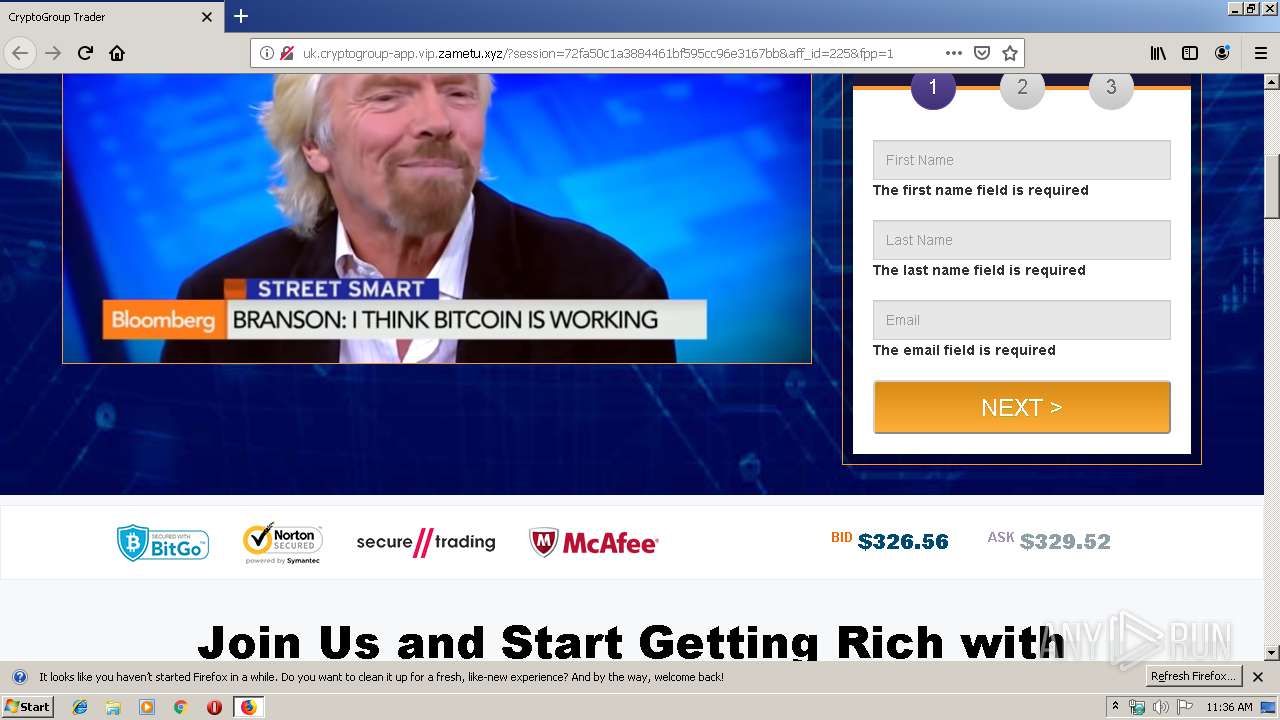
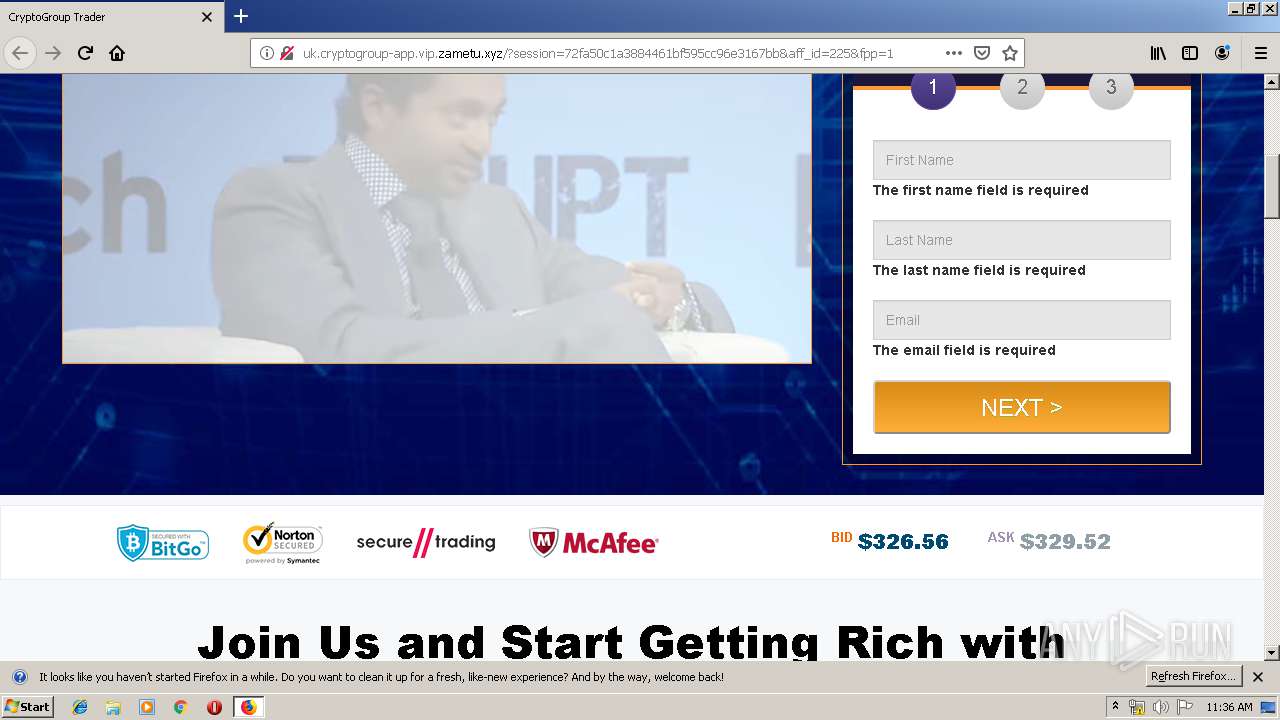
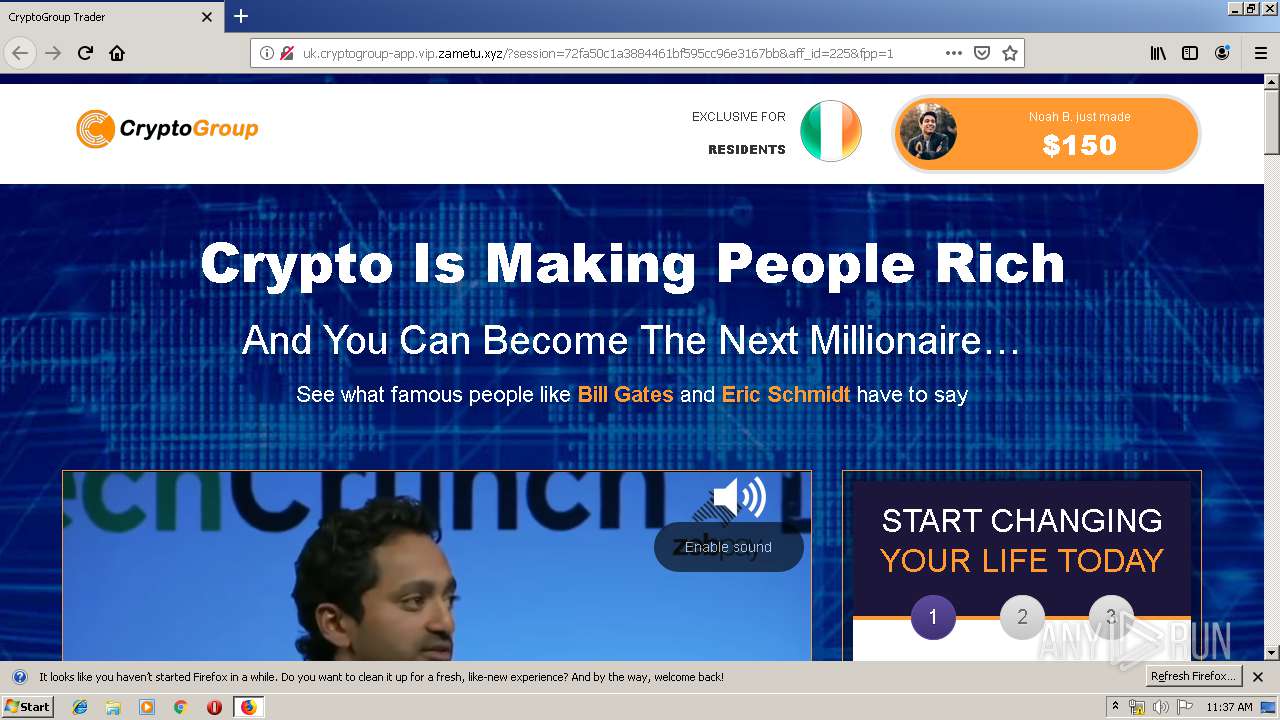
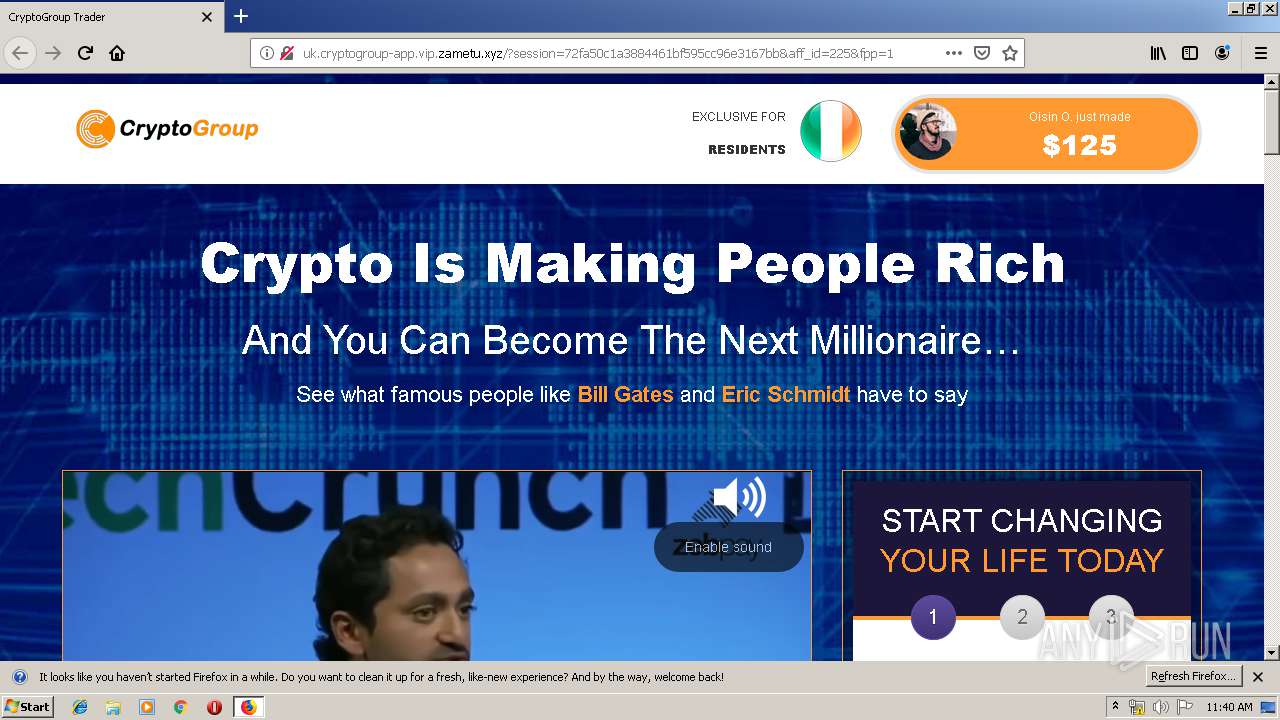
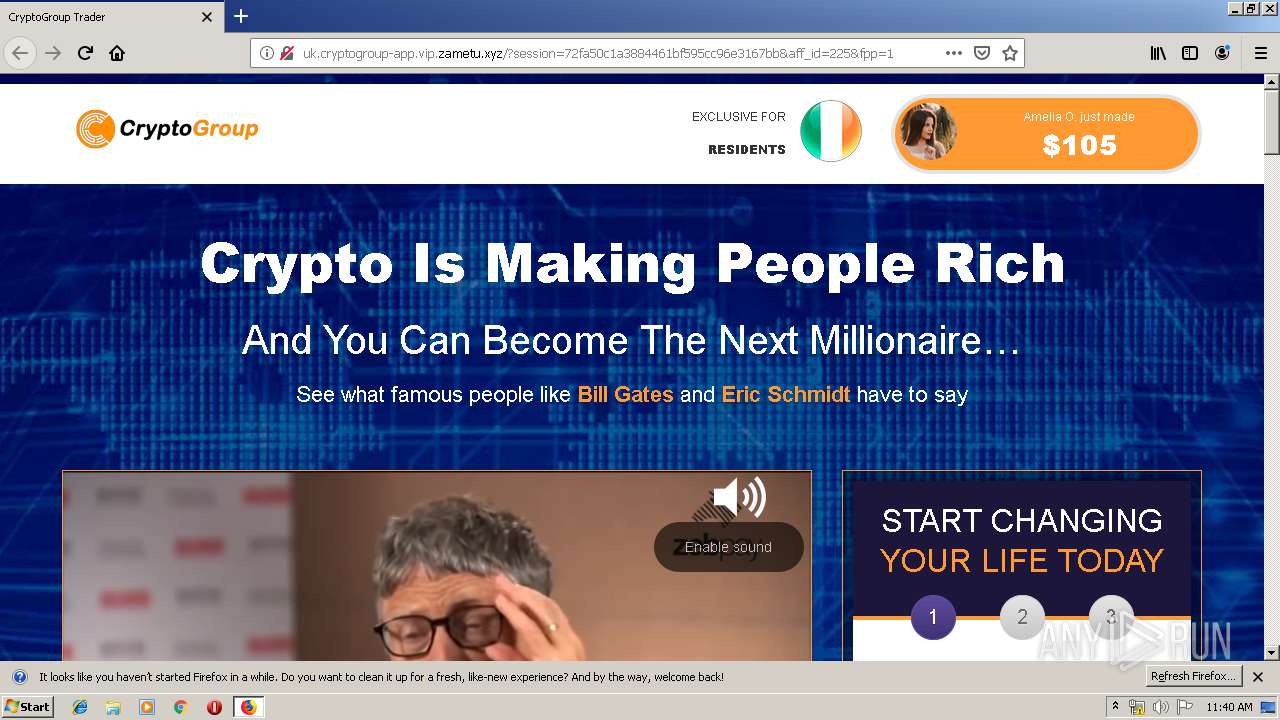
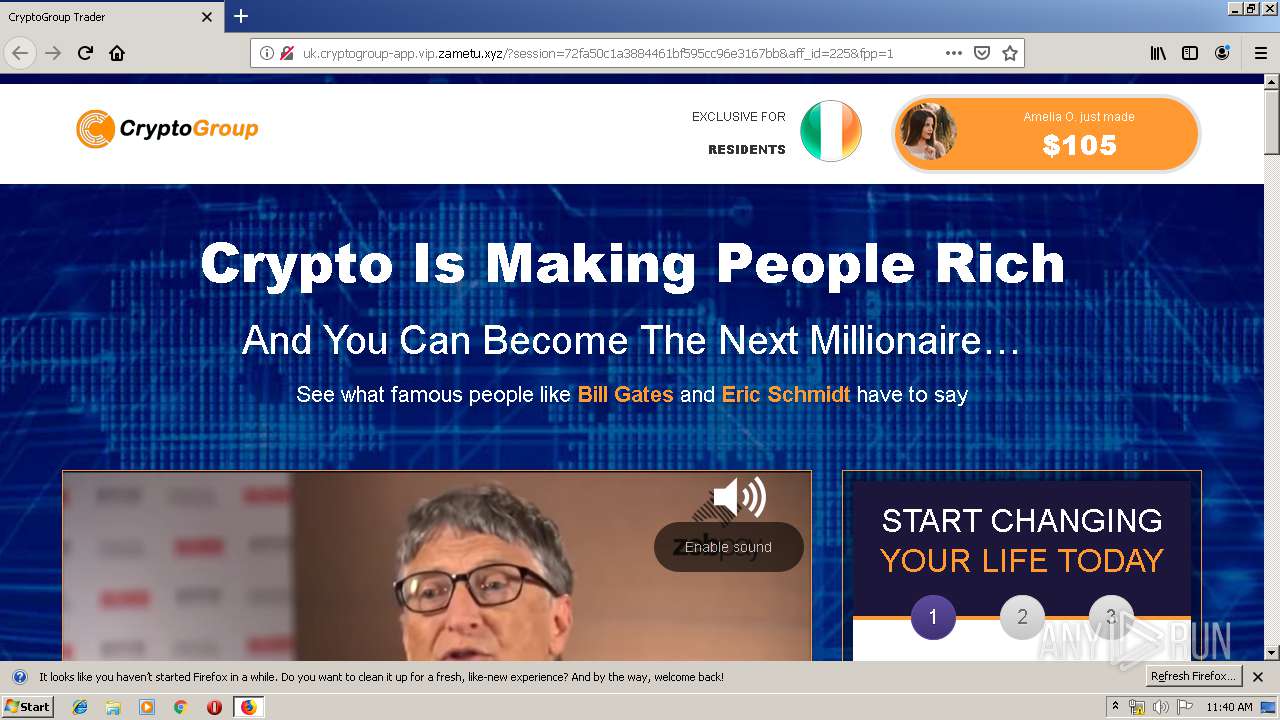
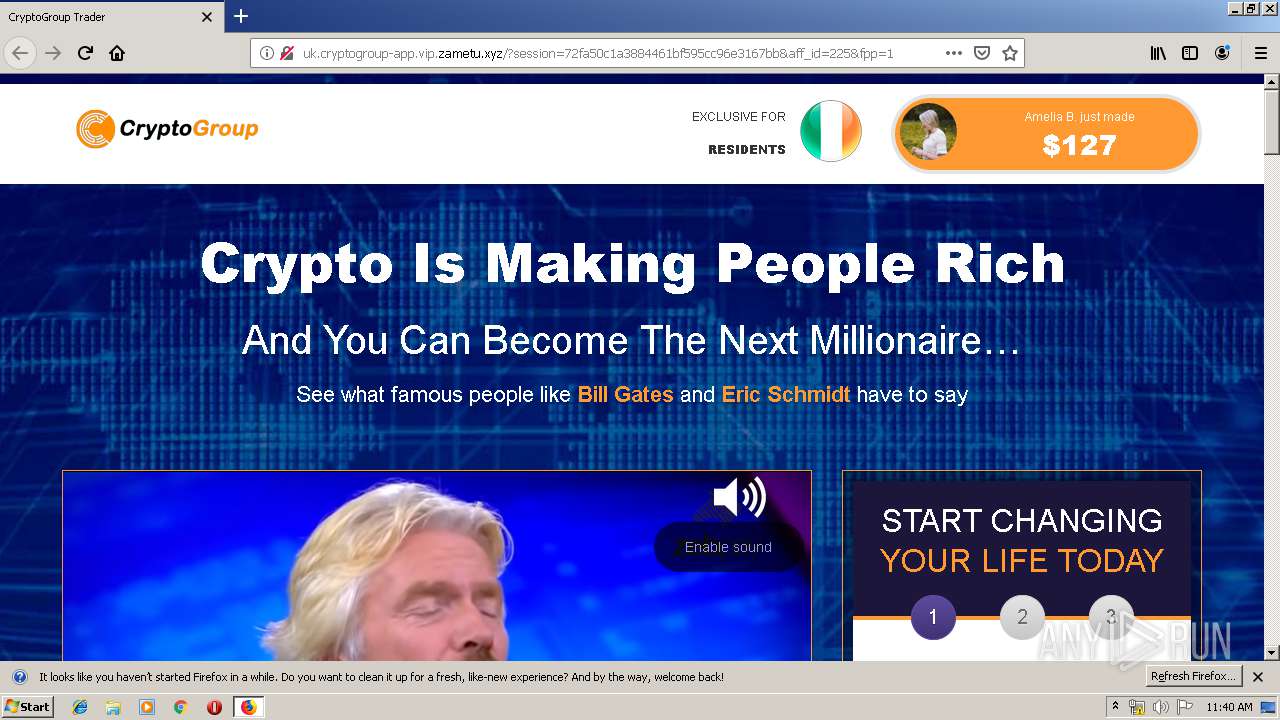
| URL: | https://presorwamma1978.blogspot.ie/ |
| Full analysis: | https://app.any.run/tasks/ff063fa8-c9bd-49b9-a5ca-ff0825bb9ddc |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 10:35:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 702C169351C783B1BC8D5E4F5D79830E |
| SHA1: | 0AF13EBCF32F8303C4452BF4182C2D4D6C575436 |
| SHA256: | 98ECA0EEC6AAD046F2BD72B3AC534CFCF39F3CBAB08CABE9B740D5547FFDB67C |
| SSDEEP: | 3:N8TAZVXzBKn:2wj8n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- firefox.exe (PID: 3024)
INFO
Application launched itself
- firefox.exe (PID: 3024)
Reads CPU info
- firefox.exe (PID: 3024)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3024)
Reads settings of System Certificates
- firefox.exe (PID: 3024)
Creates files in the user directory
- firefox.exe (PID: 3024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3024.20.1765771499\1689676507" -childID 3 -isForBrowser -prefsHandle 2680 -prefMapHandle 3520 -prefsLen 6720 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3024 "\\.\pipe\gecko-crash-server-pipe.3024" 2864 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://presorwamma1978.blogspot.ie/" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3024.3.1004813123\910900586" -childID 1 -isForBrowser -prefsHandle 1564 -prefMapHandle 1696 -prefsLen 1 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3024 "\\.\pipe\gecko-crash-server-pipe.3024" 1568 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 3832 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3024.0.835438062\1946379323" -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3024 "\\.\pipe\gecko-crash-server-pipe.3024" 1172 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 3924 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3024.13.1502426773\493453740" -childID 2 -isForBrowser -prefsHandle 2556 -prefMapHandle 2560 -prefsLen 5842 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3024 "\\.\pipe\gecko-crash-server-pipe.3024" 2576 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
Total events
573
Read events
560
Write events
13
Delete events
0
Modification events
| (PID) Process: | (3024) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (3024) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3024) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3024) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
377
Text files
117
Unknown types
81
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\pluginreg.dat.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flash-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3024 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashallow-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
101
DNS requests
139
Threats
57
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
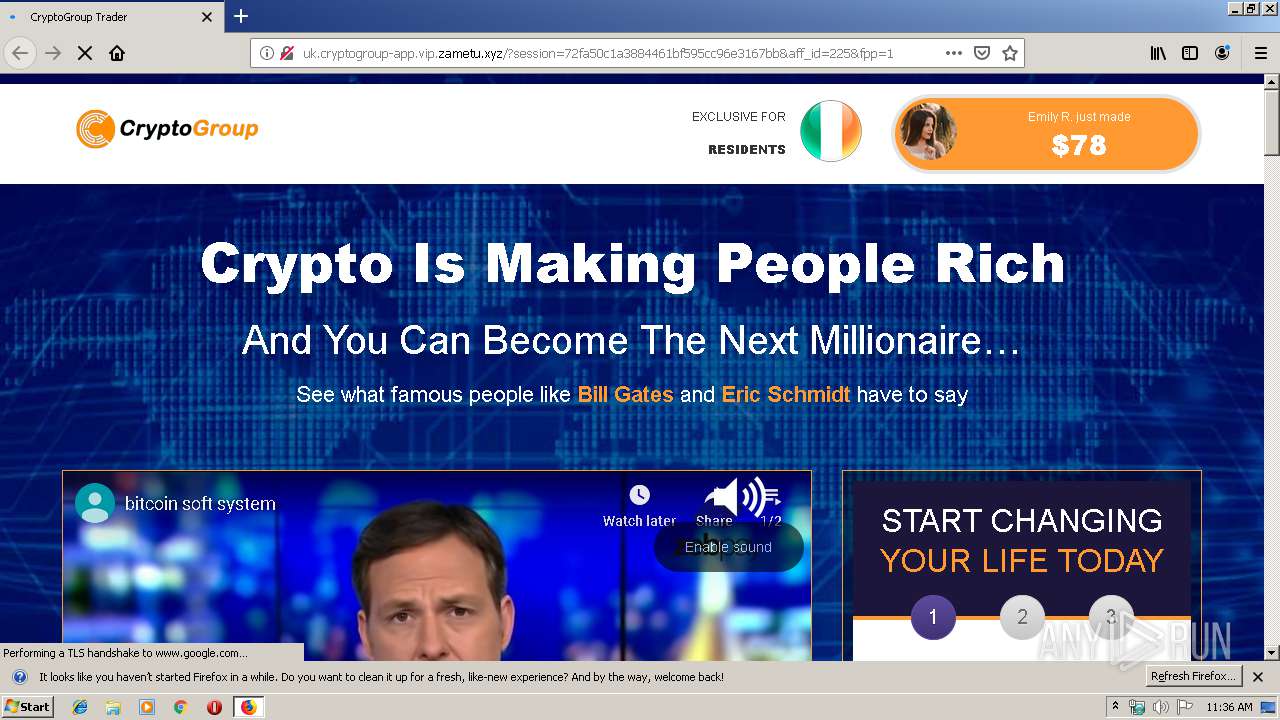
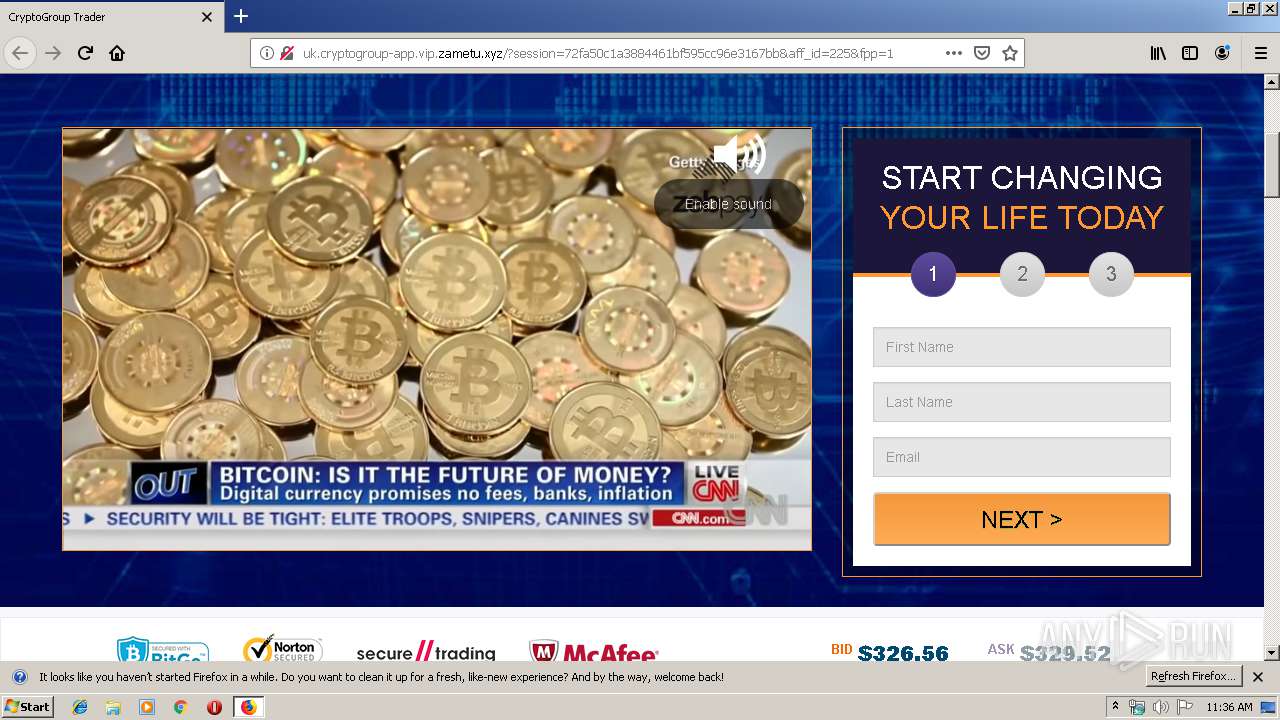
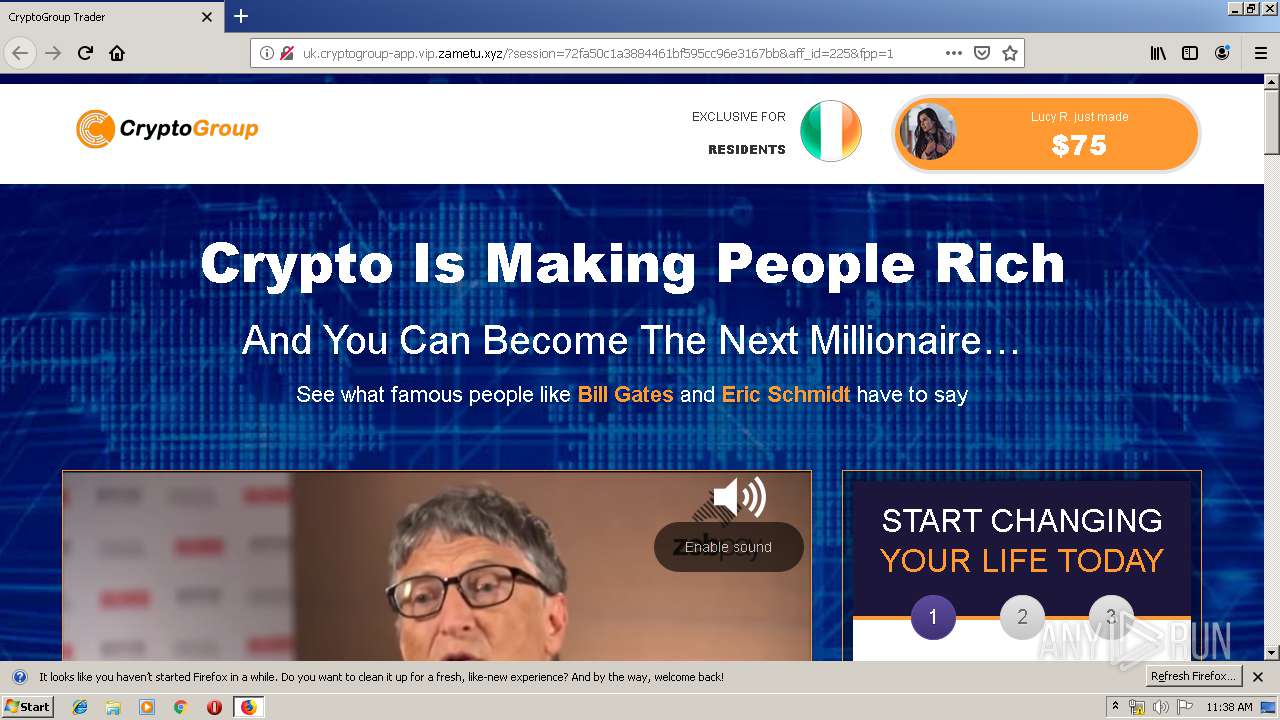
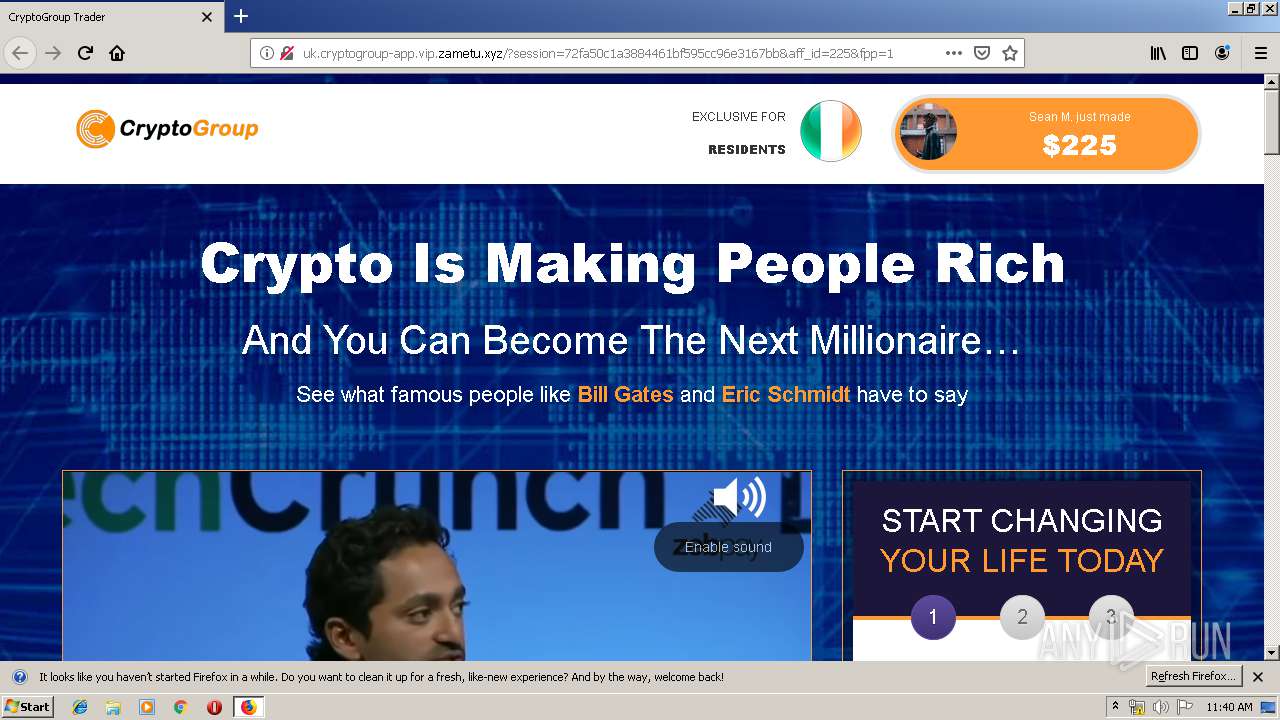
3024 | firefox.exe | GET | — | 130.193.35.172:80 | http://webfinansoz.top/und14.html | RU | — | — | suspicious |
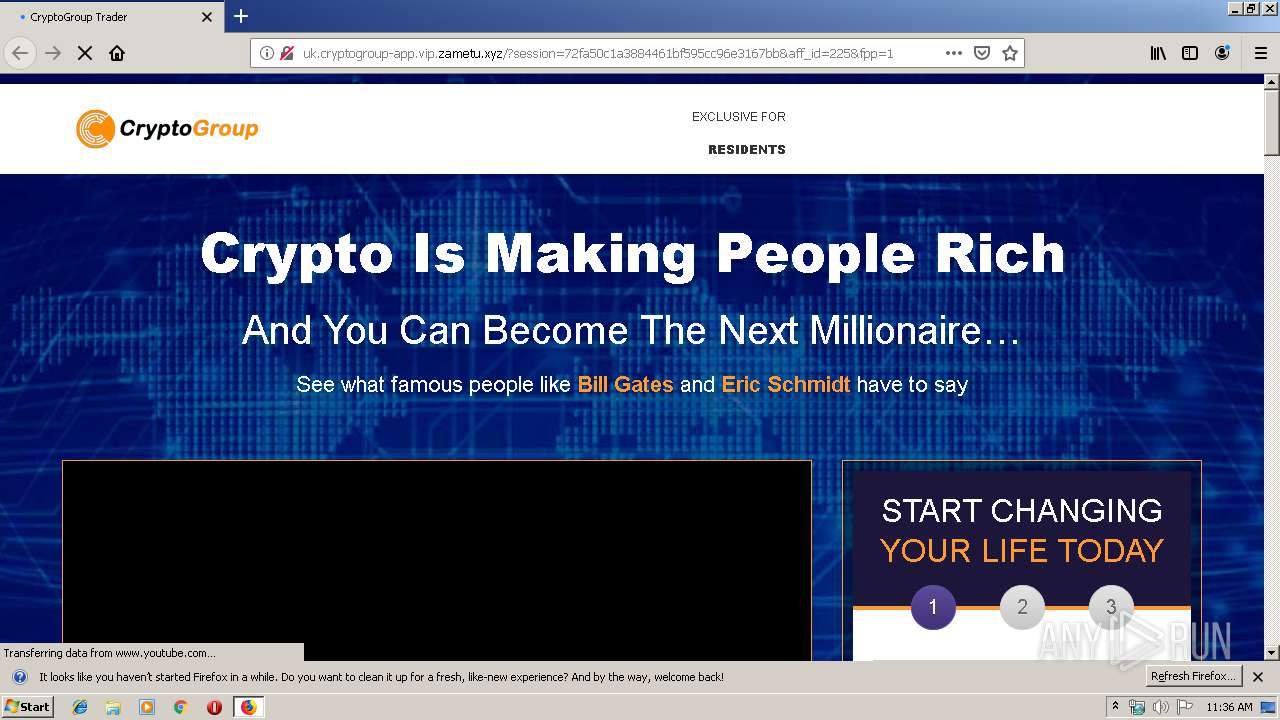
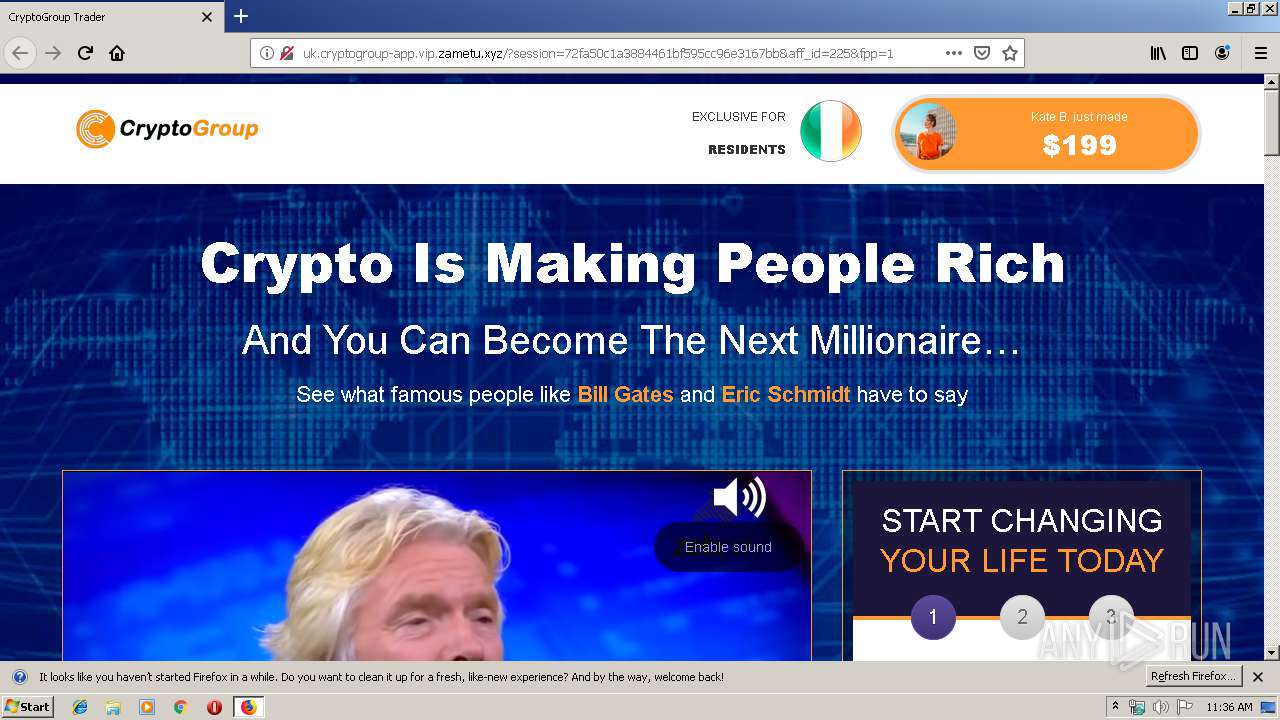
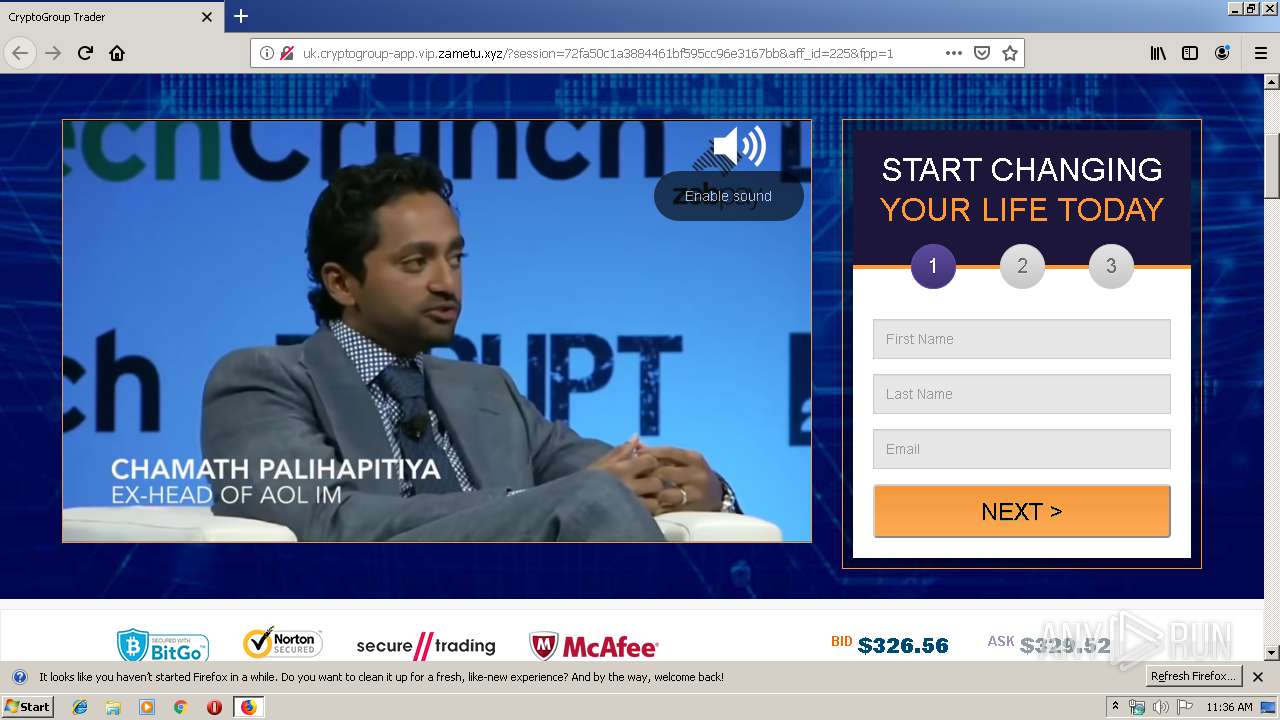
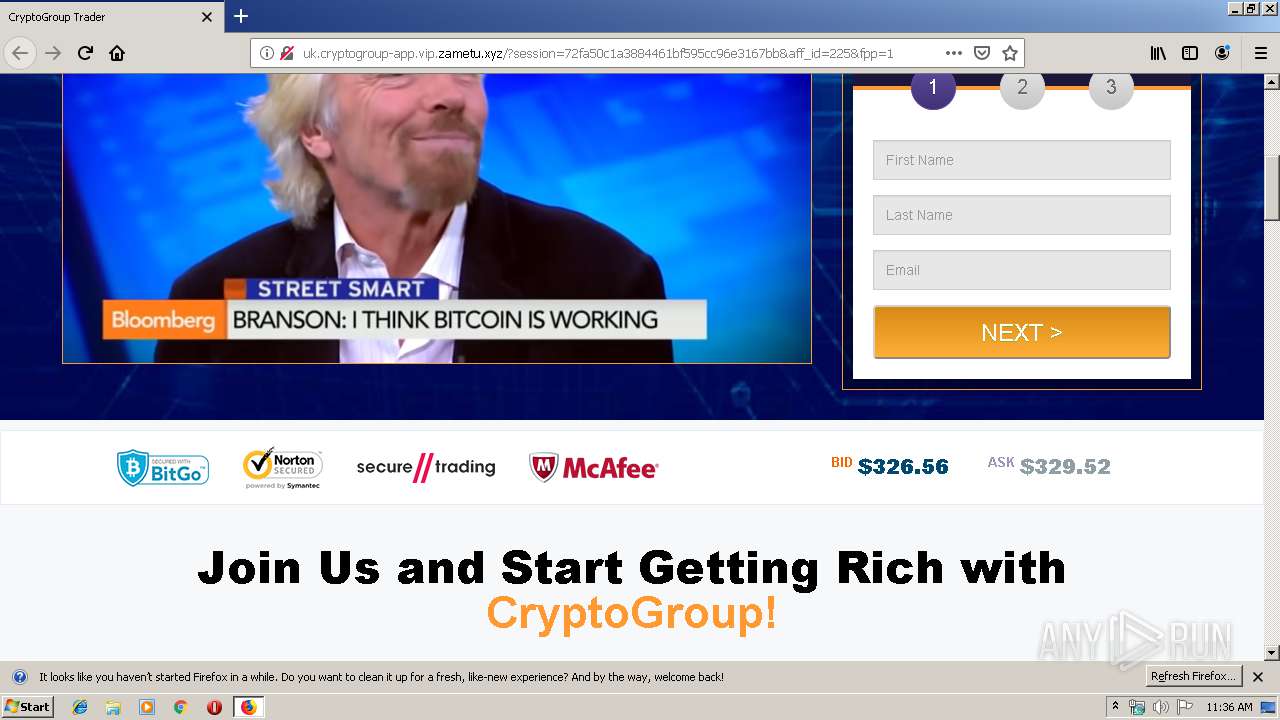
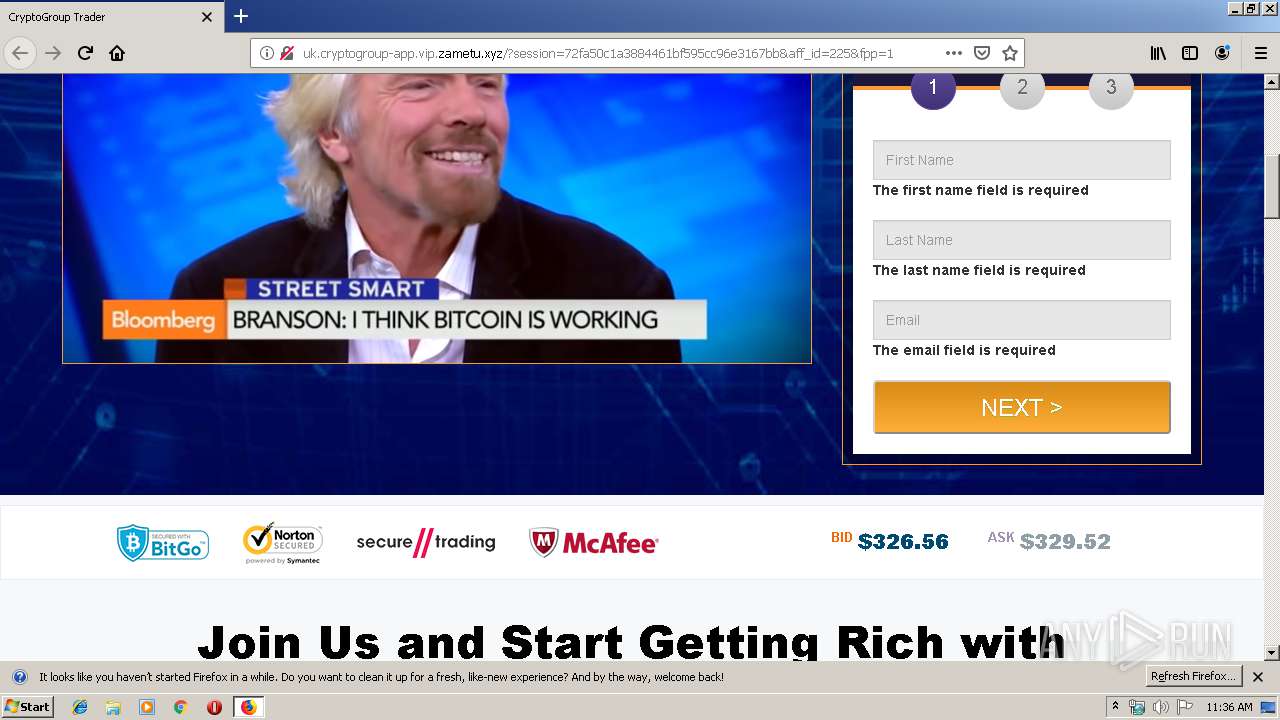
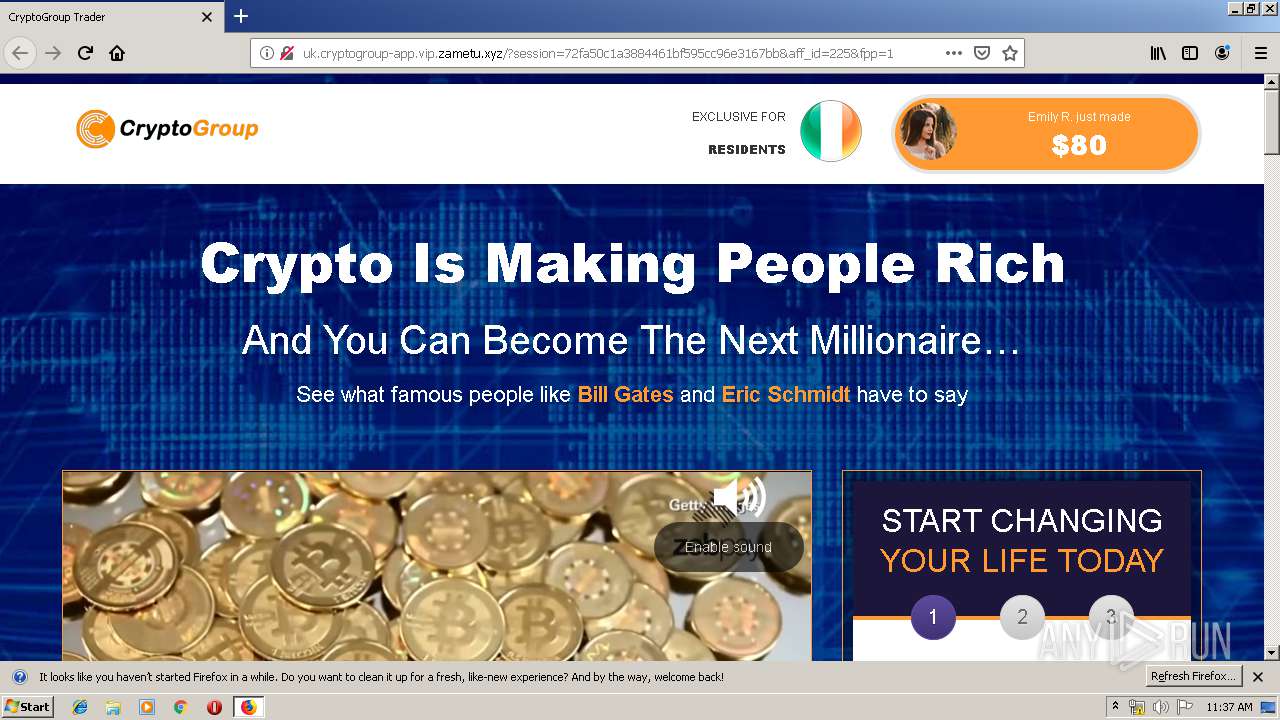
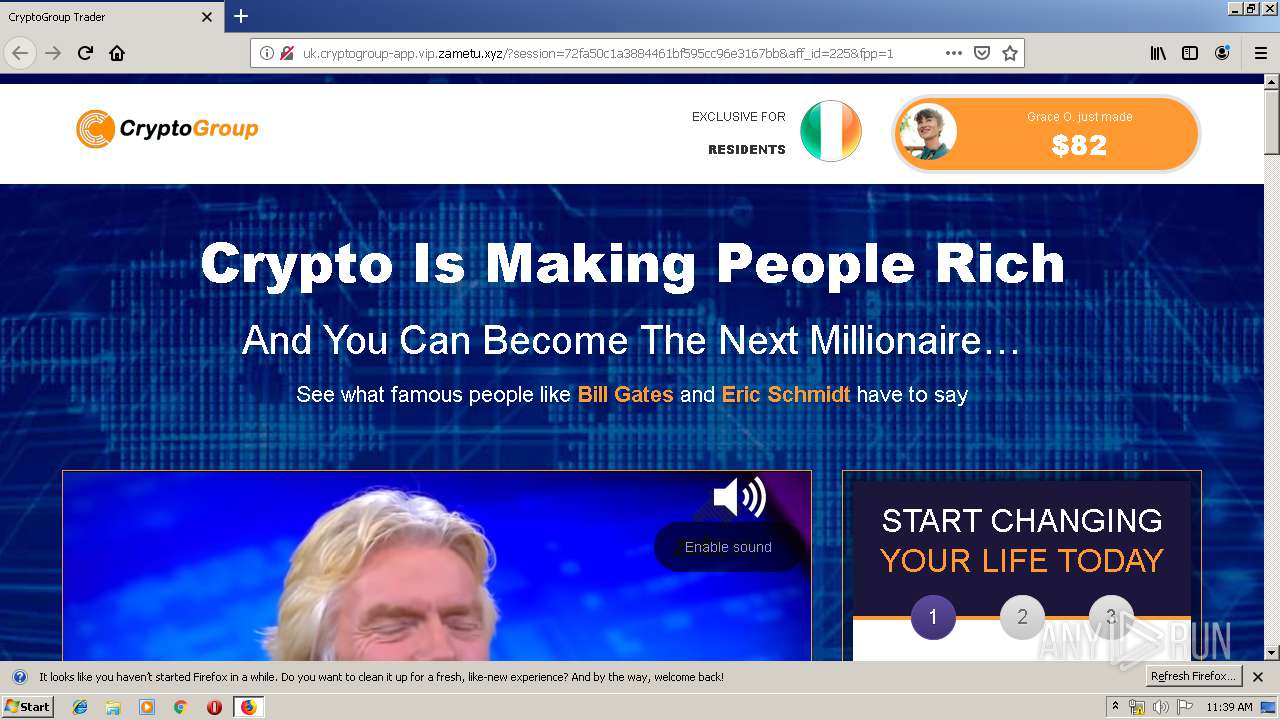
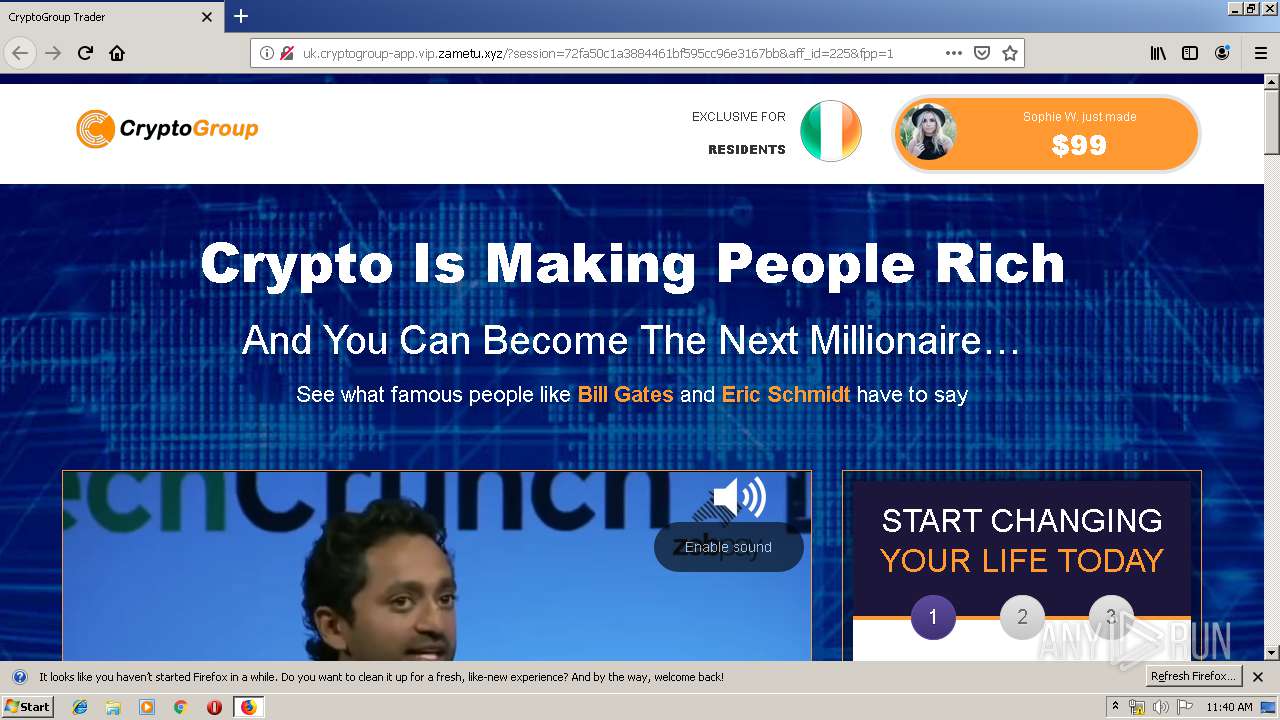
3024 | firefox.exe | GET | — | 104.18.63.52:80 | http://vip.zametu.xyz/.well-known/http-opportunistic | US | — | — | malicious |
3024 | firefox.exe | GET | 302 | 104.18.62.52:80 | http://vip.zametu.xyz/tracker?offer_id=2560&aff_id=225&u=1187:100&pl=518:100&aff_sub2=14 | US | — | — | malicious |
3024 | firefox.exe | GET | — | 104.18.63.52:80 | http://uk.cryptogroup-app.vip.zametu.xyz/.well-known/http-opportunistic | US | — | — | malicious |
3024 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3024 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3024 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3024 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3024 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3024 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3024 | firefox.exe | 52.210.139.31:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | malicious |
3024 | firefox.exe | 172.217.22.33:443 | presorwamma1978.blogspot.ie | Google Inc. | US | whitelisted |
3024 | firefox.exe | 95.100.39.17:80 | detectportal.firefox.com | Akamai International B.V. | DE | whitelisted |
3024 | firefox.exe | 52.34.92.178:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3024 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3024 | firefox.exe | 99.86.118.58:443 | snippets.cdn.mozilla.net | AT&T Services, Inc. | US | unknown |
3024 | firefox.exe | 216.58.206.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3024 | firefox.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3024 | firefox.exe | 34.215.70.240:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3024 | firefox.exe | 34.209.86.85:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod1-elb-eu-west-1.prod.mozaws.net |
| whitelisted |
presorwamma1978.blogspot.ie |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
blogspot.l.googleusercontent.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3024 | firefox.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3024 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3024 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3024 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3024 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3024 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3024 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3024 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3024 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |