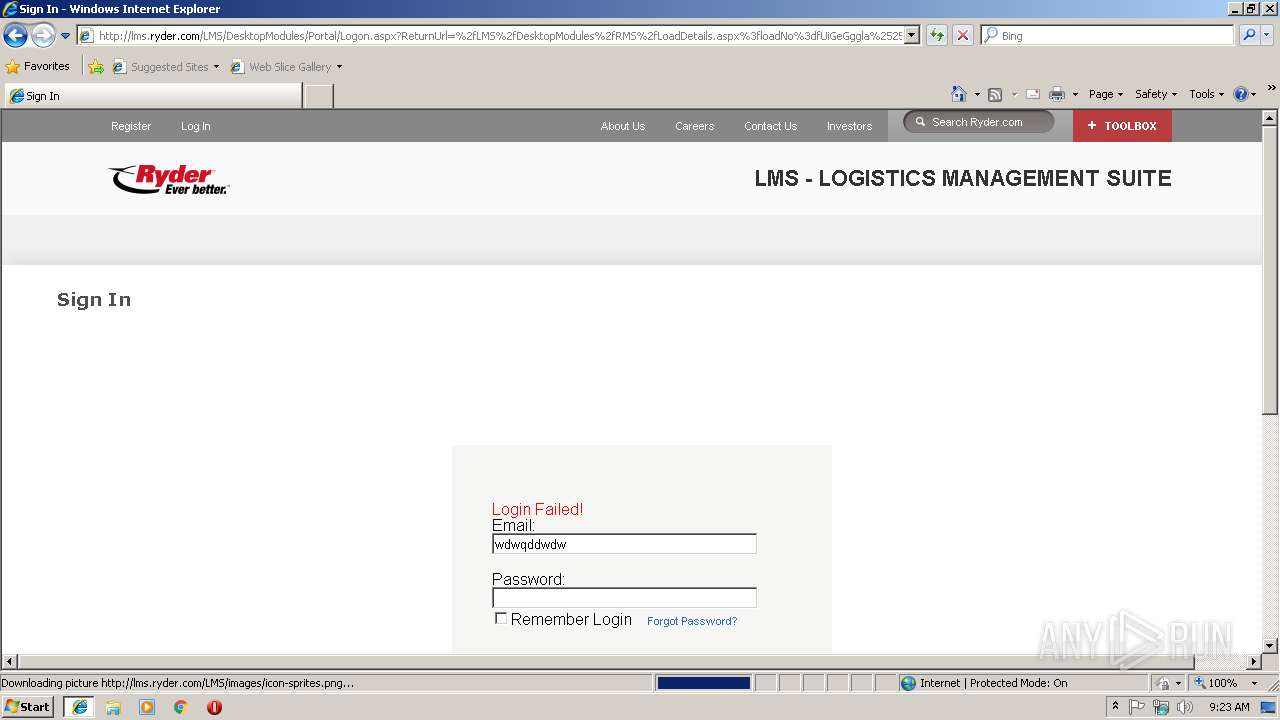
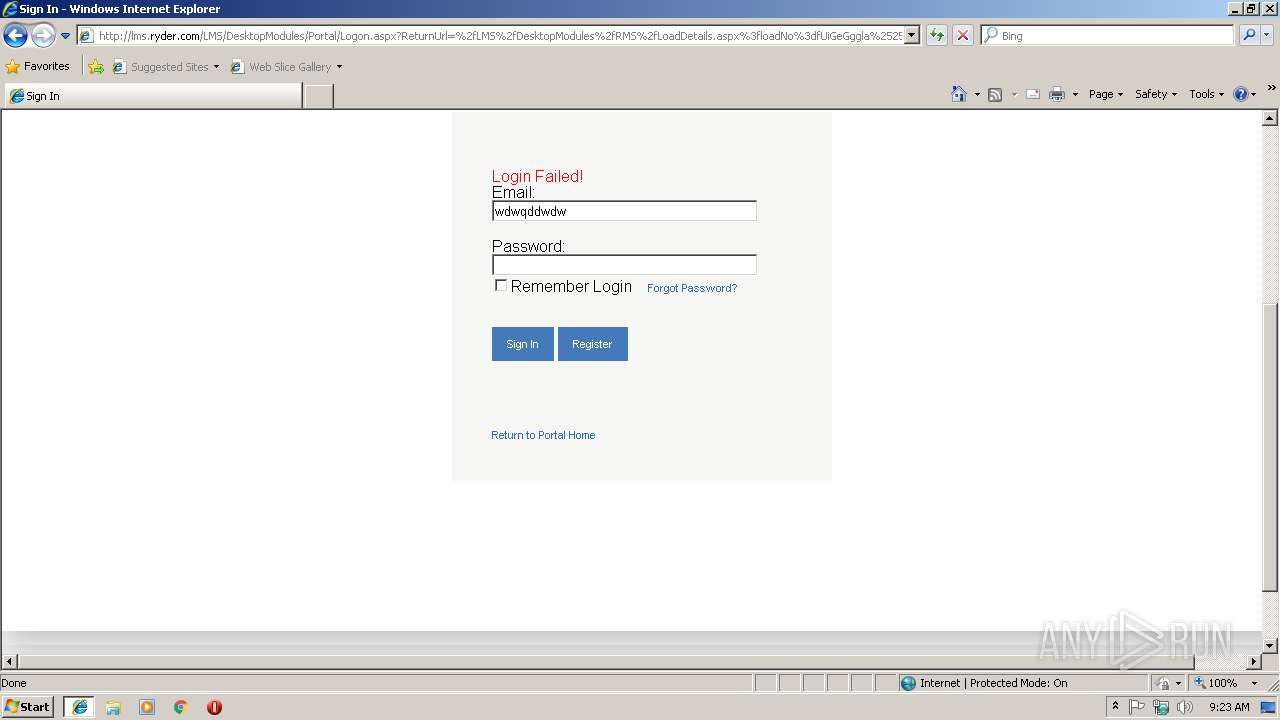
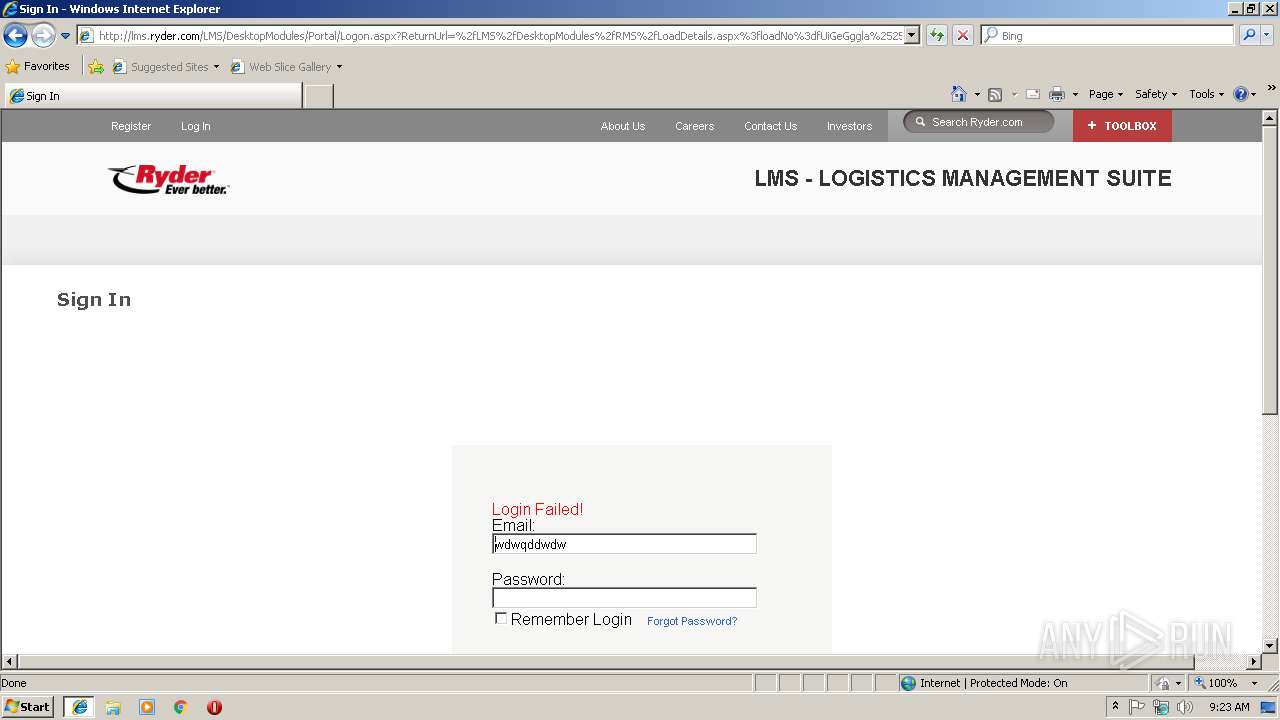
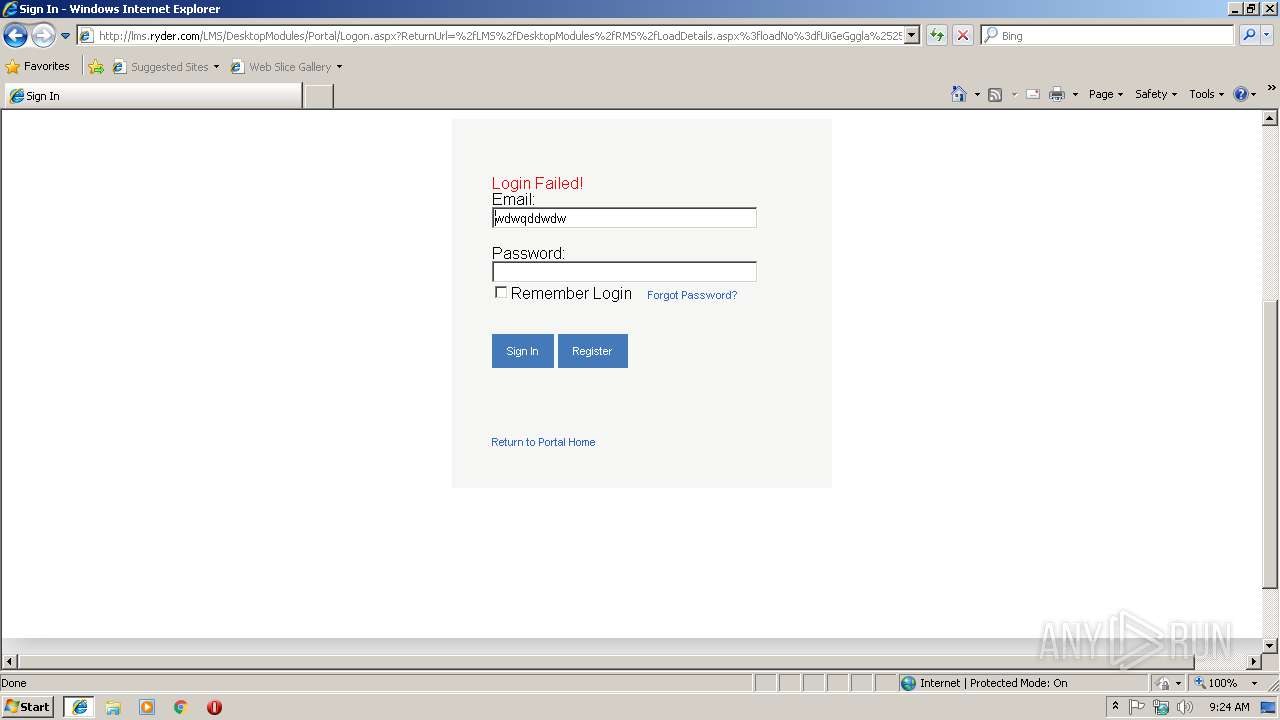
| URL: | http://lms.ryder.com/LMS//DesktopModules/RMS/LoadDetails.aspx?loadNo=fUiGeGggla%252cHr00PYLE.Zw%253d%253d |
| Full analysis: | https://app.any.run/tasks/ea96e35b-e950-4d88-9c57-52429c7cb72f |
| Verdict: | No threats detected |
| Analysis date: | January 24, 2019, 09:22:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 81DB35D217E2EA04810CE1FC2CF7D79E |
| SHA1: | 15FC22AD6A53FD264AA5570F083A52EE08D80E7A |
| SHA256: | 98C92531C0A869BEA2E787BD38FEC6A5564C346C5F5CC068E2D585F980CBA30D |
| SSDEEP: | 3:N1KSIbwLdZLzAw3mh9IM/qE2KYtlAupQzXCt:CSnxntlhprt |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3148)
Reads internet explorer settings
- iexplore.exe (PID: 3148)
Application launched itself
- iexplore.exe (PID: 2704)
Changes internet zones settings
- iexplore.exe (PID: 2704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2704 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2704 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
406
Read events
342
Write events
61
Delete events
3
Modification events
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {AFFBC299-1FB9-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100040018000900170014007A03 | |||
Executable files
0
Suspicious files
0
Text files
29
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2704 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2704 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
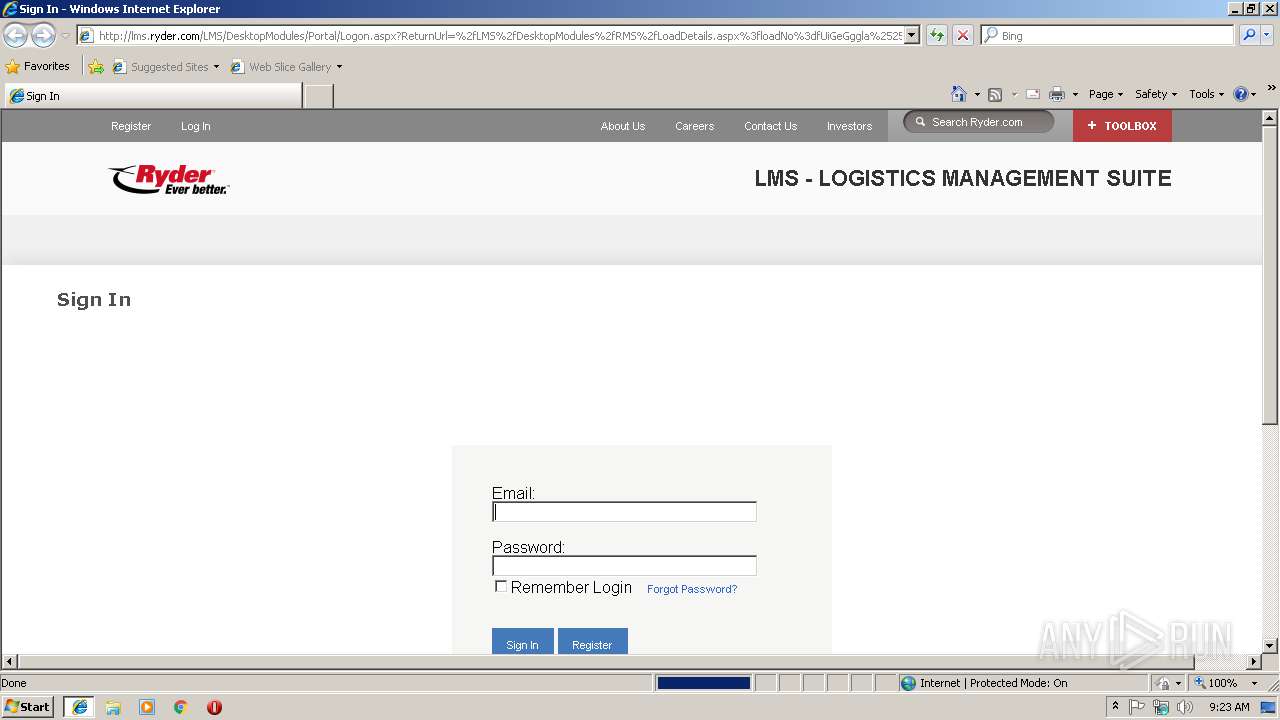
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\Logon[1].aspx | — | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\Logon[1].htm | html | |
MD5:AE2CC88498FAEFBC39138AD019D7ABB9 | SHA256:54AE2E1433A6ACEA520C4A0D890E25A9E1B4A53652A5D7676BE6D585F829D5CA | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\fleetcare[1].png | image | |
MD5:DE8B6844B6901DD60072FBB168A65DCF | SHA256:B1659AFDCC8796D91CCD32F426F1E34141E206F81F533D621B76F48CA21B9AC8 | |||
| 2704 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[3].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\es5-shim[1].js | text | |
MD5:083B5A949488201ED685D6C65FF18FC4 | SHA256:5451F9AF2B085DD8FF927B11F92223B280245C44E94160A9A6AA758874872C6A | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\Arsenal[1].css | text | |
MD5:49597BDC5EFDD77605F6162DE0BDB064 | SHA256:49444BBEF6CCCFACF2D8E3AF98630E9ED4D29FE712081438B84893BC0ADC3906 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\WebResource[2].axd | text | |
MD5:A870B45AC5D6B0D4E18C4829C7B660B4 | SHA256:144524233F795D6A425B76F7AE5C0BB622B5F67E2E6AE73532AD526528CA07CF | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\PIE[1].htc | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
9
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/images/Header/Toolbox/rydersmart.png | US | image | 1.37 Kb | malicious |
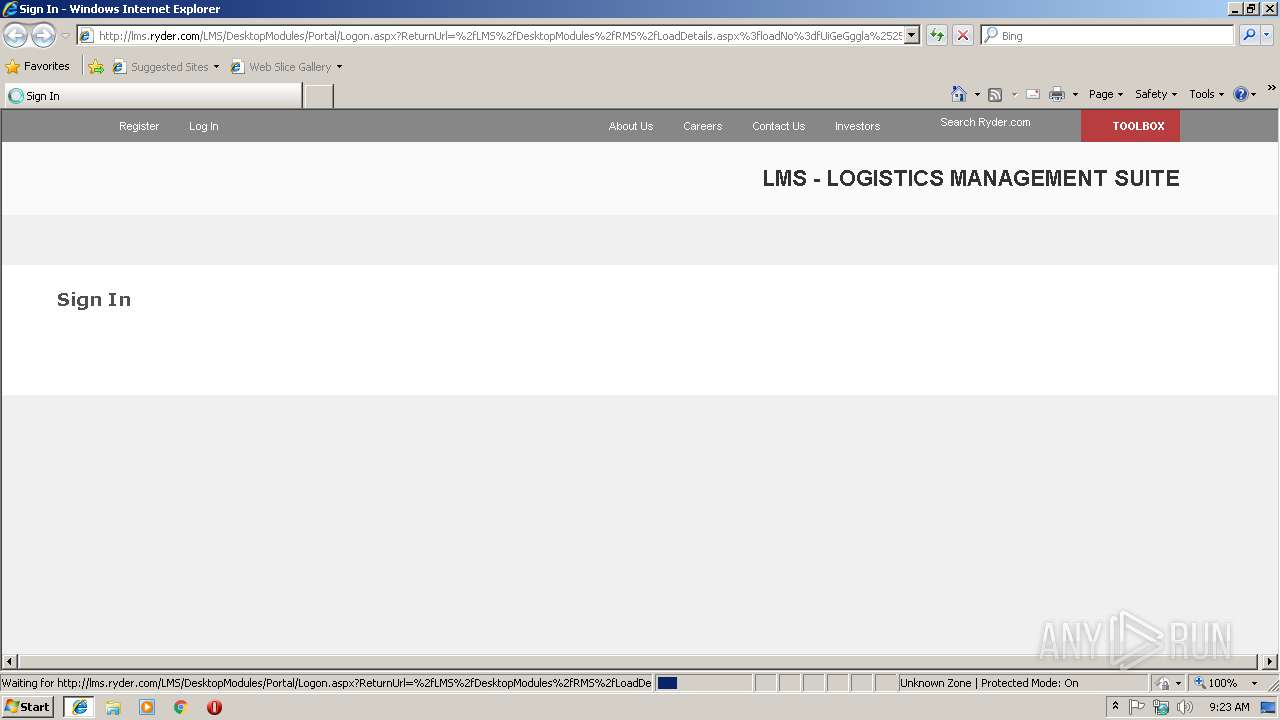
3148 | iexplore.exe | GET | 302 | 168.218.95.148:80 | http://lms.ryder.com/LMS//DesktopModules/RMS/LoadDetails.aspx?loadNo=fUiGeGggla%252cHr00PYLE.Zw%253d%253d | US | html | 267 b | malicious |
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/DesktopModules/Portal/Logon.aspx?ReturnUrl=%2fLMS%2fDesktopModules%2fRMS%2fLoadDetails.aspx%3floadNo%3dfUiGeGggla%25252cHr00PYLE.Zw%25253d%25253d | US | html | 12.5 Kb | malicious |
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/Libraries/LegacyBrowserSupport/html5.js | US | html | 2.37 Kb | malicious |
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/styles/Arsenal.New.css | US | text | 4.01 Kb | malicious |
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/WebResource.axd?d=pynGkmcFUV13He1Qd6_TZLZ0fMdeWNRznLOLlL9kaZZ6PcHCTfnrTVZmE7EJDRdfahErOAjffAdImPuj8j8aAw2&t=636767463772892011 | US | text | 22.5 Kb | malicious |
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/styles/Arsenal.css | US | text | 6.84 Kb | malicious |
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/Libraries/LegacyBrowserSupport/es5-shim.js | US | text | 13.1 Kb | malicious |
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/lms.js | US | text | 1.19 Kb | malicious |
3148 | iexplore.exe | GET | 200 | 168.218.95.148:80 | http://lms.ryder.com/LMS/images/Header/Toolbox/locations.png | US | image | 1.45 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2704 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3148 | iexplore.exe | 168.218.95.148:80 | lms.ryder.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
2704 | iexplore.exe | 168.218.95.148:80 | lms.ryder.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
lms.ryder.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3148 | iexplore.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious request with 'invoice' in http uri |