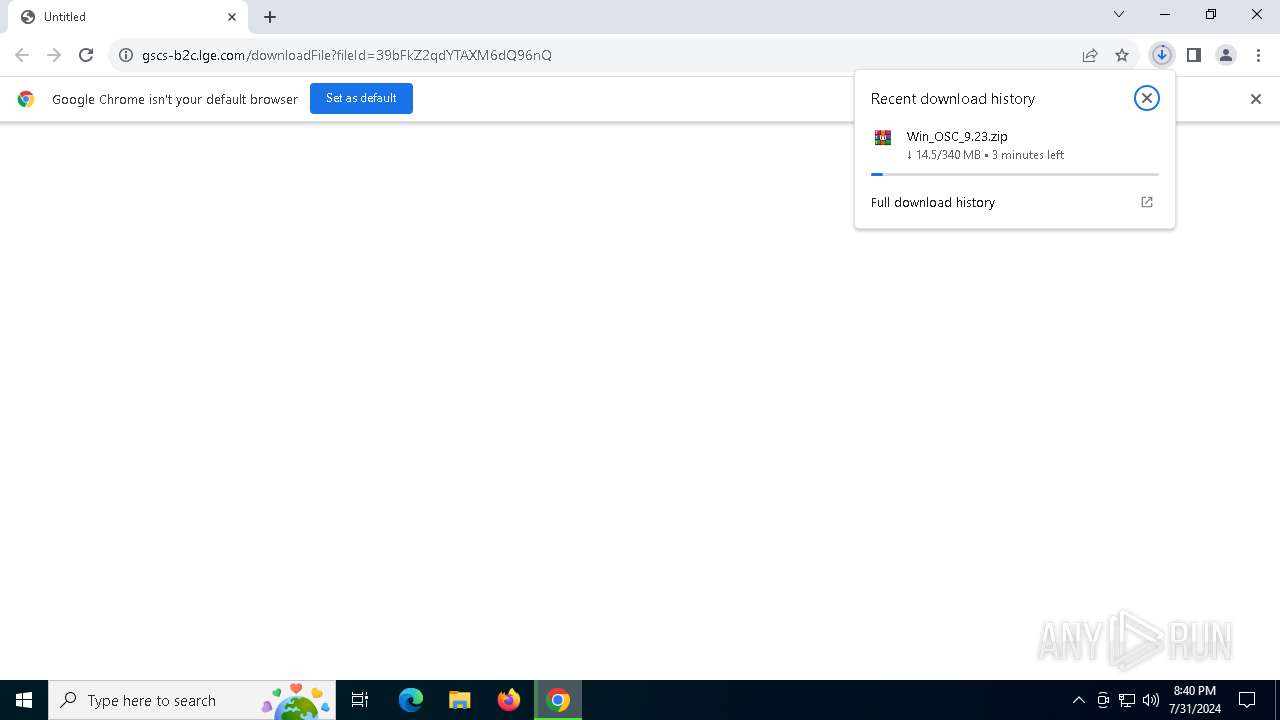
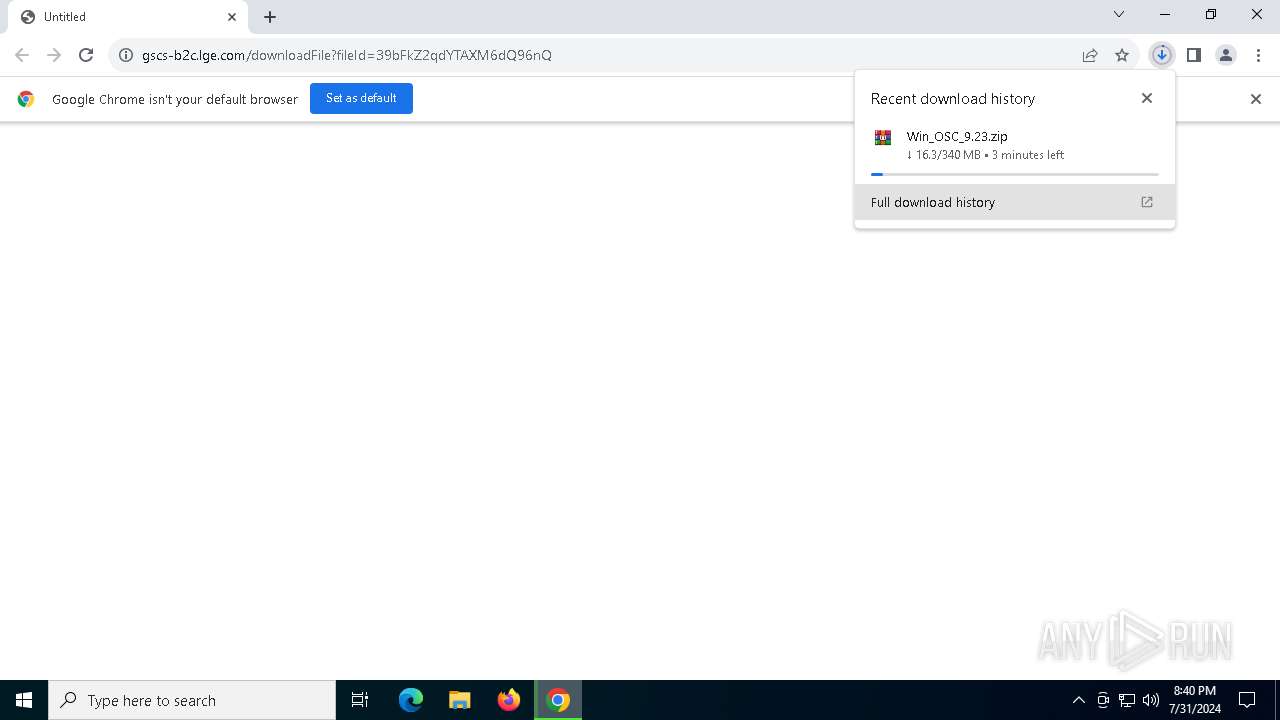
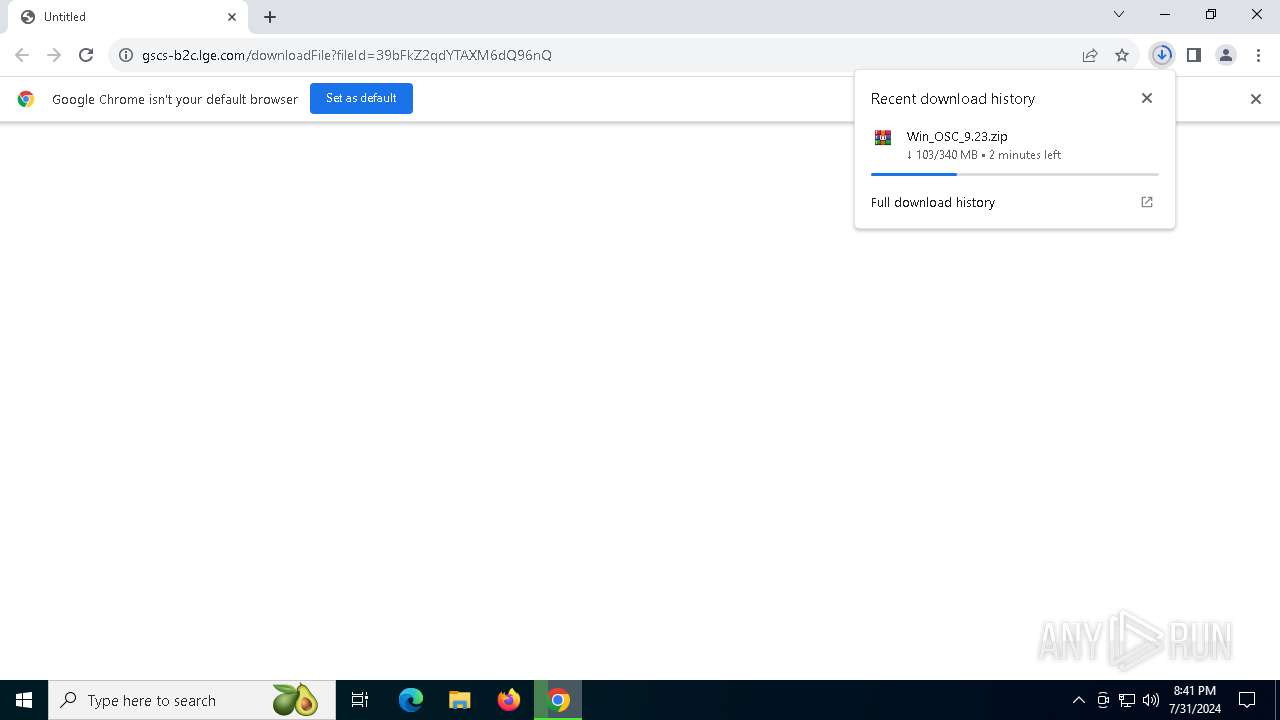
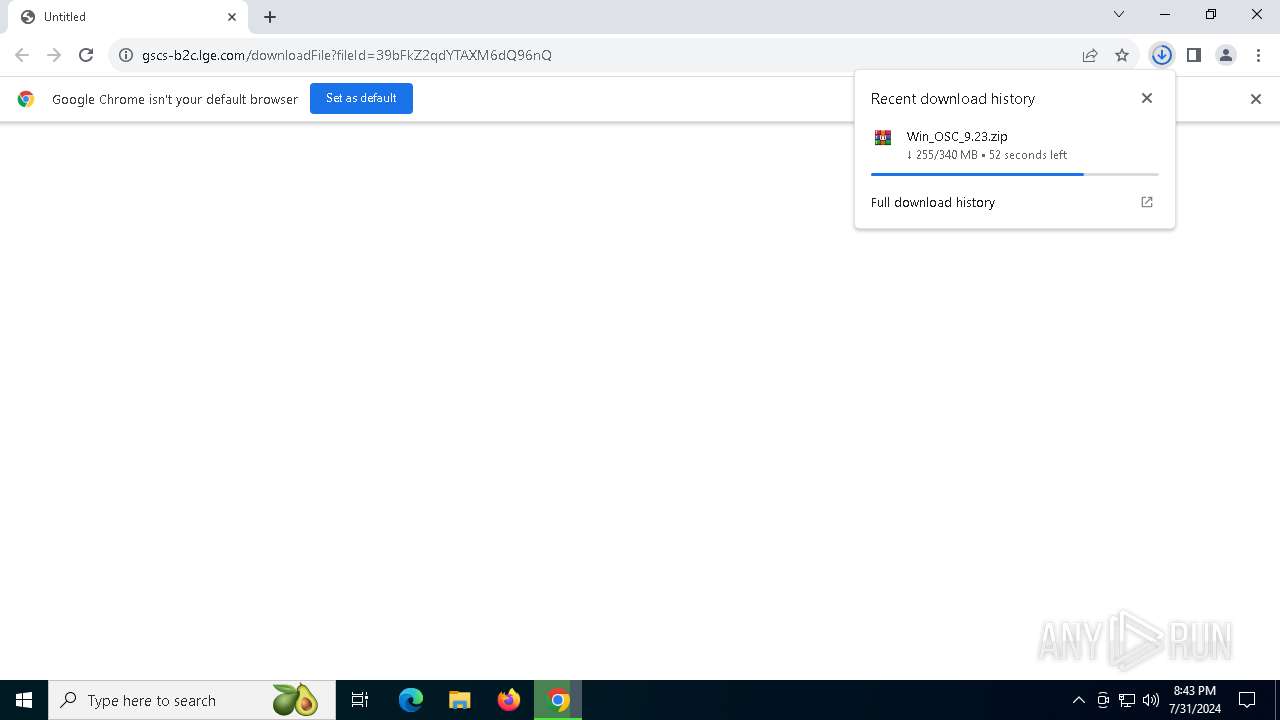
| URL: | https://gscs-b2c.lge.com/downloadFile?fileId=39bFkZ2qdYTAXM6dQ96nQ |
| Full analysis: | https://app.any.run/tasks/17b332a3-2ca5-4bef-be14-52da9c530770 |
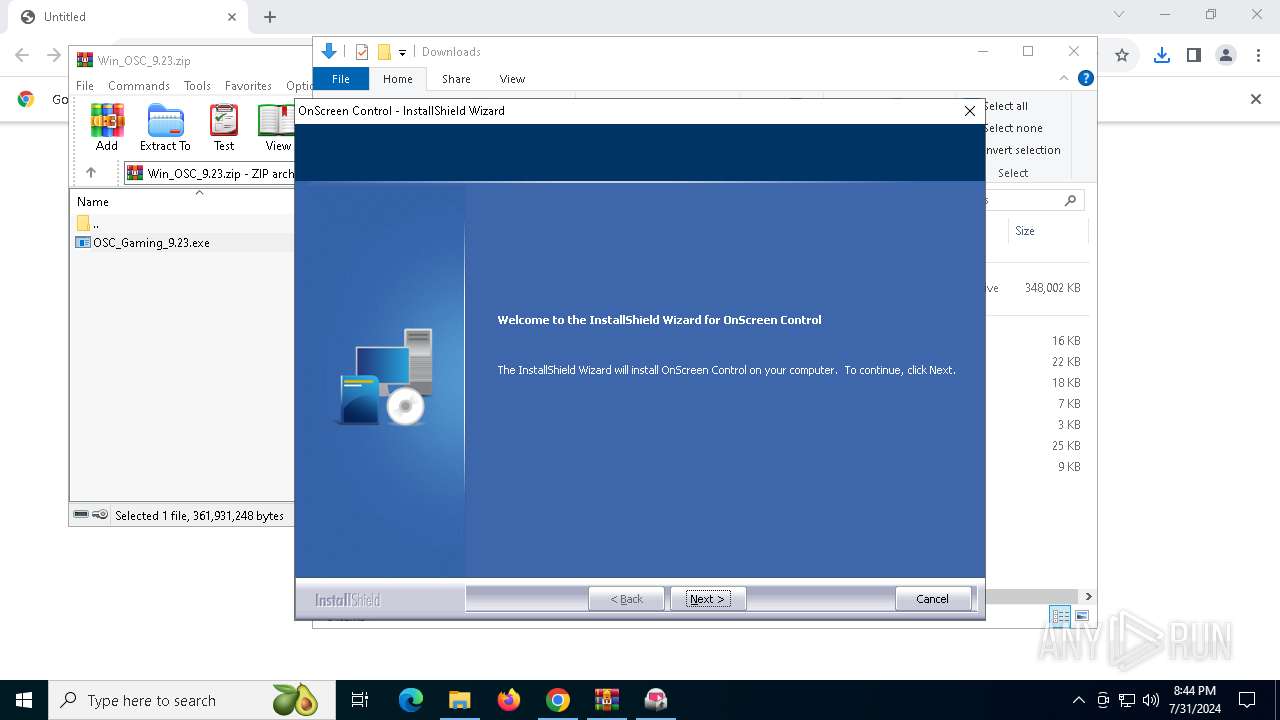
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2024, 20:40:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 22BD7EF33C73133E11B3D18F9244B1E5 |
| SHA1: | AF5787F7A910E04D7CB0DE55BEB622C1FAB537A4 |
| SHA256: | 98E3ECD43A864046EC2B7A49EEDF458EA1ED17C4001DFCDAD98CF3BEBA3B621E |
| SSDEEP: | 3:N83+34CALRBKi4cA9y/o8xRTBJA:2H6i43yQ8TM |
MALICIOUS
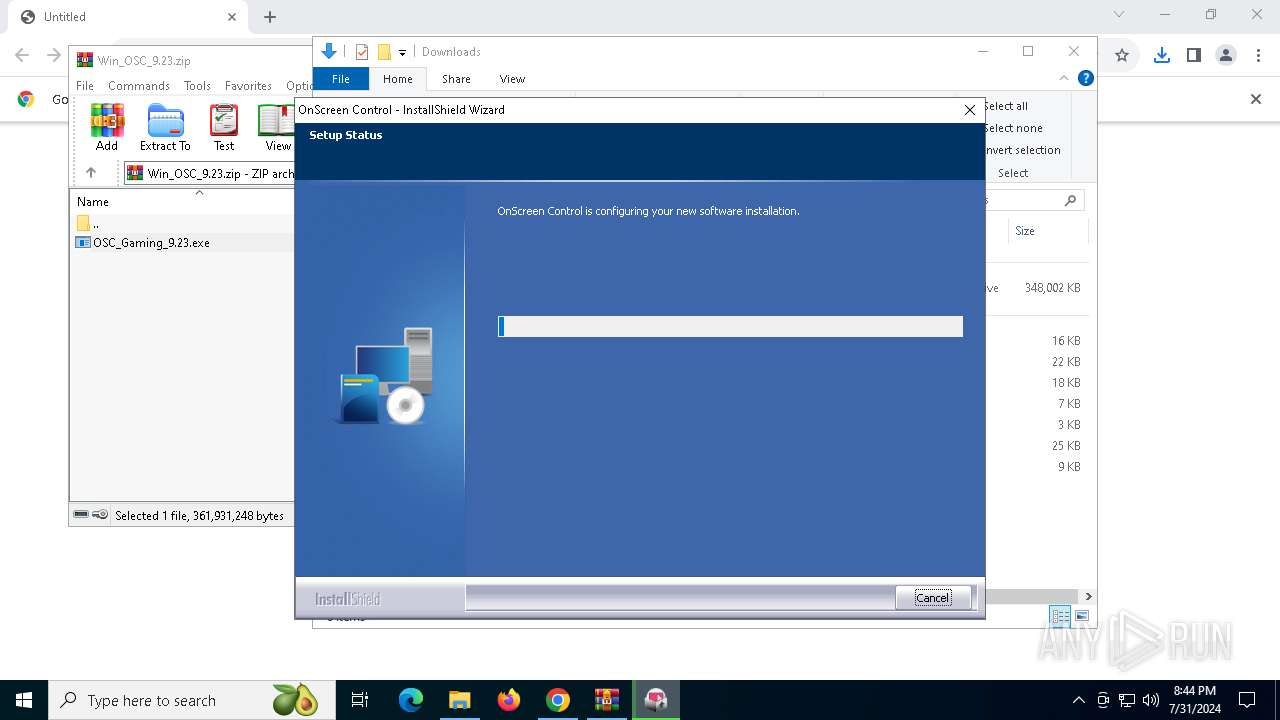
Changes the autorun value in the registry
- OSC_Gaming_9.23.exe (PID: 1860)
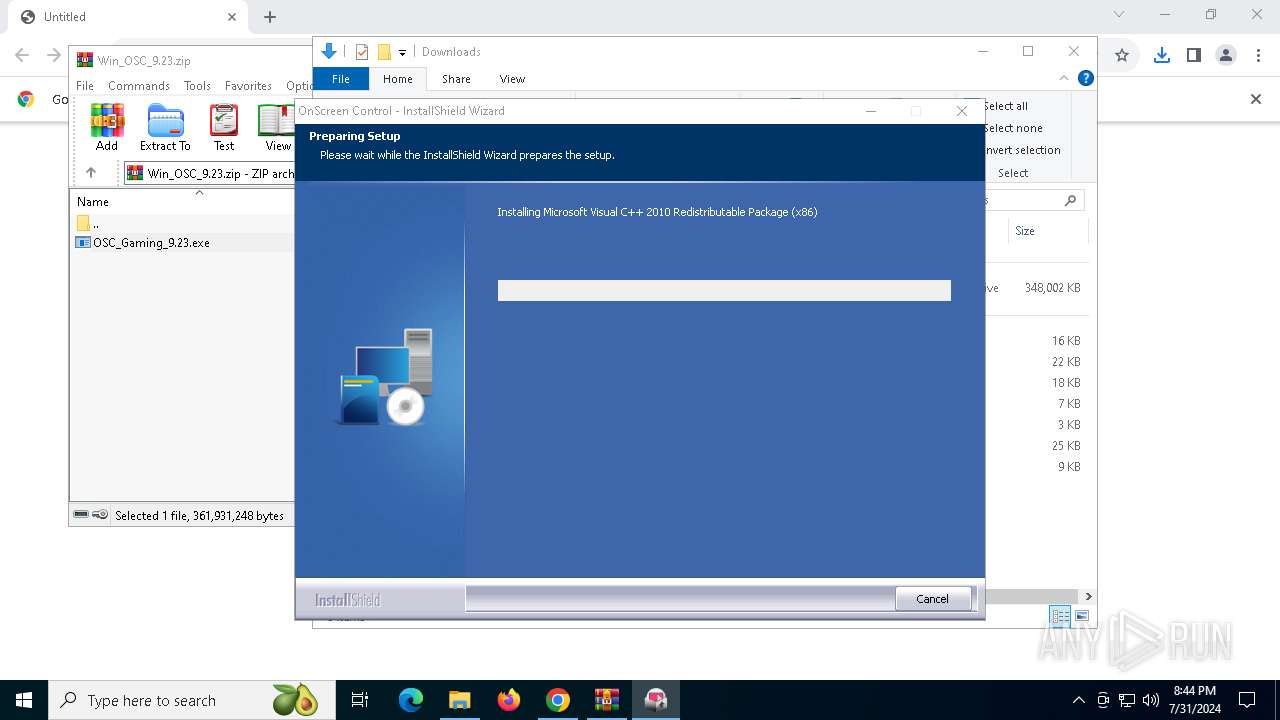
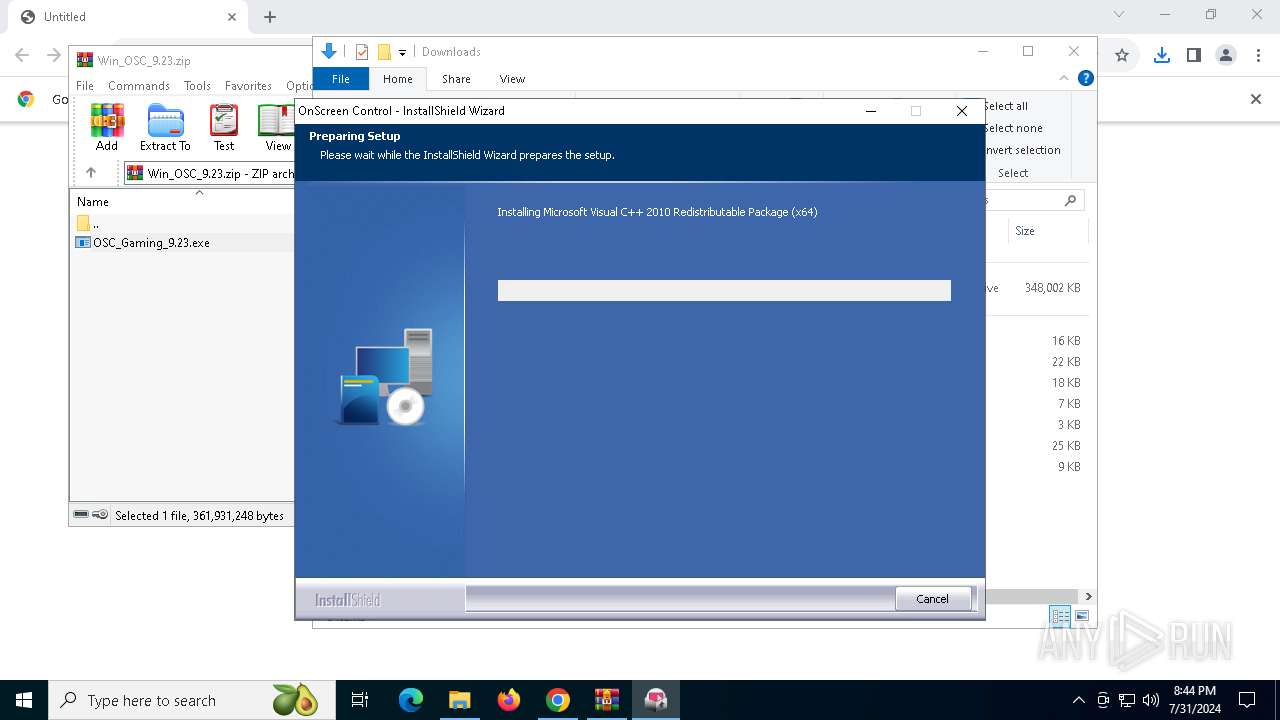
Drops the executable file immediately after the start
- OSC_Gaming_9.23.exe (PID: 300)
- vcredist_x86.exe (PID: 5180)
- OSC_Gaming_9.23.exe (PID: 1860)
- msiexec.exe (PID: 752)
- vcredist_x64.exe (PID: 5064)
- msiexec.exe (PID: 1920)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 232)
- OSC_Gaming_9.23.exe (PID: 1860)
- Setup.exe (PID: 6156)
- Setup.exe (PID: 2872)
Searches for installed software
- OSC_Gaming_9.23.exe (PID: 300)
- OSC_Gaming_9.23.exe (PID: 1860)
- dllhost.exe (PID: 3988)
Executable content was dropped or overwritten
- OSC_Gaming_9.23.exe (PID: 300)
- OSC_Gaming_9.23.exe (PID: 1860)
- vcredist_x86.exe (PID: 5180)
- vcredist_x64.exe (PID: 5064)
Process drops legitimate windows executable
- OSC_Gaming_9.23.exe (PID: 300)
- vcredist_x86.exe (PID: 5180)
- msiexec.exe (PID: 752)
- vcredist_x64.exe (PID: 5064)
- msiexec.exe (PID: 1920)
- OSC_Gaming_9.23.exe (PID: 1860)
Starts a Microsoft application from unusual location
- vcredist_x86.exe (PID: 5180)
- vcredist_x64.exe (PID: 5064)
Reads the date of Windows installation
- OSC_Gaming_9.23.exe (PID: 1860)
Creates file in the systems drive root
- vcredist_x86.exe (PID: 5180)
- vcredist_x64.exe (PID: 5064)
Checks Windows Trust Settings
- Setup.exe (PID: 6156)
- msiexec.exe (PID: 752)
- Setup.exe (PID: 2872)
- msiexec.exe (PID: 1920)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 752)
- msiexec.exe (PID: 1920)
- OSC_Gaming_9.23.exe (PID: 1860)
The process drops C-runtime libraries
- msiexec.exe (PID: 752)
- msiexec.exe (PID: 1920)
Executes as Windows Service
- VSSVC.exe (PID: 5180)
INFO
Application launched itself
- chrome.exe (PID: 6316)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6316)
Checks supported languages
- OSC_Gaming_9.23.exe (PID: 300)
- OSC_Gaming_9.23.exe (PID: 1860)
- vcredist_x86.exe (PID: 5180)
- Setup.exe (PID: 6156)
- msiexec.exe (PID: 752)
- vcredist_x64.exe (PID: 5064)
- Setup.exe (PID: 2872)
- msiexec.exe (PID: 1920)
- ISBEW64.exe (PID: 7044)
- ISBEW64.exe (PID: 2400)
- ISBEW64.exe (PID: 2700)
- ISBEW64.exe (PID: 3068)
- ISBEW64.exe (PID: 5152)
- ISBEW64.exe (PID: 7024)
- TaskBarUnPin.exe (PID: 2360)
- TaskBarUnPin.exe (PID: 5880)
- ISBEW64.exe (PID: 3648)
- TaskBarUnPin.exe (PID: 4236)
- KillOnScreenControl.exe (PID: 6216)
- TaskBarUnPin.exe (PID: 3276)
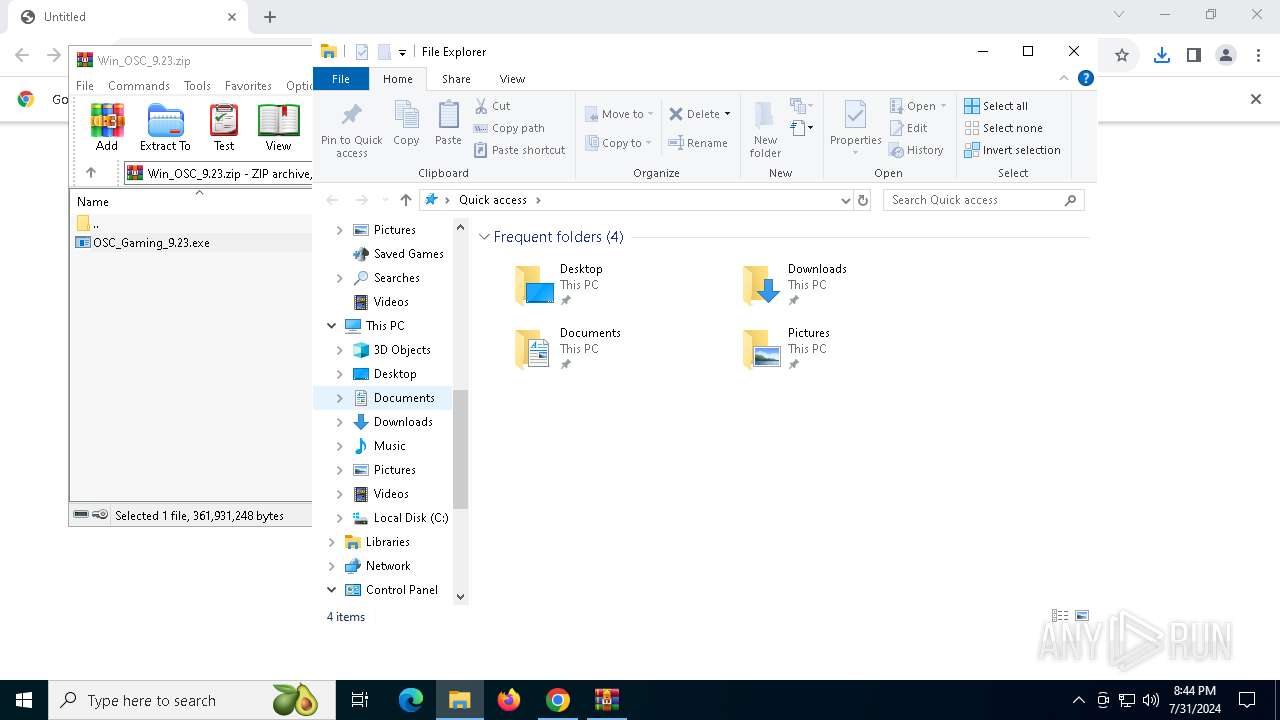
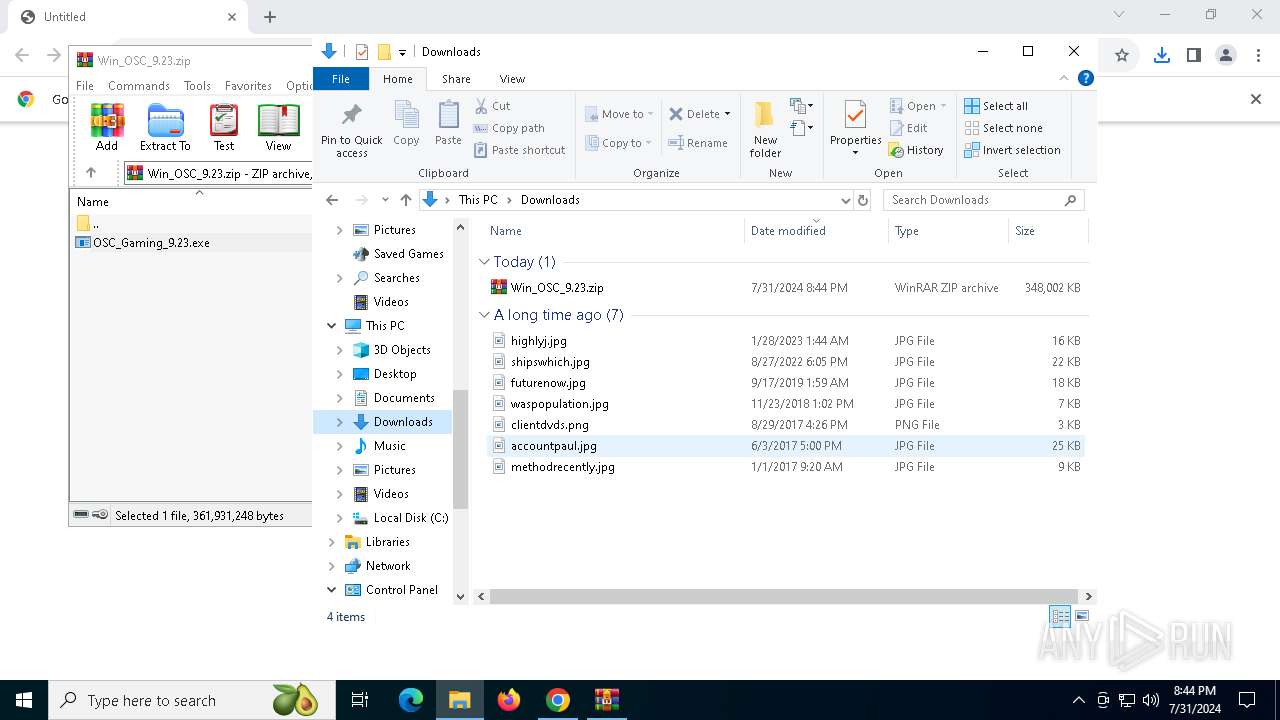
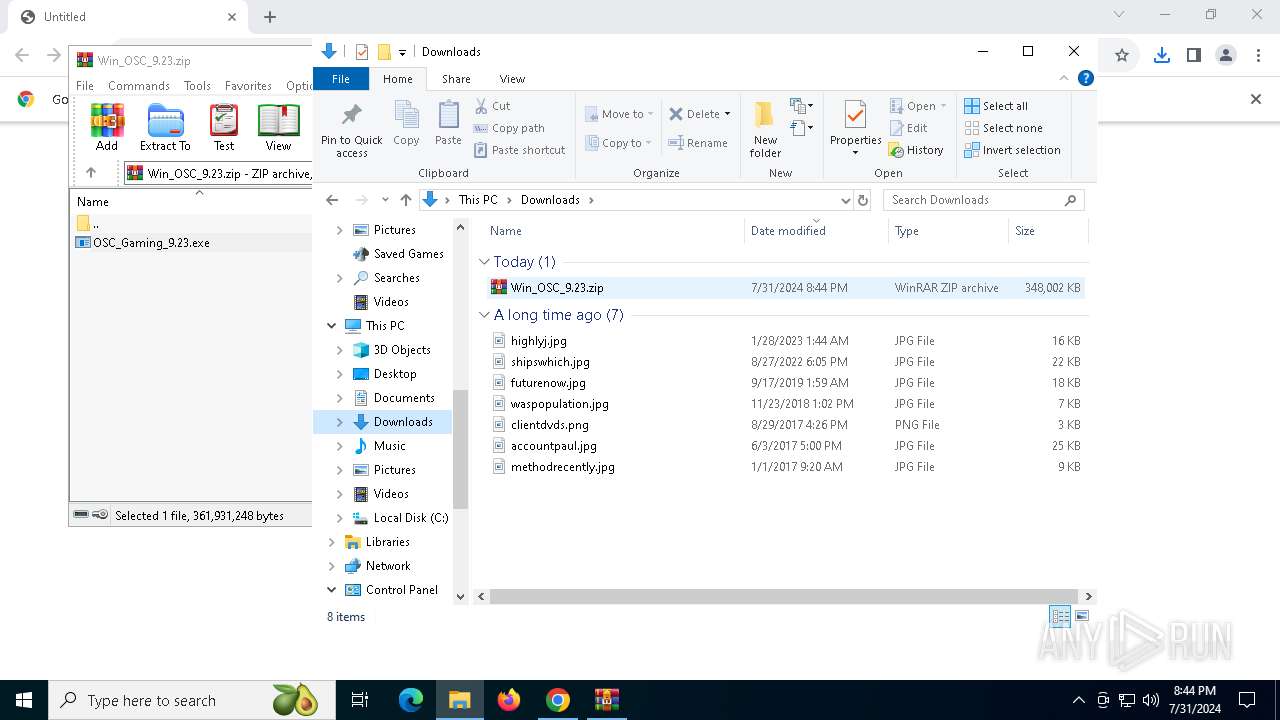
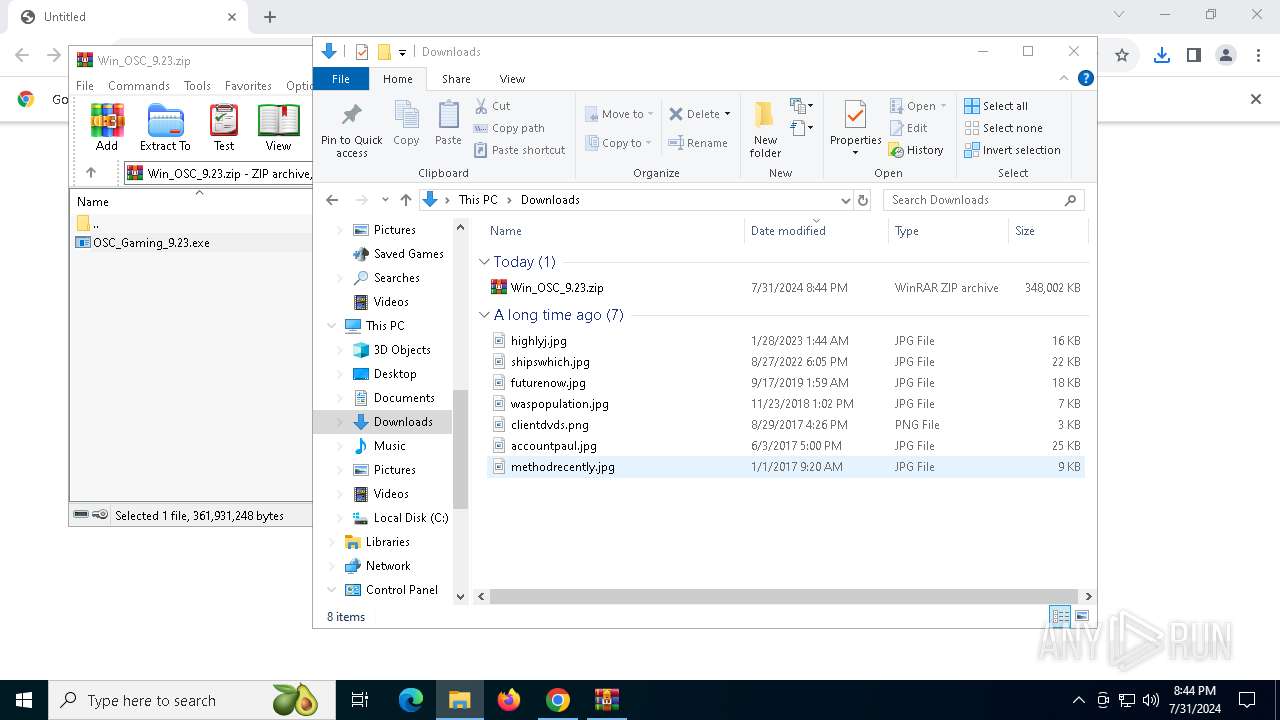
The process uses the downloaded file
- chrome.exe (PID: 368)
- chrome.exe (PID: 6316)
- WinRAR.exe (PID: 232)
Reads the computer name
- OSC_Gaming_9.23.exe (PID: 300)
- OSC_Gaming_9.23.exe (PID: 1860)
- vcredist_x86.exe (PID: 5180)
- Setup.exe (PID: 6156)
- msiexec.exe (PID: 752)
- vcredist_x64.exe (PID: 5064)
- Setup.exe (PID: 2872)
- msiexec.exe (PID: 1920)
- ISBEW64.exe (PID: 7044)
- ISBEW64.exe (PID: 2400)
- ISBEW64.exe (PID: 2700)
- ISBEW64.exe (PID: 3068)
- ISBEW64.exe (PID: 5152)
- ISBEW64.exe (PID: 7024)
- ISBEW64.exe (PID: 3648)
Create files in a temporary directory
- OSC_Gaming_9.23.exe (PID: 300)
- OSC_Gaming_9.23.exe (PID: 1860)
- Setup.exe (PID: 6156)
- Setup.exe (PID: 2872)
Process checks computer location settings
- OSC_Gaming_9.23.exe (PID: 1860)
Reads the machine GUID from the registry
- vcredist_x86.exe (PID: 5180)
- Setup.exe (PID: 6156)
- msiexec.exe (PID: 752)
- vcredist_x64.exe (PID: 5064)
- Setup.exe (PID: 2872)
- msiexec.exe (PID: 1920)
Reads CPU info
- Setup.exe (PID: 6156)
- Setup.exe (PID: 2872)
Reads the software policy settings
- Setup.exe (PID: 6156)
- msiexec.exe (PID: 752)
- Setup.exe (PID: 2872)
- msiexec.exe (PID: 1920)
Executable content was dropped or overwritten
- msiexec.exe (PID: 752)
- msiexec.exe (PID: 1920)
- chrome.exe (PID: 5988)
Creates files or folders in the user directory
- msiexec.exe (PID: 752)
Creates a software uninstall entry
- msiexec.exe (PID: 752)
- msiexec.exe (PID: 1920)
Drops the executable file immediately after the start
- chrome.exe (PID: 5988)
Creates files in the program directory
- OSC_Gaming_9.23.exe (PID: 1860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
193
Monitored processes
51
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
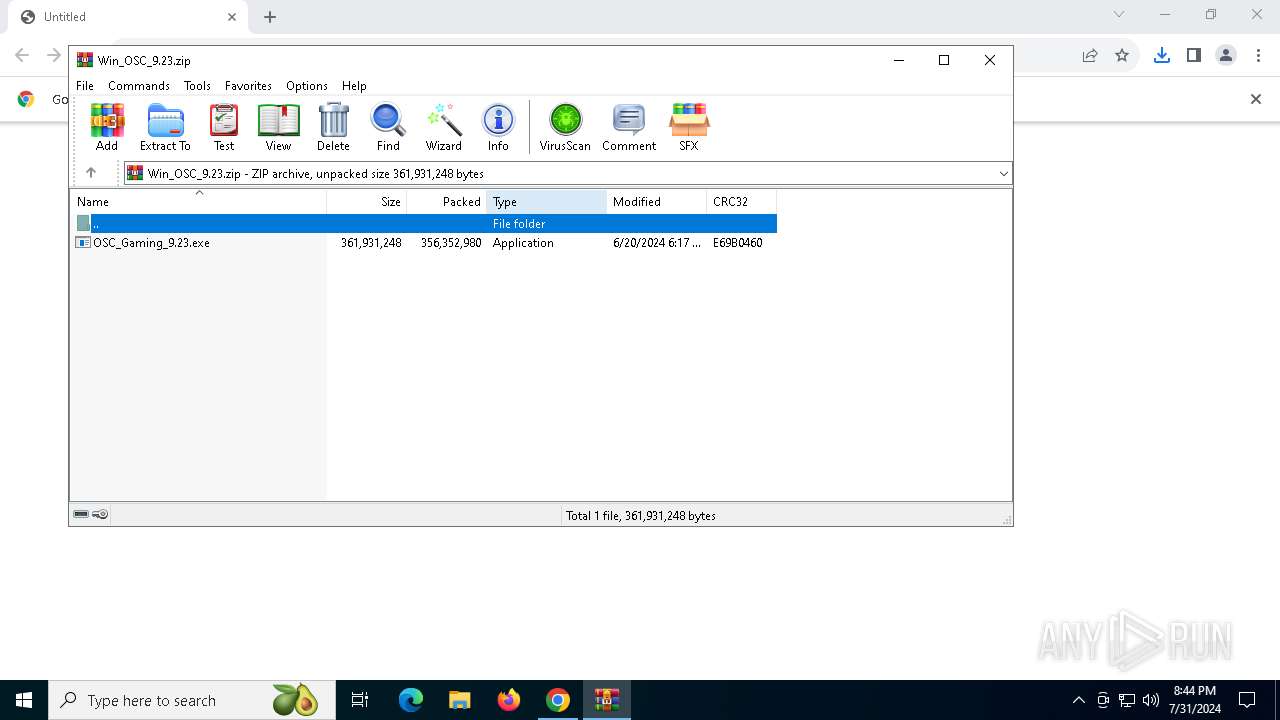
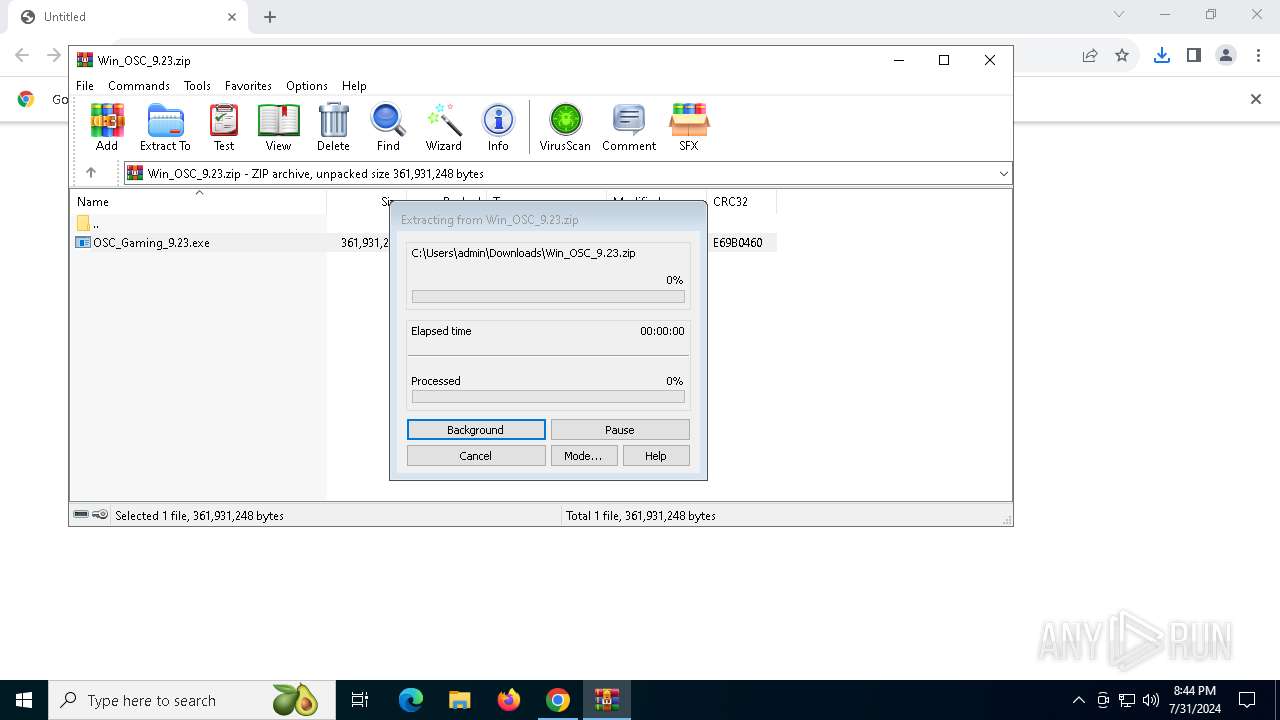
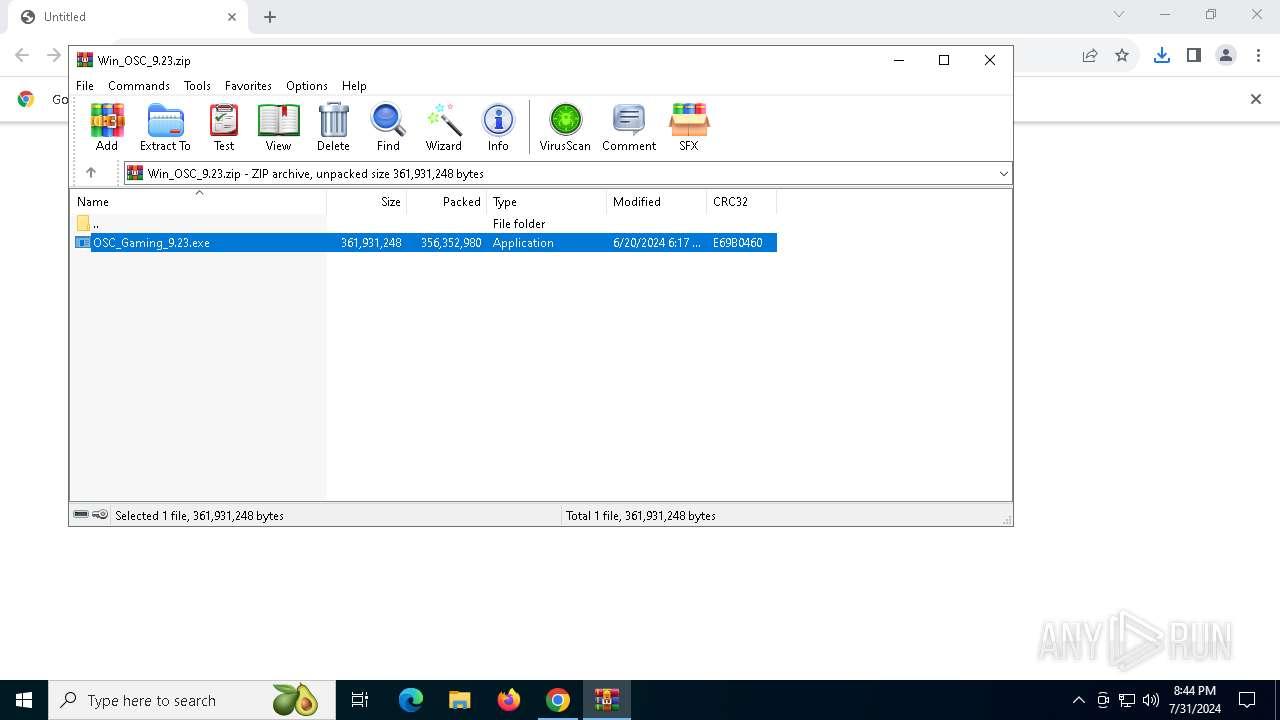
| 232 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Win_OSC_9.23.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
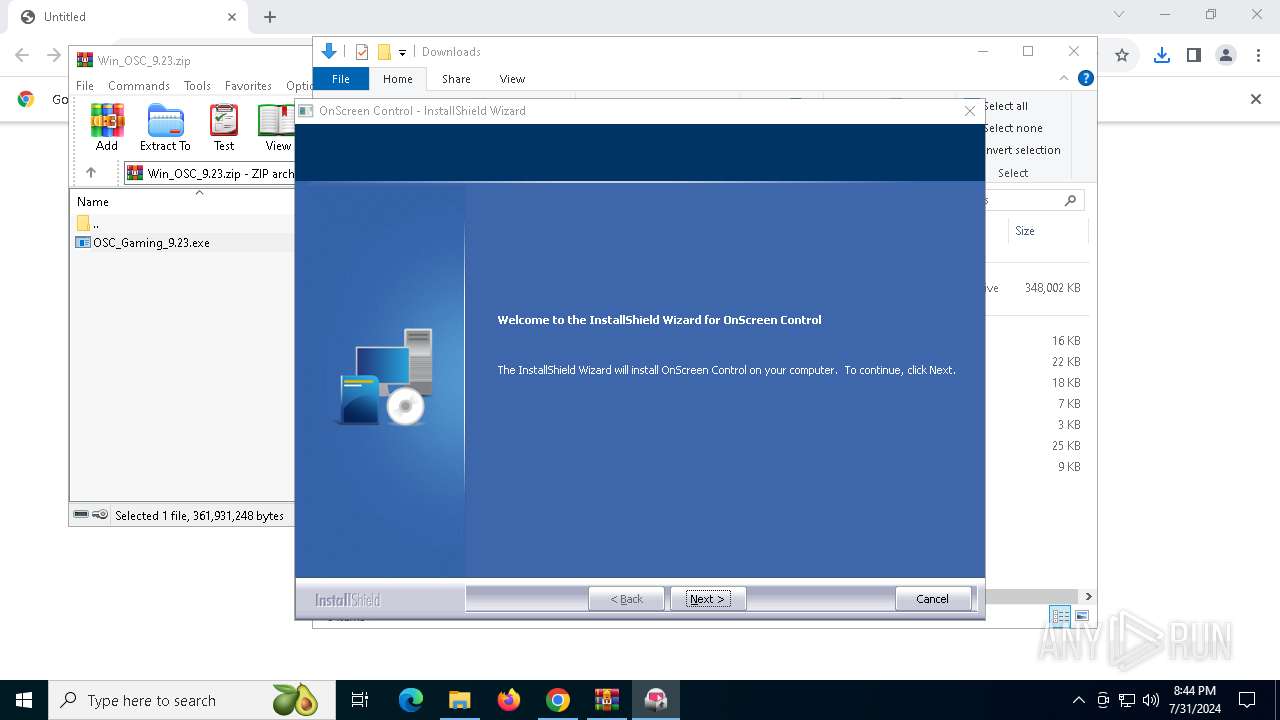
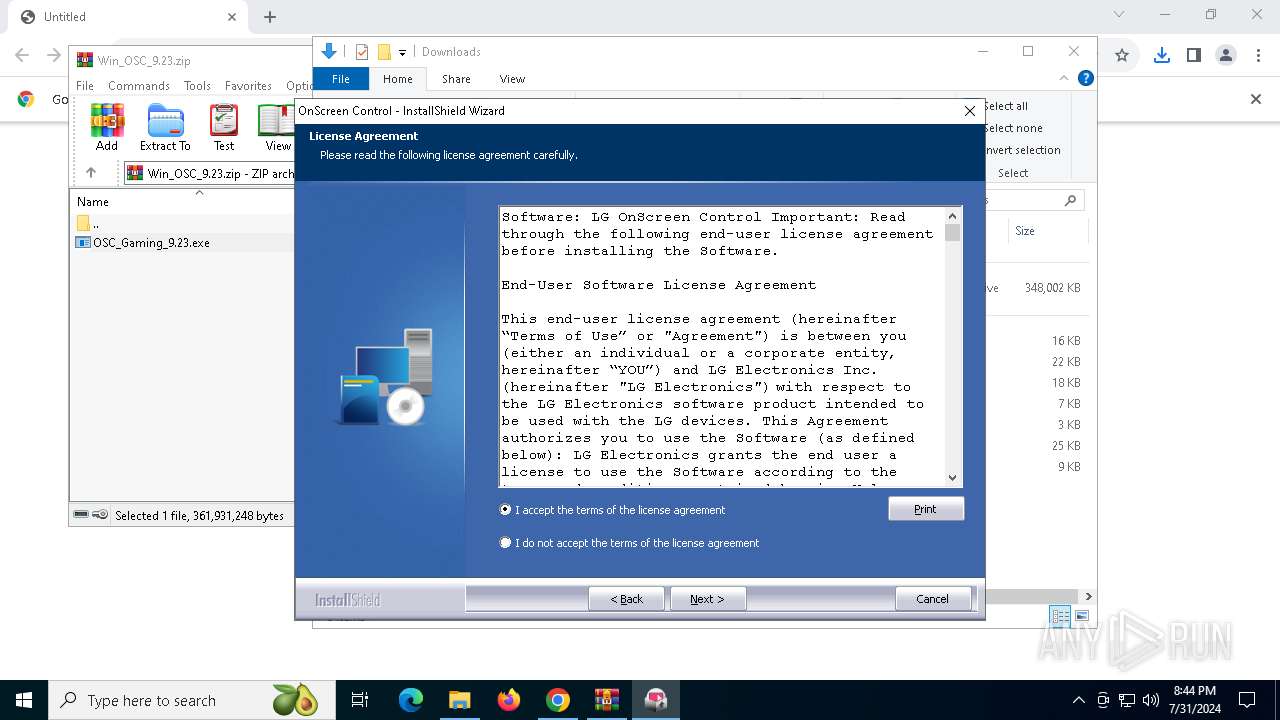
| 300 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa232.46604\OSC_Gaming_9.23.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa232.46604\OSC_Gaming_9.23.exe | WinRAR.exe | ||||||||||||
User: admin Company: LG Electronics Inc Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Version: 9.23.0 Modules
| |||||||||||||||
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3832 --field-trial-handle=1900,i,8799048295649459950,6800183000360869883,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5192 --field-trial-handle=1900,i,8799048295649459950,6800183000360869883,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 532 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5444 --field-trial-handle=1900,i,8799048295649459950,6800183000360869883,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4932 --field-trial-handle=1900,i,8799048295649459950,6800183000360869883,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
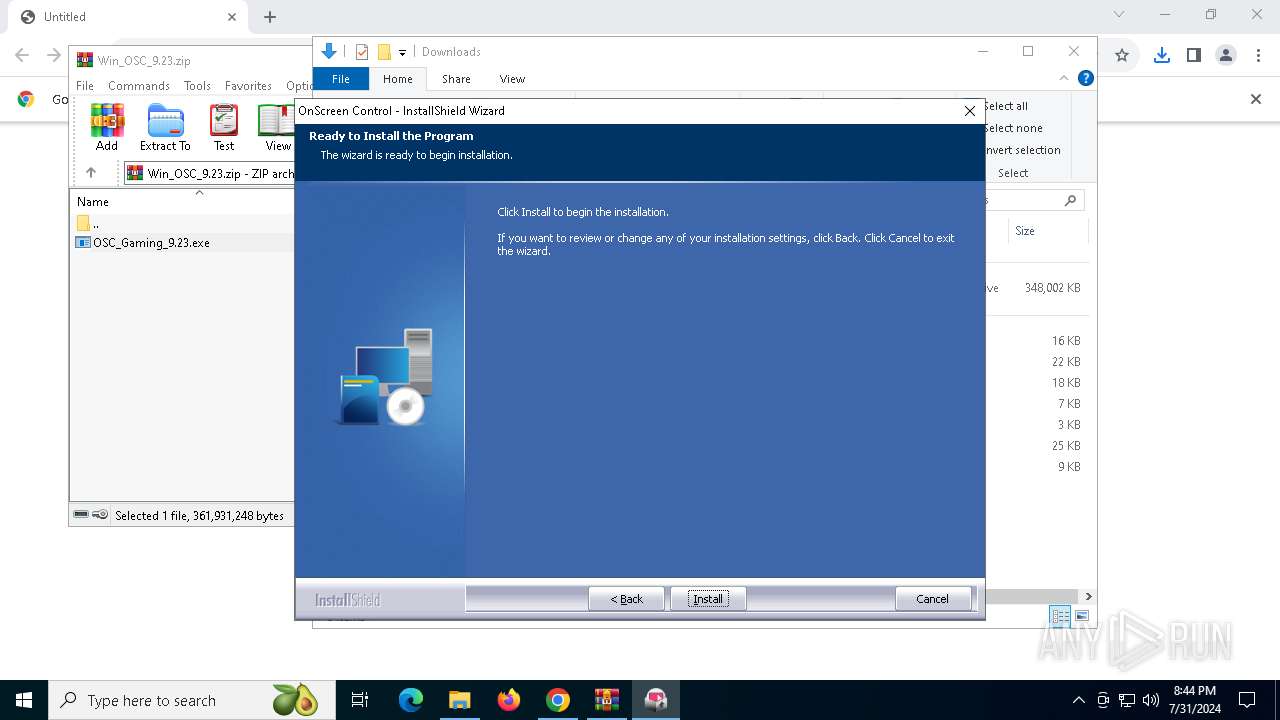
| 1860 | C:\Users\admin\AppData\Local\Temp\{A36B0FD4-895F-4C2D-887A-962415A89C71}\OSC_Gaming_9.23.exe -package:"C:\Users\admin\AppData\Local\Temp\Rar$EXa232.46604\OSC_Gaming_9.23.exe" -no_selfdeleter -IS_temp -media_path:"C:\Users\admin\AppData\Local\Temp\{A36B0FD4-895F-4C2D-887A-962415A89C71}\Disk1\" -tempdisk1folder:"C:\Users\admin\AppData\Local\Temp\{A36B0FD4-895F-4C2D-887A-962415A89C71}\" -IS_OriginalLauncher:"C:\Users\admin\AppData\Local\Temp\{A36B0FD4-895F-4C2D-887A-962415A89C71}\Disk1\OSC_Gaming_9.23.exe" | C:\Users\admin\AppData\Local\Temp\{A36B0FD4-895F-4C2D-887A-962415A89C71}\OSC_Gaming_9.23.exe | OSC_Gaming_9.23.exe | ||||||||||||
User: admin Company: LG Electronics Inc Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Version: 9.23.0 Modules
| |||||||||||||||
| 1920 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
43 267
Read events
42 567
Write events
652
Delete events
48
Modification events
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
226
Suspicious files
303
Text files
755
Unknown types
163
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe653d.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe654d.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 6316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
61
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7016 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
7016 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
7016 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
7016 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
7016 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/act6xkz2kfieukn5ttujpwzwclsa_8987/hfnkpimlhhgieaddgfemjhofmfblmnib_8987_all_ac6fxonbbcotseg4jmr2b6yrij5a.crx3 | unknown | — | — | whitelisted |
7016 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2208 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7016 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
7016 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrga7eefaxjfdmmgfkiaxjg4yjq_2024.7.12.235938/eeigpngbgcognadeebkilcpcaedhellh_2024.07.12.235938_all_a6r64uyugl6fjh3lupjqo6w7ai.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5040 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1116 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6588 | chrome.exe | 142.250.153.84:443 | accounts.google.com | GOOGLE | US | unknown |
6316 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6588 | chrome.exe | 41.63.96.2:443 | gscs-b2c.lge.com | LLNW | ZA | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6316 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
gscs-b2c.lge.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|
Setup.exe | The operation completed successfully.
|