| download: | decompiler |
| Full analysis: | https://app.any.run/tasks/6881dd2d-57eb-42a2-870b-327784b77486 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 23:31:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 6C9DC03190A168583D5FC84509C0039B |
| SHA1: | 35129CE3AF74F06823FBB90B91B1A4481E12F25D |
| SHA256: | 98E0F8CB65D022FAAA67F72B04D01CAB0D9C6ED29242720DCA571006084A195E |
| SSDEEP: | 1536:/5ueoZ63MEfeXY5HFuoQdvi6khYt8YSOufco4fuBY1+6n5u20yJhsHbzABj0W5eS:/QV03MEfpHFuoQdvi6khYt8YSOufco4t |
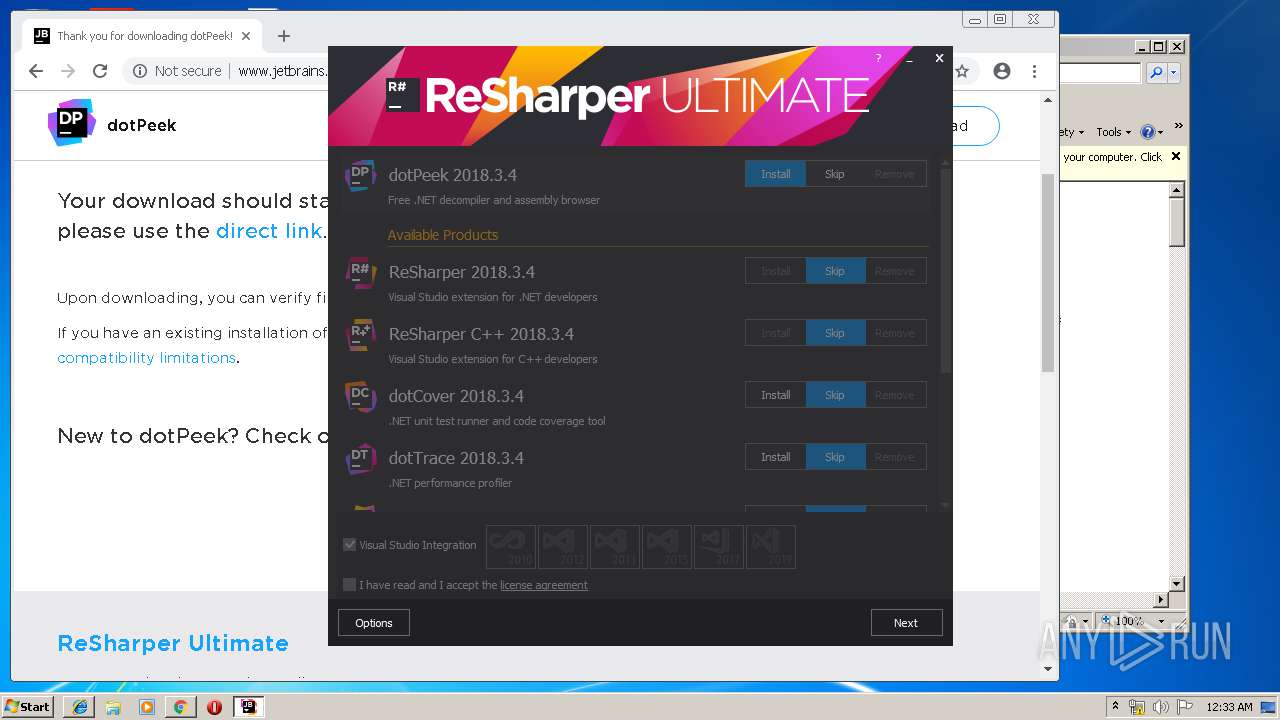
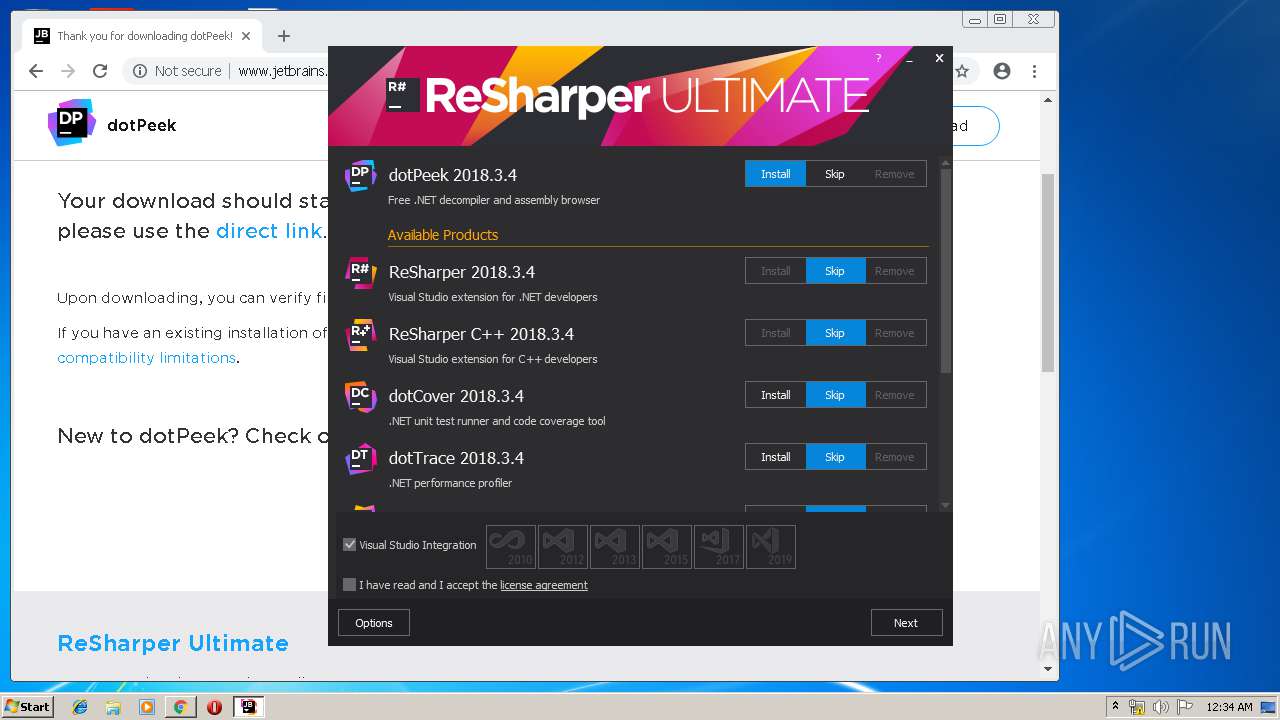
MALICIOUS
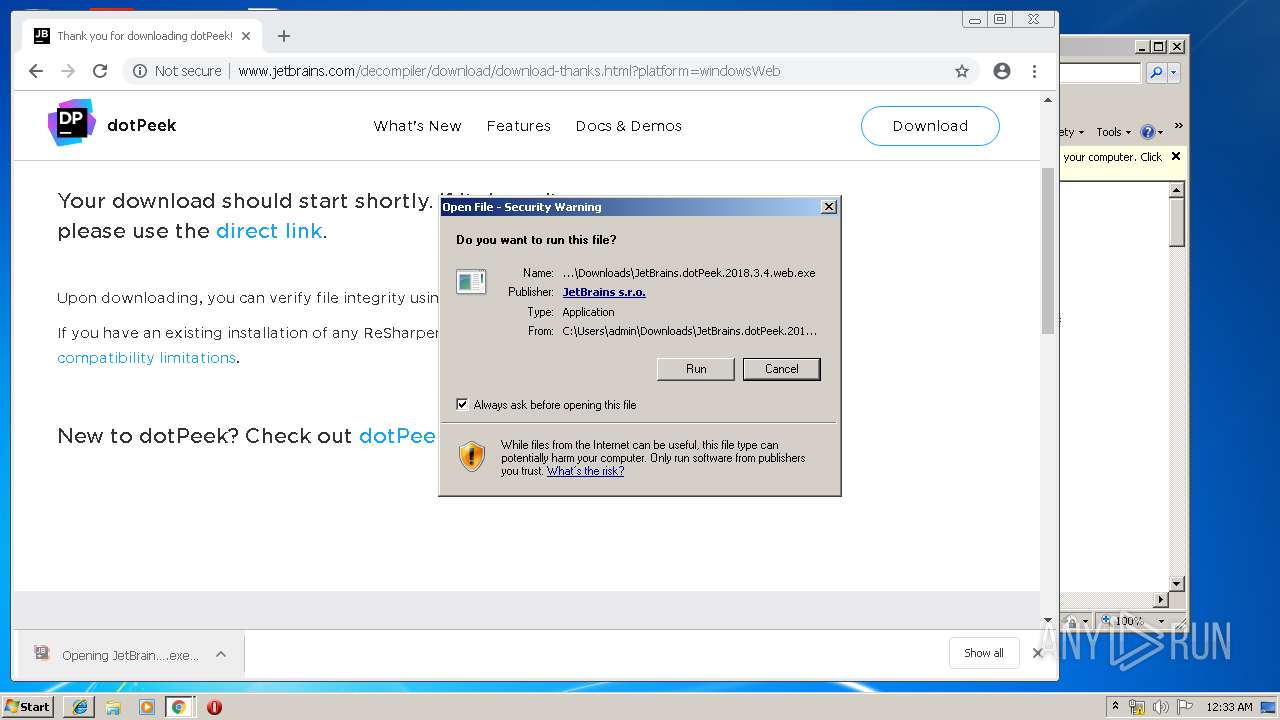
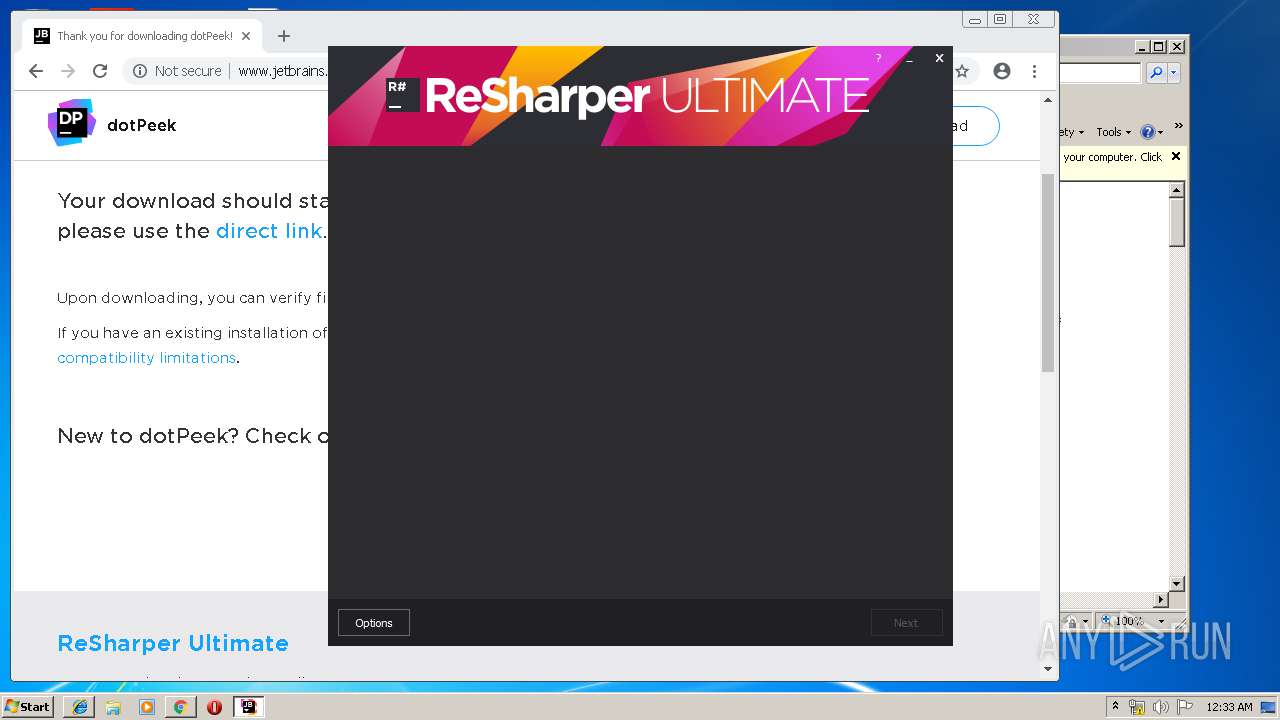
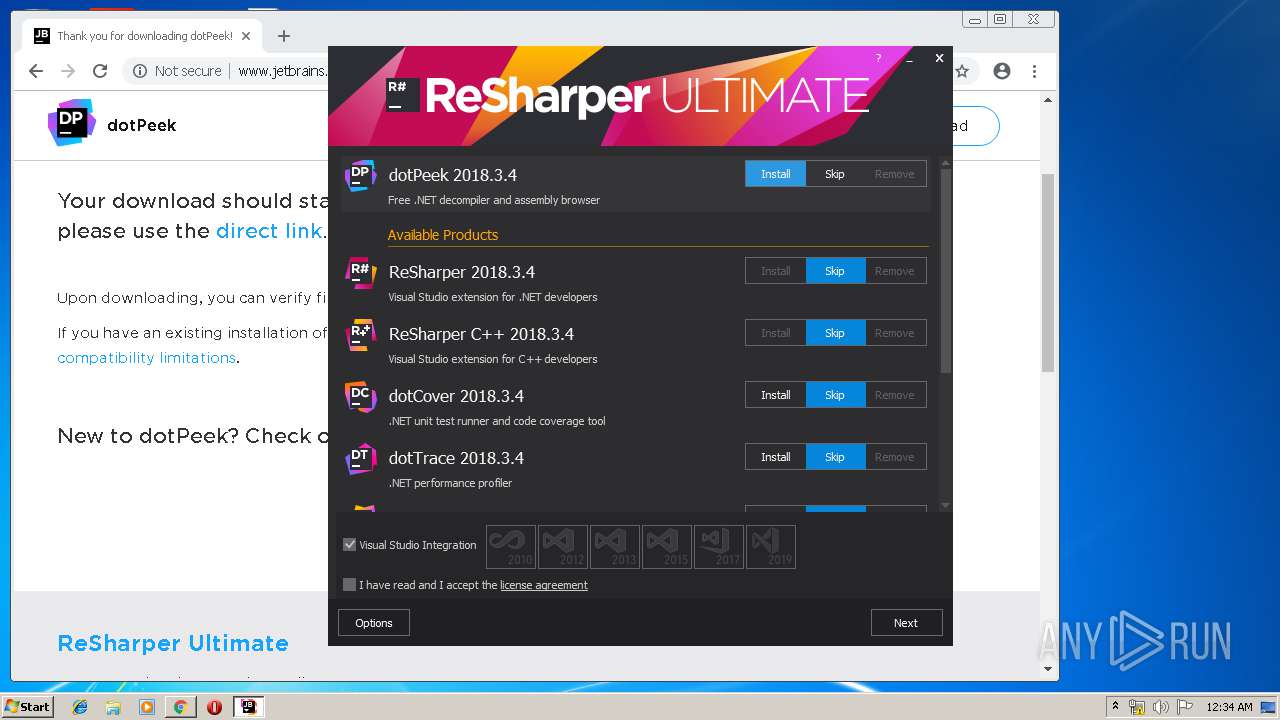
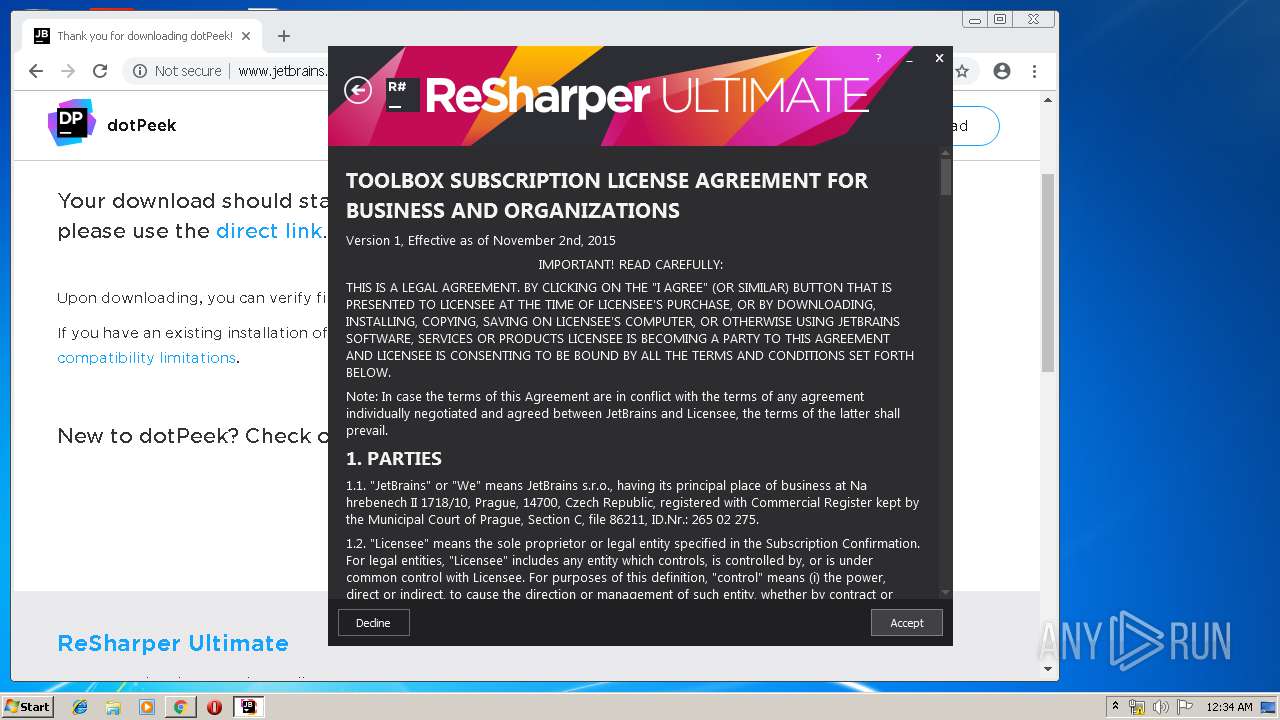
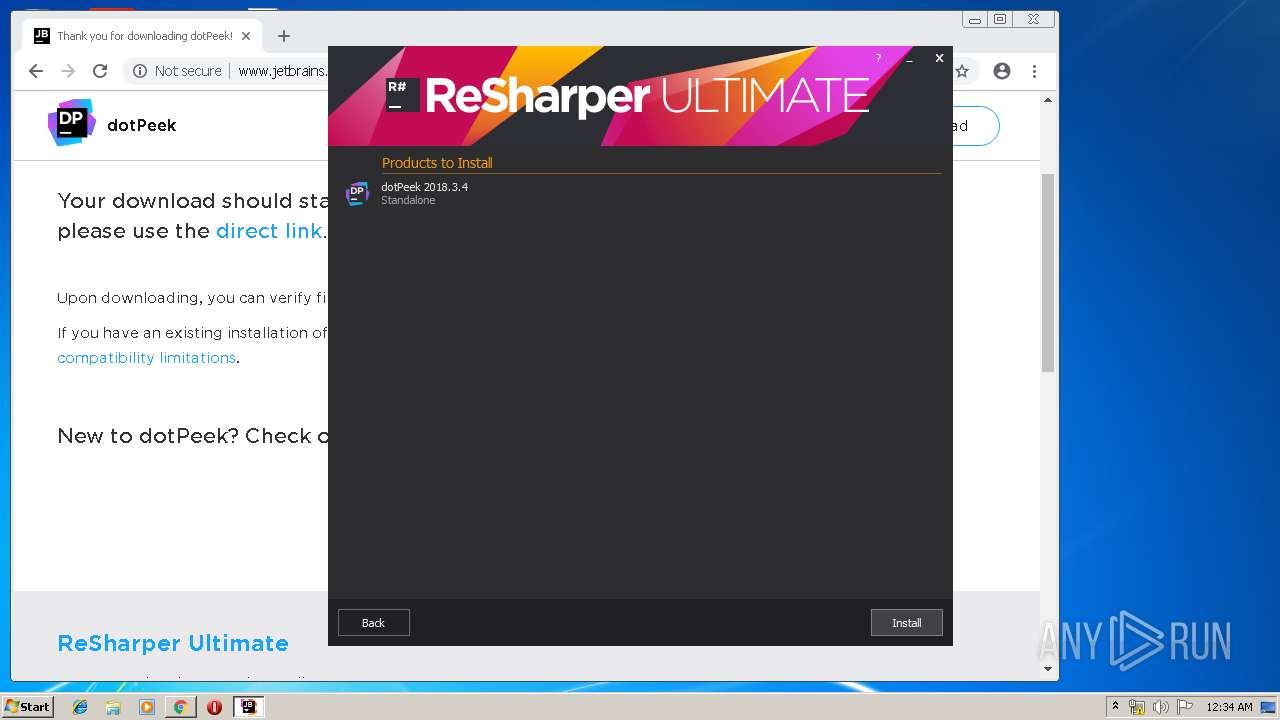
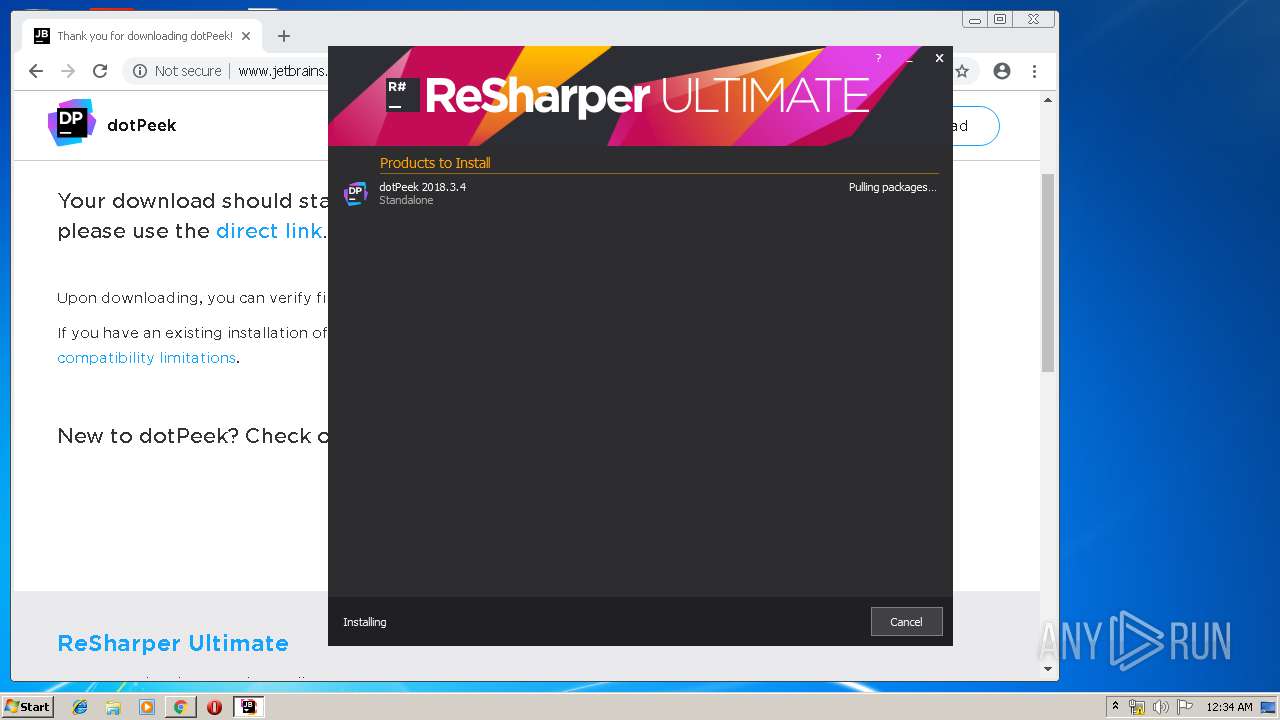
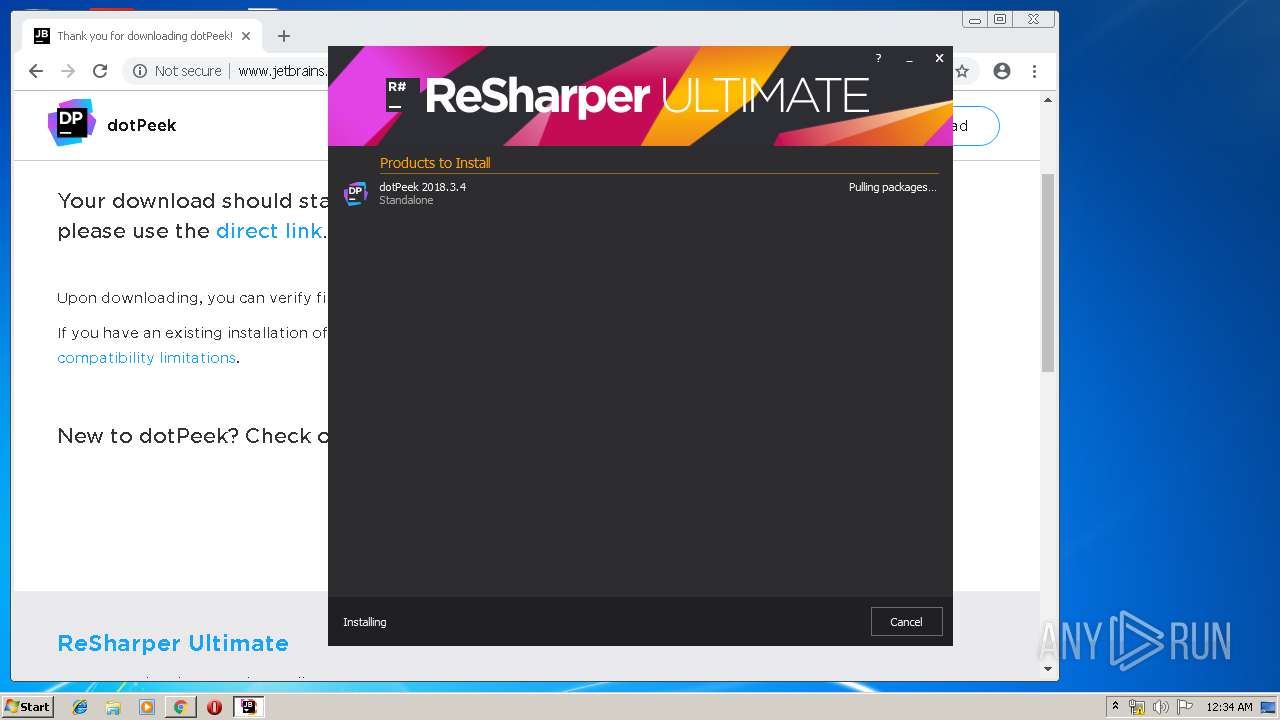
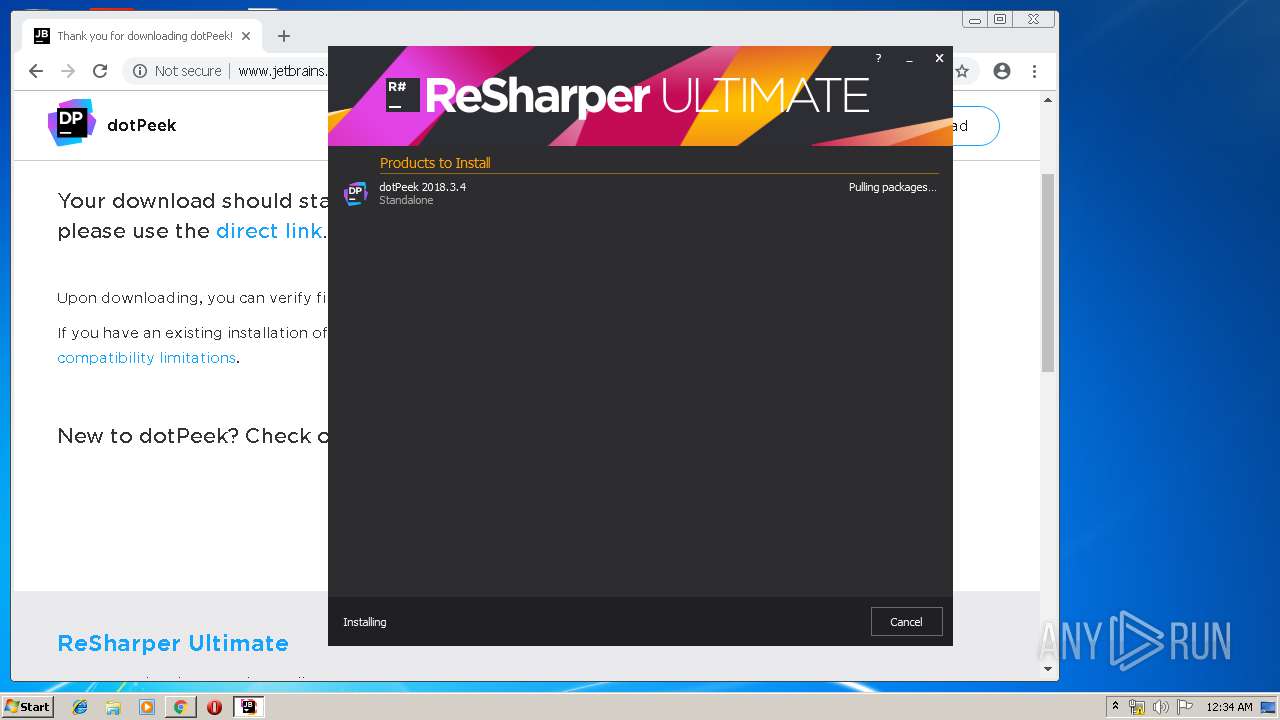
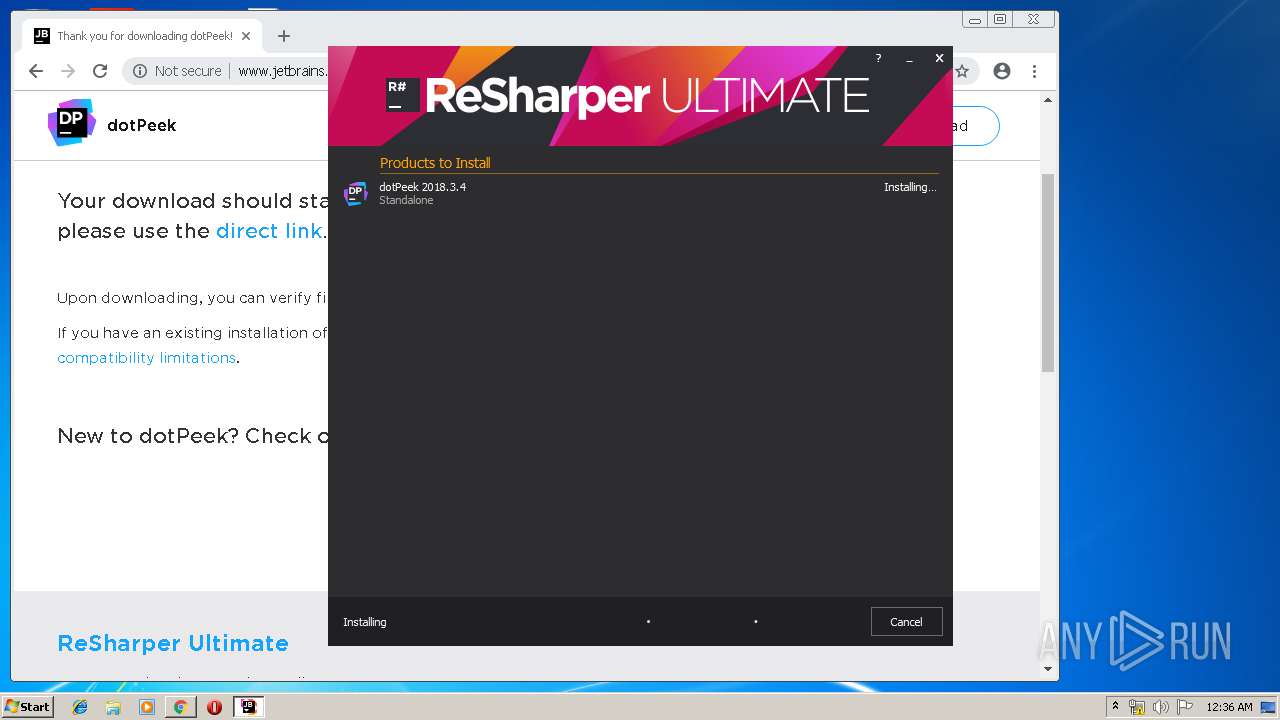
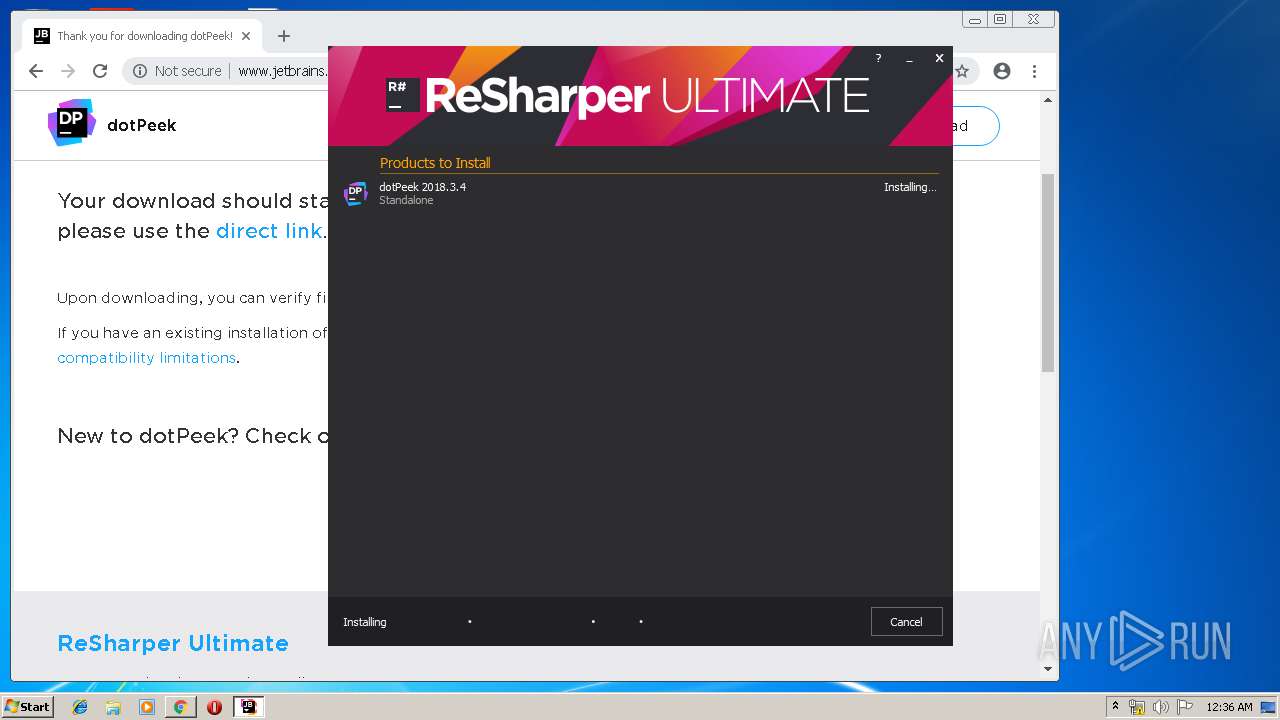
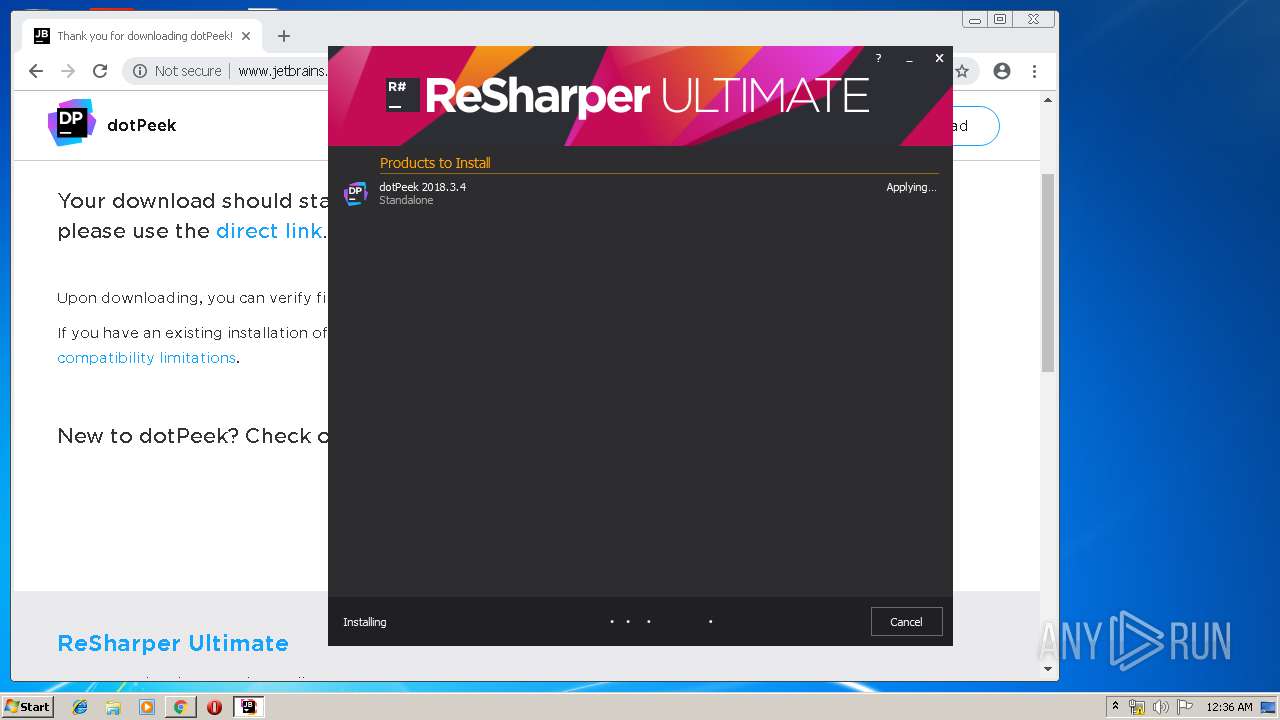
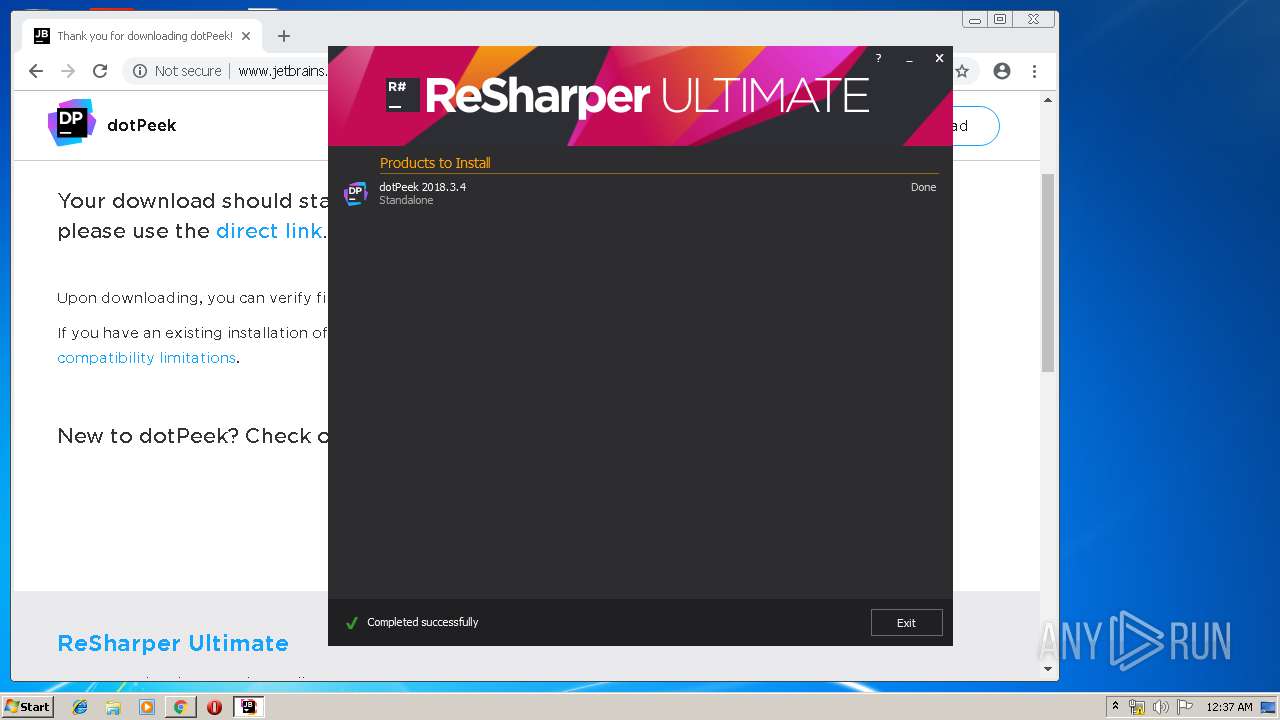
Application was dropped or rewritten from another process
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
Loads dropped or rewritten executable
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1860)
Executable content was dropped or overwritten
- chrome.exe (PID: 1860)
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
Creates files in the program directory
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
Reads Environment values
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
Creates a software uninstall entry
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
Creates files in the user directory
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
INFO
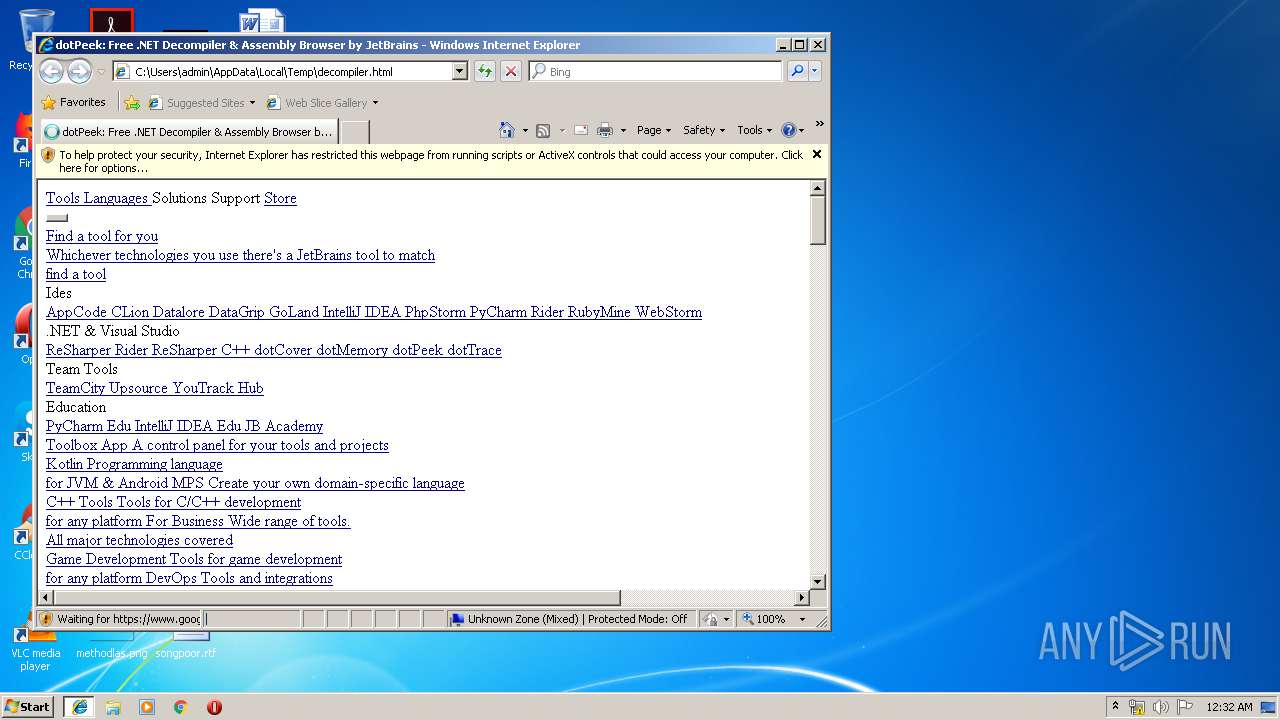
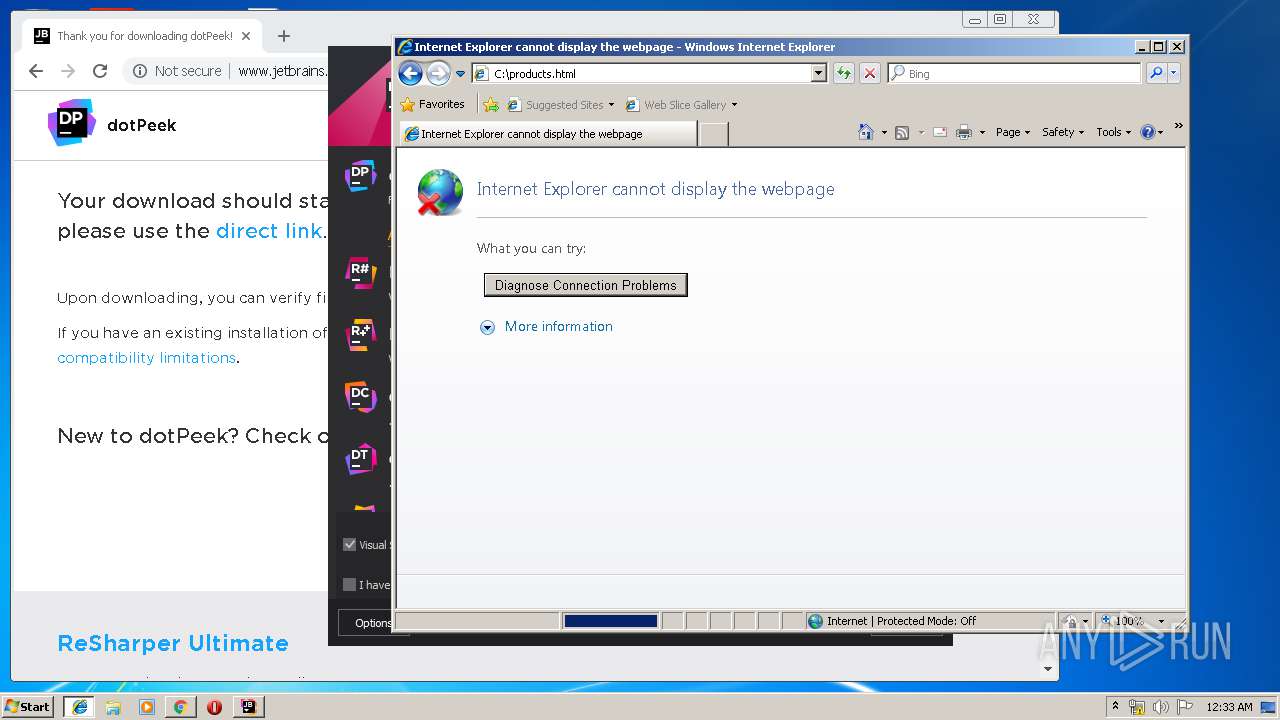
Changes internet zones settings
- iexplore.exe (PID: 2516)
Creates files in the user directory
- iexplore.exe (PID: 3708)
- iexplore.exe (PID: 2516)
Application launched itself
- iexplore.exe (PID: 2516)
- chrome.exe (PID: 1860)
Reads internet explorer settings
- iexplore.exe (PID: 3708)
Reads settings of System Certificates
- chrome.exe (PID: 1860)
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
Reads Internet Cache Settings
- iexplore.exe (PID: 3708)
- chrome.exe (PID: 1860)
Dropped object may contain Bitcoin addresses
- JetBrains.dotPeek.2018.3.4.web.exe (PID: 596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
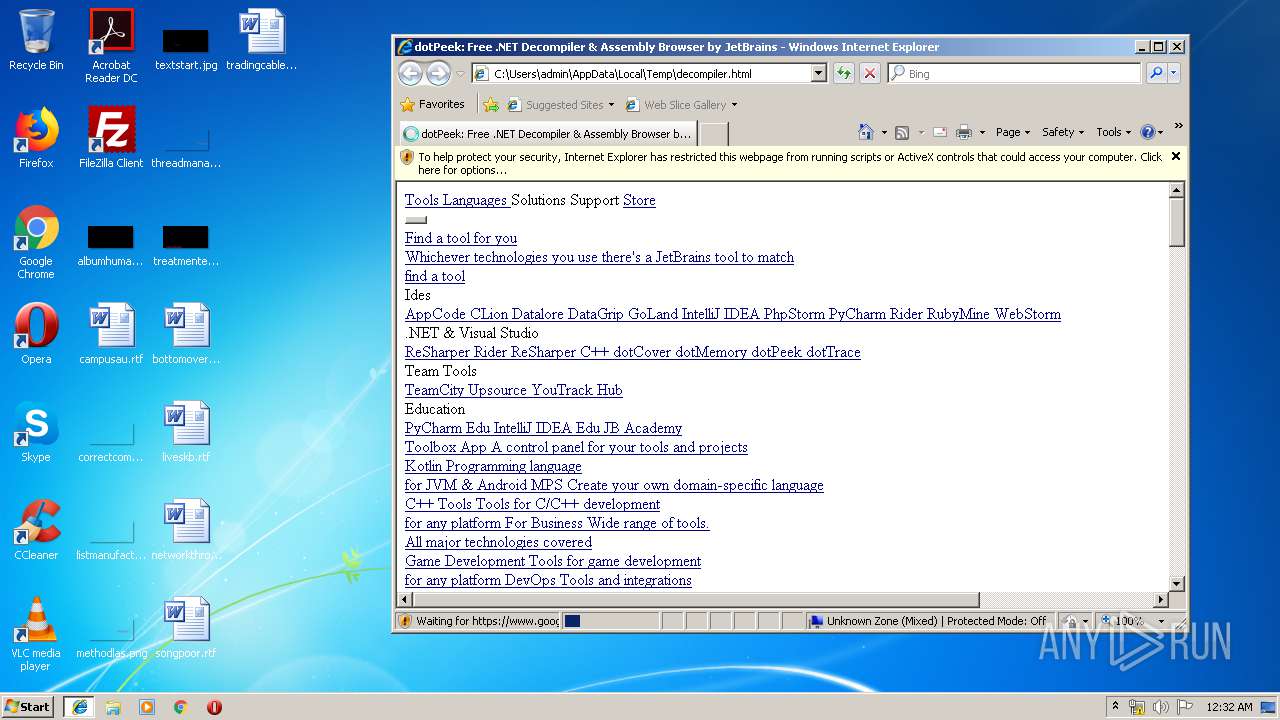
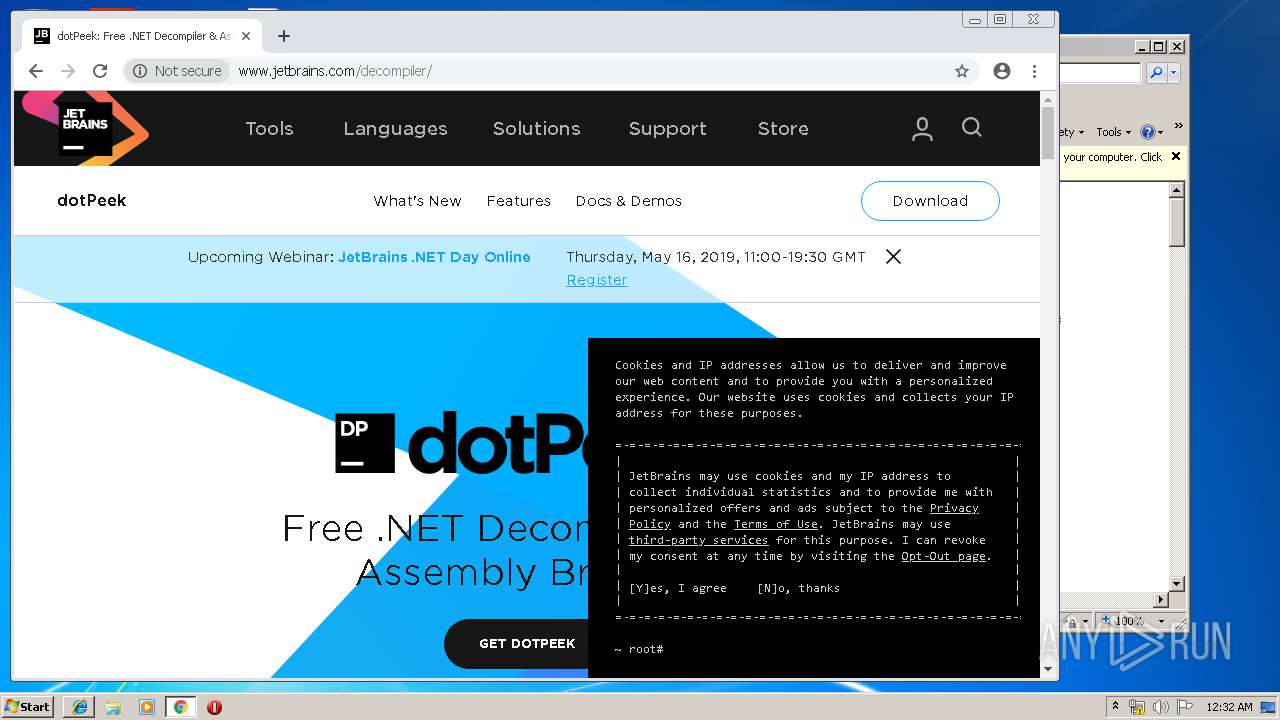
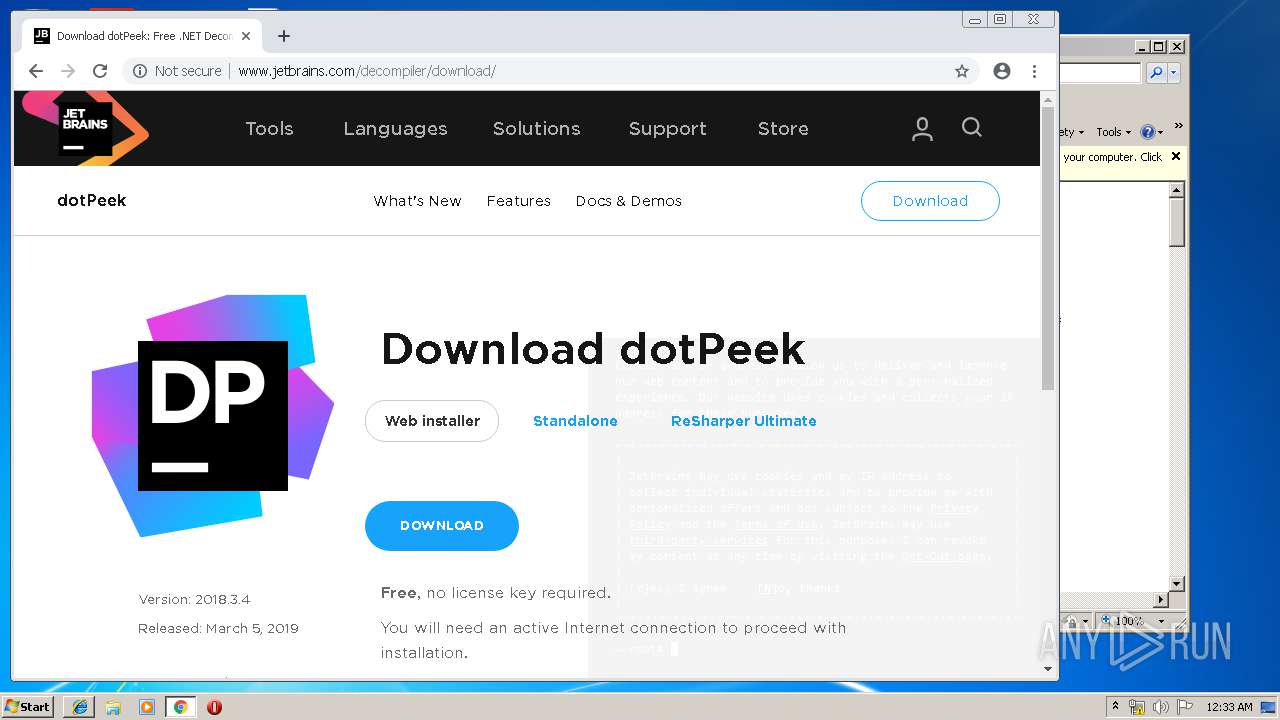
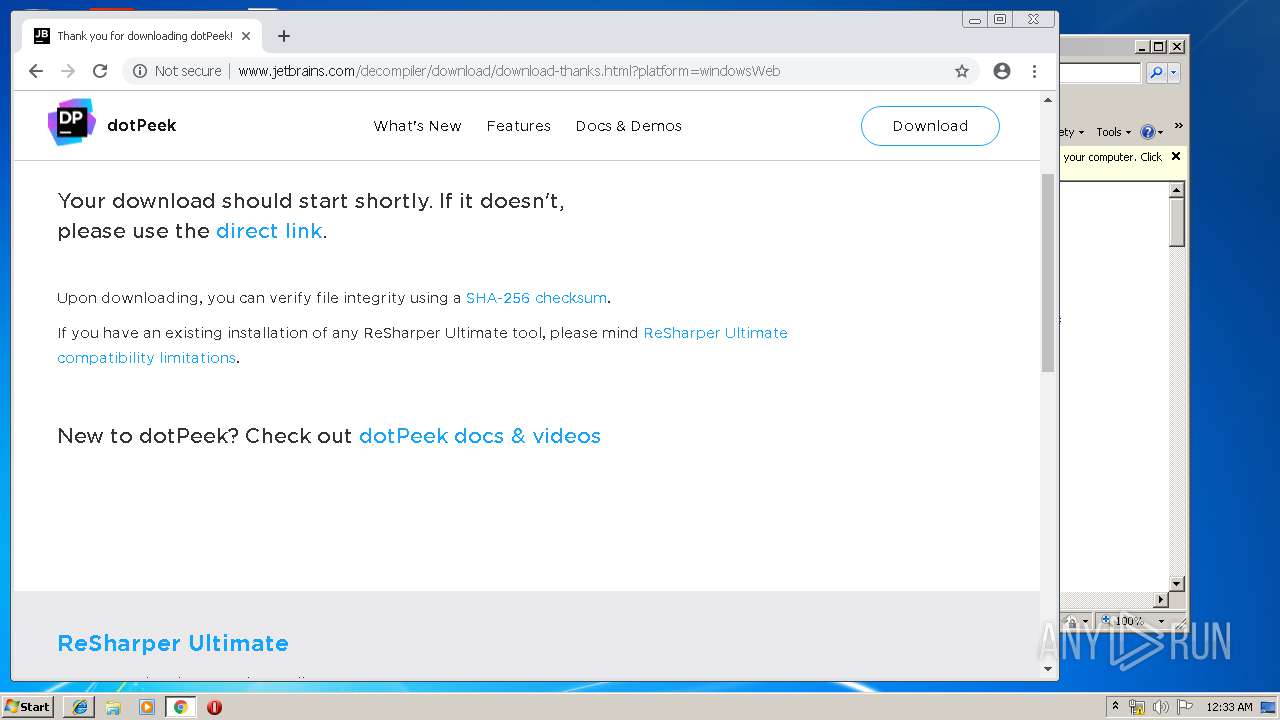
| Title: | dotPeek: Free .NET Decompiler & Assembly Browser by JetBrains |
|---|---|
| HTTPEquivXUaCompatible: | IE=edge |
| viewport: | width=device-width, maximum-scale=1 |
| appleMobileWebAppTitle: | JetBrains |
| applicationName: | JetBrains |
| msapplicationTileColor: | #000000 |
| themeColor: | #000000 |
| Description: | dotPeek is a free tool based on ReSharper. It can reliably decompile any .NET assembly into C# or IL code. |
| image: | http://resources.jetbrains.com/storage/products/dotpeek/img/meta/dotpeek_1280x800.png |
| twitterCard: | summary_large_image |
| twitterSite: | @dotPeek |
| twitterTitle: | dotPeek: Free .NET Decompiler & Assembly Browser by JetBrains |
| twitterDescription: | dotPeek is a free tool based on ReSharper. It can reliably decompile any .NET assembly into C# or IL code. |
| twitterCreator: | @dotPeek |
| twitterImageSrc: | http://resources.jetbrains.com/storage/products/dotpeek/img/meta/dotpeek_1280x800.png |
| twitterLabel1: | Platforms: |
| twitterData1: | Windows |
| twitterLabel2: | Rating: |
| twitterData2: | Awesome |
Total processes
56
Monitored processes
23
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15039991702979276501,563054637220489990,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13925129012887188711 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13925129012887188711 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15039991702979276501,563054637220489990,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12343166544028711432 --mojo-platform-channel-handle=4372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
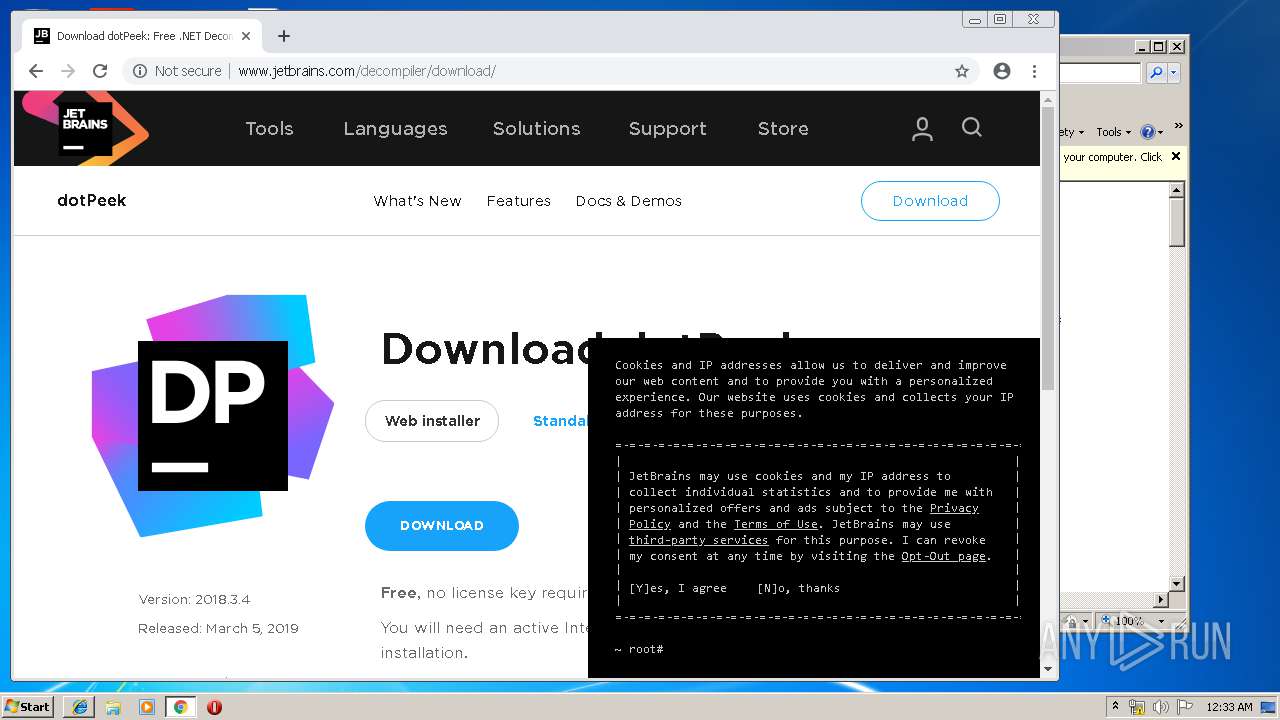
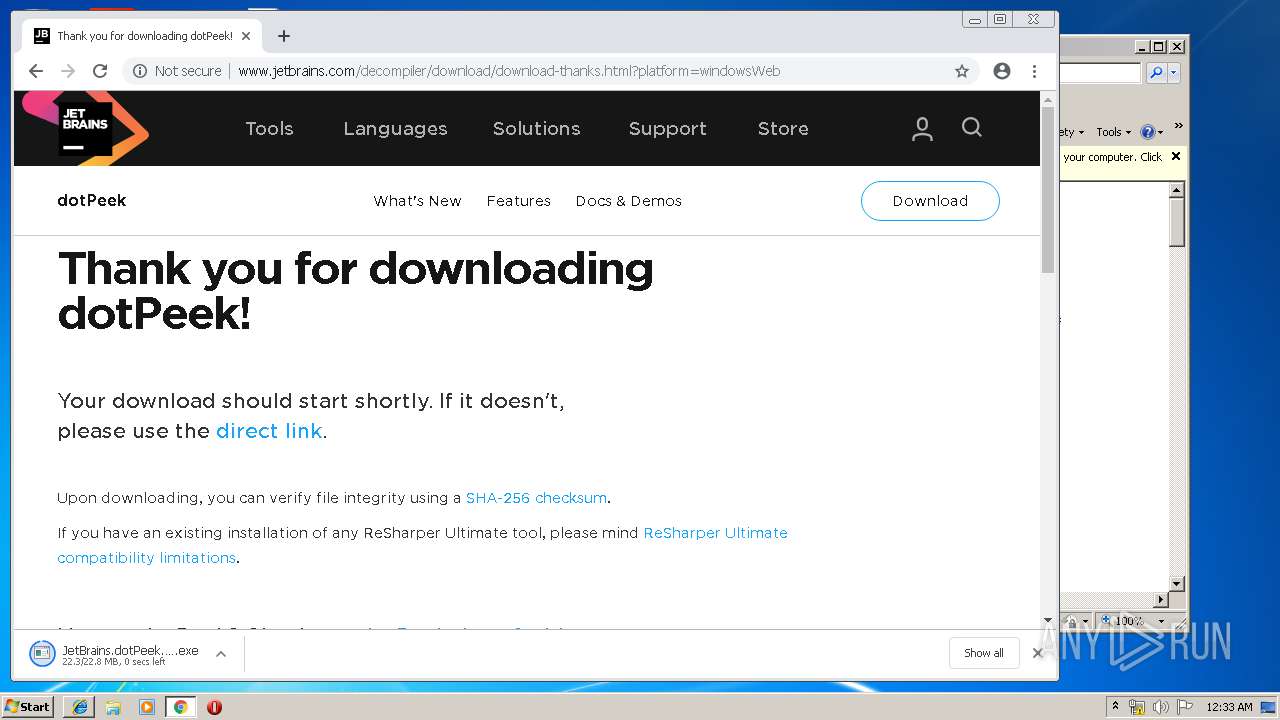
| 596 | "C:\Users\admin\Downloads\JetBrains.dotPeek.2018.3.4.web.exe" | C:\Users\admin\Downloads\JetBrains.dotPeek.2018.3.4.web.exe | chrome.exe | ||||||||||||
User: admin Company: JetBrains Integrity Level: MEDIUM Description: JetBrains dotPeek 2018.3.4 Web Installer Exit code: 0 Version: 183.0.20190304.75654 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15039991702979276501,563054637220489990,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17551315803534400751 --mojo-platform-channel-handle=4036 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15039991702979276501,563054637220489990,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10420209771247212121 --mojo-platform-channel-handle=2620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1916 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15039991702979276501,563054637220489990,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12153596967666183385 --mojo-platform-channel-handle=4300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15039991702979276501,563054637220489990,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12142449884070497577 --mojo-platform-channel-handle=4124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,15039991702979276501,563054637220489990,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16742853597768360605 --mojo-platform-channel-handle=4192 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 792
Read events
1 586
Write events
200
Delete events
6
Modification events
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {0518E9FD-6620-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307040002001700170020000D004A03 | |||
Executable files
393
Suspicious files
175
Text files
1 211
Unknown types
70
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cd4b9de3-c768-4c80-b265-e91fd5cef130.tmp | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
45
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1860 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 508 b | whitelisted |
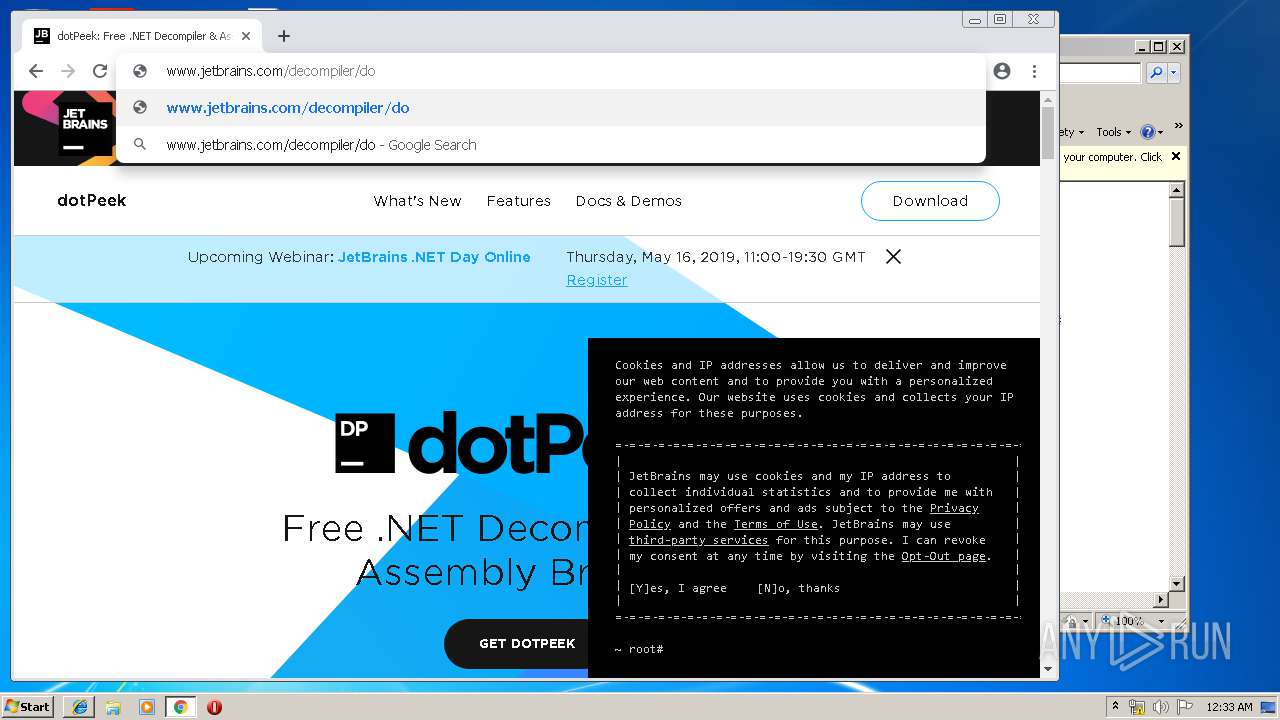
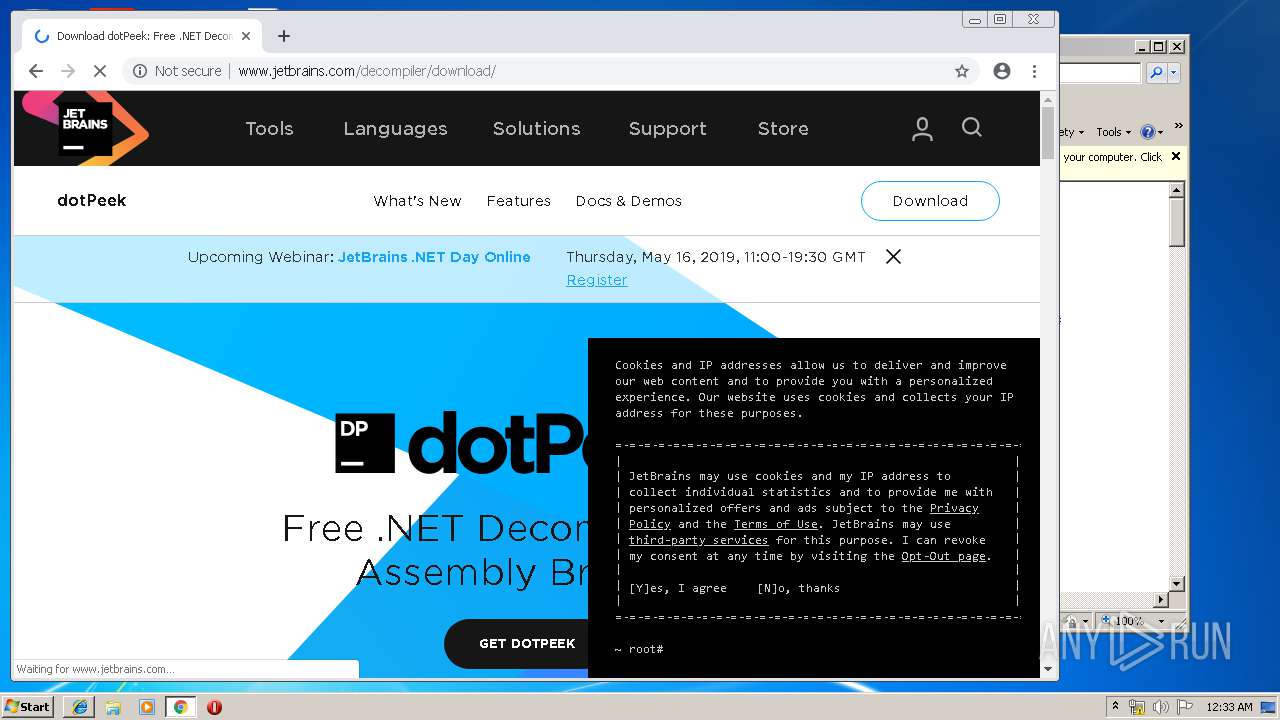
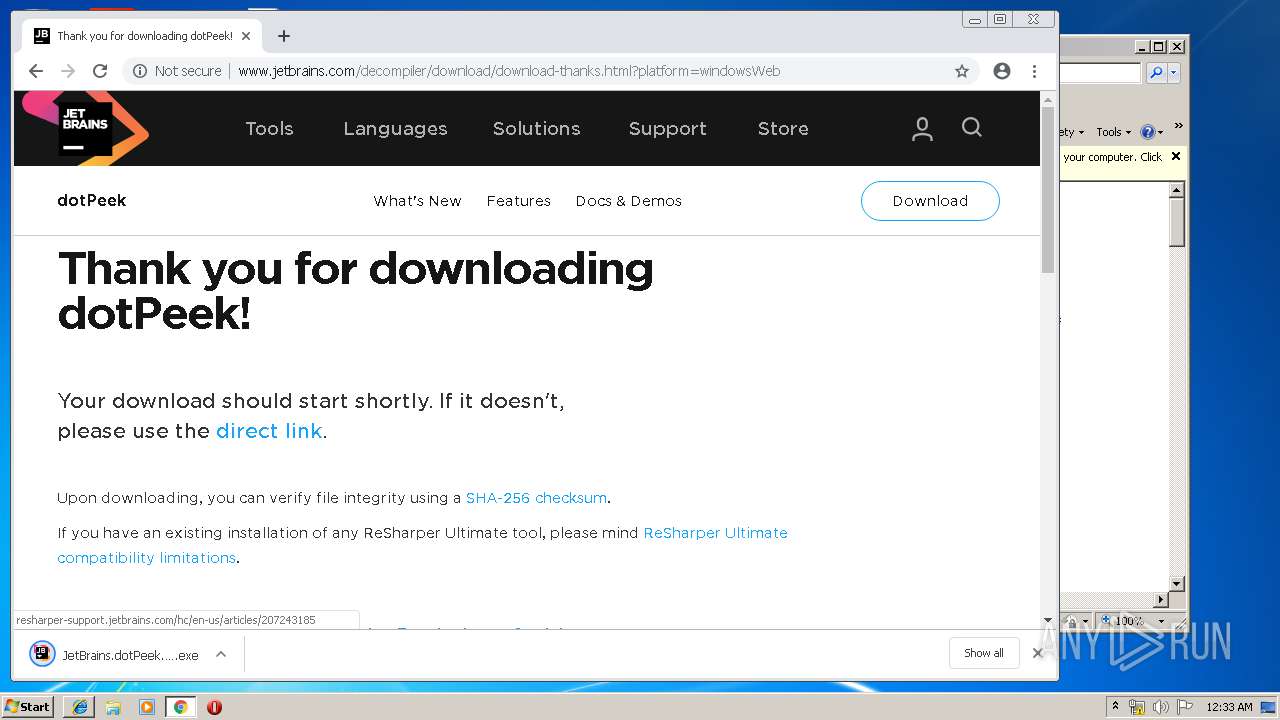
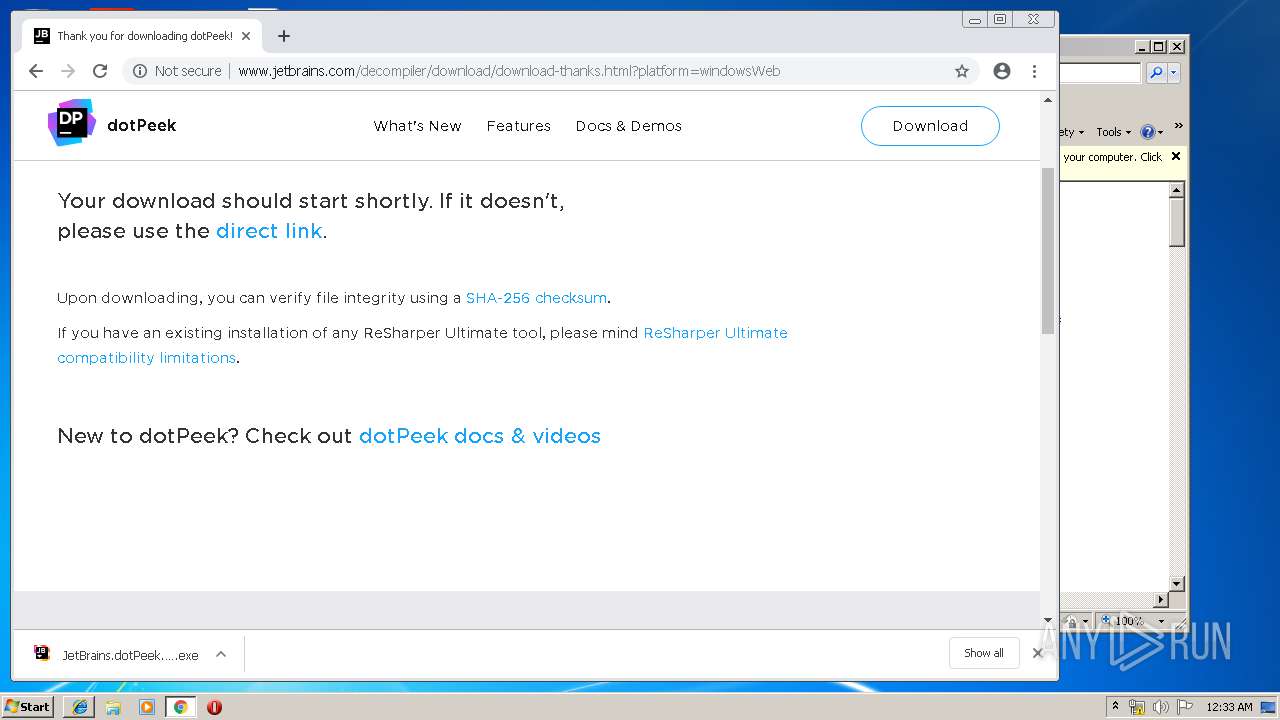
1860 | chrome.exe | GET | 200 | 54.171.36.92:80 | http://www.jetbrains.com/decompiler/ | IE | html | 14.8 Kb | suspicious |
1860 | chrome.exe | GET | 200 | 194.9.25.78:80 | http://r3---sn-5uh5o-f5fs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.219.109&mm=28&mn=sn-5uh5o-f5fs&ms=nvh&mt=1556061560&mv=u&pl=24&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
1860 | chrome.exe | GET | 200 | 54.171.36.92:80 | http://www.jetbrains.com/_assets/common.71a4398a44ff792e8f31b2398ec3241e.css | IE | text | 56.2 Kb | suspicious |
1860 | chrome.exe | GET | 200 | 54.171.36.92:80 | http://www.jetbrains.com/_assets/decompiler/index.entry.2aa07ad38aa3464dfca79df812fb2496.css | IE | text | 327 b | suspicious |
1860 | chrome.exe | GET | 200 | 54.171.36.92:80 | http://www.jetbrains.com/_assets/default-page.73edaeadfa147c426fbb9c7f52602063.css | IE | text | 16.5 Kb | suspicious |
1860 | chrome.exe | GET | 200 | 54.171.36.92:80 | http://www.jetbrains.com/_assets/banner-rotator.entry.9bcd98acf978b2fc69e0712fcc1da802.css | IE | text | 4.82 Kb | suspicious |
1860 | chrome.exe | GET | 200 | 54.171.36.92:80 | http://www.jetbrains.com/_assets/common.5d59f0417df51bb7f411.js | IE | text | 722 Kb | suspicious |
1860 | chrome.exe | GET | 200 | 54.171.36.92:80 | http://www.jetbrains.com/_assets/default-page.24dbac2b9d885d4c377a.js | IE | text | 92.3 Kb | suspicious |
1860 | chrome.exe | GET | 200 | 54.171.36.92:80 | http://www.jetbrains.com/_assets/decompiler/index.entry.5a497138c63c098682b9.js | IE | text | 1.80 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3708 | iexplore.exe | 172.217.16.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2516 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1860 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1860 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1860 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1860 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
1860 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1860 | chrome.exe | 216.58.205.238:443 | apis.google.com | Google Inc. | US | whitelisted |
1860 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1860 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | <unnamed-thread>:1 | Added omnipresent logger with type [JetBrains.UI.Application.LogEventListener] and level [INFO]. Filters: <len=1>[BurstFilter[level=ERROR, rate=5]]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | <unnamed-thread>:1 | Added omnipresent logger with type [JetBrains.Util.Logging.FileLogEventListener] and level [VERBOSE]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | <unnamed-thread>:13 | Added omnipresent logger with type [JetBrains.Util.Logging.FileLogEventListener] and level [VERBOSE]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | JetPool(L) #1:20 | Added omnipresent logger with type [JetBrains.Build.Engine.IsolatedBuild.IsolatedBuildGuest+BuildLogEventListener] and level [VERBOSE]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | JetPool(L) #1:20 | Added omnipresent logger with type [JetBrains.Util.Logging.FileLogEventListener] and level [INFO]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | JetPool(L) #1:20 | Added omnipresent logger with type [JetBrains.Util.Logging.FileLogEventListener] and level [VERBOSE]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | JetPool(L) #1:20 | Removed omnipresent logger with type [JetBrains.Util.Logging.FileLogEventListener] and level [VERBOSE]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | JetPool(L) #1:20 | Removed omnipresent logger with type [JetBrains.Build.Engine.IsolatedBuild.IsolatedBuildGuest+BuildLogEventListener] and level [VERBOSE]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | JetPool(L) #1:20 | Removed omnipresent logger with type [JetBrains.Build.Engine.IsolatedBuild.IsolatedBuildGuest+BuildLogEventListener] and level [VERBOSE]
|
JetBrains.dotPeek.2018.3.4.web.exe | I| --LOGLOG:Logger-- | <unnamed-thread>:13 | Removed omnipresent logger with type [JetBrains.Util.Logging.FileLogEventListener] and level [VERBOSE]
|