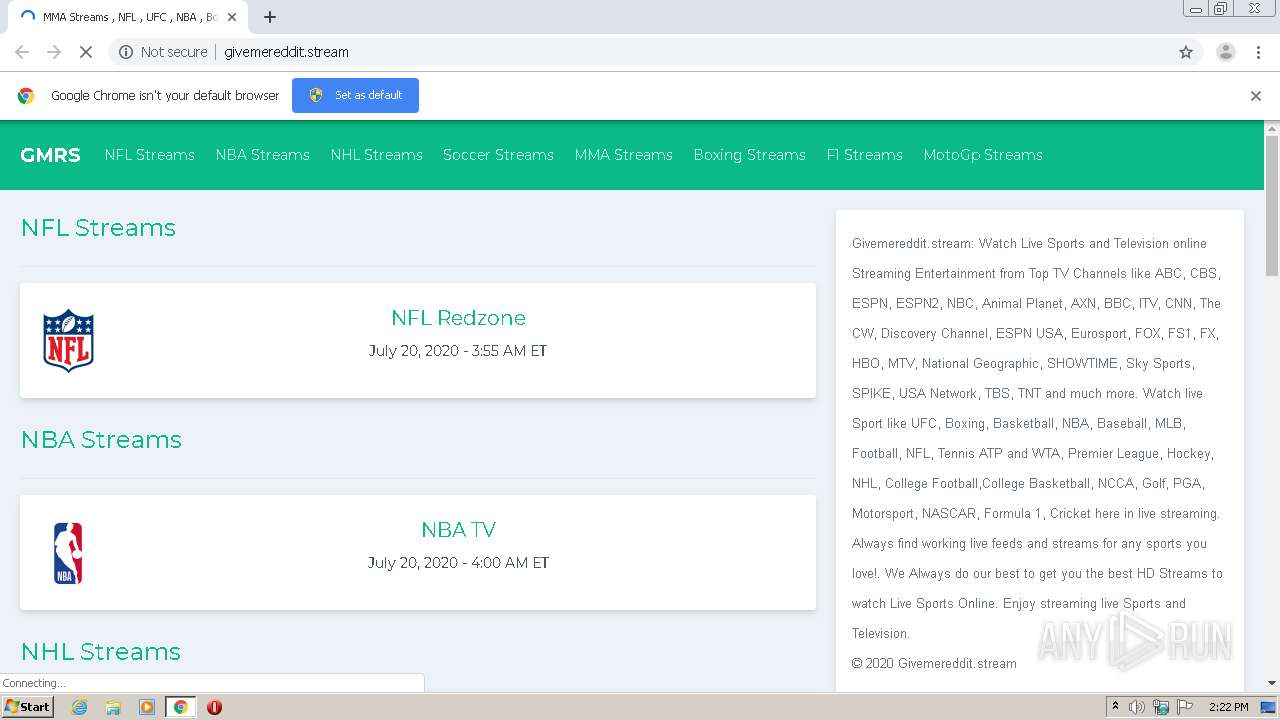
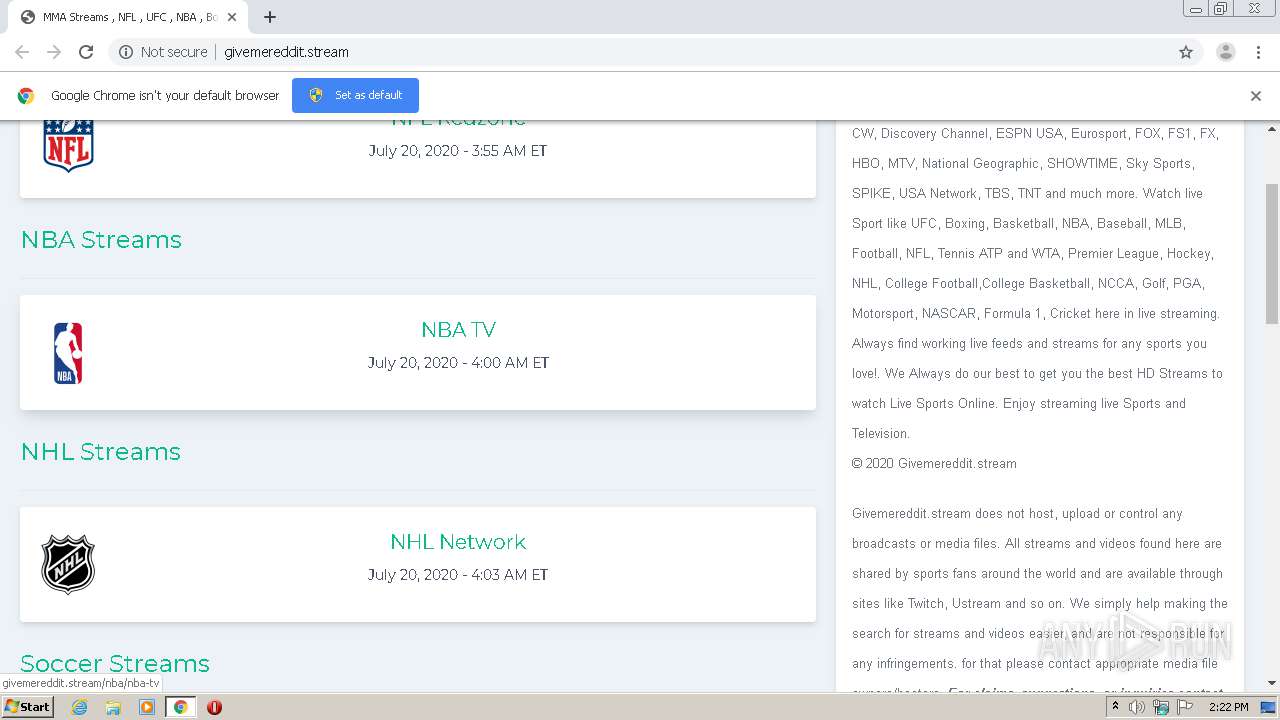
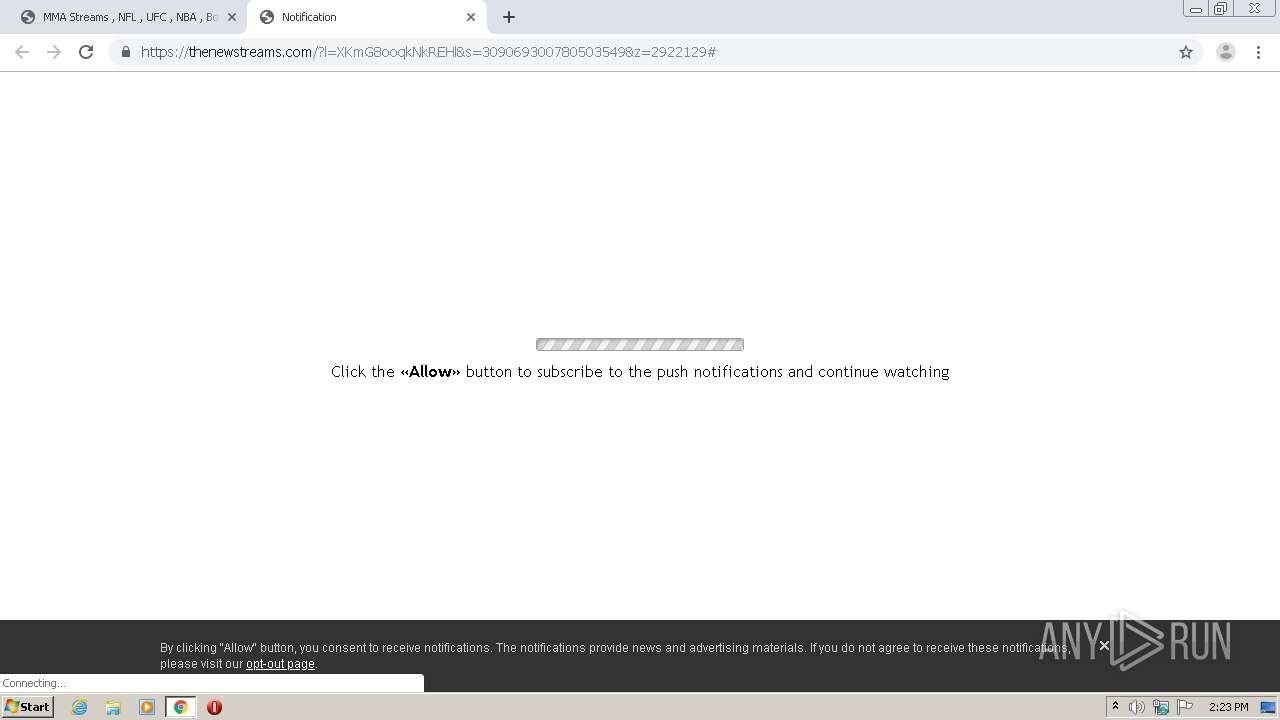
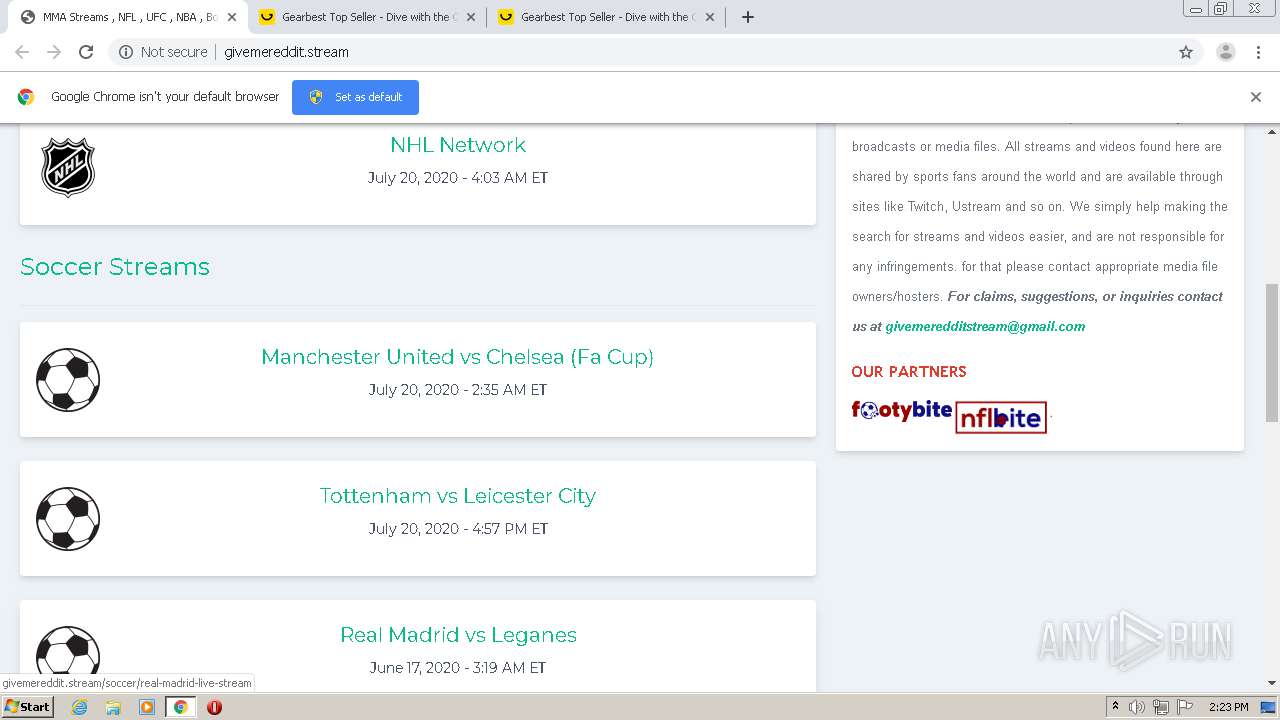
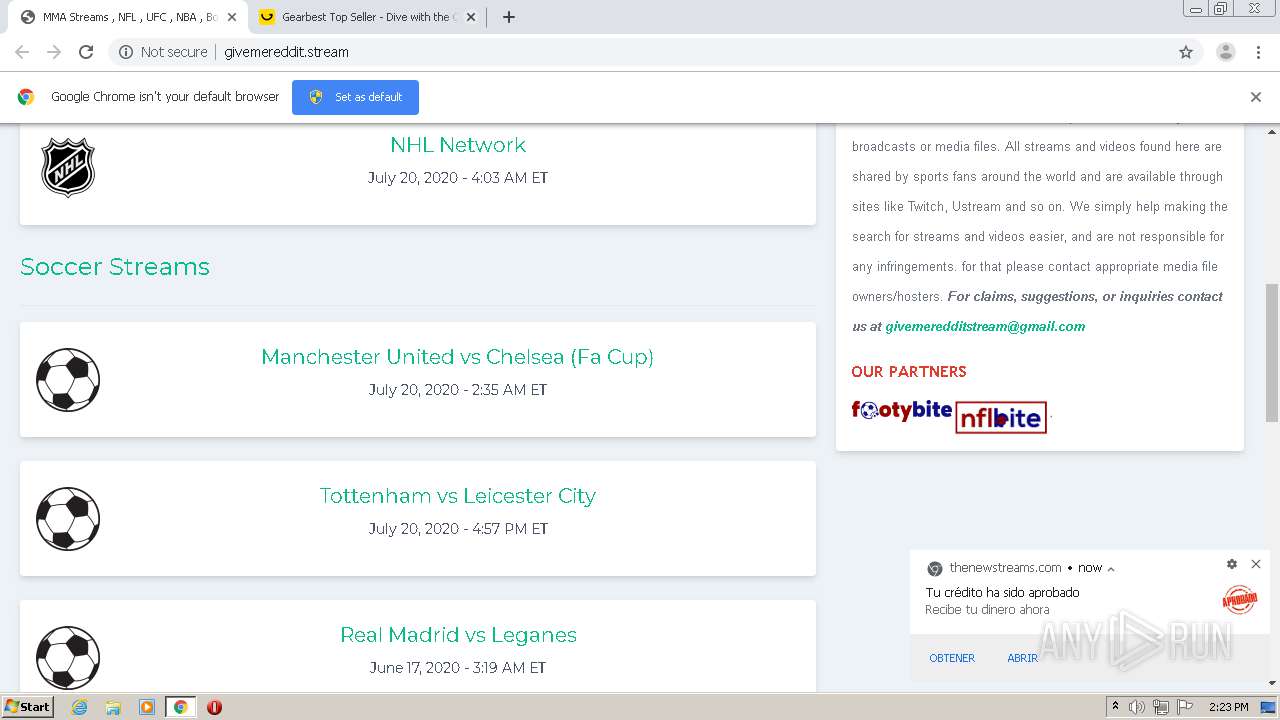
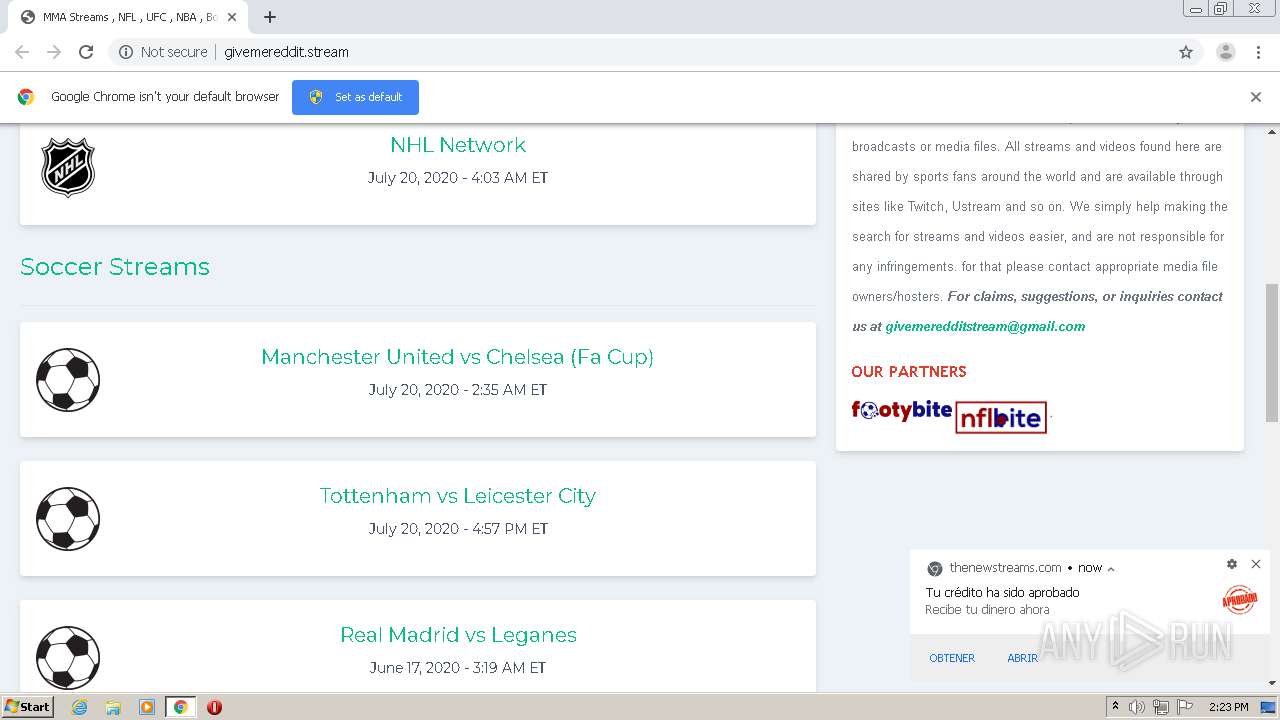
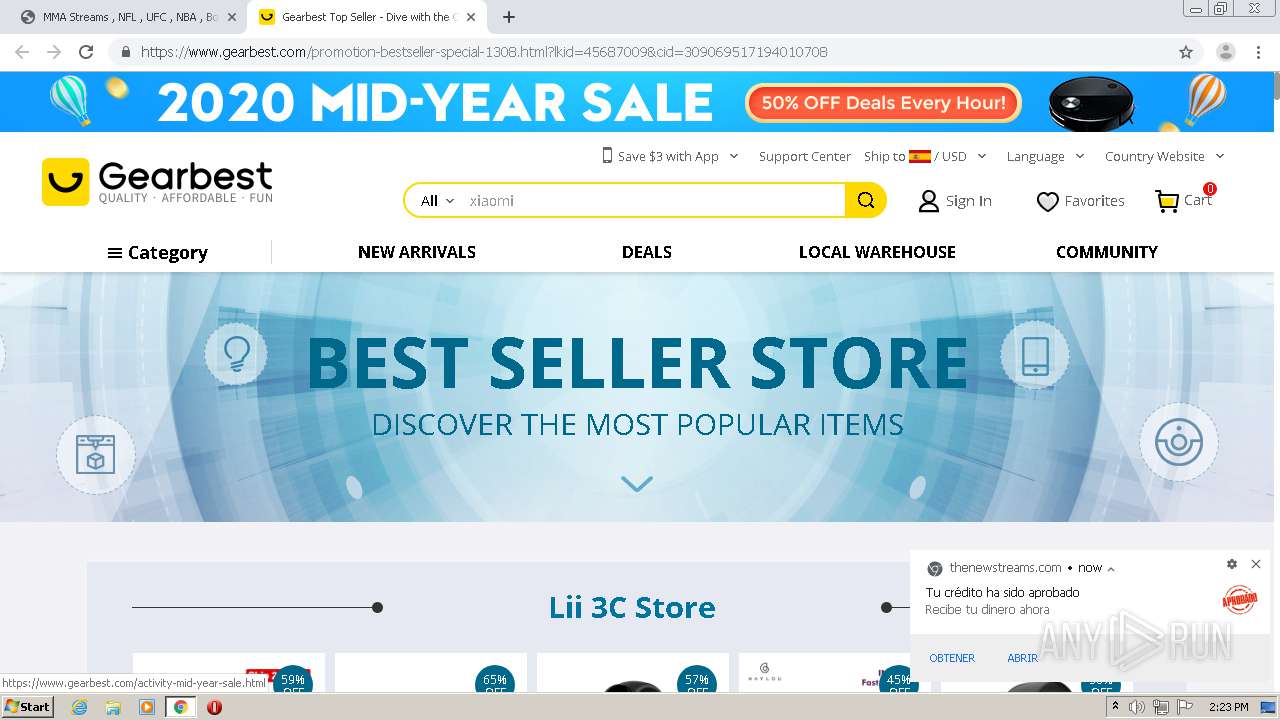
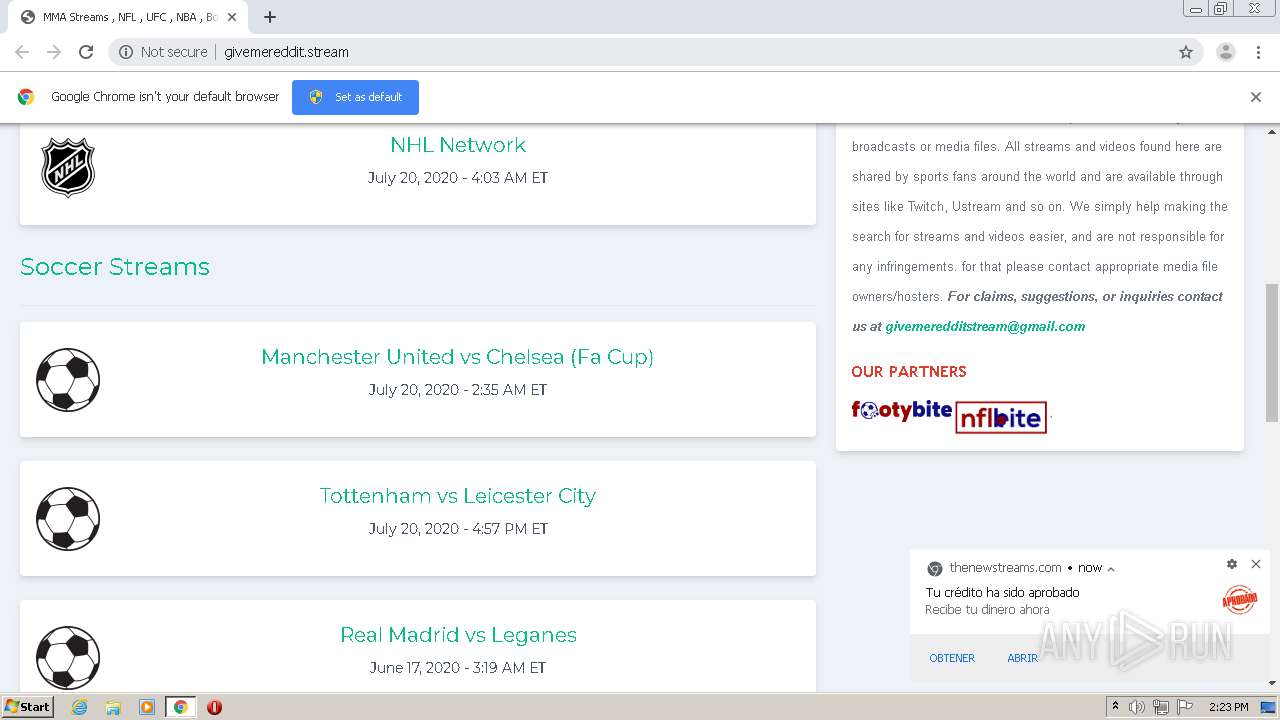
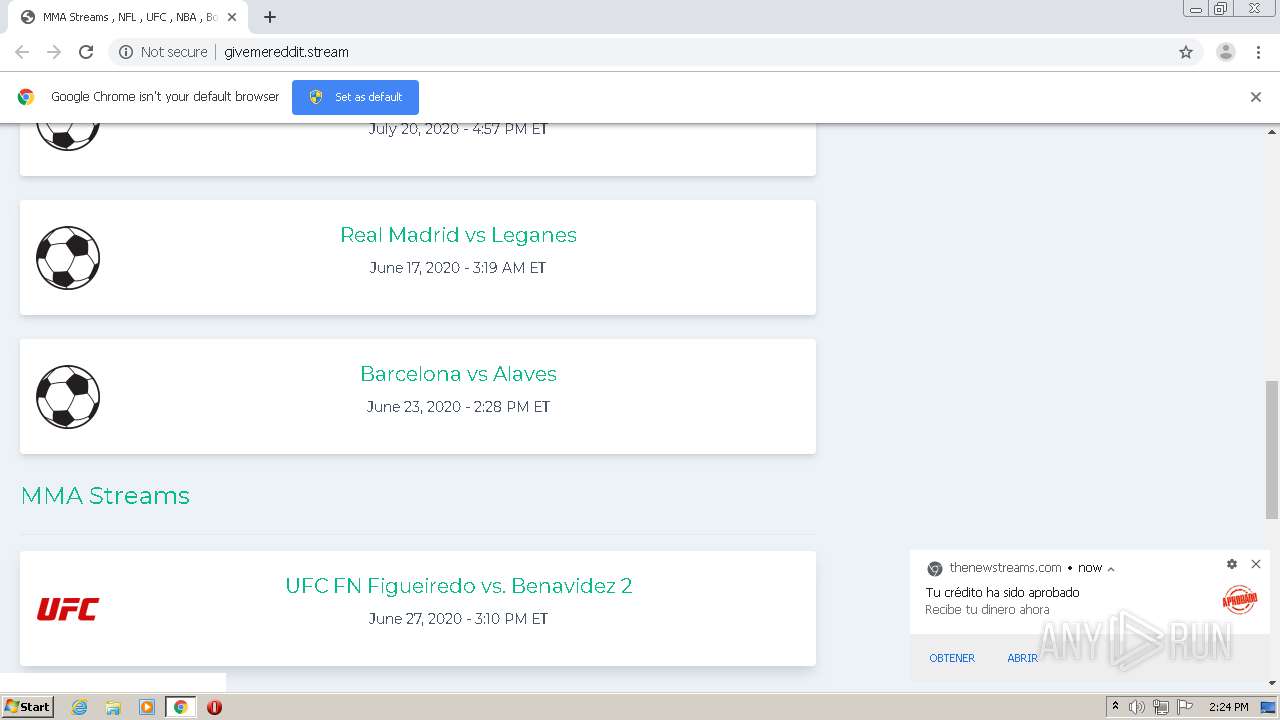
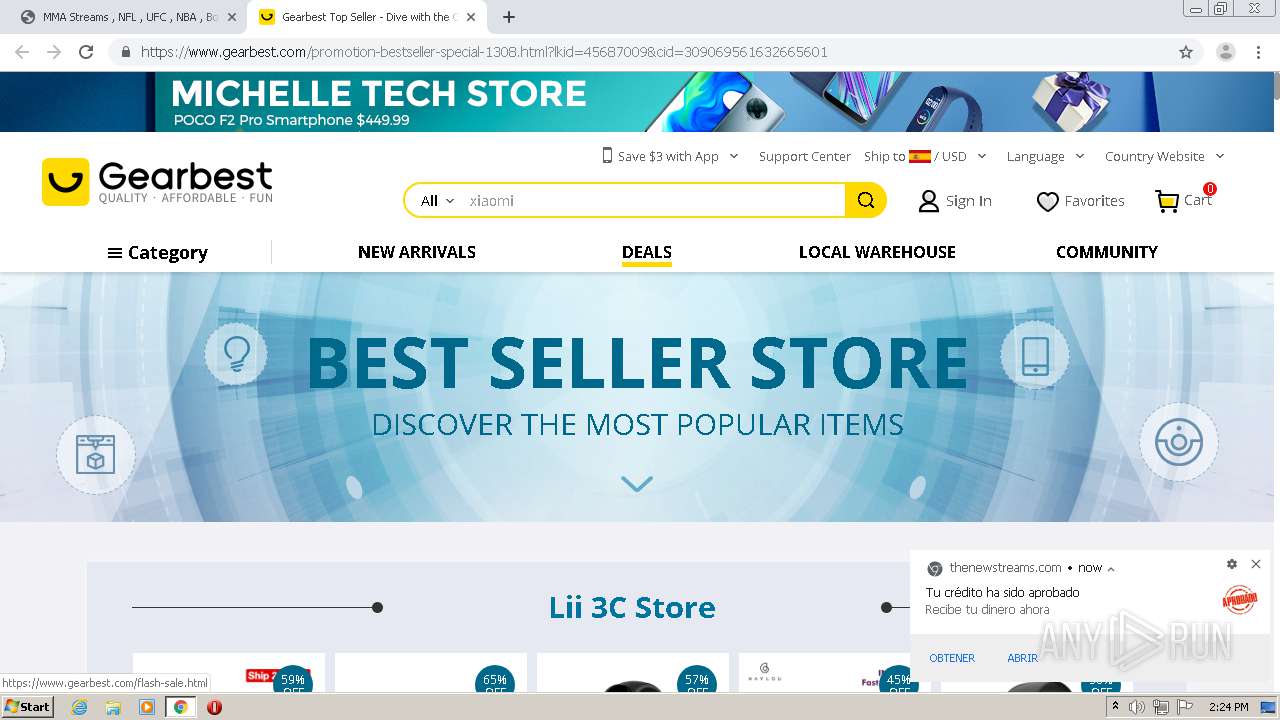
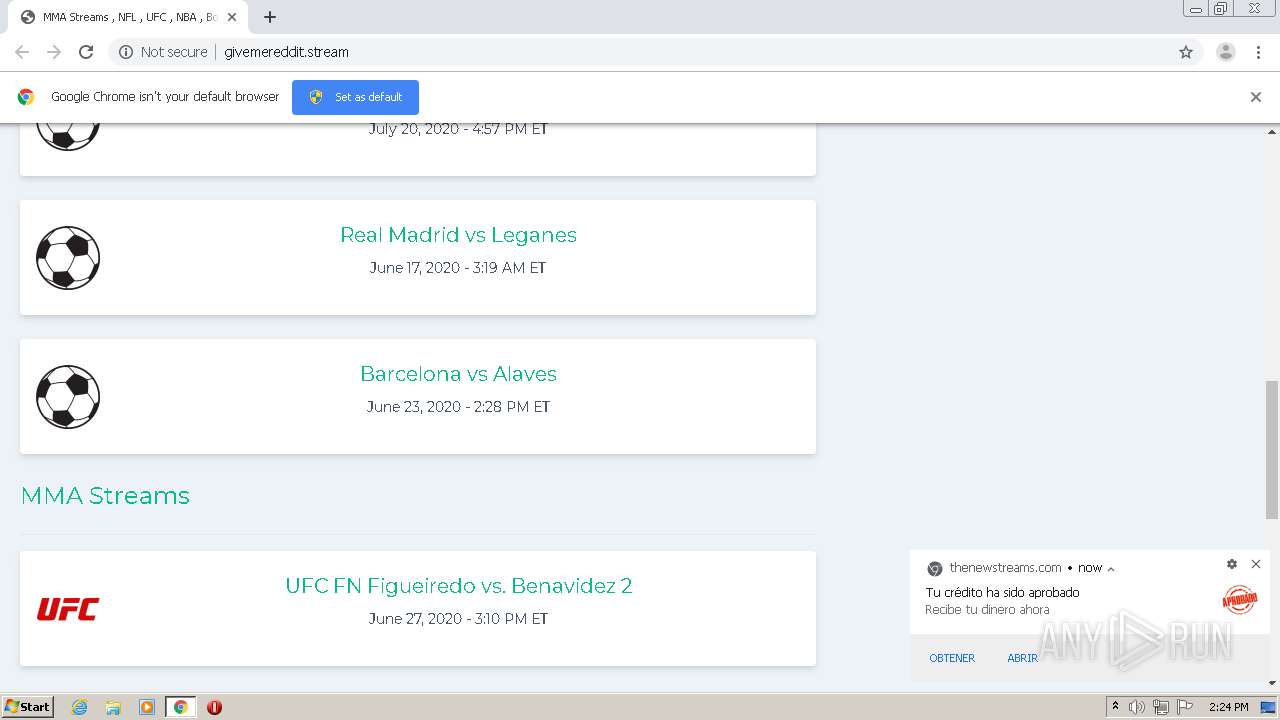
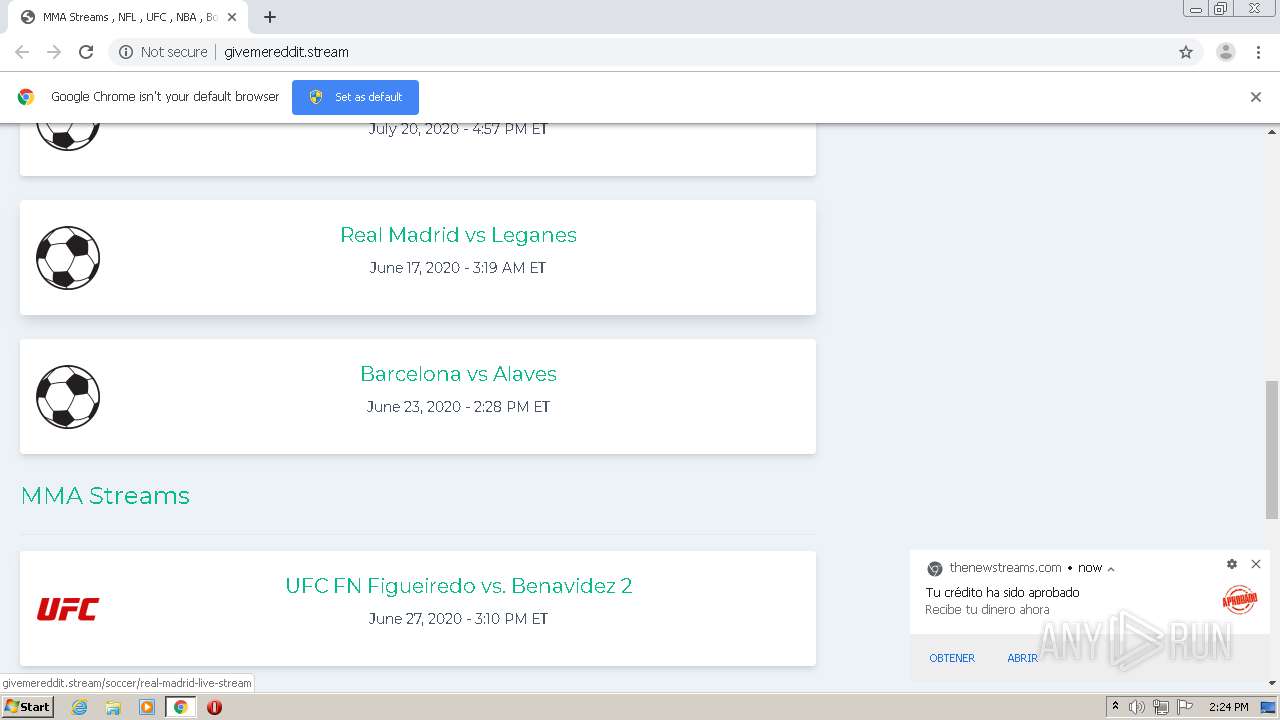
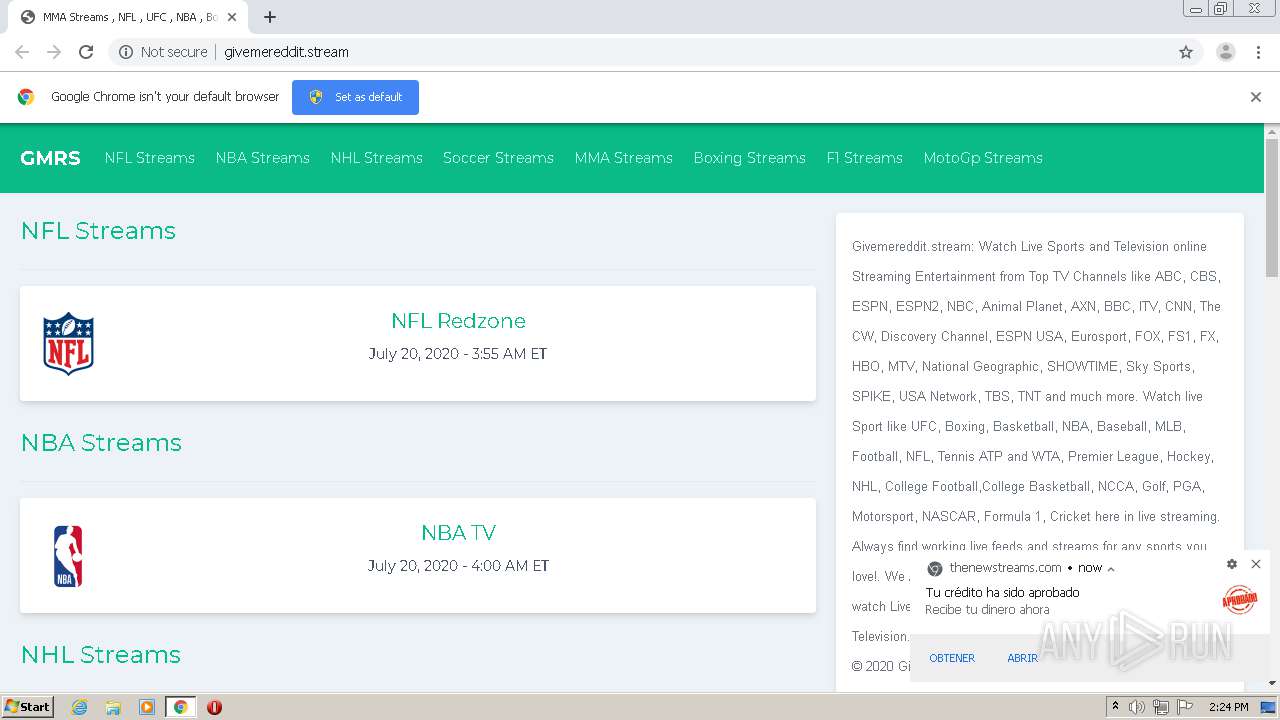
| URL: | http://givemereddit.stream/soccer/arsenal-live-stream&kw=[""arsenal"",""vs"",""manchester"",""city"",""live"",""stream"",""-"",""gmrs""]&key=861e110f04bd782c5c00507b79e9784f&scrWidth=1280&scrHeight=720&tz=-4&ship=&pst=&v=20.6.v.8&res=7.29&dev=r&uuid=49d6abfb-9547-45d9-9682-1920a16b69f8:2:2 |
| Full analysis: | https://app.any.run/tasks/959c0396-28ee-4c33-9c05-f18e2f9e0d56 |
| Verdict: | No threats detected |
| Analysis date: | July 20, 2020, 13:22:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 729894B8246643C601D941665F694E4F |
| SHA1: | 83E7409527371C2B2E2FD4B6A4BC3E469468BEDF |
| SHA256: | 98B6165312D8DE0E2F04530FDC2B9303C7653060F08A803C307A215457DE3490 |
| SSDEEP: | 6:CyM9U6tQcKp0QhOfXLEnsmNAX3gsTkWRnHpnWOJPkV7FvFKvNLavdEZcIabnG:NOU6tq0uOfLEnTNWgydd49KFZcIabG |
MALICIOUS
No malicious indicators.SUSPICIOUS
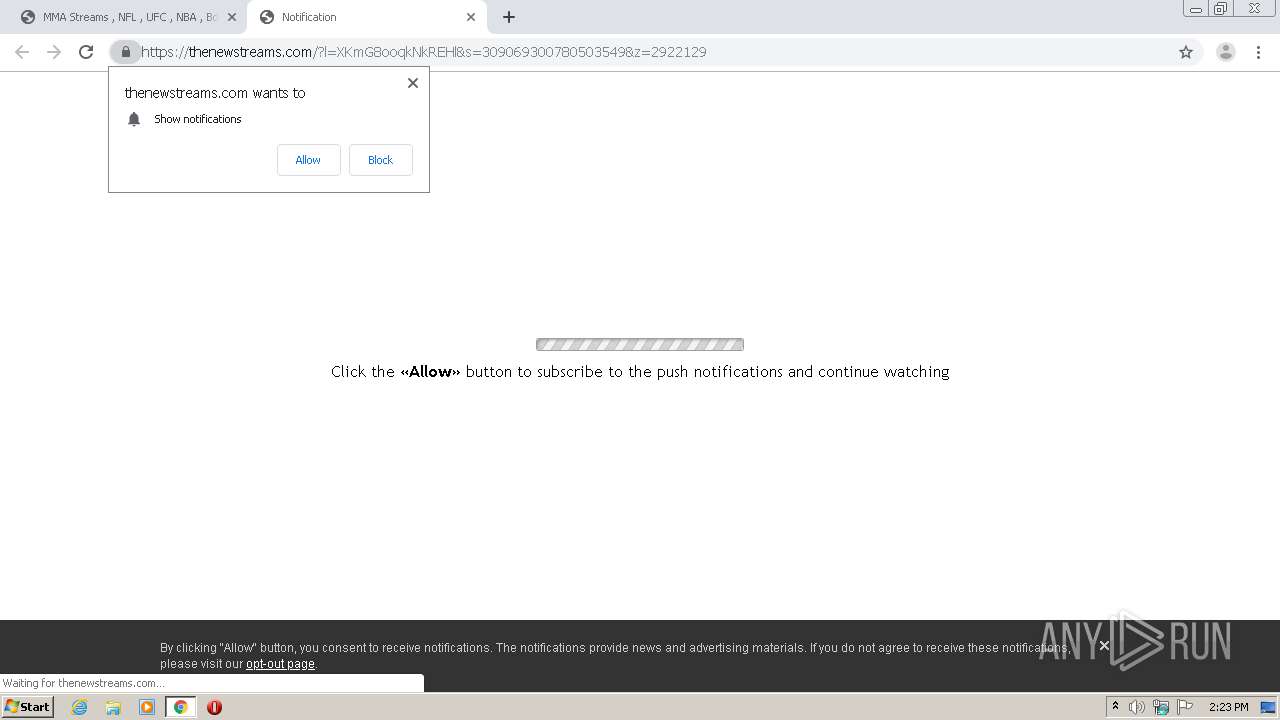
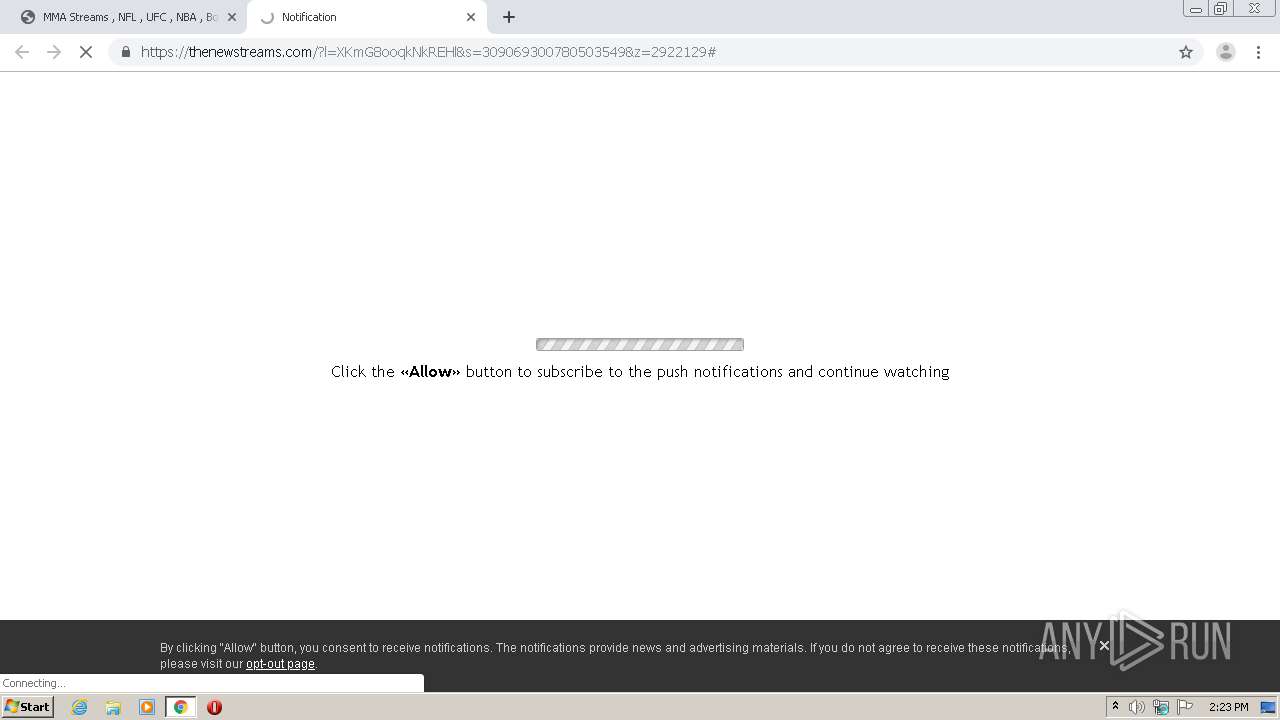
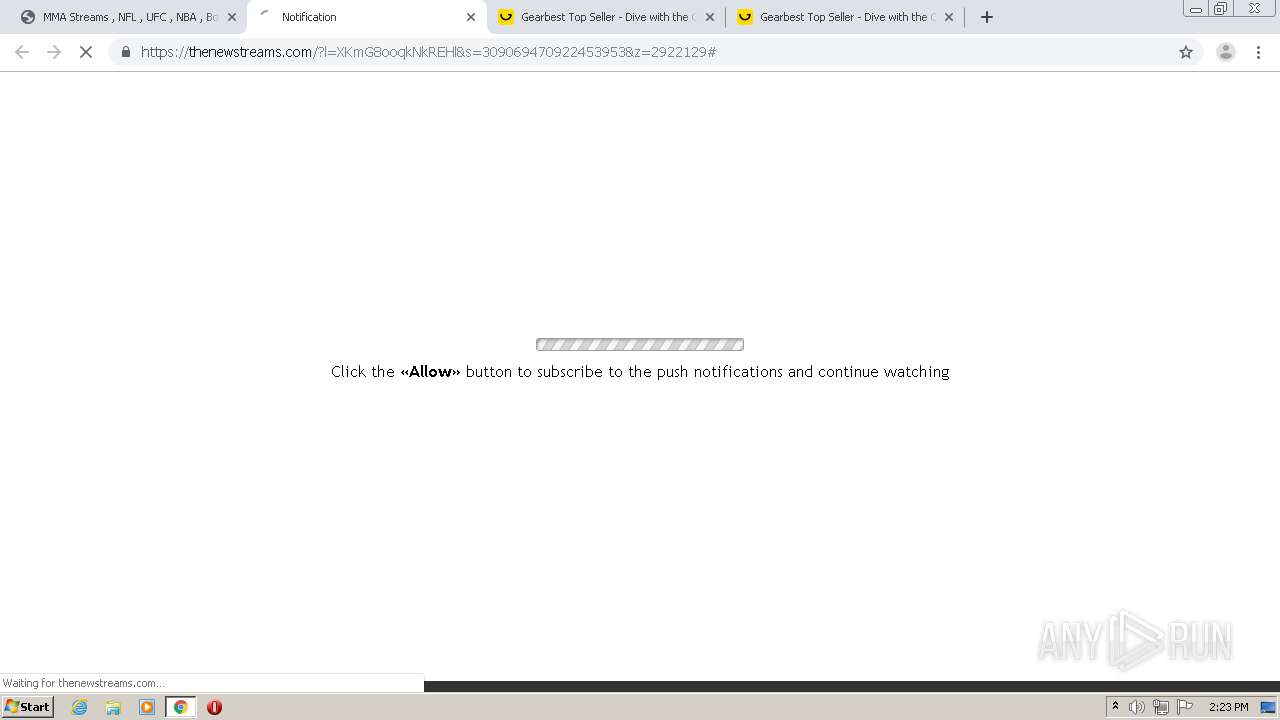
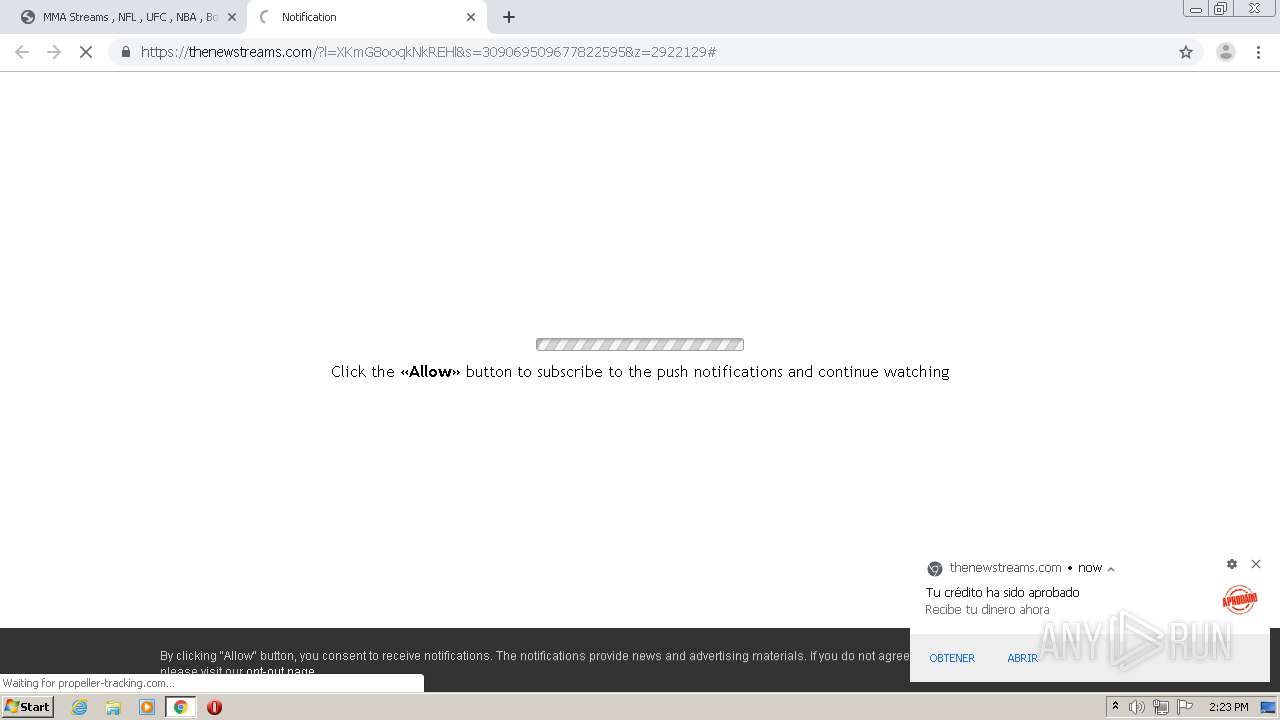
Modifies files in Chrome extension folder
- chrome.exe (PID: 932)
INFO
Reads the hosts file
- chrome.exe (PID: 4024)
- chrome.exe (PID: 932)
Reads settings of System Certificates
- chrome.exe (PID: 4024)
Changes settings of System certificates
- chrome.exe (PID: 4024)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 932)
Creates files in the user directory
- chrome.exe (PID: 932)
Application launched itself
- chrome.exe (PID: 932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
60
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3023786012429594307 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14412938732595013892 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9683509047555356571 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15602807971536845385 --mojo-platform-channel-handle=3448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16615456221358277378 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://givemereddit.stream/soccer/arsenal-live-stream&kw=[""arsenal"",""vs"",""manchester"",""city"",""live"",""stream"",""-"",""gmrs""]&key=861e110f04bd782c5c00507b79e9784f&scrWidth=1280&scrHeight=720&tz=-4&ship=&pst=&v=20.6.v.8&res=7.29&dev=r&uuid=49d6abfb-9547-45d9-9682-1920a16b69f8:2:2" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7004357978931403544 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9517329540008265136 --mojo-platform-channel-handle=4508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9494552076252981652 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13167775317437729843,7116552049851676541,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14997146597426431984 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
694
Read events
567
Write events
122
Delete events
5
Modification events
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 932-13239724967371625 |
Value: 259 | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
464
Text files
325
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F159AA8-3A4.pma | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d65ee0d0-2927-4e69-86de-e06ae2d722cf.tmp | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFb049e.TMP | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFb048e.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFb04bd.TMP | text | |
MD5:AC43135B8C9FED46A92448C4E711F45C | SHA256:D840BA7CEBACF86DDBAD75BFB61A53449AA7AE3DE6B8ADC97FE45624626A6F09 | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFb0692.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
