| URL: | elgoog.im |
| Full analysis: | https://app.any.run/tasks/1793f27b-760f-4d6d-a190-fa8bb2ad5d78 |
| Verdict: | Malicious activity |
| Analysis date: | December 17, 2023, 16:23:09 |
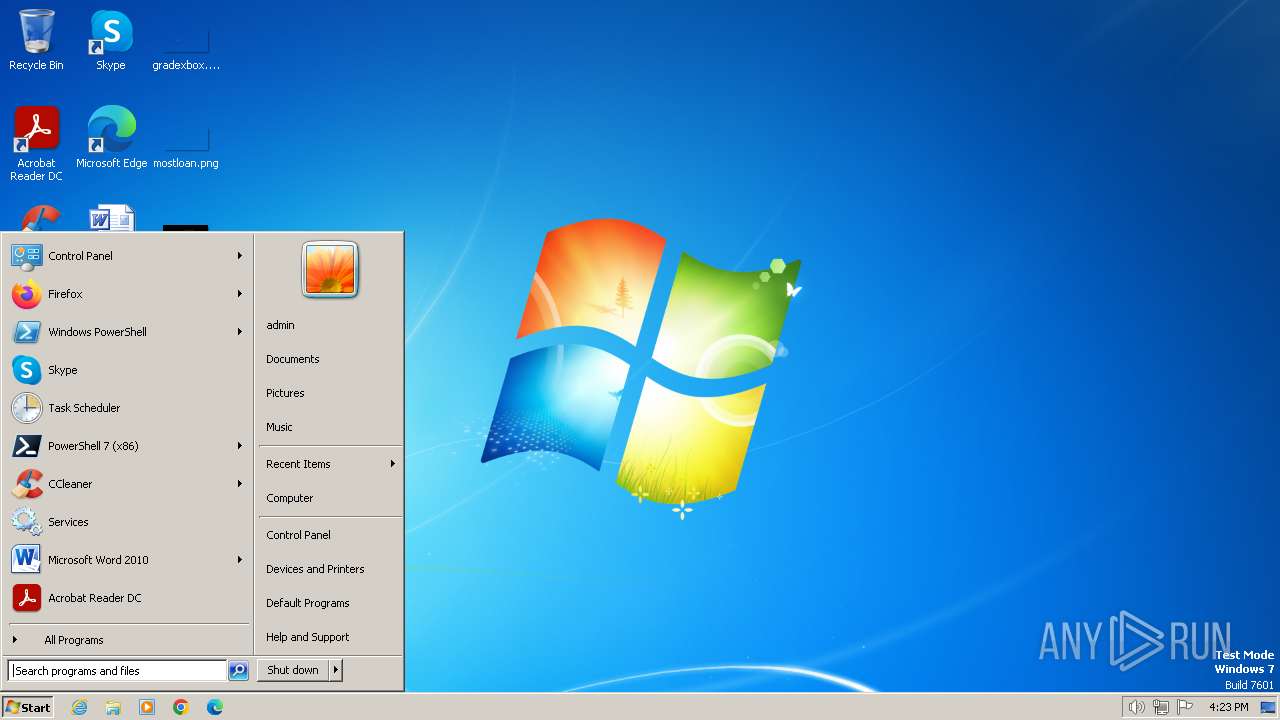
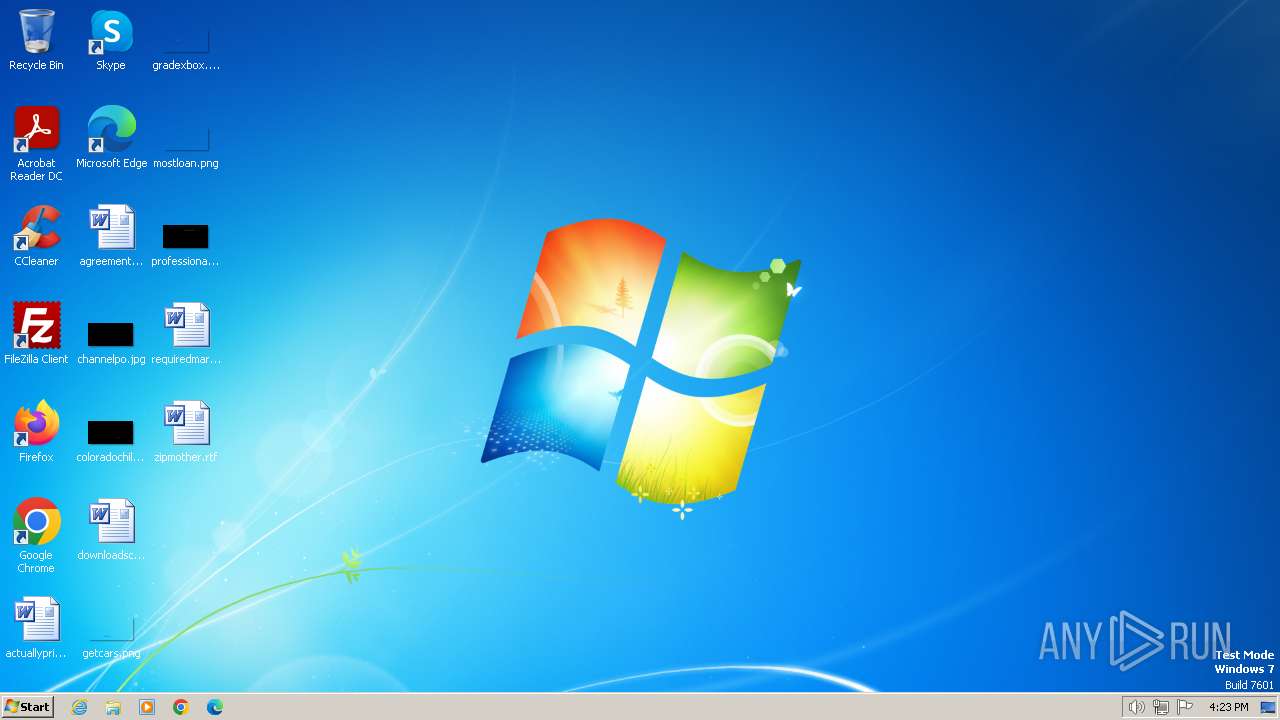
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2A97C05933A0CEC0C9E2AB7A57EA3795 |
| SHA1: | 17A87443395864AAC25C5C7D12611E1260AC6C73 |
| SHA256: | 98BC598A89DD596D8347710BC741B8E5C91D0BA784A79EBF23AB0A75B28ABD39 |
| SSDEEP: | 3:skI:skI |
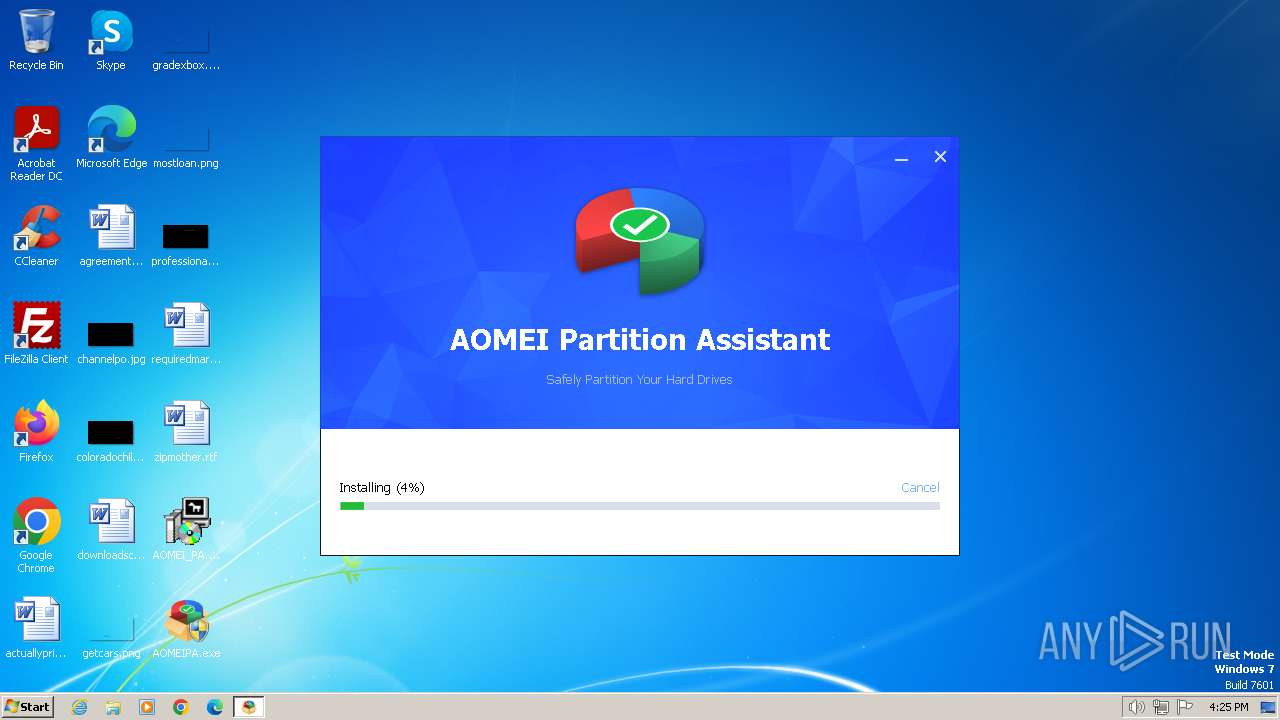
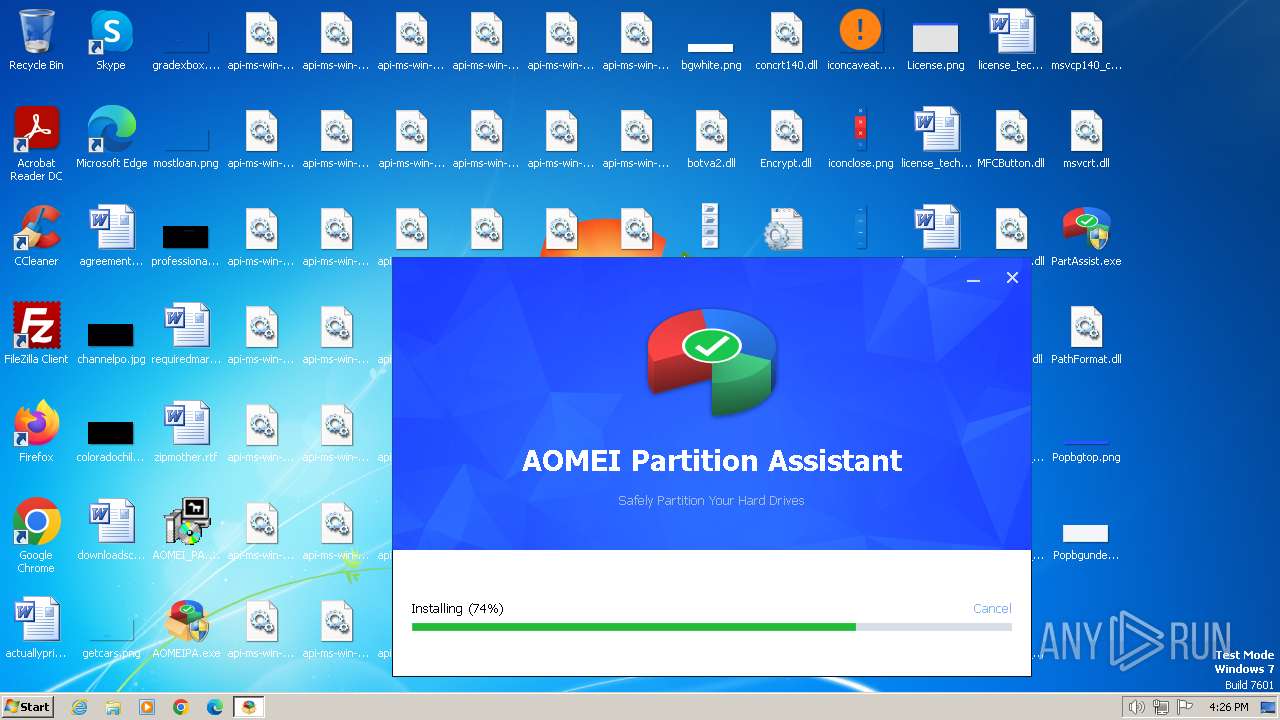
MALICIOUS
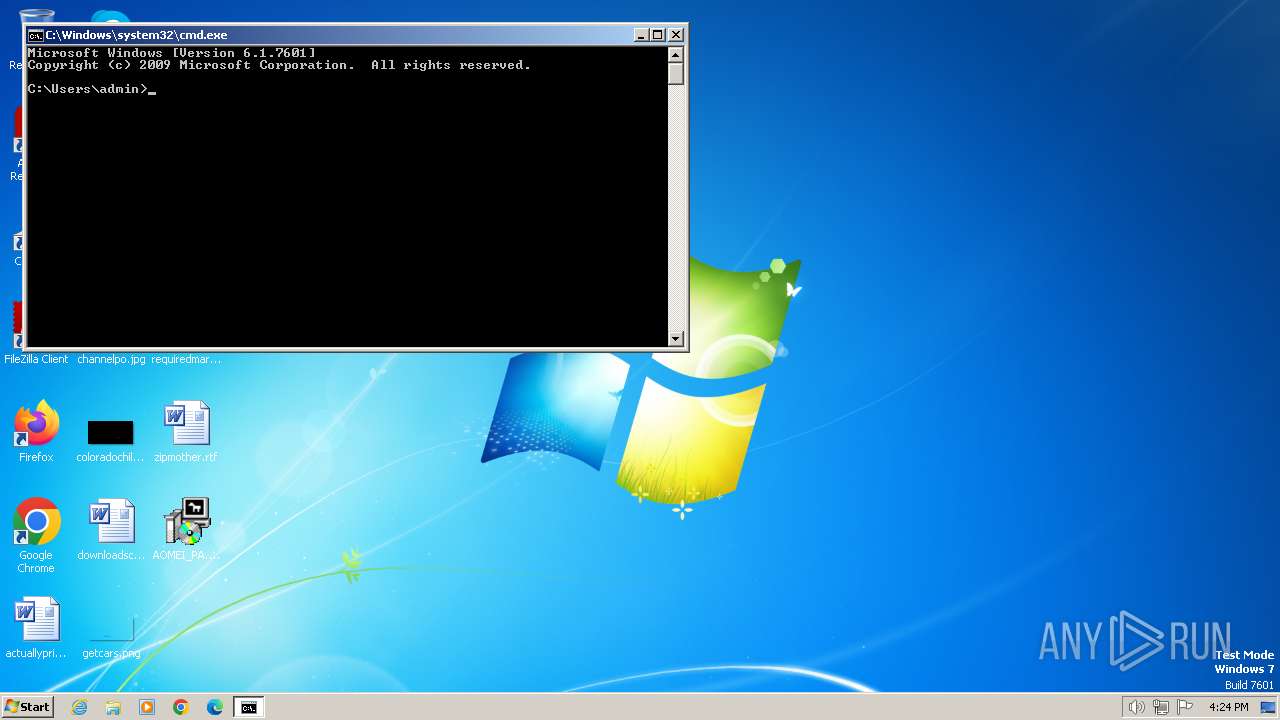
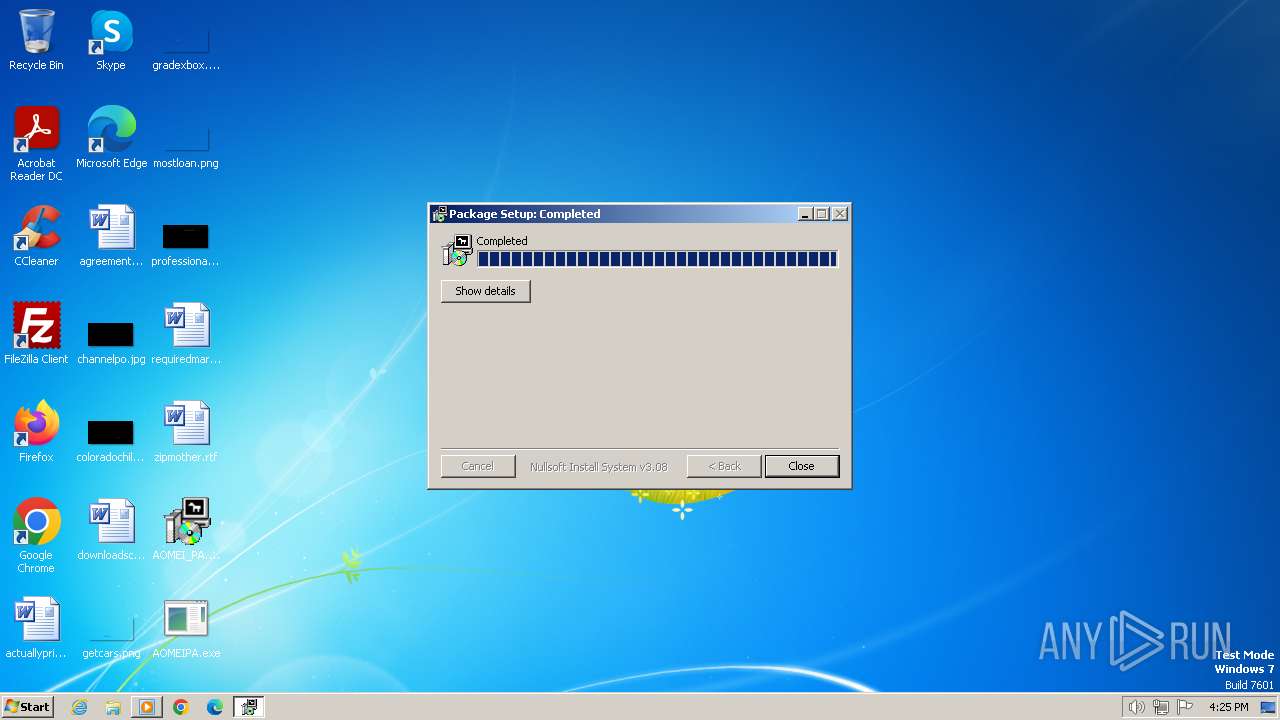
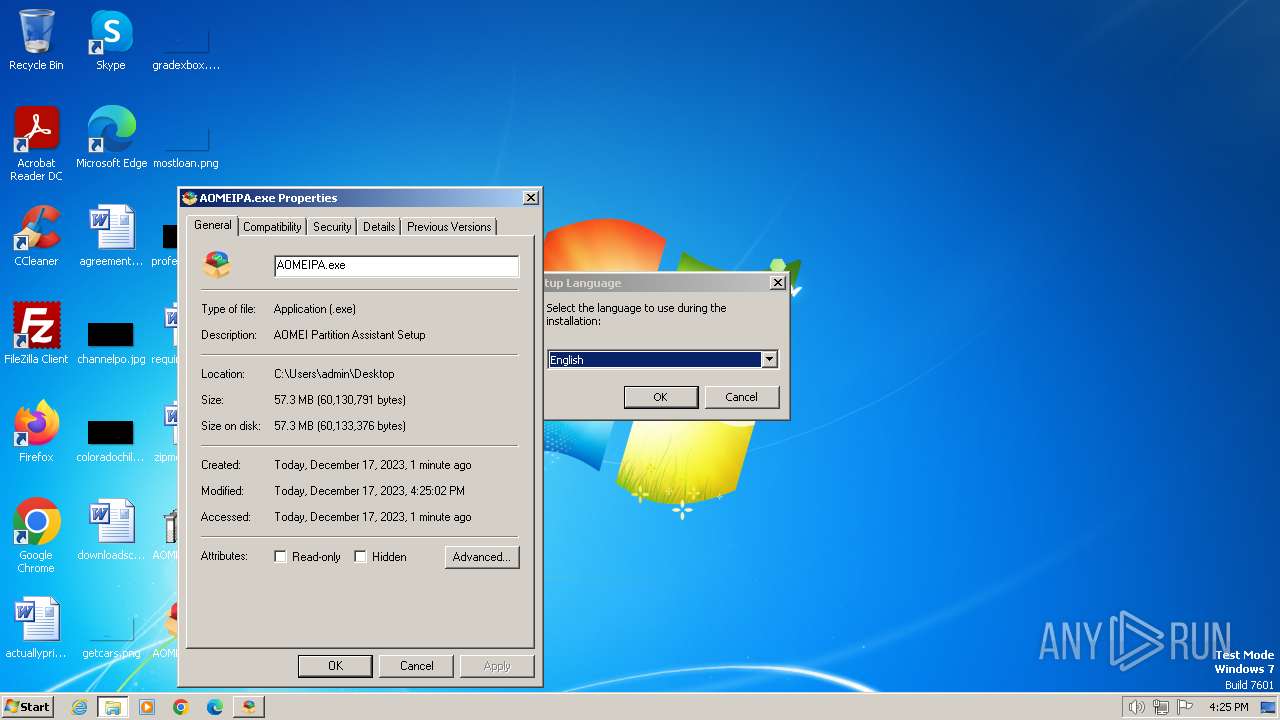
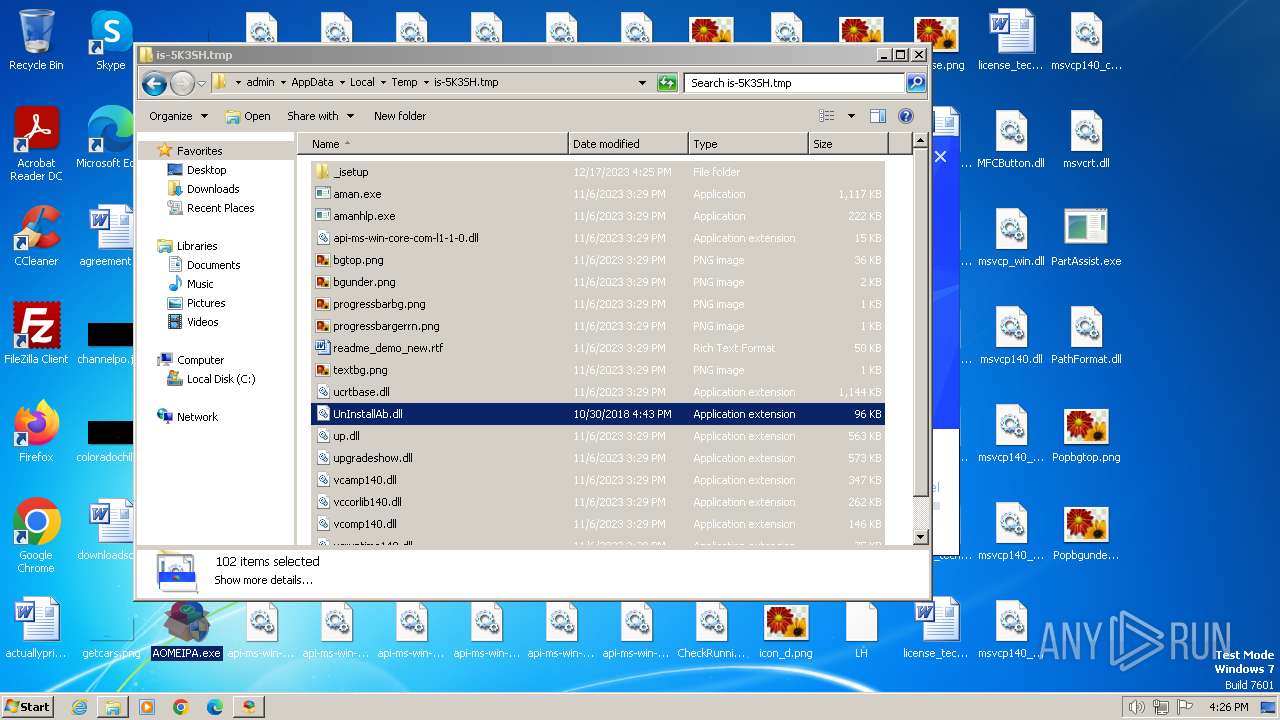
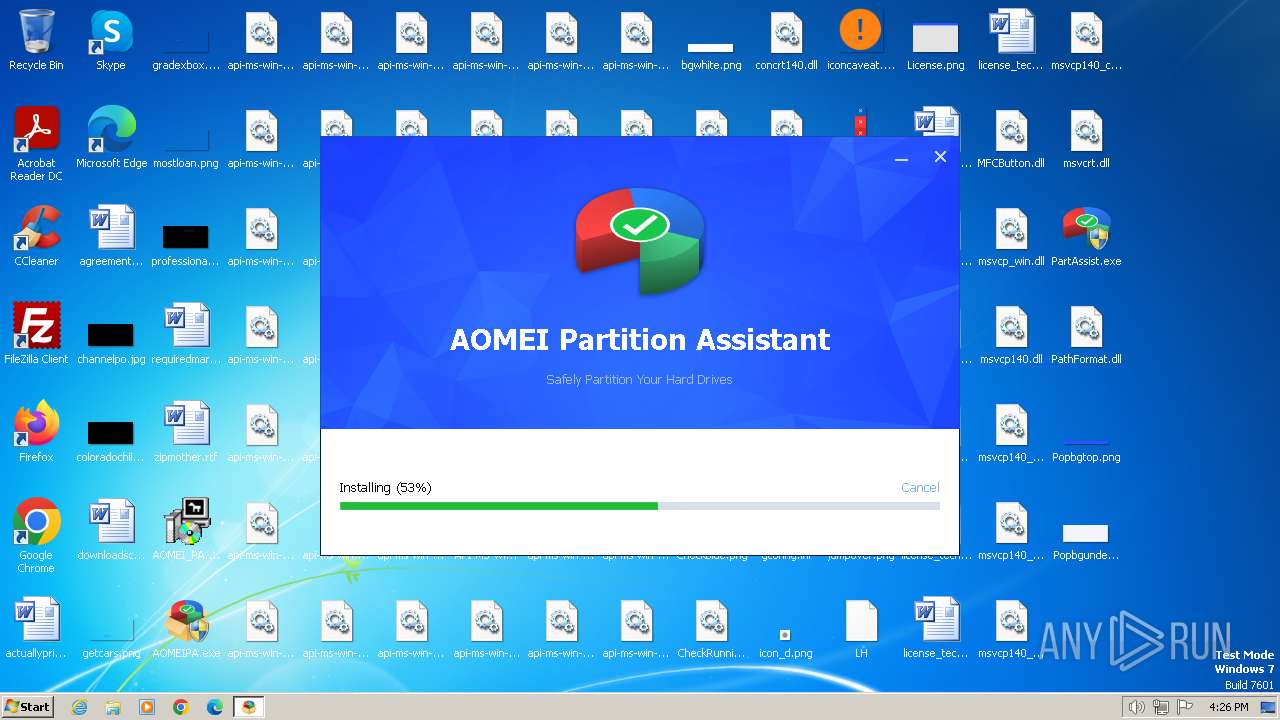
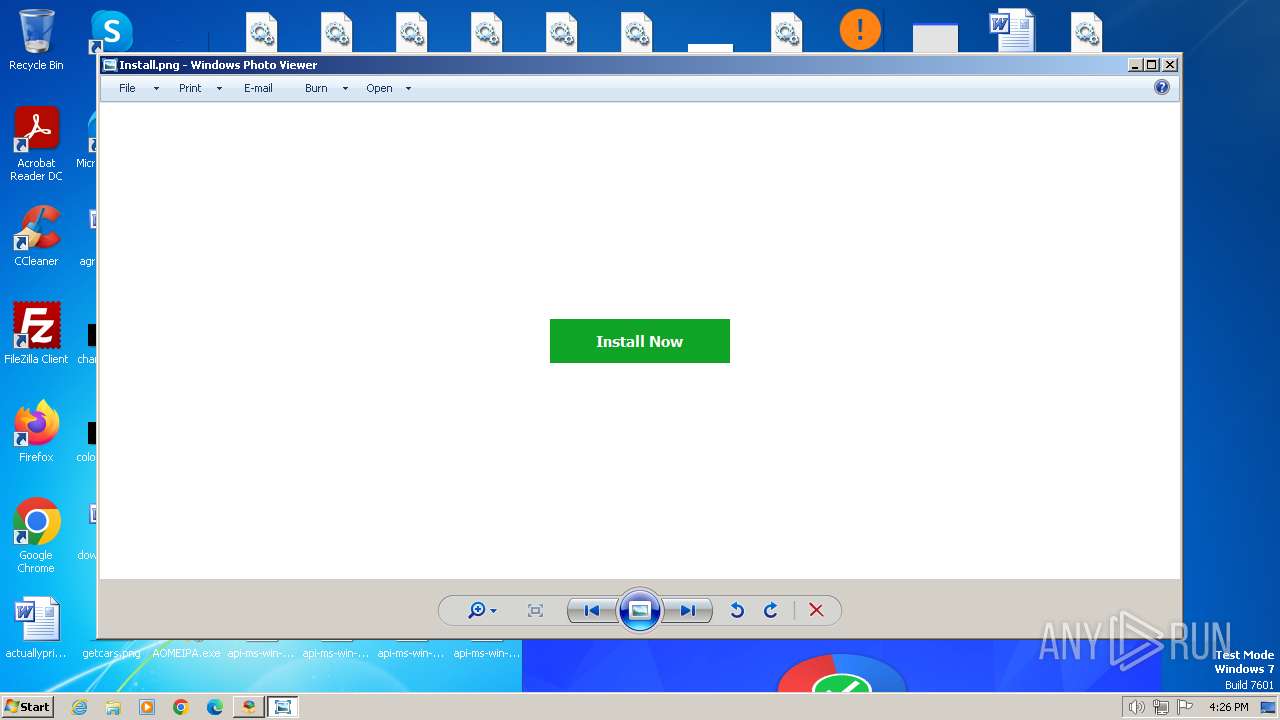
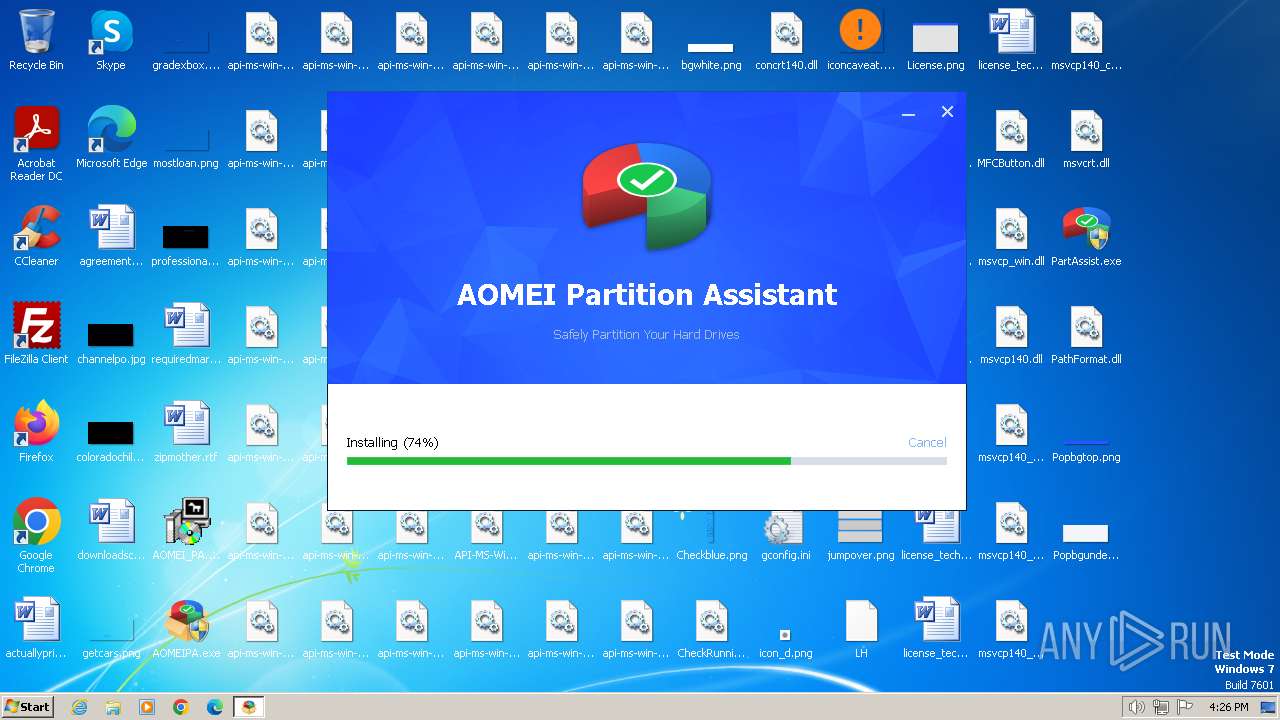
Drops the executable file immediately after the start
- AOMEI_PA.exe (PID: 2732)
- AOMEIPA.exe (PID: 3016)
- TechOrig.exe (PID: 3124)
- TechOrig.tmp (PID: 1124)
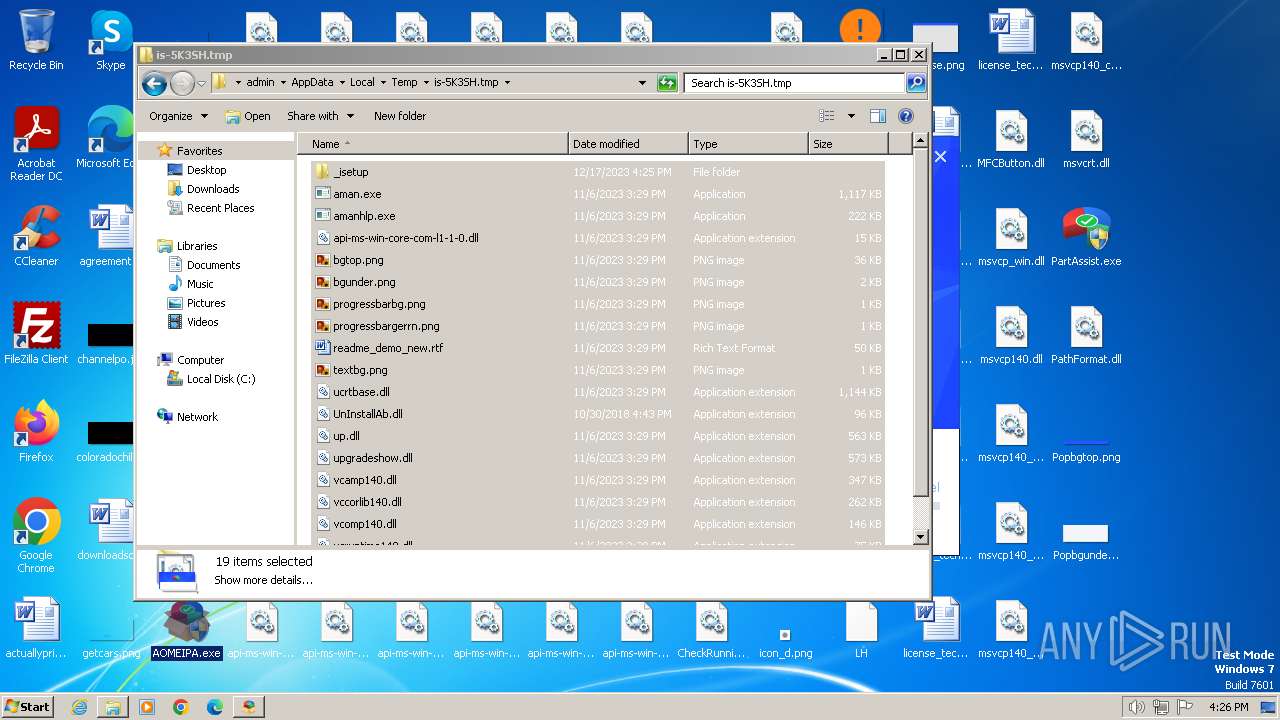
Creates a writable file in the system directory
- TechOrig.tmp (PID: 1124)
Actions looks like stealing of personal data
- aman.exe (PID: 604)
SUSPICIOUS
Reads settings of System Certificates
- AOMEI_PA.exe (PID: 2732)
- GaHlp.exe (PID: 3768)
Reads security settings of Internet Explorer
- AOMEI_PA.exe (PID: 2732)
Checks Windows Trust Settings
- AOMEI_PA.exe (PID: 2732)
Reads the Internet Settings
- AOMEI_PA.exe (PID: 2732)
- TechOrig.tmp (PID: 1124)
Process drops legitimate windows executable
- TechOrig.tmp (PID: 1124)
Reads the Windows owner or organization settings
- TechOrig.tmp (PID: 1124)
The process drops C-runtime libraries
- TechOrig.tmp (PID: 1124)
Uses NETSH.EXE to add a firewall rule or allowed programs
- hstart.exe (PID: 2752)
- hstart.exe (PID: 2944)
Drops 7-zip archiver for unpacking
- TechOrig.tmp (PID: 1124)
Drops a system driver (possible attempt to evade defenses)
- TechOrig.tmp (PID: 1124)
INFO
Checks proxy server information
- AOMEI_PA.exe (PID: 2732)
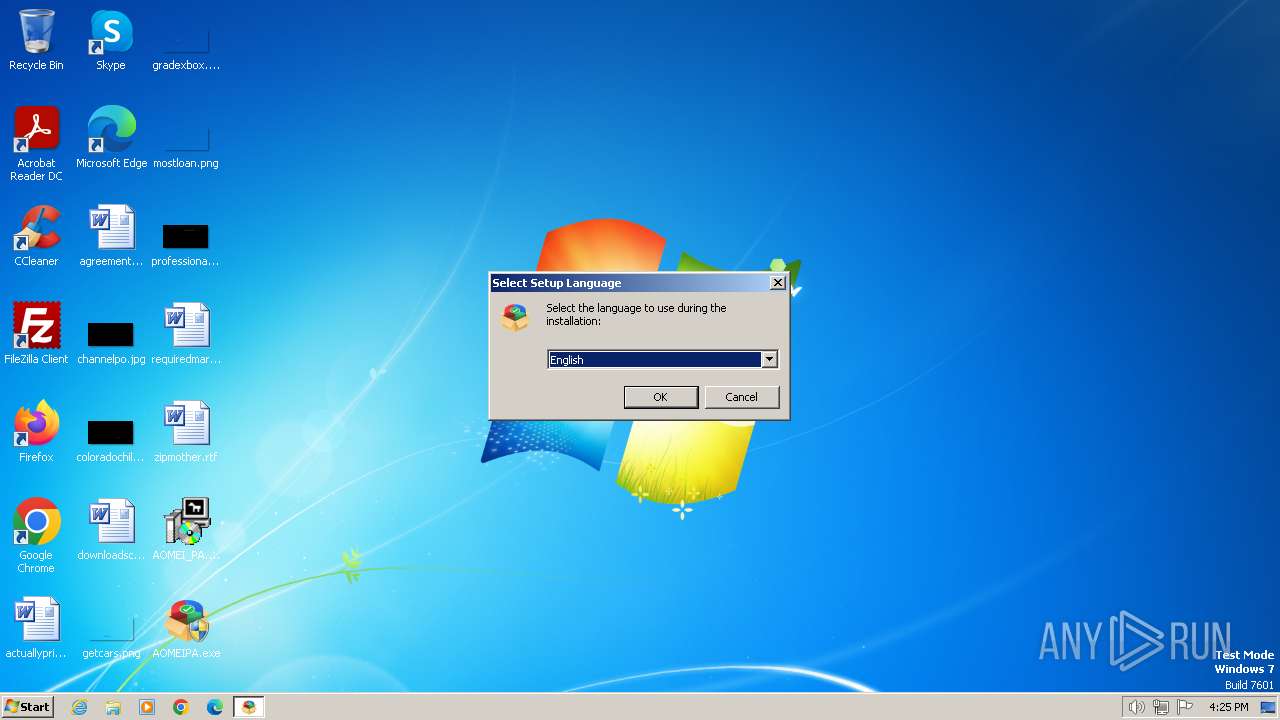
Checks supported languages
- AOMEI_PA.exe (PID: 2732)
- AOMEIPA.exe (PID: 3016)
- TechOrig.tmp (PID: 1124)
- aman.exe (PID: 604)
- hstart.exe (PID: 2944)
- hstart.exe (PID: 2752)
- TechOrig.exe (PID: 3124)
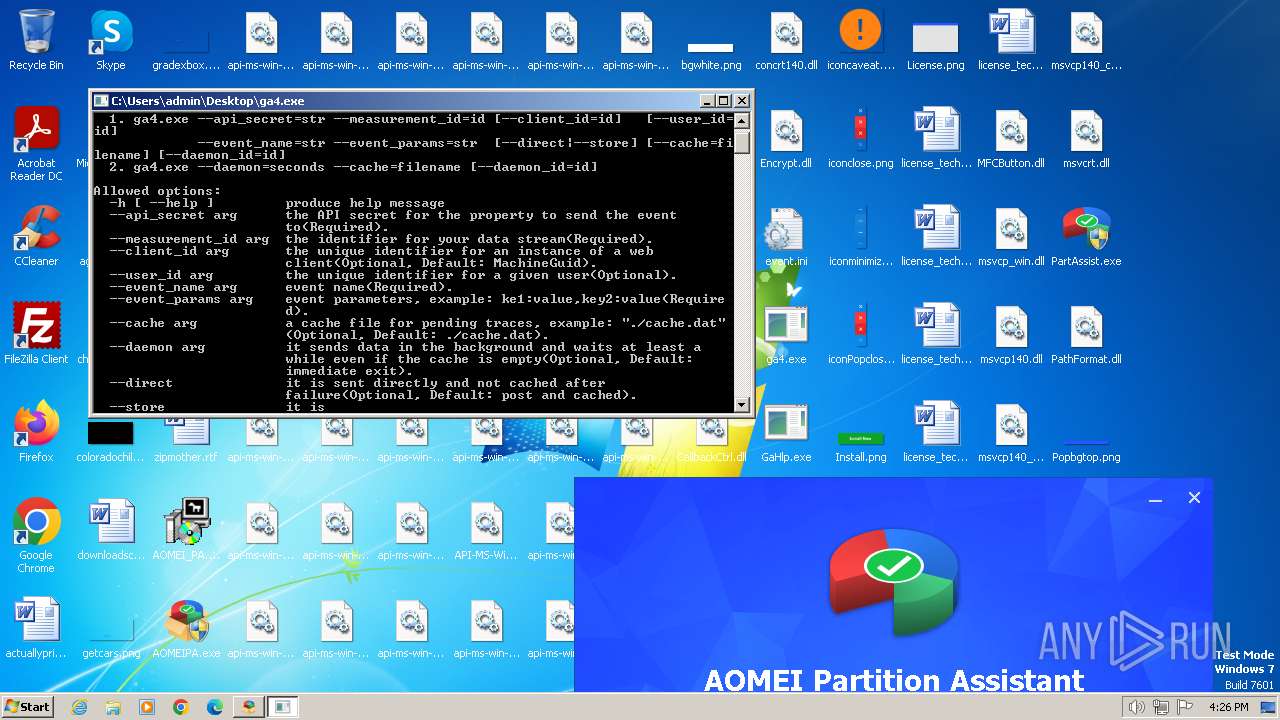
- ga4.exe (PID: 3864)
- GaHlp.exe (PID: 3768)
- loaddrv.exe (PID: 2244)
- loaddrv.exe (PID: 1796)
- loaddrv.exe (PID: 2644)
- loaddrv.exe (PID: 2628)
Reads the computer name
- AOMEI_PA.exe (PID: 2732)
- AOMEIPA.exe (PID: 3016)
- TechOrig.tmp (PID: 1124)
- GaHlp.exe (PID: 3768)
- loaddrv.exe (PID: 2244)
- loaddrv.exe (PID: 1796)
- loaddrv.exe (PID: 2644)
- loaddrv.exe (PID: 2628)
Reads the machine GUID from the registry
- AOMEI_PA.exe (PID: 2732)
- GaHlp.exe (PID: 3768)
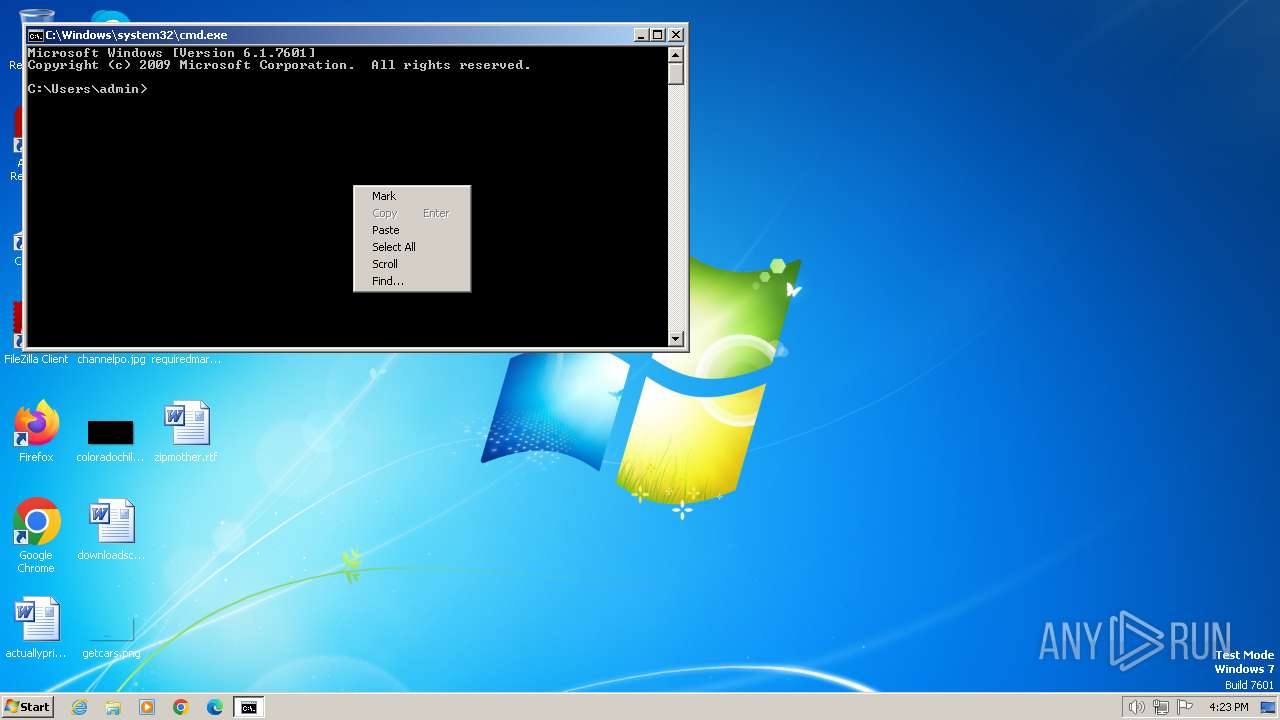
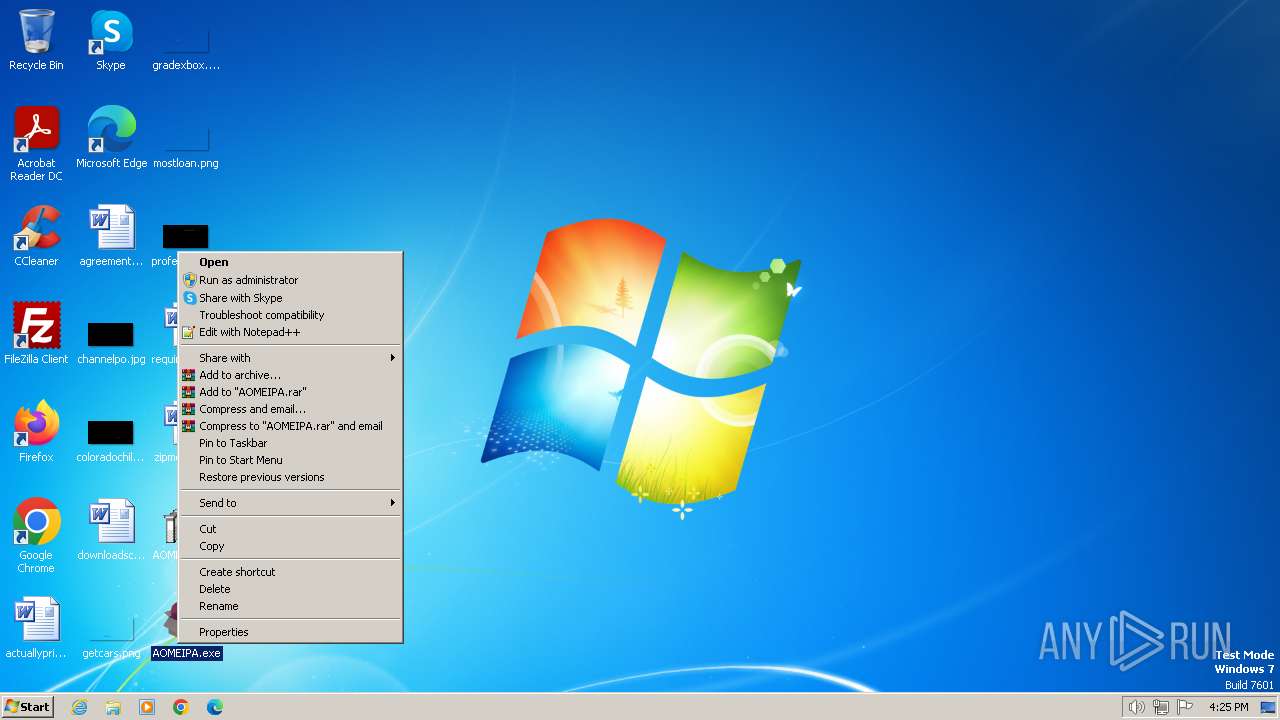
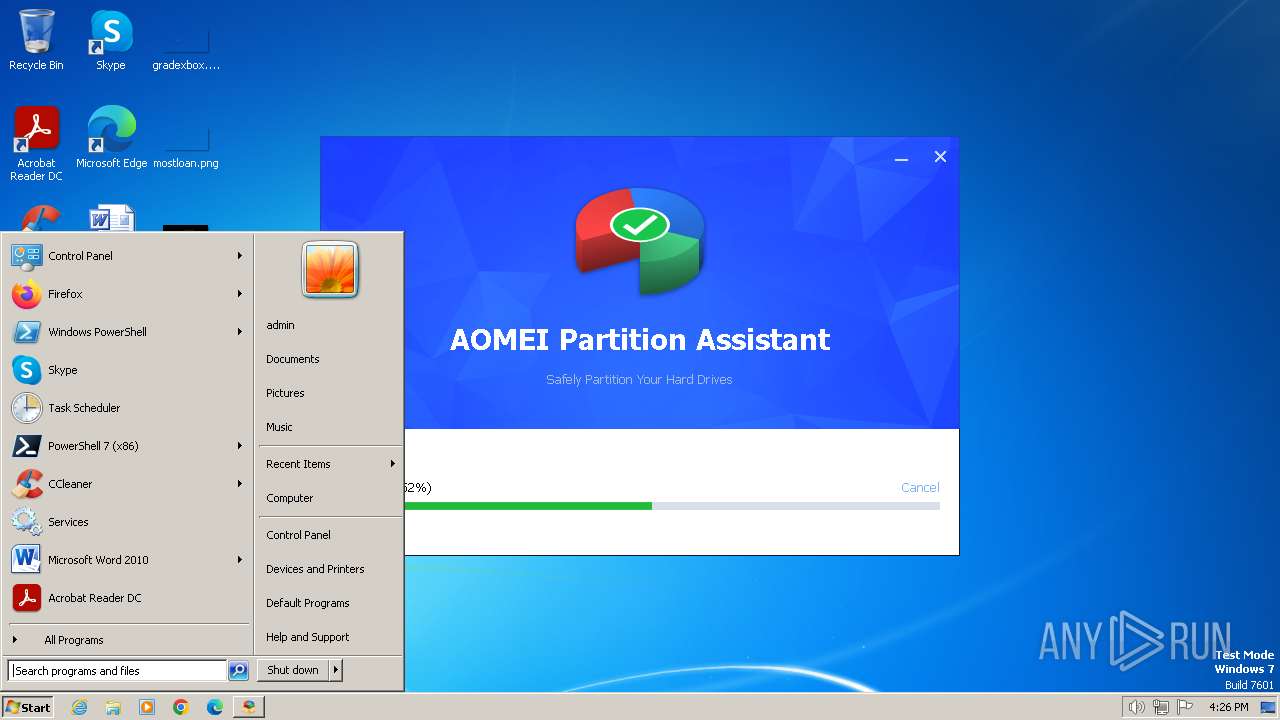
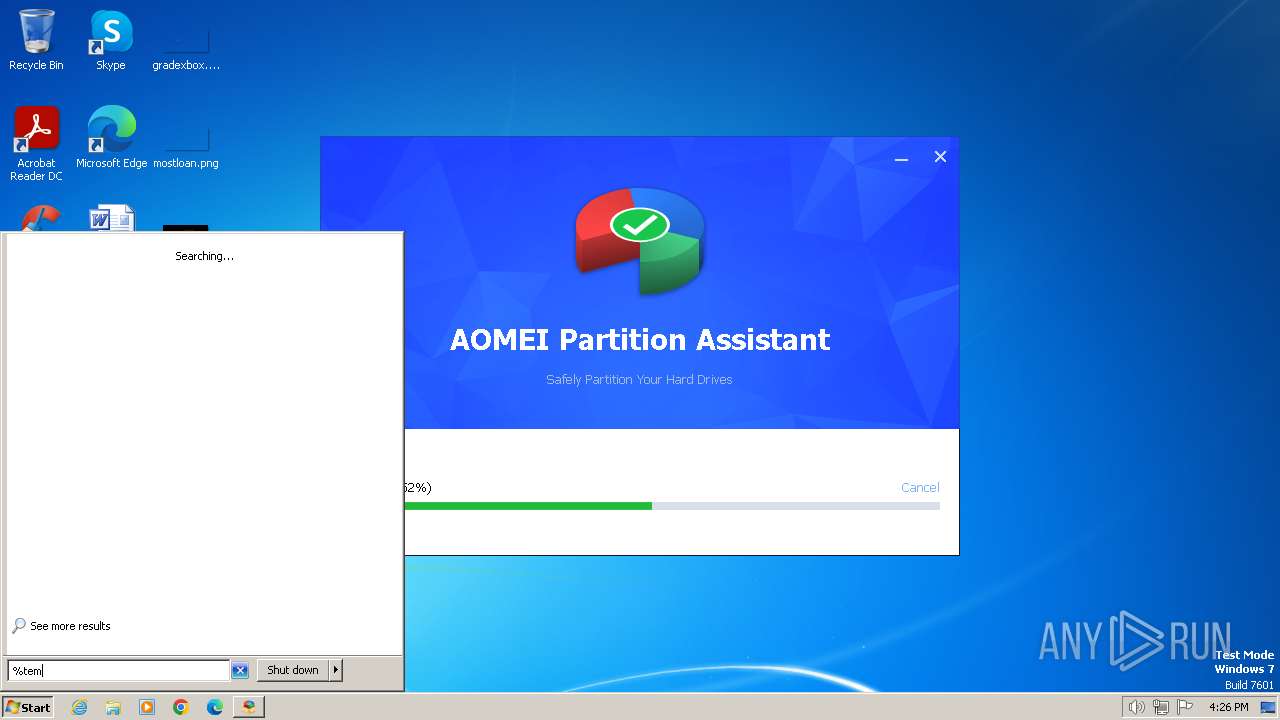
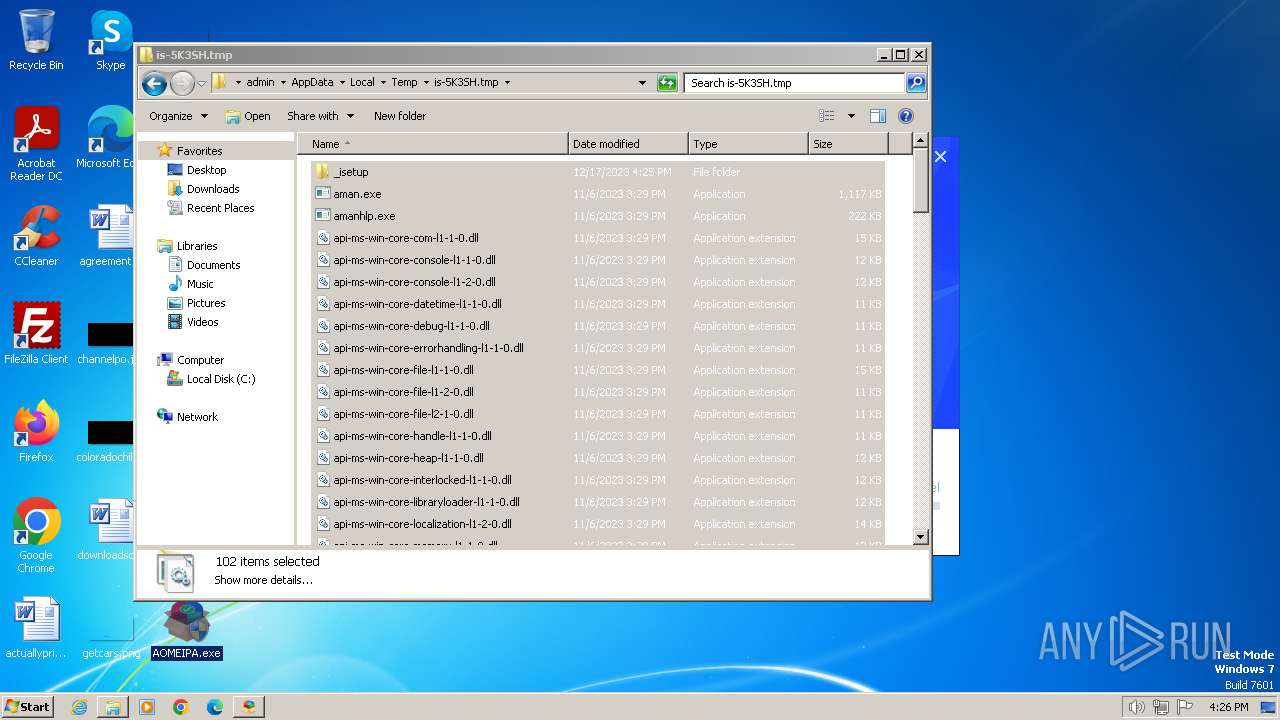
Manual execution by a user
- cmd.exe (PID: 1572)
- AOMEI_PA.exe (PID: 2732)
- AOMEIPA.exe (PID: 2852)
- AOMEIPA.exe (PID: 3016)
- verclsid.exe (PID: 3352)
- ga4.exe (PID: 3864)
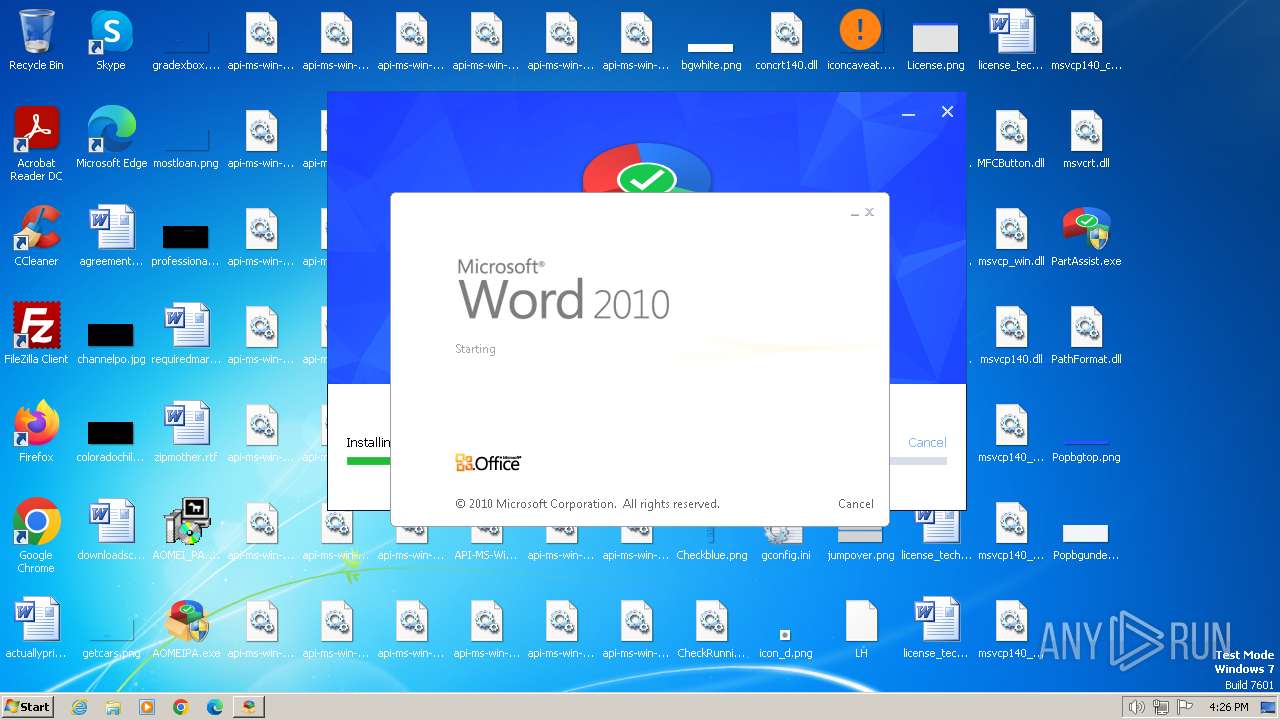
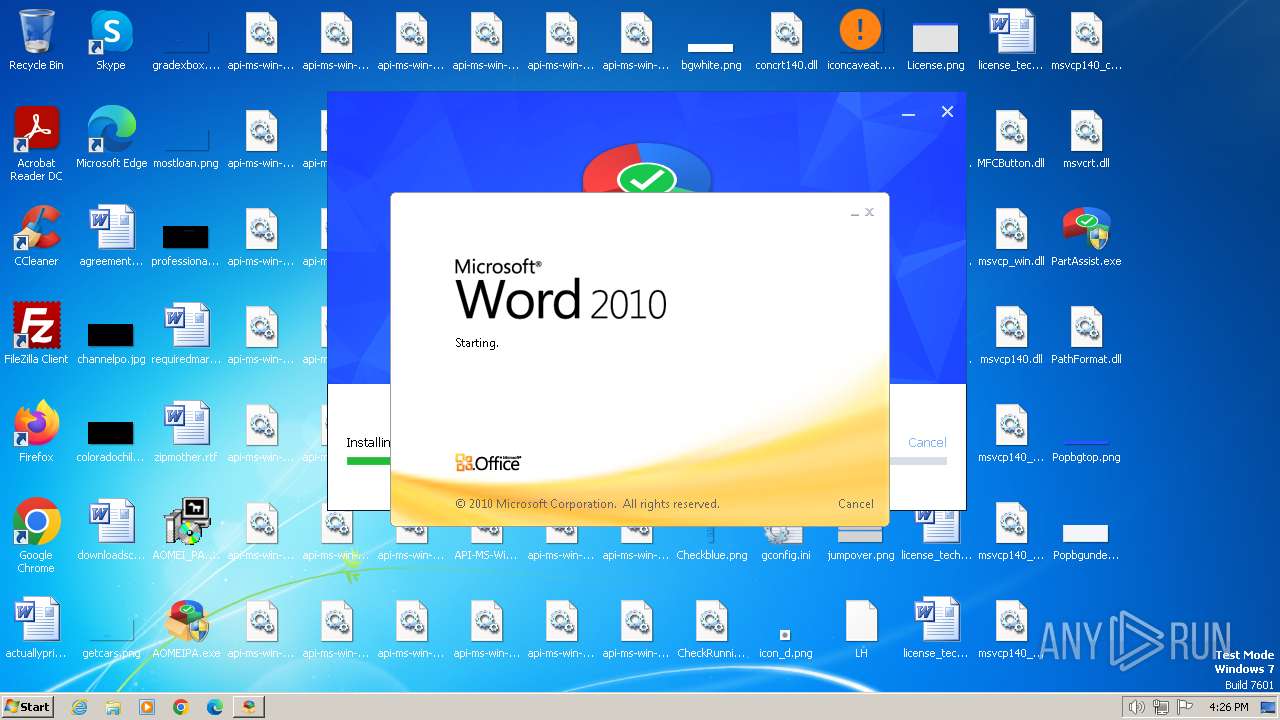
- WINWORD.EXE (PID: 2248)
- GaHlp.exe (PID: 3768)
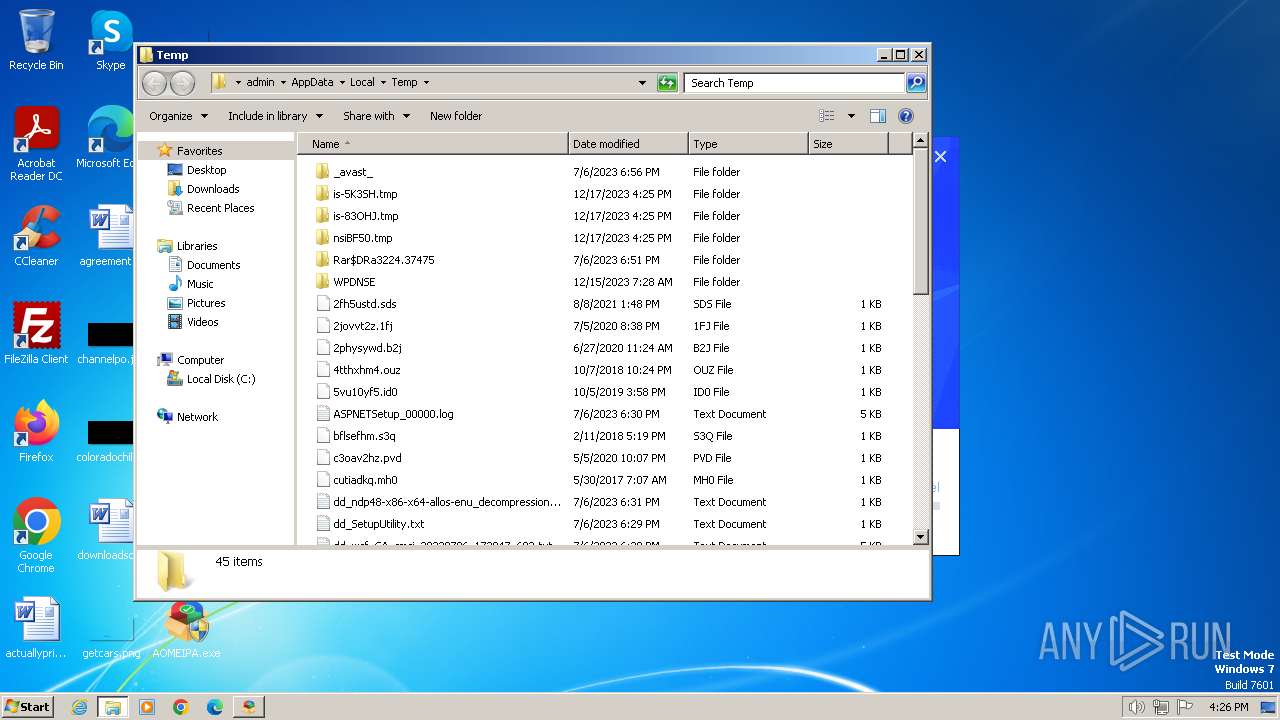
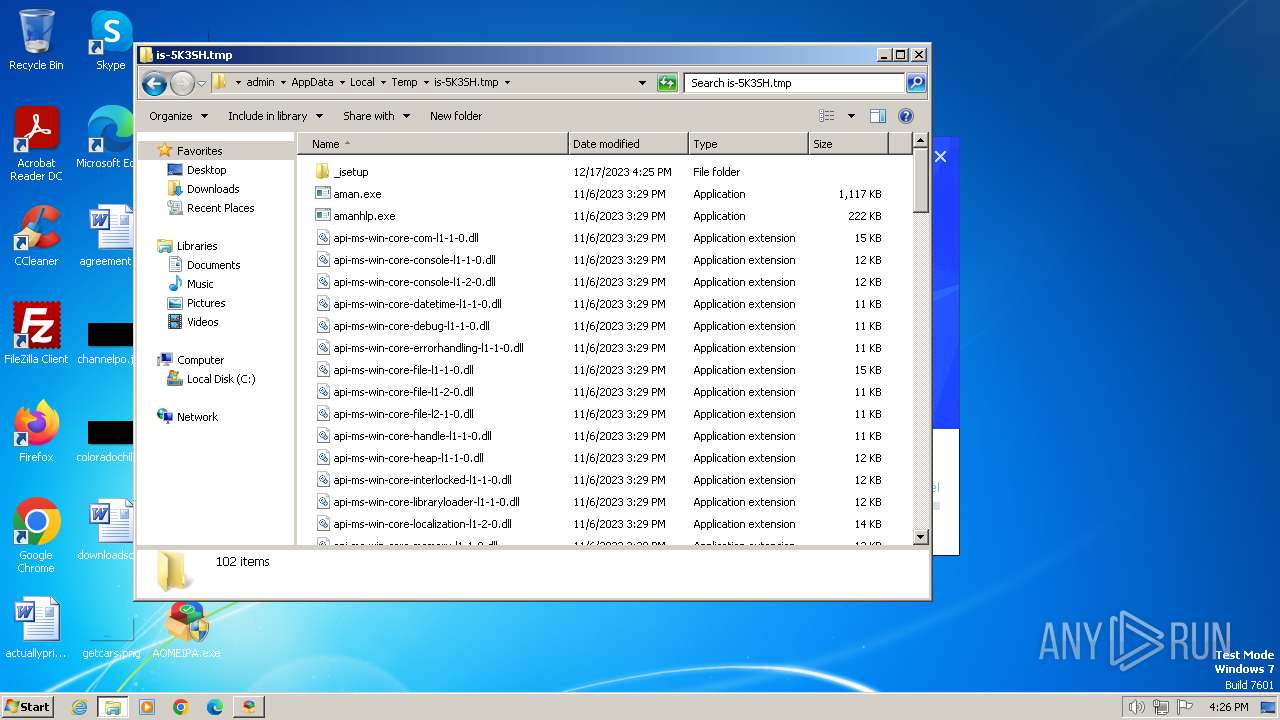
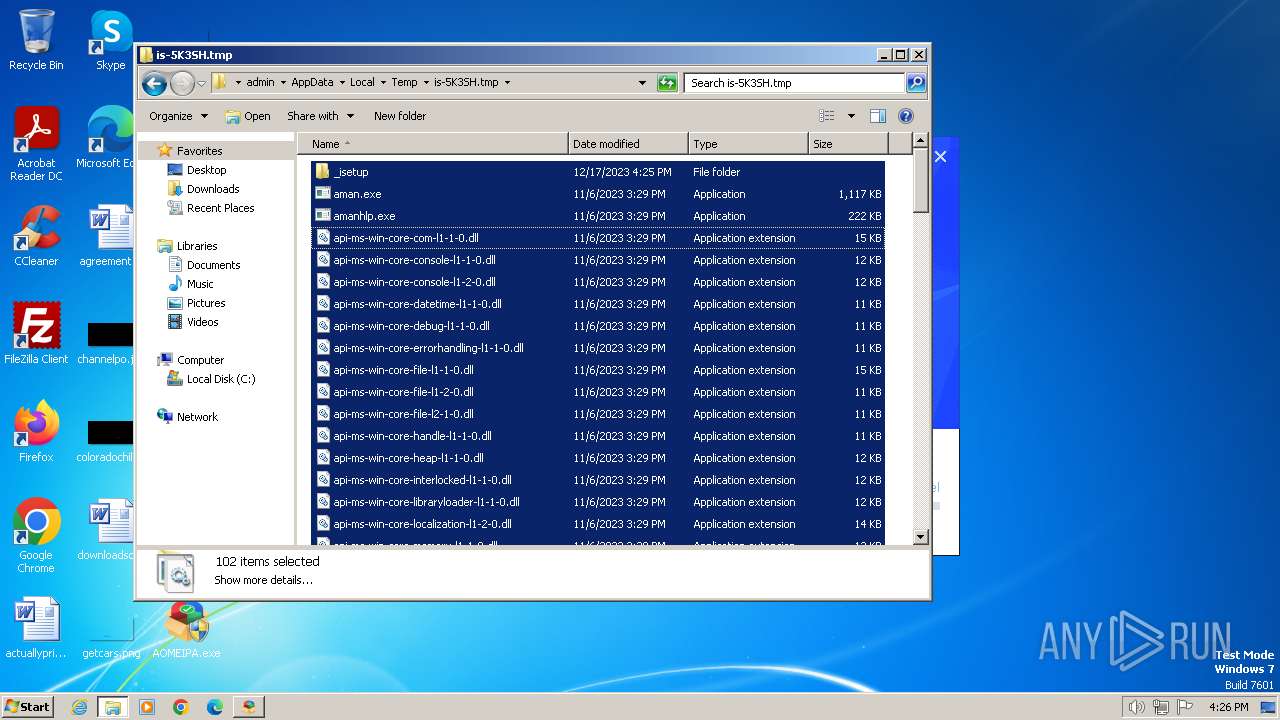
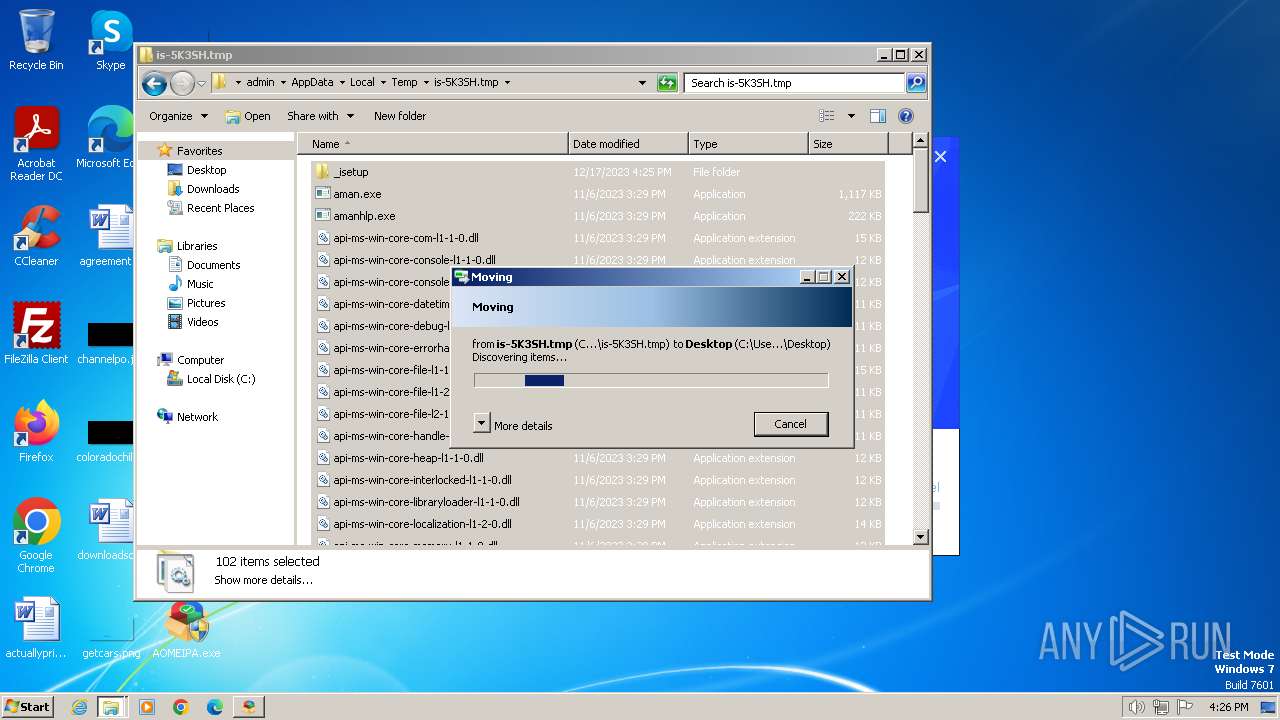
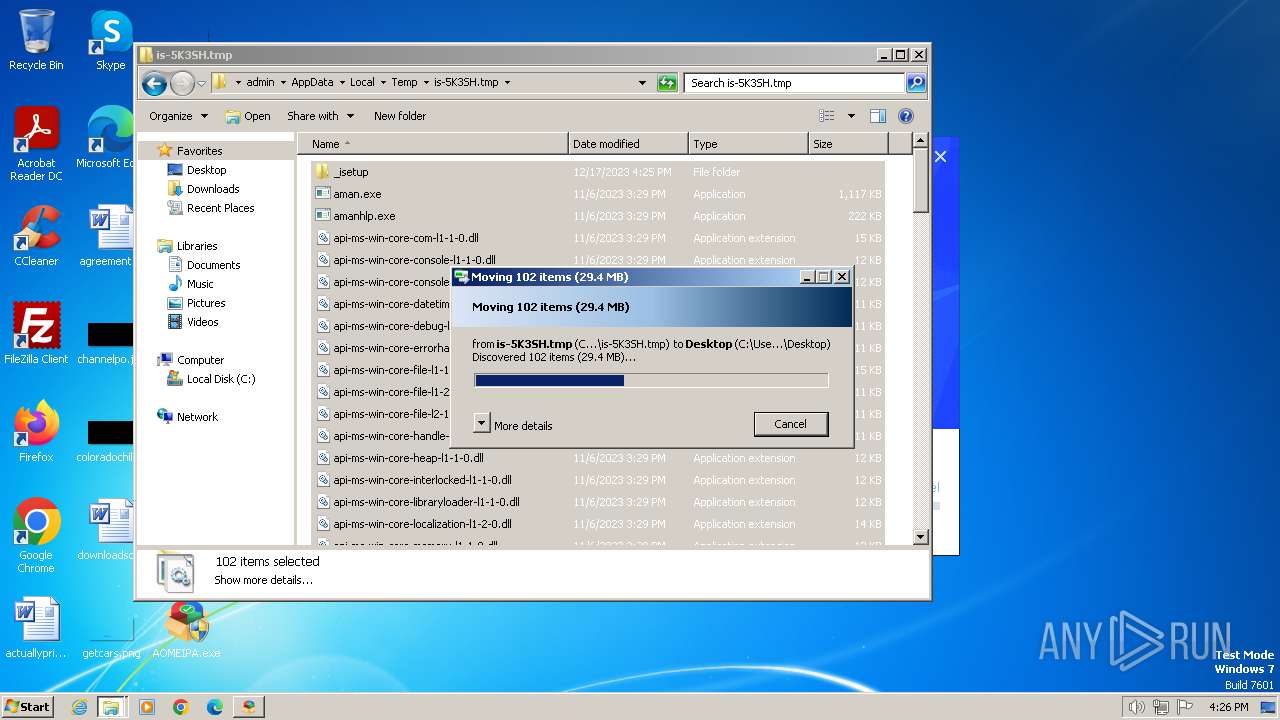
Create files in a temporary directory
- AOMEI_PA.exe (PID: 2732)
- AOMEIPA.exe (PID: 3016)
- TechOrig.exe (PID: 3124)
- TechOrig.tmp (PID: 1124)
Application launched itself
- chrome.exe (PID: 128)
Creates files or folders in the user directory
- AOMEI_PA.exe (PID: 2732)
- aman.exe (PID: 604)
Creates files in the program directory
- aman.exe (PID: 604)
- TechOrig.tmp (PID: 1124)
Reads Environment values
- GaHlp.exe (PID: 3768)
Reads product name
- GaHlp.exe (PID: 3768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
30
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "elgoog.im" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1048 --field-trial-handle=1172,i,10883338599166317368,12998740964255942869,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 604 | "C:\Users\admin\AppData\Local\Temp\is-5K3SH.tmp\aman.exe" -Cookies | C:\Users\admin\AppData\Local\Temp\is-5K3SH.tmp\aman.exe | TechOrig.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1268 --field-trial-handle=1172,i,10883338599166317368,12998740964255942869,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1460 --field-trial-handle=1172,i,10883338599166317368,12998740964255942869,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1028 | netsh.exe advfirewall firewall add rule name="AOMEI PA Blocker (x86)" dir=out action=block program="%programfiles%\AOMEI Partition Assistant\PartAssist.exe" enable=yes | C:\Windows\System32\netsh.exe | — | hstart.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e558b38,0x6e558b48,0x6e558b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1124 | "C:\Users\admin\AppData\Local\Temp\is-83OHJ.tmp\TechOrig.tmp" /SL5="$2015C,59811911,619008,C:\Users\admin\AppData\Local\Temp\nsiBF50.tmp\AOMEIPA\MAININST\TechOrig.exe" | C:\Users\admin\AppData\Local\Temp\is-83OHJ.tmp\TechOrig.tmp | — | TechOrig.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1572 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1796 | "C:\Program Files\AOMEI Partition Assistant\ddm\loaddrv.exe" | C:\Program Files\AOMEI Partition Assistant\ddm\loaddrv.exe | TechOrig.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
13 453
Read events
12 834
Write events
481
Delete events
138
Modification events
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
534
Suspicious files
82
Text files
1 040
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe1597.TMP | — | |
MD5:— | SHA256:— | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe1b25.TMP | — | |
MD5:— | SHA256:— | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe15b6.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
28
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2732 | AOMEI_PA.exe | GET | 200 | 95.101.54.195:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgO3gm2F4pJBL5SmZb2cuYymjg%3D%3D | unknown | binary | 503 b | unknown |
2732 | AOMEI_PA.exe | GET | 200 | 23.201.254.55:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2732 | AOMEI_PA.exe | GET | 200 | 2.16.100.177:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e9719bd77e611492 | unknown | compressed | 65.2 Kb | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a414549a770d7263 | unknown | — | — | unknown |
2732 | AOMEI_PA.exe | GET | 200 | 2.16.100.177:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b8cc33aa6bc3fb9a | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
128 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
668 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
668 | chrome.exe | 104.21.39.158:443 | elgoog.im | CLOUDFLARENET | — | unknown |
668 | chrome.exe | 142.250.185.138:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
668 | chrome.exe | 142.250.185.232:443 | www.googletagmanager.com | GOOGLE | US | unknown |
668 | chrome.exe | 151.101.193.44:443 | cdn.taboola.com | FASTLY | US | unknown |
668 | chrome.exe | 216.239.34.36:443 | region1.analytics.google.com | GOOGLE | US | unknown |
668 | chrome.exe | 142.250.185.99:443 | www.google.de | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
elgoog.im |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdn.taboola.com |
| whitelisted |
region1.analytics.google.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.de |
| whitelisted |
www.google.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
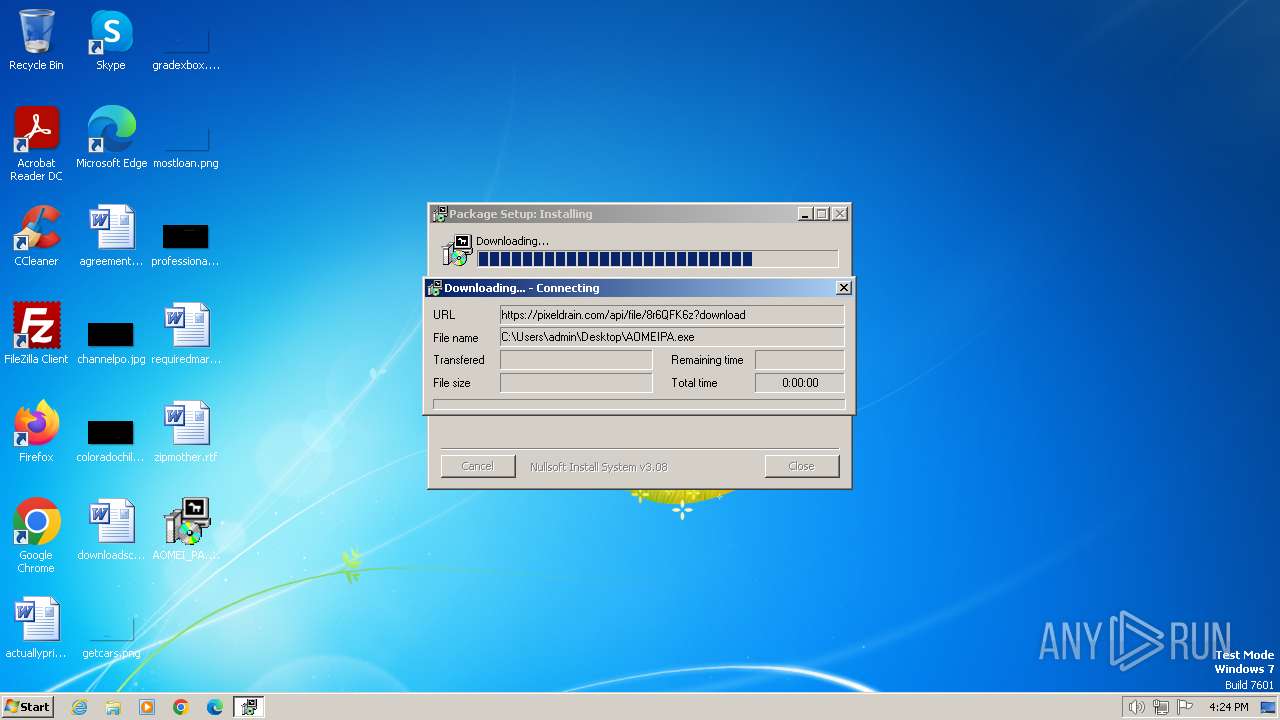
1080 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
2732 | AOMEI_PA.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
Process | Message |
|---|---|
loaddrv.exe | OpenService() Faild !
|
loaddrv.exe | ------------Uninstall AMPA Drive-----------------
|
loaddrv.exe | OpenSCManager() ok !
|
loaddrv.exe | Failed to Uninstall drive.
|
loaddrv.exe | ------------Install AMPA Drive-----------------
|
loaddrv.exe | OpenSCManager() ok !
|
loaddrv.exe | CrateService() ok !
|
loaddrv.exe | StartService() Faild!
|
loaddrv.exe | Failed to Install drive.
|
loaddrv.exe | Failed to Uninstall drive.
|