| File name: | edonkey143.exe |
| Full analysis: | https://app.any.run/tasks/ba0f6958-5852-4013-9e7e-48954ee0c72c |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2024, 14:58:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 10FB786348E42B0412809857EEF40185 |
| SHA1: | 63E1C46332096318E1205883163FD93AFEB83D6C |
| SHA256: | 990BE5B4E799F7A945363B4477E526FC1D1797C71437A9B0B6069C44533147CD |
| SSDEEP: | 98304:Xcz6VJ6usLBc9+bCEjkhC1vhKJxHSjaI6tvdXZ5XbTNz32IQLdx7opDZx2i8cc5a:ZACBNv |
MALICIOUS
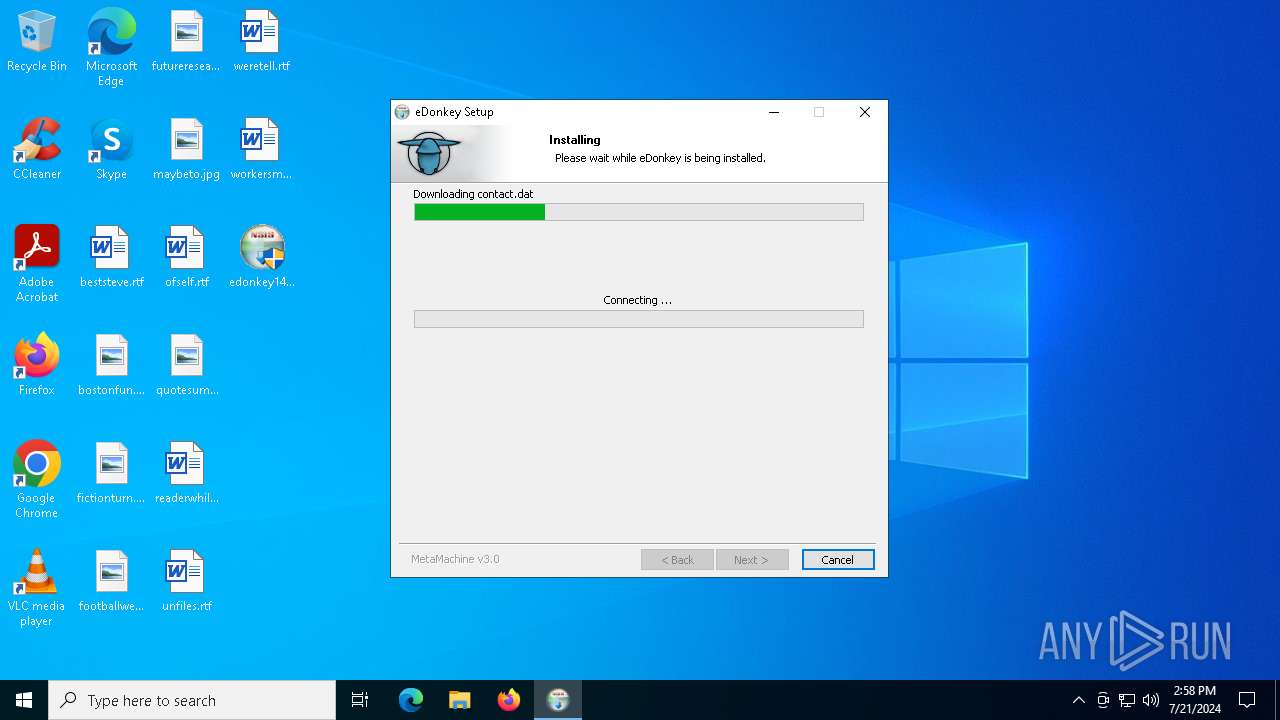
Drops the executable file immediately after the start
- edonkey143.exe (PID: 5636)
Changes the autorun value in the registry
- edonkey143.exe (PID: 5636)
SUSPICIOUS
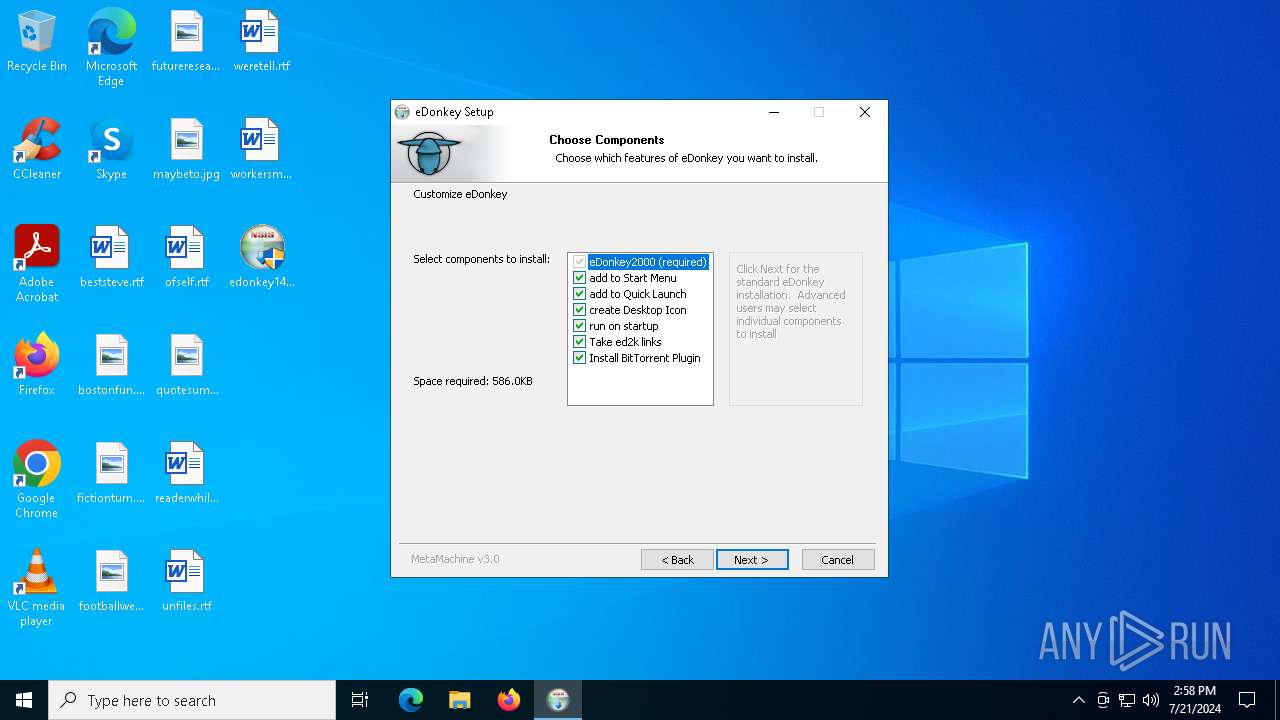
Creates a software uninstall entry
- edonkey143.exe (PID: 5636)
Executable content was dropped or overwritten
- edonkey143.exe (PID: 5636)
Reads security settings of Internet Explorer
- edonkey143.exe (PID: 5636)
INFO
Create files in a temporary directory
- edonkey143.exe (PID: 5636)
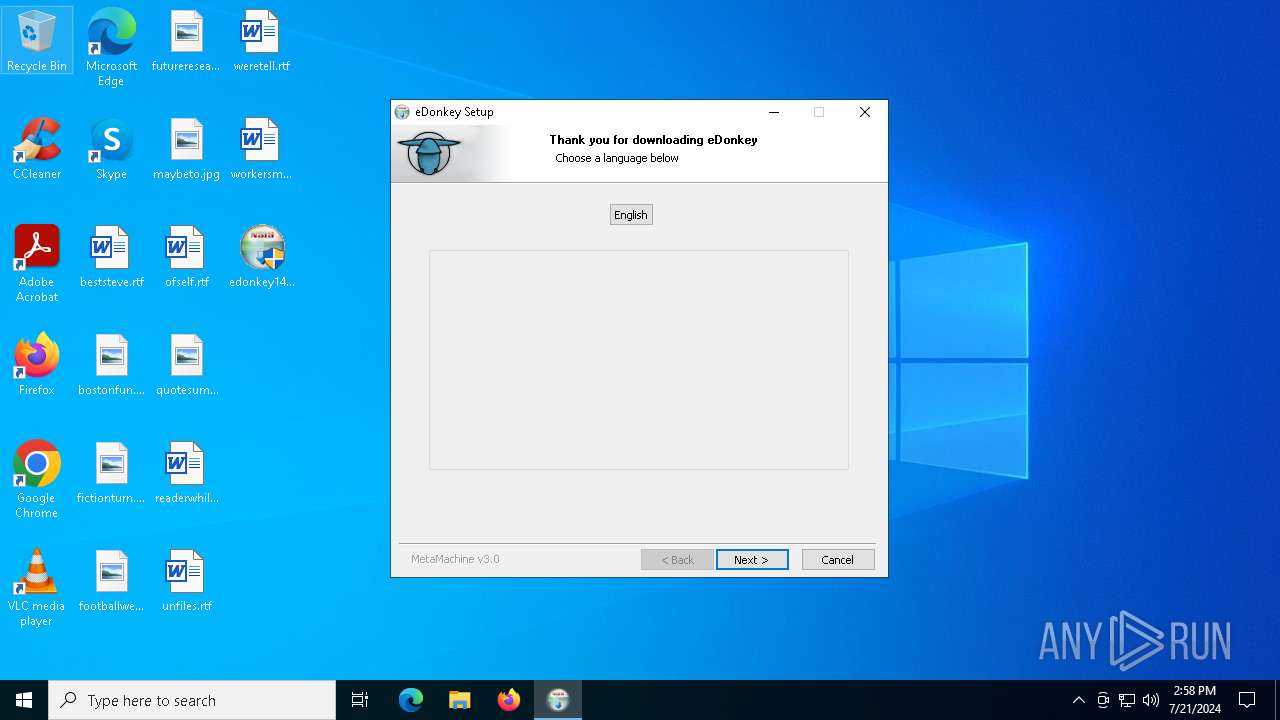
Checks supported languages
- edonkey2000.exe (PID: 7196)
- edonkey2000.exe (PID: 6068)
- edonkey143.exe (PID: 5636)
Reads the computer name
- edonkey143.exe (PID: 5636)
Creates files in the program directory
- edonkey143.exe (PID: 5636)
Checks proxy server information
- edonkey143.exe (PID: 5636)
Creates files or folders in the user directory
- edonkey143.exe (PID: 5636)
UPX packer has been detected
- edonkey143.exe (PID: 5636)
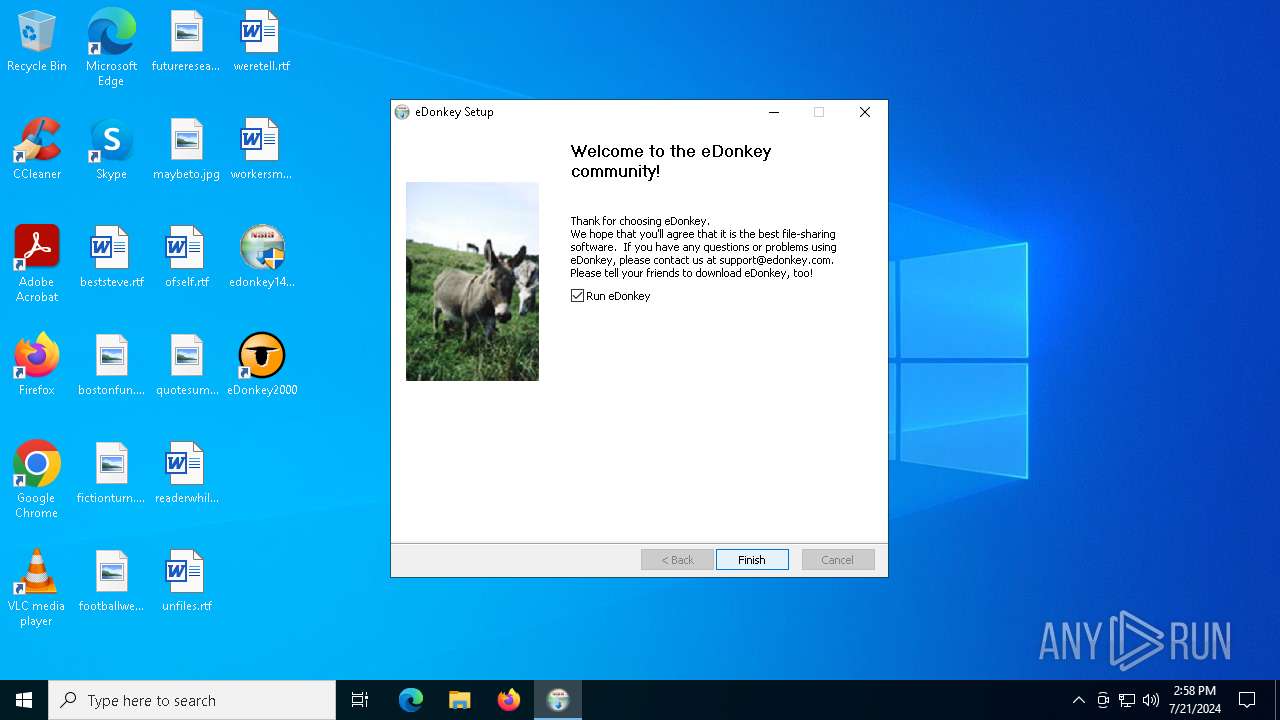
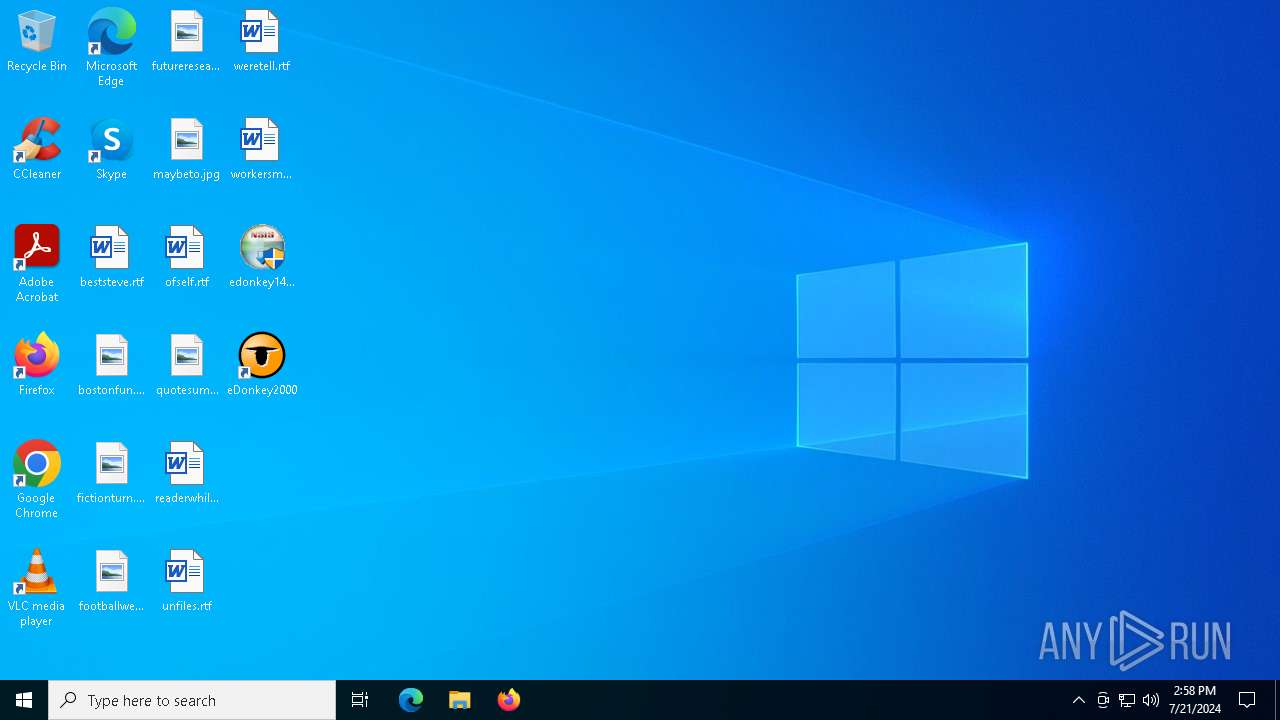
Manual execution by a user
- edonkey2000.exe (PID: 6068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:08:26 18:19:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 165376 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31a3 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
146
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2648 | "C:\Users\admin\Desktop\edonkey143.exe" | C:\Users\admin\Desktop\edonkey143.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5636 | "C:\Users\admin\Desktop\edonkey143.exe" | C:\Users\admin\Desktop\edonkey143.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
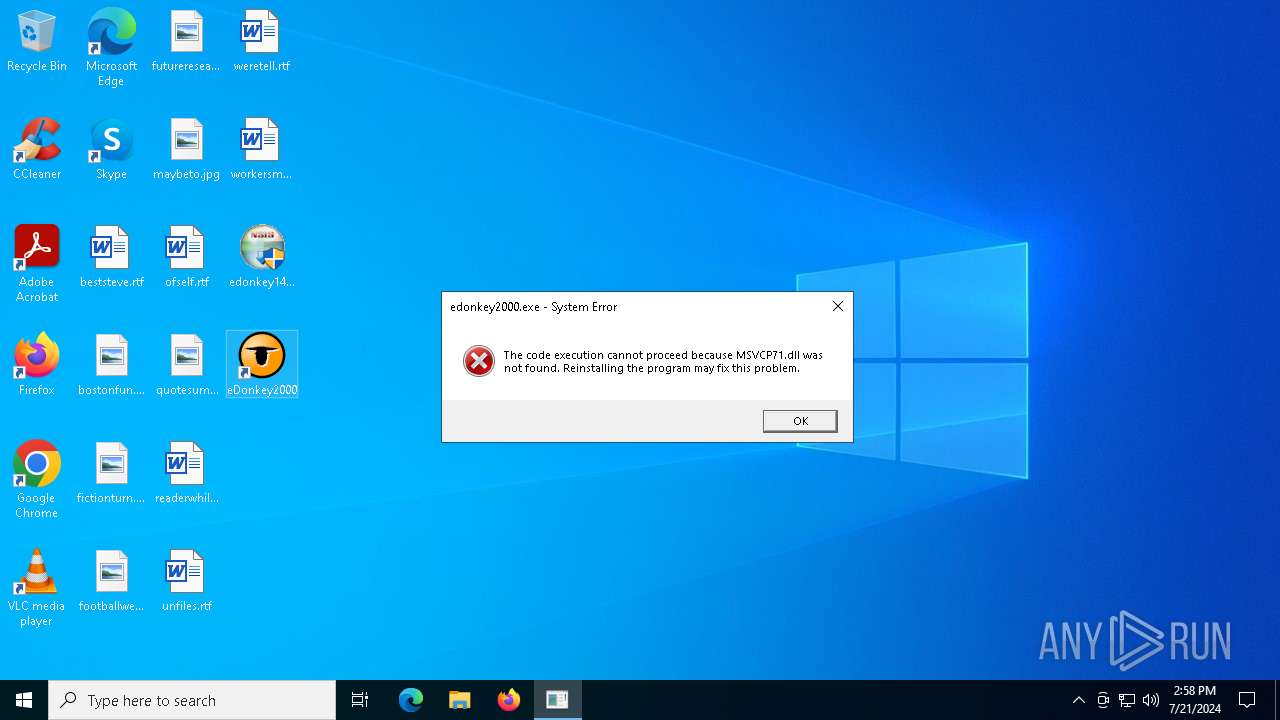
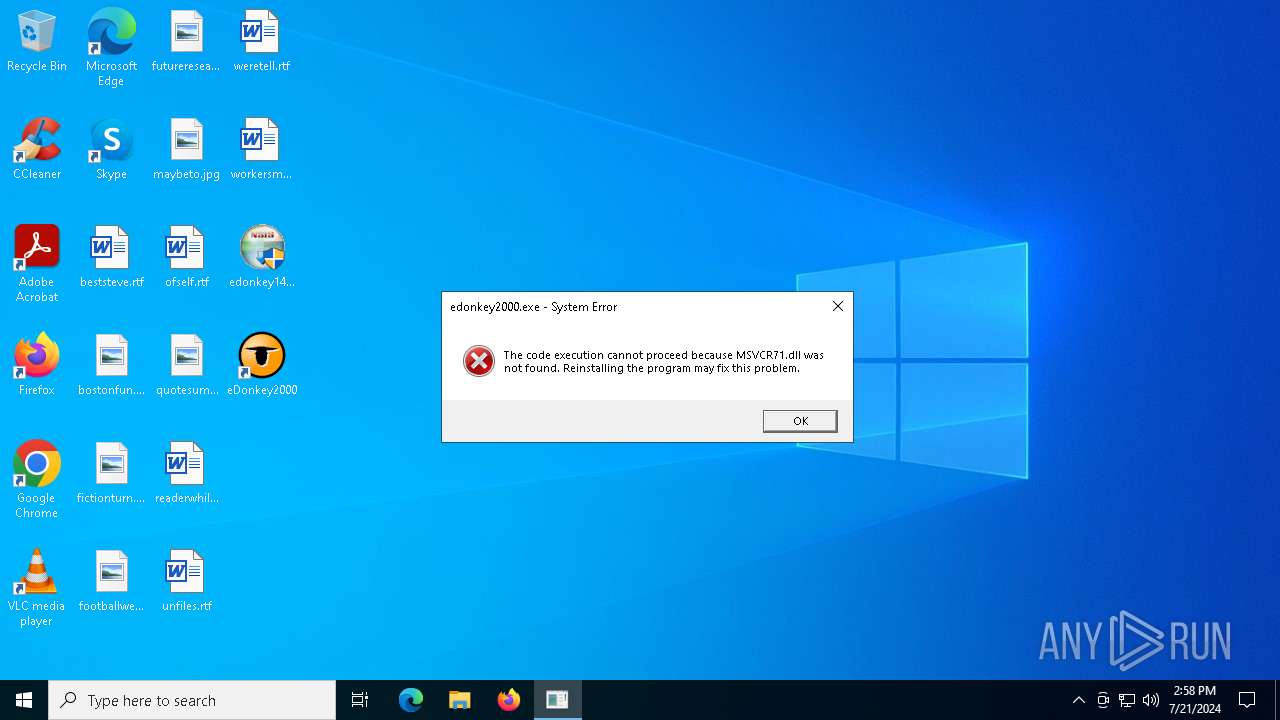
| 6068 | "C:\Program Files (x86)\eDonkey2000\edonkey2000.exe" | C:\Program Files (x86)\eDonkey2000\edonkey2000.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6484 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7196 | "C:\Program Files (x86)\eDonkey2000\eDonkey2000.exe" | C:\Program Files (x86)\eDonkey2000\edonkey2000.exe | — | edonkey143.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225781 Modules
| |||||||||||||||
Total events
5 469
Read events
5 461
Write events
8
Delete events
0
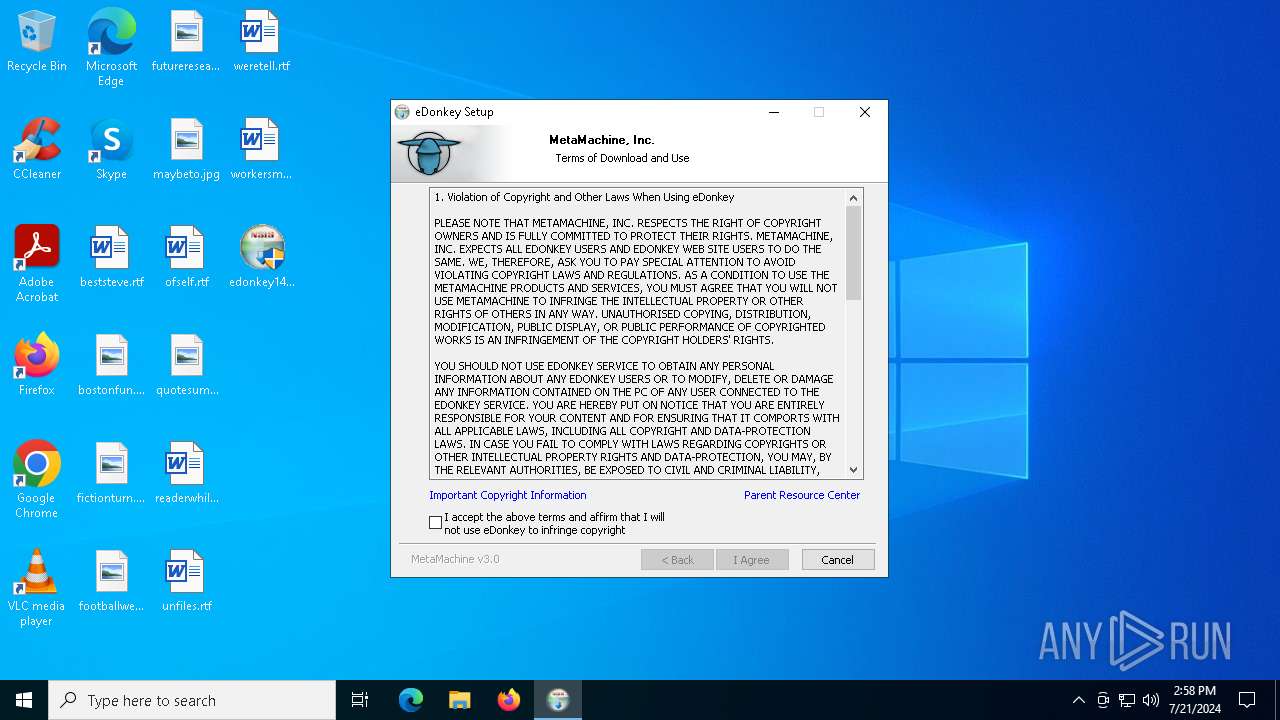
Modification events
| (PID) Process: | (5636) edonkey143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\SOFTWARE\MM\eDonkey2000 |
| Operation: | write | Name: | installDir |
Value: C:\Program Files (x86)\eDonkey2000 | |||
| (PID) Process: | (5636) edonkey143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\eDonkey2000 |
| Operation: | write | Name: | DisplayName |
Value: eDonkey2000 | |||
| (PID) Process: | (5636) edonkey143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\eDonkey2000 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\eDonkey2000\uninstall_eDonkey2000.exe" | |||
| (PID) Process: | (5636) edonkey143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\eDonkey2000 |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Program Files (x86)\eDonkey2000\eDonkey2000.exe" | |||
| (PID) Process: | (5636) edonkey143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\eDonkey2000 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (5636) edonkey143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\eDonkey2000 |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (5636) edonkey143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | eDonkey2000 |
Value: C:\Program Files (x86)\eDonkey2000\eDonkey2000.exe -t | |||
| (PID) Process: | (5636) edonkey143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ed2k |
| Operation: | write | Name: | URL Protocol |
Value: | |||
Executable files
14
Suspicious files
8
Text files
143
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\NSISdl.dll | executable | |
MD5:7459B4D61DD26D2864CB79CAE1A5229F | SHA256:262BB55F83A9B8CC5CCA3743D04937A85628E3FFCBB91300356C1F03A96432B4 | |||
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\license.ini | html | |
MD5:61AFCEDCE02349F9DBB4D9BC8223B56A | SHA256:1035BBCF4CDF0D70E9132E1EAE459C22ECB2C253F2AAB2B0011C6FC8CBDBC679 | |||
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\launch.ini | html | |
MD5:61AFCEDCE02349F9DBB4D9BC8223B56A | SHA256:1035BBCF4CDF0D70E9132E1EAE459C22ECB2C253F2AAB2B0011C6FC8CBDBC679 | |||
| 5636 | edonkey143.exe | C:\Program Files (x86)\eDonkey2000\blacklist.txt | text | |
MD5:4F09B6445F43236A1302D4F6A1582FC4 | SHA256:9AA15C626587759382509F46340DAB33A8DE546C96933FC47F71324C94DE1BEB | |||
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\contact.dat | html | |
MD5:61AFCEDCE02349F9DBB4D9BC8223B56A | SHA256:1035BBCF4CDF0D70E9132E1EAE459C22ECB2C253F2AAB2B0011C6FC8CBDBC679 | |||
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\InstallOptions.dll | executable | |
MD5:56984F2FC6FCD8357F07BE61C7874029 | SHA256:F8EE2D2305153B0FFCCF8DC3C29E3360A3792FBEAF06D8636F2C65761DCF9218 | |||
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\lang.ini | html | |
MD5:61AFCEDCE02349F9DBB4D9BC8223B56A | SHA256:1035BBCF4CDF0D70E9132E1EAE459C22ECB2C253F2AAB2B0011C6FC8CBDBC679 | |||
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\InstallOptionsEx.dll | executable | |
MD5:EC32672F247BAFB784A970E8253DCA34 | SHA256:AC11223BDCEC43D1AAC9E6649E390AB588CA9C02095C53870CDE565239142414 | |||
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\smalldonk.bmp | image | |
MD5:72BA9E97E9C92404B3CF7A4CE9767D35 | SHA256:858EB2DCE3F5119D7DD19E4D03790C214CB8E56BAC752312221FFD808958C62A | |||
| 5636 | edonkey143.exe | C:\Users\admin\AppData\Local\Temp\nsg90E5.tmp\search.ini | html | |
MD5:61AFCEDCE02349F9DBB4D9BC8223B56A | SHA256:1035BBCF4CDF0D70E9132E1EAE459C22ECB2C253F2AAB2B0011C6FC8CBDBC679 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
45
DNS requests
17
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
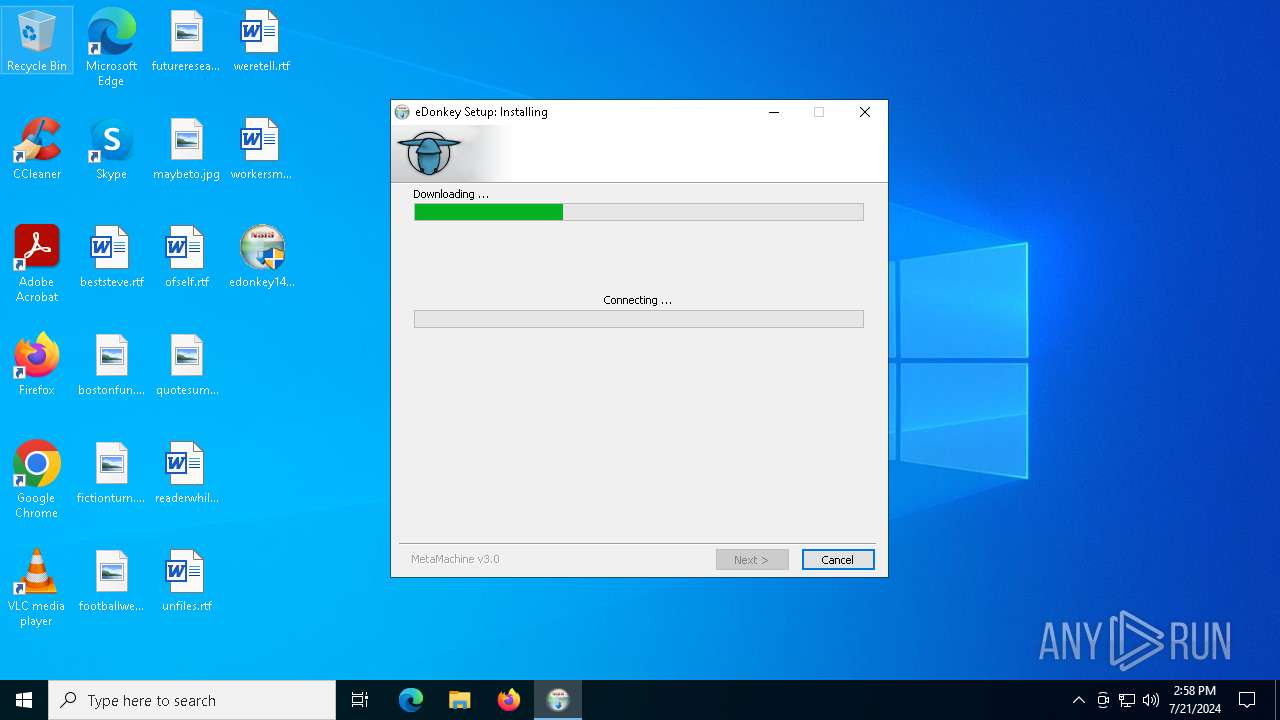
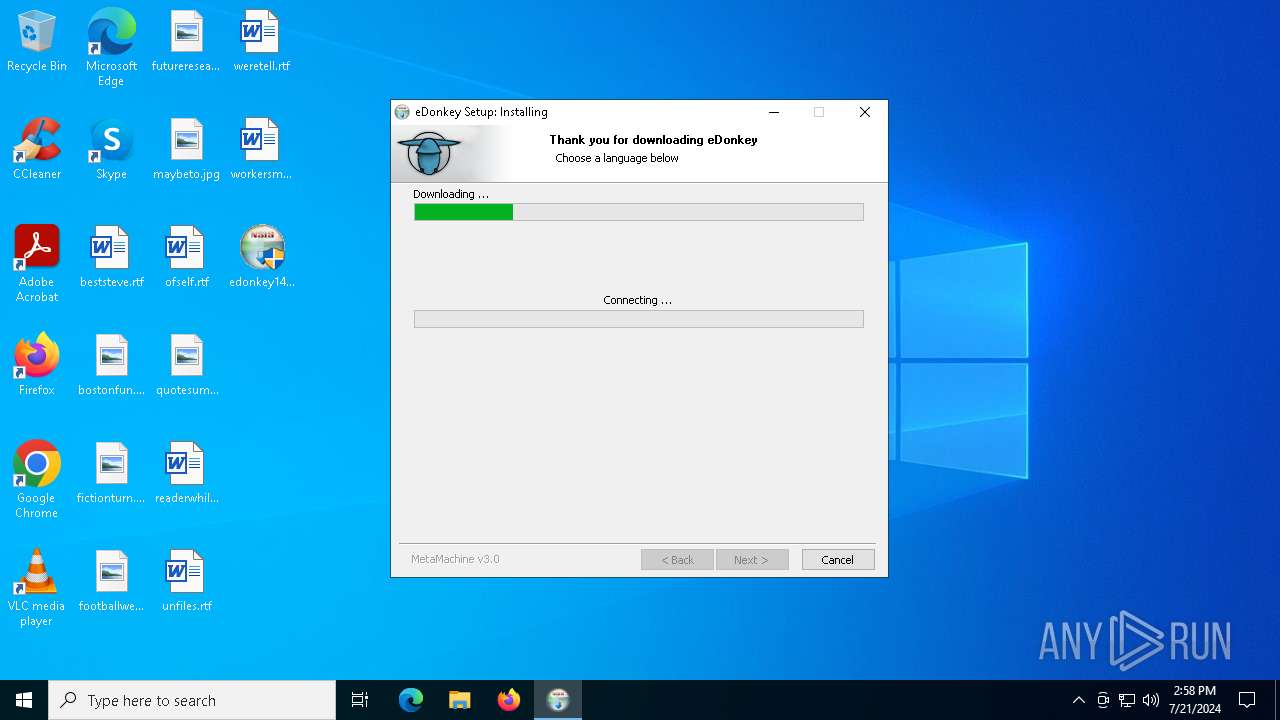
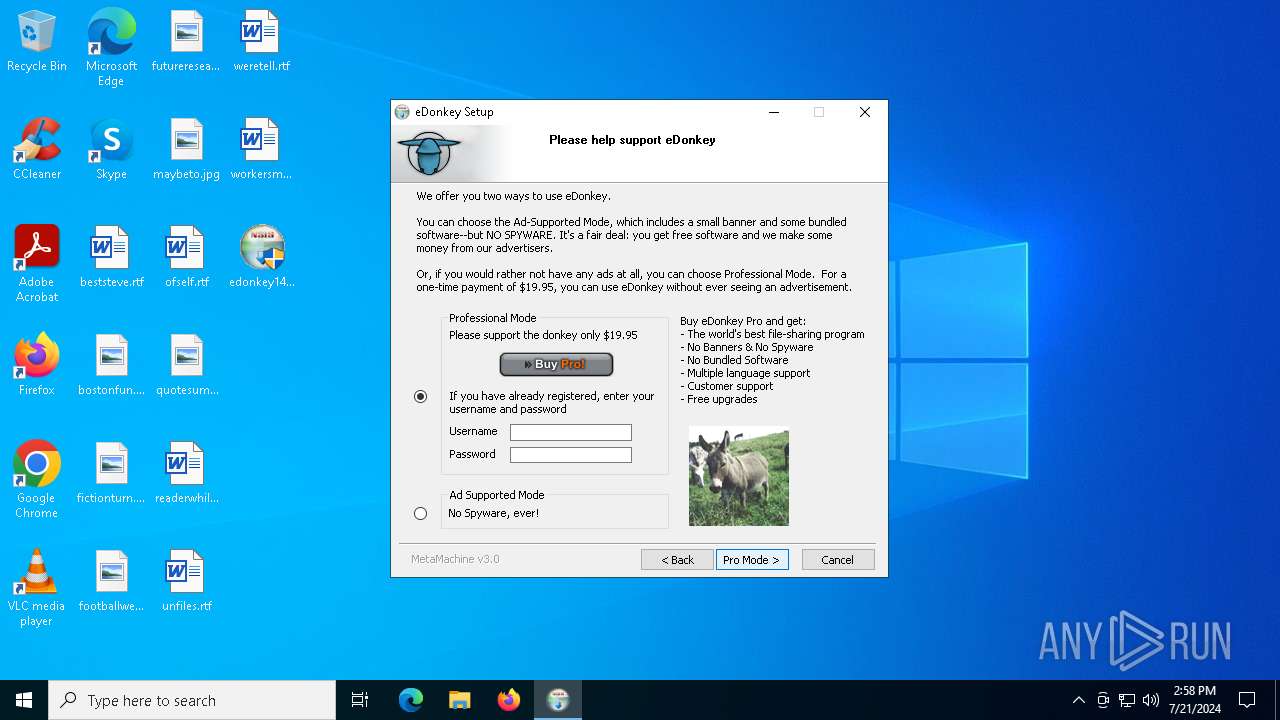
5636 | edonkey143.exe | GET | — | 104.143.9.210:80 | http://install.overnet.com/install.php?page=search&lang=EN&client_version=1.4.3&installer_version=3.0 | unknown | — | — | malicious |
5636 | edonkey143.exe | GET | — | 104.143.9.210:80 | http://install.overnet.com/install.php?page=lang&client_type=20&client_version=1.4.3&installer_version=3.0&lang_code=1033 | unknown | — | — | malicious |
5636 | edonkey143.exe | GET | — | 104.143.9.210:80 | http://install.overnet.com/install.php?page=license&lang=EN&client_version=1.4.3&installer_version=3.0 | unknown | — | — | malicious |
5636 | edonkey143.exe | GET | — | 104.143.9.210:80 | http://install.overnet.com/install.php?page=reg&lang=EN&client_type=20&client_version=1.4.3&installer_version=3.0 | unknown | — | — | malicious |
5636 | edonkey143.exe | GET | — | 104.143.9.210:80 | http://install.overnet.com/install.php?page=launch&lang=EN&client_version=1.4.3&installer_version=3.0 | unknown | — | — | malicious |
5636 | edonkey143.exe | GET | — | 104.143.9.210:80 | http://install.overnet.com/install.php?page=bundles&lang=EN&existing=&bundle_id=&client_version=1.4.3&installer_version=3.0 | unknown | — | — | malicious |
5636 | edonkey143.exe | GET | — | 104.143.9.210:80 | http://install.overnet.com/contact.dat.php?client_version=1.4.3&installer_version=3.0 | unknown | — | — | malicious |
5636 | edonkey143.exe | GET | 200 | 199.59.243.226:80 | http://ww1.edonkey2000.com/ | unknown | — | — | unknown |
5636 | edonkey143.exe | GET | 302 | 82.192.82.228:80 | http://met.edonkey2000.com/server.met | unknown | — | — | unknown |
5636 | edonkey143.exe | GET | — | 104.143.9.210:80 | http://install.overnet.com/summary.php?install_date=&client_type=20&client_version=1.4.3&bundles=®_ind=0&installer_version=3.0 | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4716 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5620 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7856 | svchost.exe | 4.208.221.206:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5636 | edonkey143.exe | 104.143.9.210:80 | install.overnet.com | TP | US | unknown |
2760 | svchost.exe | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7268 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
install.overnet.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
licensing.mp.microsoft.com |
| whitelisted |
met.edonkey2000.com |
| unknown |
arc.msn.com |
| whitelisted |
ww1.edonkey2000.com |
| unknown |
download.edonkey.com |
| unknown |
Threats
20 ETPRO signatures available at the full report