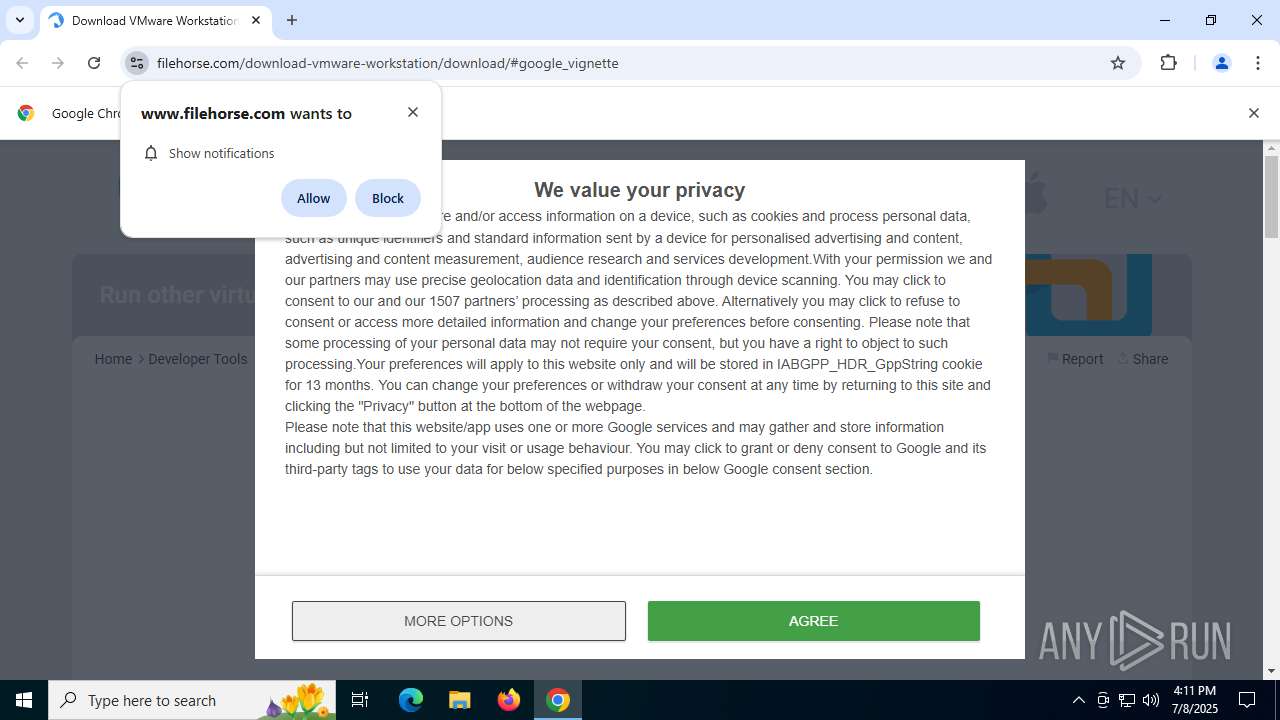
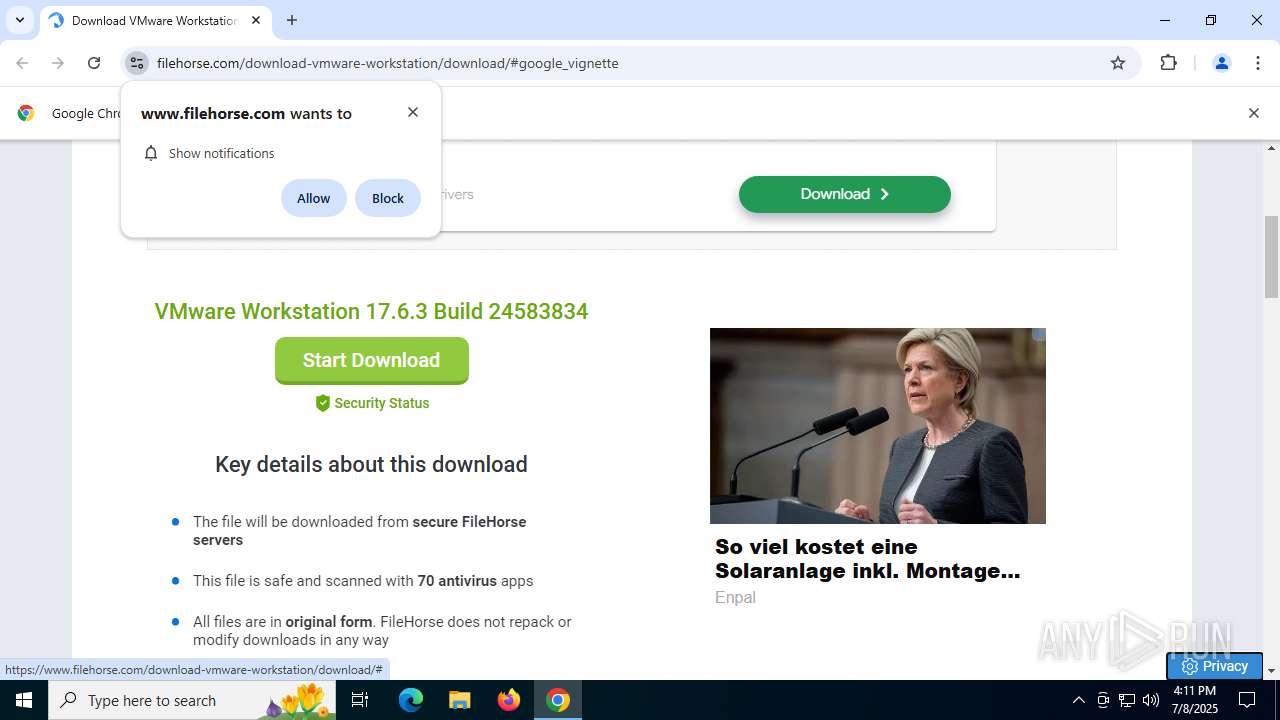
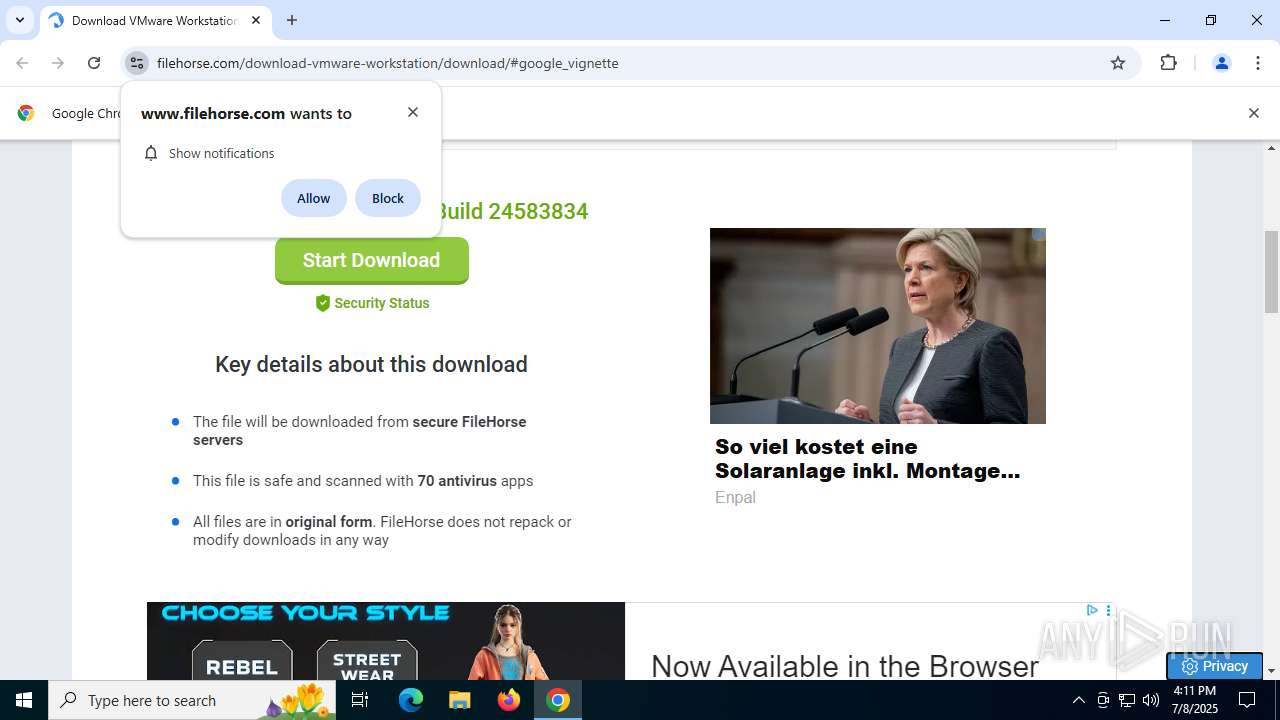
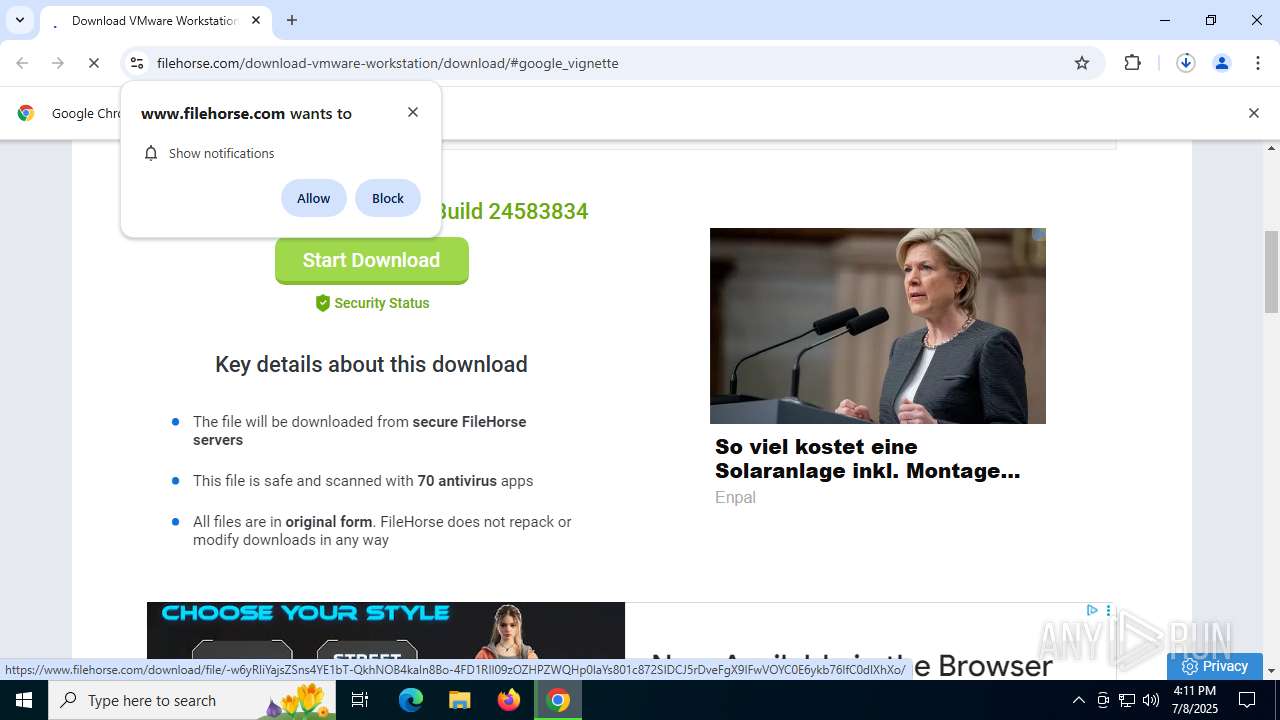
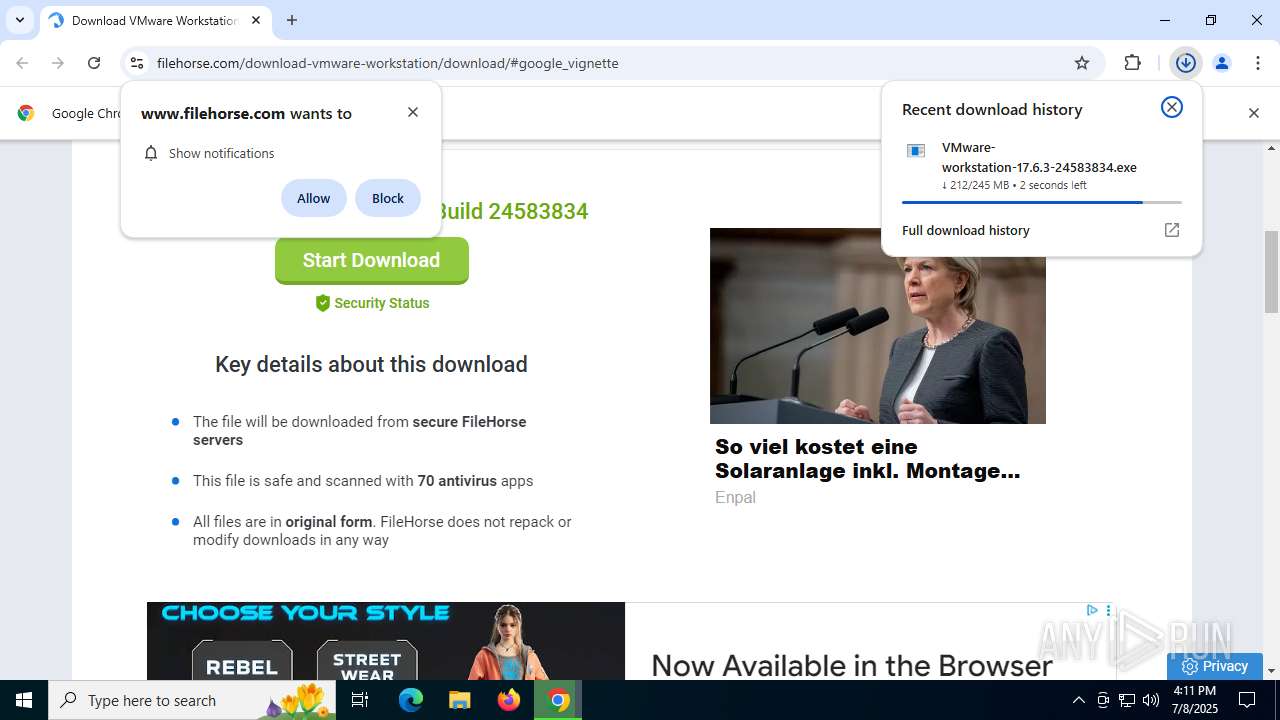
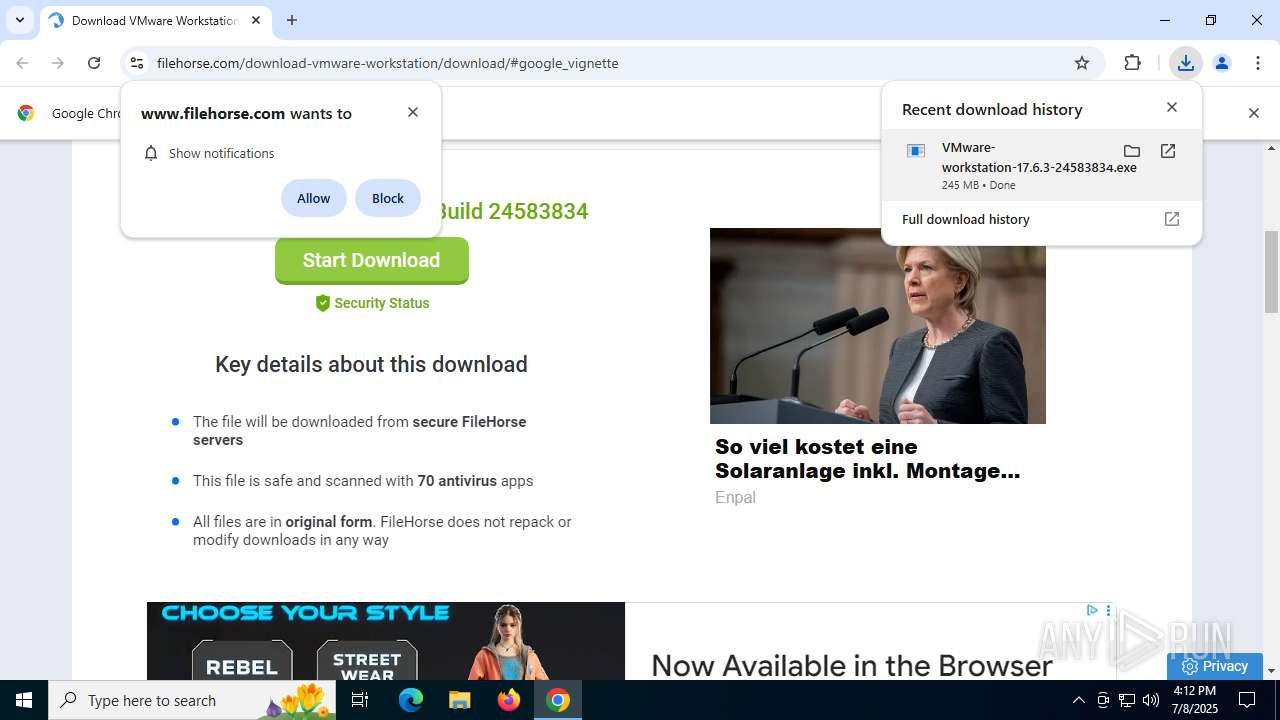
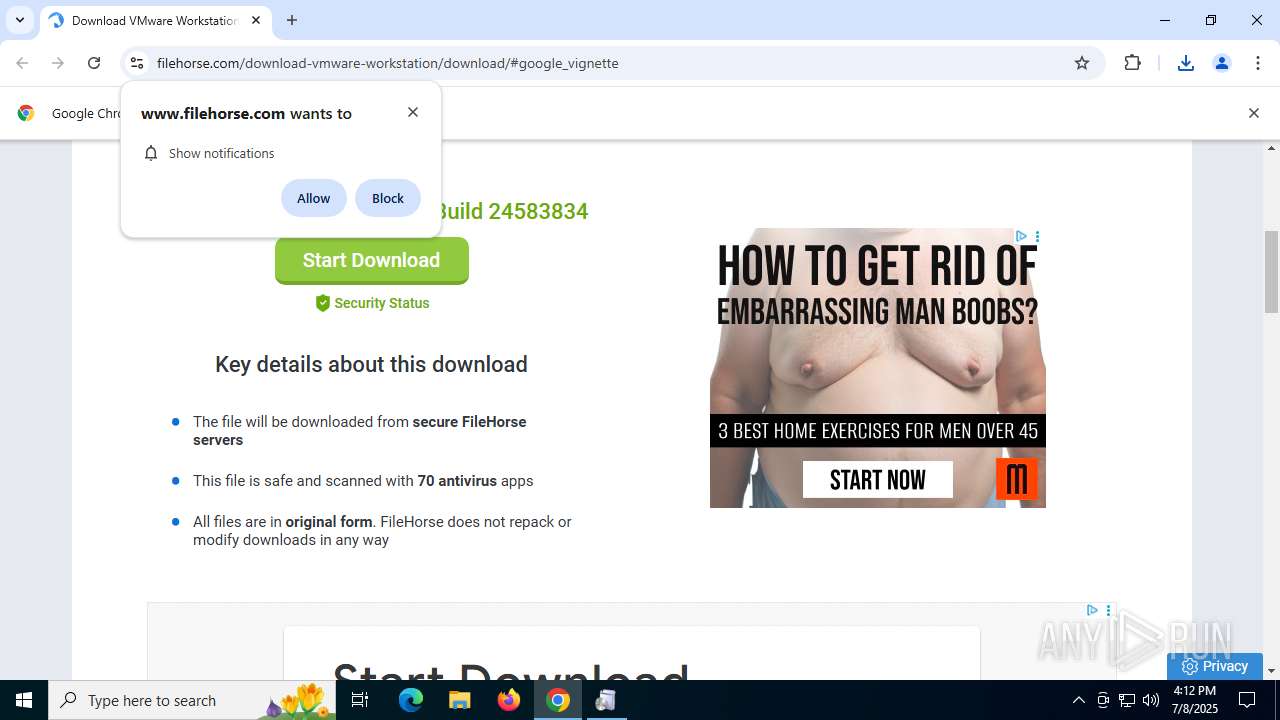
| URL: | https://www.filehorse.com/download-vmware-workstation/download/#google_vignette |
| Full analysis: | https://app.any.run/tasks/33b088d2-c09b-4488-9752-6ebb815d9d91 |
| Verdict: | Malicious activity |
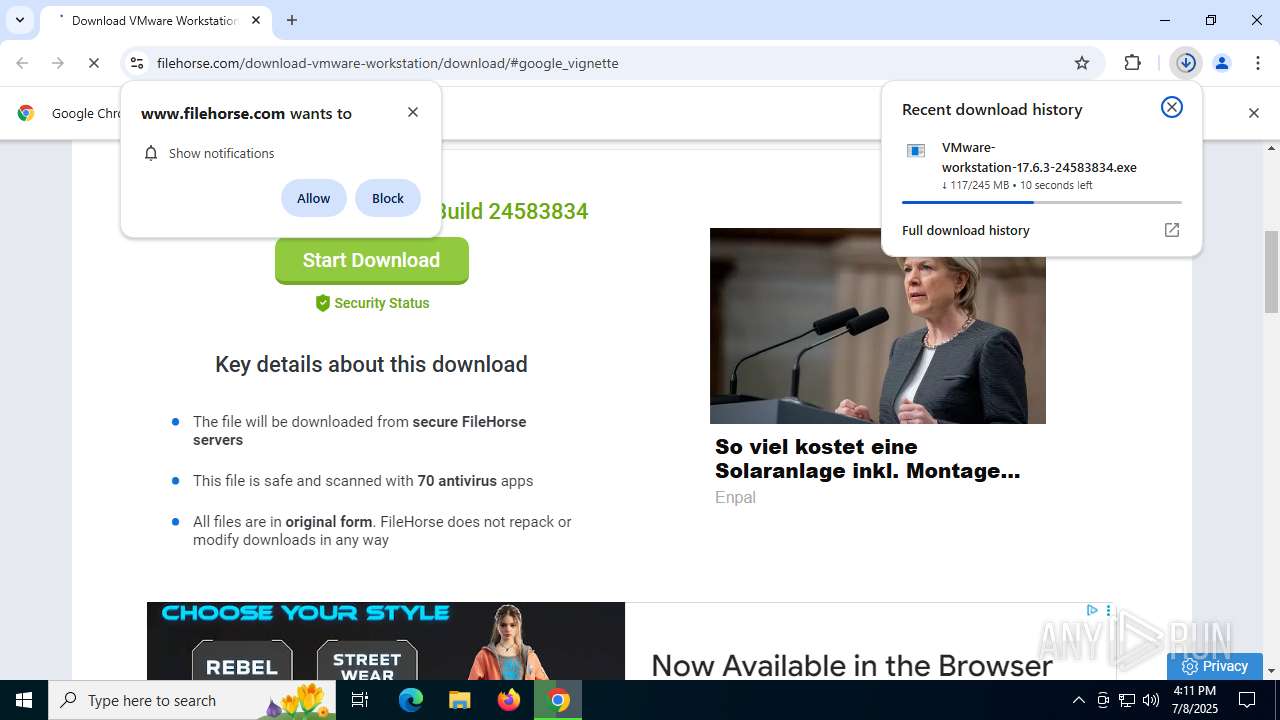
| Analysis date: | July 08, 2025, 16:10:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MD5: | 6BBE96D75E5B8EF2250AB1693F26120B |
| SHA1: | 731292C950D56AB42C6D5D55C05AA0BE1389C797 |
| SHA256: | 98D30A61ADC172D855431254D16AB48EC892B3B7729F026EAF3998DF9919CC92 |
| SSDEEP: | 3:N8DSLQiKbGGBKJTcQMOWfK+B4GEKDAw:2OLQpbGNtPchEKcw |
MALICIOUS
Changes the autorun value in the registry
- VC_redist.x86.exe (PID: 6900)
- VC_redist.x64.exe (PID: 3964)
- msiexec.exe (PID: 5236)
- msiexec.exe (PID: 7104)
Reads a specific registry key of the VM
- msiexec.exe (PID: 4664)
- msiexec.exe (PID: 2764)
- msiexec.exe (PID: 5236)
- vnetlib64.exe (PID: 1852)
- vnetlib64.exe (PID: 8928)
- vnetlib64.exe (PID: 3576)
- vnetlib64.exe (PID: 2160)
- vnetlib64.exe (PID: 7864)
- vnetlib64.exe (PID: 9000)
- vnetlib64.exe (PID: 8816)
- vnetlib64.exe (PID: 6900)
- vnetlib64.exe (PID: 5080)
- vnetlib64.exe (PID: 5500)
- vnetlib64.exe (PID: 6312)
- vnetlib64.exe (PID: 5288)
- vnetlib64.exe (PID: 9188)
- vnetlib64.exe (PID: 6372)
- vnetlib64.exe (PID: 6760)
- vnetlib64.exe (PID: 9072)
- vnetlib64.exe (PID: 8924)
- vnetlib64.exe (PID: 9076)
- vnetlib64.exe (PID: 8916)
- vnetlib64.exe (PID: 1868)
- vnetlib64.exe (PID: 1484)
- vnetlib64.exe (PID: 4828)
- vnetlib64.exe (PID: 6940)
- vnetlib64.exe (PID: 1936)
- vnetlib64.exe (PID: 7732)
- vnetlib64.exe (PID: 7632)
- vnetlib64.exe (PID: 4512)
- vmnat.exe (PID: 3968)
- msiexec.exe (PID: 7104)
- vnetlib64.exe (PID: 1700)
- vnetlib64.exe (PID: 6704)
- vnetlib64.exe (PID: 9016)
- vmware-authd.exe (PID: 5720)
Starts NET.EXE for service management
- msiexec.exe (PID: 2764)
- net.exe (PID: 9024)
- net.exe (PID: 3092)
SUSPICIOUS
Executable content was dropped or overwritten
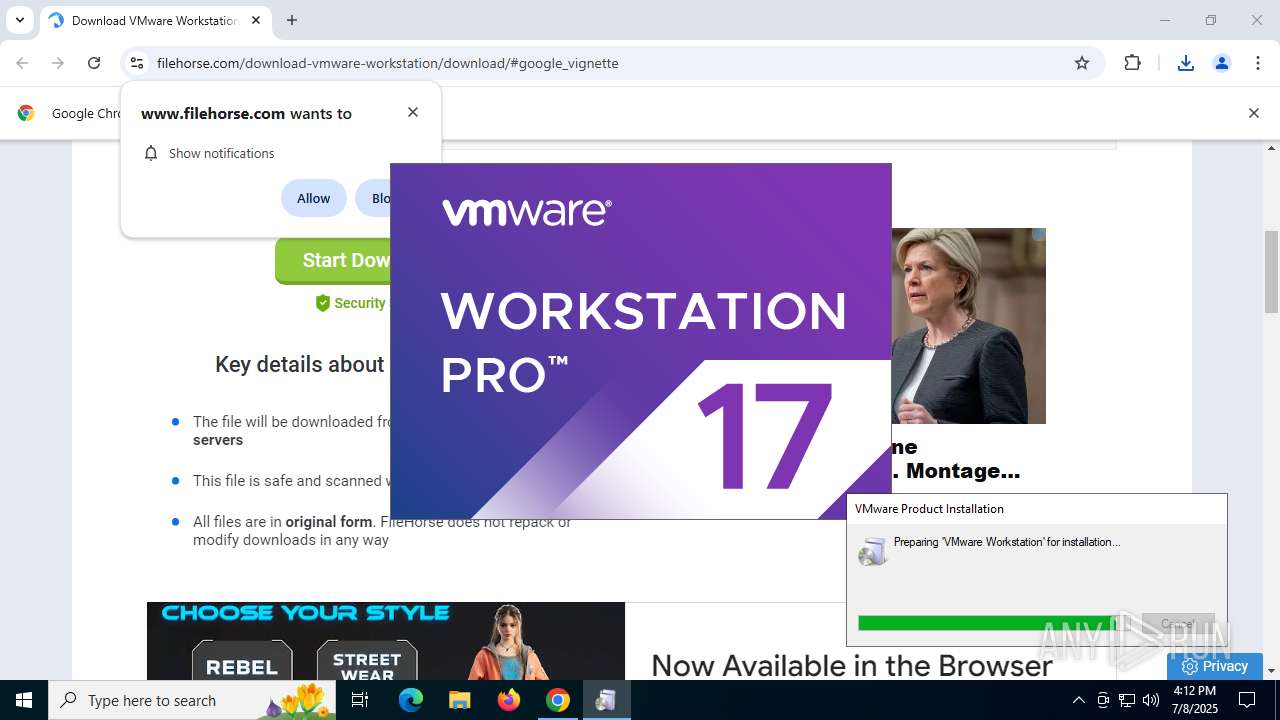
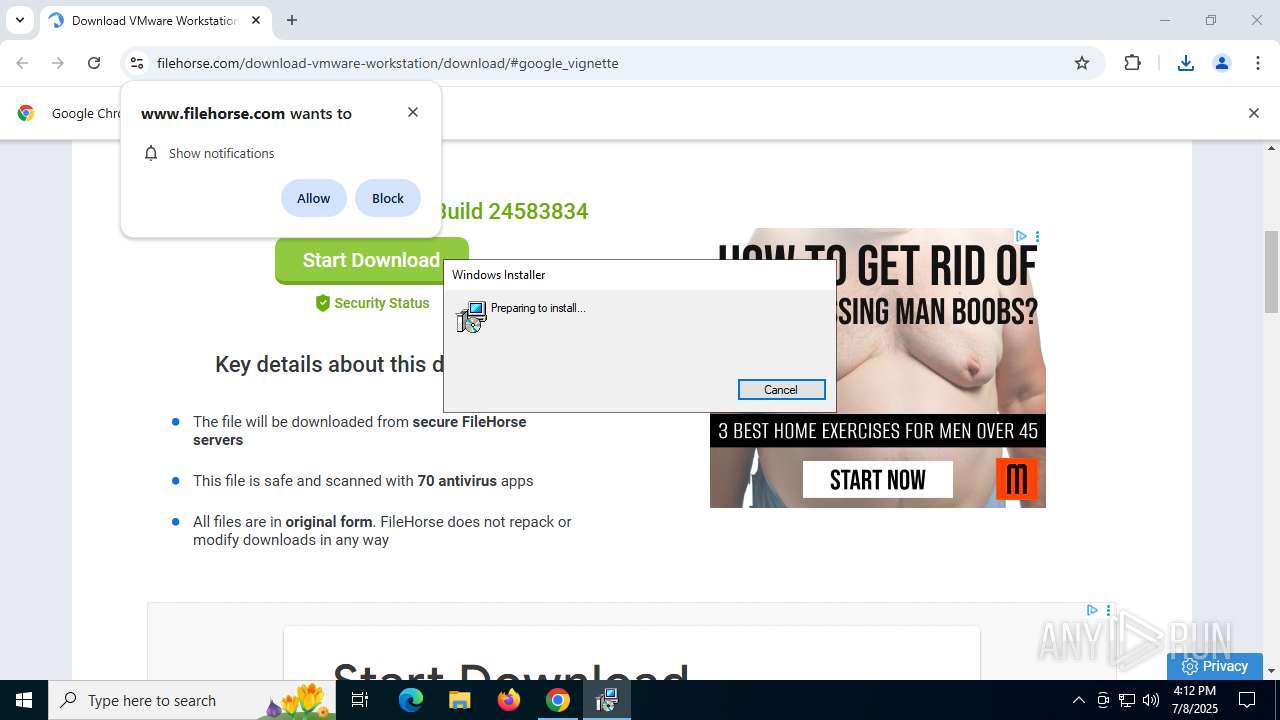
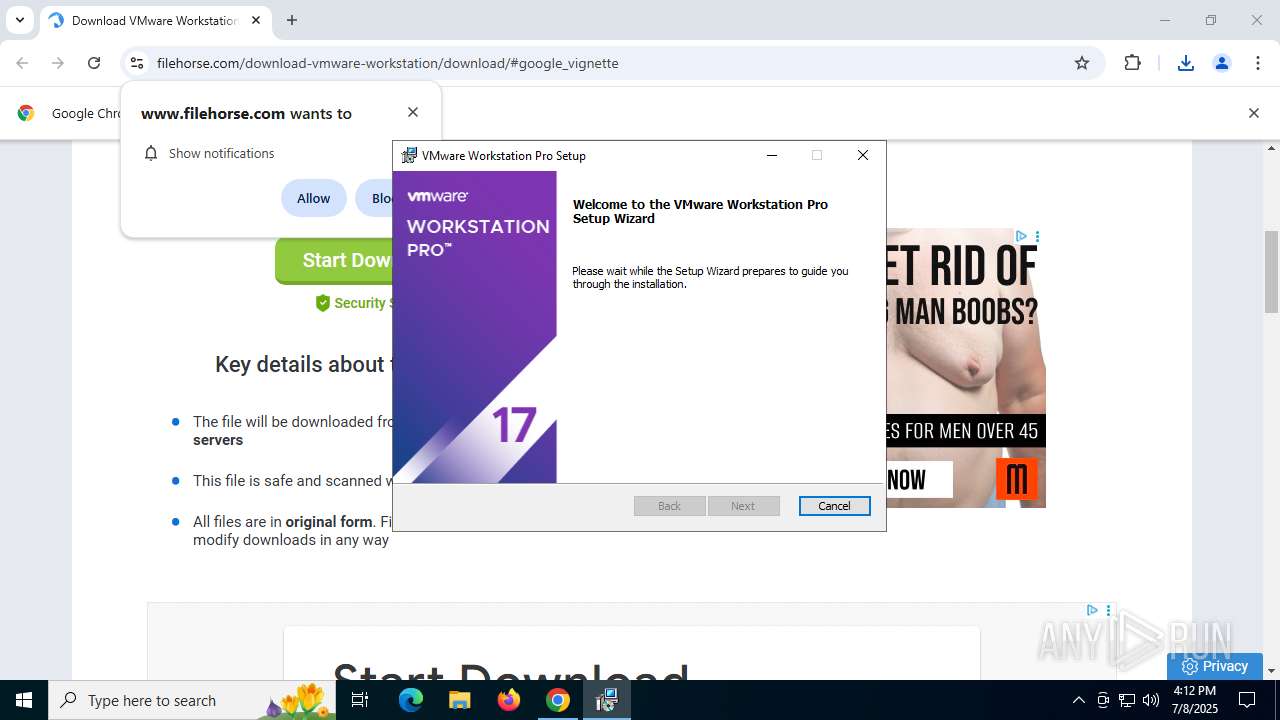
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- vcredist_x86.exe (PID: 7864)
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8760)
- vcredist_x64.exe (PID: 8696)
- VC_redist.x86.exe (PID: 6348)
- VC_redist.x64.exe (PID: 8520)
- drvinst.exe (PID: 4968)
- vnetlib64.exe (PID: 8816)
- vnetlib64.exe (PID: 7632)
- drvinst.exe (PID: 5764)
- vnetlib64.exe (PID: 4512)
- drvinst.exe (PID: 6672)
- drvinst.exe (PID: 1528)
- drvinst.exe (PID: 8976)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 7728)
Process drops legitimate windows executable
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- vcredist_x86.exe (PID: 7864)
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8760)
- vcredist_x64.exe (PID: 8696)
- msiexec.exe (PID: 7104)
- msiexec.exe (PID: 5236)
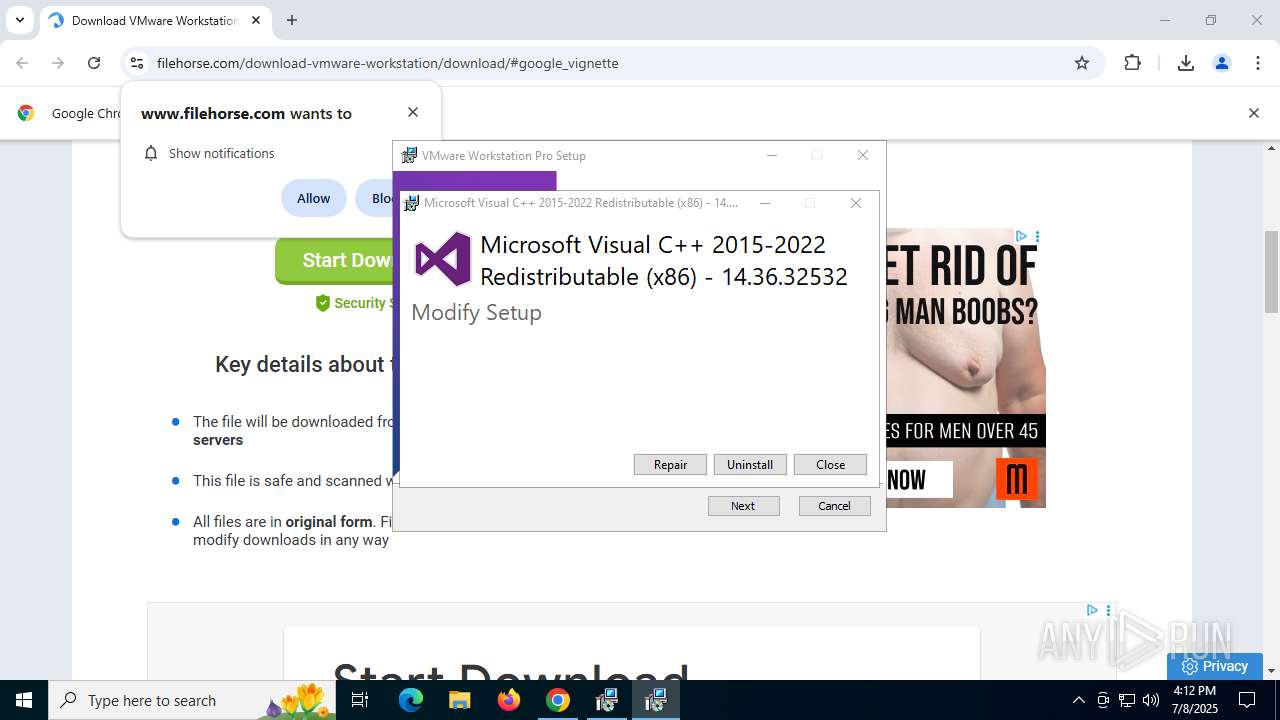
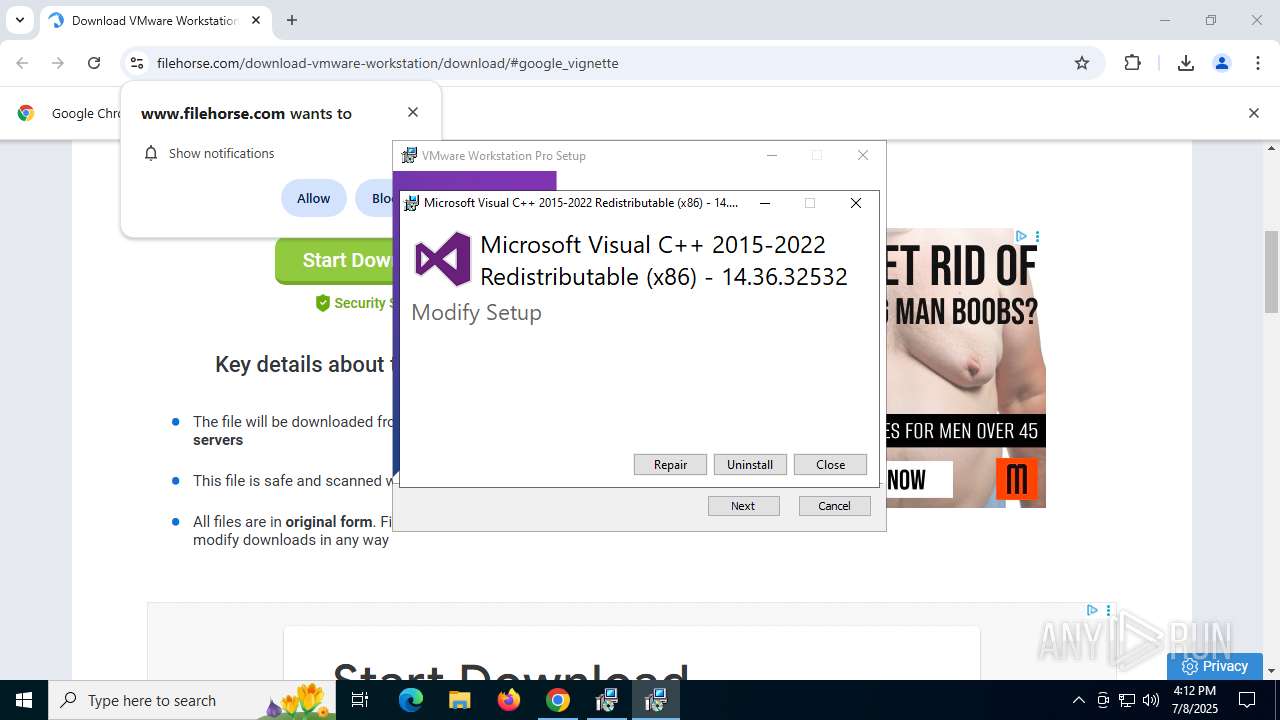
Starts a Microsoft application from unusual location
- vcredist_x86.exe (PID: 7864)
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8760)
- vcredist_x64.exe (PID: 8696)
- VC_redist.x86.exe (PID: 6900)
- VC_redist.x64.exe (PID: 3964)
Searches for installed software
- vcredist_x86.exe (PID: 868)
- dllhost.exe (PID: 1984)
- vcredist_x64.exe (PID: 8696)
- VC_redist.x86.exe (PID: 6348)
- VC_redist.x64.exe (PID: 8520)
Executes as Windows Service
- VSSVC.exe (PID: 8376)
- vmnat.exe (PID: 3968)
- vmnetdhcp.exe (PID: 8744)
- vmware-usbarbitrator64.exe (PID: 5140)
- vmware-authd.exe (PID: 5720)
Starts itself from another location
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8696)
Reads security settings of Internet Explorer
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8696)
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
Reads the Windows owner or organization settings
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- msiexec.exe (PID: 5236)
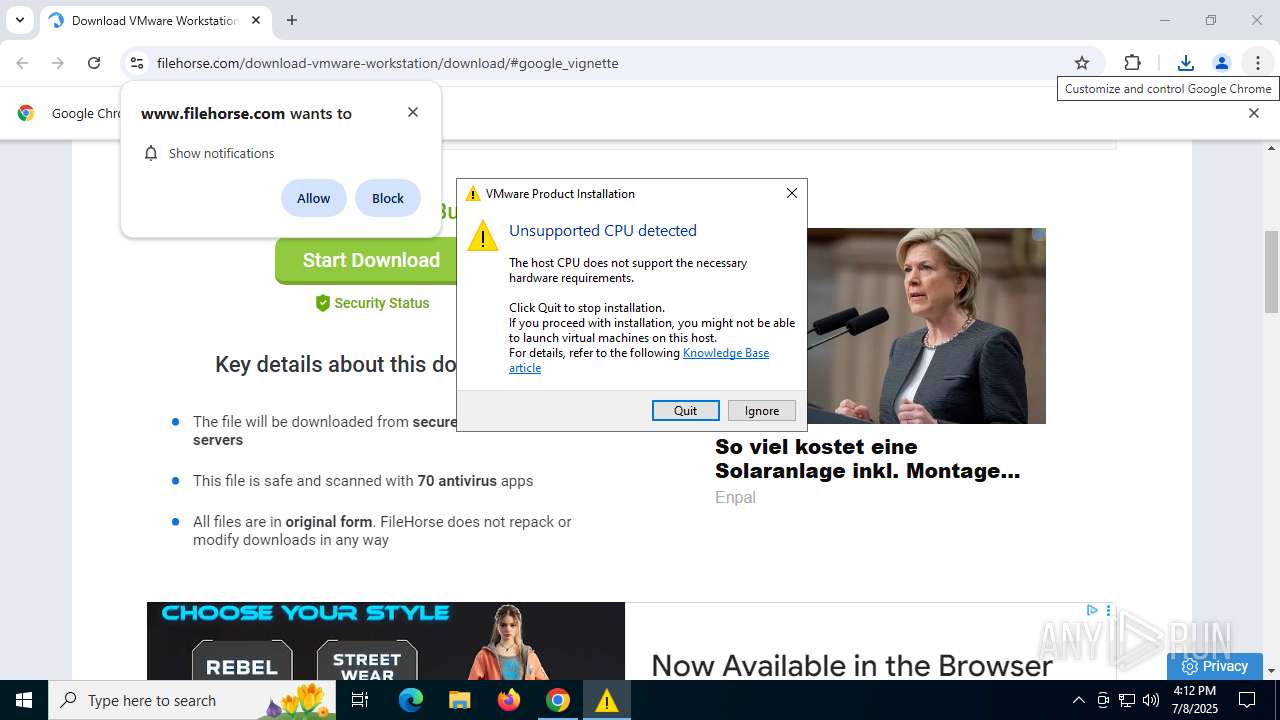
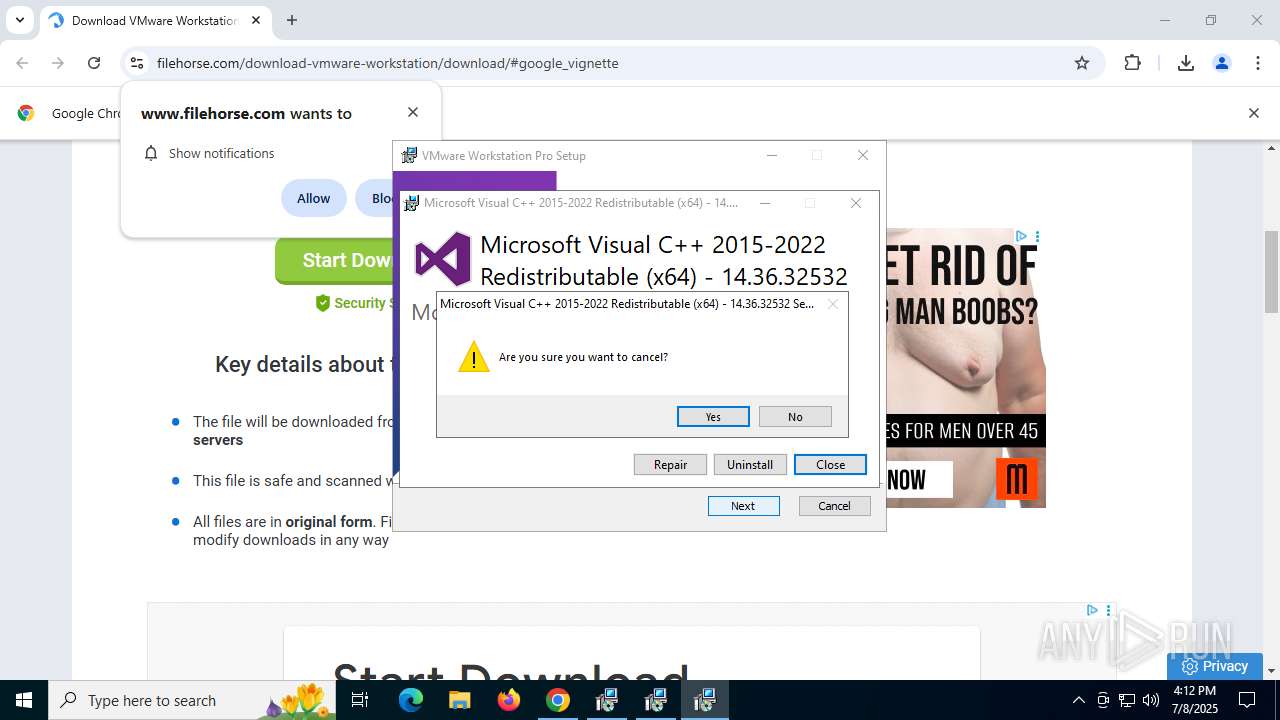
Executes application which crashes
- msiexec.exe (PID: 5416)
Application launched itself
- VC_redist.x86.exe (PID: 9056)
- VC_redist.x86.exe (PID: 1352)
- VC_redist.x64.exe (PID: 1268)
- msiexec.exe (PID: 5236)
- VC_redist.x64.exe (PID: 6372)
Process checks presence of unattended files
- msiexec.exe (PID: 5236)
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 5236)
- drvinst.exe (PID: 4968)
- vnetlib64.exe (PID: 8816)
- drvinst.exe (PID: 5764)
- vnetlib64.exe (PID: 7632)
- vnetlib64.exe (PID: 4512)
- drvinst.exe (PID: 6672)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 7728)
- msiexec.exe (PID: 7104)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 5236)
The process checks if it is being run in the virtual environment
- vnetlib64.exe (PID: 8928)
- vnetlib64.exe (PID: 7732)
- drvinst.exe (PID: 5764)
- msiexec.exe (PID: 4664)
- vnetlib64.exe (PID: 7632)
- vnetlib64.exe (PID: 4512)
- drvinst.exe (PID: 1528)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 3196)
- msiexec.exe (PID: 2764)
Creates files in the driver directory
- drvinst.exe (PID: 4968)
- vnetlib64.exe (PID: 8816)
- drvinst.exe (PID: 5764)
- vnetlib64.exe (PID: 7632)
- vnetlib64.exe (PID: 4512)
- vnetlib64.exe (PID: 6704)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 6672)
- drvinst.exe (PID: 7728)
- msiexec.exe (PID: 7104)
Creates or modifies Windows services
- vnetlib64.exe (PID: 8816)
- vnetlib64.exe (PID: 7632)
- vnetlib64.exe (PID: 4512)
- drvinst.exe (PID: 8976)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 3196)
- drvinst.exe (PID: 1528)
Creates/Modifies COM task schedule object
- vnetlib64.exe (PID: 7632)
- msiexec.exe (PID: 2764)
Starts NET.EXE for network exploration
- msiexec.exe (PID: 2764)
- net.exe (PID: 3092)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 5020)
- msiexec.exe (PID: 5236)
- msiexec.exe (PID: 7104)
- msiexec.exe (PID: 4664)
Application launched itself
- chrome.exe (PID: 5020)
Checks supported languages
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- vcredist_x86.exe (PID: 7864)
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8760)
- vcredist_x64.exe (PID: 8696)
- VC_redist.x86.exe (PID: 6900)
- VC_redist.x64.exe (PID: 3964)
- msiexec.exe (PID: 5236)
- msiexec.exe (PID: 5416)
- VC_redist.x86.exe (PID: 9056)
- VC_redist.x86.exe (PID: 6348)
- VC_redist.x86.exe (PID: 1352)
- VC_redist.x64.exe (PID: 6372)
- VC_redist.x64.exe (PID: 1268)
- VC_redist.x64.exe (PID: 8520)
- msiexec.exe (PID: 2140)
- msiexec.exe (PID: 2764)
- msiexec.exe (PID: 2280)
- msiexec.exe (PID: 7104)
- msiexec.exe (PID: 4664)
- vnetlib64.exe (PID: 8928)
- vnetlib64.exe (PID: 8816)
- vnetlib64.exe (PID: 1852)
- drvinst.exe (PID: 4968)
- vnetlib64.exe (PID: 2160)
- vnetlib64.exe (PID: 3576)
- vnetlib64.exe (PID: 7864)
- vnetlib64.exe (PID: 9000)
- vnetlib64.exe (PID: 6900)
- vnetlib64.exe (PID: 5500)
- vnetlib64.exe (PID: 5080)
- vnetlib64.exe (PID: 5288)
- vnetlib64.exe (PID: 6312)
- vnetlib64.exe (PID: 9188)
- vnetlib64.exe (PID: 9076)
- vnetlib64.exe (PID: 6760)
- vnetlib64.exe (PID: 6372)
- vnetlib64.exe (PID: 9072)
- vnetlib64.exe (PID: 8916)
- vnetlib64.exe (PID: 1868)
- vnetlib64.exe (PID: 1484)
- vnetlib64.exe (PID: 4828)
- vnetlib64.exe (PID: 6940)
- vnetlib64.exe (PID: 1936)
- vnetlib64.exe (PID: 8924)
- vnetlib64.exe (PID: 7632)
- drvinst.exe (PID: 5764)
- vnetlib64.exe (PID: 7732)
- vnetlib64.exe (PID: 4512)
- vmnetdhcp.exe (PID: 8744)
- vnetlib64.exe (PID: 6704)
- vmnat.exe (PID: 3968)
- drvinst.exe (PID: 6672)
- drvinst.exe (PID: 1528)
- vnetlib64.exe (PID: 9016)
- drvinst.exe (PID: 8976)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 7728)
- drvinst.exe (PID: 3196)
- vmware-usbarbitrator64.exe (PID: 5140)
- vmware-authd.exe (PID: 5720)
Reads the computer name
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- vcredist_x86.exe (PID: 868)
- VC_redist.x86.exe (PID: 6900)
- vcredist_x64.exe (PID: 8696)
- VC_redist.x64.exe (PID: 3964)
- msiexec.exe (PID: 5236)
- msiexec.exe (PID: 5416)
- VC_redist.x86.exe (PID: 6348)
- VC_redist.x64.exe (PID: 8520)
- msiexec.exe (PID: 2140)
- msiexec.exe (PID: 2764)
- msiexec.exe (PID: 2280)
- msiexec.exe (PID: 4664)
- msiexec.exe (PID: 7104)
- vnetlib64.exe (PID: 8928)
- drvinst.exe (PID: 4968)
- vnetlib64.exe (PID: 8816)
- vnetlib64.exe (PID: 1852)
- vnetlib64.exe (PID: 3576)
- vnetlib64.exe (PID: 2160)
- vnetlib64.exe (PID: 7864)
- vnetlib64.exe (PID: 6900)
- vnetlib64.exe (PID: 5080)
- vnetlib64.exe (PID: 5500)
- vnetlib64.exe (PID: 6312)
- vnetlib64.exe (PID: 5288)
- vnetlib64.exe (PID: 9188)
- vnetlib64.exe (PID: 9000)
- vnetlib64.exe (PID: 9076)
- vnetlib64.exe (PID: 6760)
- vnetlib64.exe (PID: 6372)
- vnetlib64.exe (PID: 8916)
- vnetlib64.exe (PID: 9072)
- vnetlib64.exe (PID: 6940)
- vnetlib64.exe (PID: 1484)
- vnetlib64.exe (PID: 4828)
- vnetlib64.exe (PID: 8924)
- vnetlib64.exe (PID: 1868)
- vnetlib64.exe (PID: 7732)
- vnetlib64.exe (PID: 7632)
- vnetlib64.exe (PID: 1936)
- drvinst.exe (PID: 5764)
- vnetlib64.exe (PID: 4512)
- vmnat.exe (PID: 3968)
- vmnetdhcp.exe (PID: 8744)
- vnetlib64.exe (PID: 6704)
- drvinst.exe (PID: 6672)
- drvinst.exe (PID: 1528)
- vnetlib64.exe (PID: 9016)
- drvinst.exe (PID: 8976)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 7728)
- drvinst.exe (PID: 3196)
- vmware-usbarbitrator64.exe (PID: 5140)
- vmware-authd.exe (PID: 5720)
Create files in a temporary directory
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8696)
- VC_redist.x86.exe (PID: 6348)
- VC_redist.x64.exe (PID: 8520)
- msiexec.exe (PID: 7104)
The sample compiled with english language support
- vcredist_x86.exe (PID: 7864)
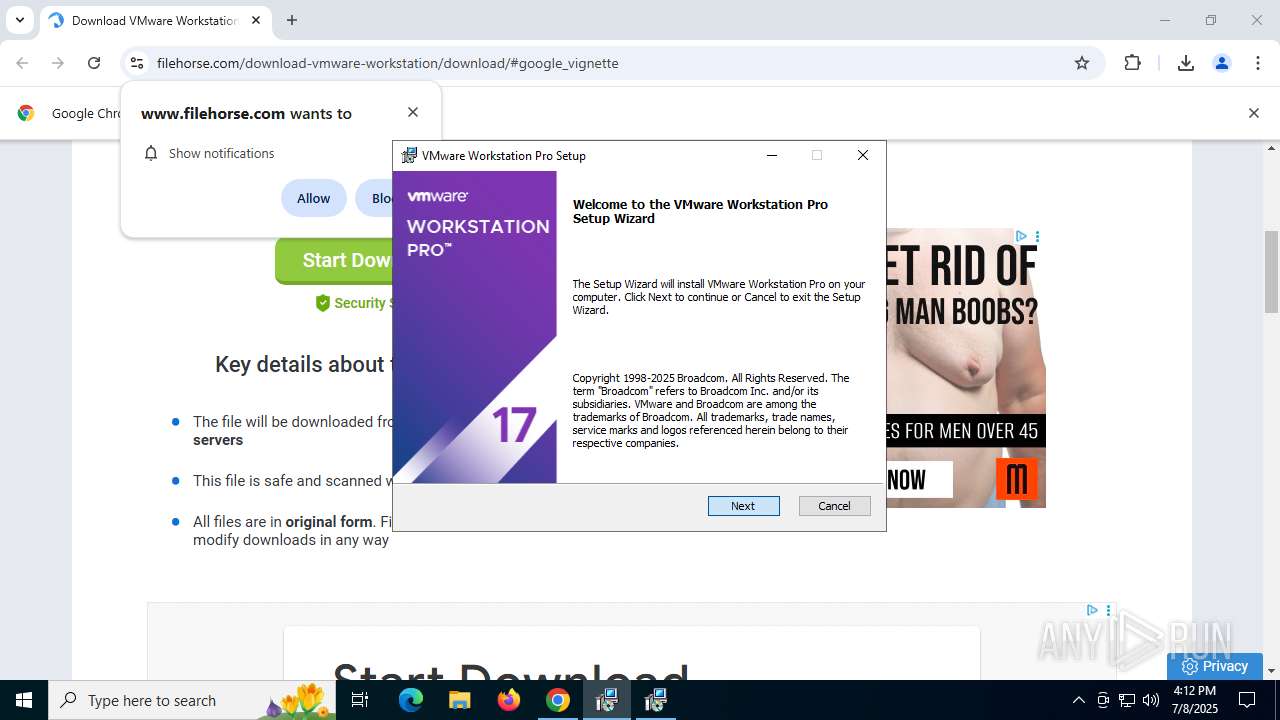
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8760)
- vcredist_x64.exe (PID: 8696)
- VC_redist.x86.exe (PID: 6348)
- VC_redist.x64.exe (PID: 8520)
- msiexec.exe (PID: 5236)
- msiexec.exe (PID: 7104)
- drvinst.exe (PID: 4968)
- vnetlib64.exe (PID: 8816)
- drvinst.exe (PID: 5764)
- vnetlib64.exe (PID: 7632)
- vnetlib64.exe (PID: 4512)
- msiexec.exe (PID: 4664)
- drvinst.exe (PID: 6672)
- drvinst.exe (PID: 8976)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 7728)
- drvinst.exe (PID: 1528)
Process checks computer location settings
- vcredist_x86.exe (PID: 868)
- vcredist_x64.exe (PID: 8696)
Manages system restore points
- SrTasks.exe (PID: 4816)
- SrTasks.exe (PID: 8844)
Launching a file from a Registry key
- VC_redist.x86.exe (PID: 6900)
- msiexec.exe (PID: 5236)
- VC_redist.x64.exe (PID: 3964)
- msiexec.exe (PID: 7104)
Checks proxy server information
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- slui.exe (PID: 8928)
Creates files or folders in the user directory
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- WerFault.exe (PID: 1688)
Reads the software policy settings
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- msiexec.exe (PID: 5236)
- slui.exe (PID: 8928)
- drvinst.exe (PID: 4968)
- vnetlib64.exe (PID: 8816)
- drvinst.exe (PID: 5764)
- vnetlib64.exe (PID: 4512)
- drvinst.exe (PID: 6672)
- vnetlib64.exe (PID: 1700)
- drvinst.exe (PID: 7728)
- msiexec.exe (PID: 7104)
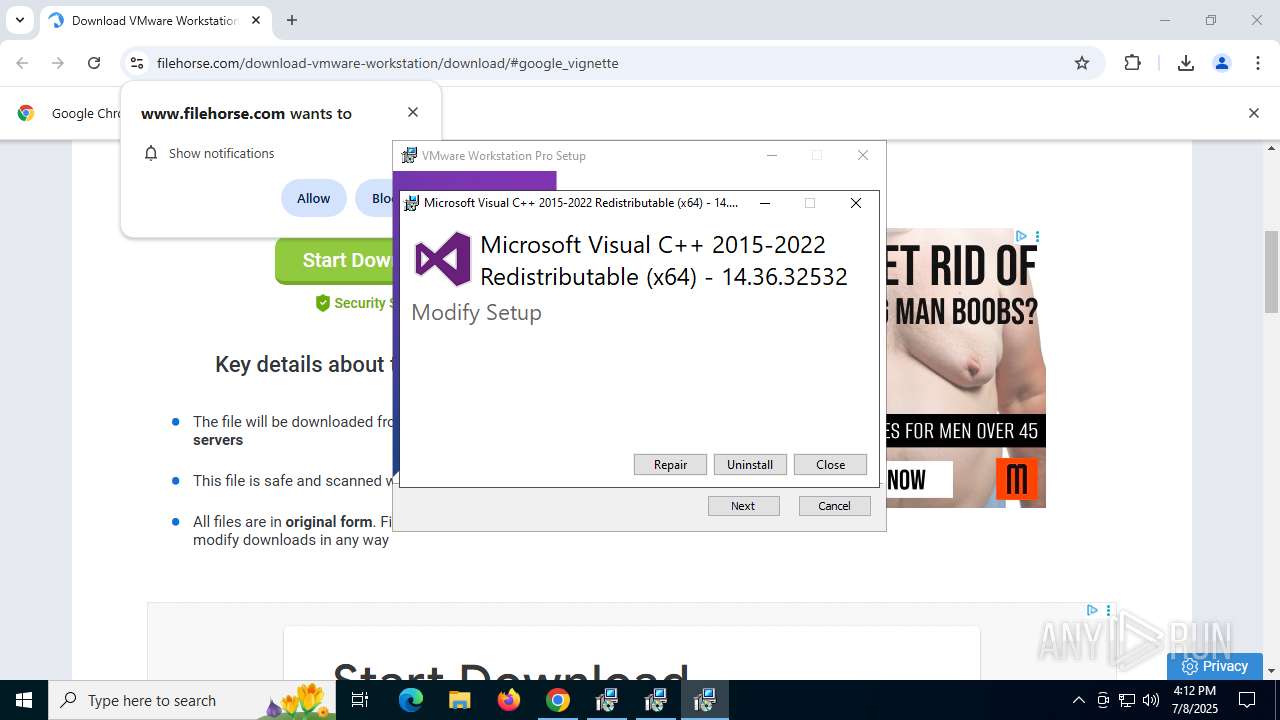
Manual execution by a user
- VC_redist.x86.exe (PID: 9056)
- VC_redist.x64.exe (PID: 6372)
Reads the machine GUID from the registry
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- msiexec.exe (PID: 5236)
- msiexec.exe (PID: 4664)
- vnetlib64.exe (PID: 8816)
- drvinst.exe (PID: 4968)
- drvinst.exe (PID: 5764)
- vnetlib64.exe (PID: 4512)
- drvinst.exe (PID: 6672)
- vnetlib64.exe (PID: 1700)
- msiexec.exe (PID: 7104)
- drvinst.exe (PID: 7728)
Creates files in the program directory
- VMware-workstation-17.6.3-24583834.exe (PID: 9044)
- vmnat.exe (PID: 3968)
- vmnetdhcp.exe (PID: 8744)
- vmware-usbarbitrator64.exe (PID: 5140)
Creates a software uninstall entry
- msiexec.exe (PID: 5236)
Creates or modifies Windows services
- msiexec.exe (PID: 7104)
Reads Environment values
- vmware-usbarbitrator64.exe (PID: 5140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
289
Monitored processes
126
Malicious processes
24
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6552,i,6480244339219756428,6679277527295387560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=8324 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 868 | "C:\WINDOWS\Temp\{554A8B28-8E7E-40A2-BD5C-2761E5EA024F}\.cr\vcredist_x86.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\{008FE649-7F8D-4960-A94C-17D0960C15A8}~setup\vcredist_x86.exe" -burn.filehandle.attached=572 -burn.filehandle.self=536 /Q /norestart | C:\Windows\Temp\{554A8B28-8E7E-40A2-BD5C-2761E5EA024F}\.cr\vcredist_x86.exe | — | vcredist_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6480,i,6480244339219756428,6679277527295387560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=8324 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1268 | "C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" | C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe | — | VC_redist.x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.36.32532 Exit code: 1602 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 1352 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | — | VC_redist.x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 1484 | "C:\Program Files (x86)\VMware\VMware Workstation\vnetlib64.exe" -- remove adapter vmnet17 | C:\Program Files (x86)\VMware\VMware Workstation\vnetlib64.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: VMware, Inc. Integrity Level: SYSTEM Description: VMware network install library executable Exit code: 4 Version: 17.6.3 build-24583834 Modules
| |||||||||||||||
| 1528 | DrvInst.exe "2" "211" "ROOT\VMWARE\0000" "C:\WINDOWS\INF\oem7.inf" "oem7.inf:fc9f1aa2477c2bb3:VMnetAdapter1.Install:17.6.0.0:*vmnetadapter1," "4cbdd083b" "000000000000021C" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1688 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5416 -s 892 | C:\Windows\SysWOW64\WerFault.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | "C:\Program Files (x86)\VMware\VMware Workstation\vnetlib64.exe" -- install vmx86inf 5;Win8 | C:\Program Files (x86)\VMware\VMware Workstation\vnetlib64.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: VMware, Inc. Integrity Level: SYSTEM Description: VMware network install library executable Exit code: 12 Version: 17.6.3 build-24583834 Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\Common Files\VMware\USB\DriverCache\vnetlib64.exe" -- install vmusb Win8 | C:\Program Files (x86)\Common Files\VMware\USB\DriverCache\vnetlib64.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: VMware, Inc. Integrity Level: SYSTEM Description: VMware network install library executable Exit code: 12 Version: 17.6.3 build-24552497 Modules
| |||||||||||||||
Total events
66 791
Read events
65 193
Write events
1 474
Delete events
124
Modification events
| (PID) Process: | (5020) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5020) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5020) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5020) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5020) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1984) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000FB78C01023F0DB01C0070000A4200000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1984) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000004BAAE61023F0DB01C0070000A4200000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1984) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000007F71EB1023F0DB01C0070000A4200000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6900) VC_redist.x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000BF14BE1023F0DB01F41A0000881C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1984) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000004BAAE61023F0DB01C0070000A4200000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
254
Suspicious files
215
Text files
412
Unknown types
305
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF175e2d.TMP | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF175e3d.TMP | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF175e3d.TMP | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF175e5c.TMP | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF175e5c.TMP | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF175e5c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
355
DNS requests
432
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6408 | chrome.exe | GET | 200 | 172.217.18.14:80 | http://clients2.google.com/time/1/current?cup2key=8:zN9taIlxLIKcyCyT9FwdlYSisUNbbdUSGrgWEAe8IK4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2520 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8668 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
9084 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
8668 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
9084 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
9084 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
9084 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4916 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6408 | chrome.exe | 104.20.1.51:443 | www.filehorse.com | CLOUDFLARENET | — | whitelisted |
6408 | chrome.exe | 142.250.185.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
6408 | chrome.exe | 172.217.18.14:80 | clients2.google.com | GOOGLE | US | whitelisted |
6408 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6408 | chrome.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.filehorse.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
static.filehorse.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
spn-v1.revampcdn.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6408 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6408 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6408 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6408 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6408 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6408 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6408 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6408 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6408 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6408 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
Process | Message |
|---|---|
VMware-workstation-17.6.3-24583834.exe | Start Pre-load DLLs.
|
VMware-workstation-17.6.3-24583834.exe | Win32U_GetFileAttributes: GetFileAttributesExW("C:\Users\admin\Downloads\1033.bmp", ...) failed, error: 2
|
VMware-workstation-17.6.3-24583834.exe | Win32U_GetFileAttributes: GetFileAttributesExW("C:\Users\admin\AppData\Local\Temp\{008FE649-7F8D-4960-A94C-17D0960C15A8}~setup\", ...) failed, error: 2
|
vmnat.exe | CodeSet_Init: no ICU
|
vmnetdhcp.exe | CodeSet_Init: no ICU
|
vmware-usbarbitrator64.exe | CodeSet_Init: no ICU
|