| File name: | devcpp-4.9.9.2_setup.exe |
| Full analysis: | https://app.any.run/tasks/1efa6082-6eb6-4777-9548-b6d6dd6dda2d |
| Verdict: | Malicious activity |
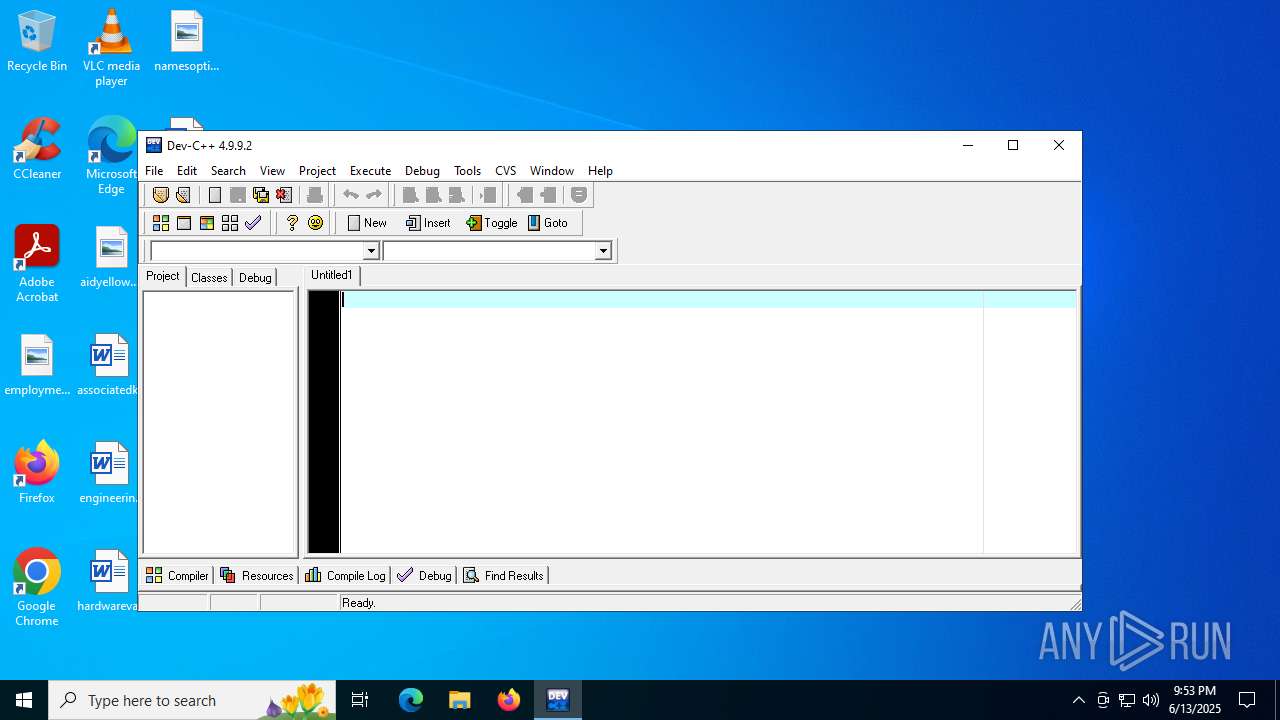
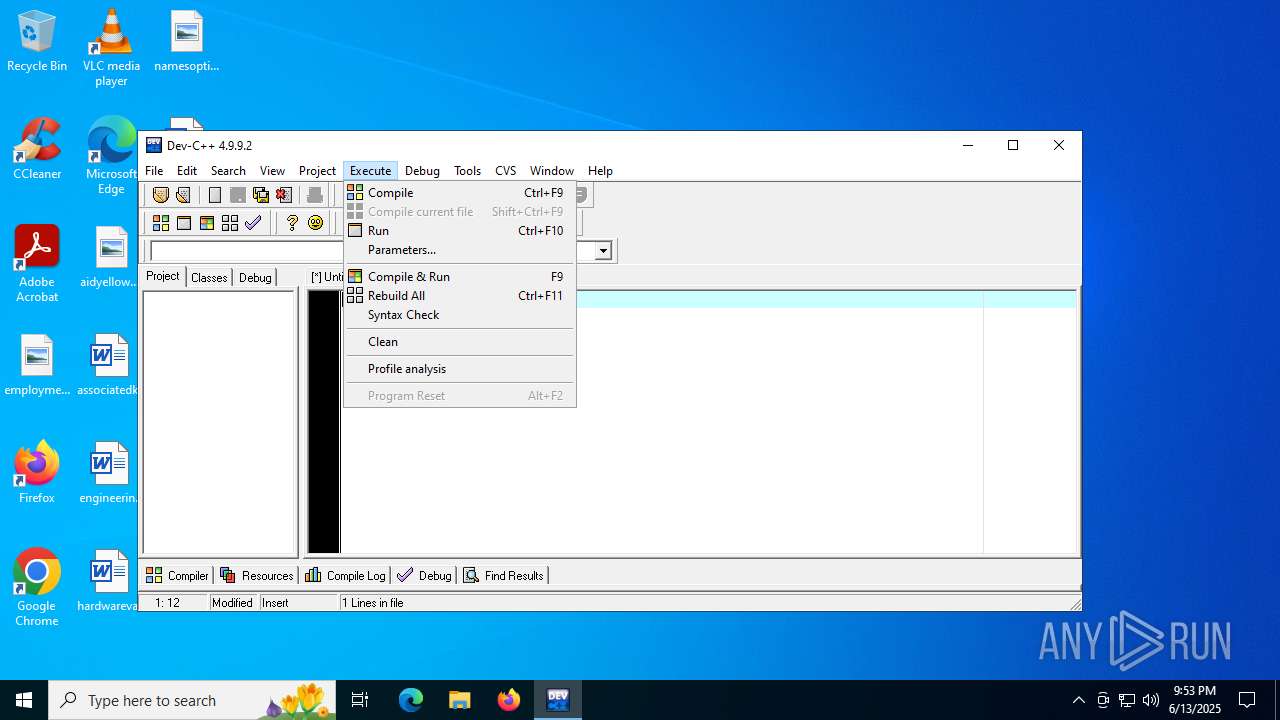
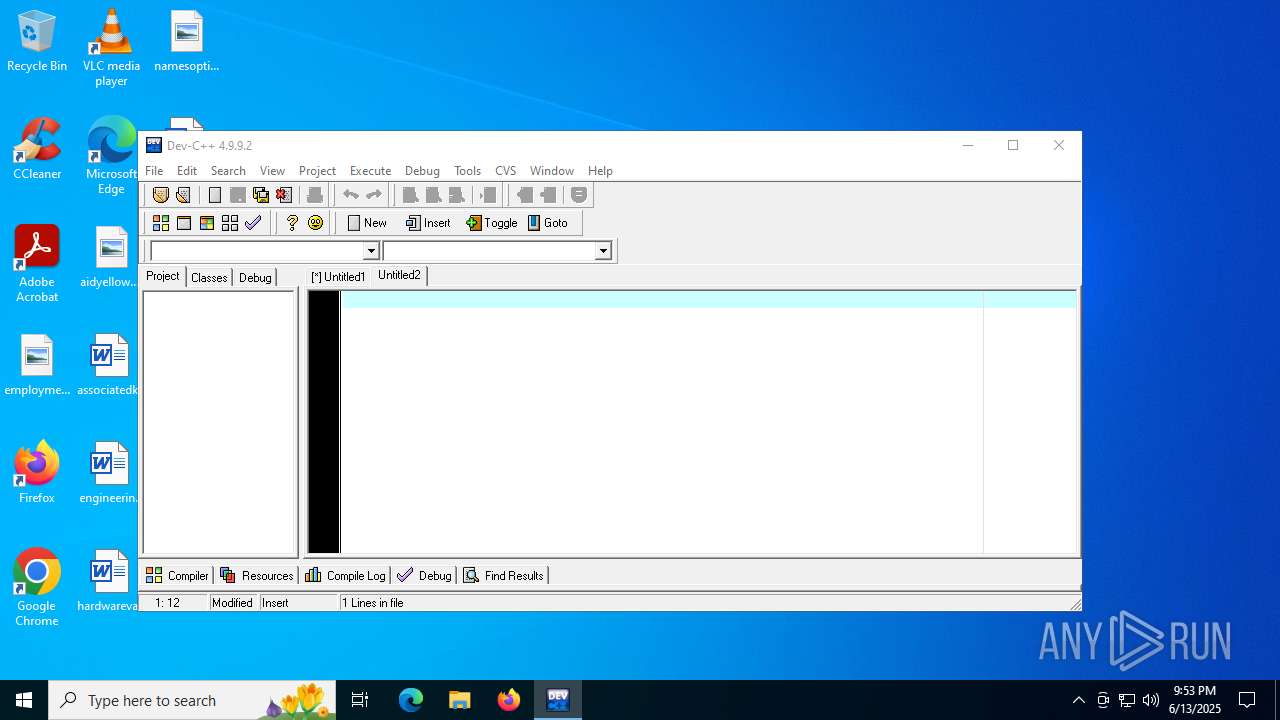
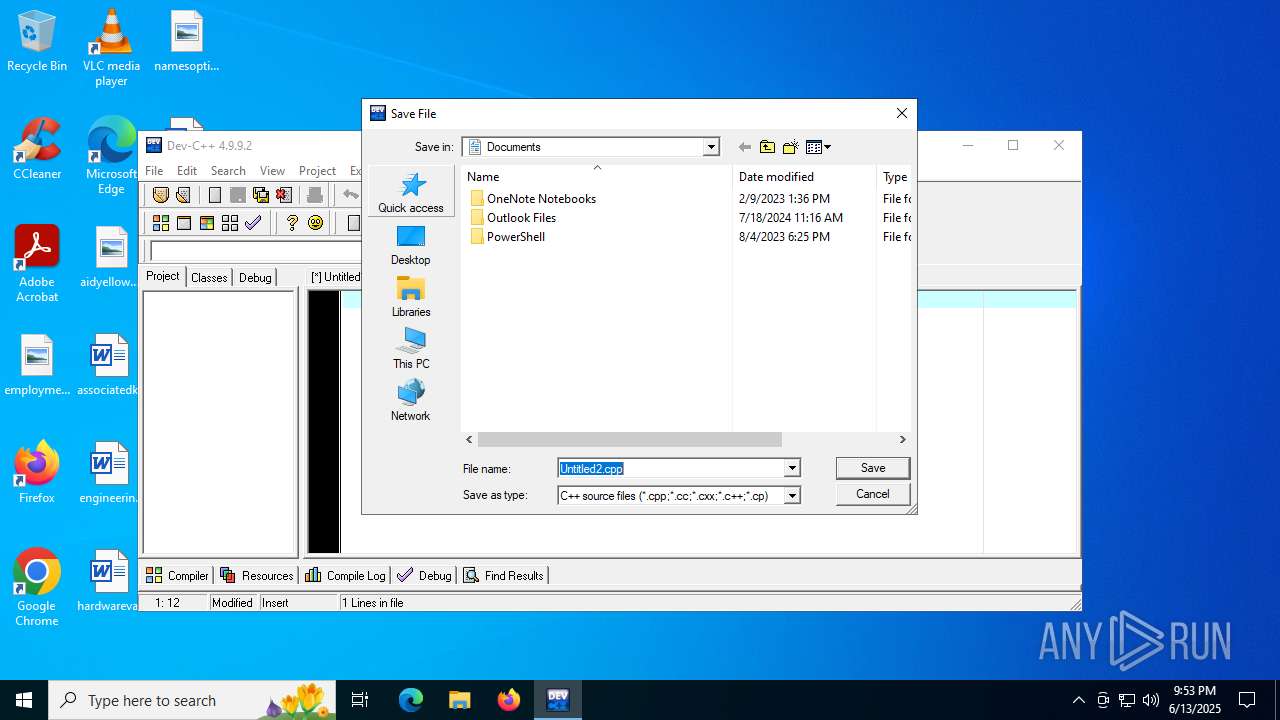
| Analysis date: | June 13, 2025, 21:49:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
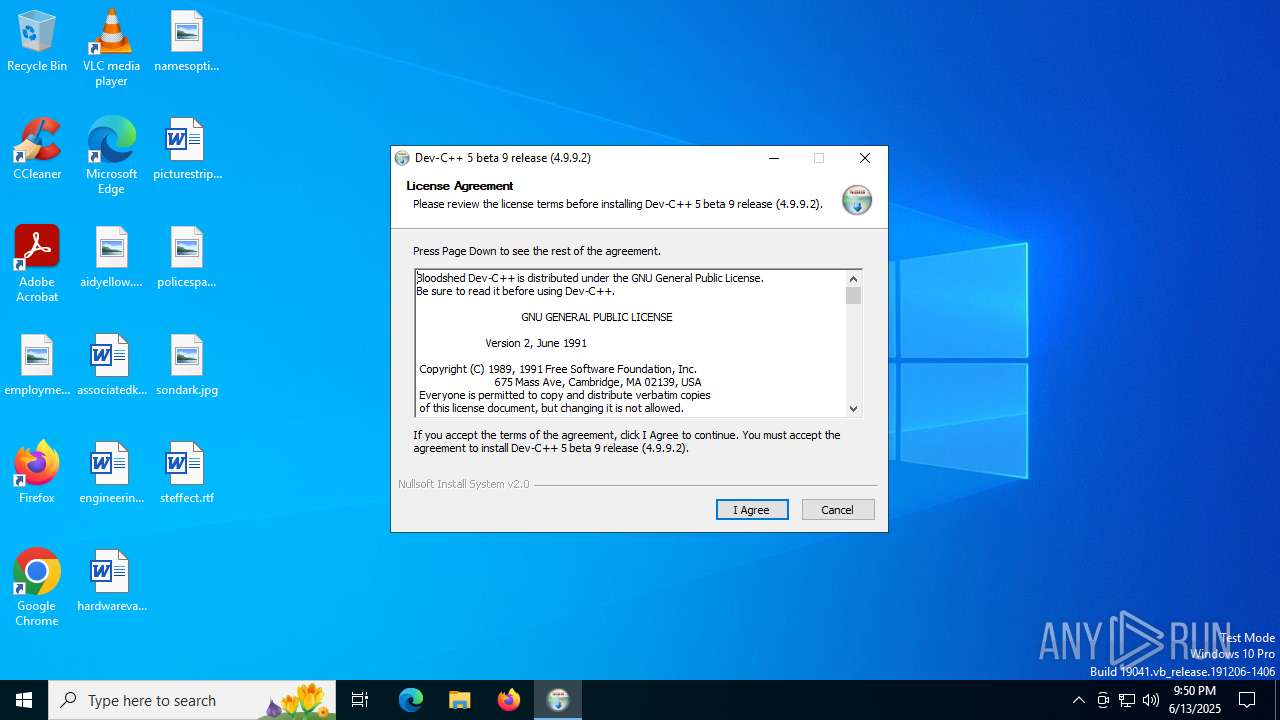
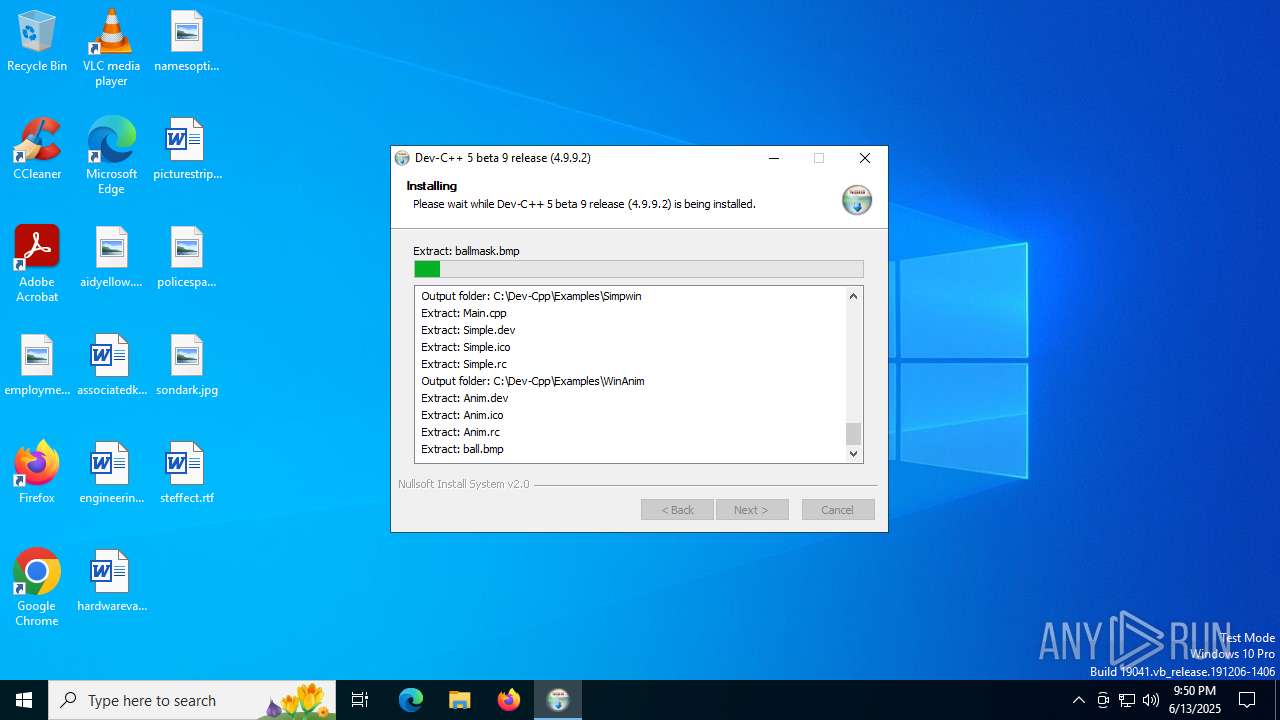
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | A0FA0A34A842DBFD9D3B0CA834311926 |
| SHA1: | E22007D1B1587CB4EAADF90E7076C3BEE61954EC |
| SHA256: | 98CA778D39CE72D1D8DD8C362A19FF5C63D8B827CD02DFBF139D4D0FD6328C40 |
| SSDEEP: | 98304:INGVdPBNZzTzSE1EnBm6IV/uwZlmeflSL2tpZZs9Ba/gmkAIvSFf3oLdmLeD1jdq:PdWwLE1dpr6wf123w0X |
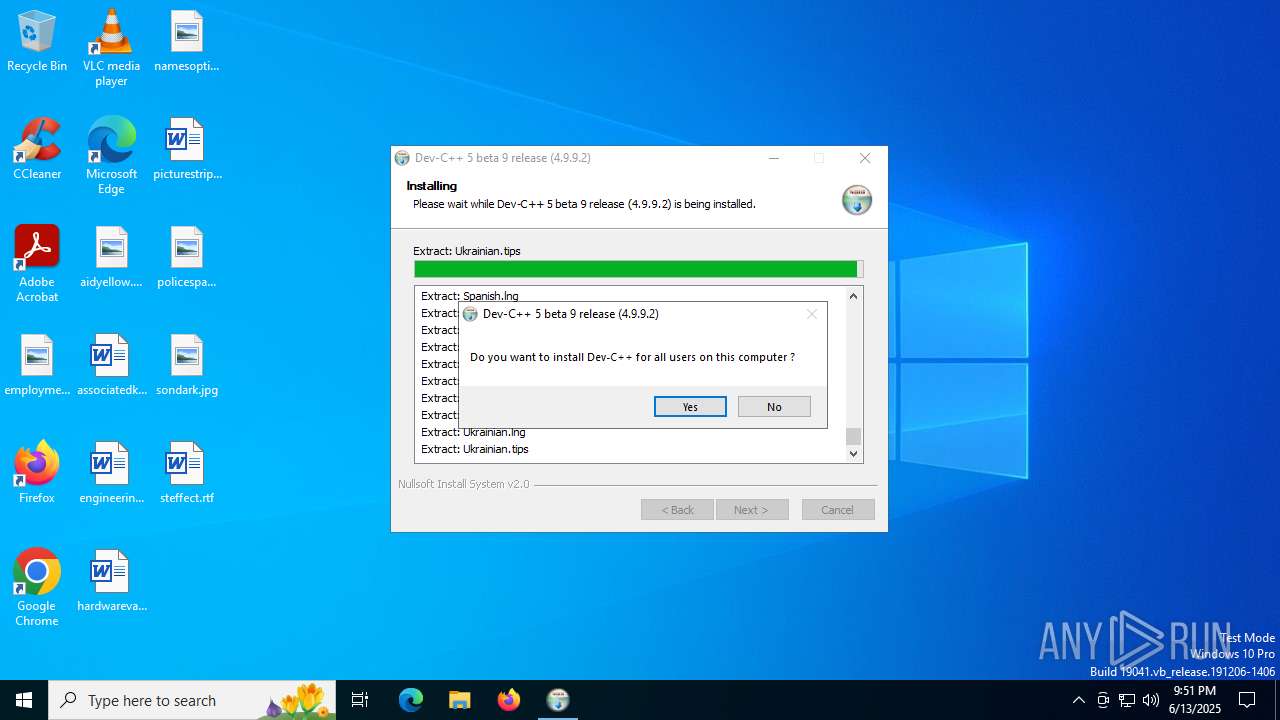
MALICIOUS
No malicious indicators.SUSPICIOUS
There is functionality for taking screenshot (YARA)
- devcpp-4.9.9.2_setup.exe (PID: 4088)
- devcpp.exe (PID: 3396)
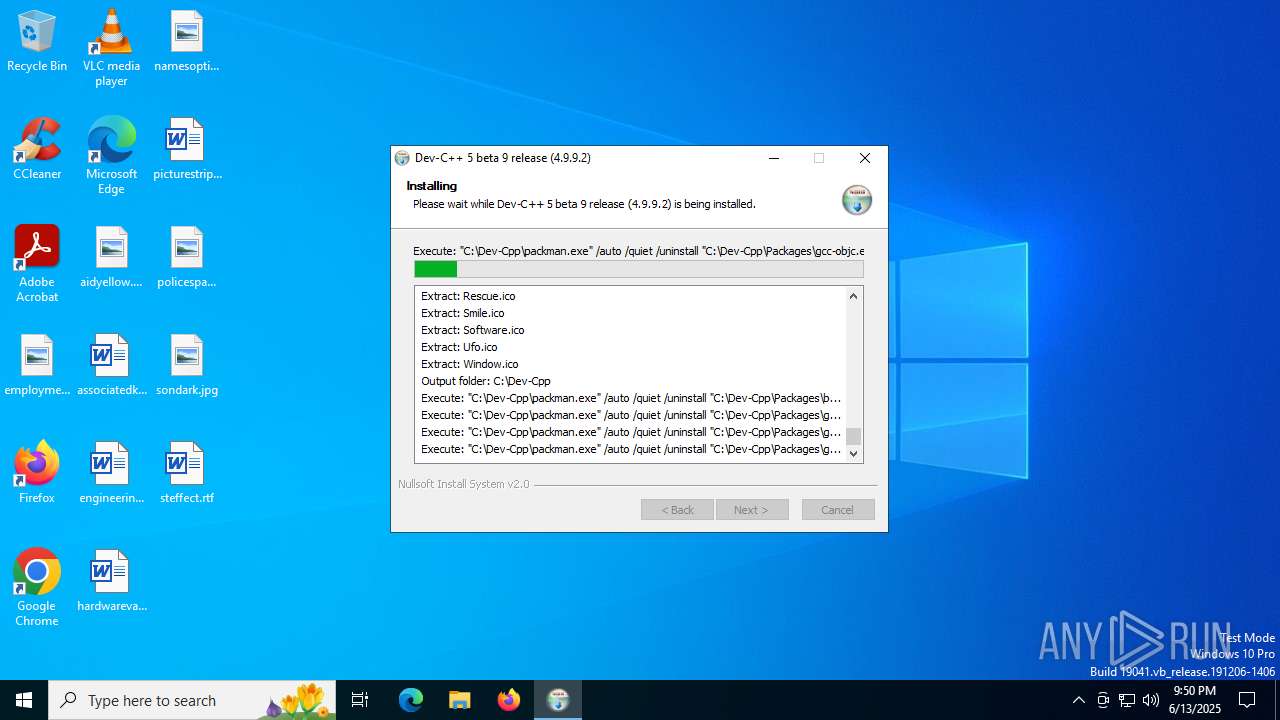
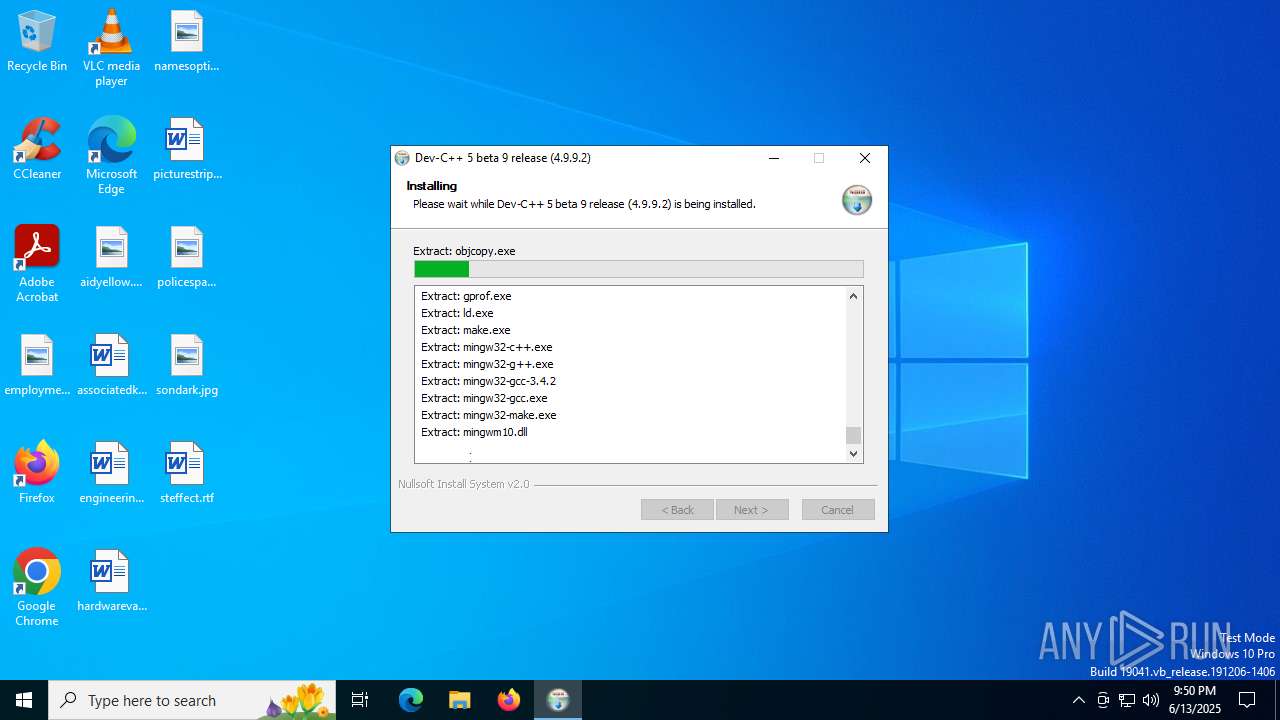
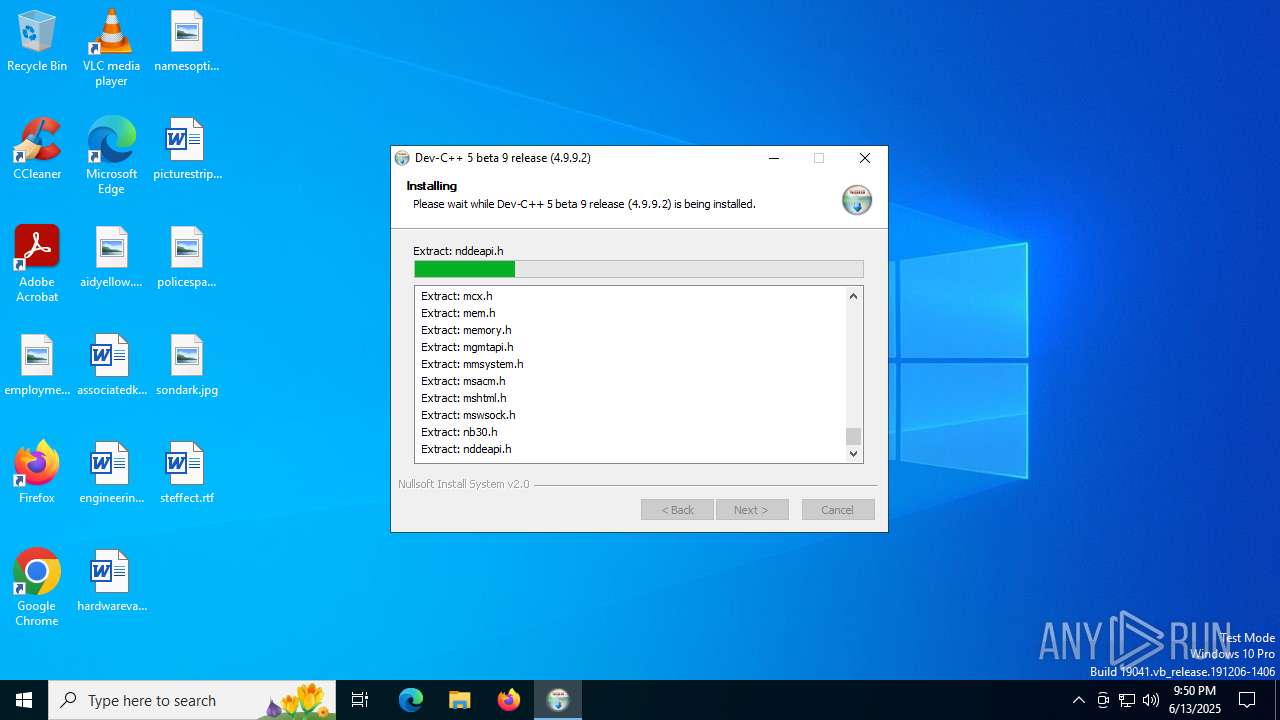
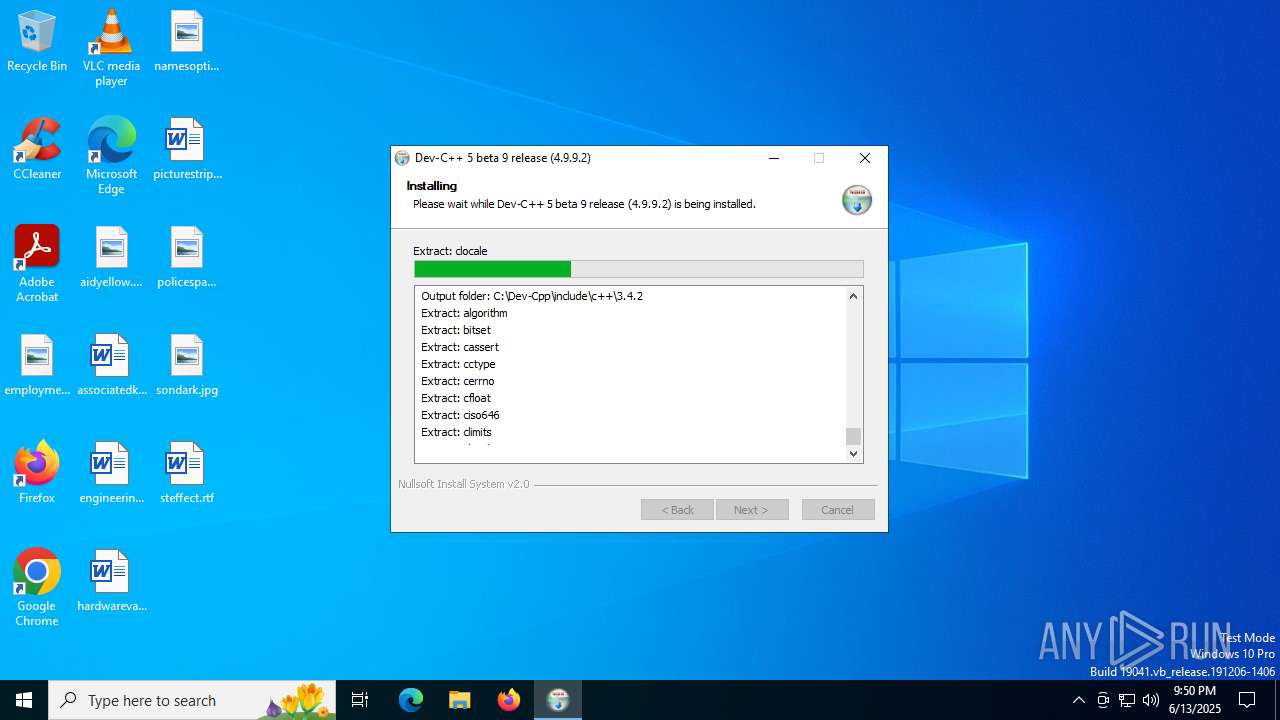
Executable content was dropped or overwritten
- devcpp-4.9.9.2_setup.exe (PID: 4088)
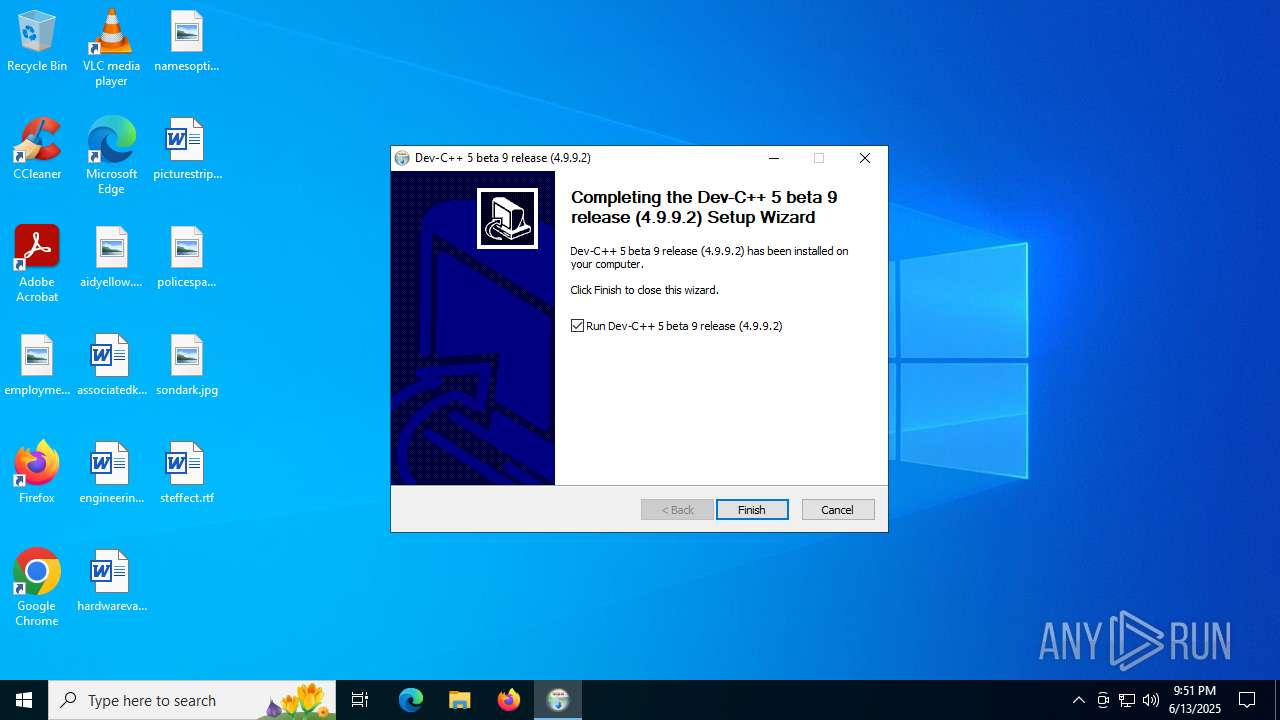
Creates a software uninstall entry
- devcpp-4.9.9.2_setup.exe (PID: 4088)
Reads security settings of Internet Explorer
- devcpp-4.9.9.2_setup.exe (PID: 4088)
The process creates files with name similar to system file names
- devcpp-4.9.9.2_setup.exe (PID: 4088)
Malware-specific behavior (creating "System.dll" in Temp)
- devcpp-4.9.9.2_setup.exe (PID: 4088)
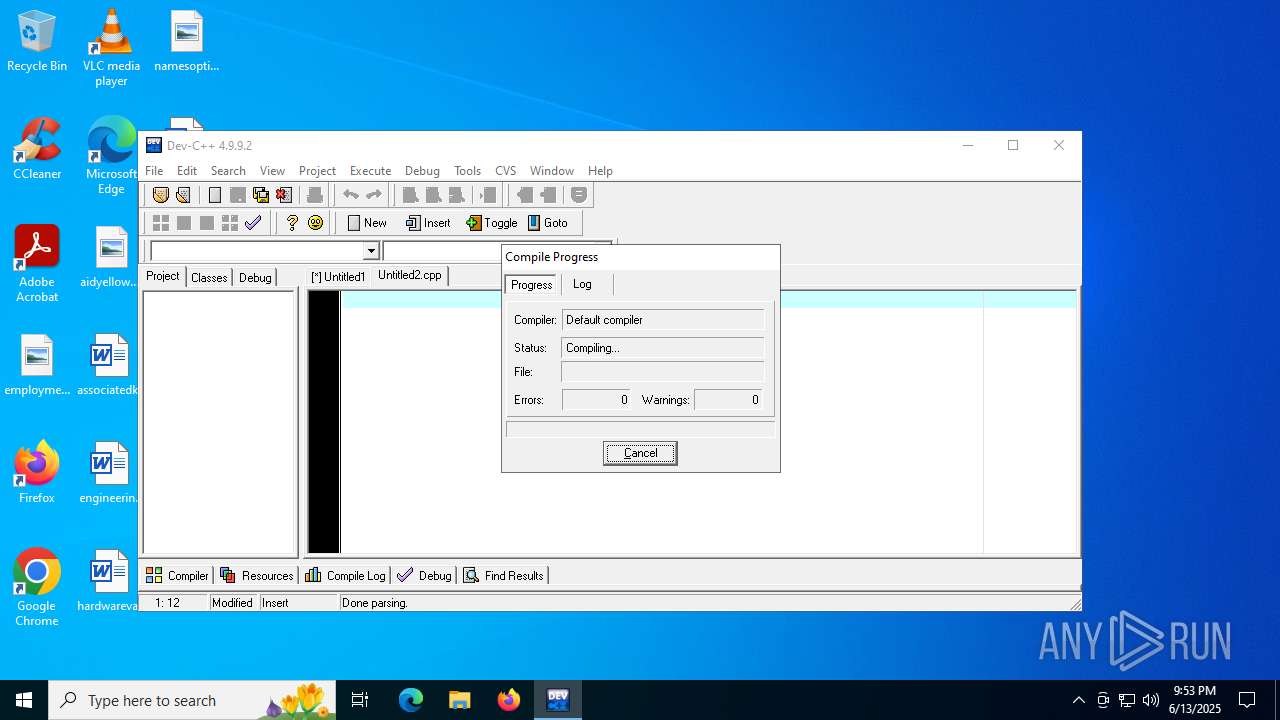
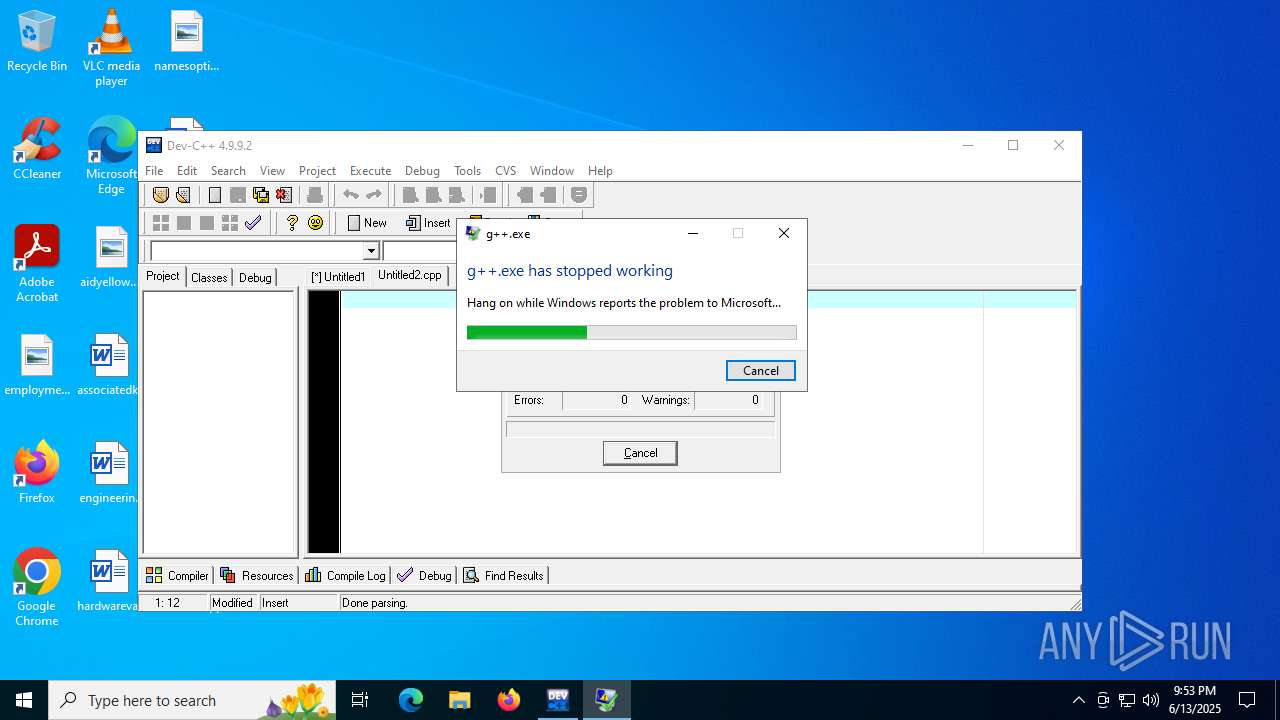
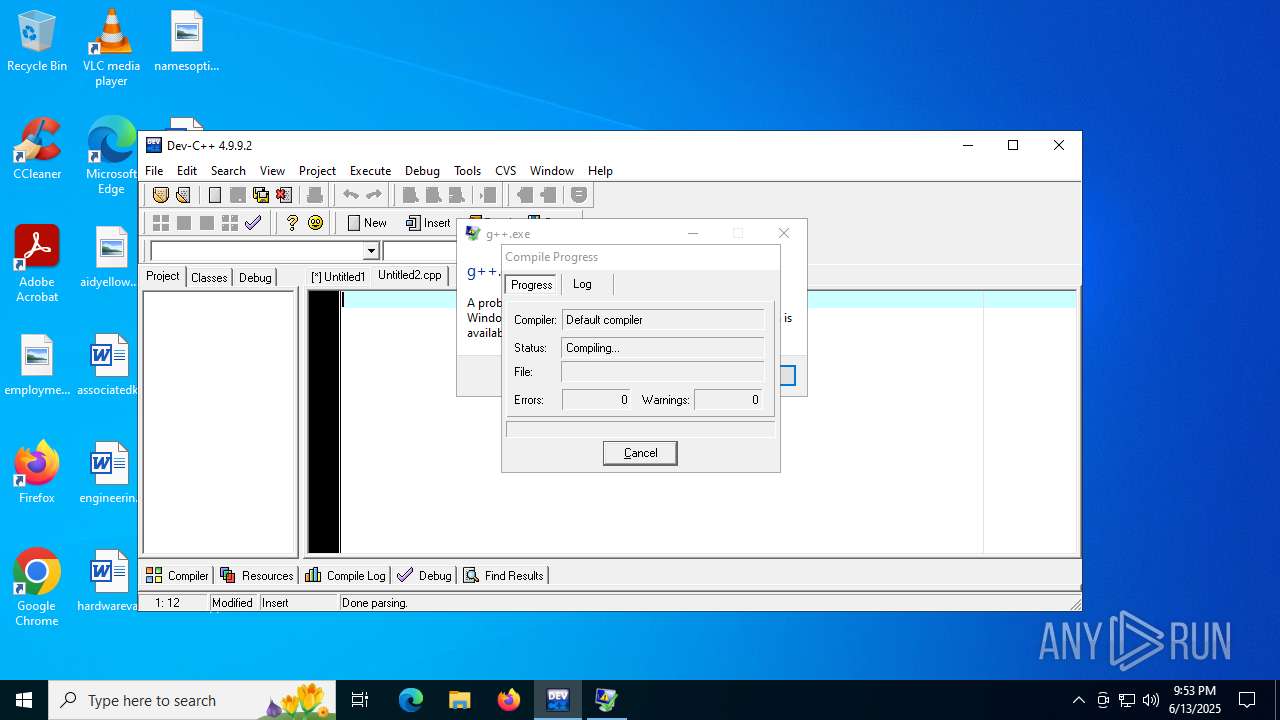
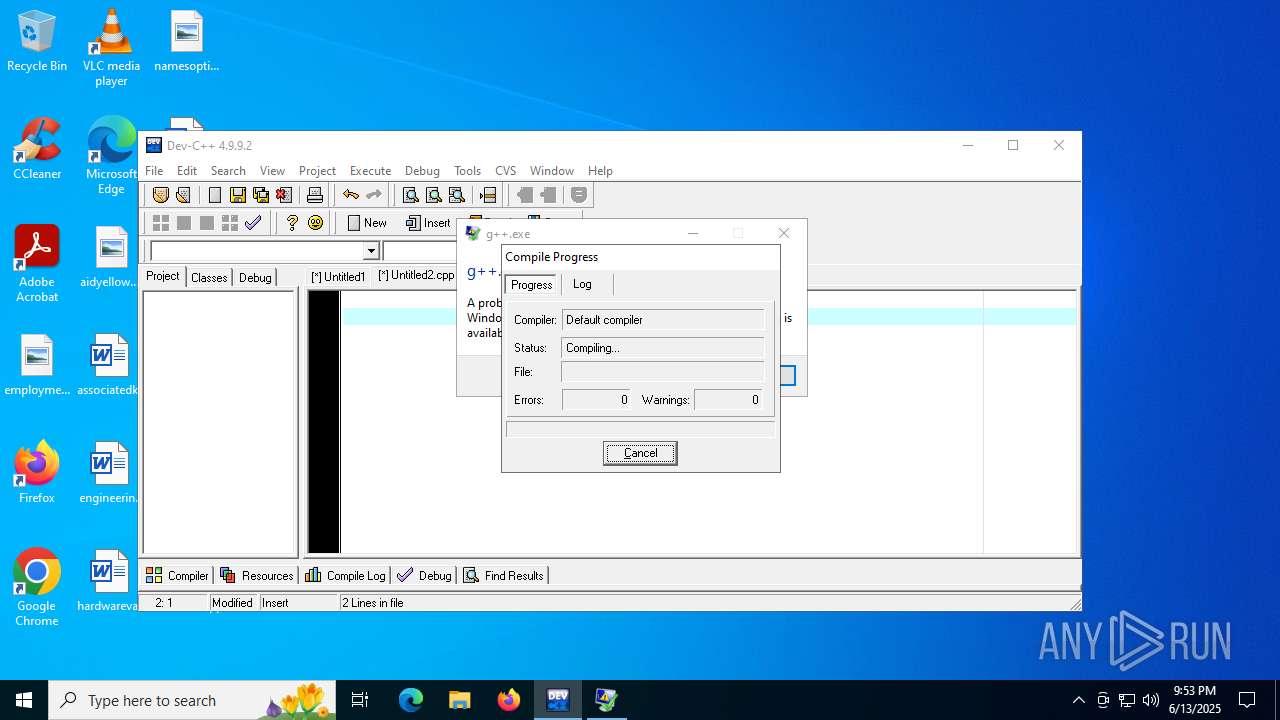
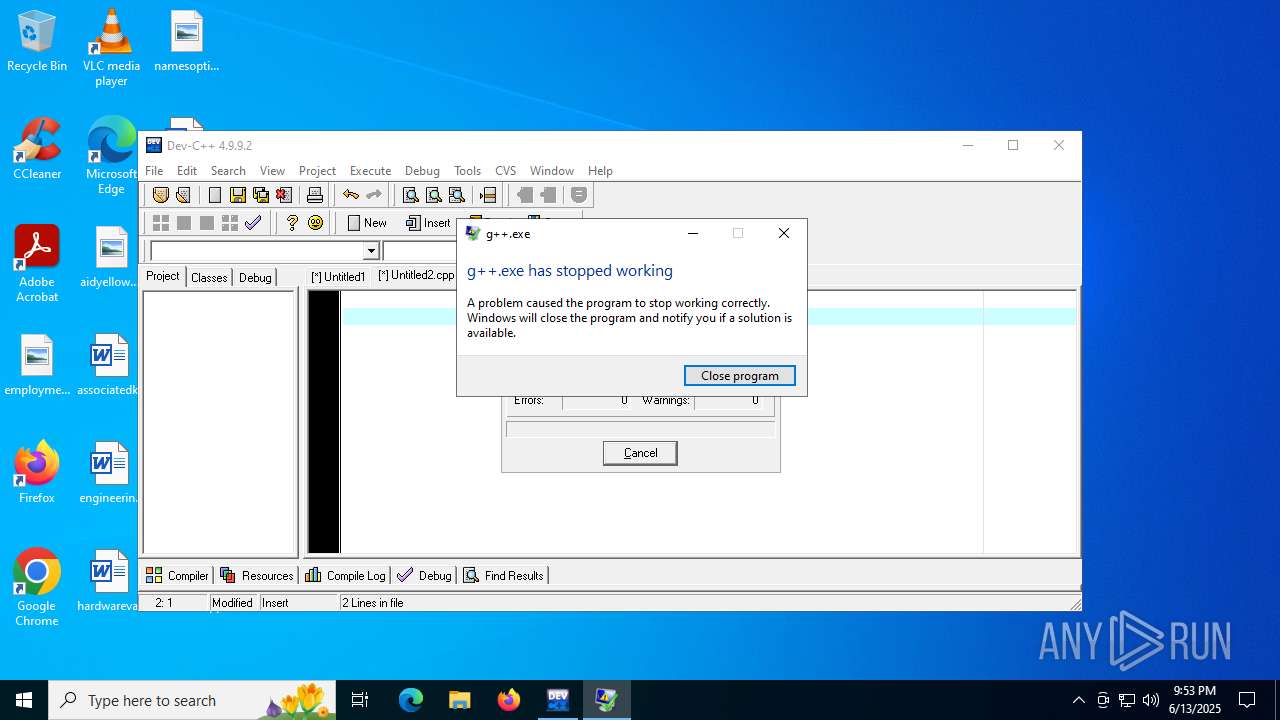
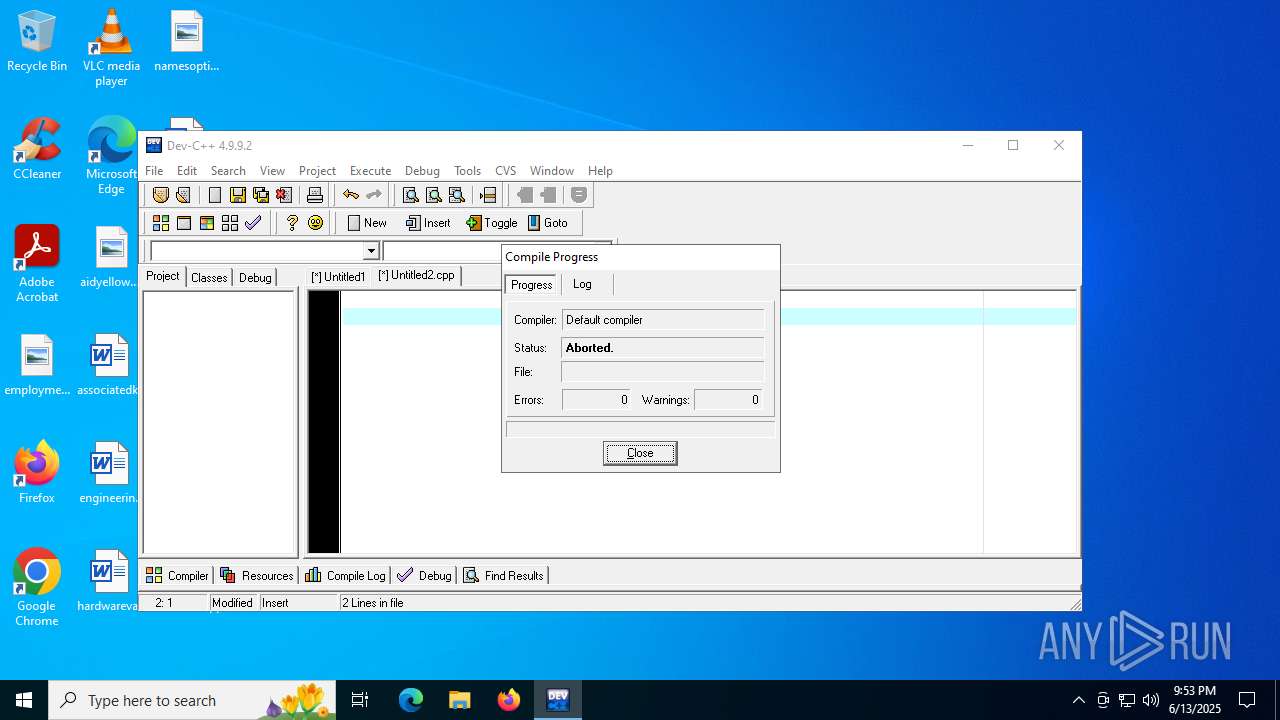
Executes application which crashes
- g++.exe (PID: 6504)
INFO
Create files in a temporary directory
- devcpp-4.9.9.2_setup.exe (PID: 4088)
Checks supported languages
- devcpp-4.9.9.2_setup.exe (PID: 4088)
- Packman.exe (PID: 5172)
- Packman.exe (PID: 5628)
- Packman.exe (PID: 4864)
- Packman.exe (PID: 1812)
- Packman.exe (PID: 6012)
- Packman.exe (PID: 2520)
- Packman.exe (PID: 4312)
- devcpp.exe (PID: 3396)
- make.exe (PID: 472)
- Packman.exe (PID: 6380)
Reads the computer name
- devcpp-4.9.9.2_setup.exe (PID: 4088)
- Packman.exe (PID: 5172)
- Packman.exe (PID: 5628)
- Packman.exe (PID: 4864)
- Packman.exe (PID: 1812)
- Packman.exe (PID: 6012)
- Packman.exe (PID: 2520)
- Packman.exe (PID: 6380)
- Packman.exe (PID: 4312)
- devcpp.exe (PID: 3396)
UPX packer has been detected
- devcpp-4.9.9.2_setup.exe (PID: 4088)
- devcpp.exe (PID: 3396)
The sample compiled with english language support
- devcpp-4.9.9.2_setup.exe (PID: 4088)
Checks proxy server information
- slui.exe (PID: 1728)
Reads the software policy settings
- slui.exe (PID: 1728)
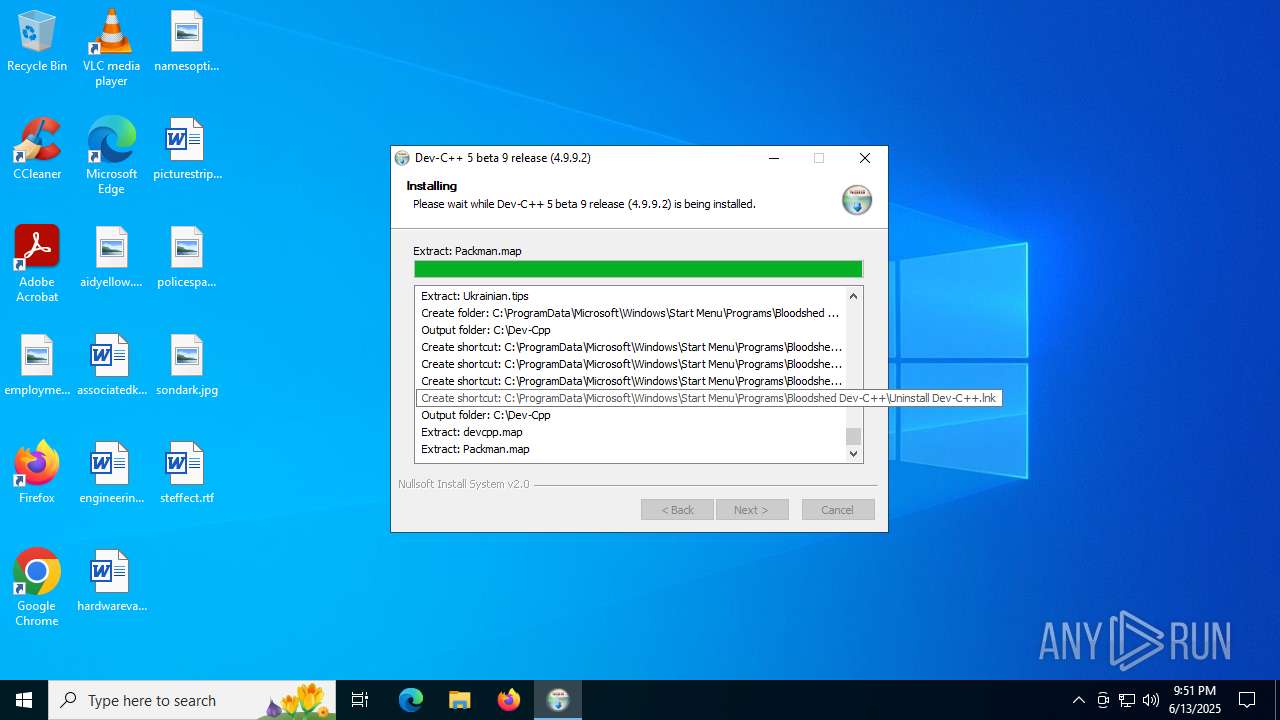
Creates files in the program directory
- devcpp-4.9.9.2_setup.exe (PID: 4088)
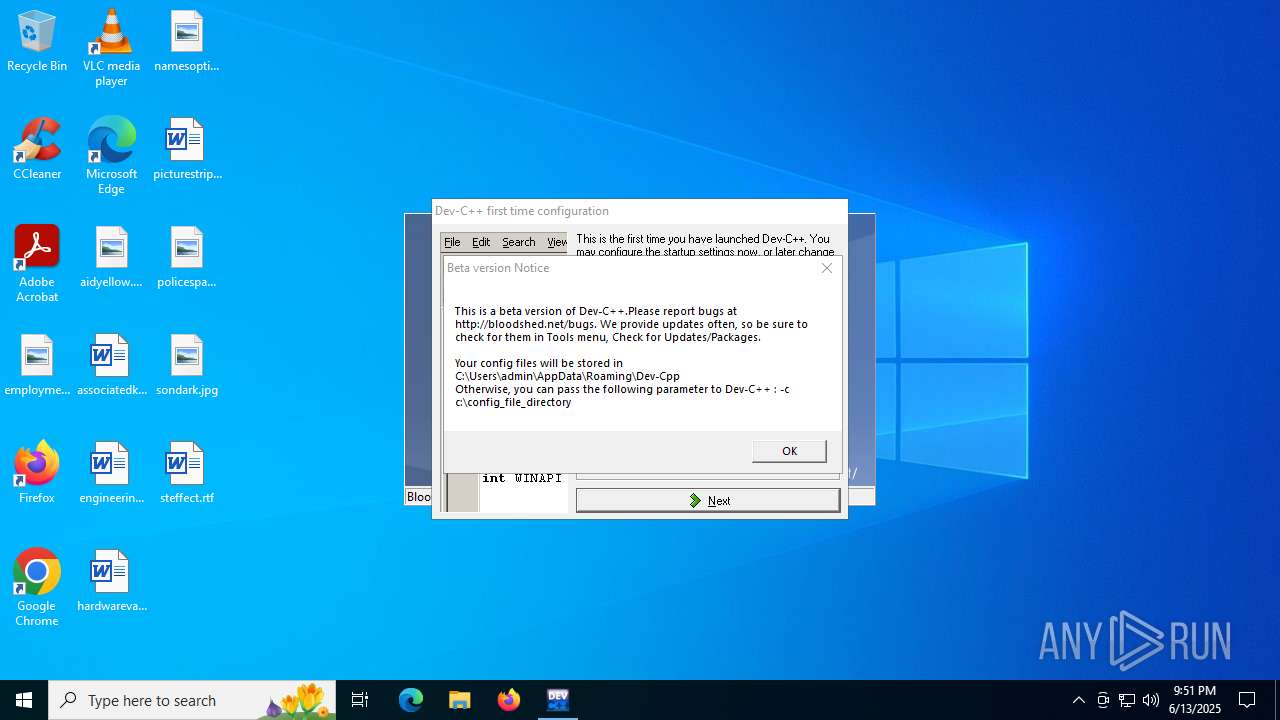
Creates files or folders in the user directory
- devcpp-4.9.9.2_setup.exe (PID: 4088)
- devcpp.exe (PID: 3396)
Compiled with Borland Delphi (YARA)
- devcpp.exe (PID: 3396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:02:07 17:26:28+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x4048 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
163
Monitored processes
17
Malicious processes
1
Suspicious processes
0
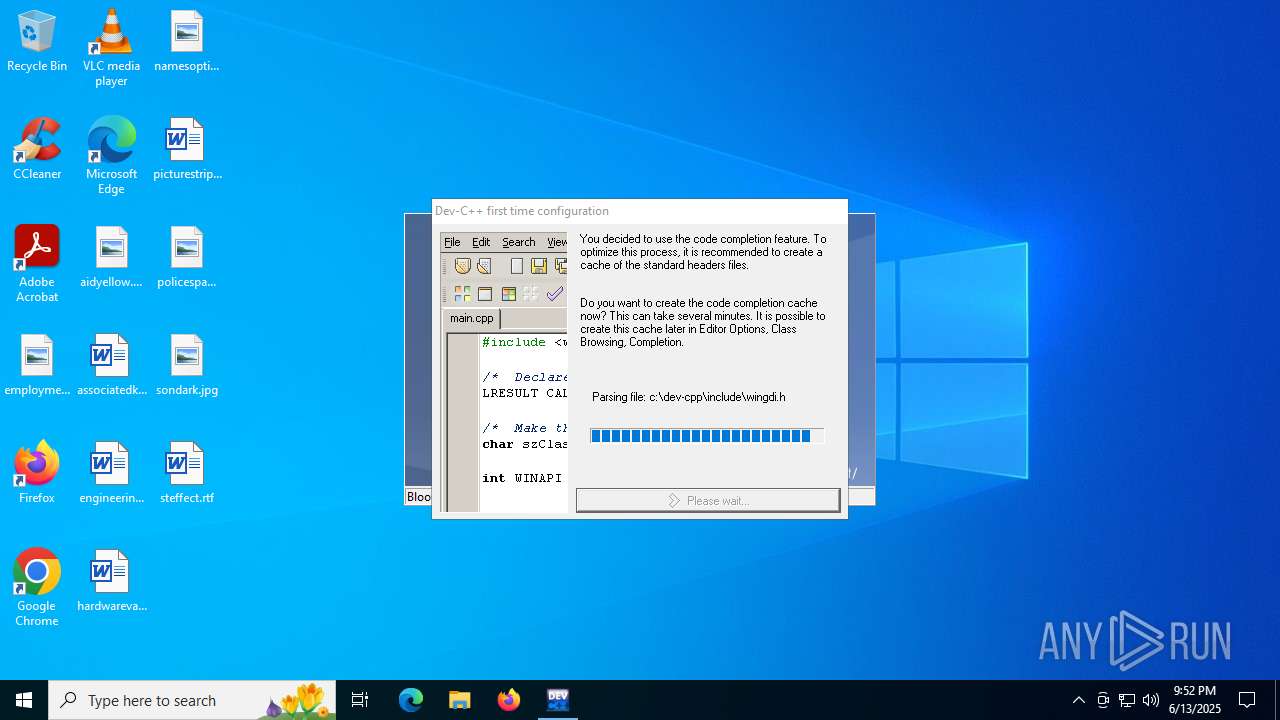
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | make.exe --v | C:\Dev-Cpp\bin\make.exe | — | devcpp.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | make.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1728 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "C:\Dev-Cpp\packman.exe" /auto /quiet /uninstall "C:\Dev-Cpp\Packages\gcc-objc.entry" | C:\Dev-Cpp\Packman.exe | — | devcpp-4.9.9.2_setup.exe | |||||||||||
User: admin Company: Bloodshed Software Integrity Level: HIGH Description: Dev-C++ Package Manager Exit code: 6 Version: 2.2.6.0 Modules
| |||||||||||||||
| 2520 | "C:\Dev-Cpp\packman.exe" /auto /quiet /uninstall "C:\Dev-Cpp\Packages\make.entry" | C:\Dev-Cpp\Packman.exe | — | devcpp-4.9.9.2_setup.exe | |||||||||||
User: admin Company: Bloodshed Software Integrity Level: HIGH Description: Dev-C++ Package Manager Exit code: 6 Version: 2.2.6.0 Modules
| |||||||||||||||
| 3396 | "C:\Dev-Cpp\devcpp.exe" | C:\Dev-Cpp\devcpp.exe | — | devcpp-4.9.9.2_setup.exe | |||||||||||
User: admin Company: Bloodshed Software Integrity Level: HIGH Description: Dev-C++ IDE Version: 4.9.9.2 Modules
| |||||||||||||||
| 4088 | "C:\Users\admin\AppData\Local\Temp\devcpp-4.9.9.2_setup.exe" | C:\Users\admin\AppData\Local\Temp\devcpp-4.9.9.2_setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4312 | "C:\Dev-Cpp\packman.exe" /auto /quiet /uninstall "C:\Dev-Cpp\Packages\w32api.entry" | C:\Dev-Cpp\Packman.exe | — | devcpp-4.9.9.2_setup.exe | |||||||||||
User: admin Company: Bloodshed Software Integrity Level: HIGH Description: Dev-C++ Package Manager Exit code: 6 Version: 2.2.6.0 Modules
| |||||||||||||||
| 4864 | "C:\Dev-Cpp\packman.exe" /auto /quiet /uninstall "C:\Dev-Cpp\Packages\gcc-g++.entry" | C:\Dev-Cpp\Packman.exe | — | devcpp-4.9.9.2_setup.exe | |||||||||||
User: admin Company: Bloodshed Software Integrity Level: HIGH Description: Dev-C++ Package Manager Exit code: 6 Version: 2.2.6.0 Modules
| |||||||||||||||
| 5172 | "C:\Dev-Cpp\packman.exe" /auto /quiet /uninstall "C:\Dev-Cpp\Packages\binutils.entry" | C:\Dev-Cpp\Packman.exe | — | devcpp-4.9.9.2_setup.exe | |||||||||||
User: admin Company: Bloodshed Software Integrity Level: HIGH Description: Dev-C++ Package Manager Exit code: 6 Version: 2.2.6.0 Modules
| |||||||||||||||
Total events
7 187
Read events
7 098
Write events
84
Delete events
5
Modification events
| (PID) Process: | (4088) devcpp-4.9.9.2_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Dev-C++ |
| Operation: | write | Name: | Install_Dir |
Value: C:\Dev-Cpp | |||
| (PID) Process: | (4088) devcpp-4.9.9.2_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Dev-C++ |
| Operation: | write | Name: | DisplayName |
Value: Dev-C++ 5 beta 9 release (4.9.9.2) | |||
| (PID) Process: | (4088) devcpp-4.9.9.2_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Dev-C++ |
| Operation: | write | Name: | UninstallString |
Value: "C:\Dev-Cpp\uninstall.exe" | |||
| (PID) Process: | (4088) devcpp-4.9.9.2_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Dev-C++ |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (4088) devcpp-4.9.9.2_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Dev-C++ |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (4088) devcpp-4.9.9.2_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Dev-C++\Backup |
| Operation: | write | Name: | Shortcuts |
Value: C:\ProgramData\Microsoft\Windows\Start Menu\Programs | |||
| (PID) Process: | (3396) devcpp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3396) devcpp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000003000000110000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (3396) devcpp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000003000000050000000200000001000000FFFFFFFF | |||
| (PID) Process: | (3396) devcpp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
Executable files
72
Suspicious files
178
Text files
697
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Users\admin\AppData\Local\Temp\nsdFC15.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Users\admin\AppData\Local\Temp\nsdFC15.tmp\ioSpecial.ini | text | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Dev-Cpp\NEWS.txt | text | |
MD5:98B40D2CA6FE05F78229984A923909BF | SHA256:AC04C5D2CD8FA9A2670C959806F5181A56B3E9BB1CC7DA150AF98BA074C86B55 | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Dev-Cpp\Packman.exe | executable | |
MD5:9A33684B8E270FFE321C5CD6D562FC72 | SHA256:D624881357AD773EBEB617BE6697E7BF3144D9484F6D8EE870A5D2AA9348E904 | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Dev-Cpp\Lang\English.tips | text | |
MD5:8266CA81755681D80E10A119CC3AEBBF | SHA256:0785EC98D2929601F2531443915554709C032356A3CD7CFB9D4C32E7DFC75E0D | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Users\admin\AppData\Local\Temp\nsdFC15.tmp\LangDLL.dll | executable | |
MD5:2C3C8976D729D28478A789217A882291 | SHA256:799F91BDD59F2133BF195C5B4CA685EE91666D981A6BCD8A6C45B7C8ECC96EEF | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Dev-Cpp\copying.txt | text | |
MD5:EB8A717170EB808B87A3B6A4A438A7E7 | SHA256:CEA462EE95EFC9CE3BFCA23A9596F443713E65F41A14C4B59AEC88EFE272E14F | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Dev-Cpp\devcpp.exe | executable | |
MD5:33B356DDBCEE822411EBEA7B2EEA14B4 | SHA256:F31375B1CBBA860ED4014038BDB8C4C816FF3CF24ED6D1F37AC756A10FD3898C | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Dev-Cpp\Templates\1-WinApp.template | text | |
MD5:11B9AFA41A18E1453B5FC3391223916C | SHA256:F4A8B818BFDDDED86A8D383B102C17AC1901ACEF79DF09C21FC4E9C39C13A69A | |||
| 4088 | devcpp-4.9.9.2_setup.exe | C:\Dev-Cpp\Lang\English.lng | text | |
MD5:1B5ED983C2C7A7F6521F006089A74236 | SHA256:8C110D6F2DA05343F5D725282FE4788807BC4085711D503A422DA15ED42B6E57 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
32
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2532 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2532 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2632 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1688 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5352 | WerFault.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5352 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6492 | backgroundTaskHost.exe | GET | 200 | 23.40.158.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2320 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2532 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2532 | SIHClient.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |