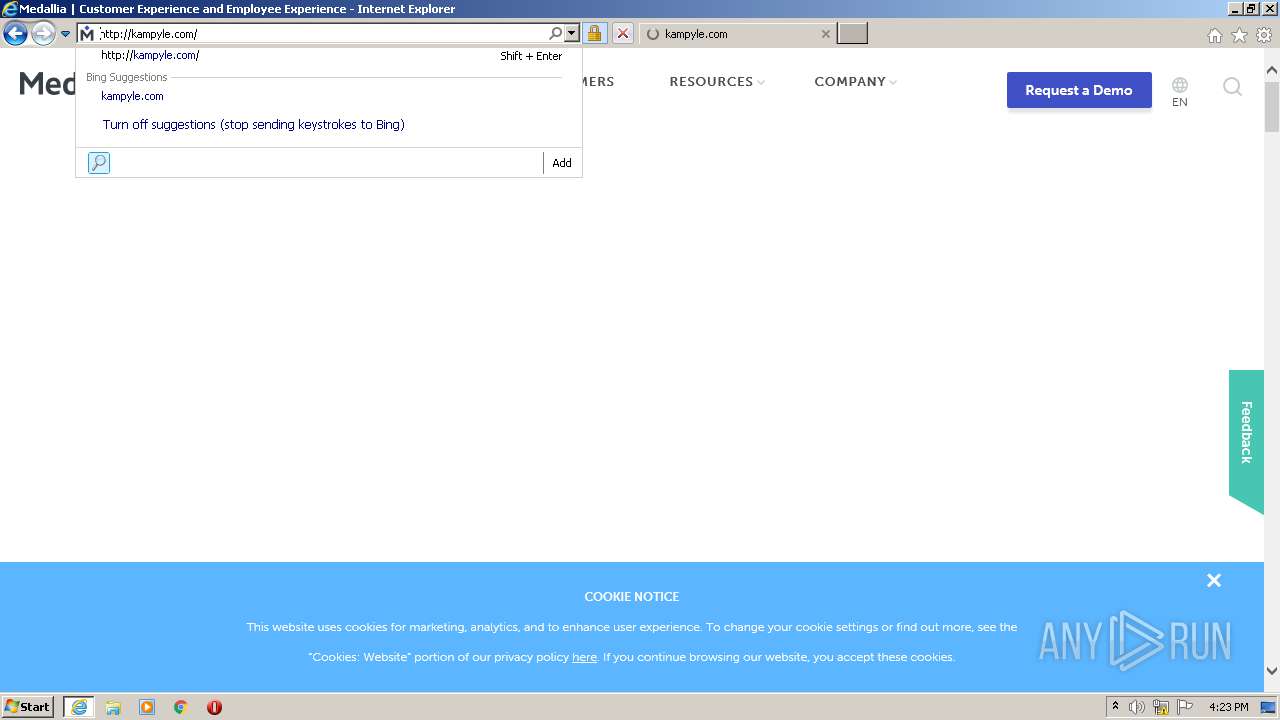
| URL: | http://nebula-cdn.kampyle.com |
| Full analysis: | https://app.any.run/tasks/614e28b9-89d7-41e0-9bac-322bb3d85677 |
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2020, 16:21:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6F228AF04E2D14B3368D82203CAB1F36 |
| SHA1: | 40017F35CD6A6C87542013B789C7BACC0BC9088B |
| SHA256: | 990AE8CA2285B61F2D623E71B0547021D7291ED5CCDCAB9CD4D66A8DE2512ABA |
| SSDEEP: | 3:N1KQi7k2n:CQG9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- iexplore.exe (PID: 184)
- iexplore.exe (PID: 992)
Application launched itself
- iexplore.exe (PID: 992)
Changes settings of System certificates
- iexplore.exe (PID: 992)
Adds / modifies Windows certificates
- iexplore.exe (PID: 992)
Reads settings of System Certificates
- iexplore.exe (PID: 992)
- iexplore.exe (PID: 184)
Reads Internet Cache Settings
- iexplore.exe (PID: 992)
- iexplore.exe (PID: 184)
Changes internet zones settings
- iexplore.exe (PID: 992)
Reads internet explorer settings
- iexplore.exe (PID: 184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:992 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://nebula-cdn.kampyle.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
734
Read events
531
Write events
200
Delete events
3
Modification events
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2360718168 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30848692 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
176
Text files
180
Unknown types
85
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 992 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\AYKO8M88.txt | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3S494YUU.txt | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SMETRZ0B.txt | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\B0XM6CZU.txt | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XDH9DCTI.txt | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\I3ETZZLP.txt | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\46DGJ8AQ.txt | — | |
MD5:— | SHA256:— | |||
| 184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\9T40O778.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
105
TCP/UDP connections
175
DNS requests
84
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
184 | iexplore.exe | GET | 302 | 96.45.83.231:80 | http://kampyle.com/ | US | — | — | whitelisted |
184 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=kampyle.com%2F&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 226 b | whitelisted |
184 | iexplore.exe | GET | 200 | 52.201.188.11:80 | http://ocsps.ssl.com/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBQMDtATfnJO6JAXDQoHl8pAaJdhTQQU3QQJB6L1en1SUxKSle44gCUNplkCCAmX7RCdHwf8 | US | der | 1.86 Kb | whitelisted |
184 | iexplore.exe | GET | 200 | 52.201.188.11:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTUkpS%2BK0oZhSMx%2FmmCZ76UqdjUxQQUJhR%2B4NzXpvfi1AQn32HxwuznMsoCEAYvzmeb5lTPQHW37Uvs1mU%3D | US | der | 1.86 Kb | whitelisted |
184 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=kampyle.com%2F&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 226 b | whitelisted |
184 | iexplore.exe | GET | 200 | 184.86.103.216:80 | http://sslcom.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkJwSV9oyR1tDse0lOpN8c | US | der | 1.63 Kb | whitelisted |
184 | iexplore.exe | GET | 200 | 52.201.188.11:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTUkpS%2BK0oZhSMx%2FmmCZ76UqdjUxQQUJhR%2B4NzXpvfi1AQn32HxwuznMsoCEAYvzmeb5lTPQHW37Uvs1mU%3D | US | der | 1.86 Kb | whitelisted |
184 | iexplore.exe | GET | 200 | 184.86.103.198:80 | http://sslcom.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkJwSV9oyR1tDse0lOpN8c | US | der | 1.63 Kb | whitelisted |
184 | iexplore.exe | GET | 200 | 52.201.188.11:80 | http://ocsps.ssl.com/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBQMDtATfnJO6JAXDQoHl8pAaJdhTQQU3QQJB6L1en1SUxKSle44gCUNplkCCAmX7RCdHwf8 | US | der | 1.86 Kb | whitelisted |
184 | iexplore.exe | GET | 200 | 23.55.163.48:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgTFHhFFwLNPxLT1l%2FDa1OEwmQ%3D%3D | US | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
184 | iexplore.exe | 151.101.1.175:80 | nebula-cdn.kampyle.com | Fastly | US | unknown |
992 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
184 | iexplore.exe | 13.107.13.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
184 | iexplore.exe | 96.45.83.231:80 | kampyle.com | Tiggee LLC | US | unknown |
184 | iexplore.exe | 52.11.183.46:443 | medallia.com | Amazon.com, Inc. | US | unknown |
184 | iexplore.exe | 184.86.103.198:80 | sslcom.ocsp-certum.com | Akamai Technologies, Inc. | US | suspicious |
184 | iexplore.exe | 141.193.213.21:443 | www.medallia.com | — | ES | whitelisted |
184 | iexplore.exe | 52.201.188.11:80 | ocsps.ssl.com | Amazon.com, Inc. | US | unknown |
184 | iexplore.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
184 | iexplore.exe | 23.55.163.48:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nebula-cdn.kampyle.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
kampyle.com |
| whitelisted |
medallia.com |
| whitelisted |
sslcom.ocsp-certum.com |
| whitelisted |
ocsps.ssl.com |
| whitelisted |
www.medallia.com |
| malicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |