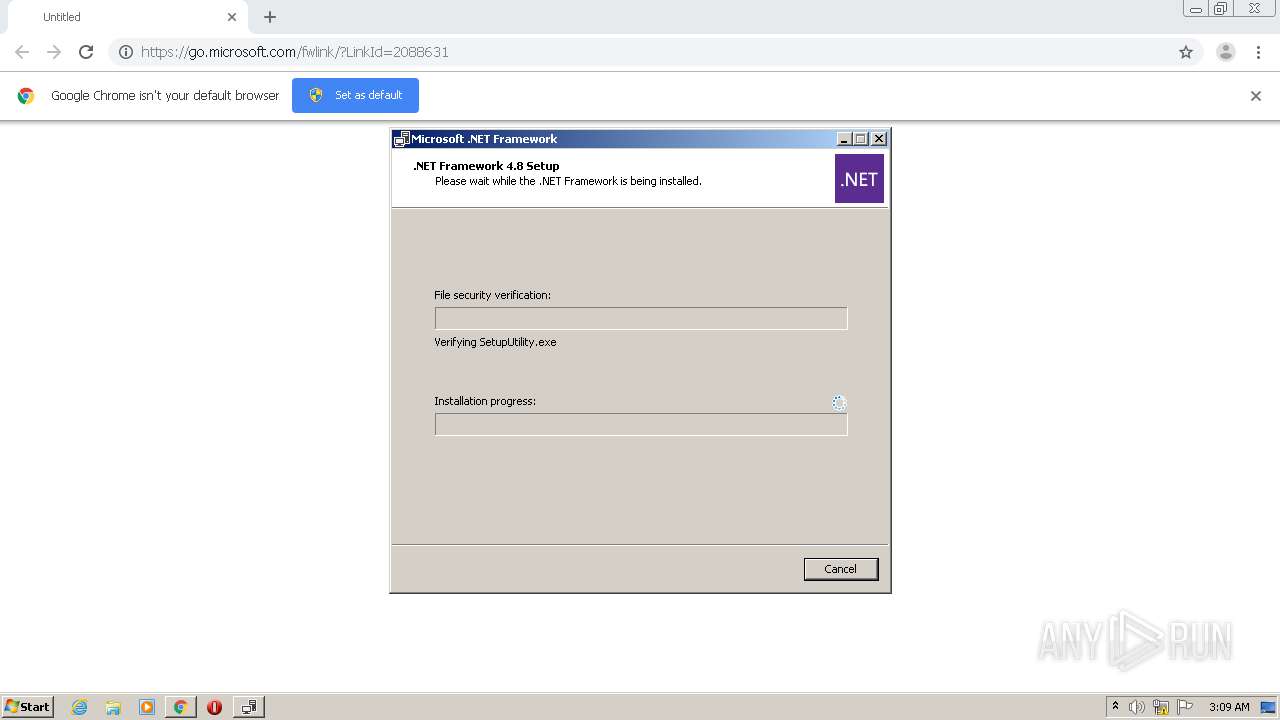
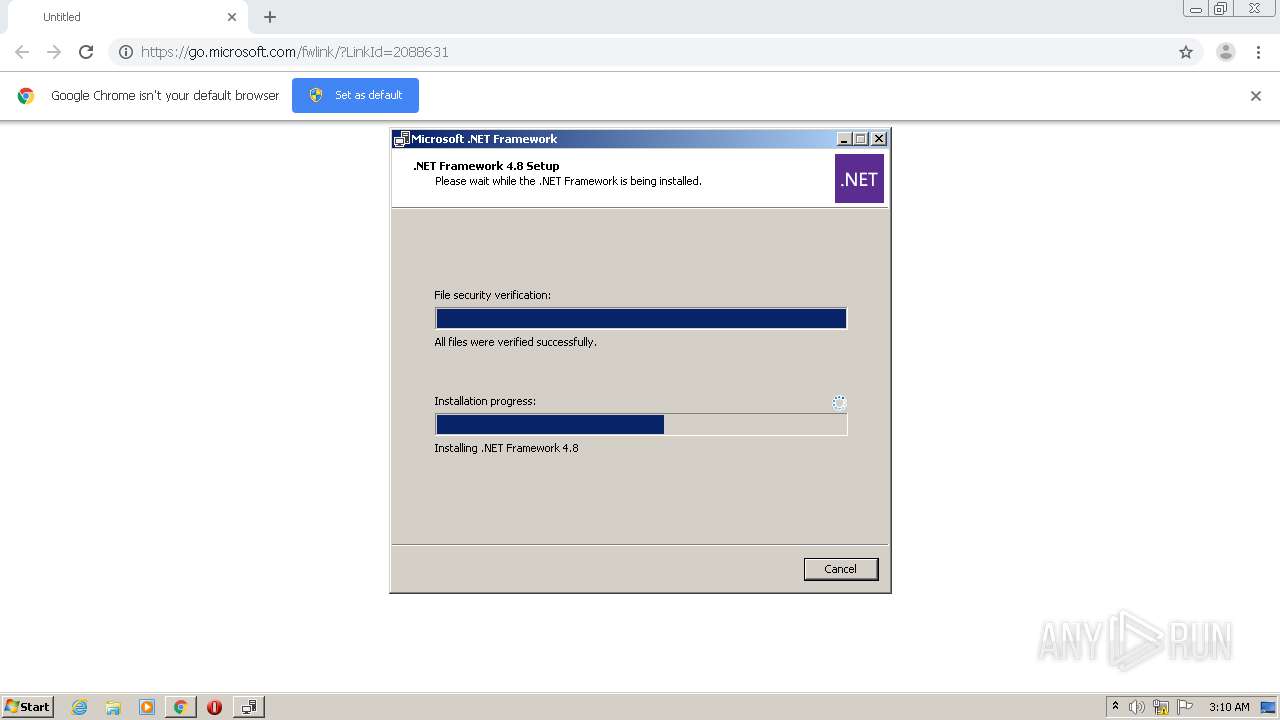
| URL: | https://go.microsoft.com/fwlink/?LinkId=2088631 |
| Full analysis: | https://app.any.run/tasks/b74d8a16-7be2-496a-899b-d62fd4bee3cf |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2021, 03:07:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | ACEE9907EBCC2F043E555BEDCE4FF3DB |
| SHA1: | CC803A0C2E71018BF20D1A93A880E1A17868C60D |
| SHA256: | 98D478F2BE3D1A59FEF13C573A165077DE64A00E1461B8CF2055ED0A3365C302 |
| SSDEEP: | 3:N8r8etR7LOCdidfn:2geDPOCdk |
MALICIOUS
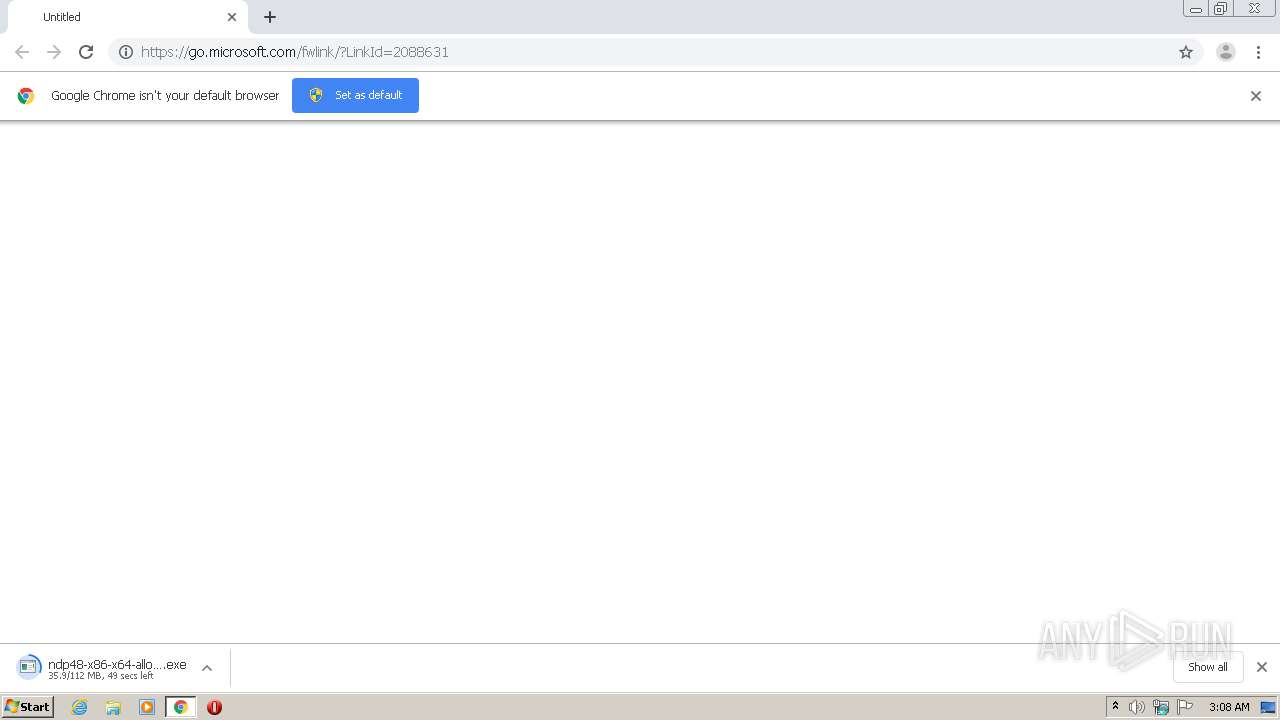
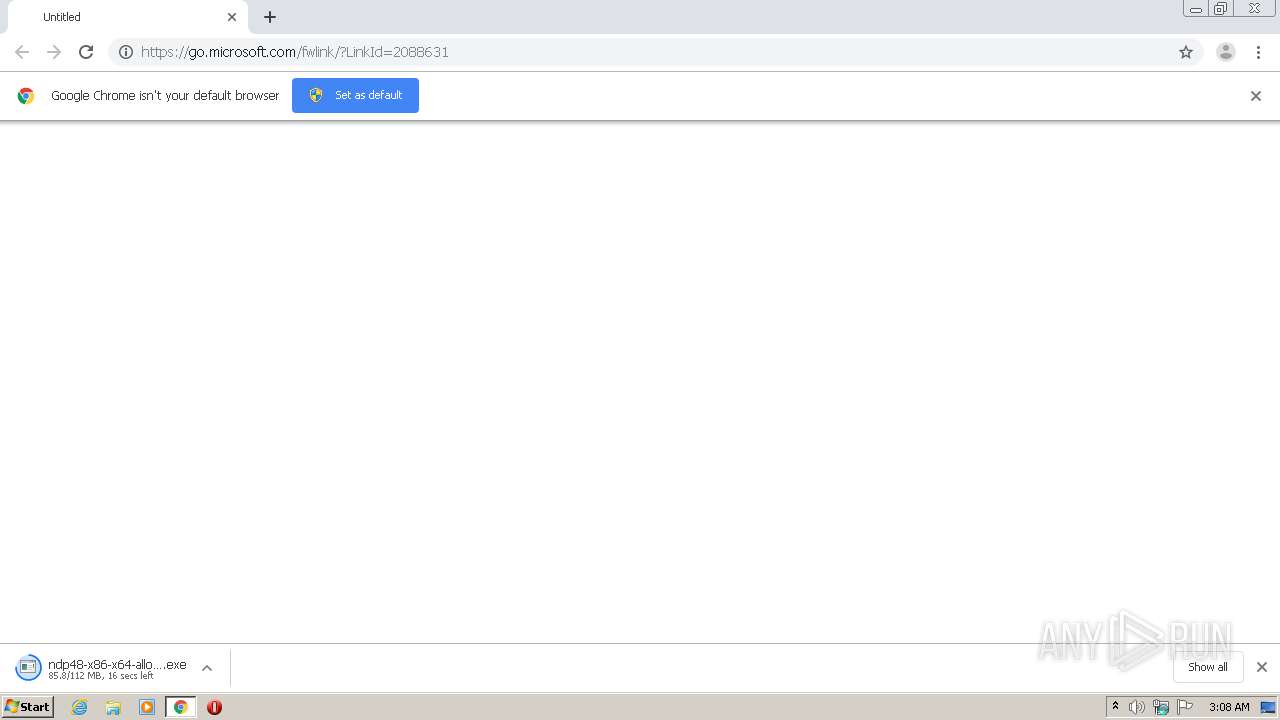
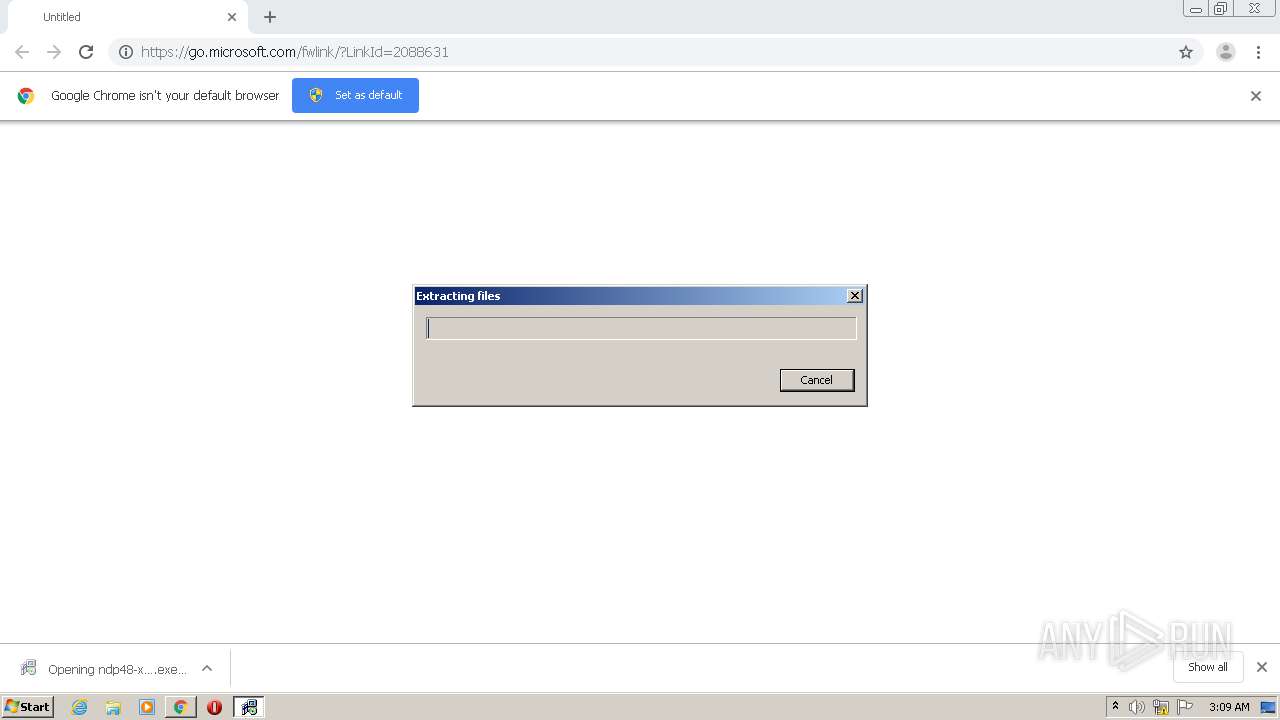
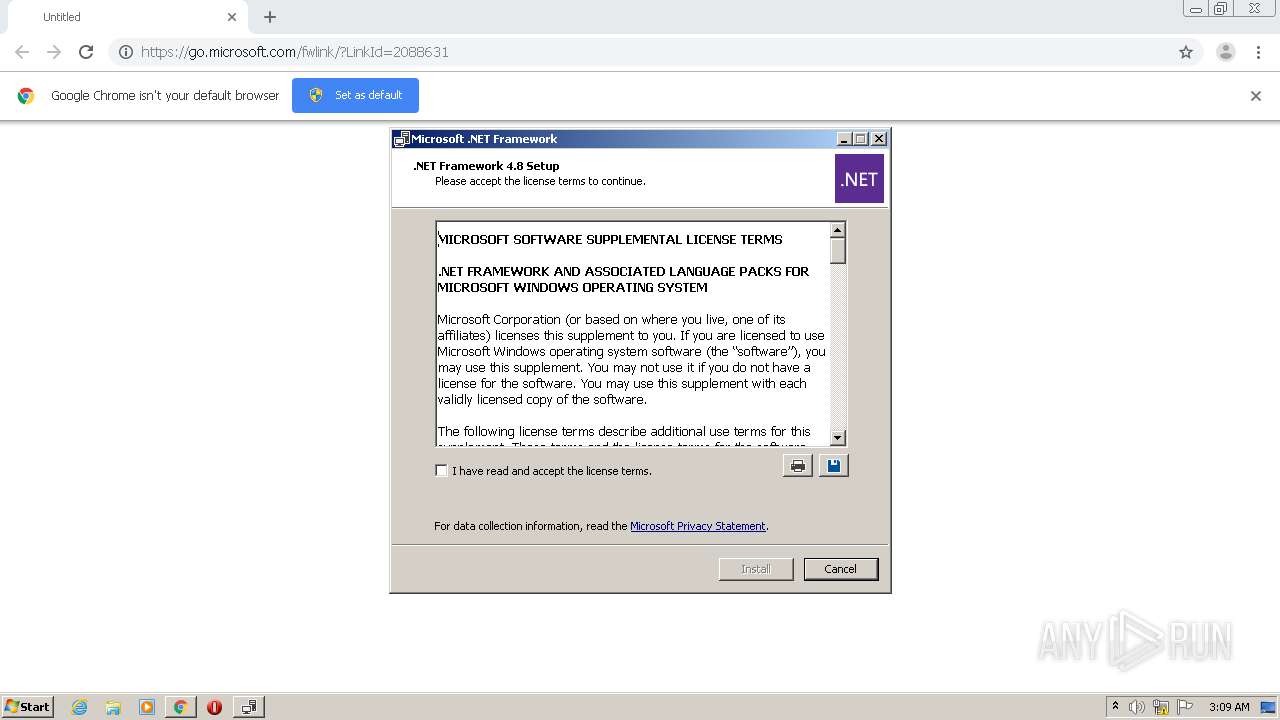
Application was dropped or rewritten from another process
- ndp48-x86-x64-allos-enu.exe (PID: 2748)
- ndp48-x86-x64-allos-enu.exe (PID: 952)
- Setup.exe (PID: 2760)
- SetupUtility.exe (PID: 3032)
- SetupUtility.exe (PID: 876)
- aspnet_regiis.exe (PID: 2576)
- regtlibv12.exe (PID: 2064)
- regtlibv12.exe (PID: 3916)
- regtlibv12.exe (PID: 2116)
- regtlibv12.exe (PID: 3820)
- regtlibv12.exe (PID: 3468)
- ServiceModelReg.exe (PID: 2928)
- ngen.exe (PID: 2880)
- regtlibv12.exe (PID: 1012)
- regtlibv12.exe (PID: 1488)
- mscorsvw.exe (PID: 3312)
- ngen.exe (PID: 2132)
- ngen.exe (PID: 2892)
- mscorsvw.exe (PID: 1236)
Loads dropped or rewritten executable
- Setup.exe (PID: 2760)
- WmiPrvSE.exe (PID: 2484)
- SearchFilterHost.exe (PID: 2144)
- ngen.exe (PID: 2880)
- svchost.exe (PID: 768)
- mscorsvw.exe (PID: 3312)
- ngen.exe (PID: 2132)
- ngen.exe (PID: 2892)
Actions looks like stealing of personal data
- ndp48-x86-x64-allos-enu.exe (PID: 2748)
Changes settings of System certificates
- Setup.exe (PID: 2760)
Loads the Task Scheduler COM API
- ngen.exe (PID: 2880)
- ngen.exe (PID: 2132)
- mscorsvw.exe (PID: 3312)
- ngen.exe (PID: 2892)
Drops executable file immediately after starts
- msiexec.exe (PID: 3072)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3360)
- ndp48-x86-x64-allos-enu.exe (PID: 2748)
- msiexec.exe (PID: 3072)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3360)
- ndp48-x86-x64-allos-enu.exe (PID: 2748)
- msiexec.exe (PID: 3072)
Adds / modifies Windows certificates
- Setup.exe (PID: 2760)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3072)
- aspnet_regiis.exe (PID: 2576)
Changes the autorun value in the registry
- msiexec.exe (PID: 3072)
Removes files from Windows directory
- lodctr.exe (PID: 1252)
- lodctr.exe (PID: 1652)
- lodctr.exe (PID: 3136)
- lodctr.exe (PID: 2172)
- lodctr.exe (PID: 2996)
- aspnet_regiis.exe (PID: 2576)
- msiexec.exe (PID: 3072)
Creates files in the Windows directory
- lodctr.exe (PID: 1252)
- aspnet_regiis.exe (PID: 2576)
- ngen.exe (PID: 2880)
- lodctr.exe (PID: 1652)
- lodctr.exe (PID: 3136)
- lodctr.exe (PID: 2172)
- lodctr.exe (PID: 2996)
- ngen.exe (PID: 2132)
- ngen.exe (PID: 2892)
- mscorsvw.exe (PID: 3312)
- msiexec.exe (PID: 3072)
Drops a file with too old compile date
- msiexec.exe (PID: 3072)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2784)
- Setup.exe (PID: 2760)
- msiexec.exe (PID: 3072)
Reads the hosts file
- chrome.exe (PID: 3360)
- chrome.exe (PID: 2784)
Application launched itself
- chrome.exe (PID: 3360)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3372)
- MsiExec.exe (PID: 3576)
- msiexec.exe (PID: 3072)
Dropped object may contain Bitcoin addresses
- ndp48-x86-x64-allos-enu.exe (PID: 2748)
- msiexec.exe (PID: 3072)
- mscorsvw.exe (PID: 3312)
Creates a software uninstall entry
- msiexec.exe (PID: 3072)
Creates or modifies windows services
- msiexec.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
46
Malicious processes
14
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,8245268611945832609,599823142782982810,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12380717629048822321 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,8245268611945832609,599823142782982810,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15599997662541347917 --mojo-platform-channel-handle=1116 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 768 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | SetupUtility.exe /screboot | C:\2b97198aaf87dd75ff34443f\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.3928.0 built by: NET48REL1 Modules
| |||||||||||||||
| 876 | "C:\Windows\system32\lodctr.exe" /m:"C:\Windows\Microsoft.NET\Framework\v4.0.30319\ServiceModelPerformanceCounters.man" | C:\Windows\system32\lodctr.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Users\admin\Downloads\ndp48-x86-x64-allos-enu.exe" | C:\Users\admin\Downloads\ndp48-x86-x64-allos-enu.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.8 Setup Exit code: 3221226540 Version: 4.8.03928.00 Modules
| |||||||||||||||
| 1012 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\System.Drawing.tlb" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: RegTLib Exit code: 0 Version: 14.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c23a9d0,0x6c23a9e0,0x6c23a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 100 -InterruptEvent 0 -NGENProcess ec -Pipe f8 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1252 | "C:\Windows\system32\lodctr.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\netmemorycache.ini" | C:\Windows\system32\lodctr.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
27 087
Read events
10 963
Write events
13 754
Delete events
2 370
Modification events
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3360-13259819274612875 |
Value: 259 | |||
Executable files
1 935
Suspicious files
43
Text files
560
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6048380B-D20.pma | — | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9307e220-ea65-473e-9239-315268e07910.tmp | — | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd8ee2.TMP | text | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFd8ee2.TMP | text | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFd9105.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2760 | Setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
2760 | Setup.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | US | der | 1.05 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | chrome.exe | 68.232.34.200:443 | download.visualstudio.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2784 | chrome.exe | 142.250.185.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2760 | Setup.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
2784 | chrome.exe | 216.58.212.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2760 | Setup.exe | 104.79.89.142:80 | www.microsoft.com | Time Warner Cable Internet LLC | US | unknown |
2784 | chrome.exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
2784 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
download.visualstudio.microsoft.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |