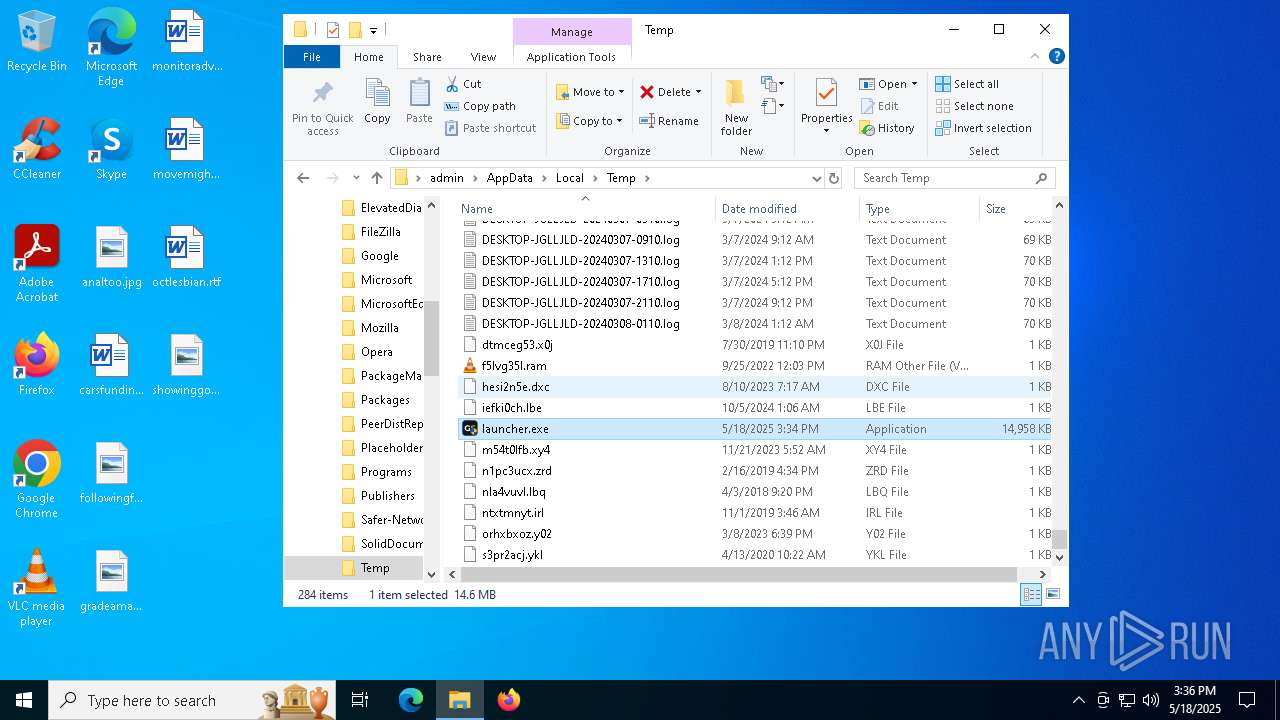
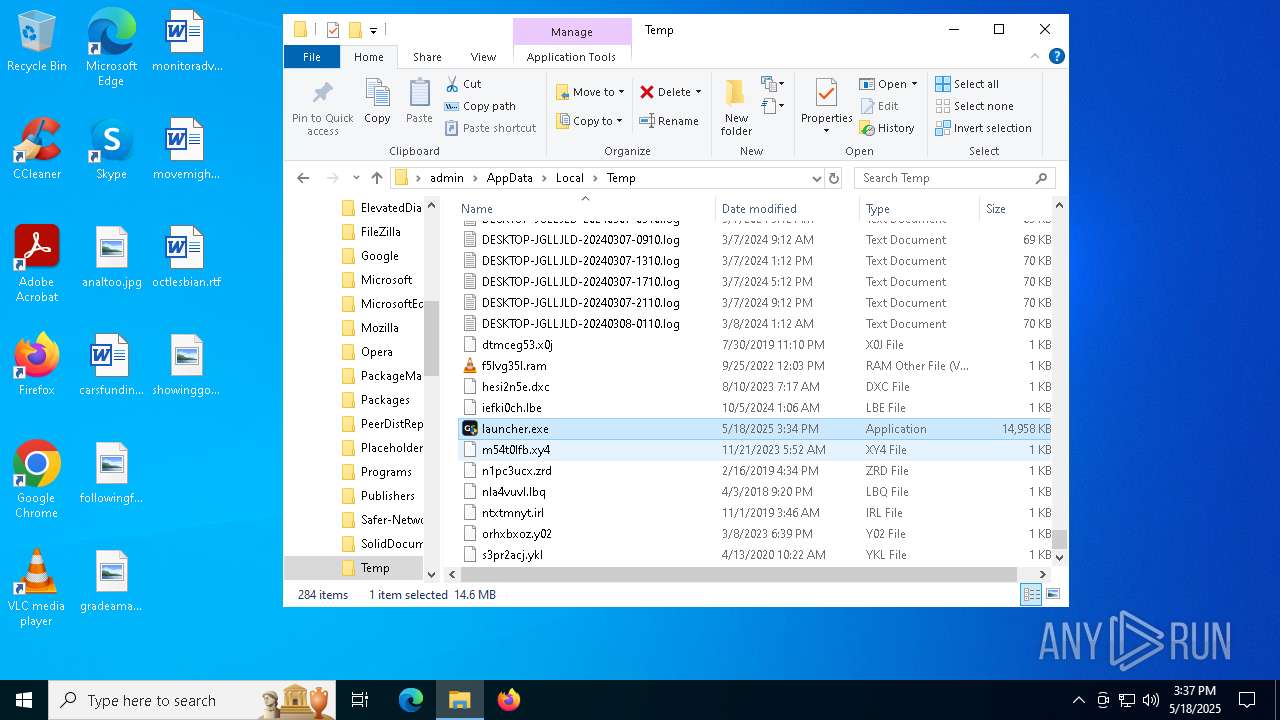
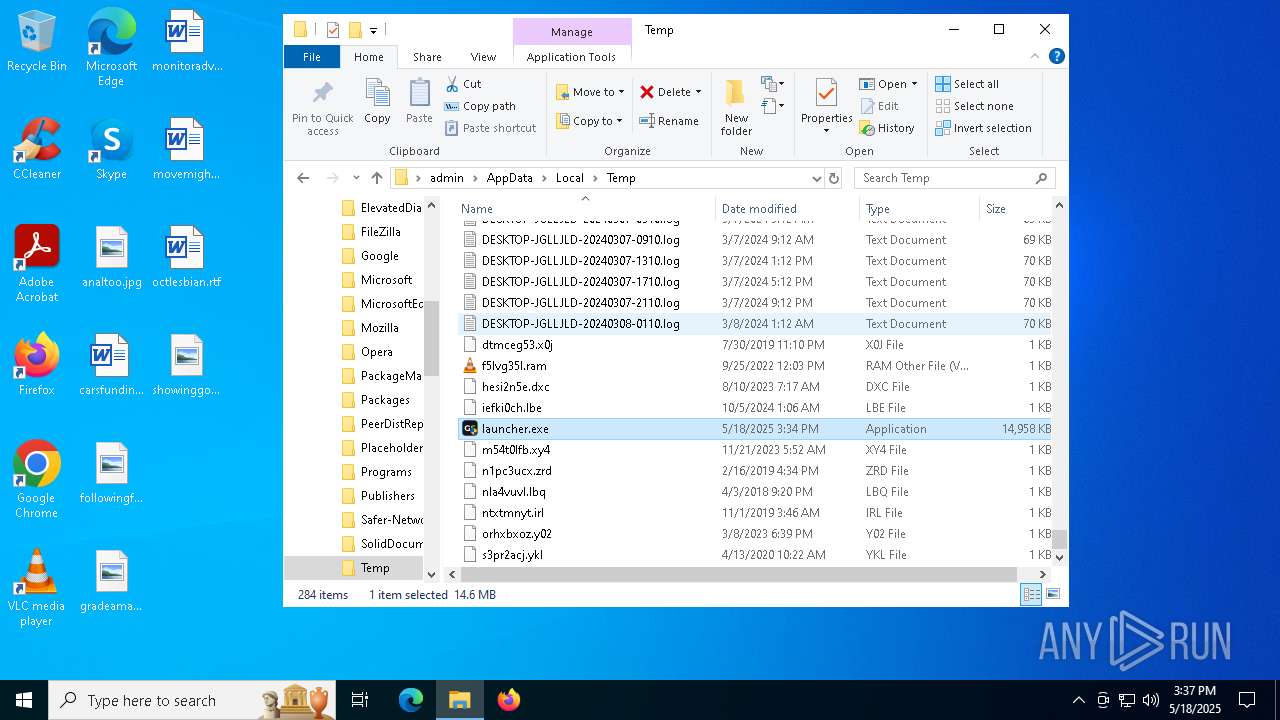
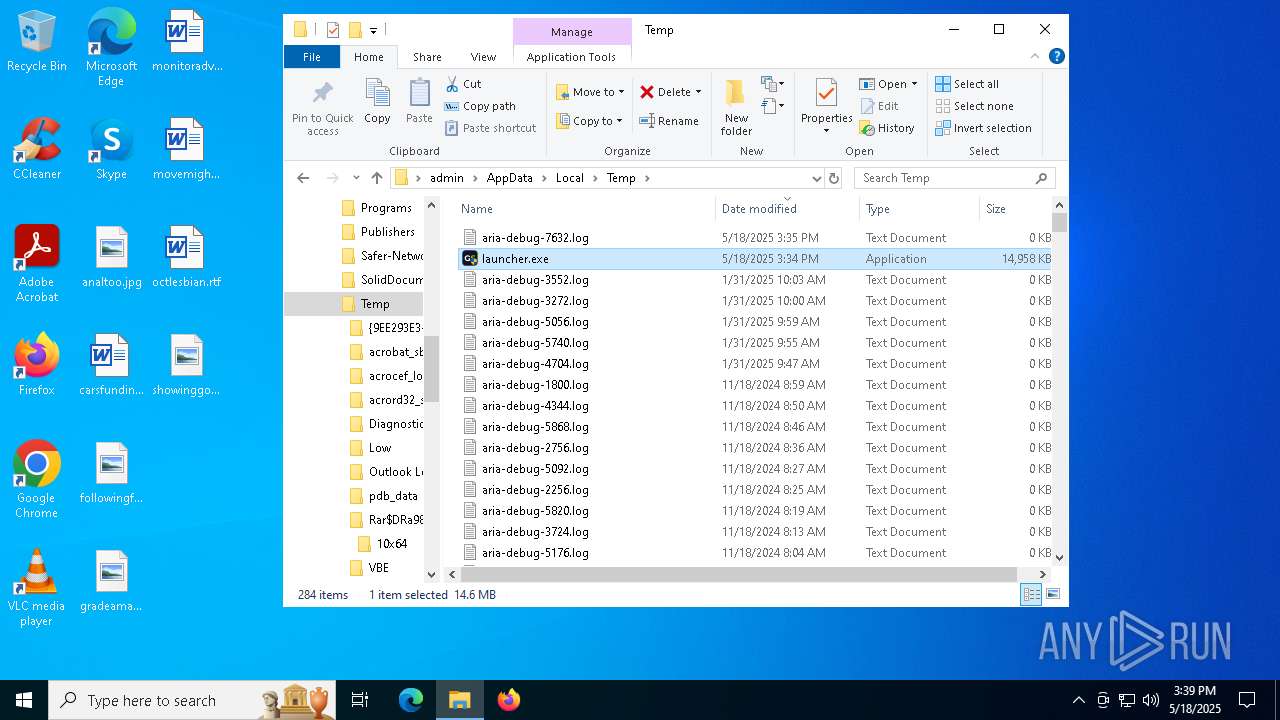
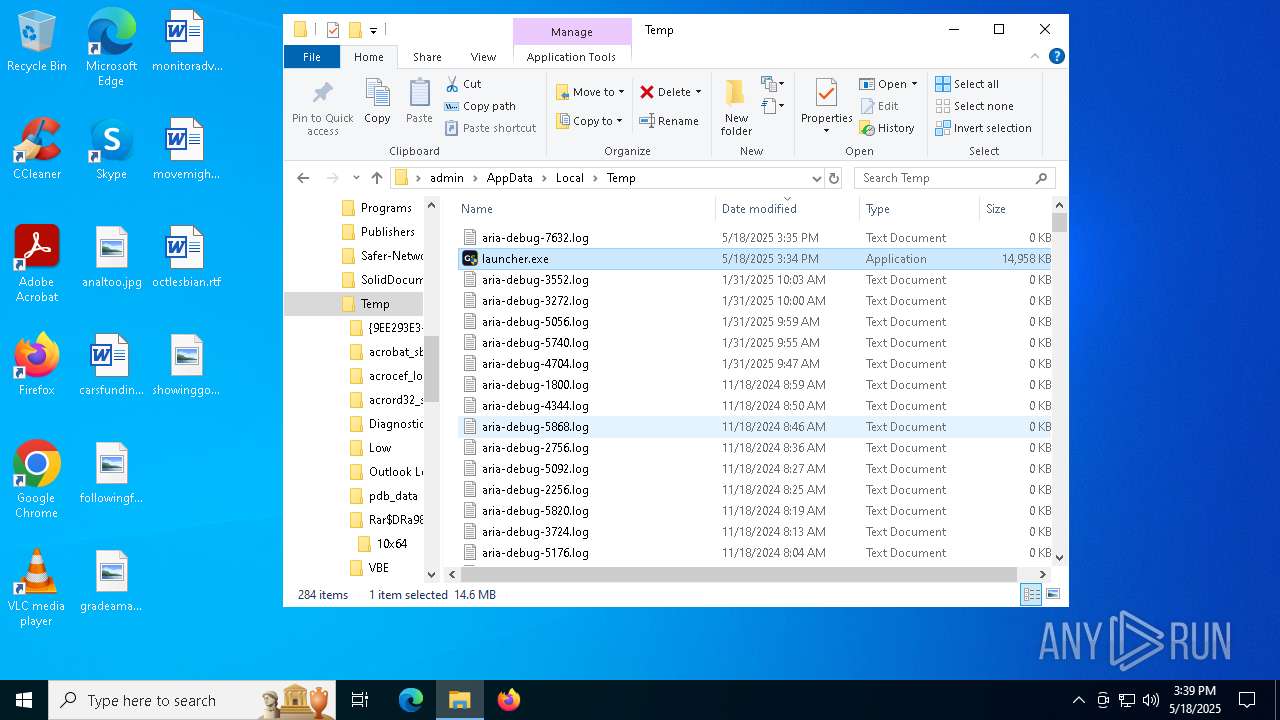
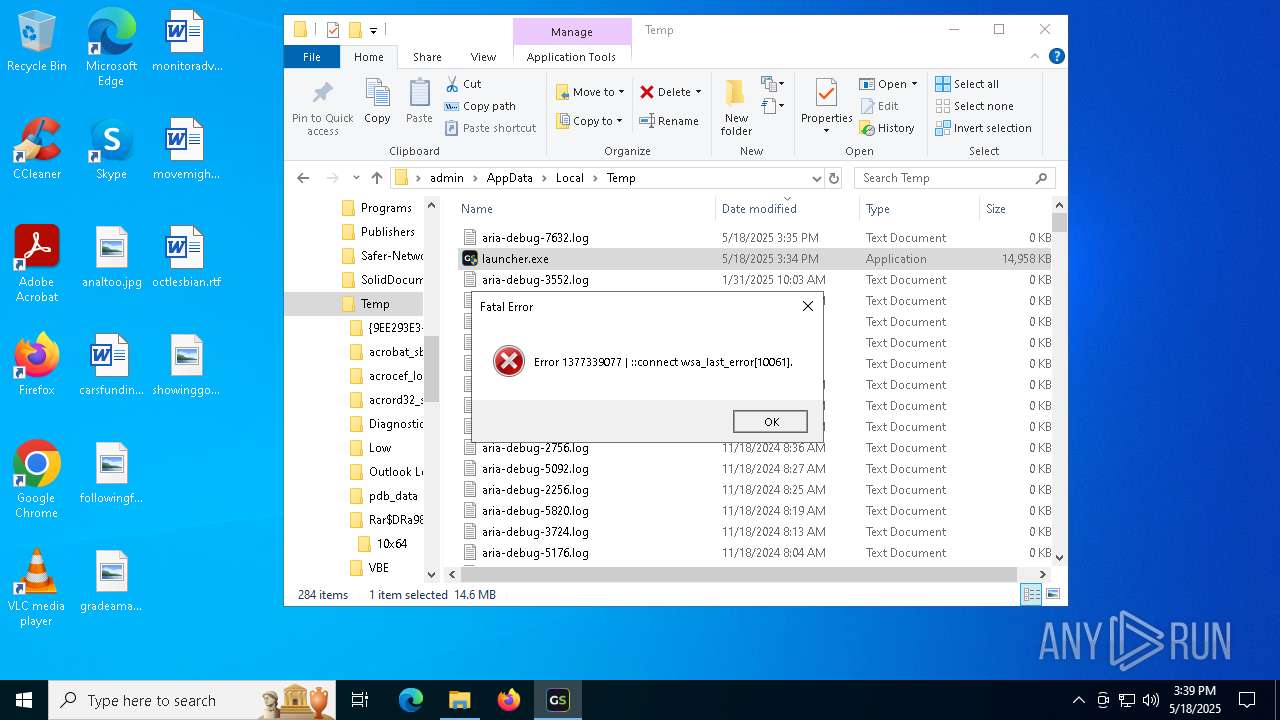
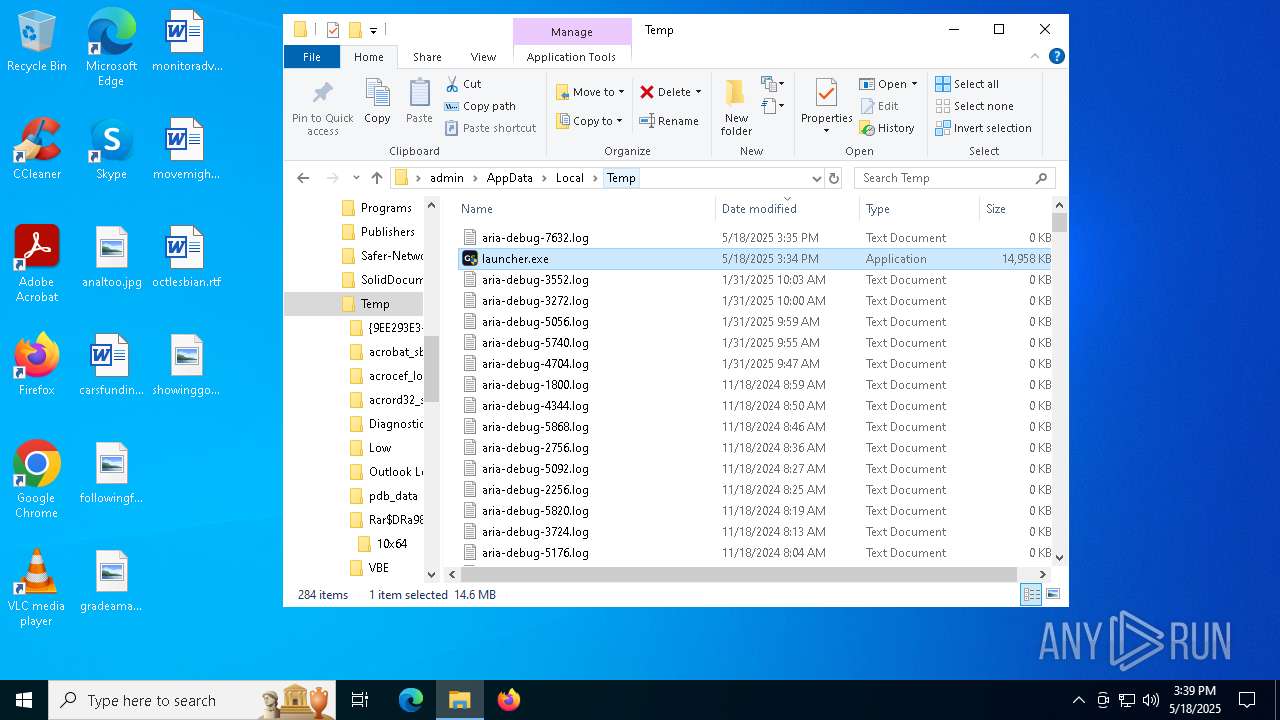
| File name: | launcher.exe |
| Full analysis: | https://app.any.run/tasks/044f7e9b-6187-48f9-a096-1de0adeb3acd |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 15:34:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | E2C01DABC296BE449E01877B7E11F74B |
| SHA1: | 6CAF2988C3D169F4F3DED073CF37A0BCF70AE553 |
| SHA256: | 98CEB8FF2F72A8083A29D04939C5F6E943DB91E94085ABE3F1E3CBB804A9BC18 |
| SSDEEP: | 393216:3g1bWv2lAiNifVQ/NSBk+VI8LXLGHsLE:3y6v2NyVQ/cVhGv |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- launcher.exe (PID: 7340)
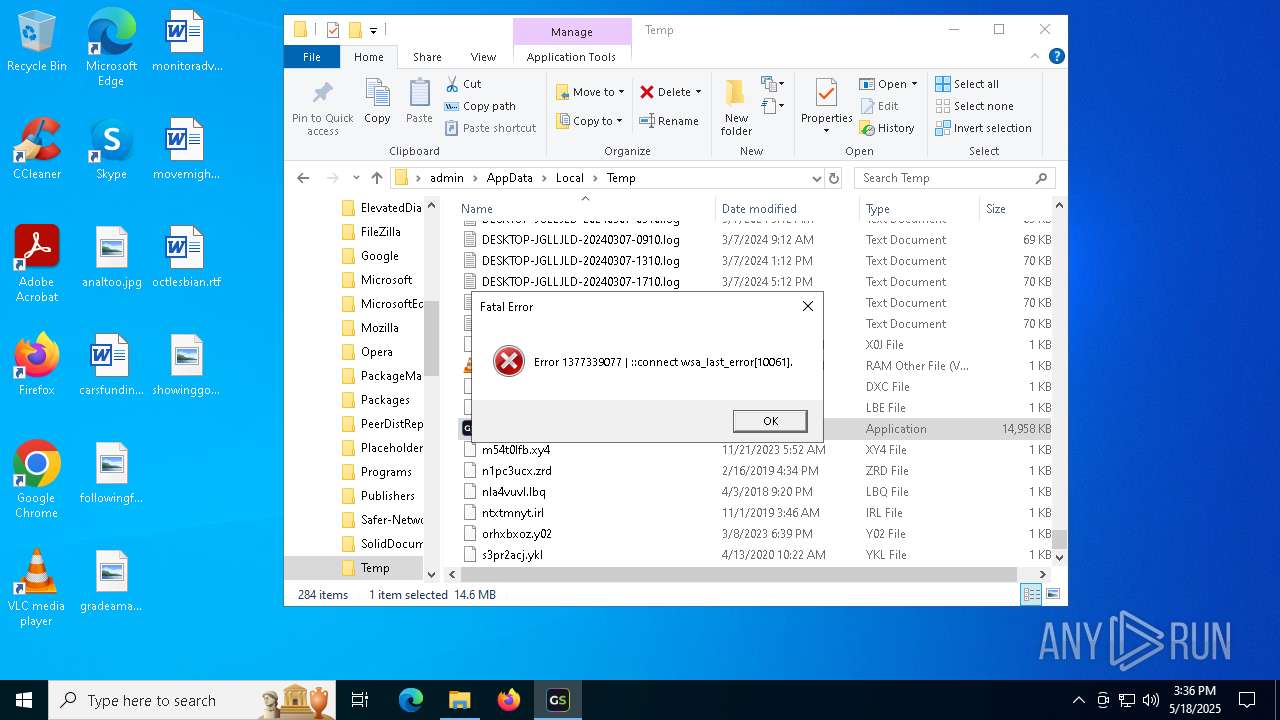
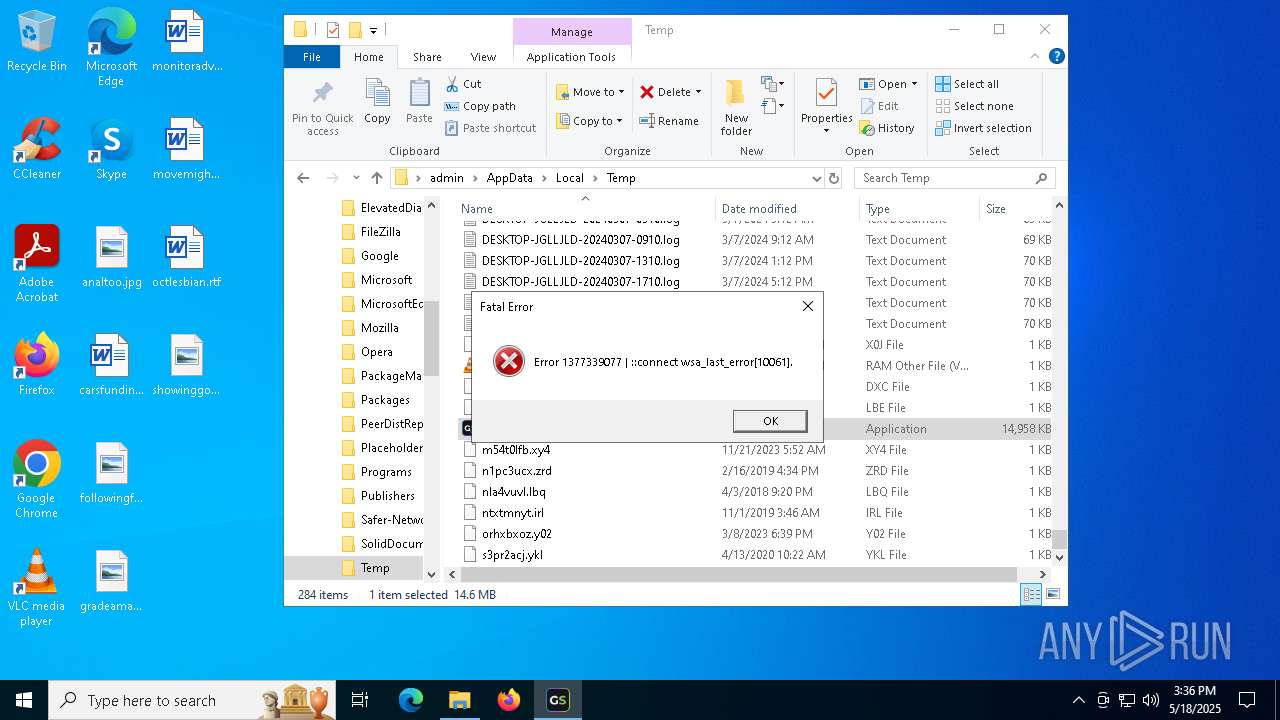
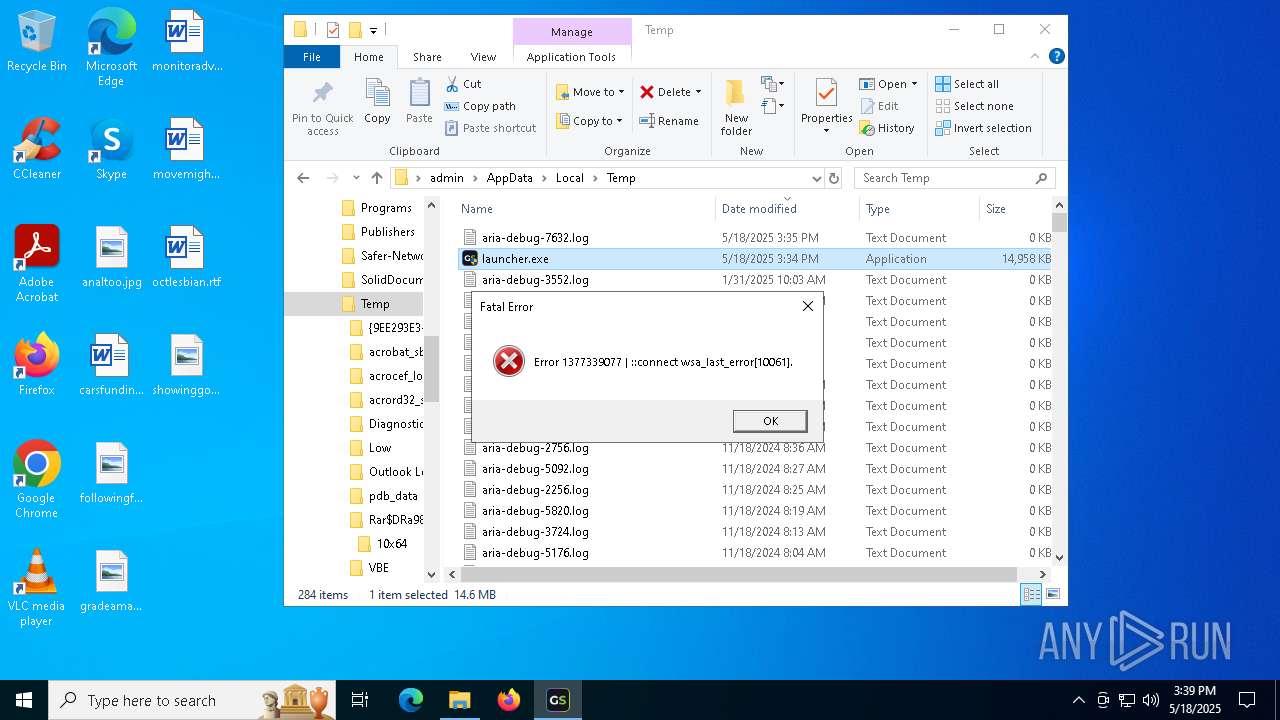
Connects to unusual port
- launcher.exe (PID: 7340)
- launcher.exe (PID: 6644)
- launcher.exe (PID: 6564)
- launcher.exe (PID: 968)
- launcher.exe (PID: 7388)
INFO
Reads the computer name
- launcher.exe (PID: 7340)
- launcher.exe (PID: 6644)
- launcher.exe (PID: 6564)
Checks supported languages
- launcher.exe (PID: 7340)
- launcher.exe (PID: 6644)
- launcher.exe (PID: 6564)
Checks proxy server information
- launcher.exe (PID: 7340)
- slui.exe (PID: 7904)
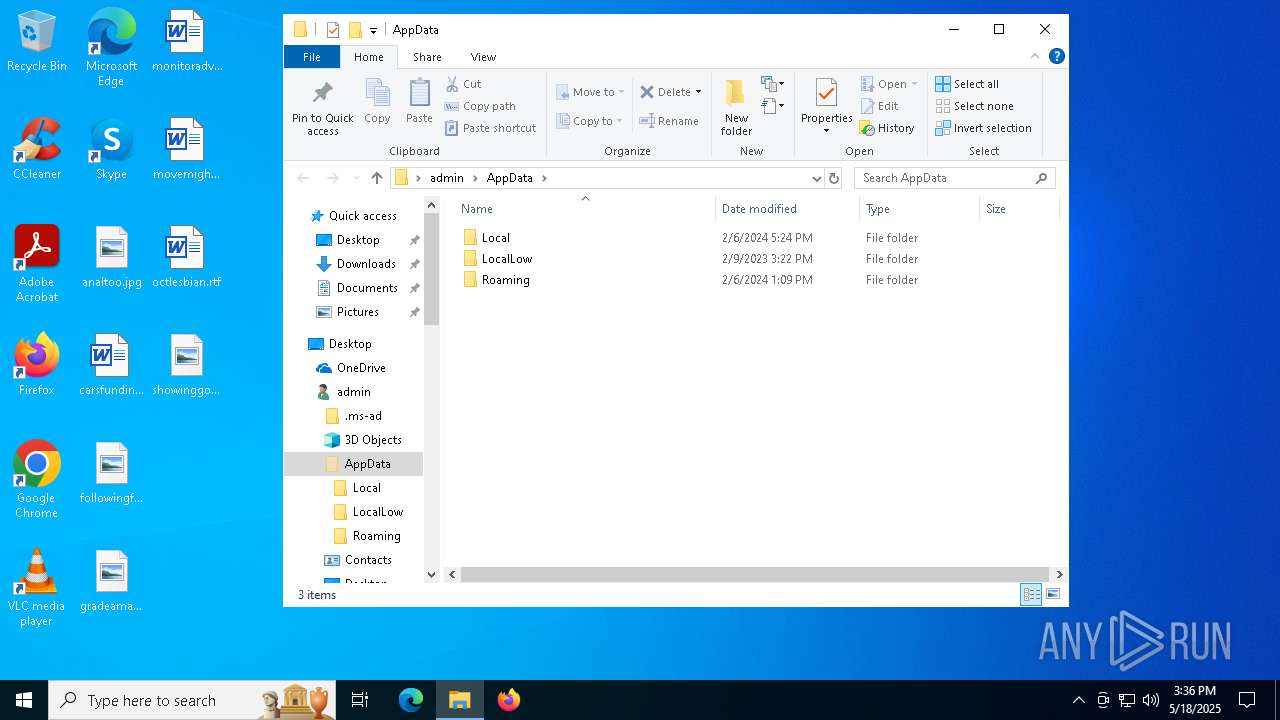
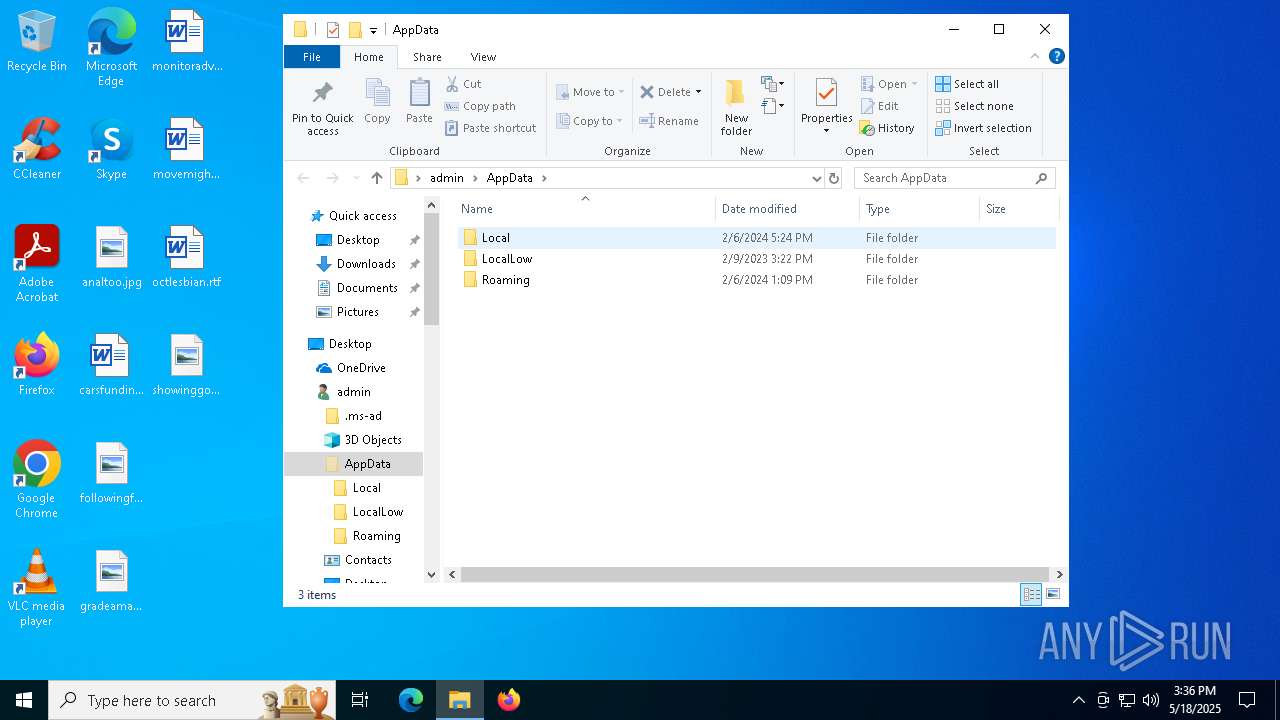
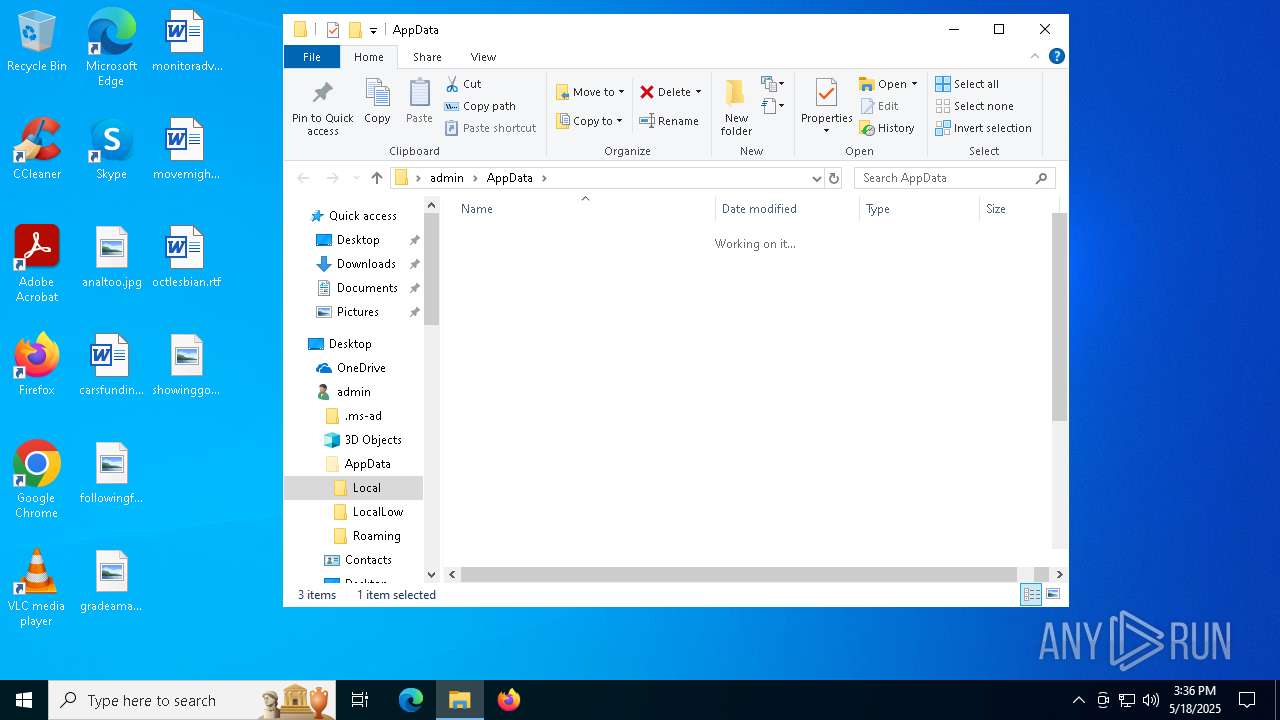
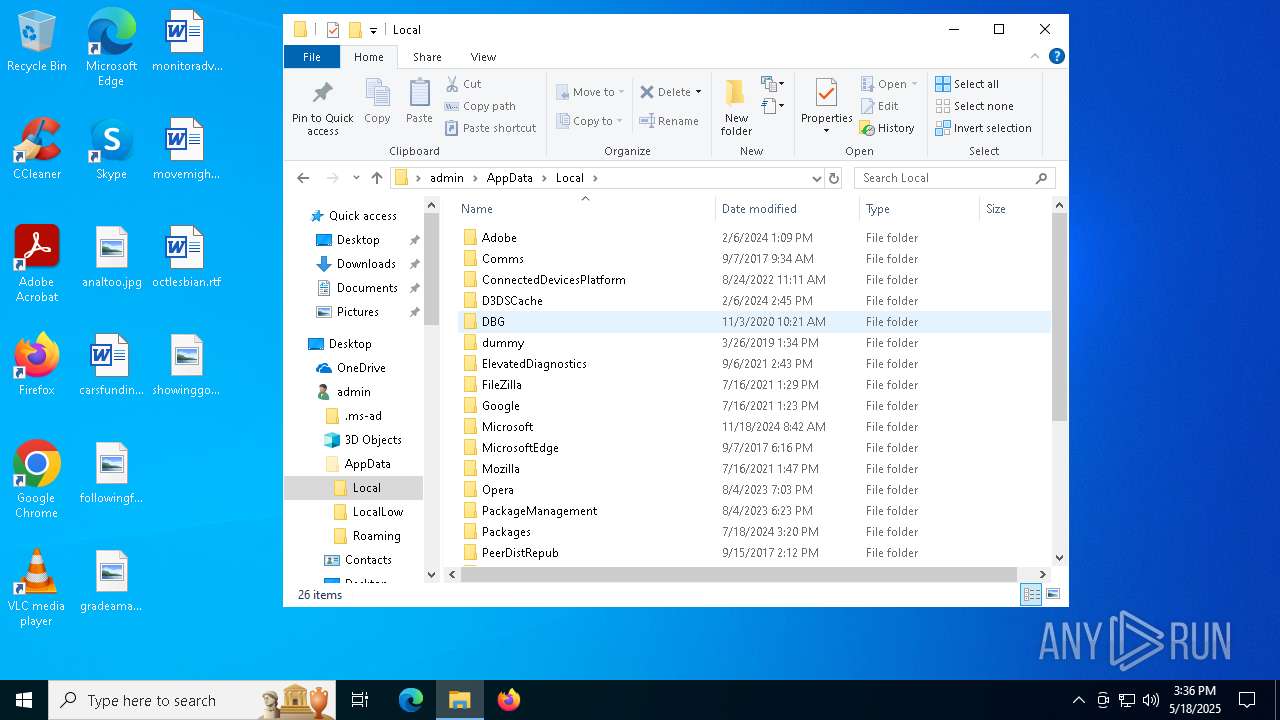
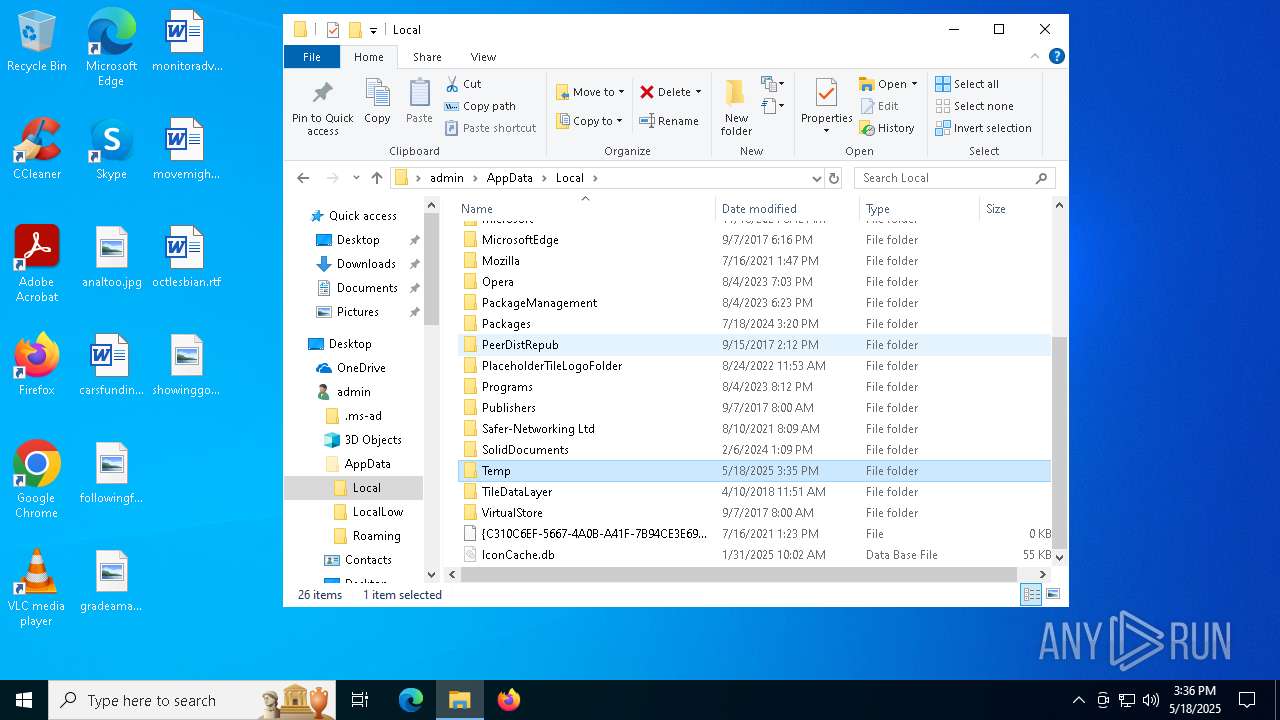
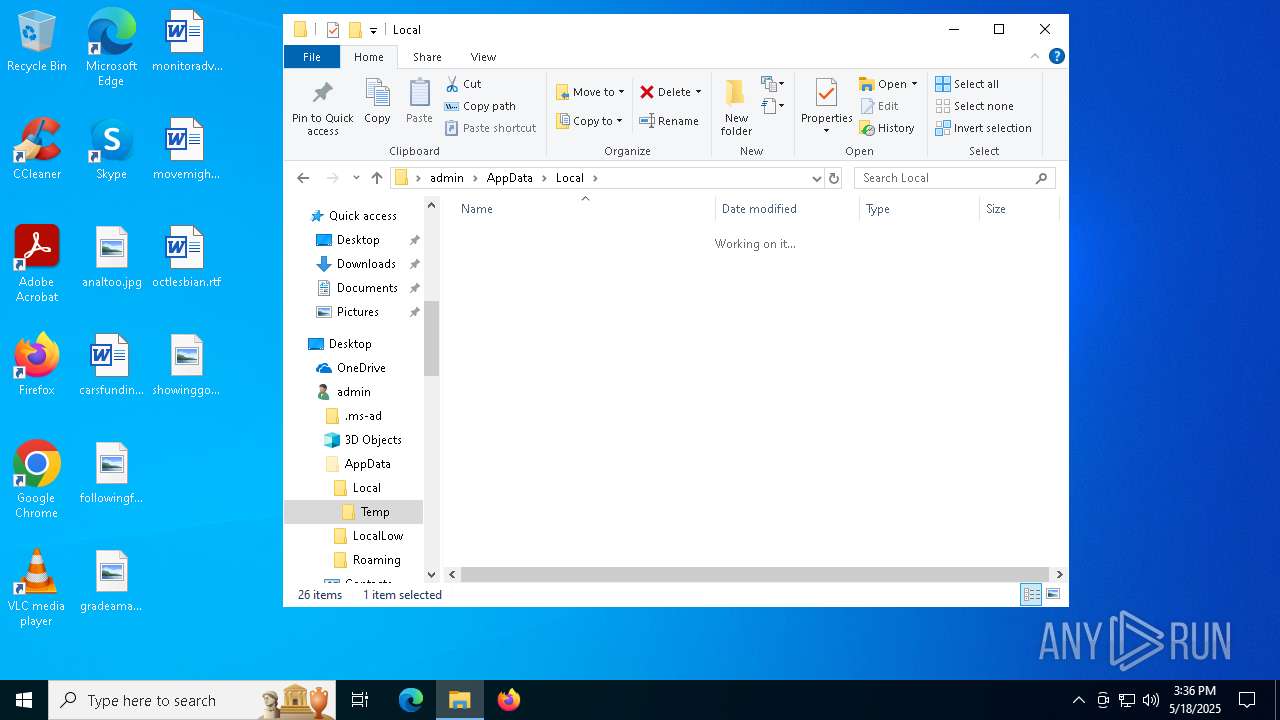
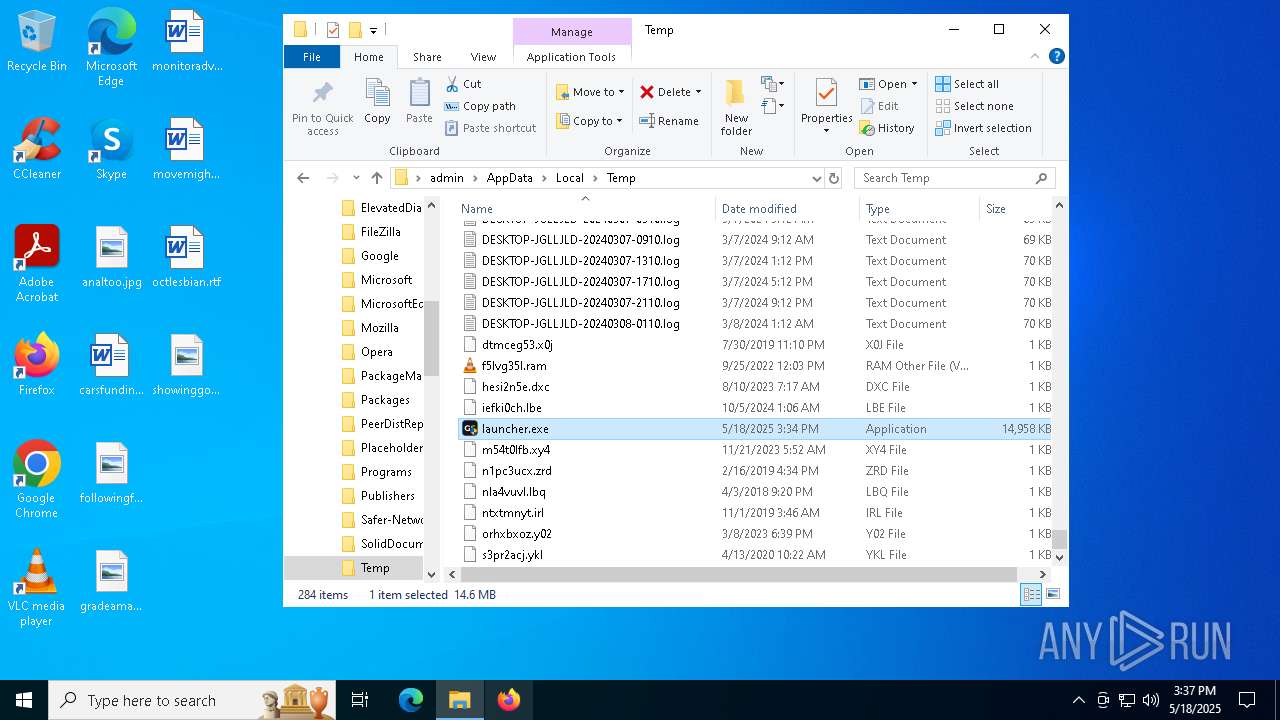
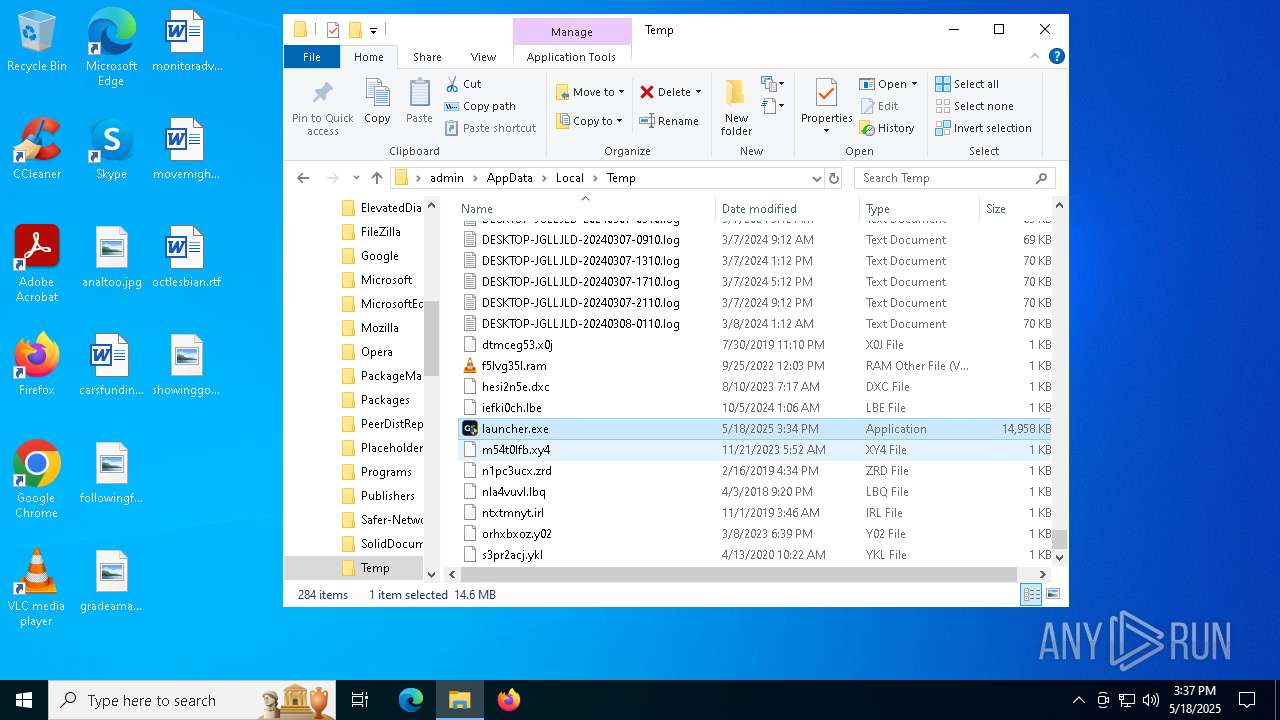
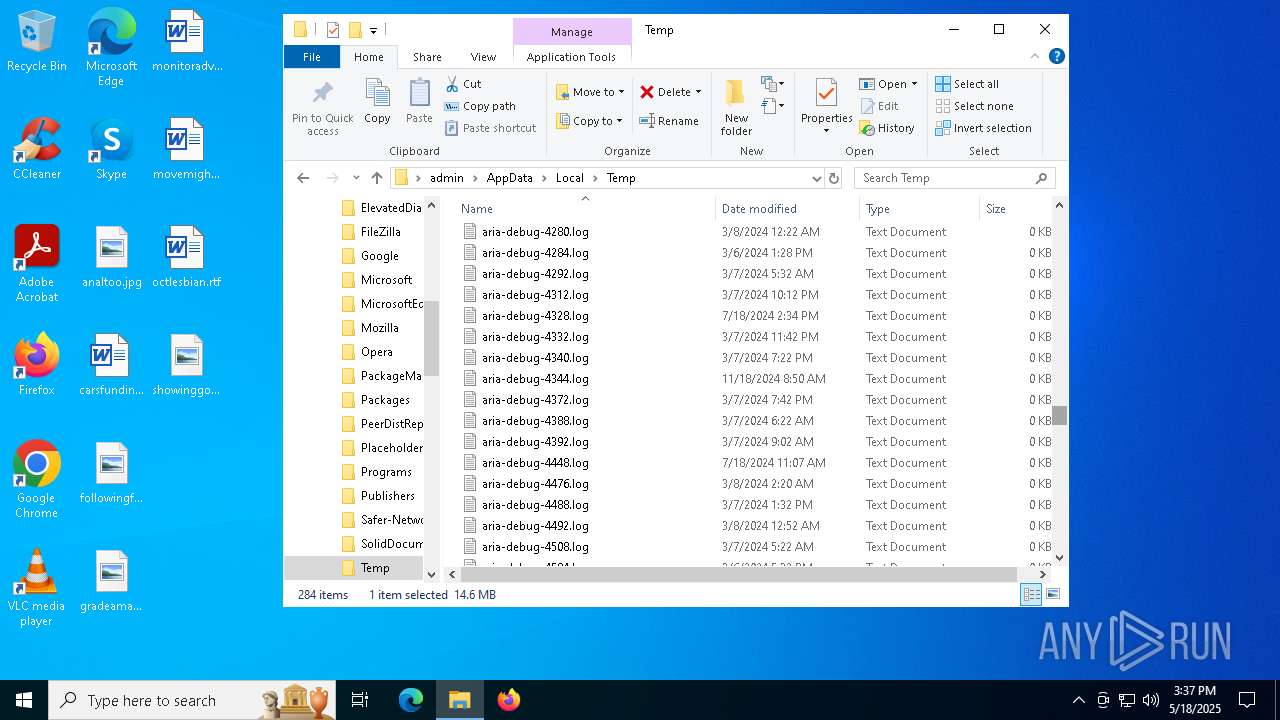
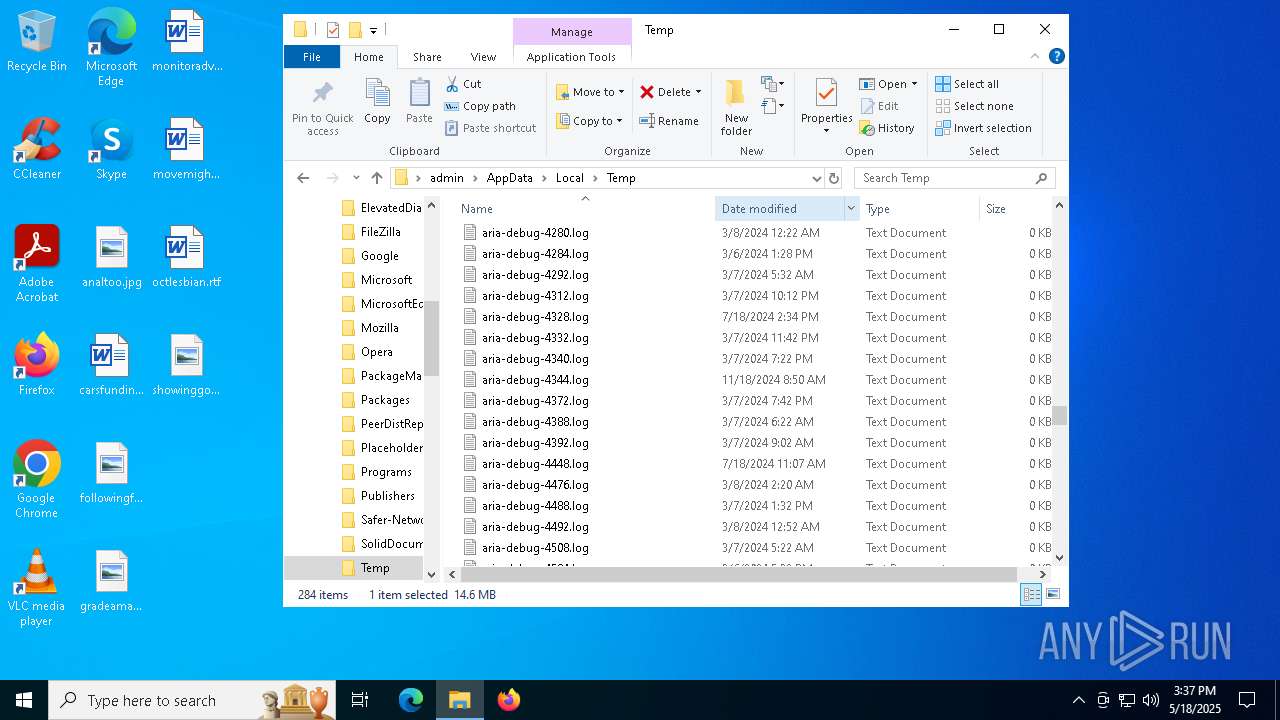
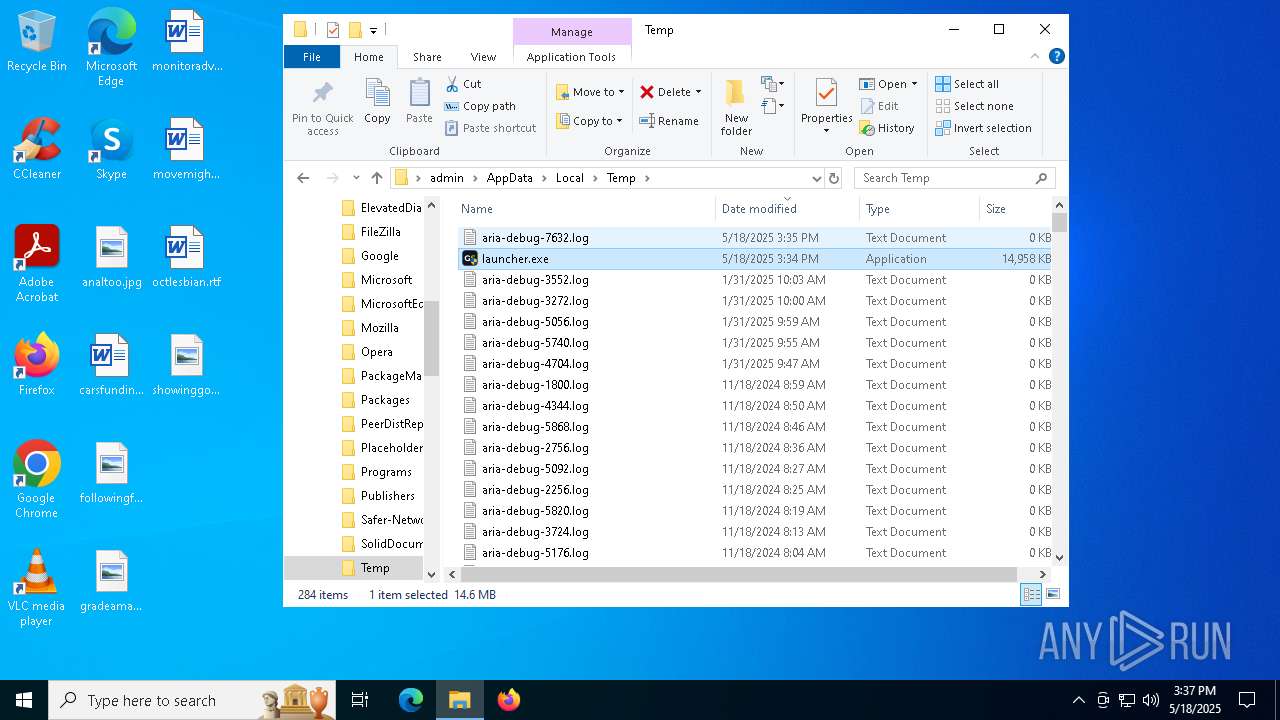
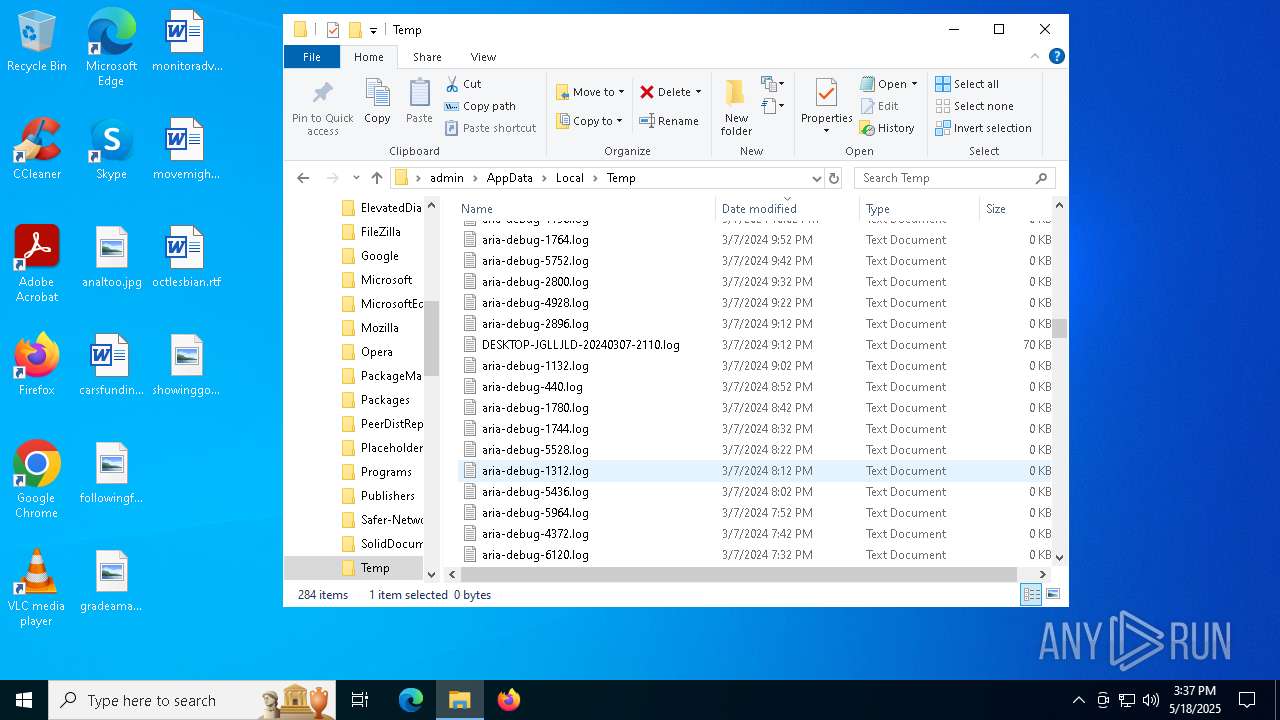
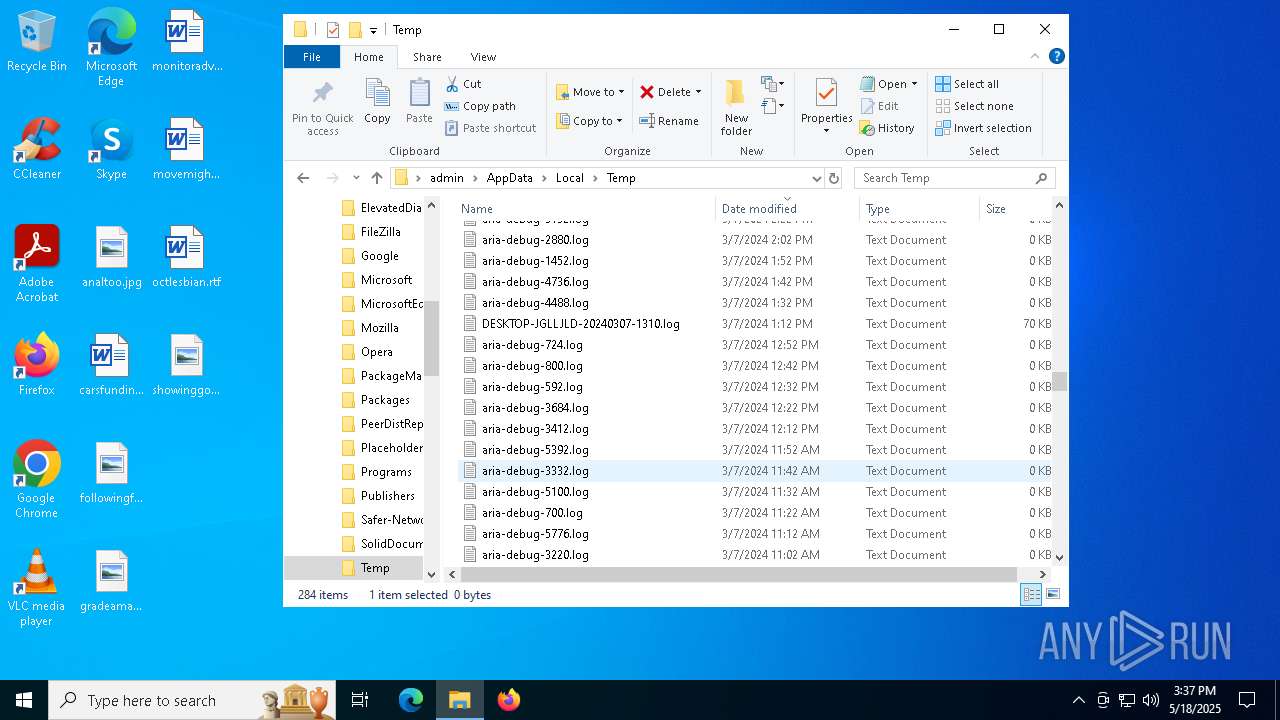
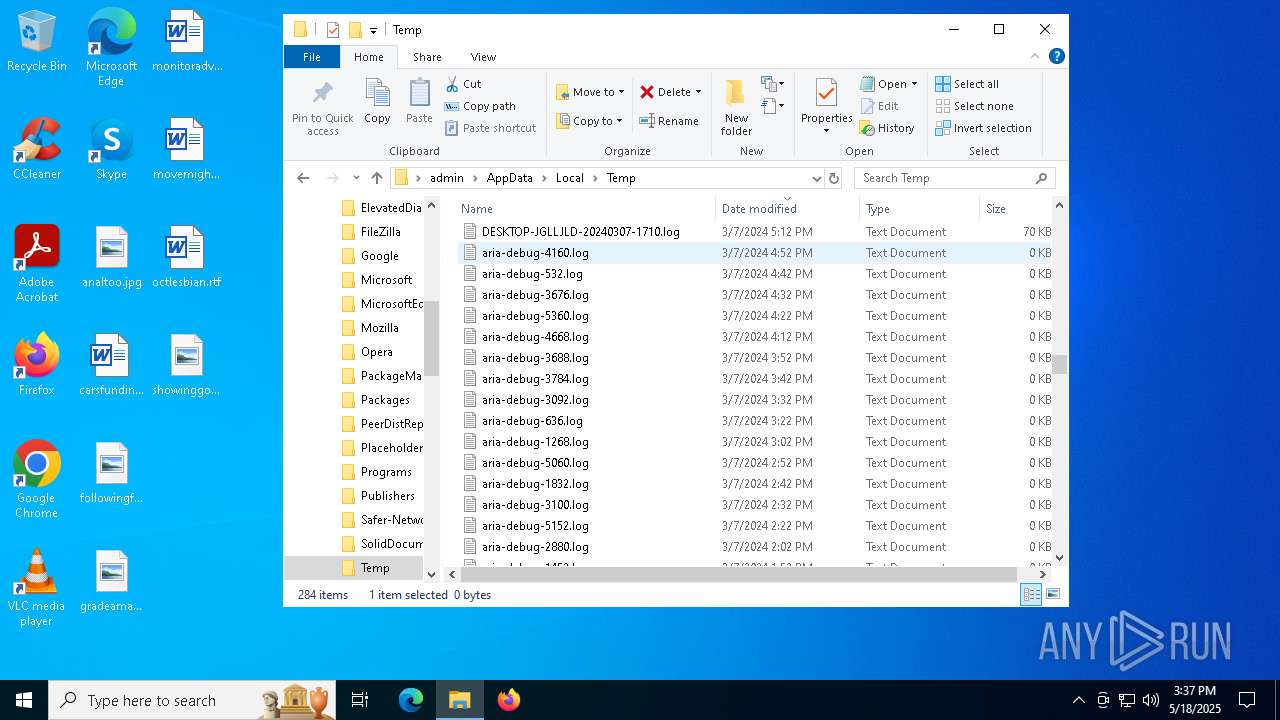
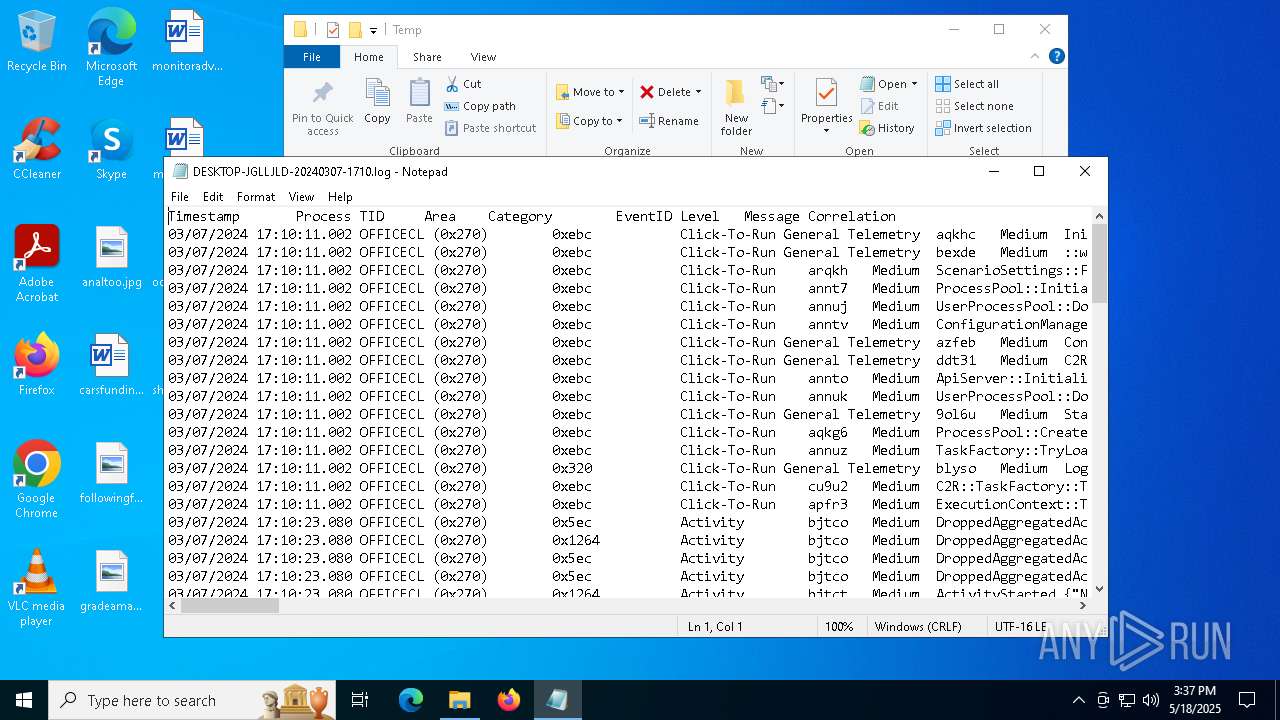
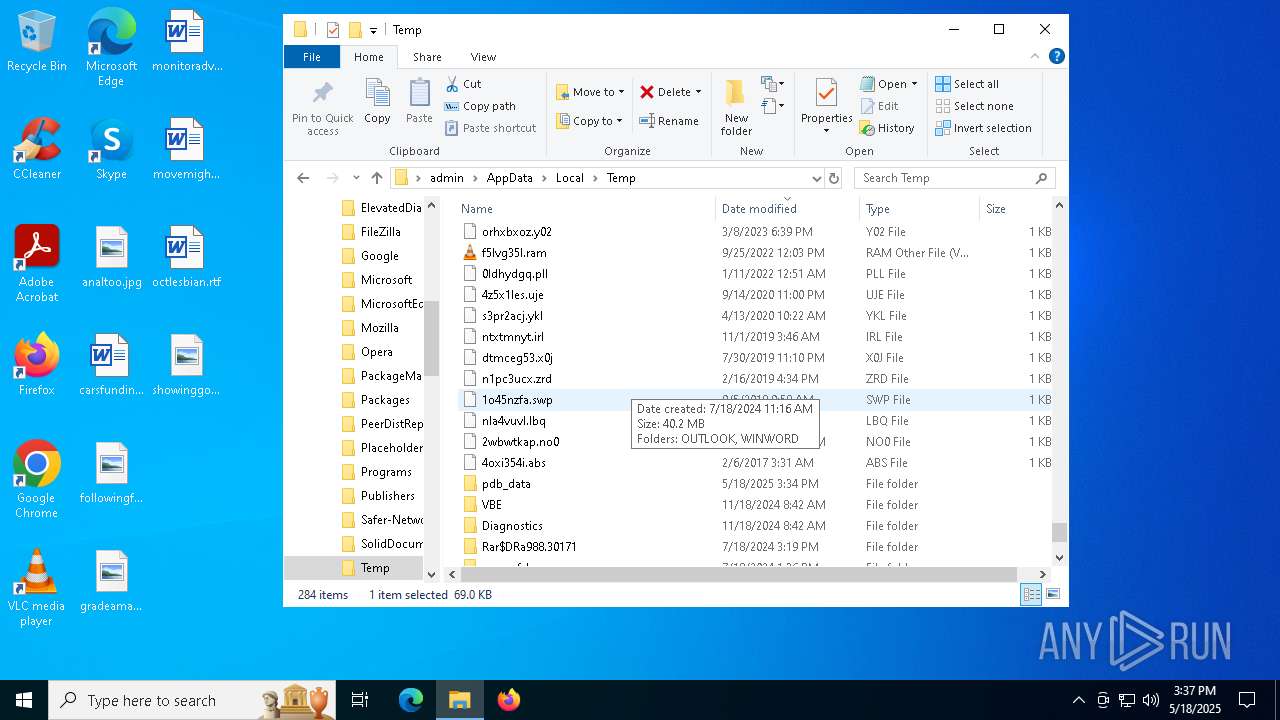
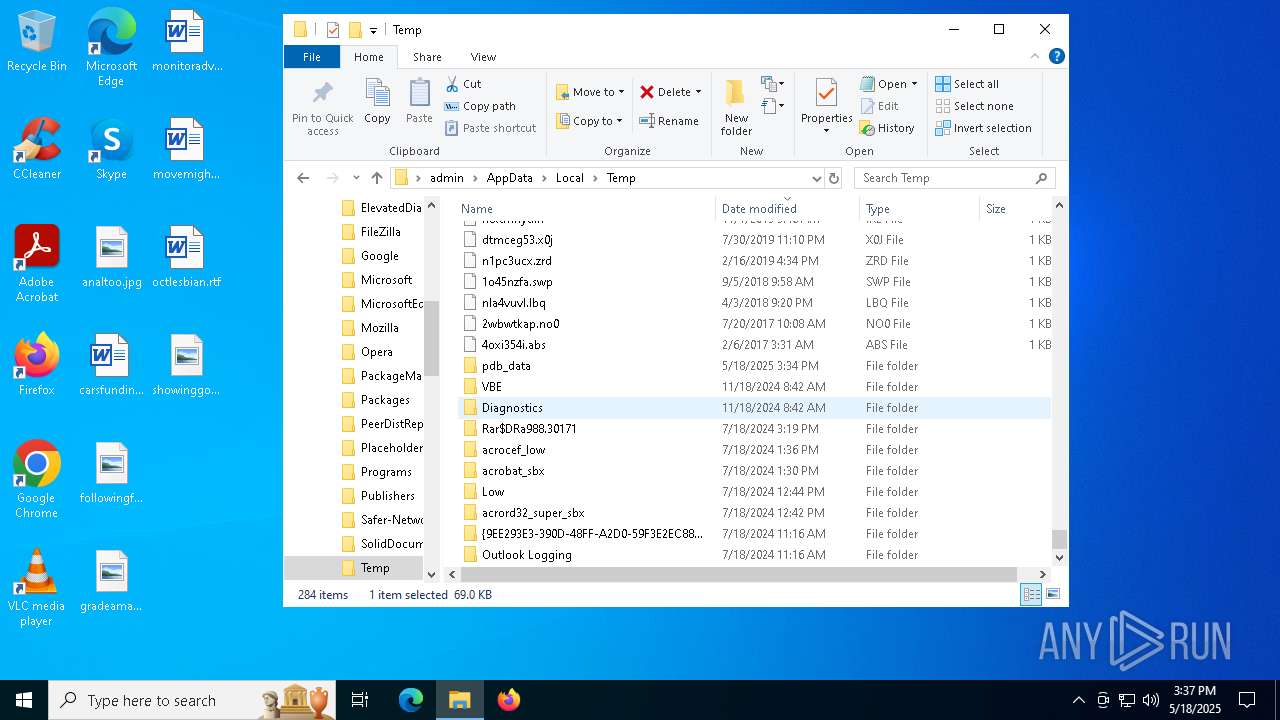
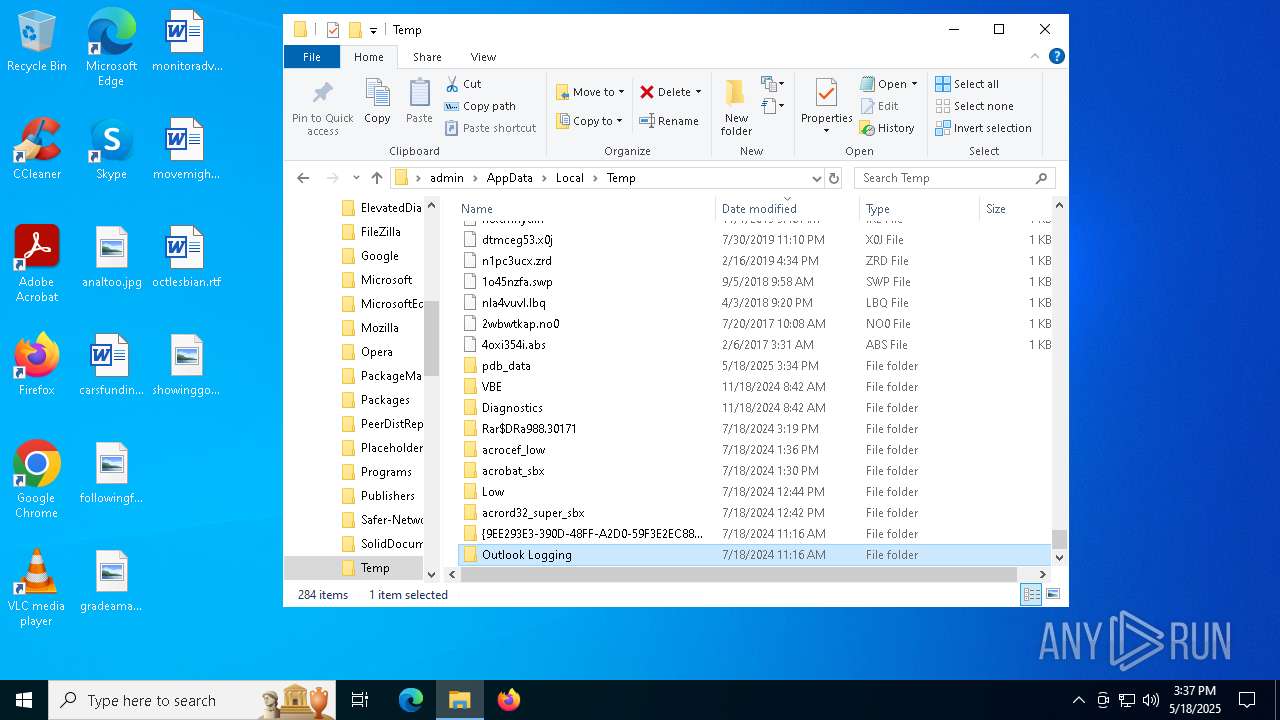
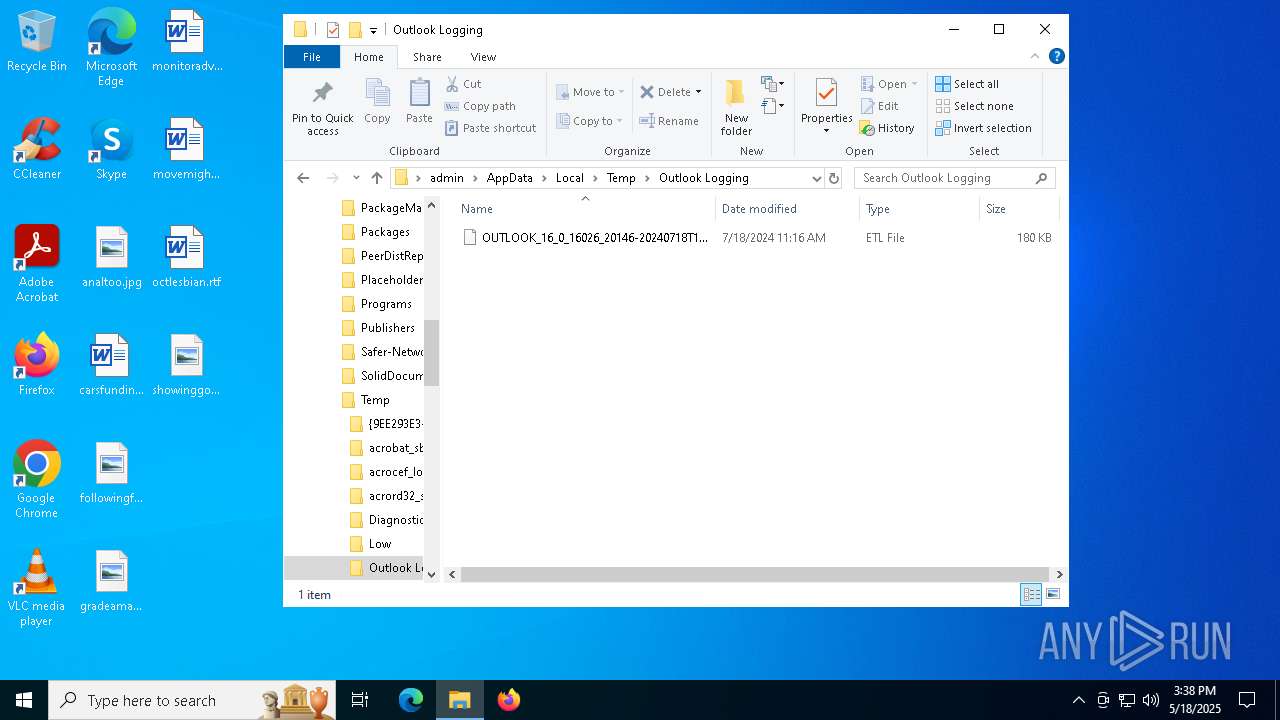
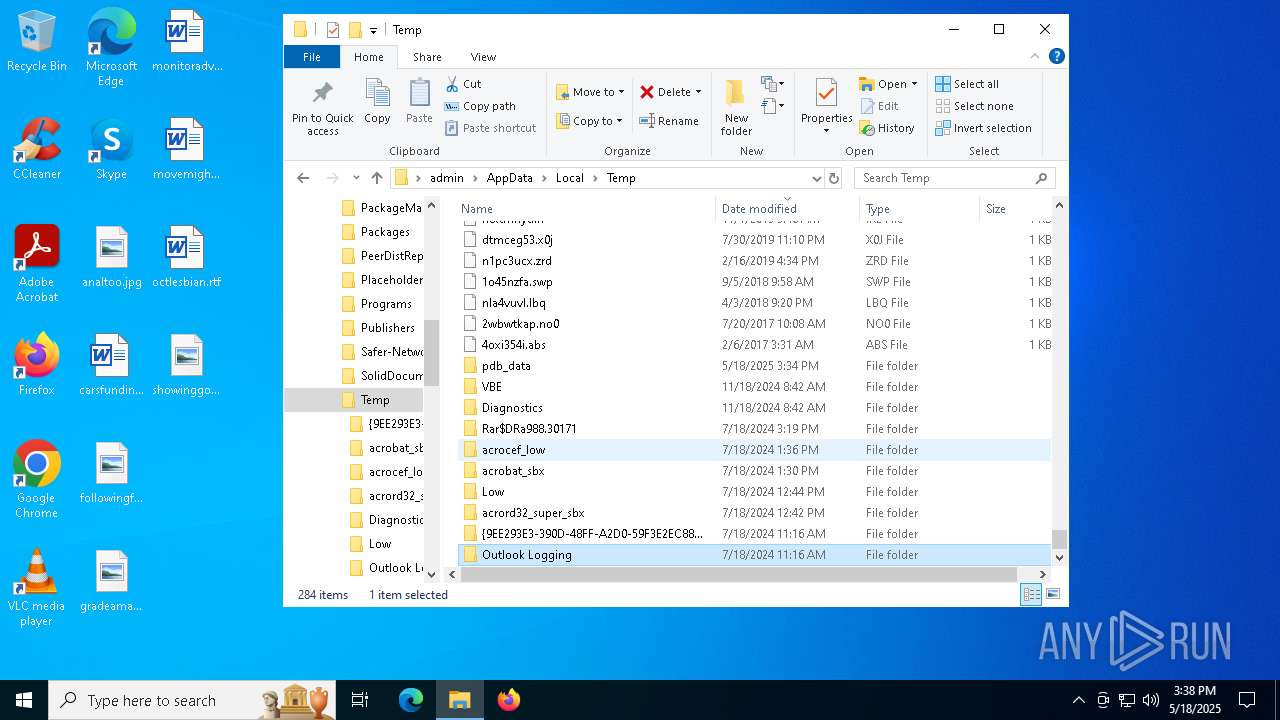
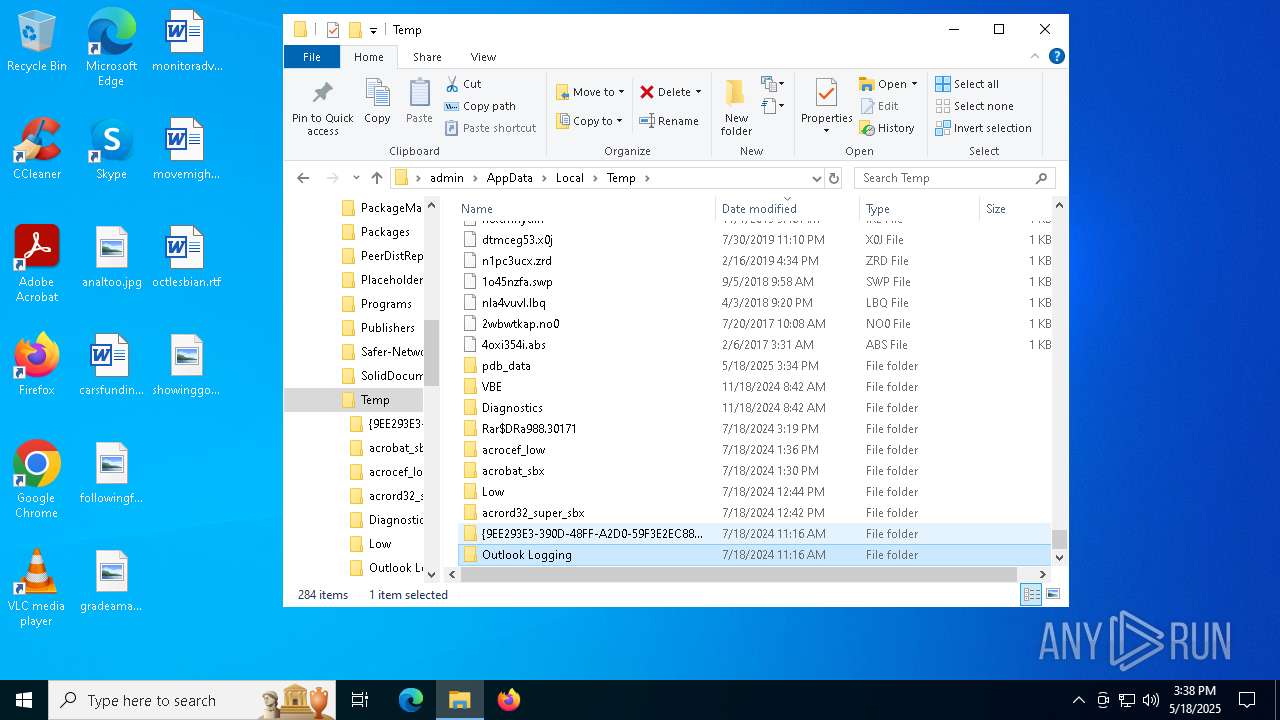
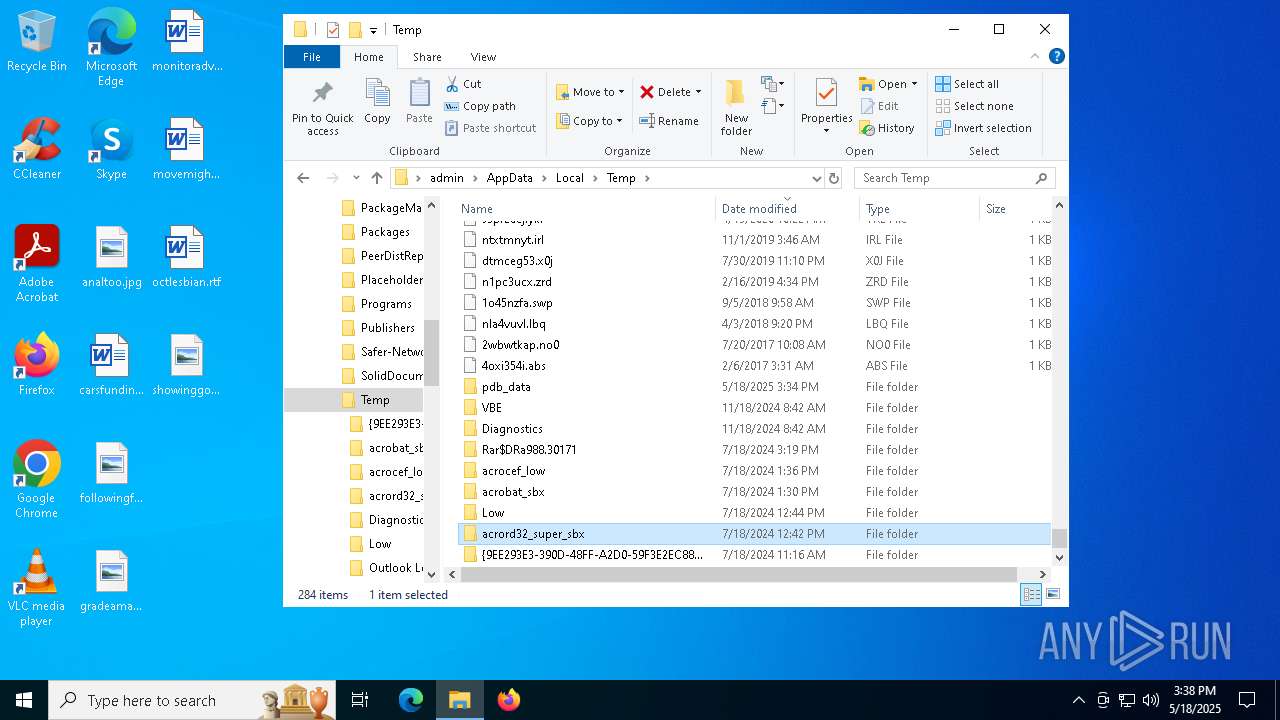
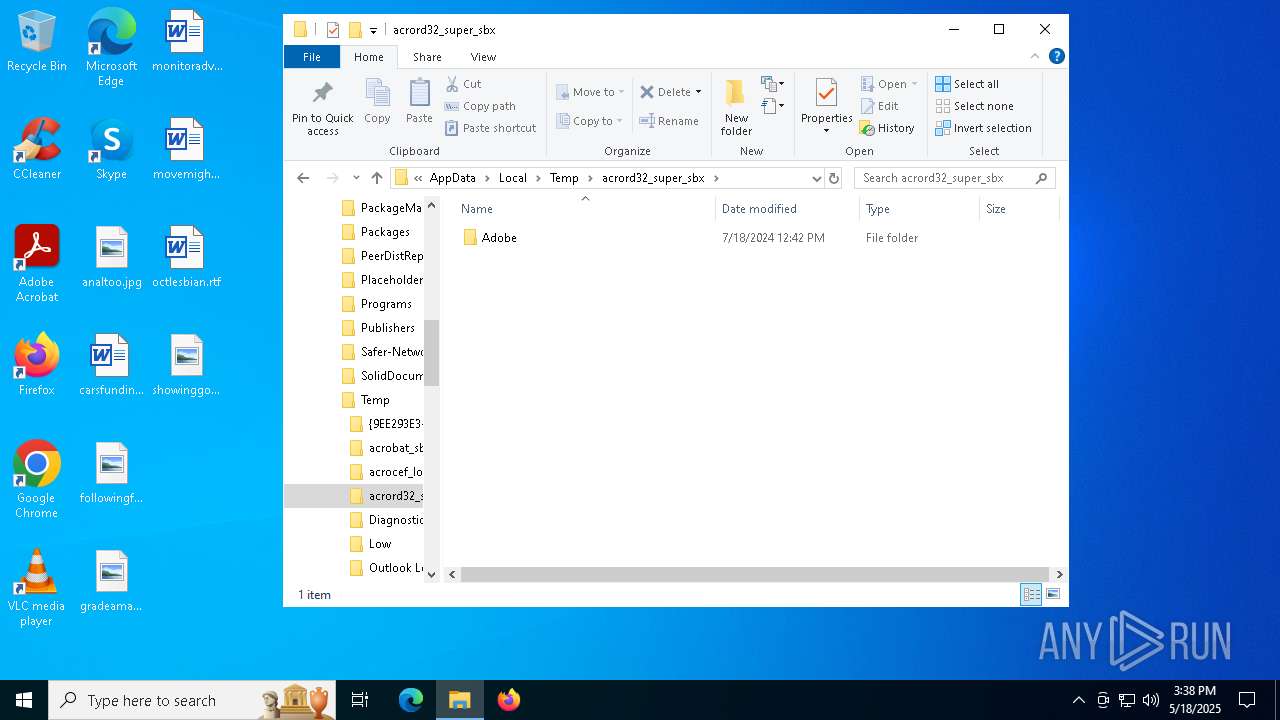
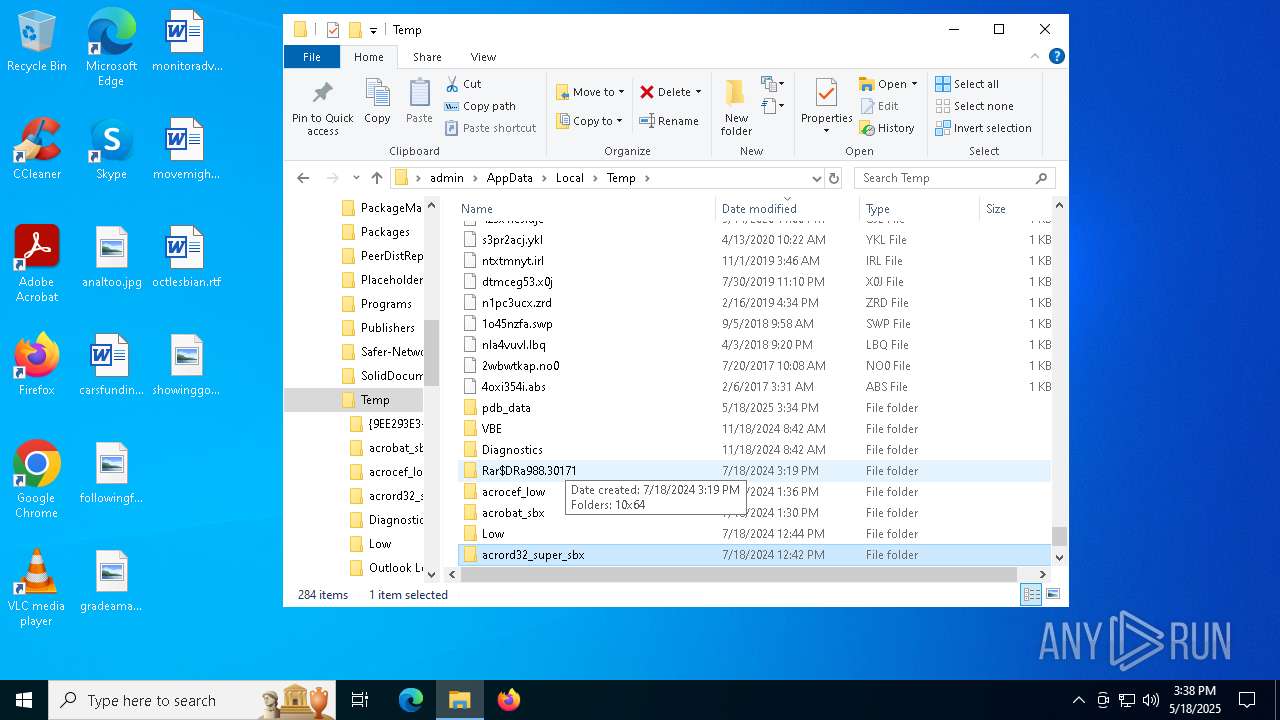
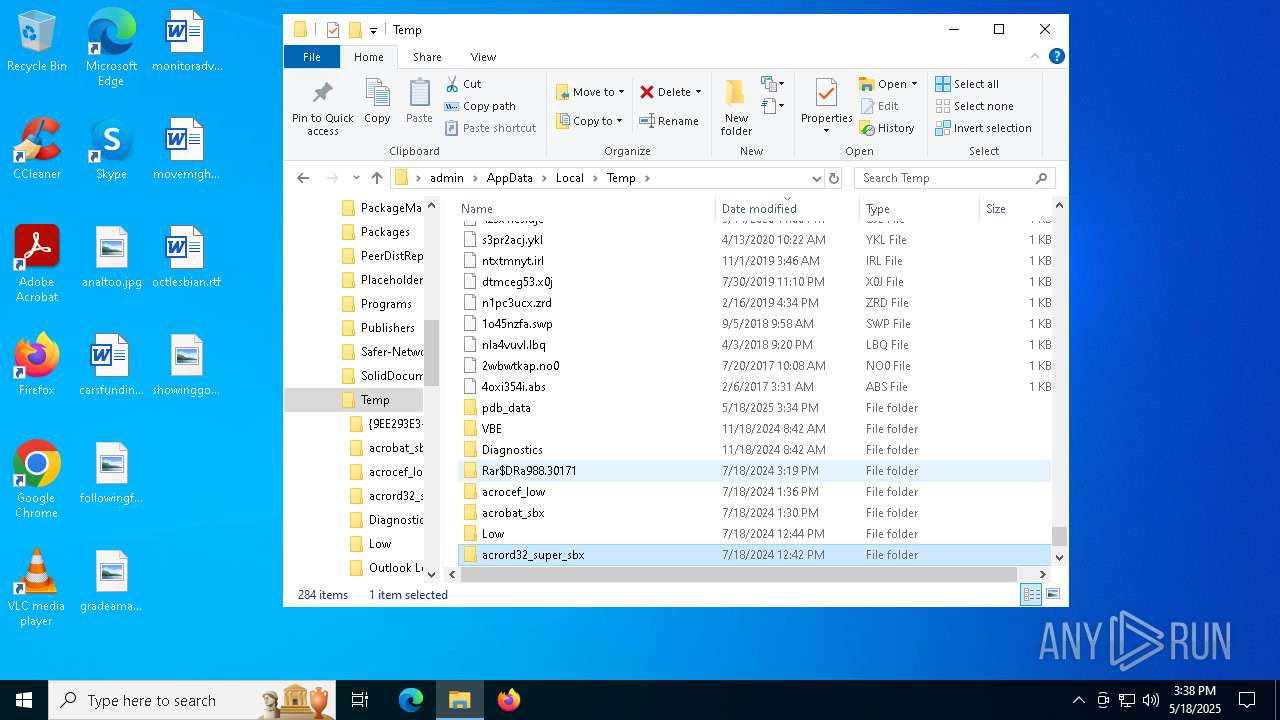
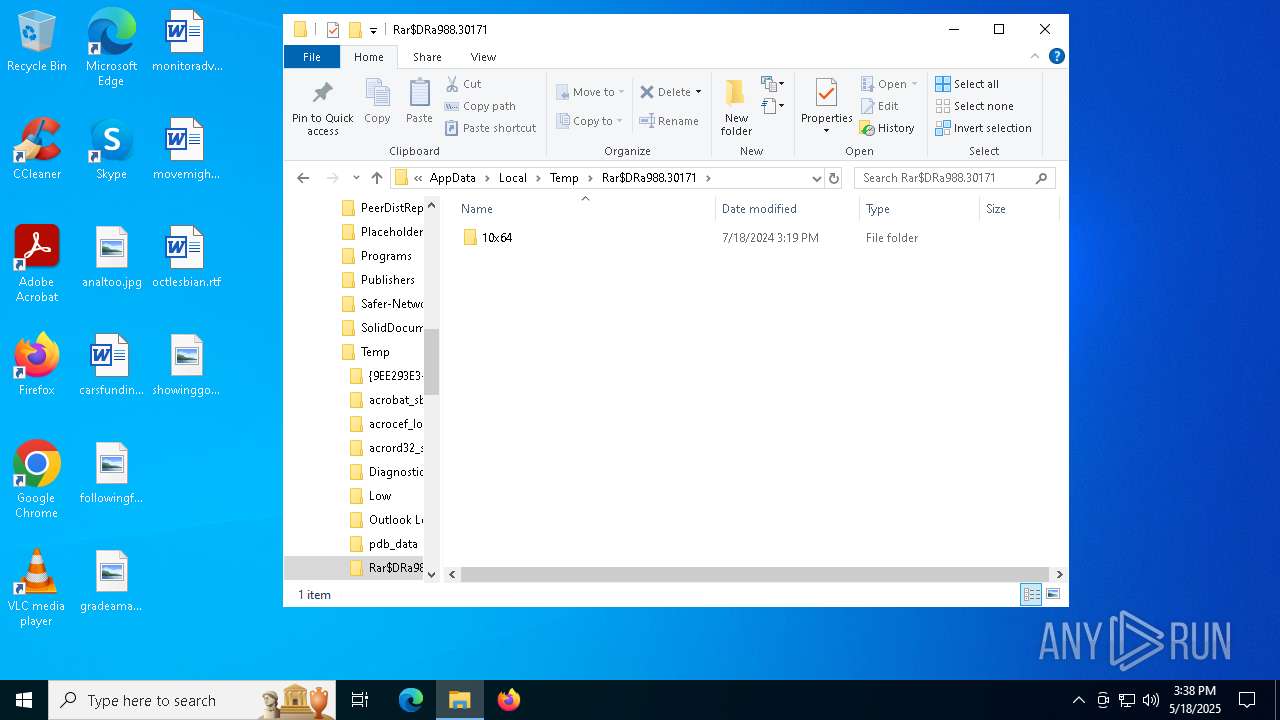
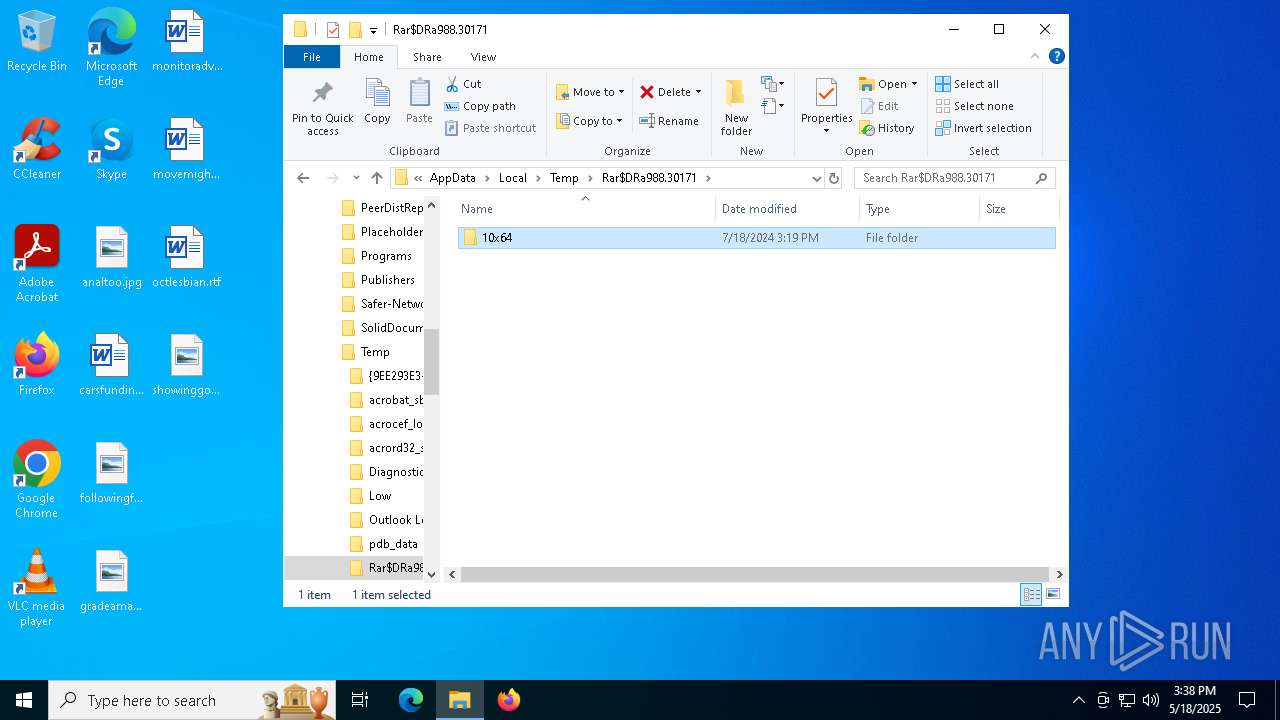
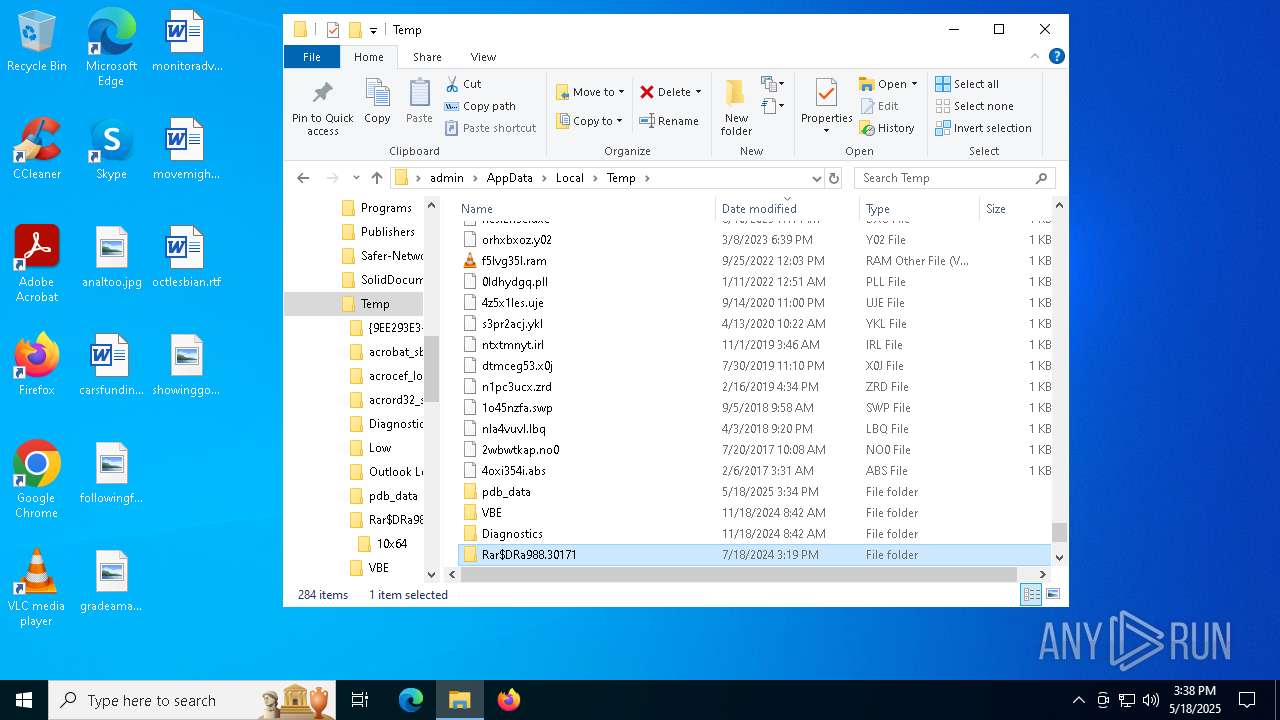
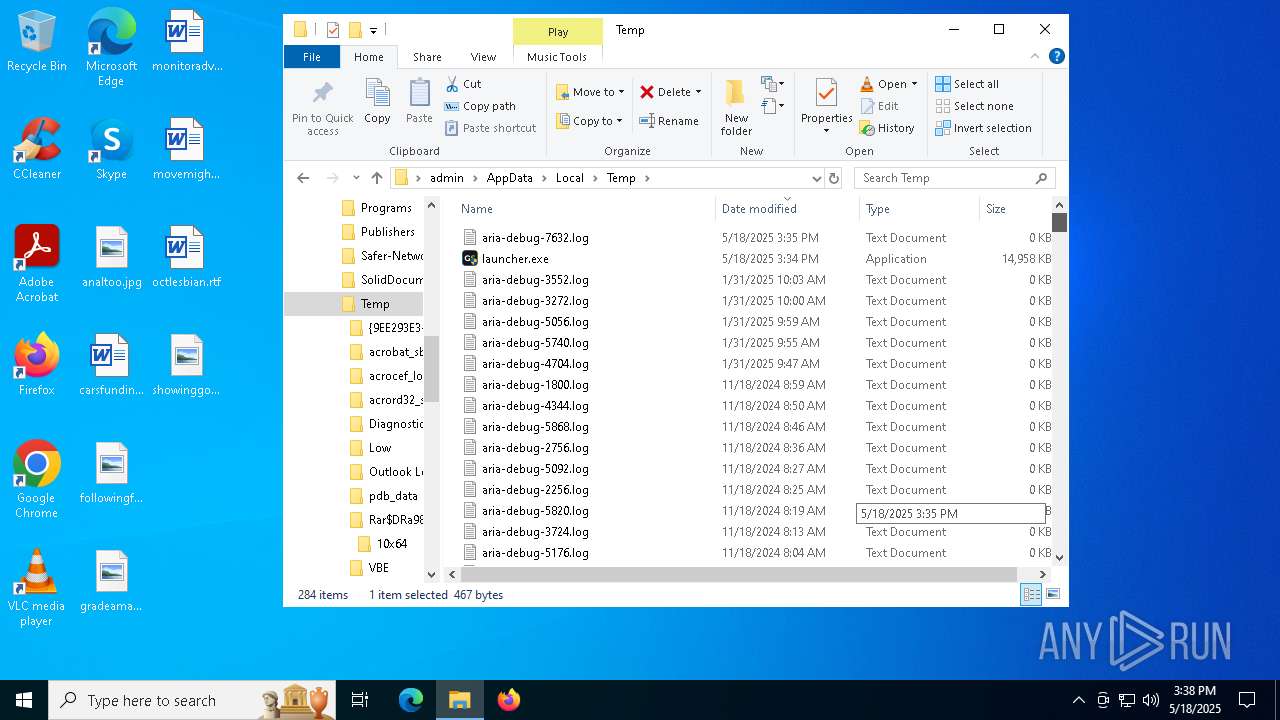
Creates files or folders in the user directory
- launcher.exe (PID: 7340)
Reads the software policy settings
- launcher.exe (PID: 7340)
- slui.exe (PID: 7904)
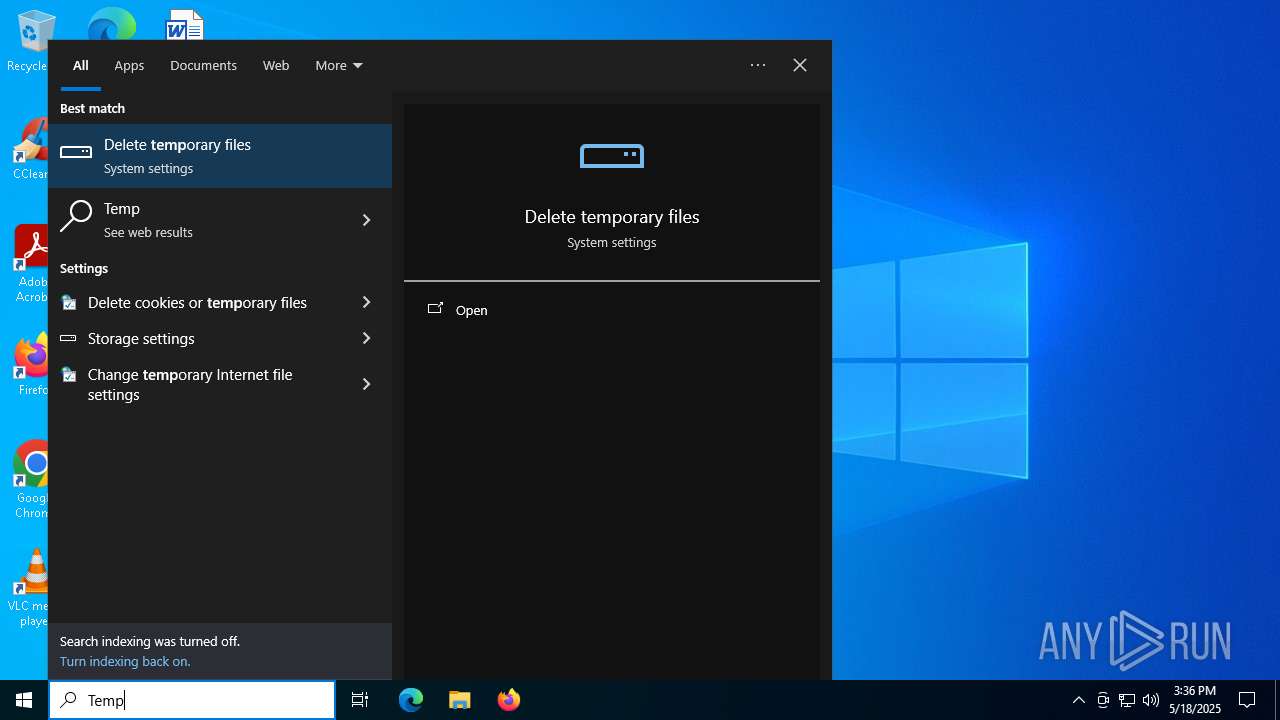
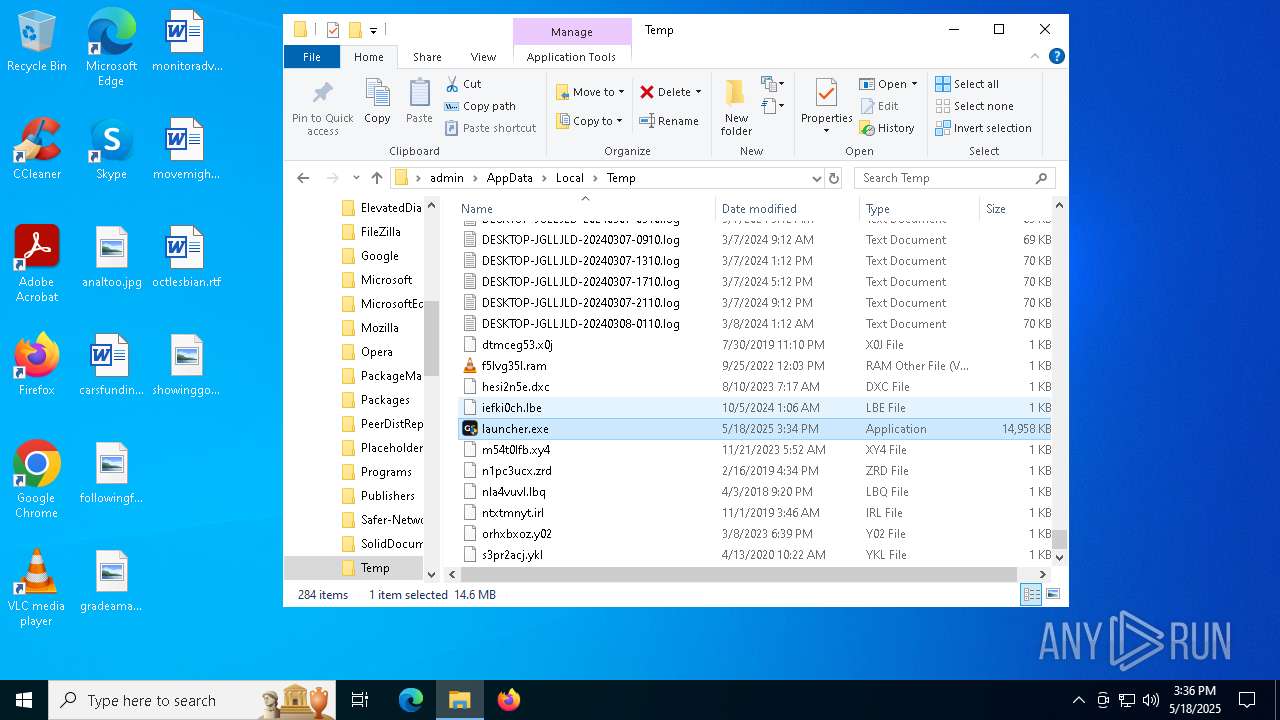
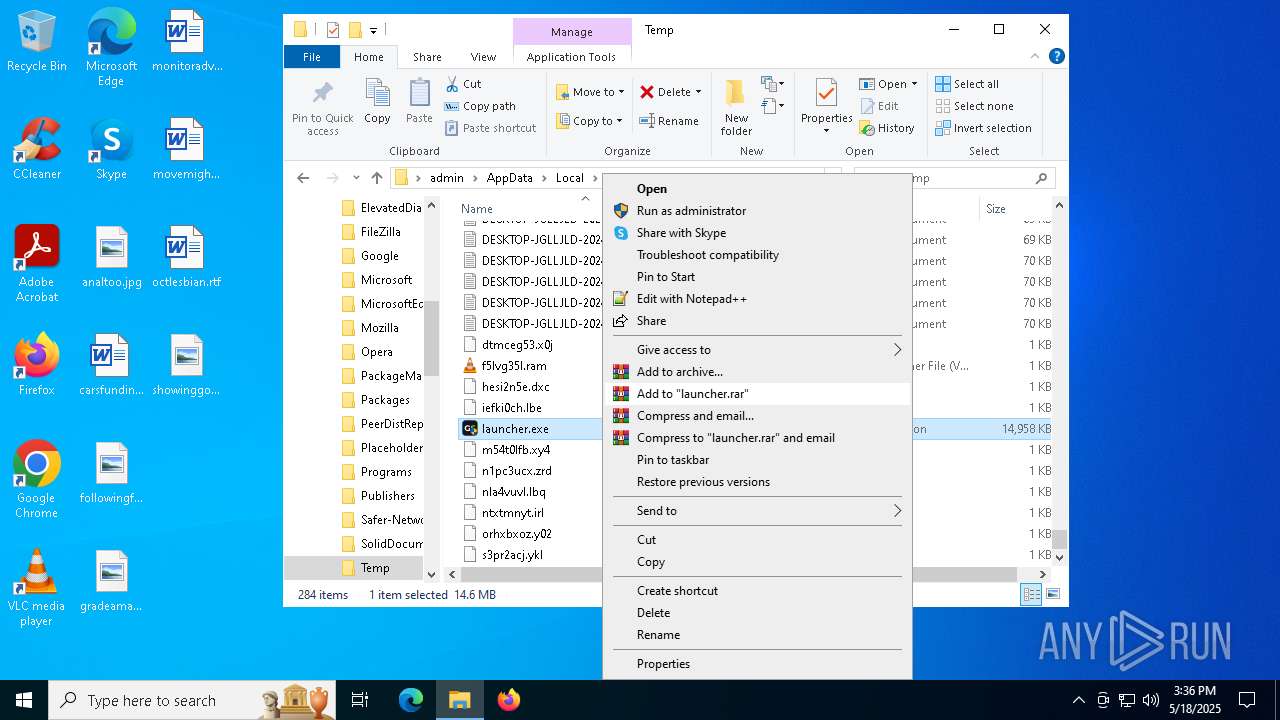
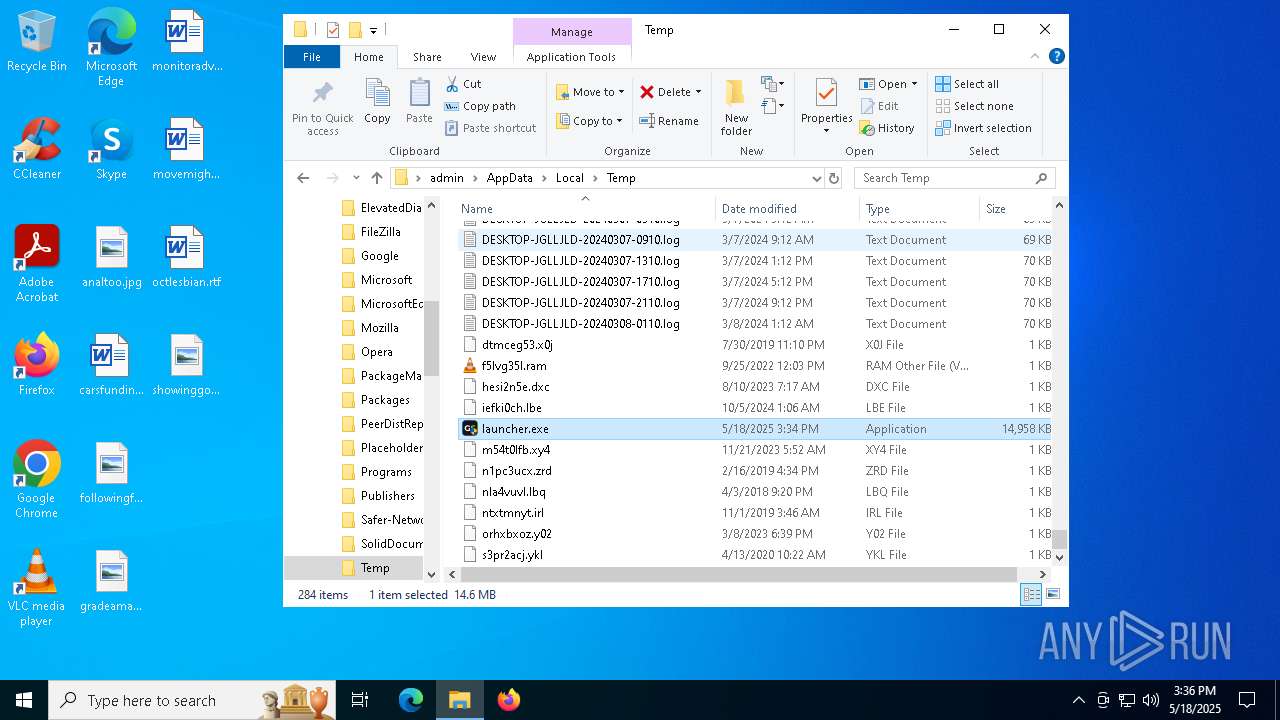
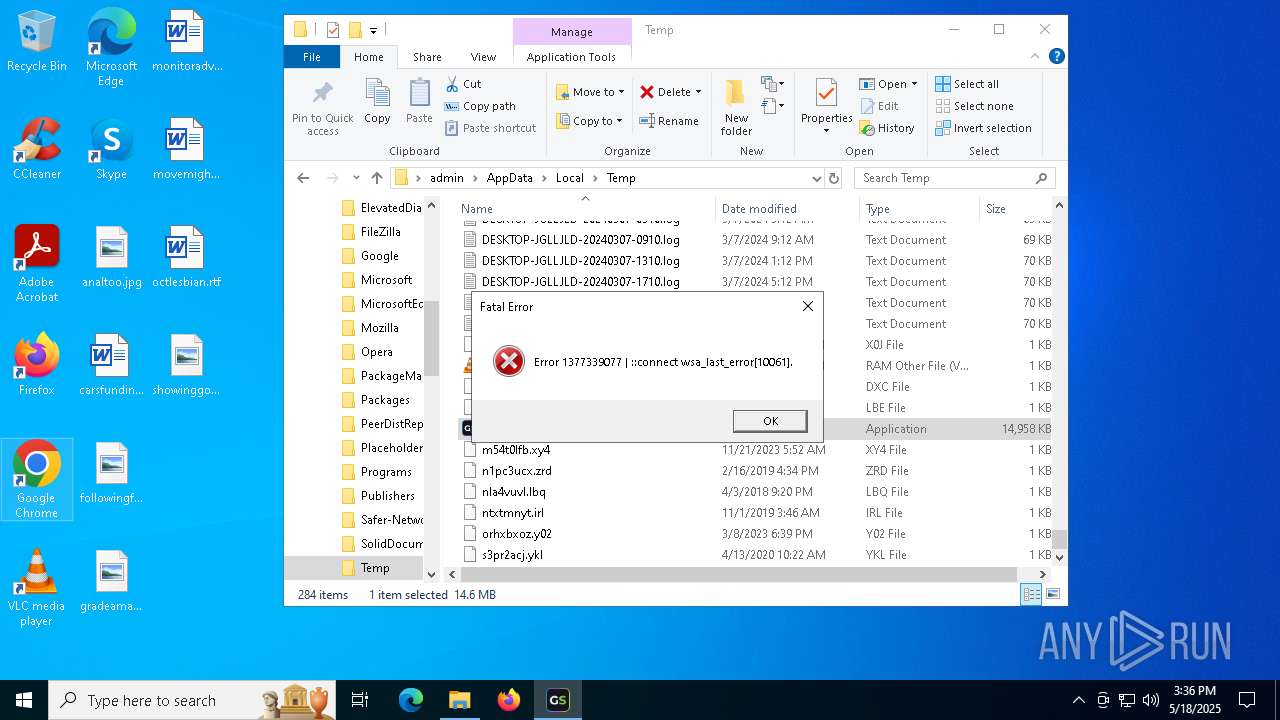
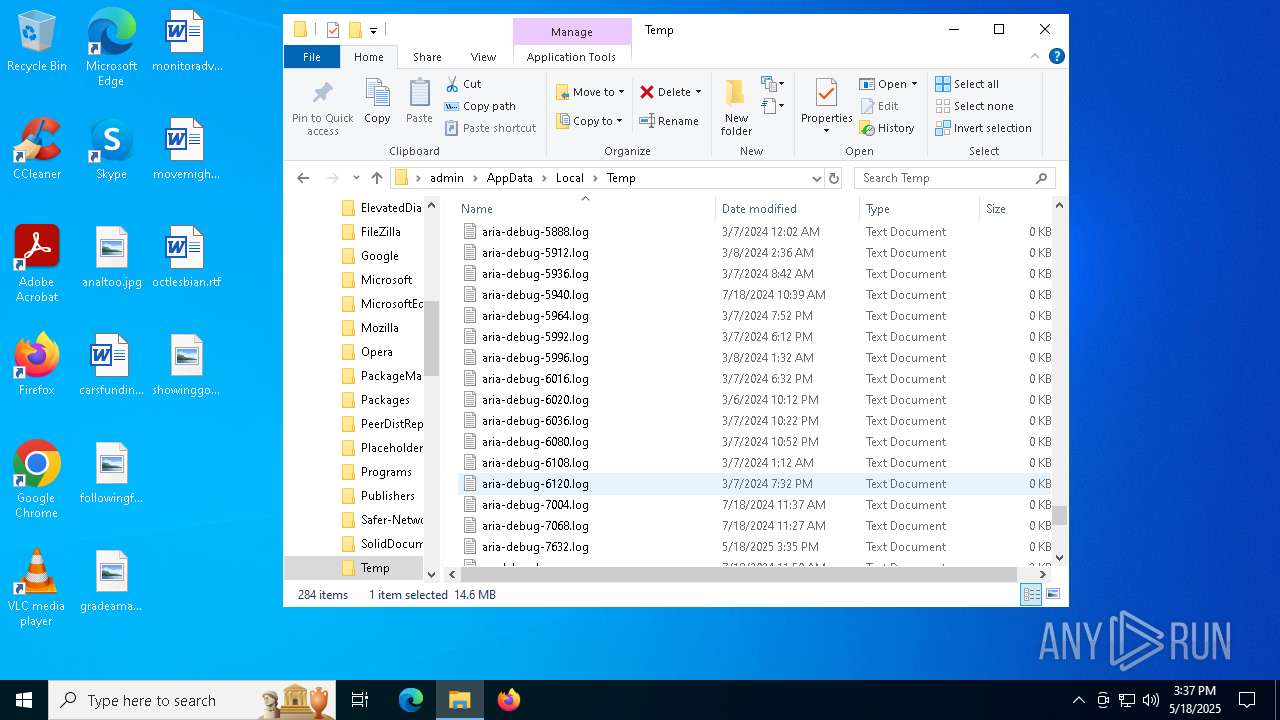
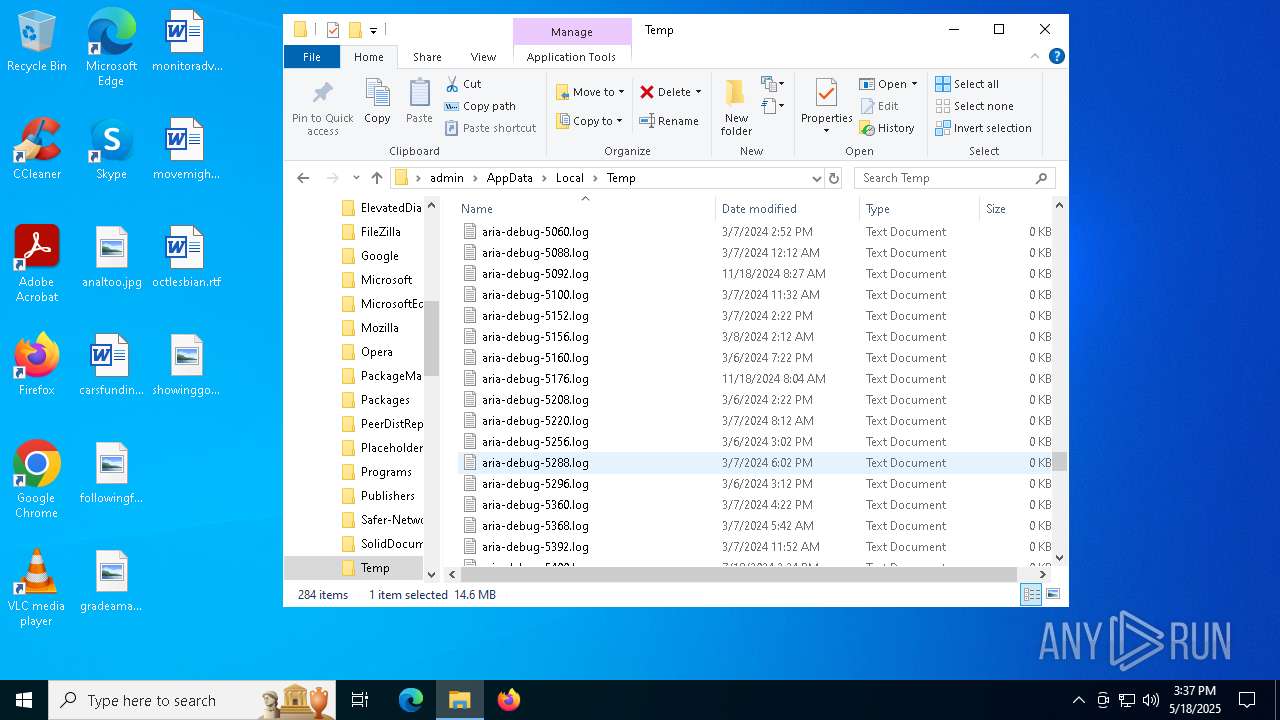
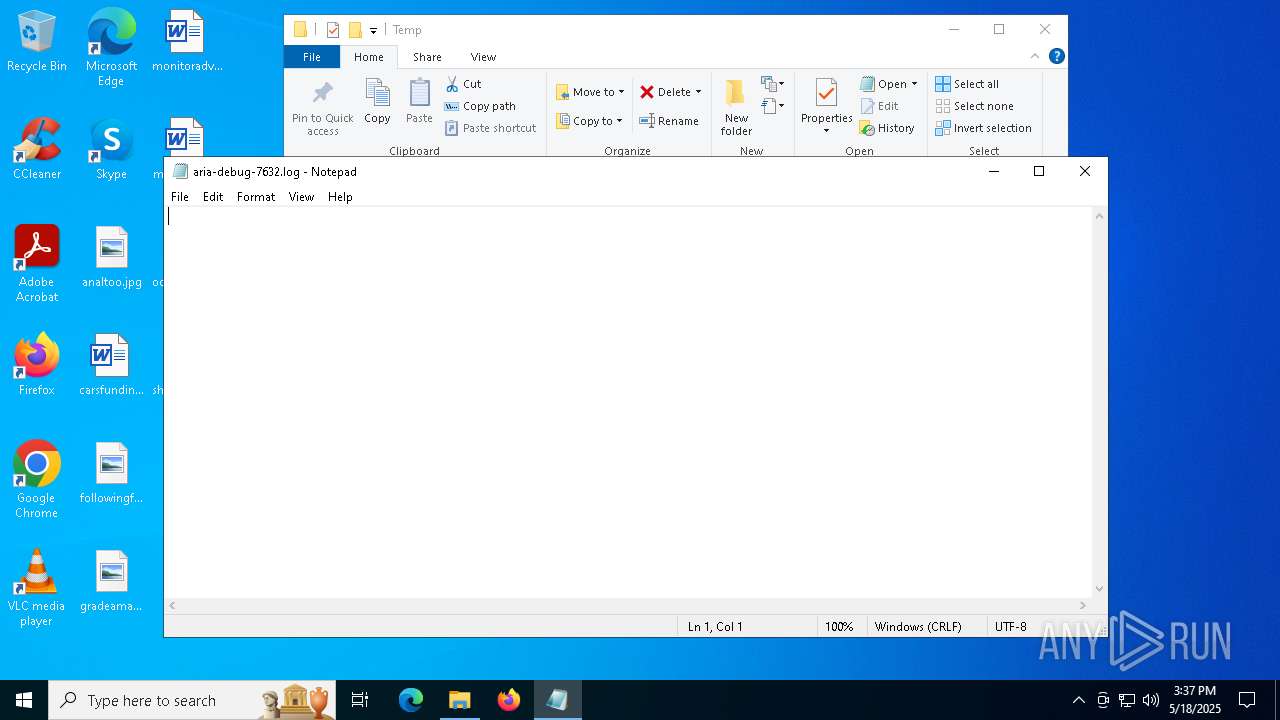
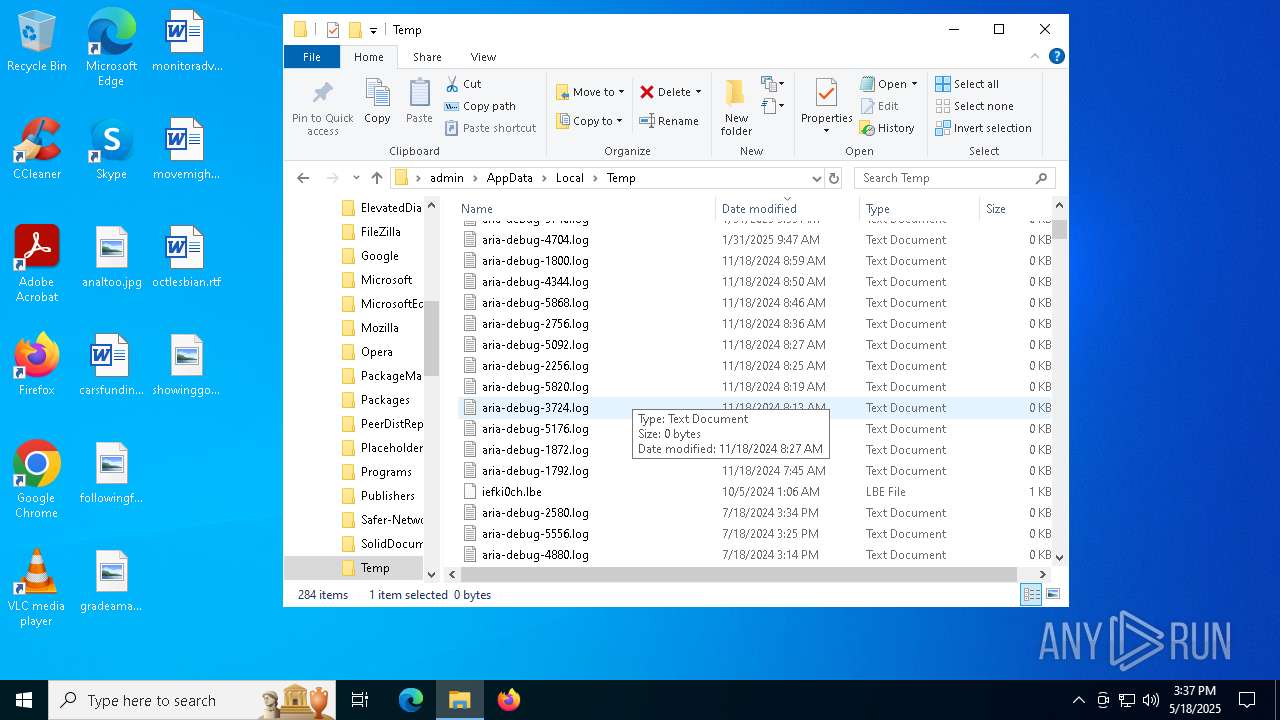
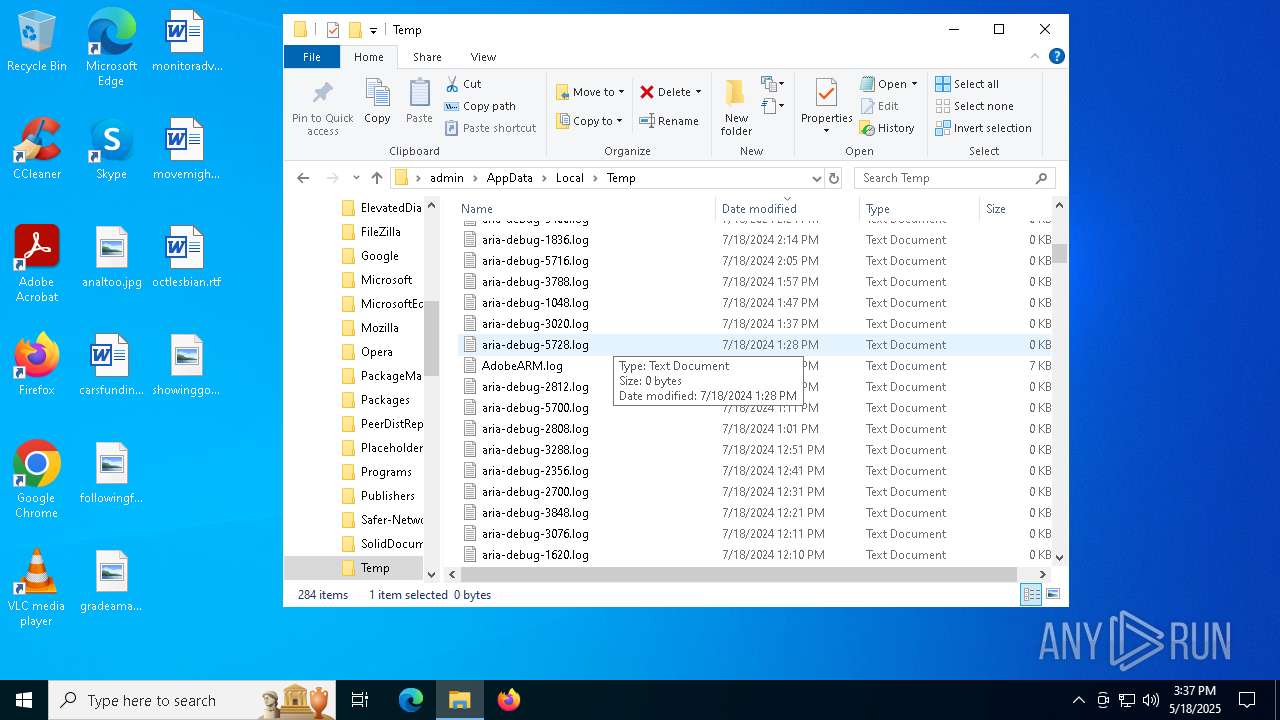
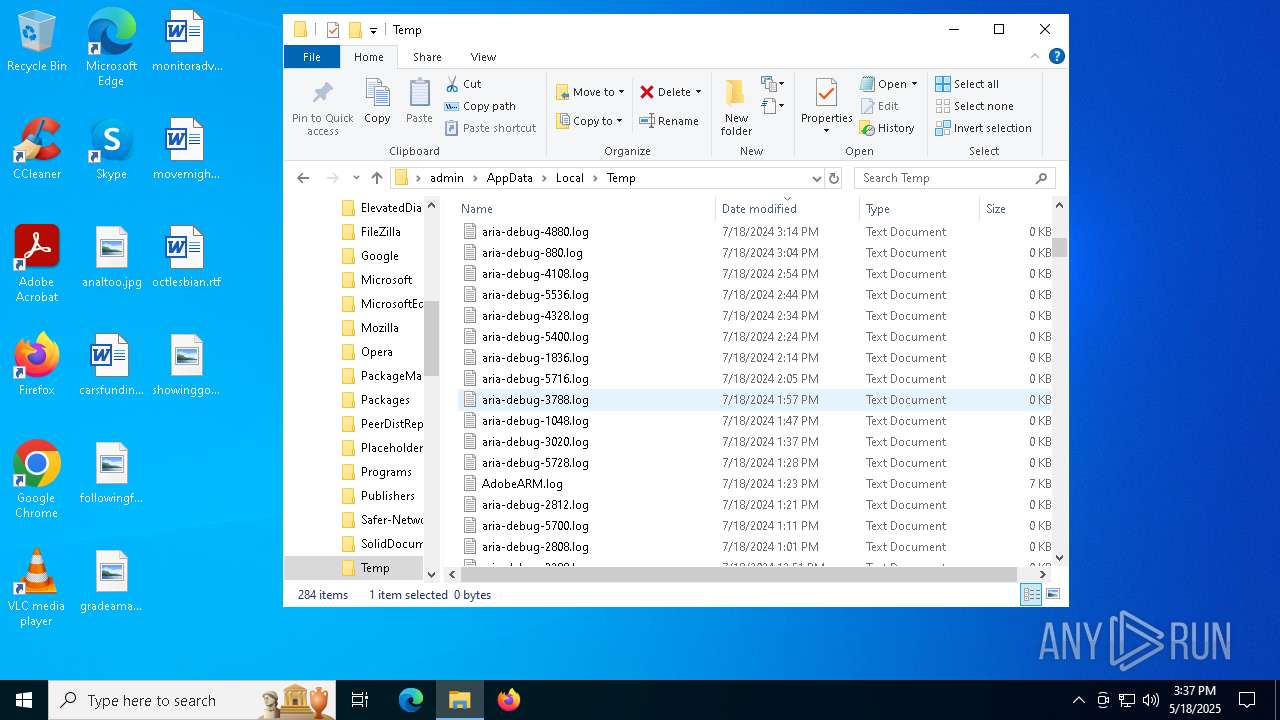
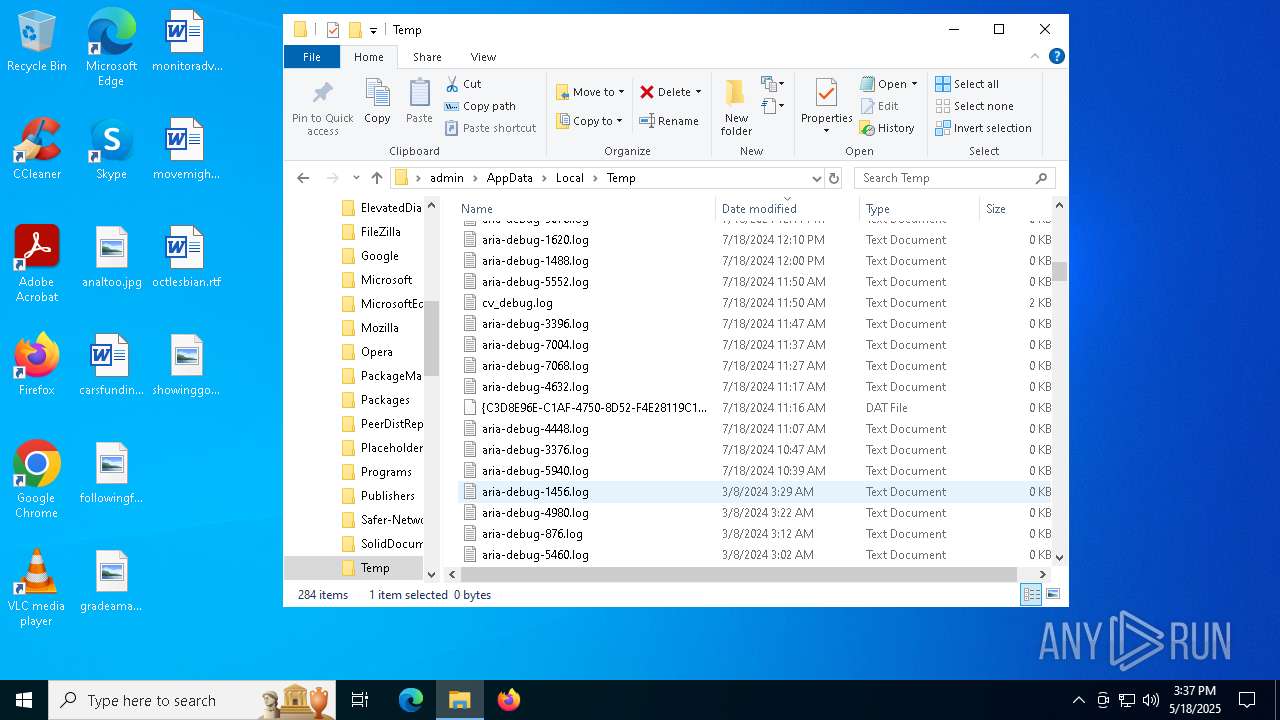
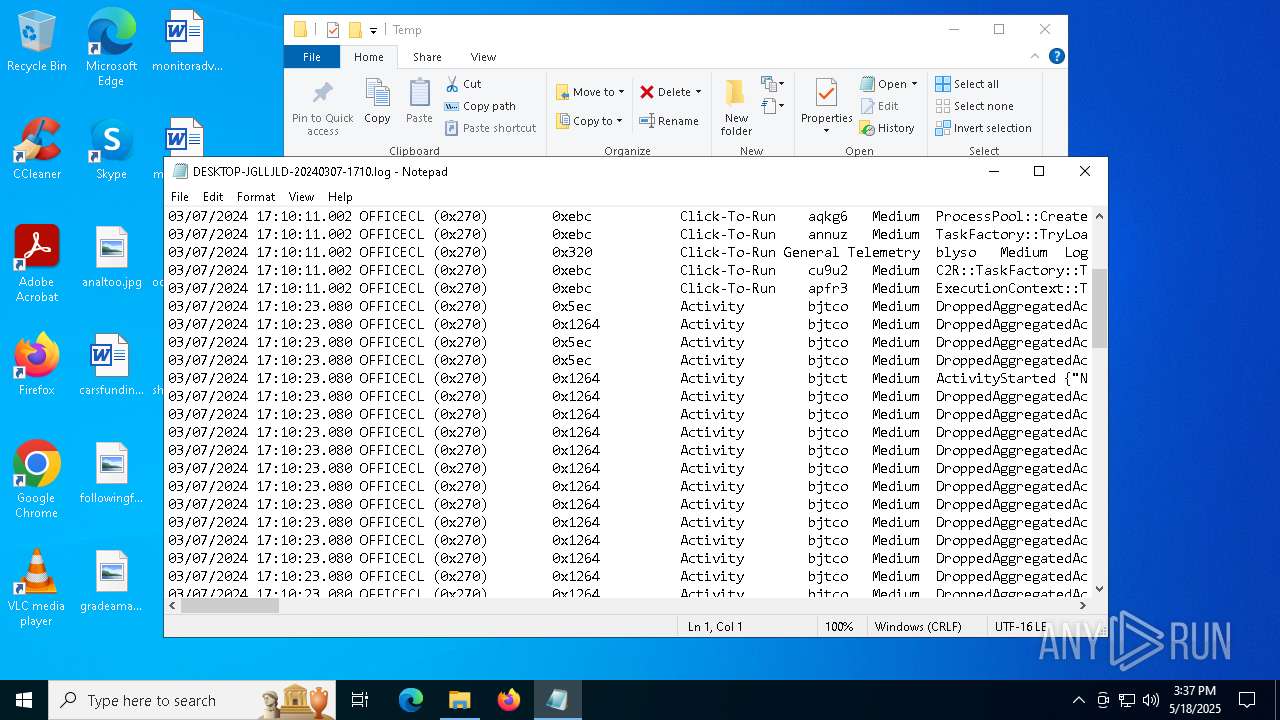
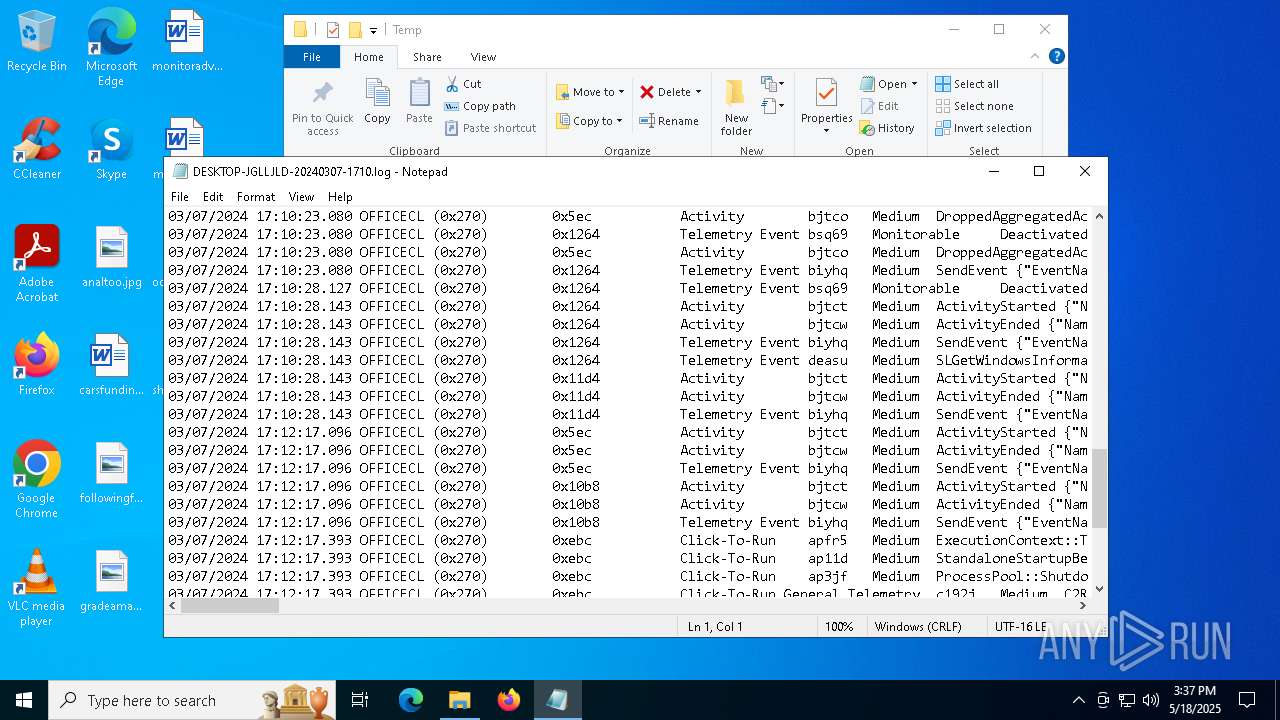
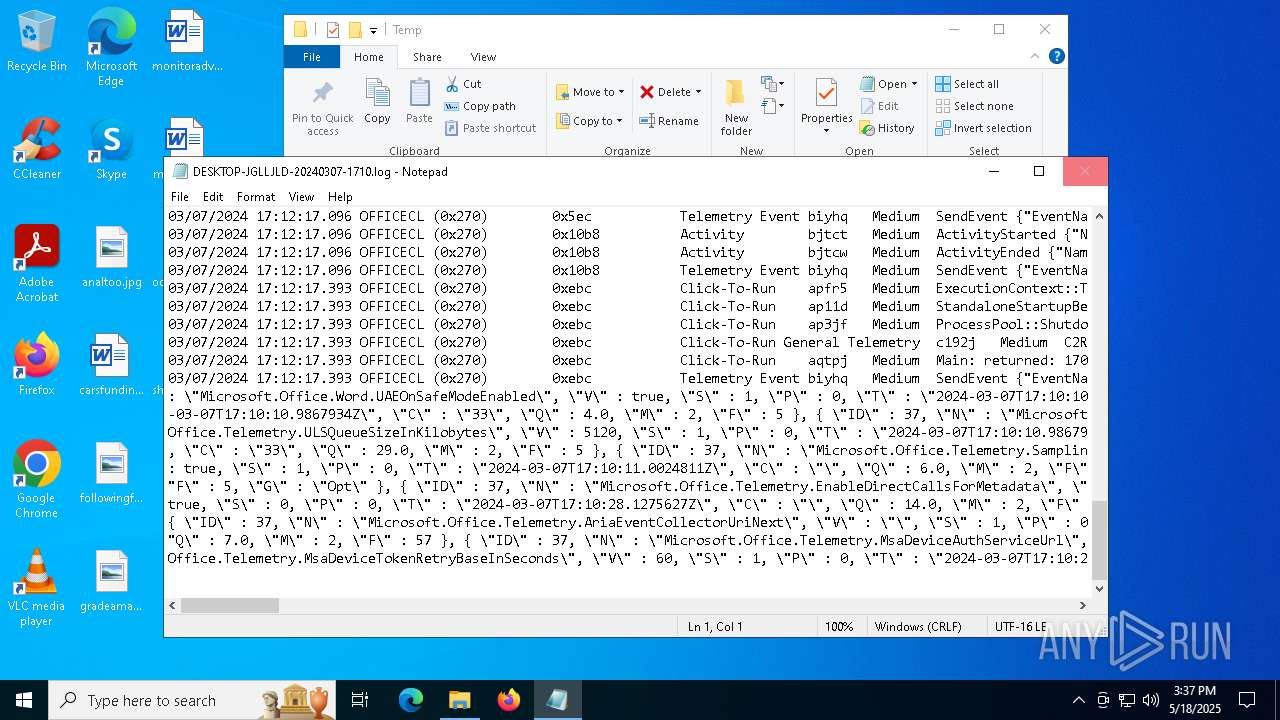
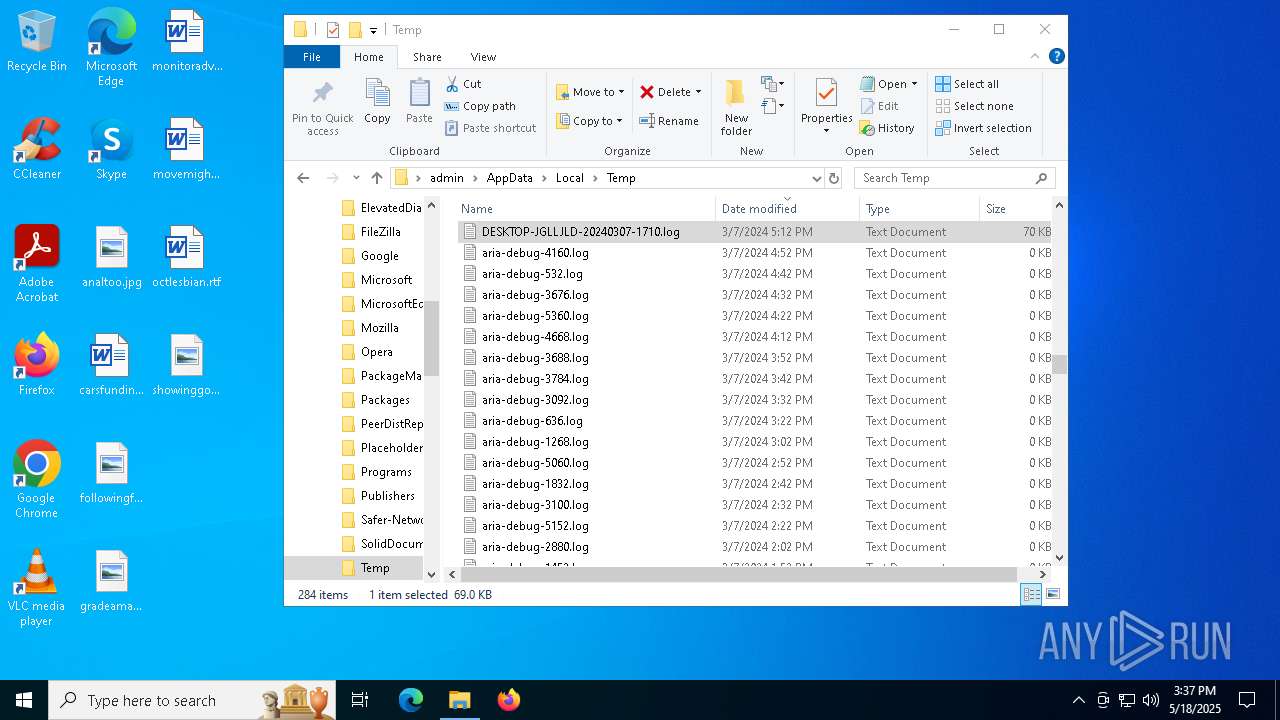
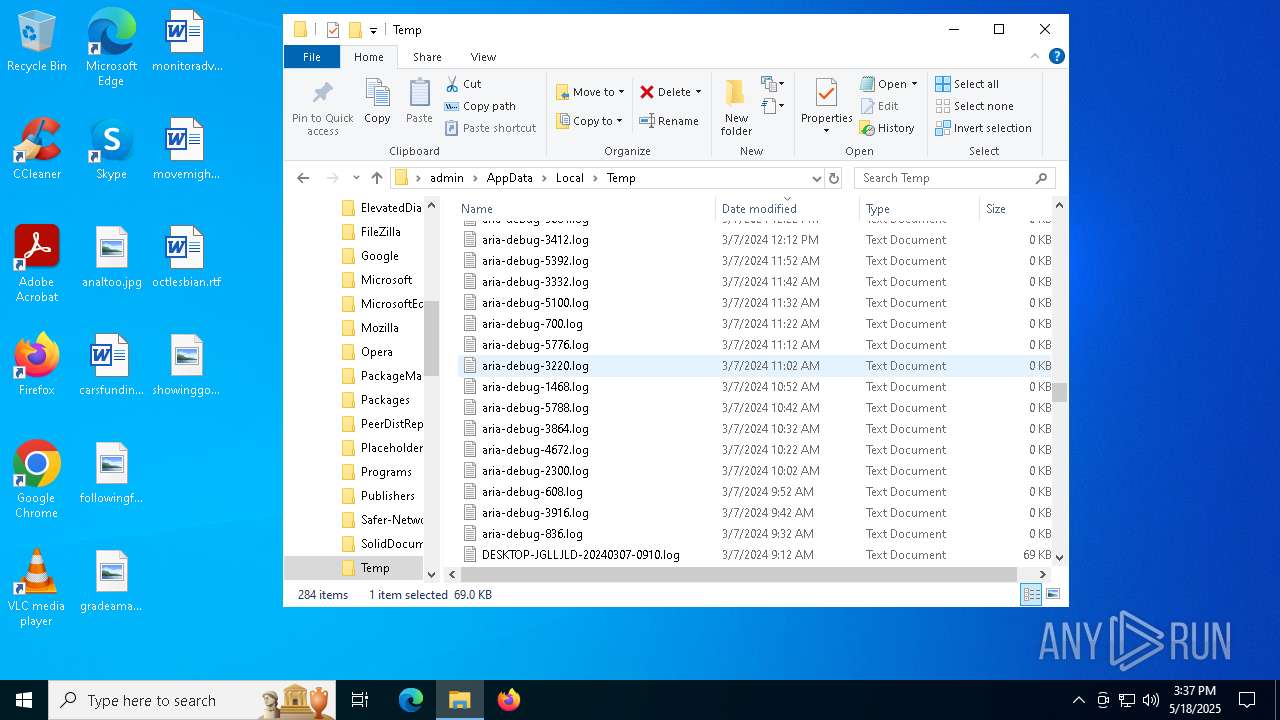
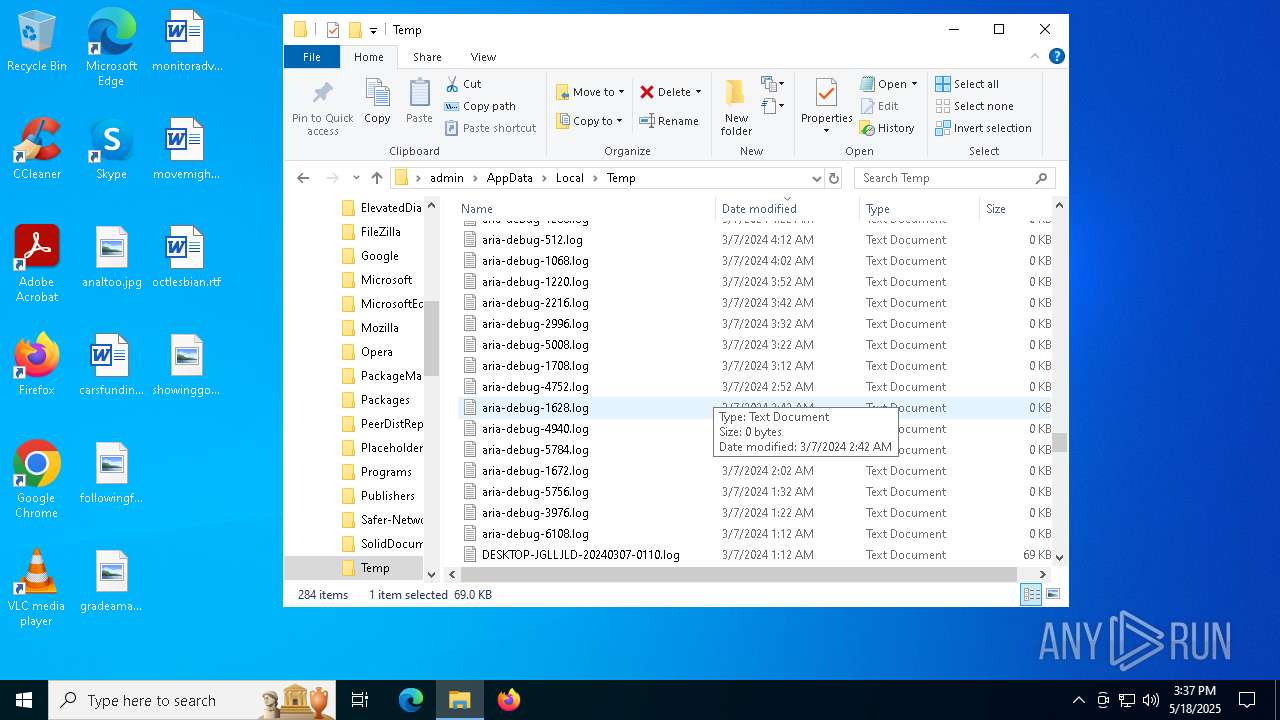
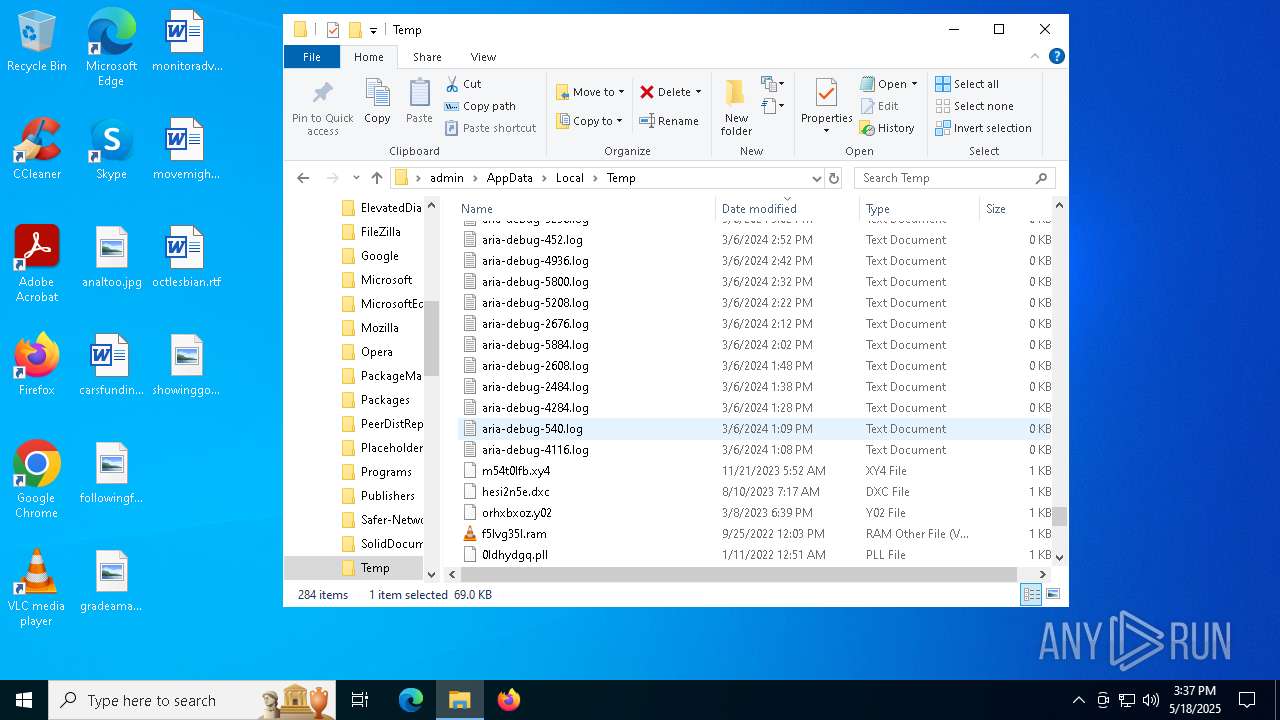
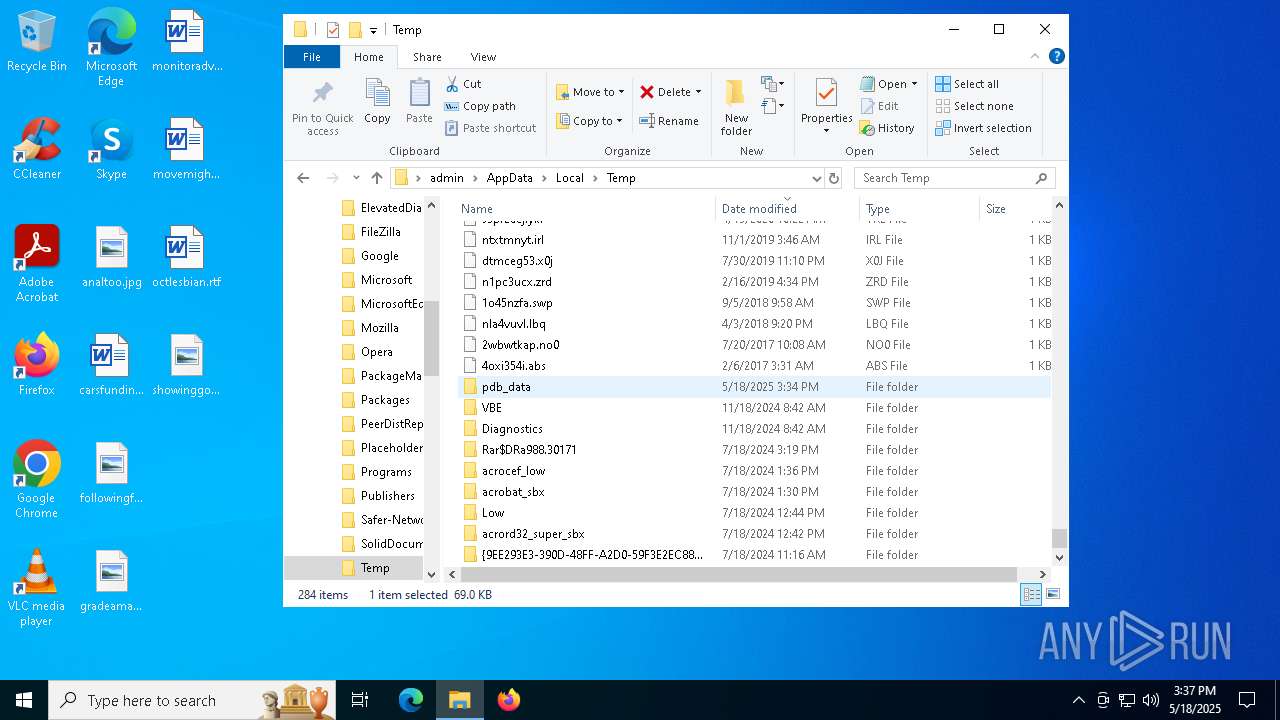
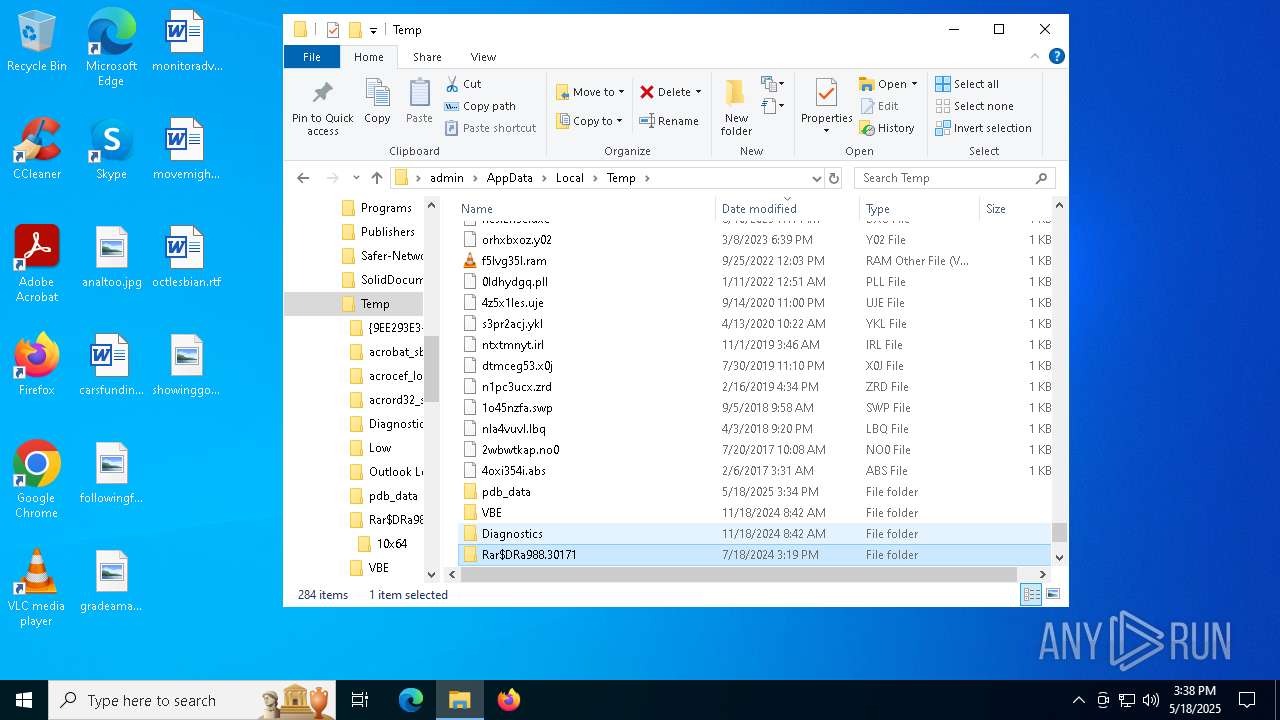
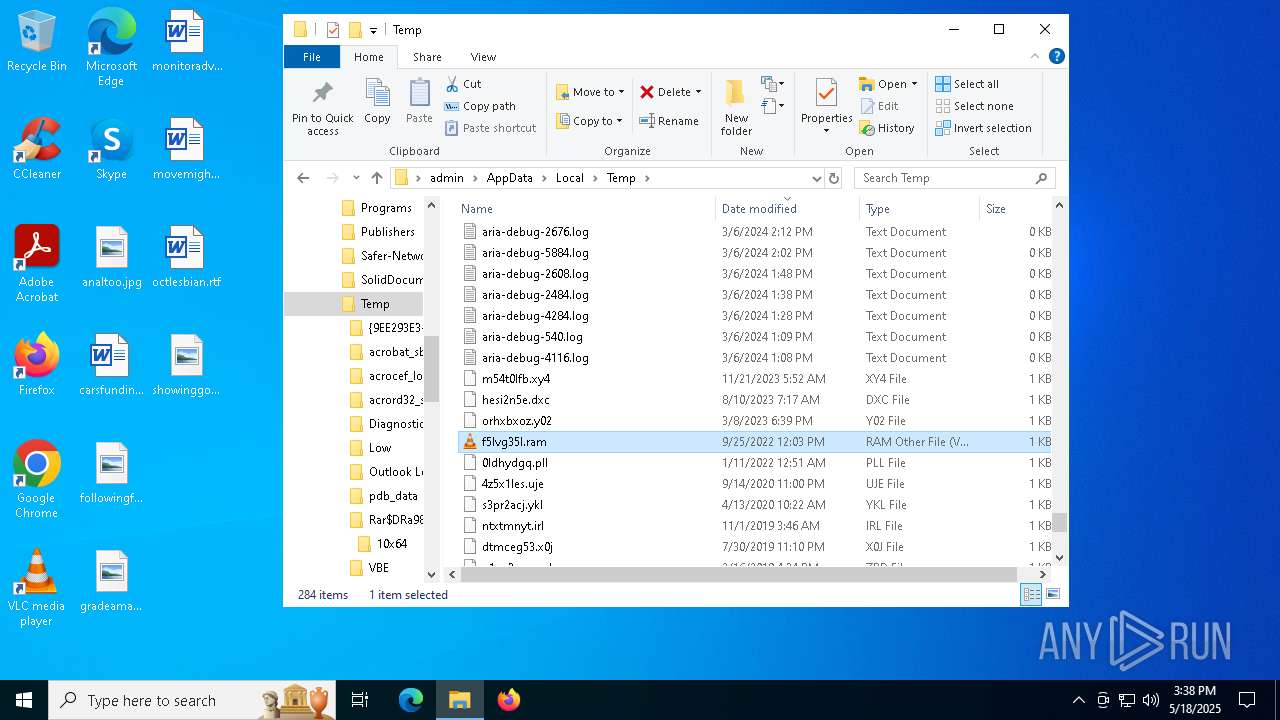
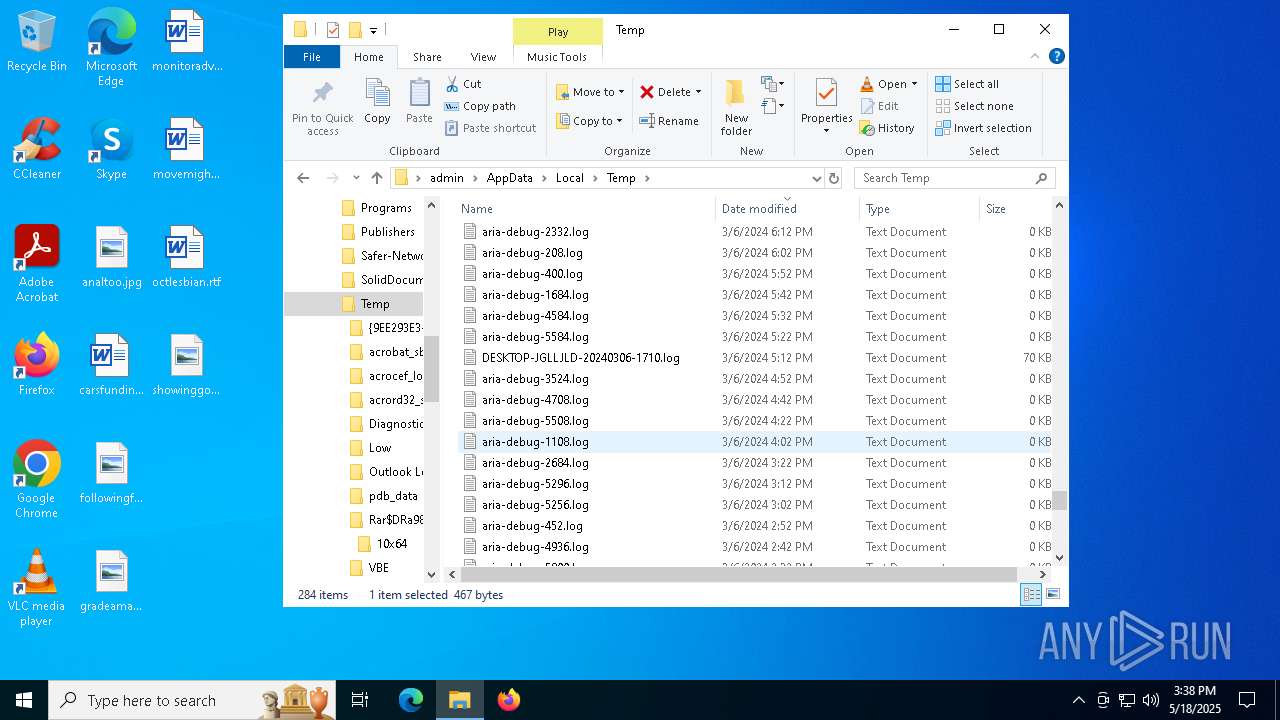
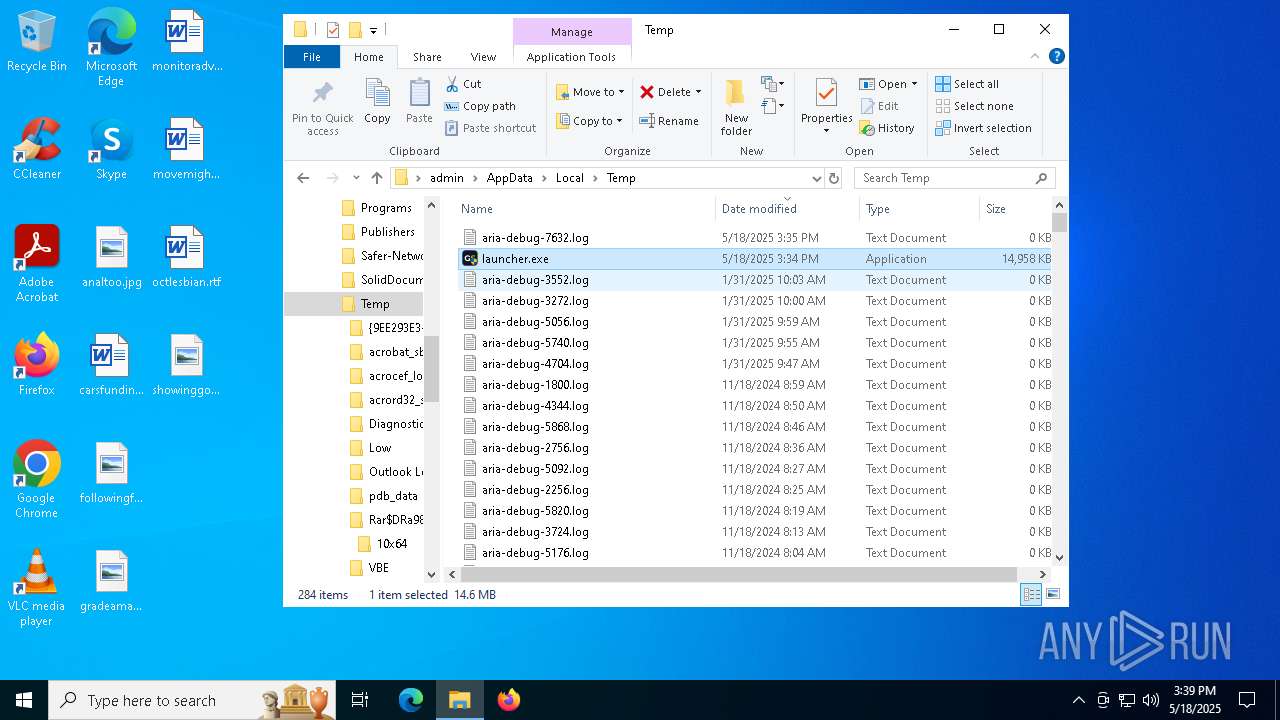
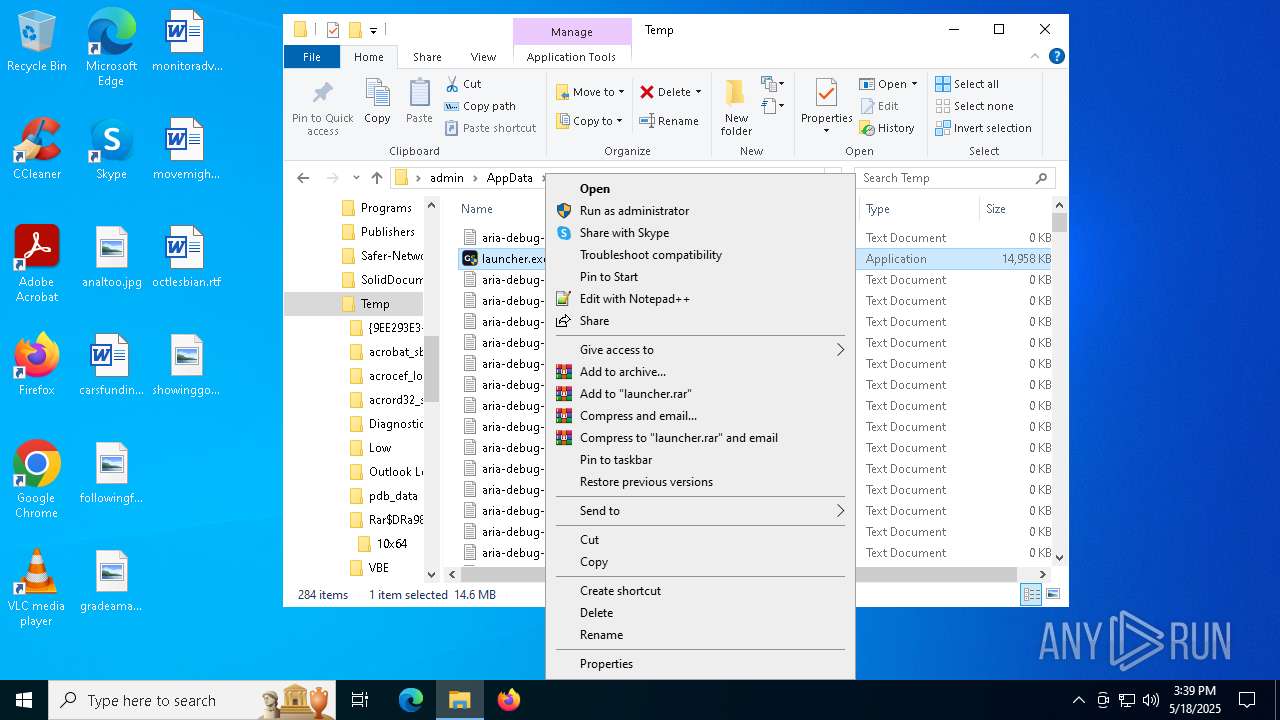
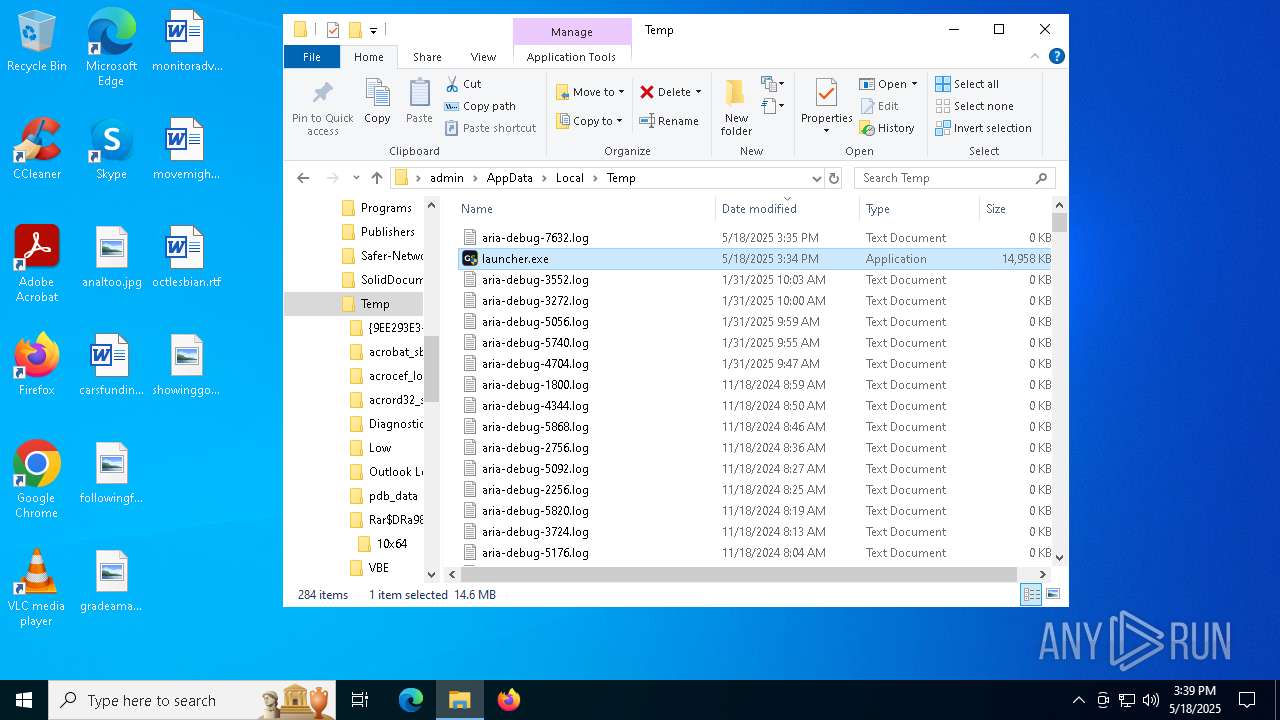
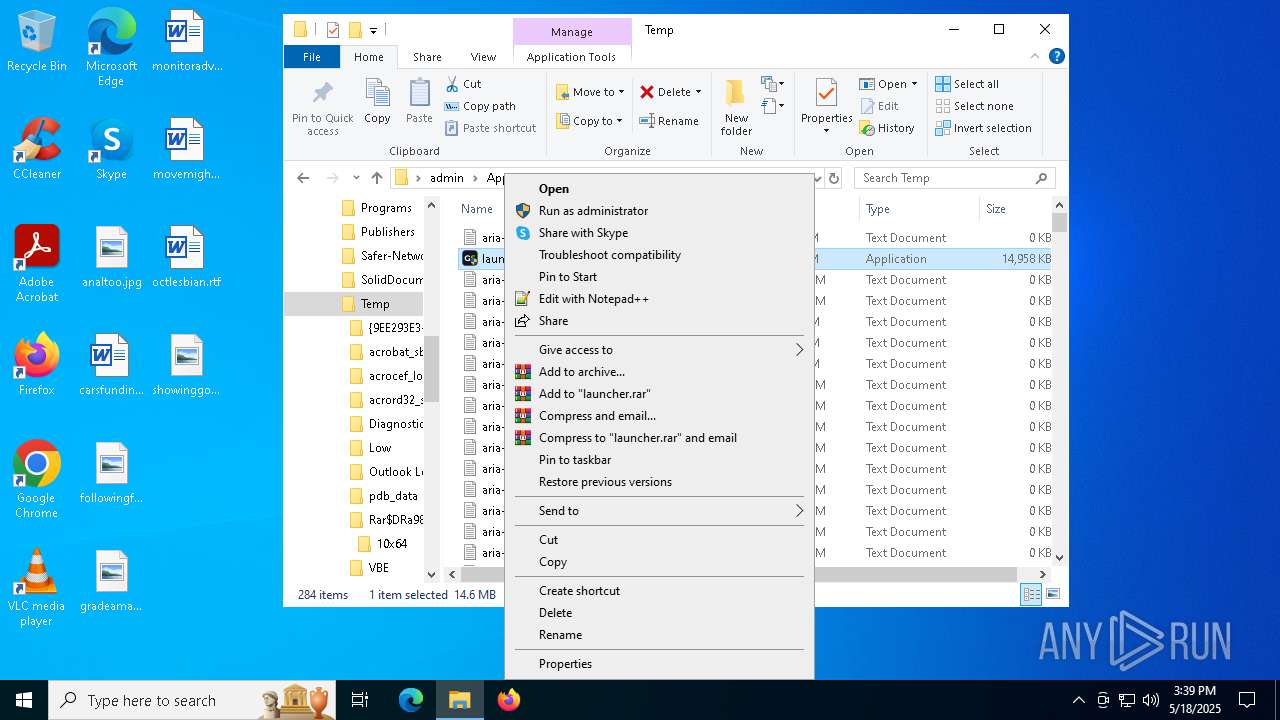
Create files in a temporary directory
- launcher.exe (PID: 7340)
Reads the machine GUID from the registry
- launcher.exe (PID: 7340)
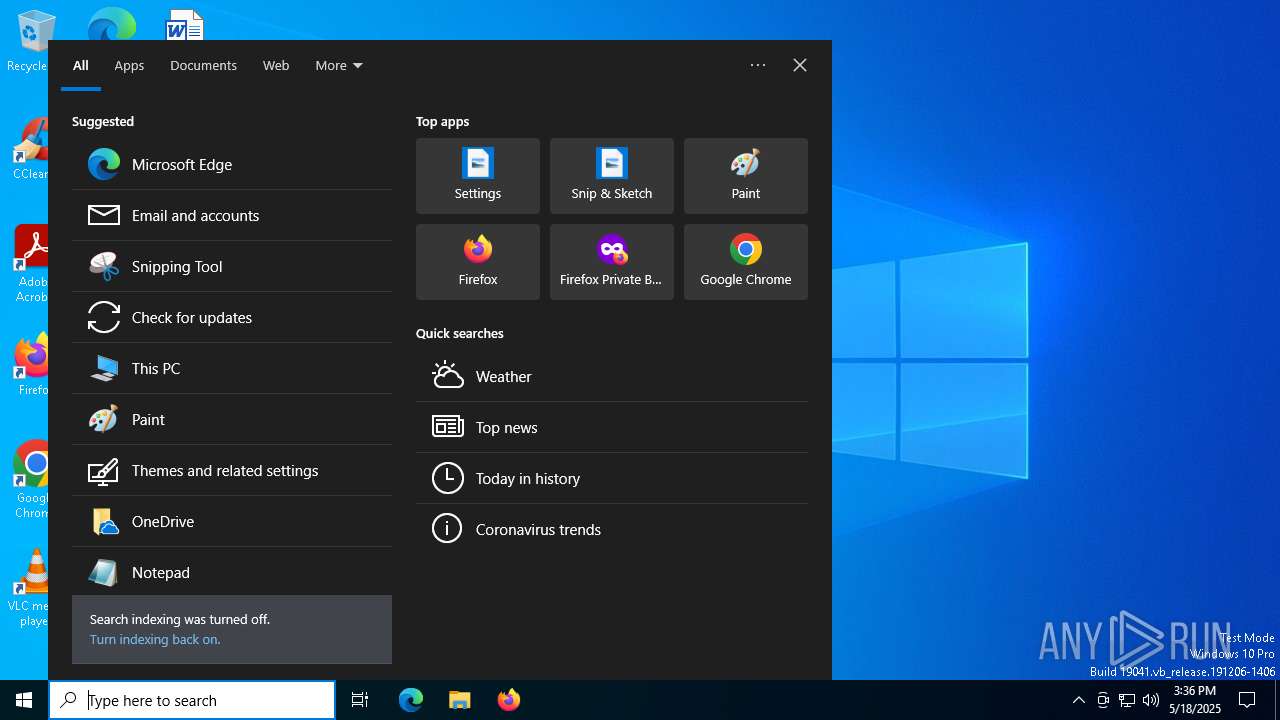
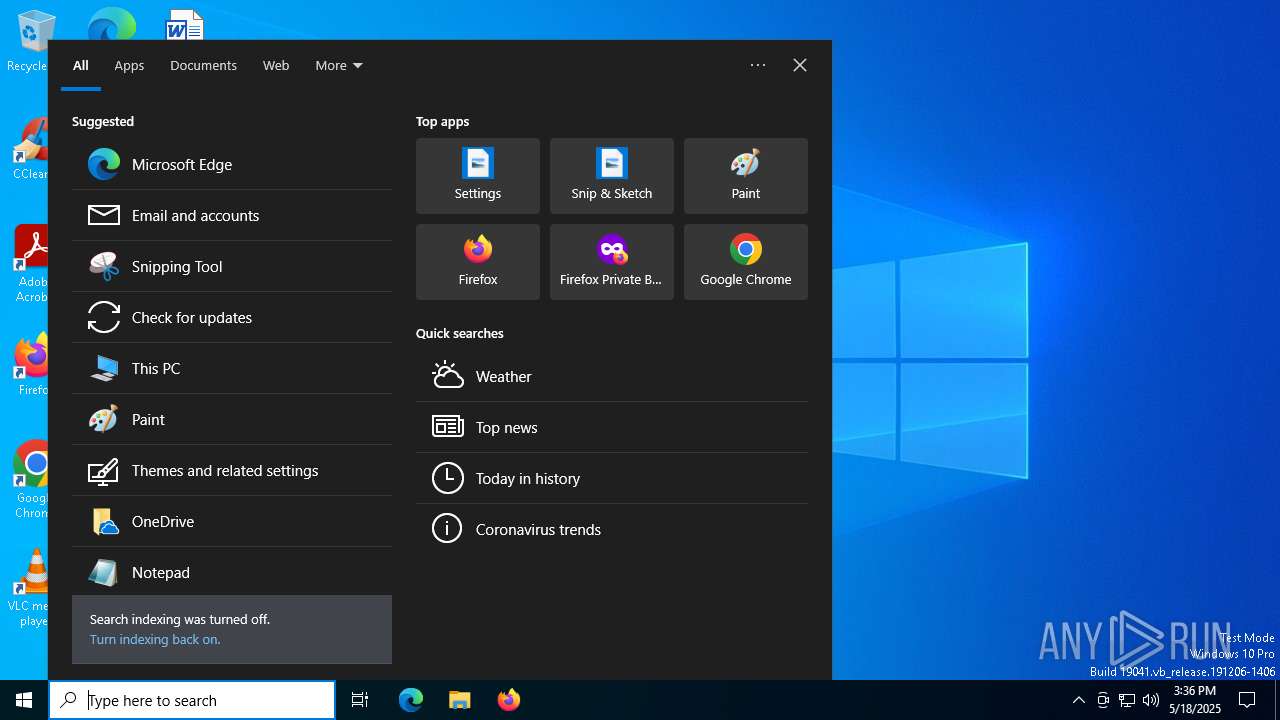
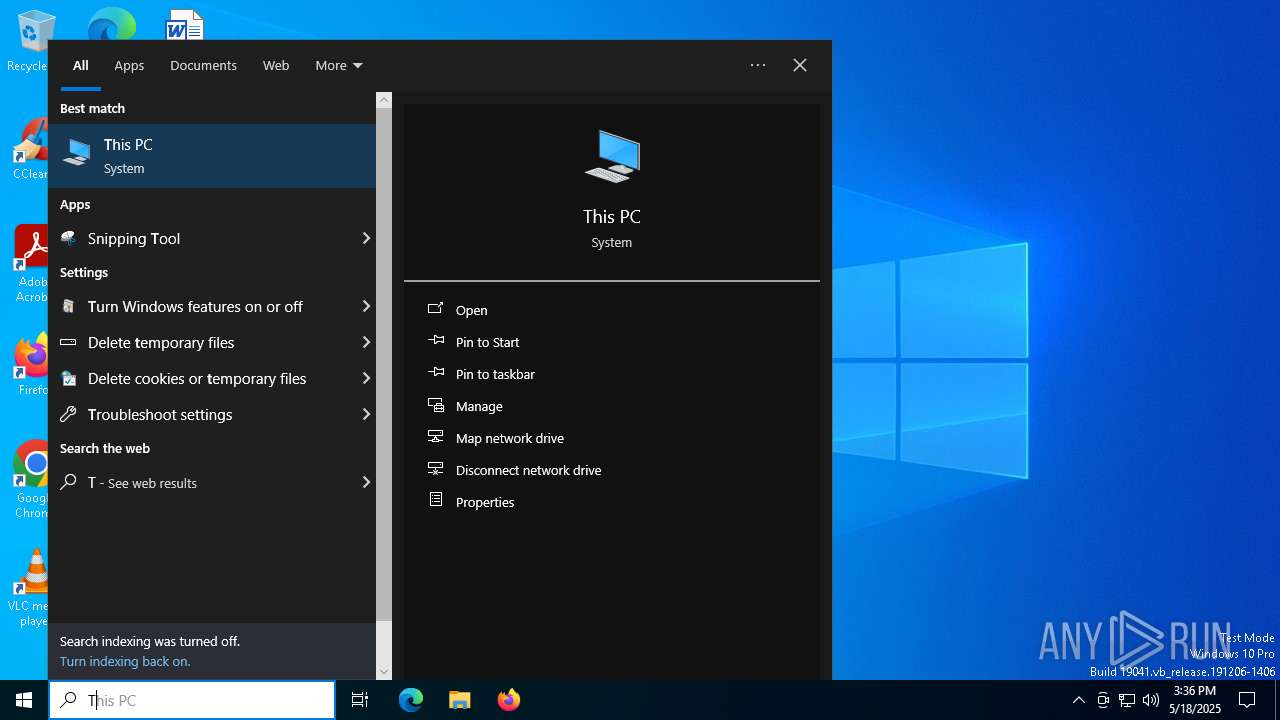
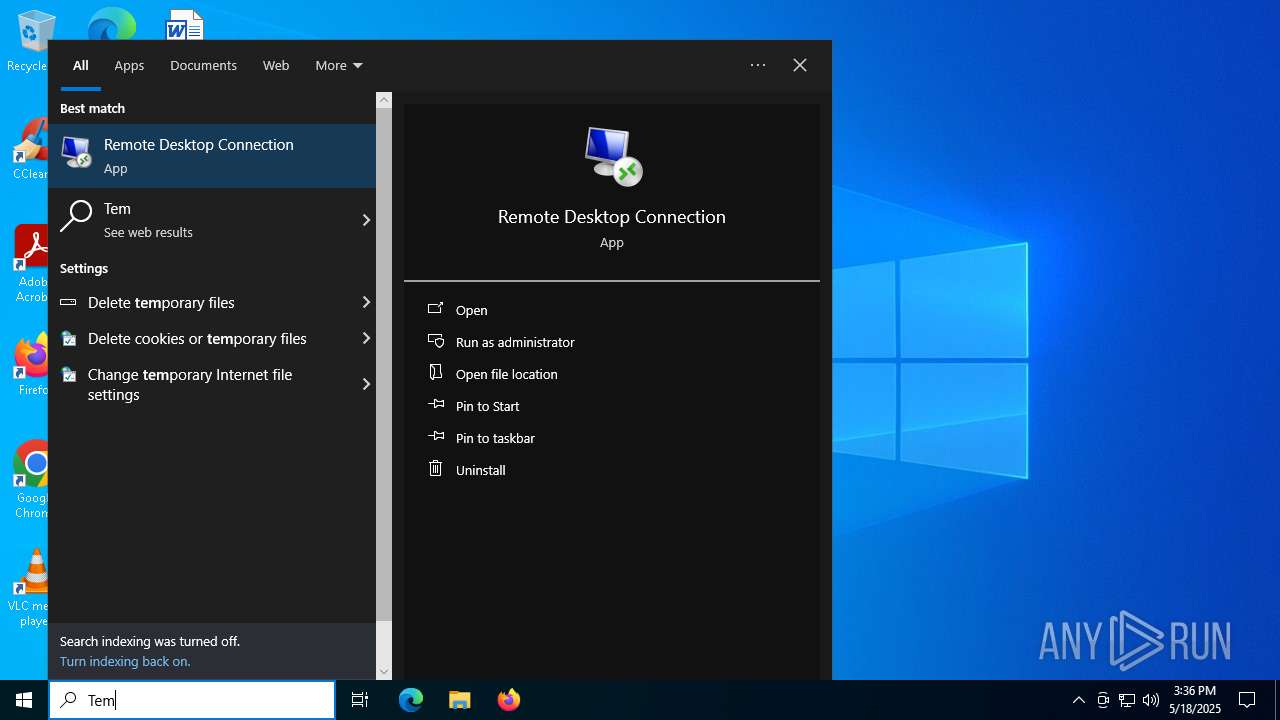
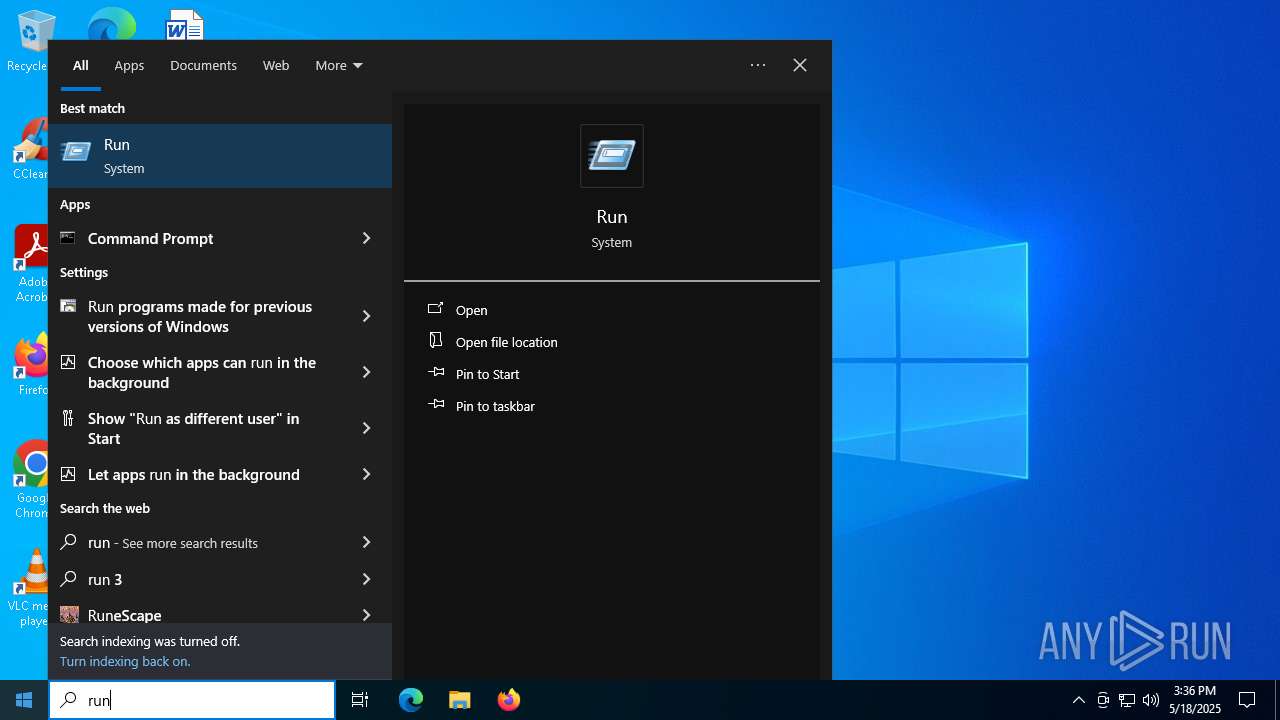
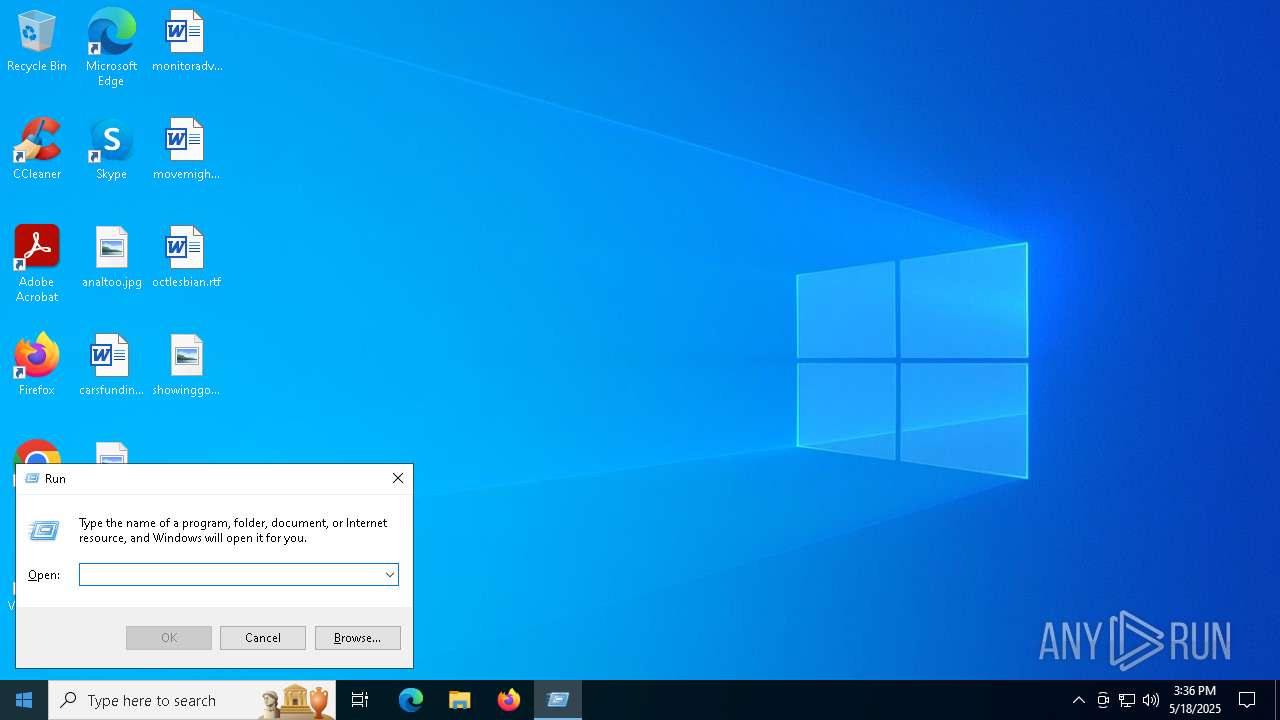
Manual execution by a user
- launcher.exe (PID: 6644)
- launcher.exe (PID: 1672)
- launcher.exe (PID: 6564)
- notepad.exe (PID: 7456)
- notepad.exe (PID: 7472)
- launcher.exe (PID: 2516)
- launcher.exe (PID: 968)
- launcher.exe (PID: 1116)
- launcher.exe (PID: 7388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2021:06:23 16:29:02+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 13420544 |
| InitializedDataSize: | 1894912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc9edc0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
146
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1116 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5380 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6564 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6644 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7244 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7340 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7388 | "C:\Users\admin\AppData\Local\Temp\launcher.exe" | C:\Users\admin\AppData\Local\Temp\launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 064
Read events
2 061
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7340) launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7340) launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7340) launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
0
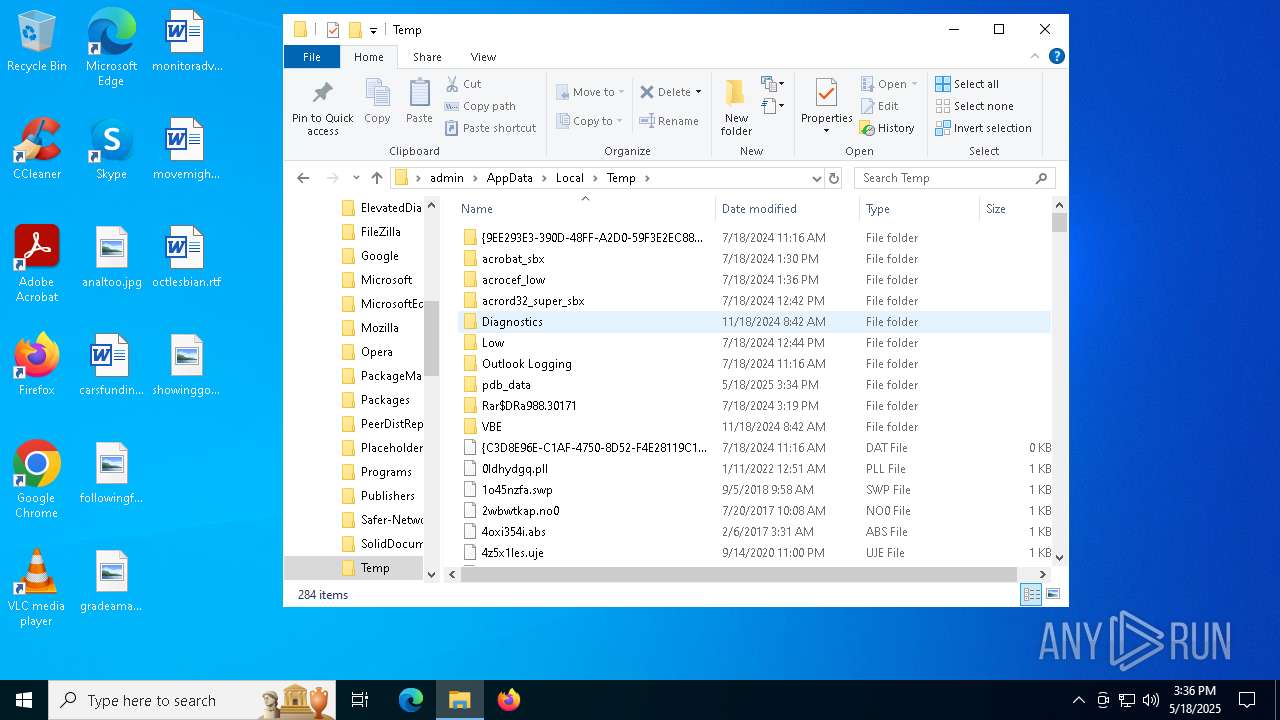
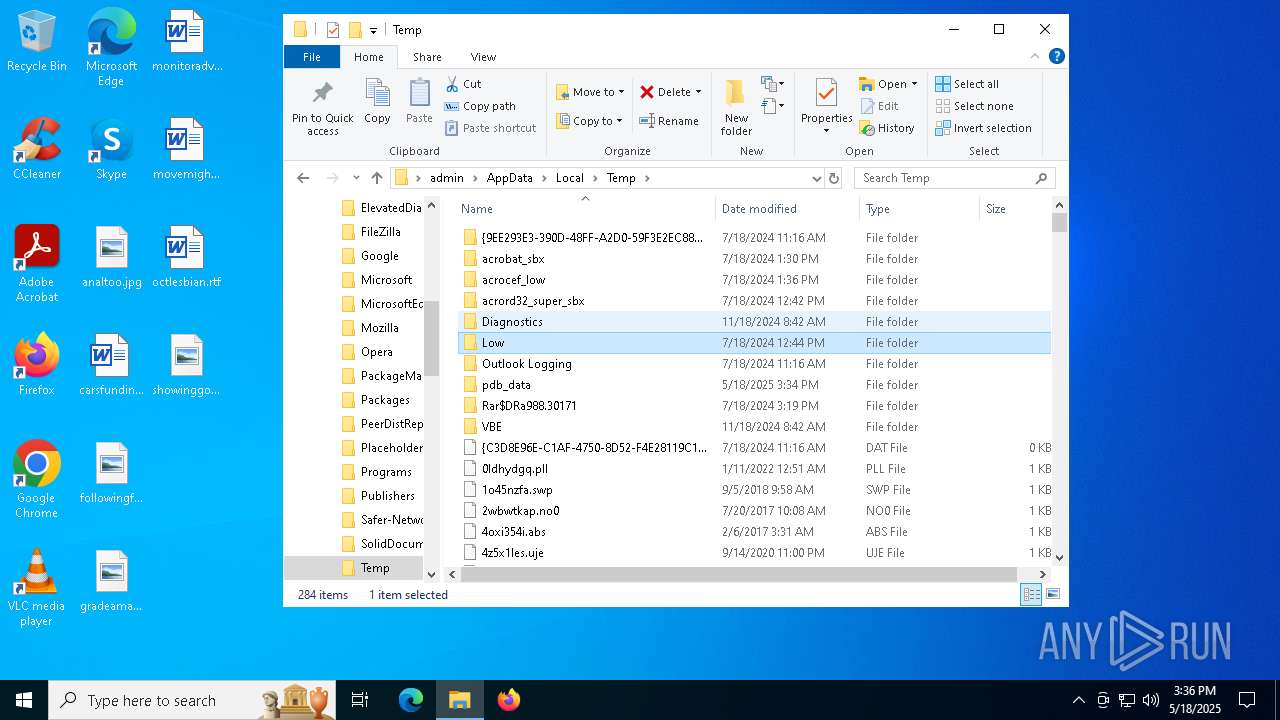
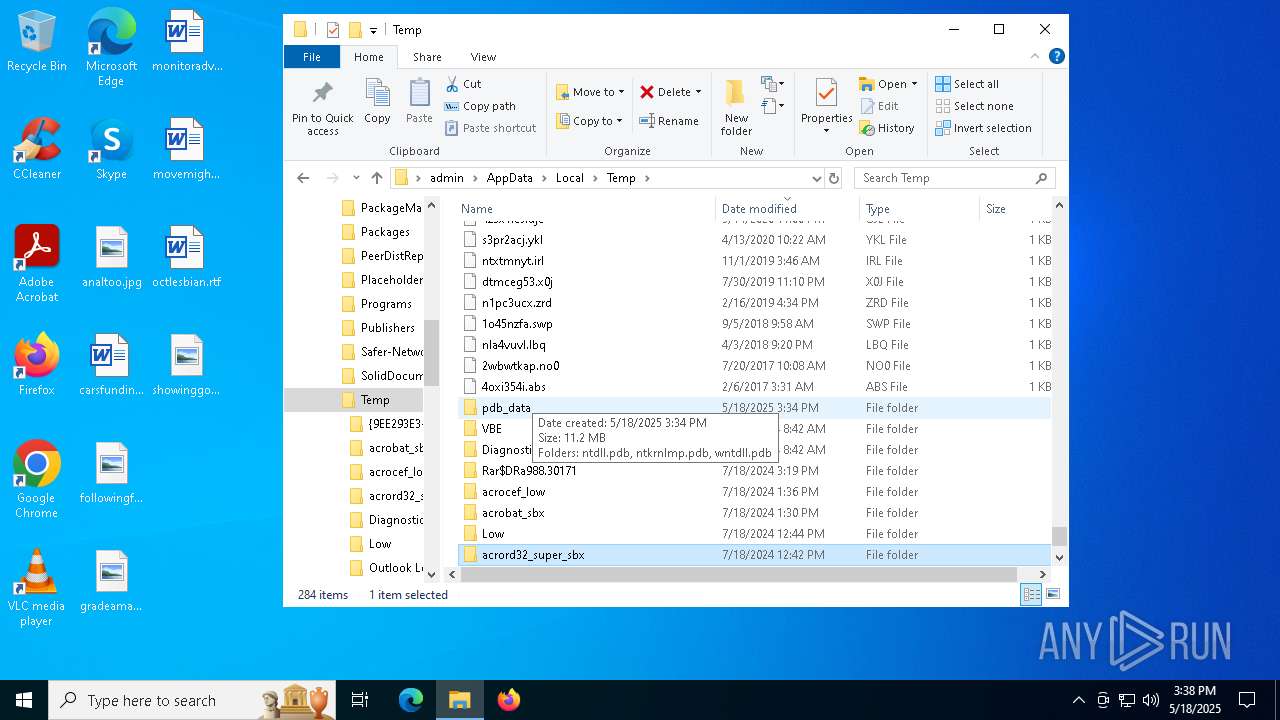
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7340 | launcher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\9C1265A28214D11E06C1F6CBA8FA418B9B74F7EEC14DBAB9A7FEE6871B369E9D00[1].blob | — | |
MD5:— | SHA256:— | |||
| 7340 | launcher.exe | C:\Users\admin\AppData\Local\Temp\pdb_data\ntkrnlmp.pdb\4dbe144182ff4156845cd3bd8b654e561\ntkrnlmp.pdb | — | |
MD5:— | SHA256:— | |||
| 7340 | launcher.exe | C:\Users\admin\AppData\Local\Temp\pdb_data\wntdll.pdb\0c832cc8d76fb9c73efb2270ec571cfb1\wntdll.pdb | binary | |
MD5:398D8BD70CD6C29473DDBCBD66B3D344 | SHA256:557CA8B41E173AFCC4D807050FE0E8E7BD3ABD1D35332C707A4ED4E9FF91C94F | |||
| 7340 | launcher.exe | C:\Users\admin\AppData\Local\Temp\pdb_data\ntdll.pdb\90c2362b9d1f1f5088abfa3bde69baaf1\ntdll.pdb | binary | |
MD5:8C39EEC3338387C44CB5B00BCEFBBEBE | SHA256:936BE8F561811E7CD991BB5876FC6E80611D11A5A8DD3B7550E659BD27E10887 | |||
| 7340 | launcher.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:1A6109119F2E22EBEE8CB6041DBF3808 | SHA256:384DEA07AB4199E8C37E7F5EFE3DB62A6196116D2306EA11A2D1AAE8D9E93CED | |||
| 7340 | launcher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\51CD4DE1C1EDDA2205D1F14D4133D2D1DF657BFD32DC83C1A5308C9944ACD94100[1].blob | binary | |
MD5:8C39EEC3338387C44CB5B00BCEFBBEBE | SHA256:936BE8F561811E7CD991BB5876FC6E80611D11A5A8DD3B7550E659BD27E10887 | |||
| 7340 | launcher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\C06093D02E7DB164EA7F701E97EF10381EA4D08D2D66F00AB885D3F000A7F3A100[1].blob | binary | |
MD5:398D8BD70CD6C29473DDBCBD66B3D344 | SHA256:557CA8B41E173AFCC4D807050FE0E8E7BD3ABD1D35332C707A4ED4E9FF91C94F | |||
| 7340 | launcher.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:4C798BD1086EF54616A934809A3B54B4 | SHA256:D79F9992BE6F082D0430D948ABEE6171139ECB4D43EAB5571935DBEC3F6ED6C1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
67
DNS requests
28
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7340 | launcher.exe | GET | 302 | 204.79.197.219:80 | http://msdl.microsoft.com/download/symbols/wntdll.pdb/0c832cc8d76fb9c73efb2270ec571cfb1/wntdll.pdb | unknown | — | — | whitelisted |
7340 | launcher.exe | GET | 302 | 204.79.197.219:80 | http://msdl.microsoft.com/download/symbols/ntdll.pdb/90c2362b9d1f1f5088abfa3bde69baaf1/ntdll.pdb | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7340 | launcher.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7340 | launcher.exe | GET | 302 | 204.79.197.219:80 | http://msdl.microsoft.com/download/symbols/ntkrnlmp.pdb/4dbe144182ff4156845cd3bd8b654e561/ntkrnlmp.pdb | unknown | — | — | whitelisted |
7684 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7684 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7340 | launcher.exe | 204.79.197.219:80 | msdl.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | launcher.exe | 20.150.70.36:443 | vsblobprodscussu5shard70.blob.core.windows.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | launcher.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
msdl.microsoft.com |
| whitelisted |
vsblobprodscussu5shard70.blob.core.windows.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
vsblobprodscussu5shard28.blob.core.windows.net |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |