| File name: | DiagnosticoBradesco_BGS.exe |
| Full analysis: | https://app.any.run/tasks/c6d29015-ee53-4bf9-92f0-7f18be777aa7 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2026, 11:51:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 3476704266CA4E5488A3650D82319D0E |
| SHA1: | EF941D7863BF662549670667544A4C993077609F |
| SHA256: | 98C92491C91DAA9B8DCC8D2614820DAC78FA437C505EB5A48E97770FEDD1E828 |
| SSDEEP: | 98304:QfTOVNWhDtvnWRsQjdDJMeFq1sPBla+Xoskb3DGTt2t9yzCzxcFBVT25yPcchTXg:9aKRy1 |
MALICIOUS
Executing a file with an untrusted certificate
- get_version.exe (PID: 7240)
- get_version.exe (PID: 7328)
Deletes shadow copies
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7556)
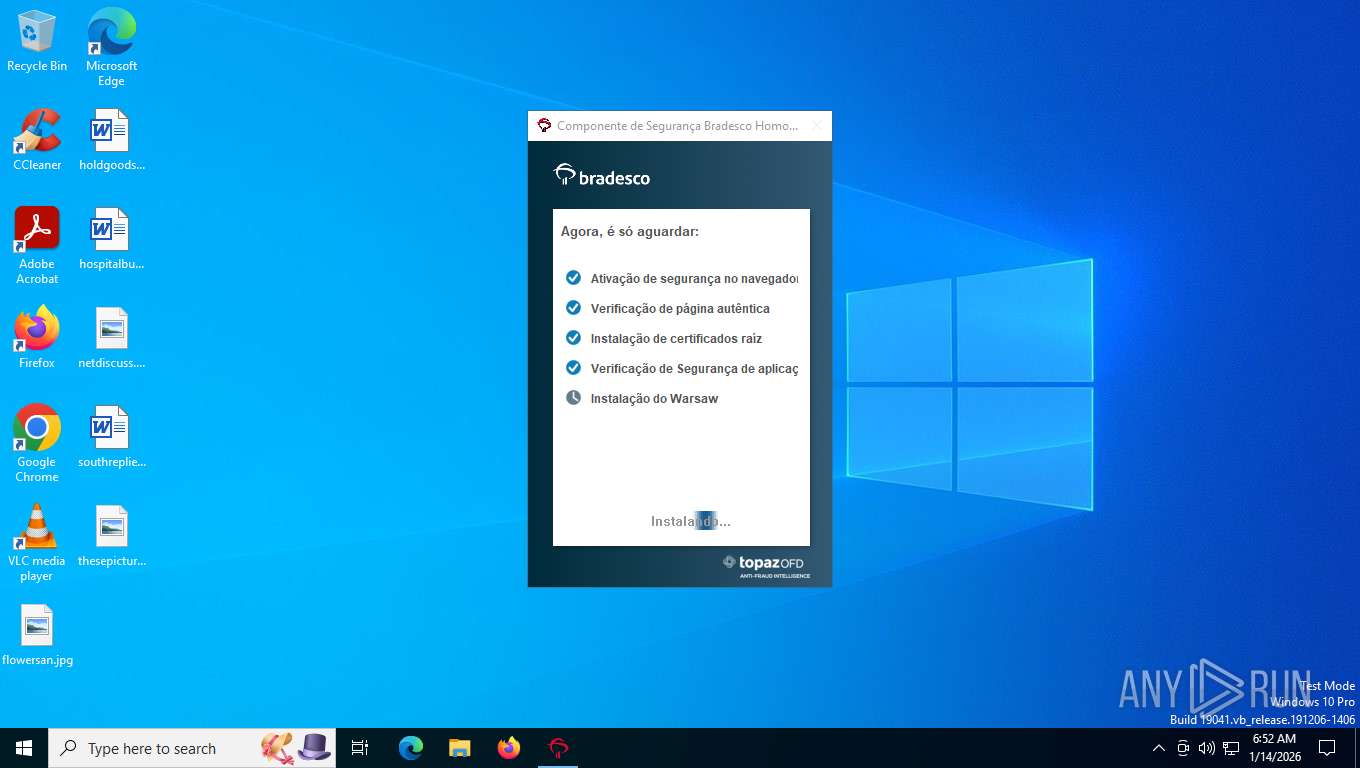
Changes settings of System certificates
- core.exe (PID: 7700)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- DiagnosticoBradesco_BGS.exe (PID: 8156)
Executes as Windows Service
- DiagnosticoBradesco_BGS.exe (PID: 8156)
- core.exe (PID: 7700)
Application launched itself
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- core.exe (PID: 7700)
Reads security settings of Internet Explorer
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- core.exe (PID: 7804)
Executable content was dropped or overwritten
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- warsaw_setup_64.tmp (PID: 6700)
- core.exe (PID: 7700)
- warsaw_setup_64.exe (PID: 5520)
Starts CMD.EXE for commands execution
- warsaw_setup_64.tmp (PID: 6700)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7556)
Process drops legitimate windows executable
- warsaw_setup_64.tmp (PID: 6700)
- core.exe (PID: 7700)
Drops a system driver (possible attempt to evade defenses)
- warsaw_setup_64.tmp (PID: 6700)
- drvinst.exe (PID: 7364)
The process drops C-runtime libraries
- warsaw_setup_64.tmp (PID: 6700)
- core.exe (PID: 7700)
Creates files in the driver directory
- warsaw_setup_64.tmp (PID: 6700)
- core.exe (PID: 7700)
Windows service management via SC.EXE
- sc.exe (PID: 4680)
Starts SC.EXE for service management
- warsaw_setup_64.tmp (PID: 6700)
Creates or modifies Windows services
- core.exe (PID: 7700)
Reads the BIOS version
- core.exe (PID: 7700)
Adds/modifies Windows certificates
- core.exe (PID: 7700)
Reads the Windows owner or organization settings
- warsaw_setup_64.tmp (PID: 6700)
INFO
Checks supported languages
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- DiagnosticoBradesco_BGS.exe (PID: 8132)
- DiagnosticoBradesco_BGS.exe (PID: 8156)
- warsaw_setup_64.tmp (PID: 6700)
- get_version.exe (PID: 7328)
- get_version.exe (PID: 7240)
- warsaw_setup_64.exe (PID: 5520)
- wstlcup.exe (PID: 3692)
- corefixer.exe (PID: 7748)
- core.exe (PID: 7700)
- core.exe (PID: 7620)
- core.exe (PID: 7804)
- drvinst.exe (PID: 7364)
Reads the machine GUID from the registry
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- DiagnosticoBradesco_BGS.exe (PID: 8132)
- DiagnosticoBradesco_BGS.exe (PID: 8156)
- get_version.exe (PID: 7240)
- get_version.exe (PID: 7328)
- core.exe (PID: 7620)
- core.exe (PID: 7700)
- core.exe (PID: 7804)
- drvinst.exe (PID: 7364)
Reads the computer name
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- DiagnosticoBradesco_BGS.exe (PID: 8132)
- DiagnosticoBradesco_BGS.exe (PID: 8156)
- warsaw_setup_64.exe (PID: 5520)
- warsaw_setup_64.tmp (PID: 6700)
- corefixer.exe (PID: 7748)
- core.exe (PID: 7620)
- core.exe (PID: 7700)
- core.exe (PID: 7804)
- drvinst.exe (PID: 7364)
Creates files in the program directory
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- DiagnosticoBradesco_BGS.exe (PID: 8156)
- warsaw_setup_64.tmp (PID: 6700)
- core.exe (PID: 7700)
Process checks computer location settings
- DiagnosticoBradesco_BGS.exe (PID: 7504)
Process checks whether UAC notifications are on
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- core.exe (PID: 7700)
Create files in a temporary directory
- DiagnosticoBradesco_BGS.exe (PID: 7504)
Checks proxy server information
- DiagnosticoBradesco_BGS.exe (PID: 7504)
- core.exe (PID: 7804)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7348)
- WMIC.exe (PID: 2256)
- WMIC.exe (PID: 7564)
The sample compiled with english language support
- warsaw_setup_64.tmp (PID: 6700)
- core.exe (PID: 7700)
Detects InnoSetup installer (YARA)
- warsaw_setup_64.exe (PID: 5520)
- warsaw_setup_64.tmp (PID: 6700)
Compiled with Borland Delphi (YARA)
- warsaw_setup_64.exe (PID: 5520)
- warsaw_setup_64.tmp (PID: 6700)
The sample compiled with portuguese language support
- warsaw_setup_64.tmp (PID: 6700)
- core.exe (PID: 7700)
Creates a software uninstall entry
- warsaw_setup_64.tmp (PID: 6700)
Reads Windows Product ID
- core.exe (PID: 7700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:08:14 13:26:54+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 2821632 |
| InitializedDataSize: | 1895424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c3bf4 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.17.0.1 |
| ProductVersionNumber: | 2.17.0.1 |
| FileFlagsMask: | 0x001f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Unknown (0016) |
| CharacterSet: | Unicode |
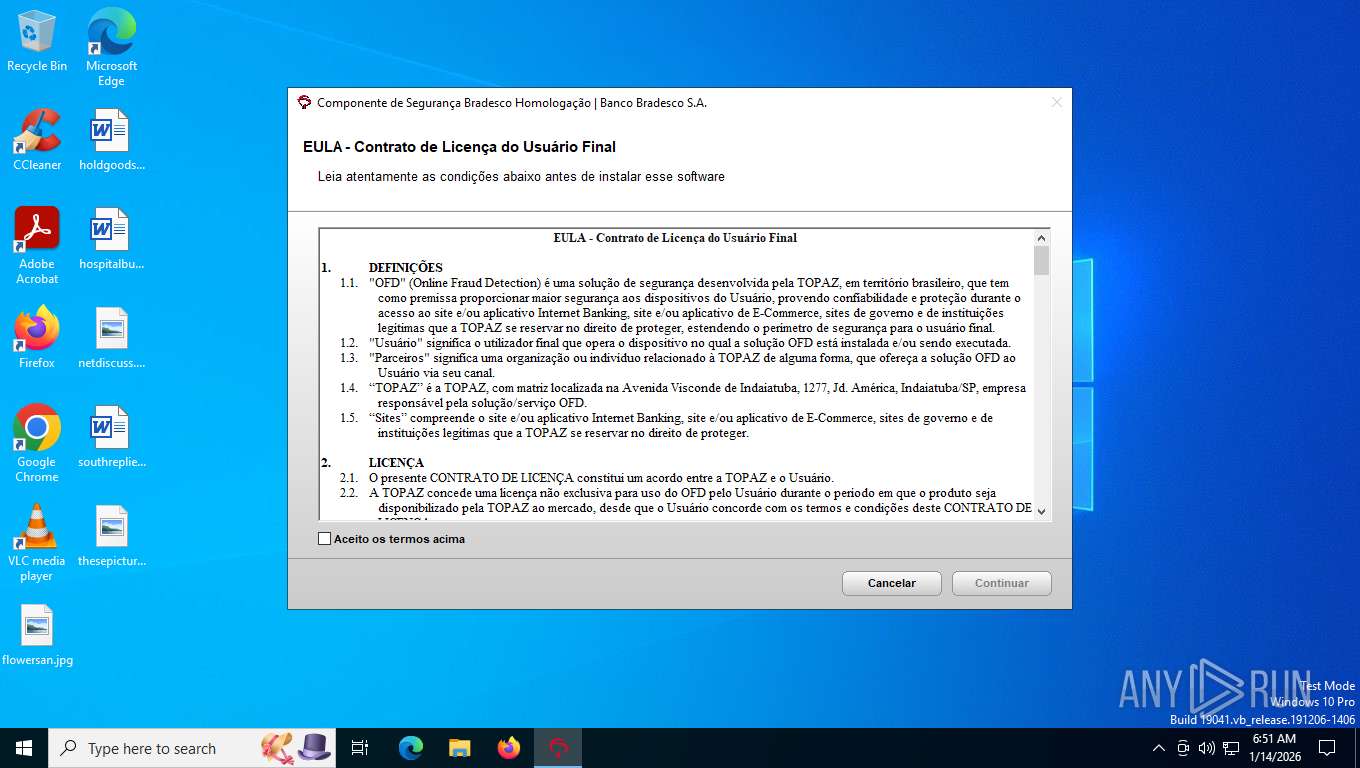
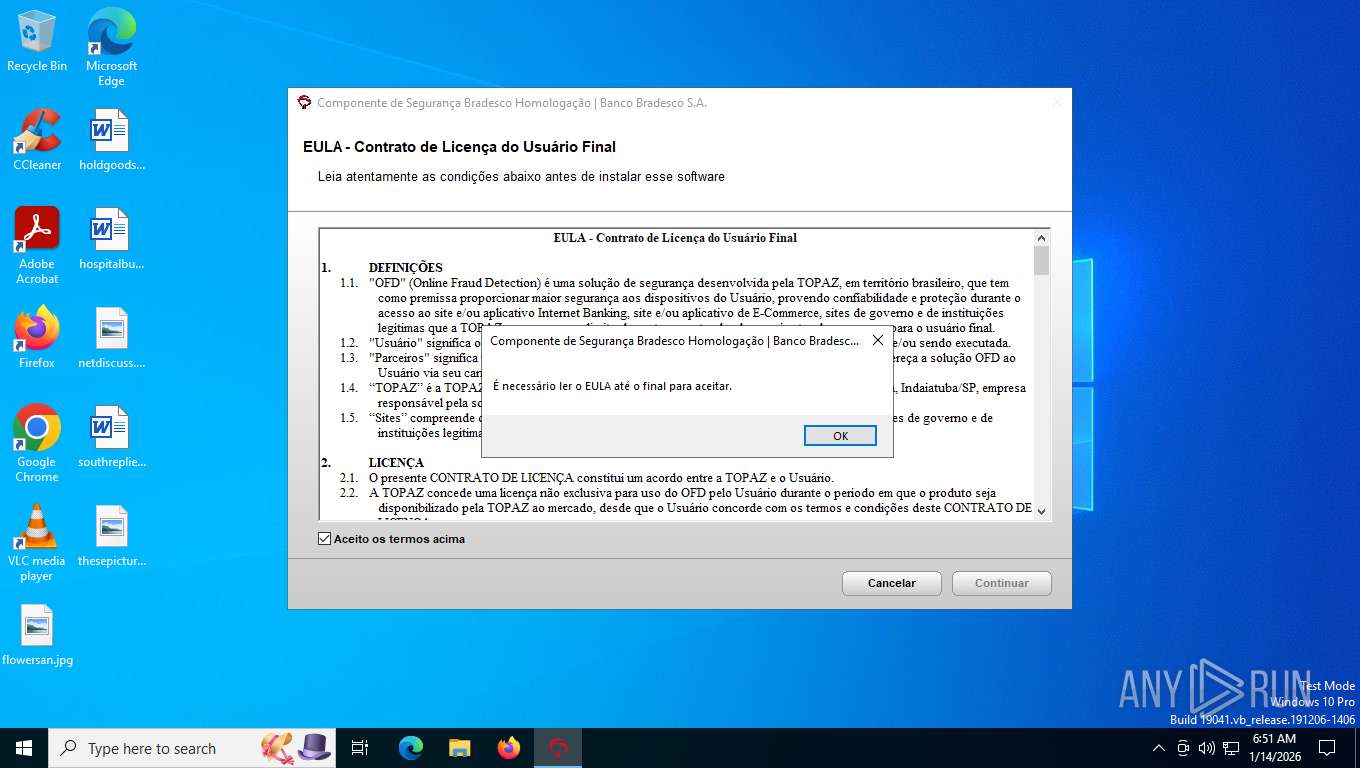
| CompanyName: | Banco Bradesco S.A. |
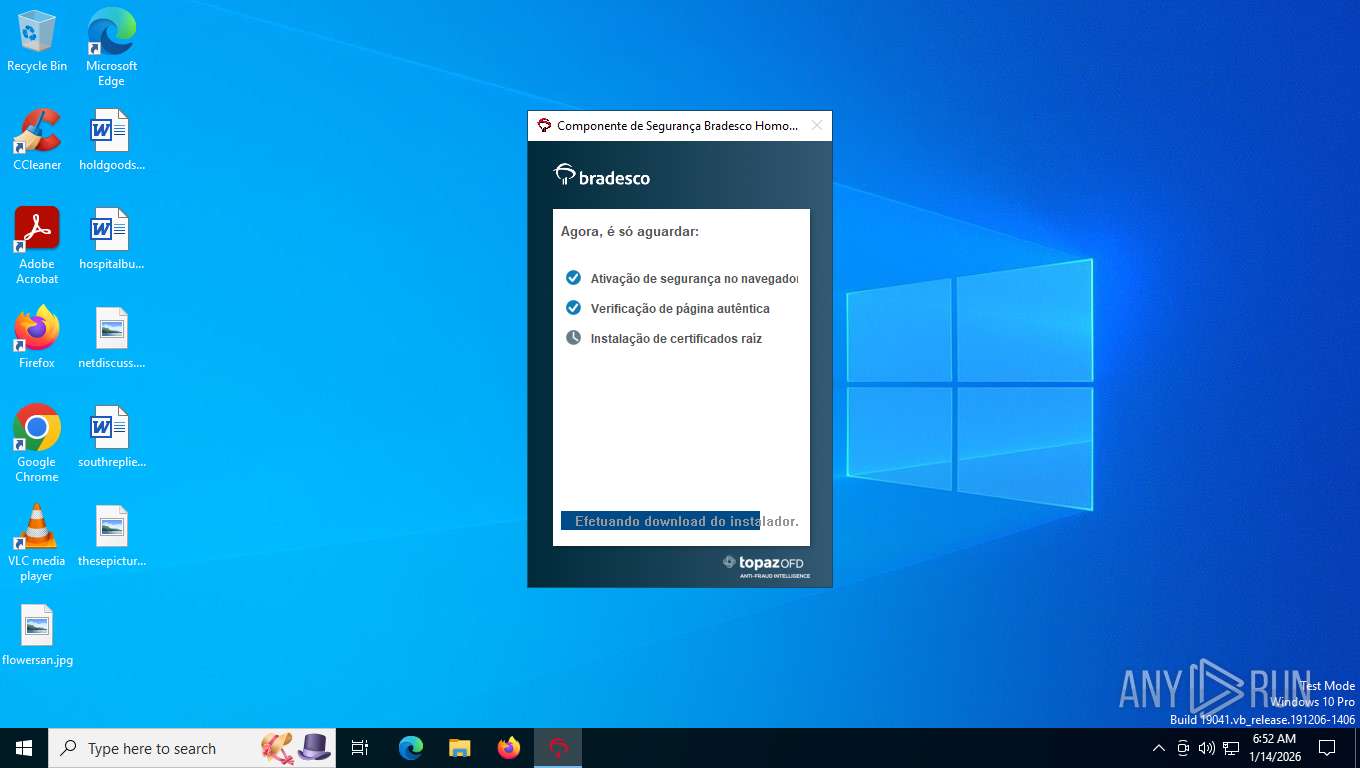
| FileDescription: | Componente de Segurança Bradesco Homologação |
| FileVersion: | 2,17,0,1 |
| InternalName: | Componente de Segurança Bradesco Homologação |
| LegalCopyright: | Copyright © 2025, Bradesco |
| OriginalFileName: | Bradesco_BGSHmg |
| PrivateBuild: | 2,17,0,1 |
| ProductName: | Componente de Segurança Bradesco Homologação |
| ProductVersion: | 2,17,0,1 |
Total processes
171
Monitored processes
27
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2256 | WMIC PROCESS WHERE "ExecutablePath like 'C:\\Program Files\\Topaz OFD\\Warsaw\\%'" DELETE | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3692 | "C:\Program Files\Topaz OFD\Warsaw\wstlcup.exe" | C:\Program Files\Topaz OFD\Warsaw\wstlcup.exe | — | warsaw_setup_64.tmp | |||||||||||
User: SYSTEM Company: Topaz OFD Integrity Level: SYSTEM Description: Topaz OFD - Certificate Updater Exit code: 0 Version: 1.0.0.2 Modules
| |||||||||||||||
| 4020 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4680 | "sc.exe" start "Warsaw Technology" | C:\Windows\System32\sc.exe | — | warsaw_setup_64.tmp | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5520 | C:\ProgramData\Temp\warsaw_setup_64.exe /verysilent /sp- /norestart /suppressmsgboxes /restartexitcode=3010 /nocancel /accepteula /log="C:\ProgramData\Temp\wslog.dat" | C:\ProgramData\Temp\warsaw_setup_64.exe | DiagnosticoBradesco_BGS.exe | ||||||||||||
User: SYSTEM Company: Topaz Integrity Level: SYSTEM Description: Warsaw Version: 2.47.1.5 Modules
| |||||||||||||||
| 6700 | "C:\WINDOWS\TEMP\is-GB6R9.tmp\warsaw_setup_64.tmp" /SL5="$60168,30299937,832512,C:\ProgramData\Temp\warsaw_setup_64.exe" /verysilent /sp- /norestart /suppressmsgboxes /restartexitcode=3010 /nocancel /accepteula /log="C:\ProgramData\Temp\wslog.dat" | C:\Windows\Temp\is-GB6R9.tmp\warsaw_setup_64.tmp | warsaw_setup_64.exe | ||||||||||||
User: SYSTEM Company: Topaz Integrity Level: SYSTEM Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 7216 | "C:\WINDOWS\system32\cmd.exe" /C WMIC PROCESS WHERE "ExecutablePath like 'C:\\Program Files\\Topaz OFD\\%'" DELETE | C:\Windows\System32\cmd.exe | — | warsaw_setup_64.tmp | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7240 | "C:\WINDOWS\TEMP\is-UA275.tmp\get_version.exe" "C:\Program Files\Topaz OFD\Warsaw\features.dat" "C:\WINDOWS\TEMP\is-UA275.tmp\version.txt" | C:\Windows\Temp\is-UA275.tmp\get_version.exe | — | warsaw_setup_64.tmp | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 7244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | get_version.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 660
Read events
20 592
Write events
63
Delete events
5
Modification events
| (PID) Process: | (7504) DiagnosticoBradesco_BGS.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | AutoHelpDesk |
Value: | |||
| (PID) Process: | (8156) DiagnosticoBradesco_BGS.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 128 | |||
| (PID) Process: | (8156) DiagnosticoBradesco_BGS.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 2688 | |||
| (PID) Process: | (7504) DiagnosticoBradesco_BGS.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoHelpDesk |
| Operation: | write | Name: | RebootTasks |
Value: ru5/6bqMudvNi3mNd0UIkQ== | |||
| (PID) Process: | (8156) DiagnosticoBradesco_BGS.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 640 | |||
| (PID) Process: | (7504) DiagnosticoBradesco_BGS.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoHelpDesk |
| Operation: | write | Name: | RebootTasks |
Value: TpselkUloPaU+zG7jQVAJONWiVXcRNT4luXNLl3RLeU= | |||
| (PID) Process: | (8156) DiagnosticoBradesco_BGS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\AutoHelpDesk |
| Operation: | write | Name: | Cert |
Value: 1201666697 | |||
| (PID) Process: | (8156) DiagnosticoBradesco_BGS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\AutoHelpDesk |
| Operation: | write | Name: | Cert |
Value: 1201666697|3381641993|1232833684 | |||
| (PID) Process: | (7504) DiagnosticoBradesco_BGS.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoHelpDesk |
| Operation: | write | Name: | RebootTasks |
Value: TpselkUloPaU+zG7jQVAJCkpiHima3vCSXWI28ZcM6l05iTKJPy9hKToR6rNIFse | |||
| (PID) Process: | (7504) DiagnosticoBradesco_BGS.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoHelpDesk |
| Operation: | write | Name: | RebootTasks |
Value: TpselkUloPaU+zG7jQVAJCkpiHima3vCSXWI28ZcM6noHp6WuRsKsz04e1NwwubVp7Jly70P3dFmrp4E/A7ctQ== | |||
Executable files
840
Suspicious files
46
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6700 | warsaw_setup_64.tmp | C:\Program Files\Topaz OFD\Warsaw:z2fzaw5z | — | |
MD5:— | SHA256:— | |||
| 8156 | DiagnosticoBradesco_BGS.exe | C:\Users\Administrator\NTUSER.DAT | binary | |
MD5:3994CE7E9D73503CE76B391AB81EE2BE | SHA256:1D1F438D4F1C42E2077251D6B6E48D5D0058718D18F9145F0BA31D64240B5379 | |||
| 7504 | DiagnosticoBradesco_BGS.exe | C:\Users\admin\AppData\Local\Temp\Componente de Segurança Bradesco Homologação.log | text | |
MD5:C928A878F6A8106798AF63029E26438D | SHA256:151C4E7CFE506B25F2C9101E6E71F34EE95DB94240208FC5805E41CA65A6109F | |||
| 7504 | DiagnosticoBradesco_BGS.exe | C:\ProgramData\Temp\_cd\5814a70b8d5491f716086e279cc369de.wtcf | binary | |
MD5:78F2FCAA601F2FB4EBC937BA532E7549 | SHA256:552F7BDCF1A7AF9E6CE672017F4F12ABF77240C78E761AC203D1D9D20AC89988 | |||
| 7504 | DiagnosticoBradesco_BGS.exe | C:\ProgramData\Temp\_cd\73a0d72b037f34e3ec212135f8909609.wtcf | binary | |
MD5:87CE0B7B2A0E4900E158719B37A89372 | SHA256:3E9099B5015E8F486C00BCEA9D111EE721FABA355A89BCF1DF69561E3DC6325C | |||
| 7504 | DiagnosticoBradesco_BGS.exe | C:\ProgramData\Temp\cert0.cer | binary | |
MD5:78F2FCAA601F2FB4EBC937BA532E7549 | SHA256:552F7BDCF1A7AF9E6CE672017F4F12ABF77240C78E761AC203D1D9D20AC89988 | |||
| 7504 | DiagnosticoBradesco_BGS.exe | C:\ProgramData\Temp\_cd\.hcd | binary | |
MD5:4EA938930CA9FC7709CAF3C9364E5ED2 | SHA256:B3D27CEC5C66B3E8DC3A77CE426A6C335209BE5F0C29B55FE4EEB09F0F1BC456 | |||
| 7504 | DiagnosticoBradesco_BGS.exe | C:\ProgramData\Temp\cert2.cer | binary | |
MD5:D474DE575C39B2D39C8583C5C065498A | SHA256:7431E5F4C3C1CE4690774F0B61E05440883BA9A01ED00BA6ABD7806ED3B118CF | |||
| 7504 | DiagnosticoBradesco_BGS.exe | C:\ProgramData\Temp\cert1.cer | binary | |
MD5:87CE0B7B2A0E4900E158719B37A89372 | SHA256:3E9099B5015E8F486C00BCEA9D111EE721FABA355A89BCF1DF69561E3DC6325C | |||
| 8156 | DiagnosticoBradesco_BGS.exe | C:\ProgramData\Temp\cert_temp\cert2.cer | binary | |
MD5:D474DE575C39B2D39C8583C5C065498A | SHA256:7431E5F4C3C1CE4690774F0B61E05440883BA9A01ED00BA6ABD7806ED3B118CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
30
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
4508 | svchost.exe | GET | 200 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | text | 1.43 Kb | whitelisted |
6916 | svchost.exe | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
6916 | svchost.exe | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
6392 | SIHClient.exe | GET | 200 | 20.3.187.198:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
6916 | svchost.exe | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
6392 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
6392 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WaaS/FeatureManagement?IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&CurrentBranch=vb_release&AccountFirstChar=&ActivationChannel=Retail&OEMModel=DELL&FlightRing=Retail&AttrDataVer=186&InstallLanguage=en-US&OSUILocale=en-US&WebExperience=1&FlightingBranchName=&ChassisTypeId=1&OSSkuId=48&App=CDM&InstallDate=1661339444&AppVer=&OSArchitecture=AMD64&DefaultUserRegion=244&TelemetryLevel=1&OSVersion=10.0.19045.4046&DeviceFamily=Windows.Desktop | unknown | text | 34.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4508 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1136 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4508 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4508 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
4508 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dn.dnofd.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |