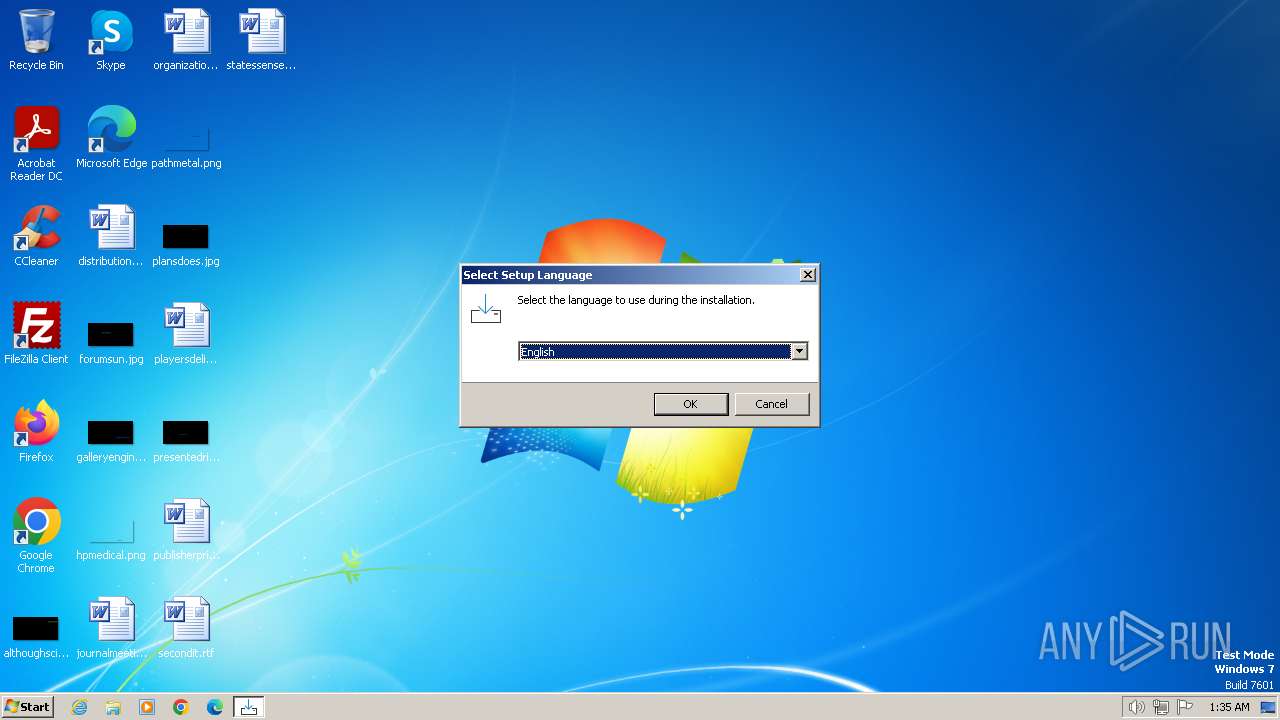
| File name: | mysetup.exe |
| Full analysis: | https://app.any.run/tasks/25bb5e31-1cd0-4d1b-b4f6-dd9a39ccb265 |
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2023, 01:35:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CC3BB487D5B9B08DE17CA261CBFEC62C |
| SHA1: | BD0491549EB7933B9BC66FE38391DC6F79C30703 |
| SHA256: | 98DBCEF30905DD2441039240BB994D5E19D3D30FFBDDC3613C6101D6B8276A84 |
| SSDEEP: | 98304:5+QqZ8fZIWHvDhkm84D0pf7FltCaWnJbql1nPfnWOVHYEnQ9FBeEnX3iRBJ8k2R8:2/ |
MALICIOUS
Runs injected code in another process
- MODULESUPDATE.EXE (PID: 712)
Create files in the Startup directory
- explorer.exe (PID: 2760)
SUSPICIOUS
Reads the Windows owner or organization settings
- mysetup.tmp (PID: 1380)
Reads the Internet Settings
- puller.exe (PID: 1840)
- MODULESUPDATE.EXE (PID: 1596)
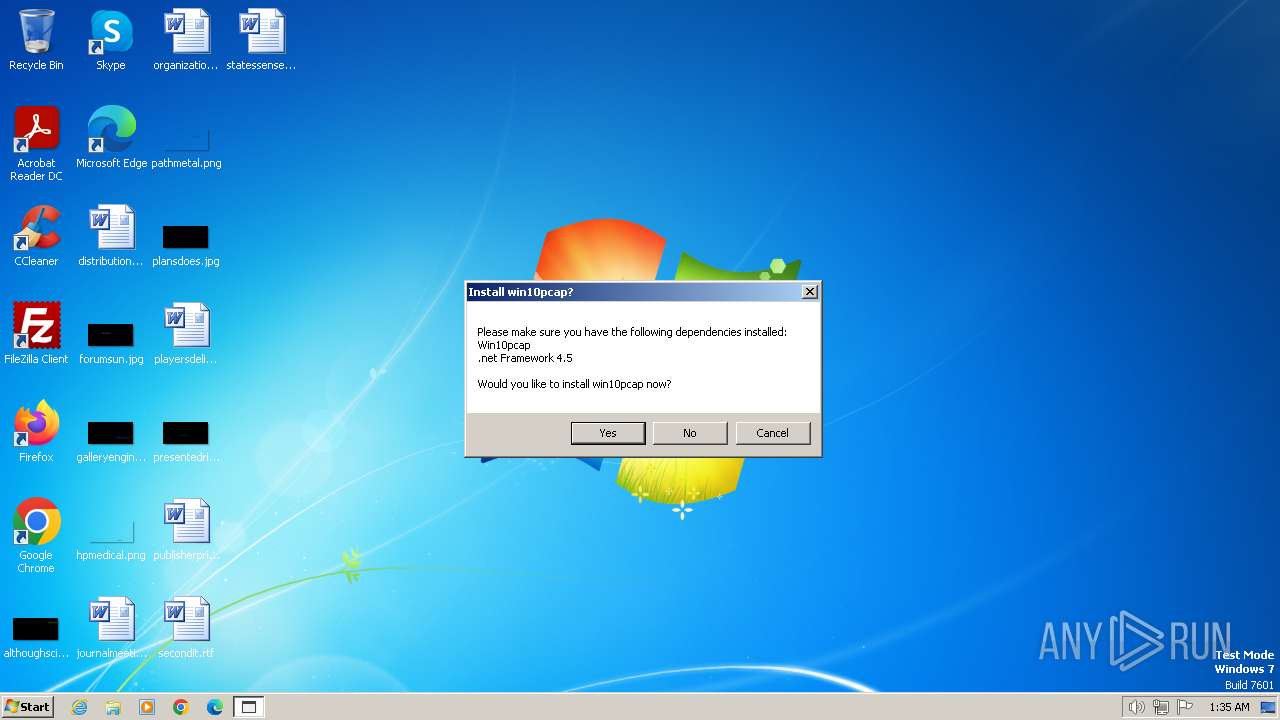
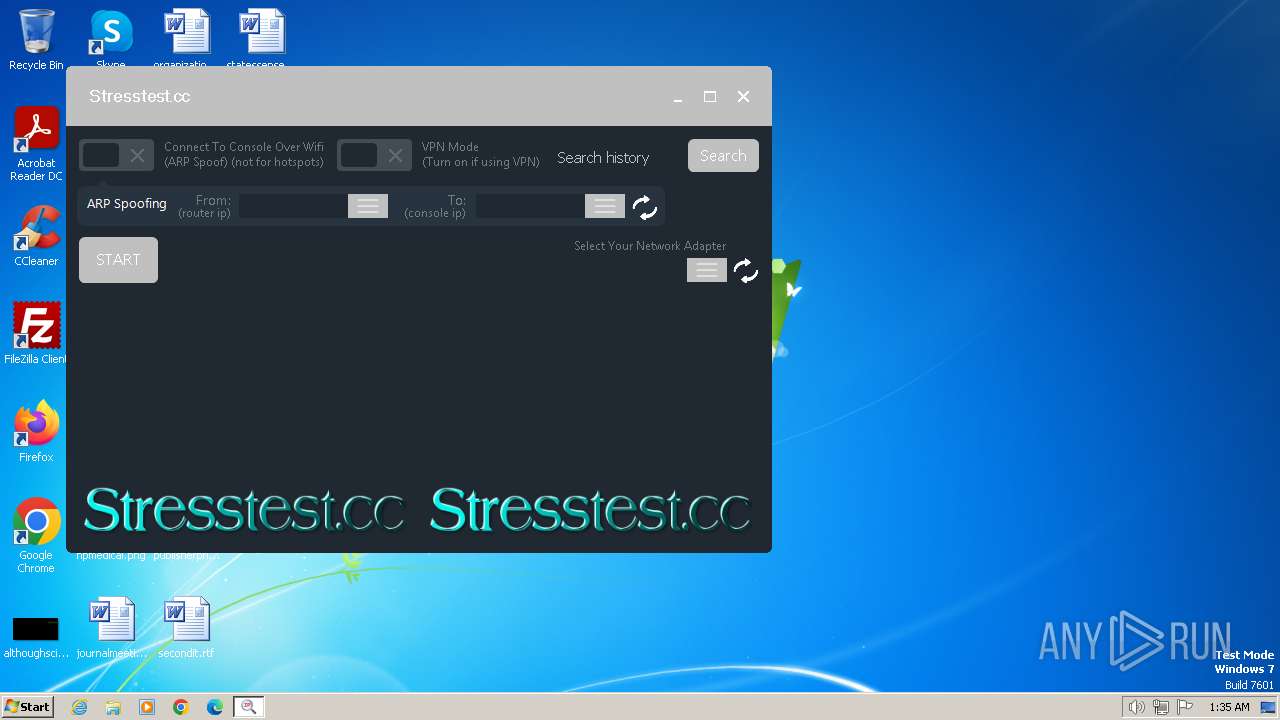
- STRESSTEST.EXE (PID: 2480)
- MODULESUPDATE.EXE (PID: 712)
- svchost.exe (PID: 908)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 2168)
- powershell.exe (PID: 2544)
The process creates files with name similar to system file names
- MODULESUPDATE.EXE (PID: 712)
- explorer.exe (PID: 2760)
Starts POWERSHELL.EXE for commands execution
- MODULESUPDATE.EXE (PID: 1596)
- svchost.exe (PID: 908)
INFO
Checks supported languages
- mysetup.exe (PID: 2016)
- mysetup.exe (PID: 128)
- mysetup.tmp (PID: 1776)
- mysetup.tmp (PID: 1380)
- puller.exe (PID: 1840)
- MODULESUPDATE.EXE (PID: 1596)
- MODULESUPDATE.EXE (PID: 712)
- svchost.exe (PID: 908)
- STRESSTEST.EXE (PID: 2480)
Create files in a temporary directory
- mysetup.exe (PID: 2016)
- mysetup.exe (PID: 128)
- MODULESUPDATE.EXE (PID: 712)
- explorer.exe (PID: 2760)
Reads the computer name
- mysetup.tmp (PID: 1776)
- mysetup.tmp (PID: 1380)
- MODULESUPDATE.EXE (PID: 1596)
- puller.exe (PID: 1840)
- MODULESUPDATE.EXE (PID: 712)
- STRESSTEST.EXE (PID: 2480)
- svchost.exe (PID: 908)
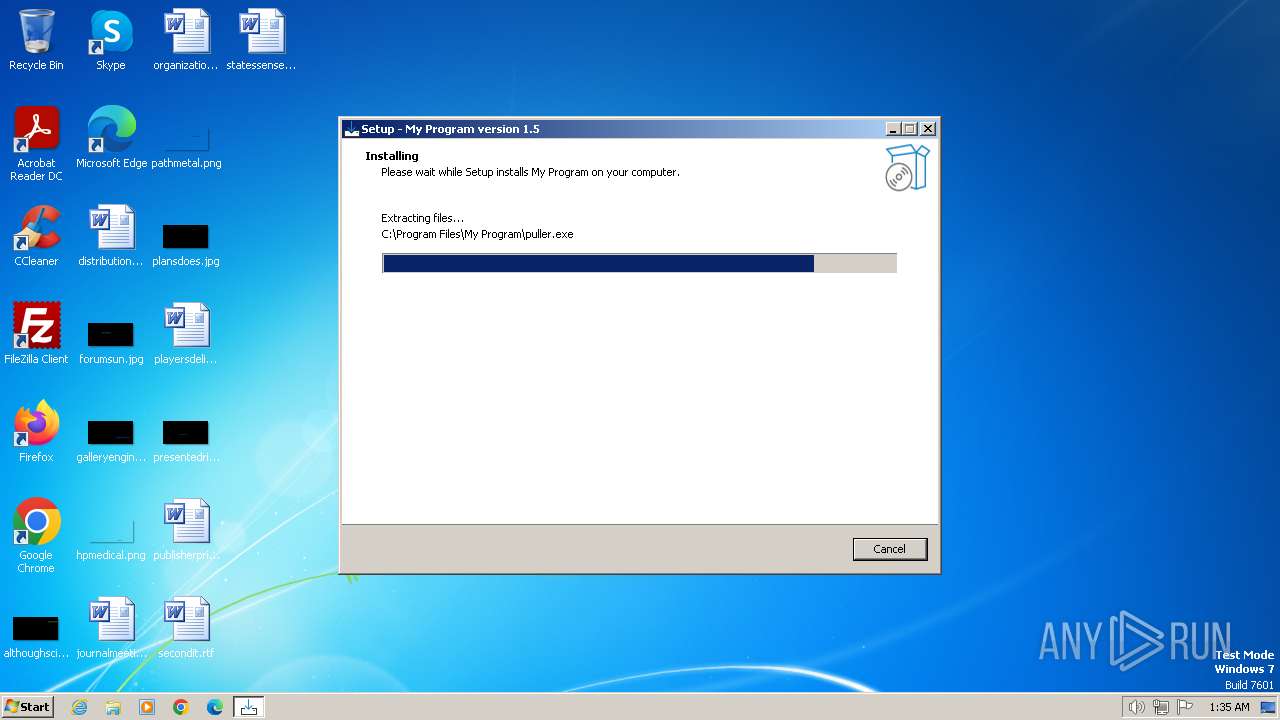
Drops the executable file immediately after the start
- mysetup.exe (PID: 128)
- mysetup.exe (PID: 2016)
- mysetup.tmp (PID: 1380)
- puller.exe (PID: 1840)
- explorer.exe (PID: 1164)
- MODULESUPDATE.EXE (PID: 712)
- explorer.exe (PID: 2760)
