| File name: | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf |
| Full analysis: | https://app.any.run/tasks/5c0383fb-8069-4b46-8727-bd498f4bfeb0 |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 10:52:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C2B5FE633003E6639E28D09B63D6A308 |
| SHA1: | 752104966DD6CC73EDDF790DAE3872CD2FA898B1 |
| SHA256: | 990B22A7F6555B227E72E7238F77924ACD52D1B08A6B395FBC24E8B9C6EF6BAF |
| SSDEEP: | 98304:tZakvT8OHGqrTmw4pzESoaXdtnTiQfcpmJUFPiXWqgVd2PM1SCNtjNldzhehzybl:zaITmaqw4caXNf5JYqPgVgPM1VbldzZl |
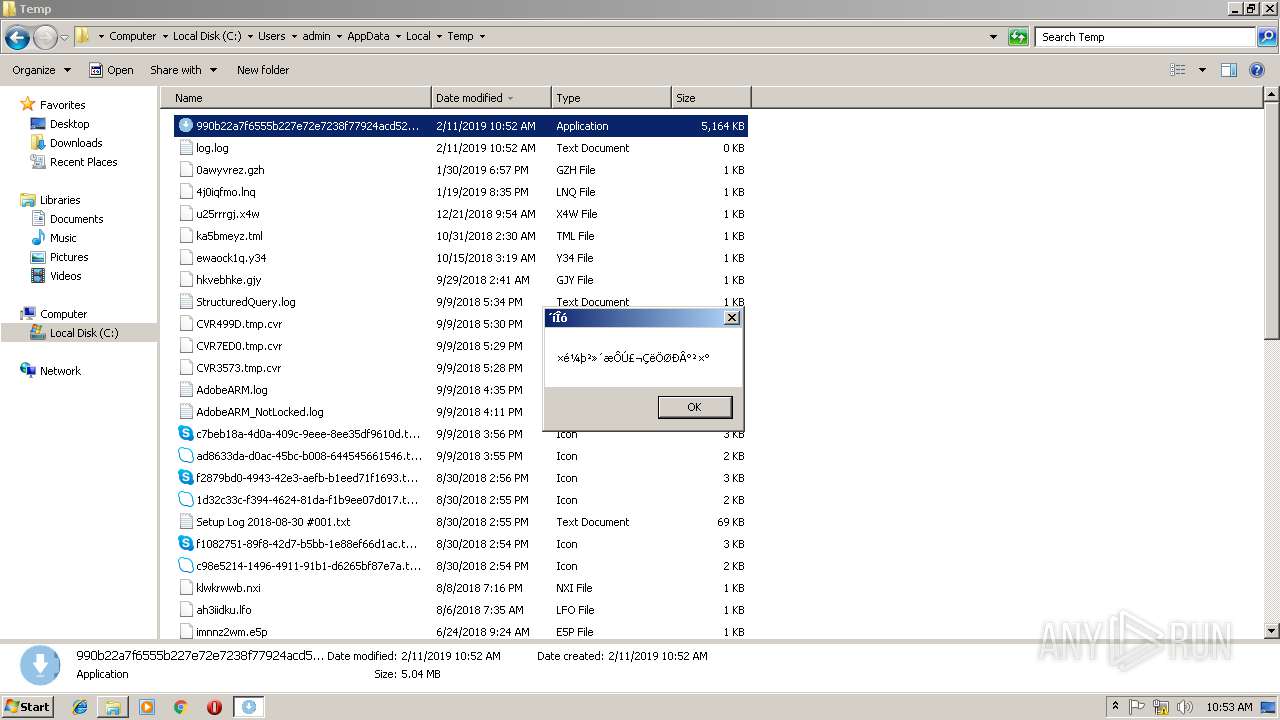
MALICIOUS
Loads dropped or rewritten executable
- 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe (PID: 2804)
- 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe (PID: 3176)
SUSPICIOUS
Executable content was dropped or overwritten
- 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe (PID: 3176)
- 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe (PID: 2804)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1972:12:25 06:33:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 380928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3861 |
| OSVersion: | 4 |
| ImageVersion: | 1.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.1.1 |
| ProductVersionNumber: | 1.1.1.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.1.1.1 |
| FileDescription: | 逍遥一仙 |
| ProductName: | M3U8批量下载器 |
| ProductVersion: | 1.1.1.1 |
| CompanyName: | 逍遥一仙 |
| LegalCopyright: | 逍遥一仙 版权所有 |
| Comments: | 逍遥一仙 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-1972 05:33:23 |
| Detected languages: |
|
| FileVersion: | 1.1.1.1 |
| FileDescription: | 逍遥一仙 |
| ProductName: | M3U8批量下载器 |
| ProductVersion: | 1.1.1.1 |
| CompanyName: | 逍遥一仙 |
| LegalCopyright: | 逍遥一仙 版权所有 |
| Comments: | 逍遥一仙 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-1972 05:33:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004DCC | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52193 |
.rdata | 0x00006000 | 0x00000A4A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.55983 |
.data | 0x00009000 | 0x00049000 | 0x00049000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.68781 |
.rsrc | 0x00052000 | 0x00010D6C | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.33479 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
129 | 1.98048 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
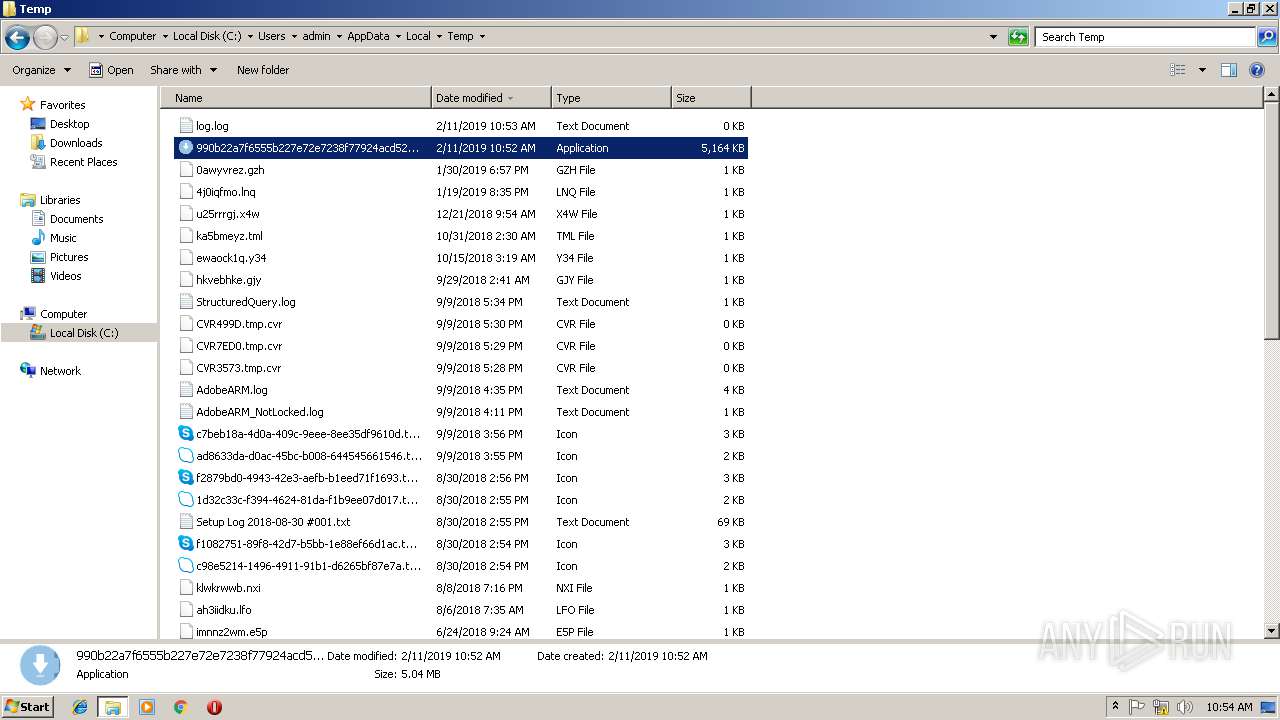
Total processes
42
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
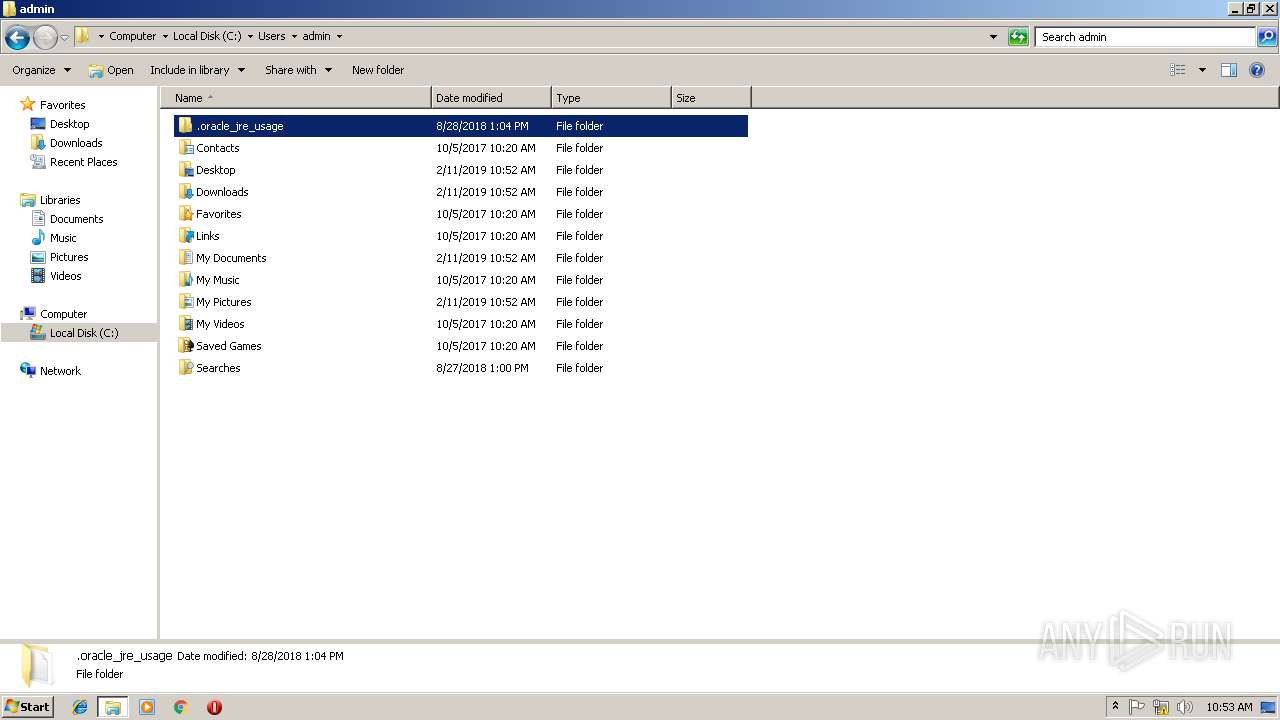
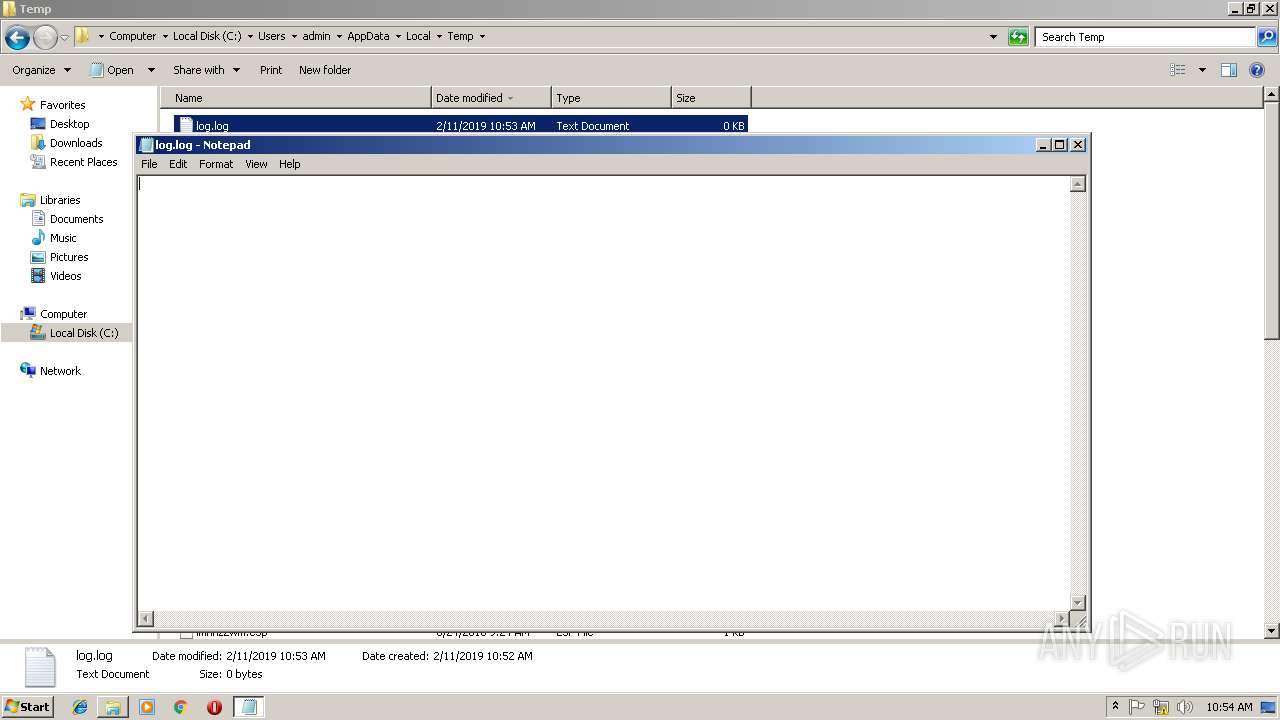
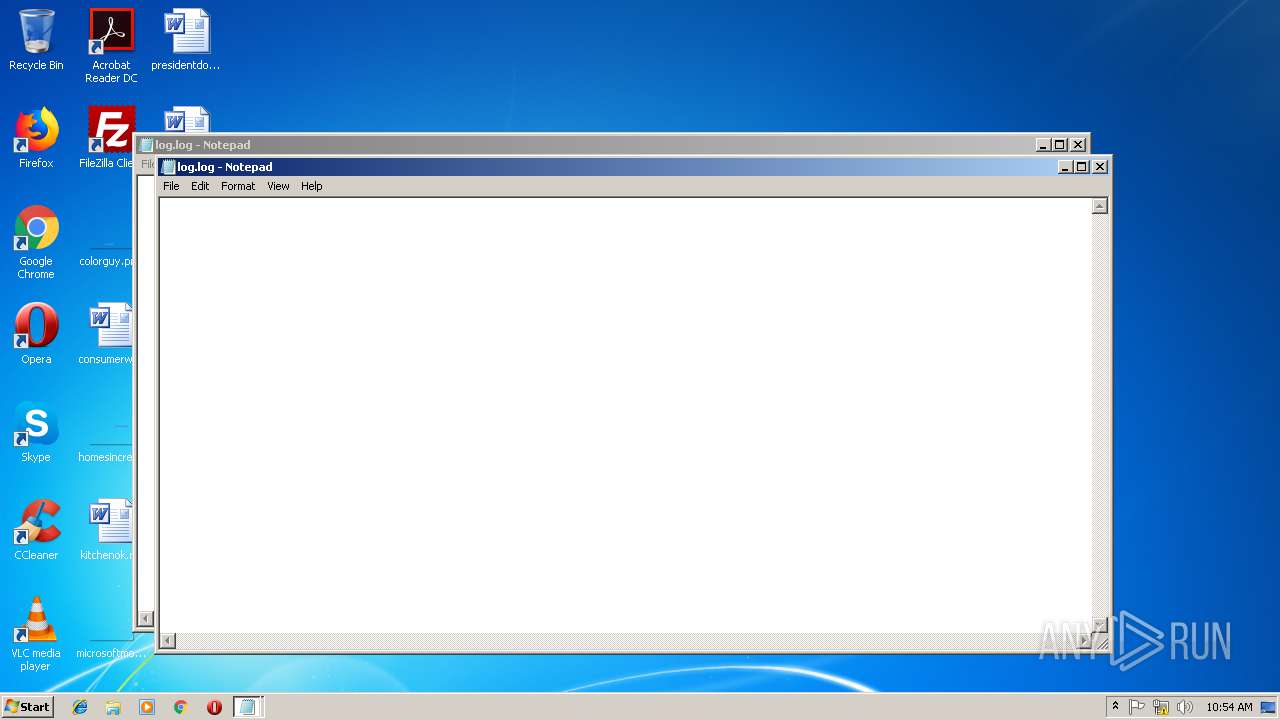
| 700 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\log.log | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | "C:\Users\admin\AppData\Local\Temp\990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe" | C:\Users\admin\AppData\Local\Temp\990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | explorer.exe | ||||||||||||
User: admin Company: 逍遥一仙 Integrity Level: MEDIUM Description: 逍遥一仙 Exit code: 0 Version: 1.1.1.1 Modules
| |||||||||||||||
| 3176 | "C:\Users\admin\AppData\Local\Temp\990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe" | C:\Users\admin\AppData\Local\Temp\990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | explorer.exe | ||||||||||||
User: admin Company: 逍遥一仙 Integrity Level: MEDIUM Description: 逍遥一仙 Exit code: 0 Version: 1.1.1.1 Modules
| |||||||||||||||
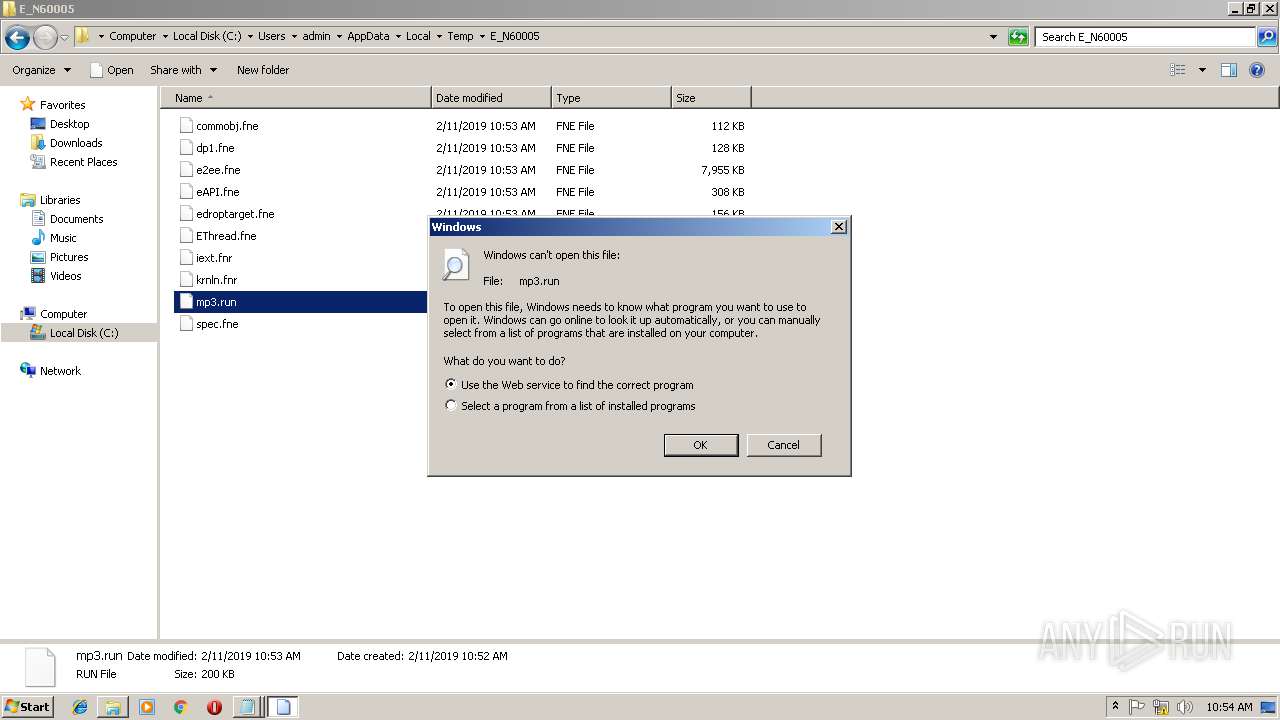
| 3180 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\E_N60005\mp3.run | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3384 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\log.log | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3520 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
72
Read events
64
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3384) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 154 | |||
| (PID) Process: | (3384) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 154 | |||
| (PID) Process: | (3384) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (3384) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (700) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 132 | |||
| (PID) Process: | (700) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 132 | |||
| (PID) Process: | (700) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (700) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
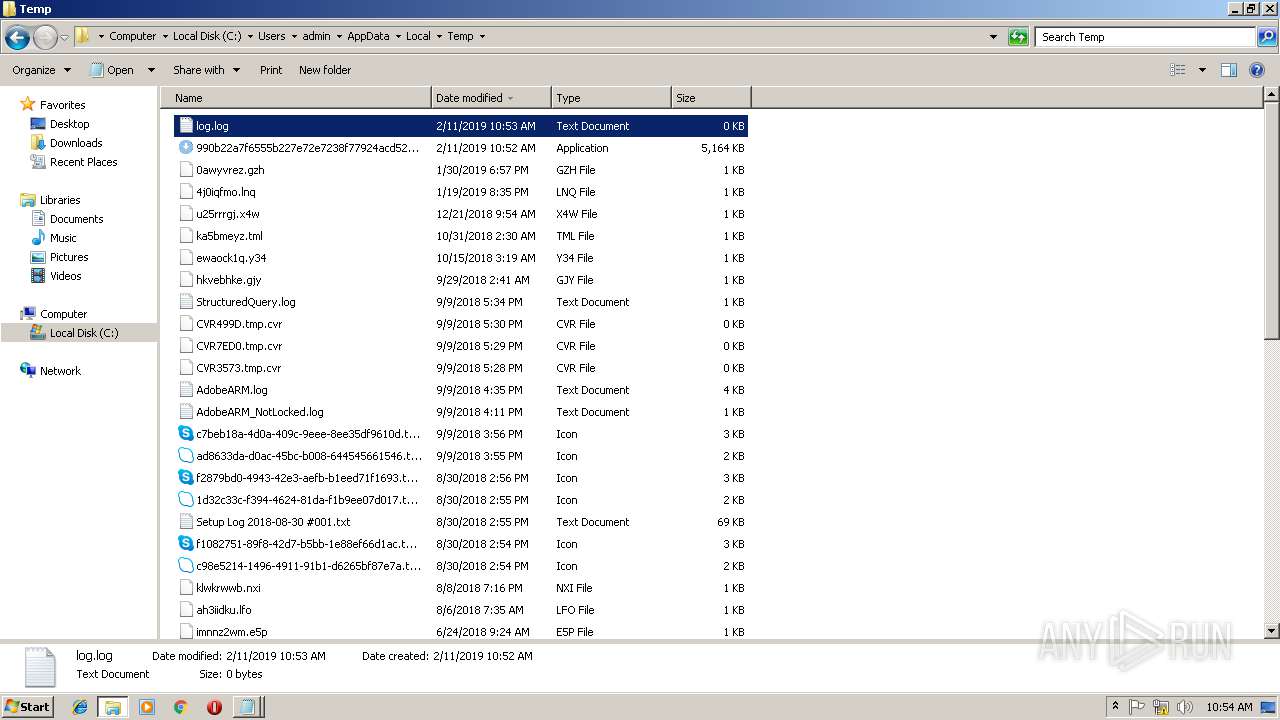
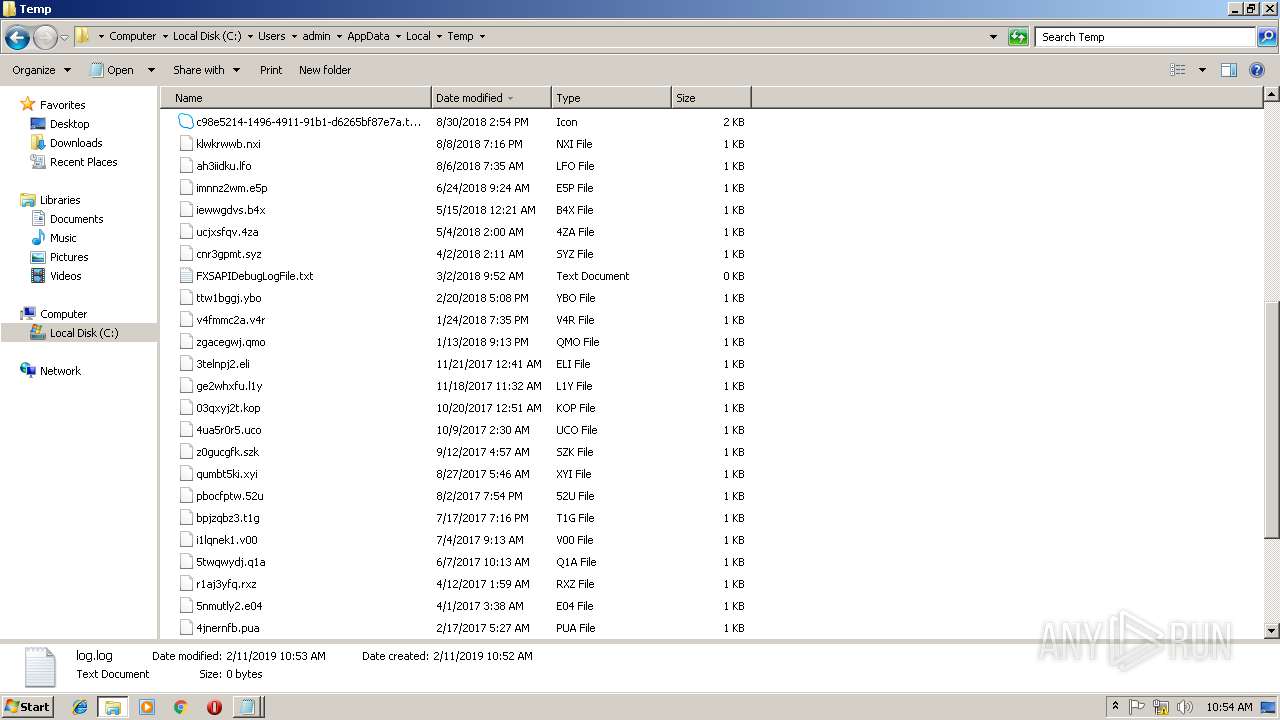
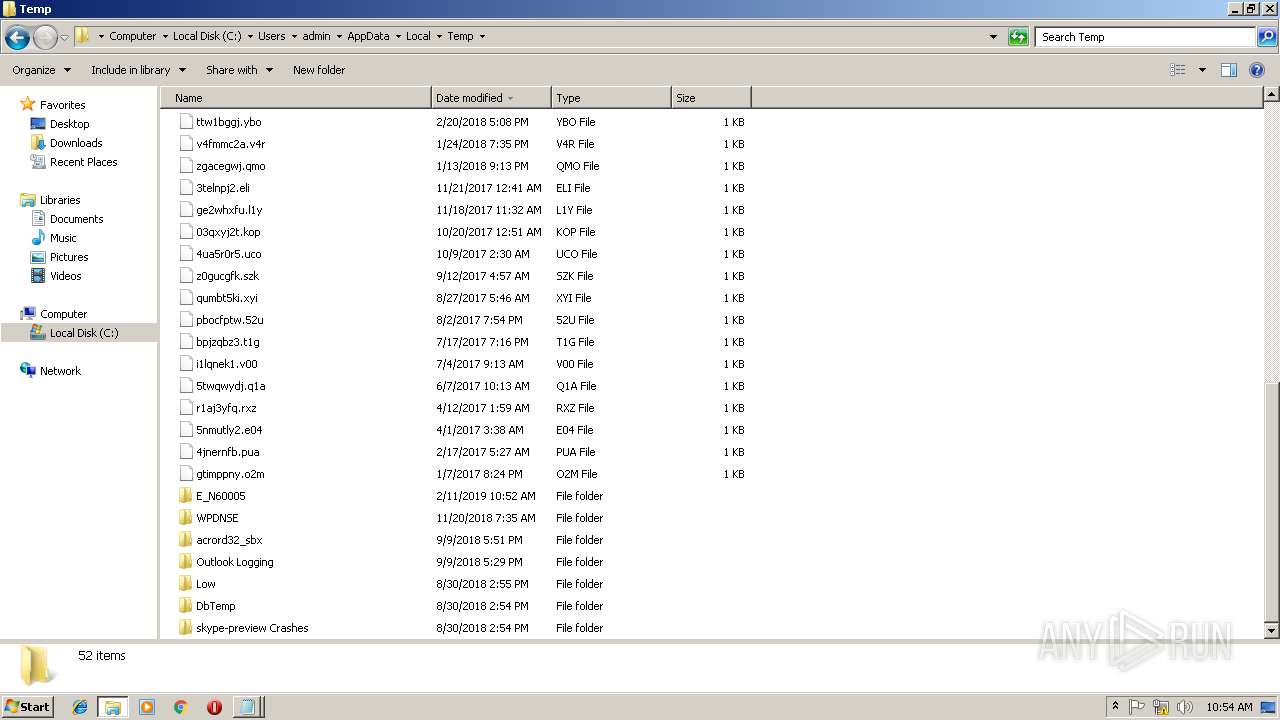
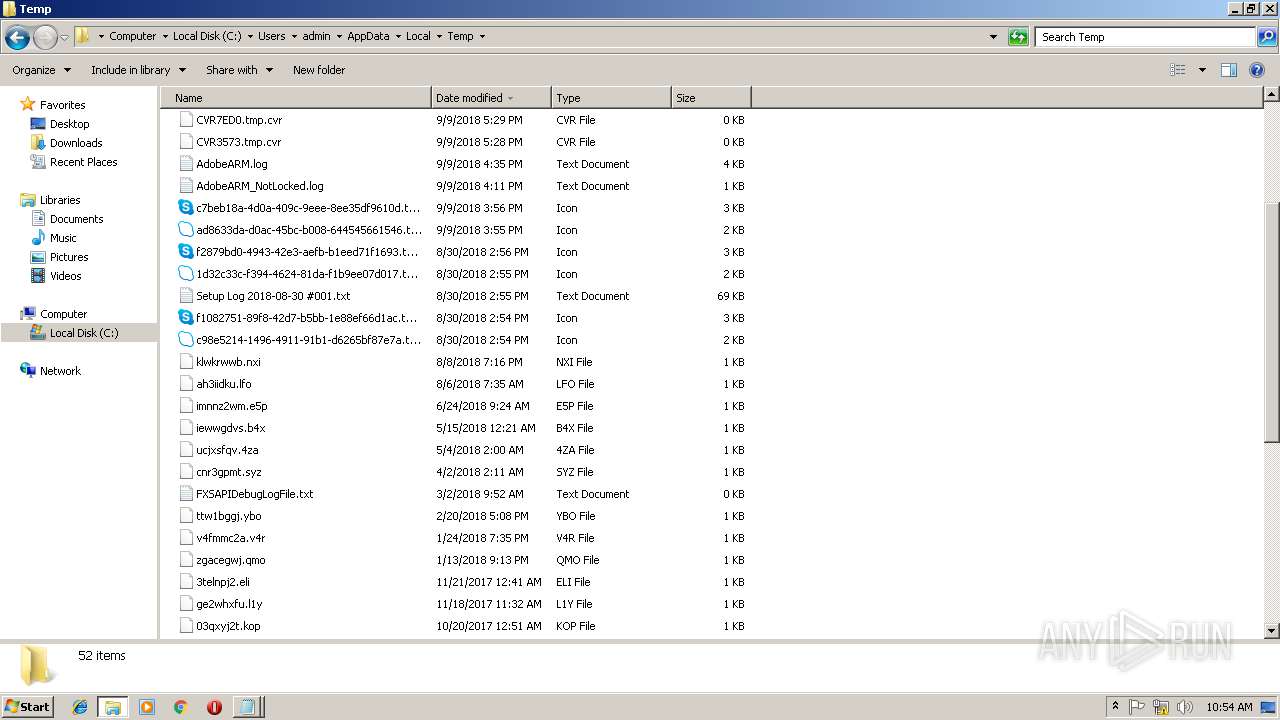
Executable files
20
Suspicious files
0
Text files
0
Unknown types
0
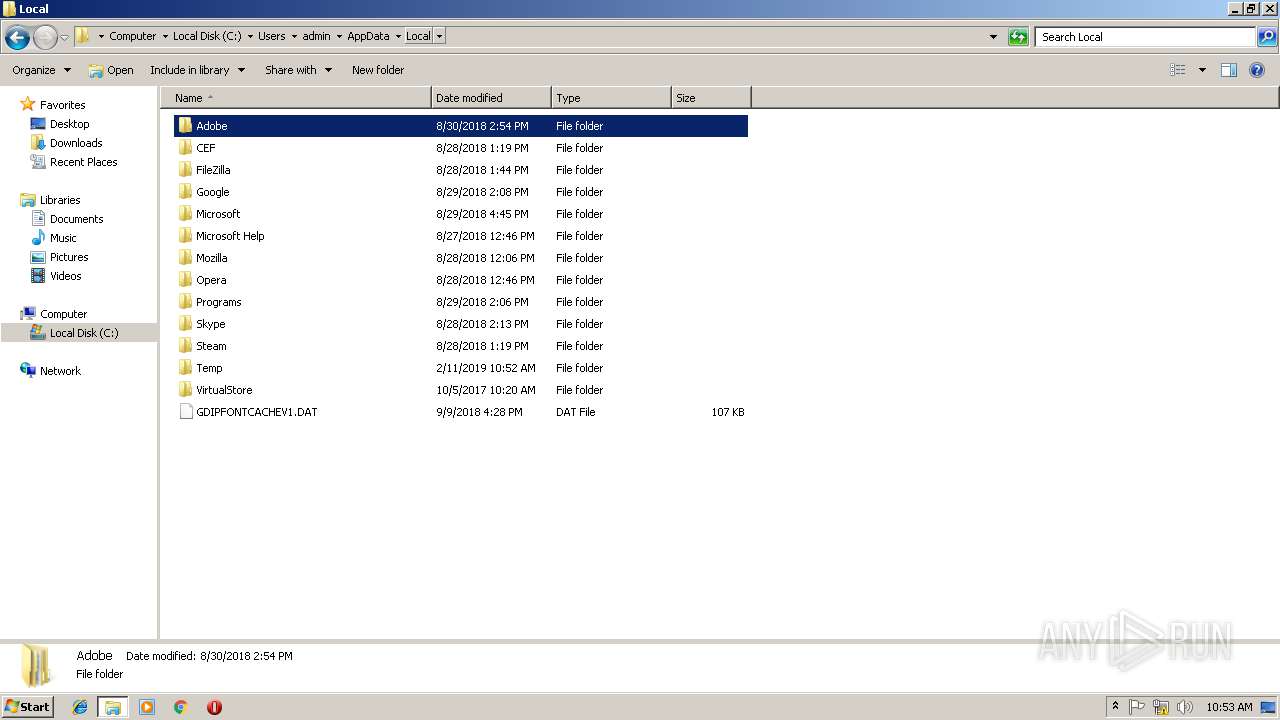
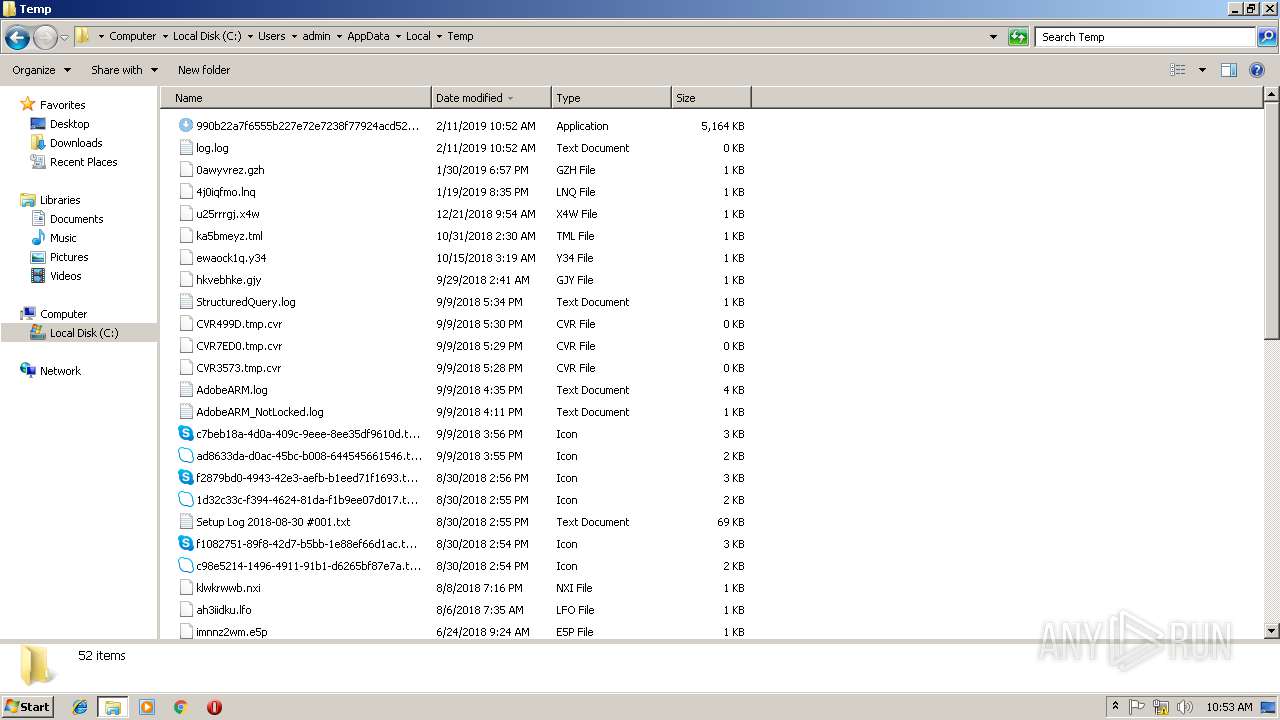
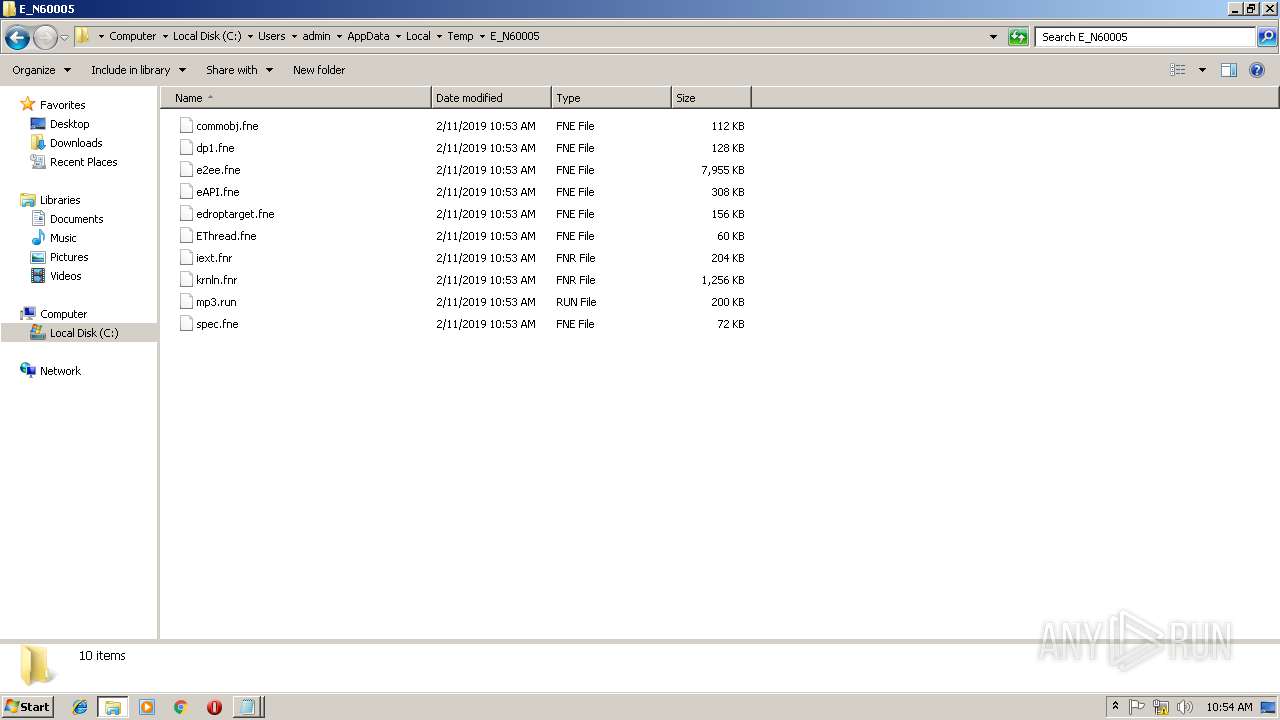
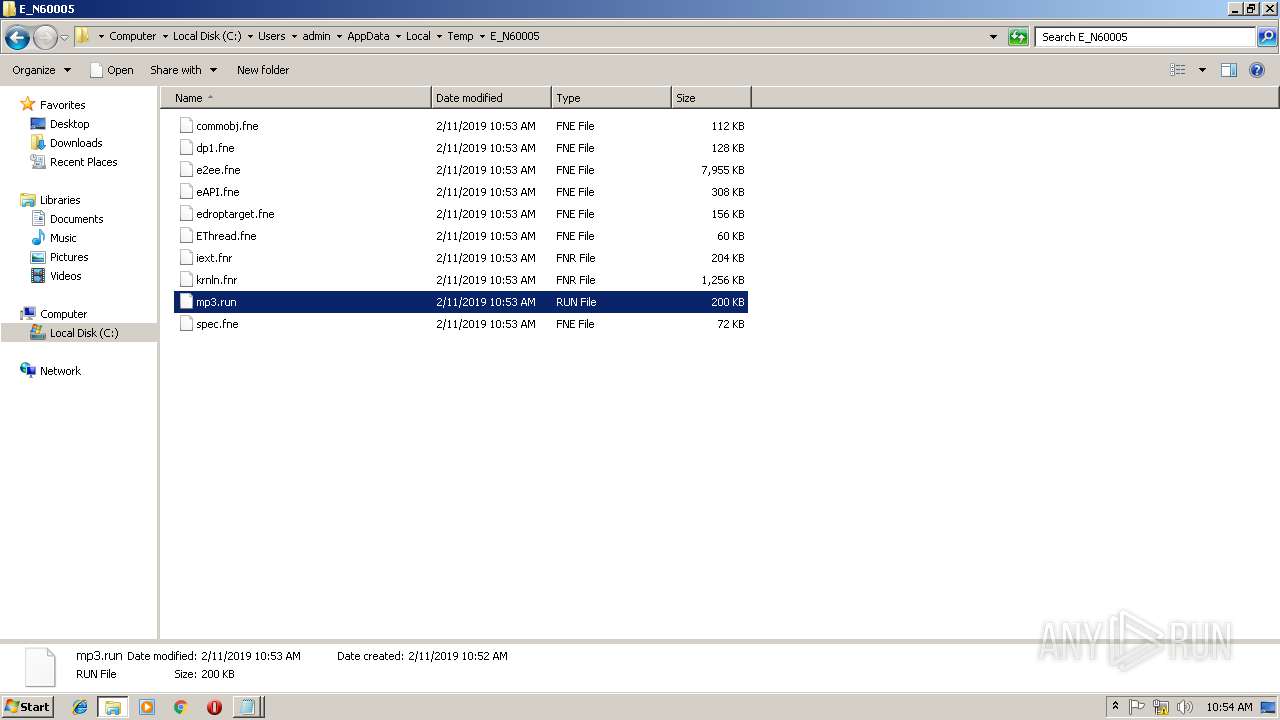
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
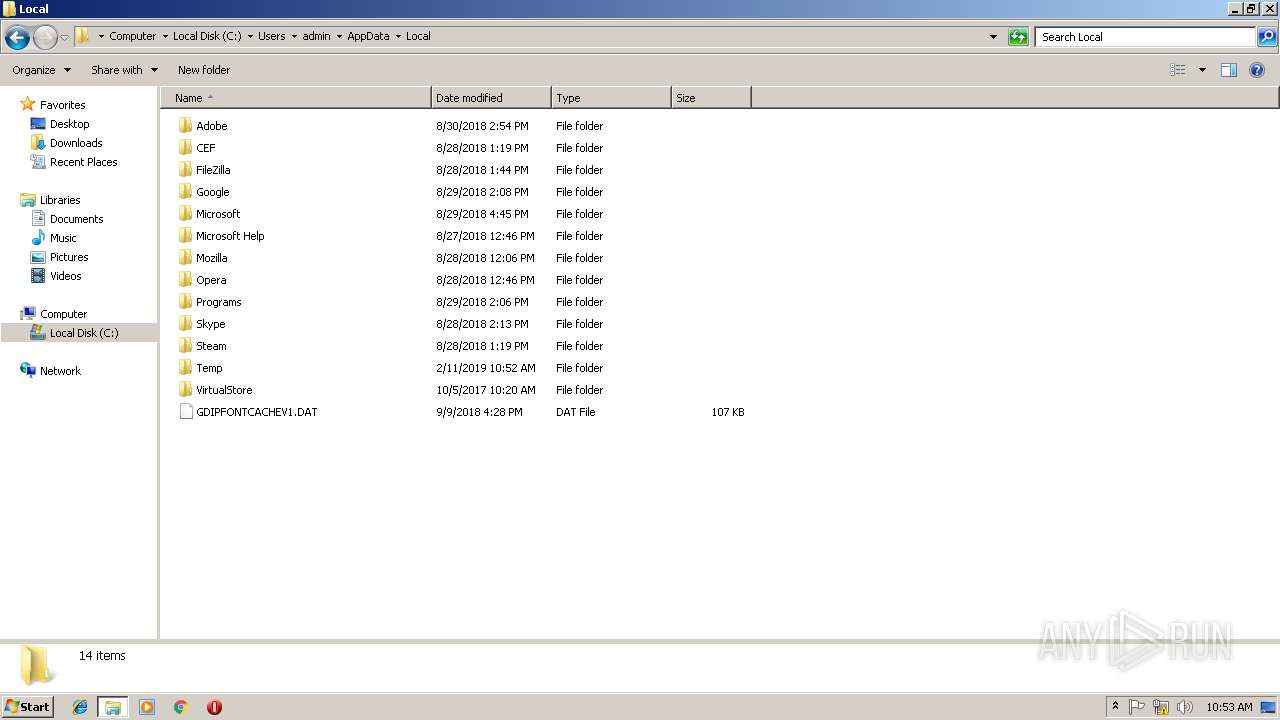
| 2804 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\e2ee.fne | executable | |
MD5:— | SHA256:— | |||
| 3176 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\e2ee.fne | executable | |
MD5:— | SHA256:— | |||
| 3176 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\iext.fnr | executable | |
MD5:856495A1605BFC7F62086D482B502C6F | SHA256:8C8254CB49F7287B97C7F952C81EDABC9F11F3FA3F02F265E67D5741998CF0BF | |||
| 3176 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\commobj.fne | executable | |
MD5:2B86AD8CD1903916AE5A3CD7EC2F1B9E | SHA256:590C9BA4CAD5A401C071F89F8468C45031A637F1C137CA320D9DBE82E4BEABD6 | |||
| 2804 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\EThread.fne | executable | |
MD5:206396257B97BD275A90CE6C2C0C37FD | SHA256:64EEF86745D7AE0168FEC357099E2E952CE74EE19576D06CC8C8C65F210CC22C | |||
| 3176 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\eAPI.fne | executable | |
MD5:7C1FF88991F5EAFAB82B1BEAEFC33A42 | SHA256:53483523C316AD8C022C2B07A5CABFFF3339BC5CB5E4AC24C3260EEA4F4D9731 | |||
| 3176 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\mp3.run | executable | |
MD5:AA877EF4D7D30B733C275C8D9B5A5588 | SHA256:D2D991A129A2D37C8C5F3DF7A593328450C34608EF036697FC800115120E6C60 | |||
| 3176 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\spec.fne | executable | |
MD5:BD6EEF5EA9A52A412A8F57490D8BD8E4 | SHA256:0C9E6EB8648F4BF5C585D5344035E91C3249BB9686A302503B4681B7BA828DC0 | |||
| 2804 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\edroptarget.fne | executable | |
MD5:CA77AEC89BD2F81BBEF77FF26B88148A | SHA256:1EAF42E6C734EB332F0EDF7D3CF7C408F72B3267AE5408675D3604A6B23319D2 | |||
| 2804 | 990b22a7f6555b227e72e7238f77924acd52d1b08a6b395fbc24e8b9c6ef6baf.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\iext.fnr | executable | |
MD5:856495A1605BFC7F62086D482B502C6F | SHA256:8C8254CB49F7287B97C7F952C81EDABC9F11F3FA3F02F265E67D5741998CF0BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report