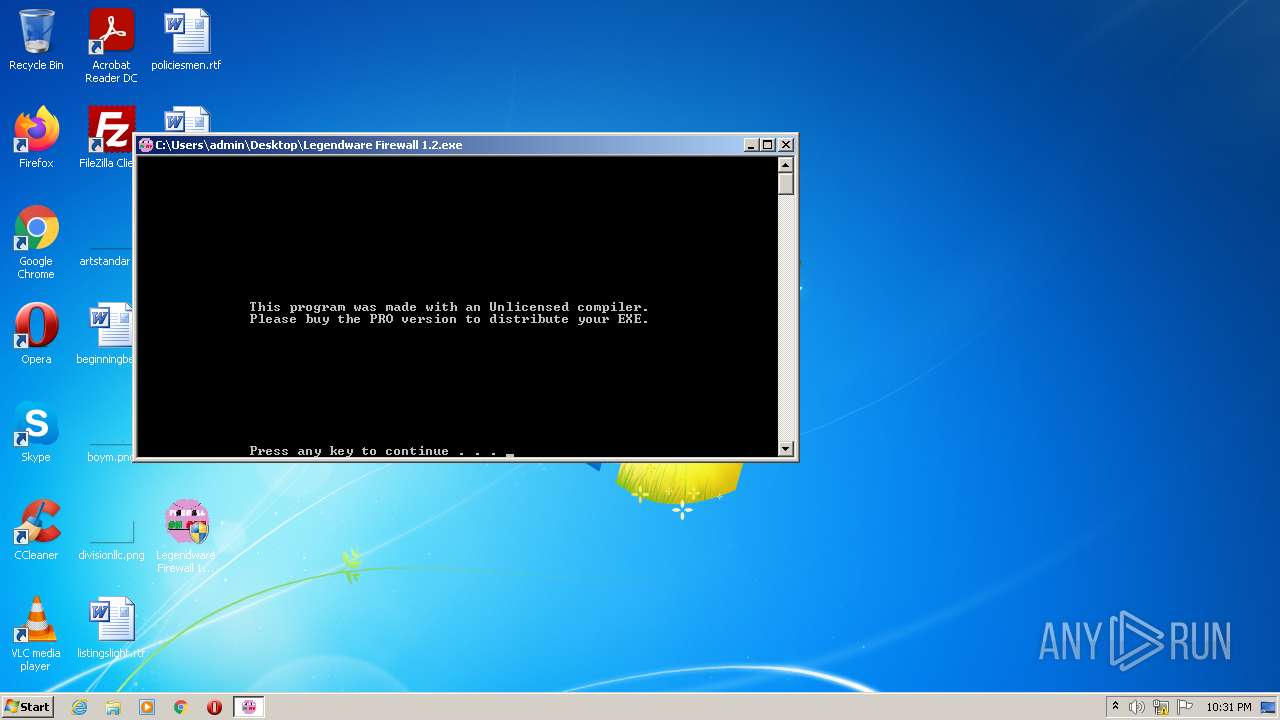
| File name: | Legendware Firewall 1.2.exe |
| Full analysis: | https://app.any.run/tasks/eee4e6f0-6fbb-4026-8caf-828c1773d0b8 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2022, 22:31:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | C0C222E33E1FB94A0A95CA1864B47031 |
| SHA1: | E4A776A247994CF3583EB18A13C4C31AB0AAAC02 |
| SHA256: | 98FAD08E81D3846D6836141D9BC4DC29BEBFFD8ABE25315946D6C826F19B34DB |
| SSDEEP: | 1536:s6nKl2yk5Ca9GBj++0z0oNEs3tlmBd/JfafE/opRyCBw:s6ek4a9X+0z9ERdhyfE/orf+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 2788)
- Legendware Firewall 1.2.exe (PID: 2484)
- cmd.exe (PID: 2864)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 1464)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 2840)
- cmd.exe (PID: 4064)
- cmd.exe (PID: 3152)
Starts CMD.EXE for commands execution
- Legendware Firewall 1.2.exe (PID: 2484)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2600)
INFO
Checks supported languages
- attrib.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductName: | Firewall On-Off |
|---|---|
| LegalCopyright: | Copyright 18-8-2020 |
| CompanyName: | Zuhu.Inc |
| FileDescription: | Turns your filewall on and off |
| ProductVersion: | 1.2.1.1 |
| FileVersion: | 1.2.1.1 |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.2.1.1 |
| FileVersionNumber: | 1.2.1.1 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x8b56 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 81920 |
| CodeSize: | 61440 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2017:01:08 19:34:33+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 08-Jan-2017 18:34:33 |
| Detected languages: |
|
| FileVersion: | 1.2.1.1 |
| ProductVersion: | 1.2.1.1 |
| FileDescription: | Turns your filewall on and off |
| CompanyName: | Zuhu.Inc |
| LegalCopyright: | Copyright 18-8-2020 |
| ProductName: | Firewall On-Off |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 08-Jan-2017 18:34:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000E6F6 | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31469 |
.rdata | 0x00010000 | 0x00000B84 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43191 |
.data | 0x00011000 | 0x00B00F98 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.55327 |
.rsrc | 0x00B12000 | 0x00010EF0 | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.40896 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99409 | 786 | Latin 1 / Western European | English - United States | RT_MANIFEST |
102 | 2.39546 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WINMM.dll |
Total processes
49
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1464 | C:\Windows\system32\cmd.exe /c echo:0>C:\Users\admin\AppData\Local\Temp\is64.txt | C:\Windows\system32\cmd.exe | — | Legendware Firewall 1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\Desktop\Legendware Firewall 1.2.exe" | C:\Users\admin\Desktop\Legendware Firewall 1.2.exe | Explorer.EXE | ||||||||||||
User: admin Company: Zuhu.Inc Integrity Level: HIGH Description: Turns your filewall on and off Exit code: 1 Version: 1.2.1.1 Modules
| |||||||||||||||
| 2600 | C:\Windows\system32\cmd.exe /c attrib +h C:\Users\admin\AppData\Local\Temp\xtmp | C:\Windows\system32\cmd.exe | — | Legendware Firewall 1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2788 | C:\Windows\system32\cmd.exe /c if not exist "C:\Users\admin\AppData\Local\Temp\efolder" mkdir "C:\Users\admin\AppData\Local\Temp\efolder" | C:\Windows\system32\cmd.exe | — | Legendware Firewall 1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2796 | attrib +h C:\Users\admin\AppData\Local\Temp\xtmp | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\is64.bat | C:\Windows\system32\cmd.exe | — | Legendware Firewall 1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2864 | C:\Windows\system32\cmd.exe /c if not exist "C:\Users\admin\AppData\Local\Temp\xtmp" mkdir "C:\Users\admin\AppData\Local\Temp\xtmp" | C:\Windows\system32\cmd.exe | — | Legendware Firewall 1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2976 | C:\Windows\system32\cmd.exe /c | C:\Windows\system32\cmd.exe | — | Legendware Firewall 1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3152 | C:\Windows\system32\cmd.exe /c pause | C:\Windows\system32\cmd.exe | — | Legendware Firewall 1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\Desktop\Legendware Firewall 1.2.exe" | C:\Users\admin\Desktop\Legendware Firewall 1.2.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Zuhu.Inc Integrity Level: MEDIUM Description: Turns your filewall on and off Exit code: 3221226540 Version: 1.2.1.1 Modules
| |||||||||||||||
Total events
138
Read events
138
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1464 | cmd.exe | C:\Users\admin\AppData\Local\Temp\is64.txt | text | |
MD5:21438EF4B9AD4FC266B6129A2F60DE29 | SHA256:13BF7B3039C63BF5A50491FA3CFD8EB4E699D1BA1436315AEF9CBE5711530354 | |||
| 2484 | Legendware Firewall 1.2.exe | C:\Users\admin\AppData\Local\Temp\is64.bat | text | |
MD5:3CCDA7F84CE40901DECC54FA4C378B65 | SHA256:1414F69F5A7123543FFAA21CAB949B359DBA46741EAB3A5DCC9E57DA912B100E | |||
| 2840 | cmd.exe | C:\Users\admin\AppData\Local\Temp\is64.fil | text | |
MD5:D406619E40F52369E12AE4671B16A11A | SHA256:2E340D2B9CED6AD419C031400FB974FEED427CFABD0C167DEA26EC732D8579BE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report