Creates files or folders in the user directory
- puller.exe (PID: 1840)
- explorer.exe (PID: 2760)
- STRESSTEST.EXE (PID: 2480)
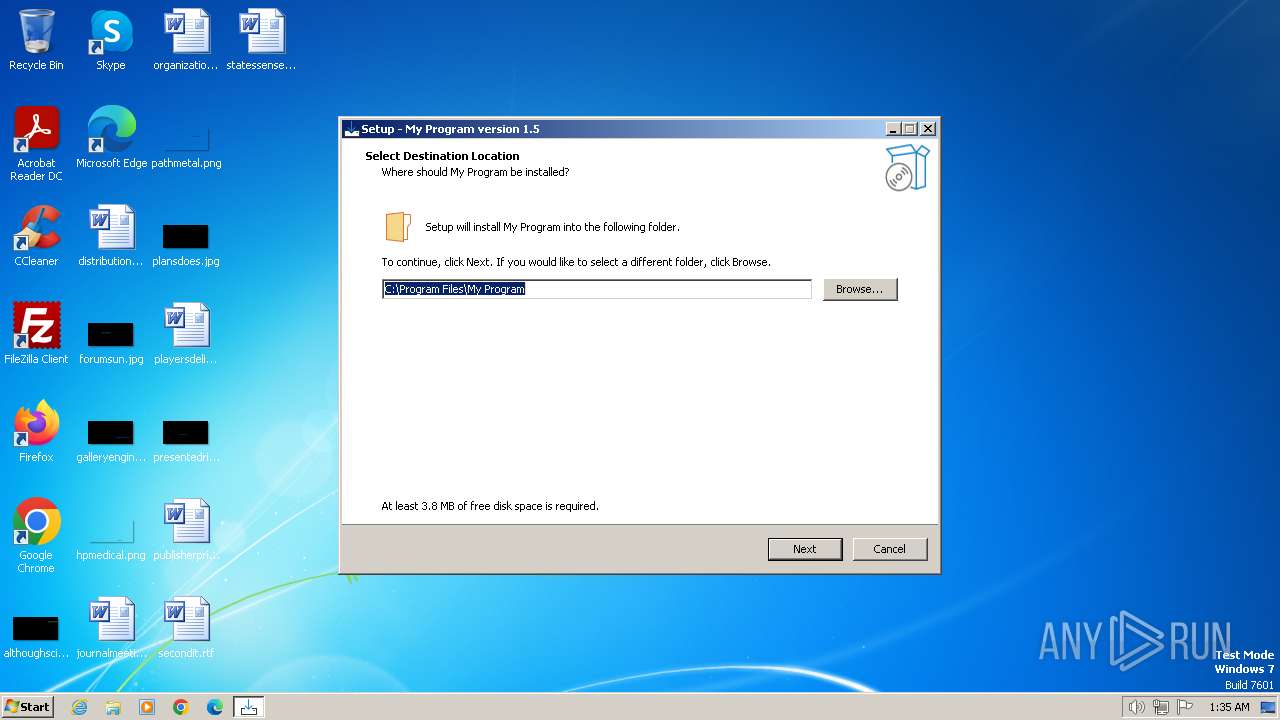
Creates files in the program directory
- mysetup.tmp (PID: 1380)
Reads the machine GUID from the registry
- STRESSTEST.EXE (PID: 2480)
Application was injected by another process
- explorer.exe (PID: 1164)
Starts itself from another location
- MODULESUPDATE.EXE (PID: 712)
The process creates files with name similar to system file names
- explorer.exe (PID: 1164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:03 10:09:11+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 89088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | My Company, Inc. |
| FileDescription: | My Program Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | My Program |
| ProductVersion: | 1.5 |
Total processes
55
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\AppData\Local\Temp\mysetup.exe" | C:\Users\admin\AppData\Local\Temp\mysetup.exe | — | explorer.exe | |||||||||||
User: admin Company: My Company, Inc. Integrity Level: MEDIUM Description: My Program Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 712 | "C:\Users\admin\AppData\Local\MODULESUPDATE.EXE" | C:\Users\admin\AppData\Local\MODULESUPDATE.EXE | — | puller.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 908 | "C:\install\svchost.exe" | C:\install\svchost.exe | — | MODULESUPDATE.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1164 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
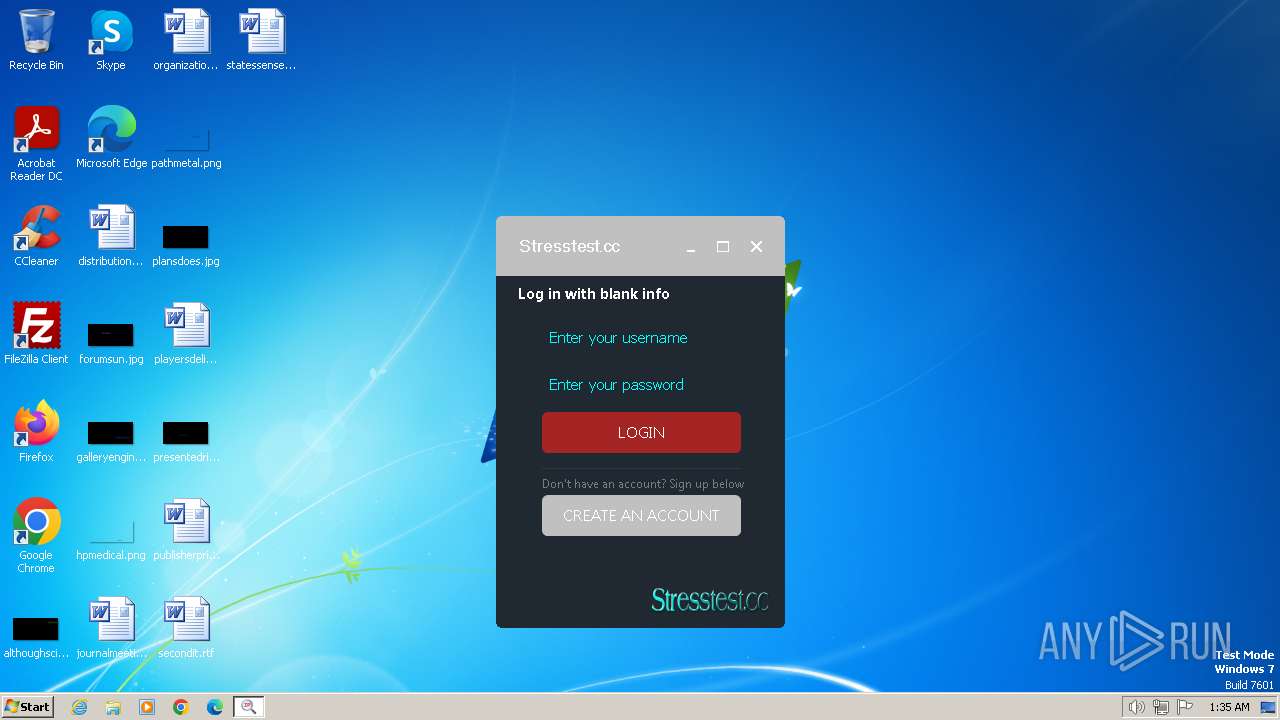
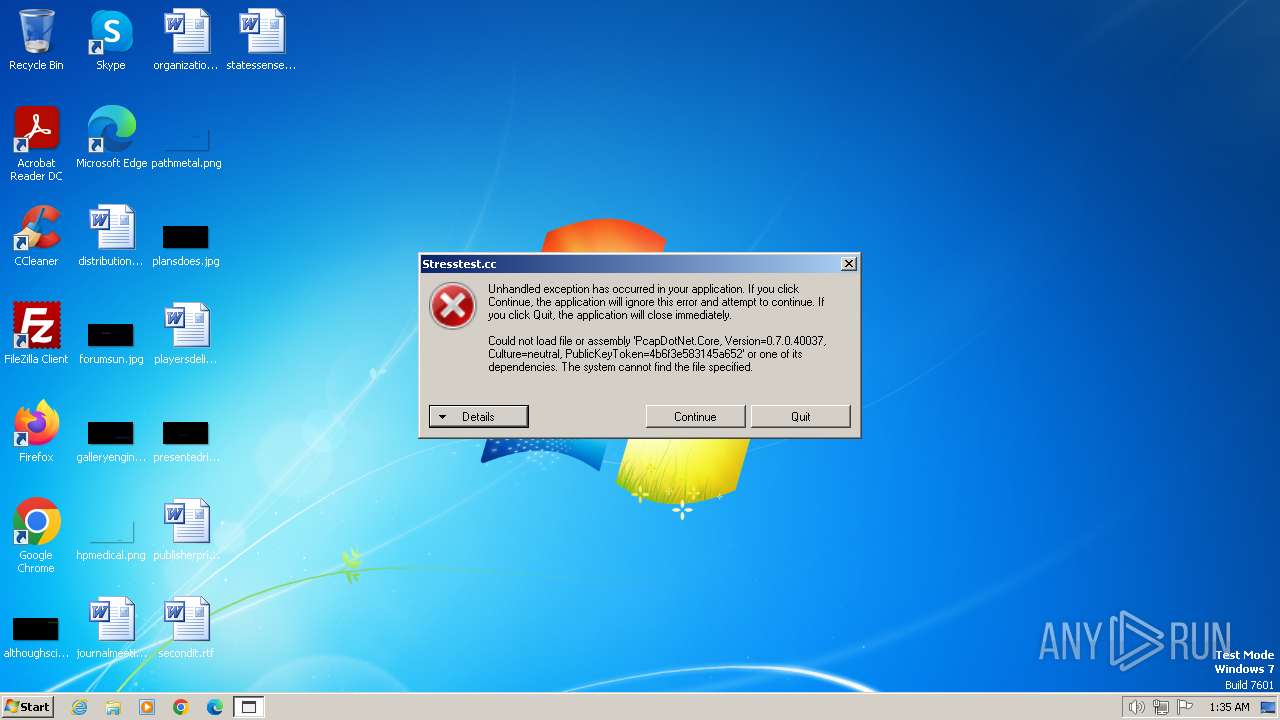
| 1264 | "C:\Users\admin\AppData\Local\STRESSTEST.EXE" | C:\Users\admin\AppData\Local\STRESSTEST.EXE | — | puller.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: IP Grabber Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1380 | "C:\Users\admin\AppData\Local\Temp\is-C9LD5.tmp\mysetup.tmp" /SL5="$501AC,1591861,831488,C:\Users\admin\AppData\Local\Temp\mysetup.exe" /SPAWNWND=$501B2 /NOTIFYWND=$301AA | C:\Users\admin\AppData\Local\Temp\is-C9LD5.tmp\mysetup.tmp | — | mysetup.exe | |||||||||||
User: admin Company: My Company, Inc. Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1596 | "C:\Users\admin\AppData\Local\MODULESUPDATE.EXE" | C:\Users\admin\AppData\Local\MODULESUPDATE.EXE | — | puller.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1776 | "C:\Users\admin\AppData\Local\Temp\is-1732Q.tmp\mysetup.tmp" /SL5="$301AA,1591861,831488,C:\Users\admin\AppData\Local\Temp\mysetup.exe" | C:\Users\admin\AppData\Local\Temp\is-1732Q.tmp\mysetup.tmp | — | mysetup.exe | |||||||||||
User: admin Company: My Company, Inc. Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\My Program\puller.exe" | C:\Program Files\My Program\puller.exe | mysetup.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2016 | "C:\Users\admin\AppData\Local\Temp\mysetup.exe" /SPAWNWND=$501B2 /NOTIFYWND=$301AA | C:\Users\admin\AppData\Local\Temp\mysetup.exe | mysetup.tmp | ||||||||||||
User: admin Company: My Company, Inc. Integrity Level: HIGH Description: My Program Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
6 471
Read events
6 395
Write events
67
Delete events
9
Modification events
| (PID) Process: | (1164) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000DBDD10622BD67741A42163F361389C4700000000020000000000106600000001000020000000714C0B985B0540658F4A2080B484A48FEA0193B4945278E76DEADC9EF300F178000000000E80000000020000200000002B477AD6A48910EDA2BF44A8E4FAAFB7E2EDF3EE6F87B8965B303D8016BD90EA30000000CB02147CAA96DADF9F5A3BD08AC8A954F632048A3EC443FAA534C64E43A96953CAB4A202A2BC0443ADBC5B693897DBB44000000078BCD17E1DCD91E99A86D38616C049FA8C5E2A7C07BB269B76B0709DC8A01ABF25866BF6638D5C4422D1151CE173748901F5A2433E1BD07914E254B07BB130FD | |||
| (PID) Process: | (1380) mysetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 115 | |||
| (PID) Process: | (1164) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1164) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1840) puller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1840) puller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1840) puller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1840) puller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1596) MODULESUPDATE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1596) MODULESUPDATE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
11
Suspicious files
8
Text files
188
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2016 | mysetup.exe | C:\Users\admin\AppData\Local\Temp\is-C9LD5.tmp\mysetup.tmp | executable | |
MD5:266673B16AB08A498DEB528139DC7213 | SHA256:C6FA242B88805720DAF185DB905717FF44F23086BB89F3409F100D4F80D95D3F | |||
| 128 | mysetup.exe | C:\Users\admin\AppData\Local\Temp\is-1732Q.tmp\mysetup.tmp | executable | |
MD5:266673B16AB08A498DEB528139DC7213 | SHA256:C6FA242B88805720DAF185DB905717FF44F23086BB89F3409F100D4F80D95D3F | |||
| 1380 | mysetup.tmp | C:\Program Files\My Program\is-CALP8.tmp | executable | |
MD5:9B889DA9A069AE4E48F47E4D150ED65C | SHA256:96B6B0B81B3E2711DA54F6F8A18CA3CA181783D150C6F3268D12B86A44CA9A6C | |||
| 1380 | mysetup.tmp | C:\Program Files\My Program\is-96Q8C.tmp | executable | |
MD5:2E9C93255CFD04F6D5DA6FE8E6BF909D | SHA256:9F195D1DBEE9D8400A6A25D6531838629466C5443881DCD3895140B68A3F8C21 | |||
| 1380 | mysetup.tmp | C:\Program Files\My Program\unins000.exe | executable | |
MD5:9B889DA9A069AE4E48F47E4D150ED65C | SHA256:96B6B0B81B3E2711DA54F6F8A18CA3CA181783D150C6F3268D12B86A44CA9A6C | |||
| 1380 | mysetup.tmp | C:\Program Files\My Program\puller.exe | executable | |
MD5:2E9C93255CFD04F6D5DA6FE8E6BF909D | SHA256:9F195D1DBEE9D8400A6A25D6531838629466C5443881DCD3895140B68A3F8C21 | |||
| 1380 | mysetup.tmp | C:\Program Files\My Program\unins000.dat | binary | |
MD5:A5F505F9F6C003114172C899BE6A91BD | SHA256:C31CC3A740987ED74B1F4A913E1555E67F0F00181F3BA5CB4E1CC1AD7A7AC773 | |||
| 1840 | puller.exe | C:\Users\admin\AppData\Local\STRESSTEST.EXE | executable | |
MD5:B0C8223D4C1D3280F3942146D4E1FDE9 | SHA256:32C271982E3B7BE1316A250CE4542886CFB061113077D4CEC6637385B2615F08 | |||
| 1840 | puller.exe | C:\Users\admin\AppData\Local\MODULESUPDATE.EXE | executable | |
MD5:94FC0D1CDE78763007CD6ED5587518C8 | SHA256:F233AD007FAEEE8376CAC874A69BB732CE30720F2390C888510DEA44954D0A1D | |||
| 1380 | mysetup.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\My Program.lnk | binary | |
MD5:4D419DF5073C1ABAEA7CCF28582A0595 | SHA256:C00F941DD46A3BF082D178DAA78A5B92C38442E67960A6F57576172EB767BB39 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
index.zeroiq.tk |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
Process | Message |
|---|---|
puller.exe | C:\Users\admin\AppData\Local\MODULESUPDATE.EXE |
puller.exe | C:\Users\admin\AppData\Local\STRESSTEST.EXE |