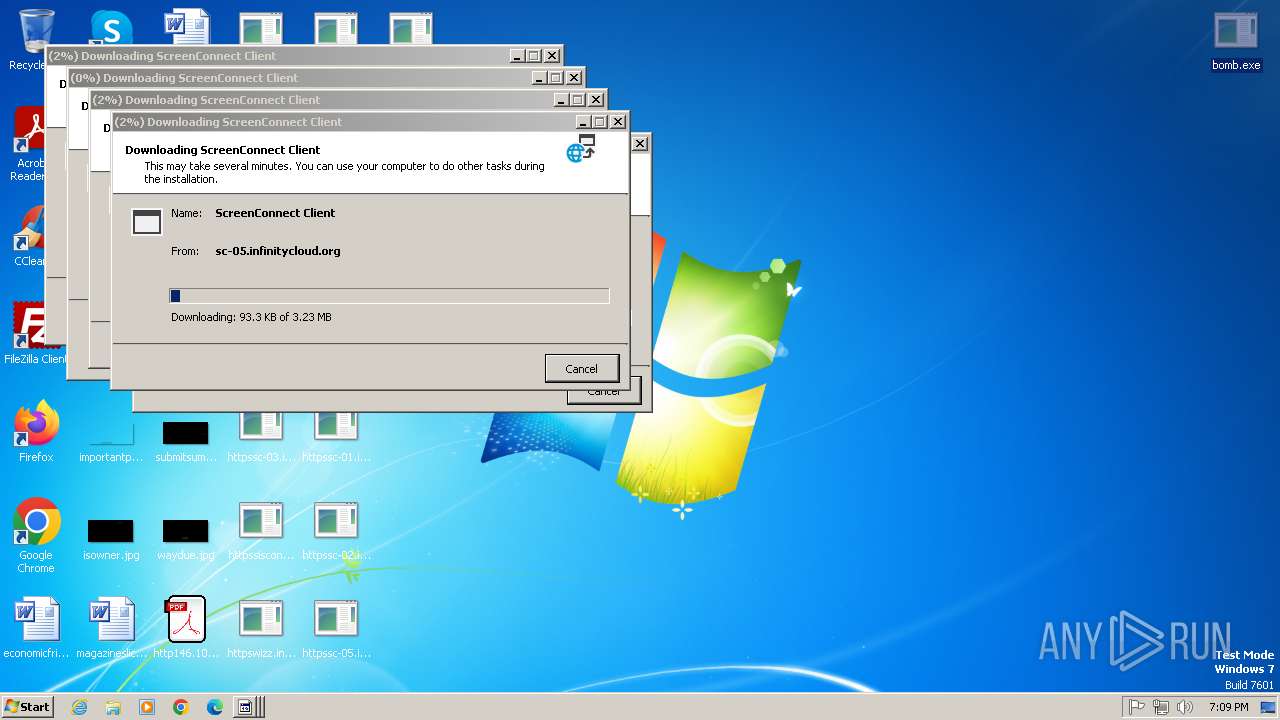
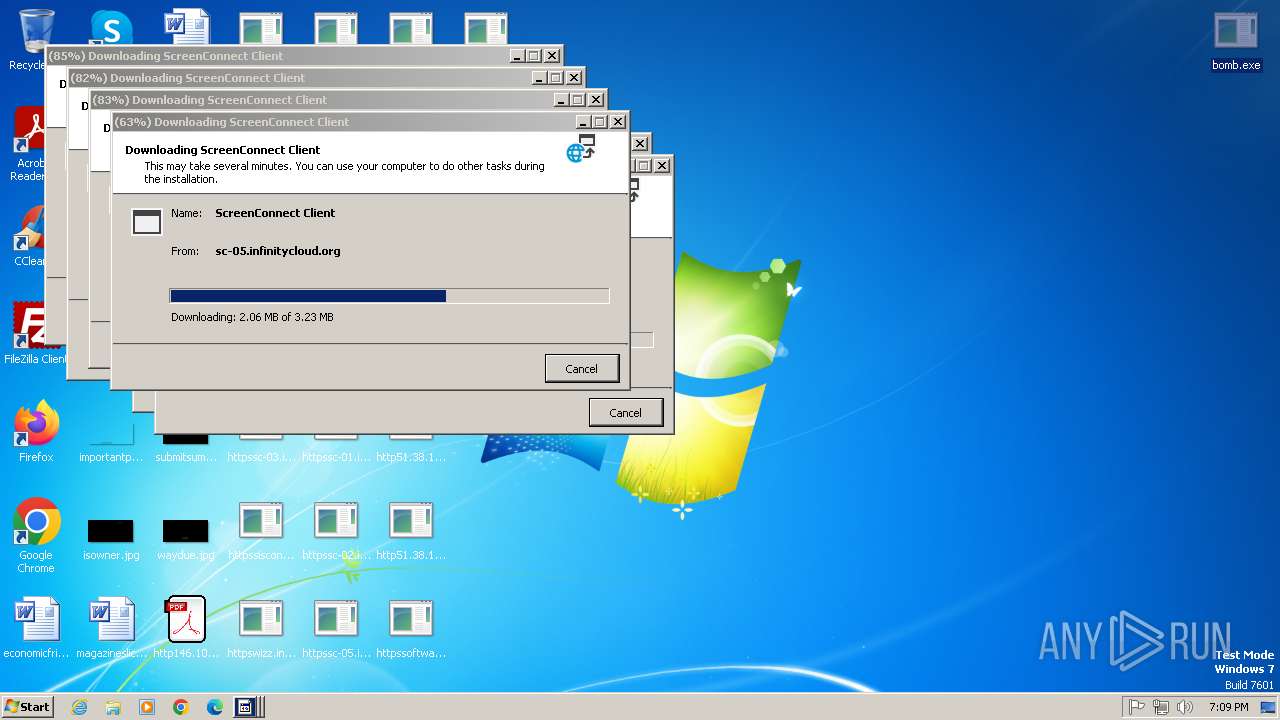
1224 | bomb.exe | GET | 200 | 146.103.7.34:80 | http://146.103.7.34/150/TiWorker.exe | unknown | — | — | unknown |
1224 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/6723359323/FxefytI.exe | unknown | — | — | unknown |
1224 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/5795480469/A2vn0Mb.exe | unknown | — | — | unknown |
1224 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/5712371530/E759x7N.exe | unknown | — | — | unknown |
1224 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/6003232782/oxDU0MW.exe | unknown | — | — | unknown |
1224 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/5494432675/ZGSI81i.exe | unknown | — | — | unknown |
1224 | bomb.exe | GET | 200 | 176.98.185.87:80 | http://176.98.185.87/widsmob_denoise_win.exe | unknown | — | — | unknown |
1224 | bomb.exe | GET | 200 | 176.98.185.87:80 | http://176.98.185.87/Quodlibet.exe | unknown | — | — | unknown |
3284 | dfsvc.exe | GET | 200 | 2.23.77.188:80 | http://cacerts.digicert.com/DigiCertTrustedG4CodeSigningRSA4096SHA3842021CA1.crt | unknown | — | — | whitelisted |
3284 | dfsvc.exe | GET | 200 | 2.23.77.188:80 | http://cacerts.digicert.com/DigiCertTrustedG4CodeSigningRSA4096SHA3842021CA1.crt | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1224 | bomb.exe | 188.114.96.3:443 | maper.info | CLOUDFLARENET | NL | malicious |
1224 | bomb.exe | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
1224 | bomb.exe | 151.101.130.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
1224 | bomb.exe | 185.156.72.2:80 | — | Tov Vaiz Partner | RU | unknown |
1224 | bomb.exe | 146.103.7.34:80 | — | — | BE | unknown |
1224 | bomb.exe | 185.72.145.109:80 | gettsveriff.com | FullSpace Ltd. | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
maper.info |
| malicious |
www.google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
gettsveriff.com |
| unknown |
sc-03.infinitycloud.org |
| unknown |
wizz.infinitycloud.org |
| unknown |
sisconnect-01.infinitycloud.org |
| unknown |
sc-02.infinitycloud.org |
| unknown |
sc-05.infinitycloud.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1224 | bomb.exe | Potential Corporate Privacy Violation | ET INFO IP Logger Redirect Domain in SNI |
1224 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1224 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1224 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1224 | bomb.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
1224 | bomb.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
1224 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1224 | bomb.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
1224 | bomb.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
1224 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
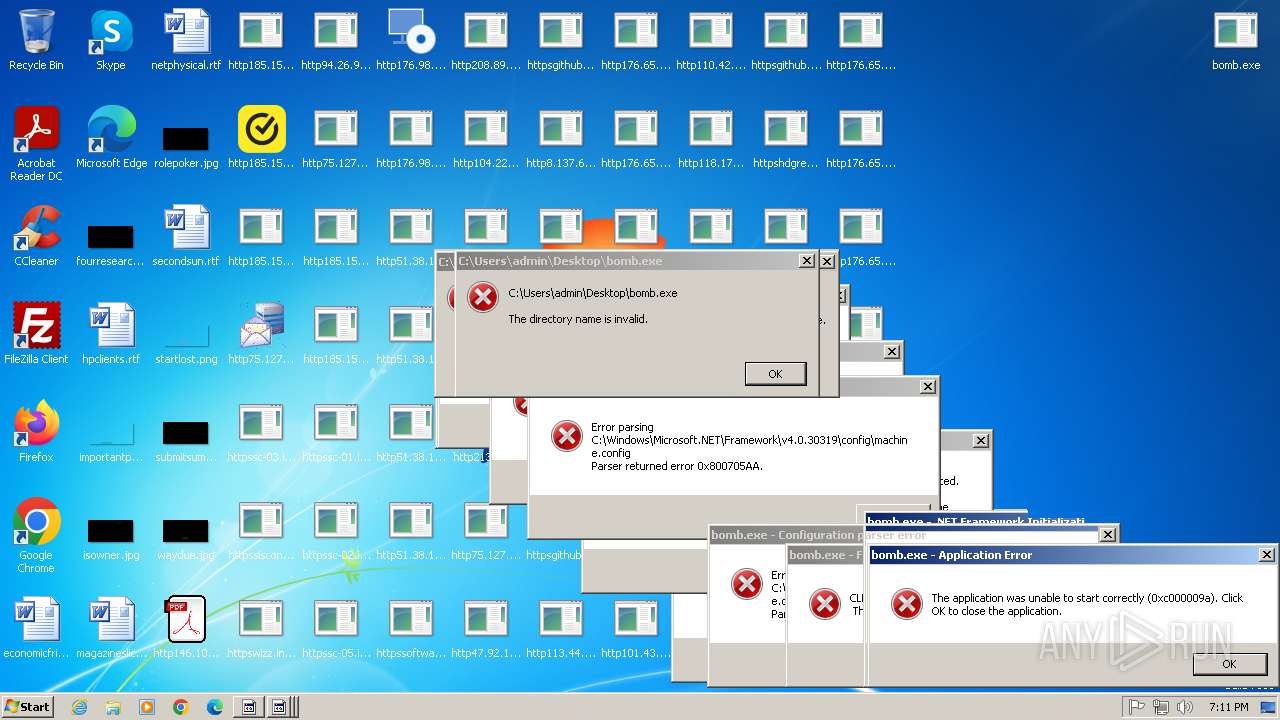
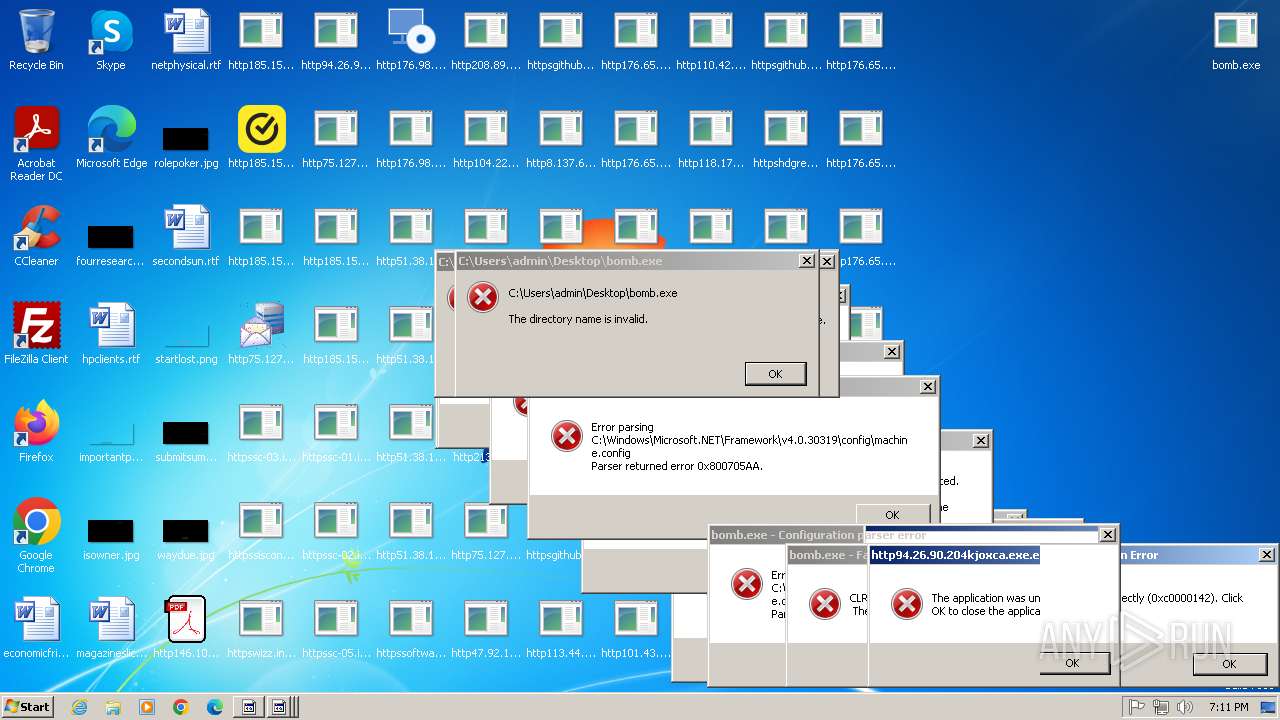
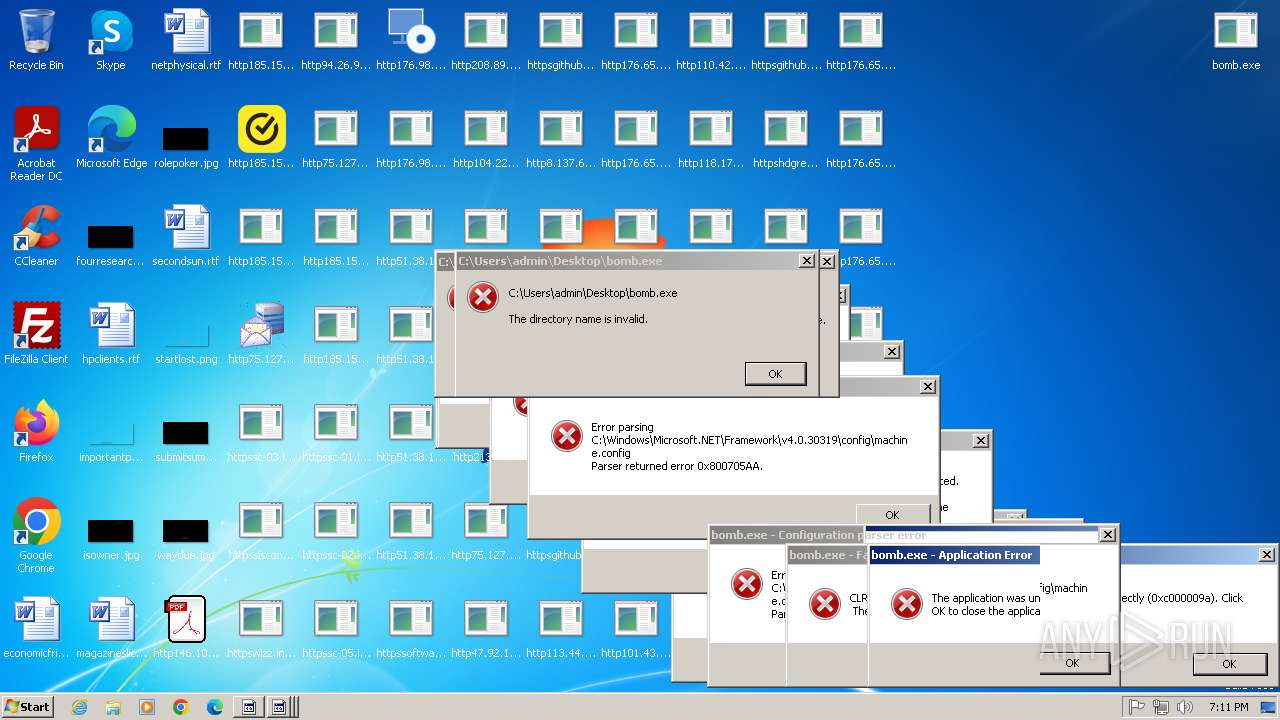
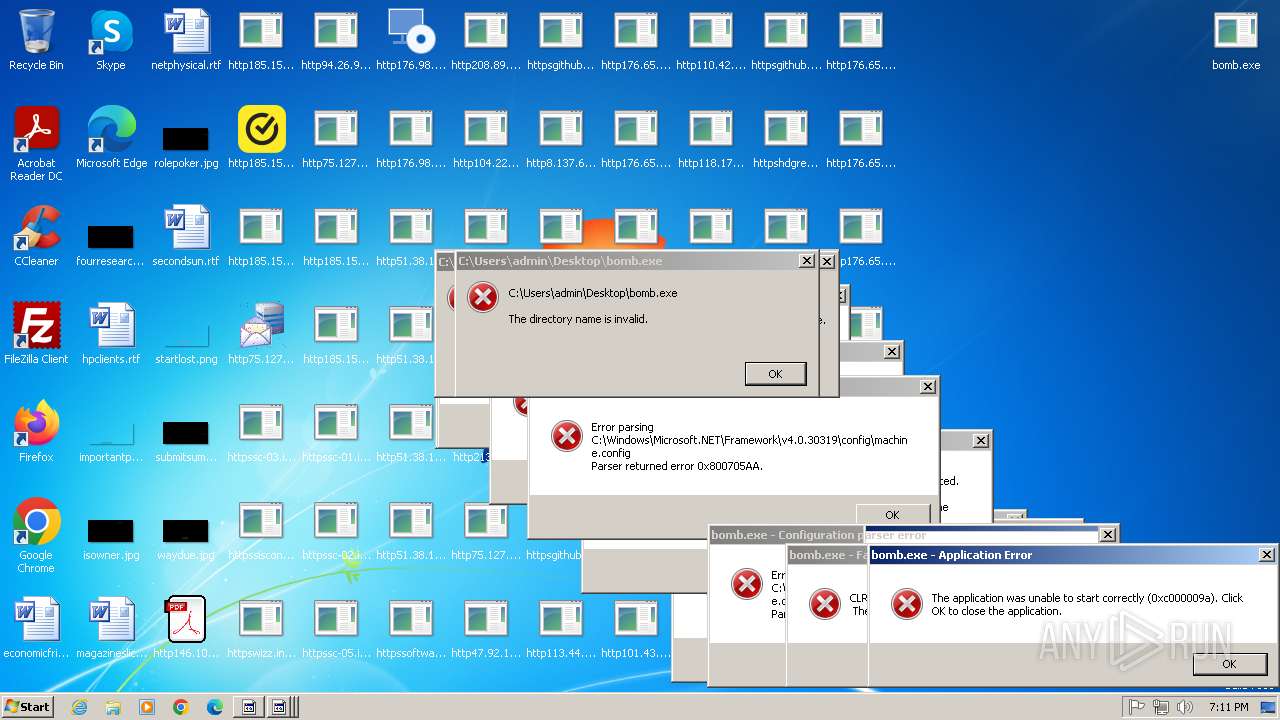
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|