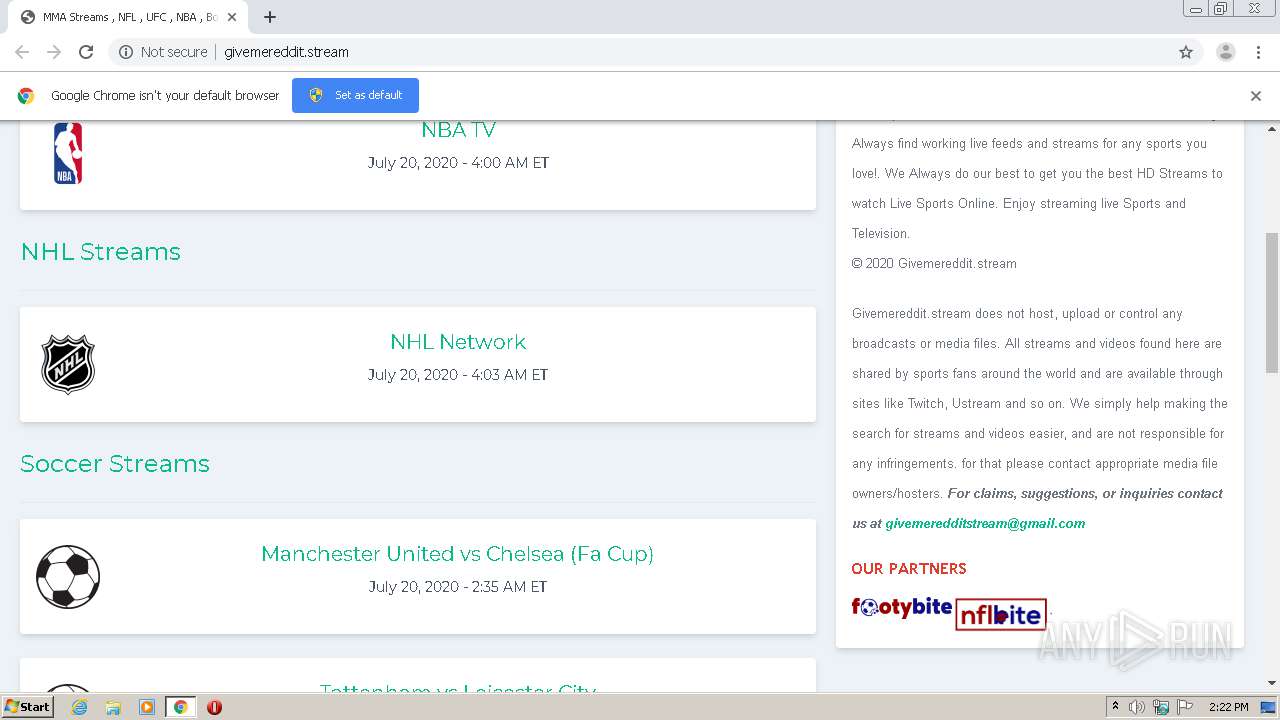
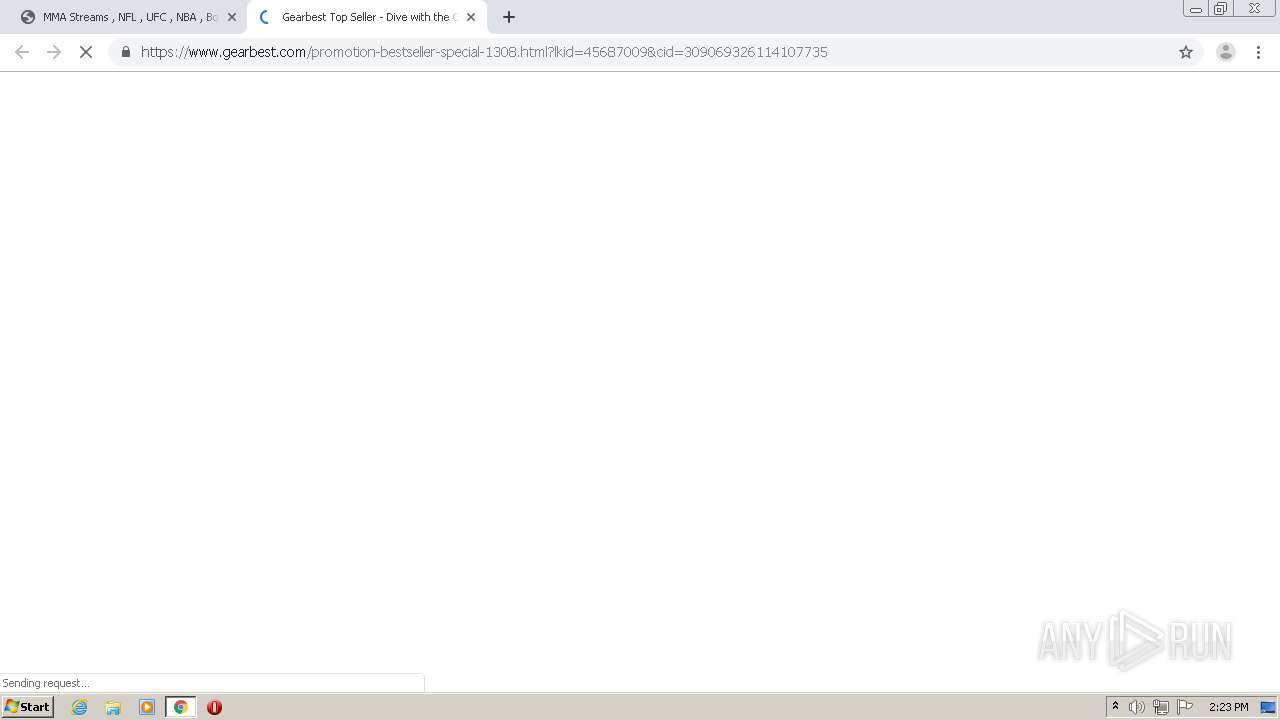
HTTP(S) requests
25
TCP/UDP connections
160
DNS requests
90
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
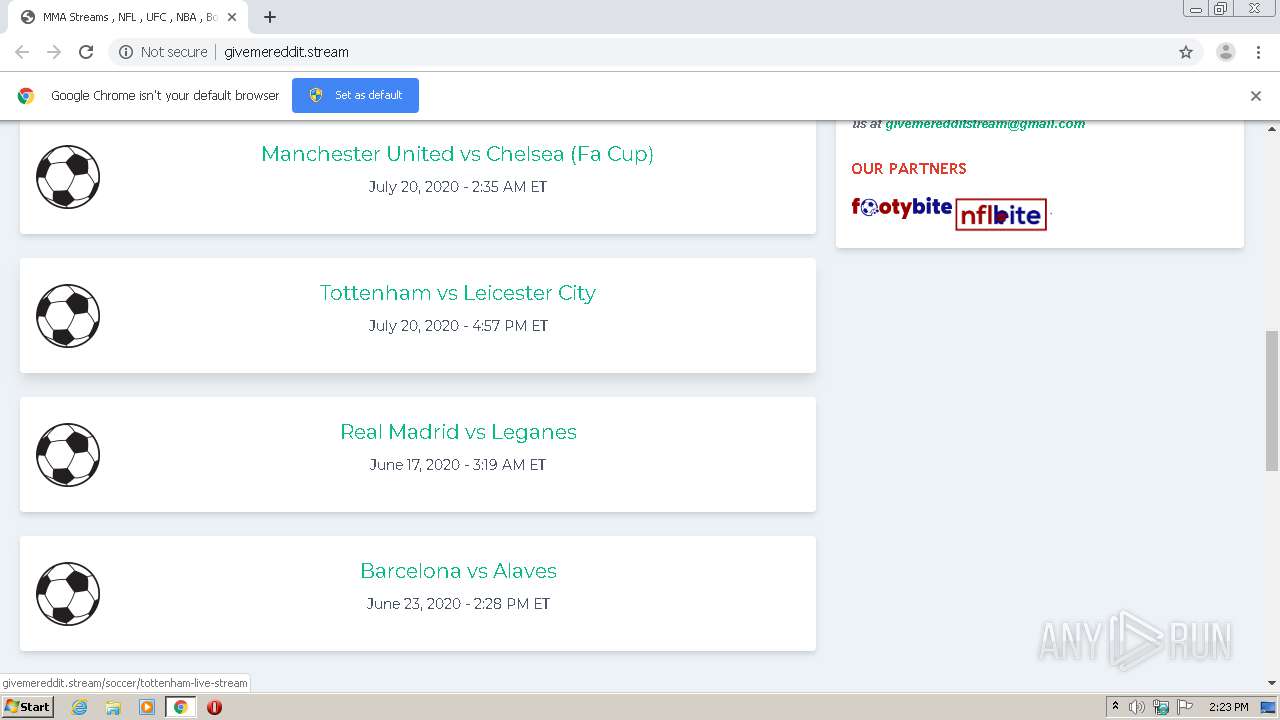
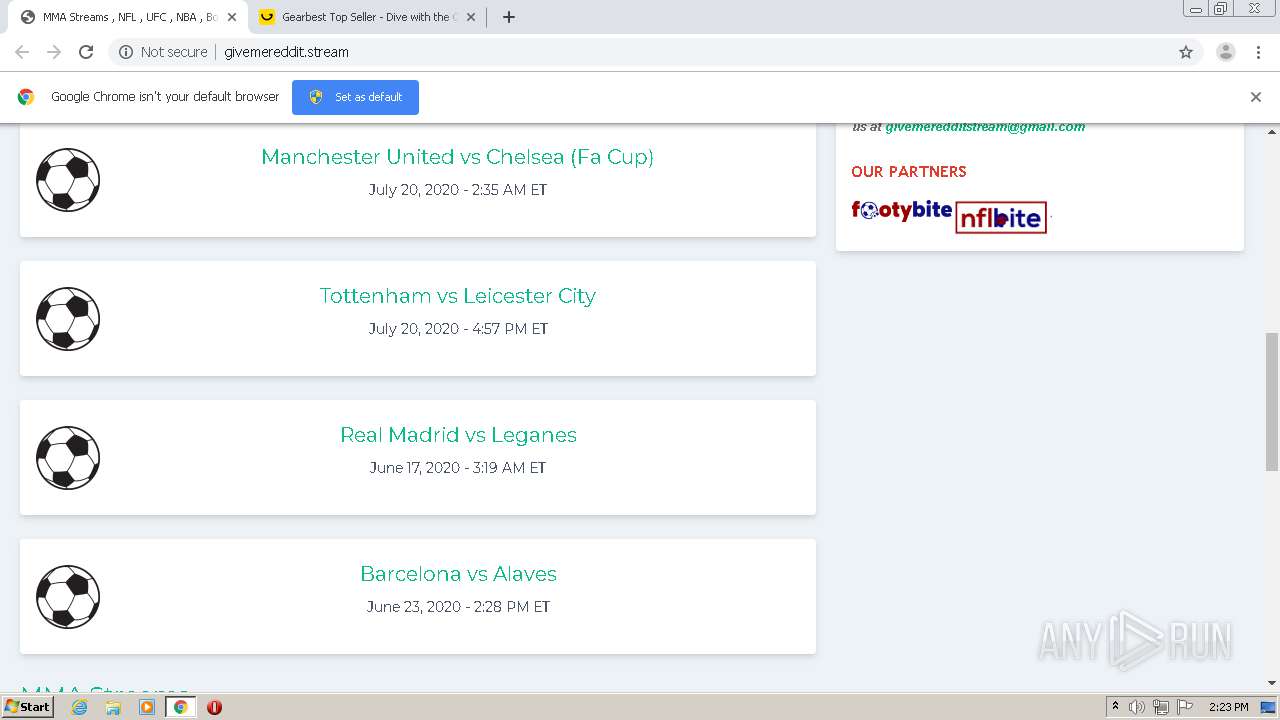
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/public/css/app.css | US | text | 2.92 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/public/images/nfl.png | US | image | 12.9 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/cdn-cgi/scripts/5c5dd728/cloudflare-static/email-decode.min.js | US | html | 655 b | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/public/images/soccer.png | US | image | 5.84 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/public/images/nhl.png | US | image | 11.4 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/public/images/nba.png | US | image | 7.65 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/public/images/boxing.png | US | image | 15.8 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/public/images/ufc.png | US | image | 3.86 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.187.146:80 | http://givemereddit.stream/public/images/formula.png | US | image | 7.07 Kb | suspicious |
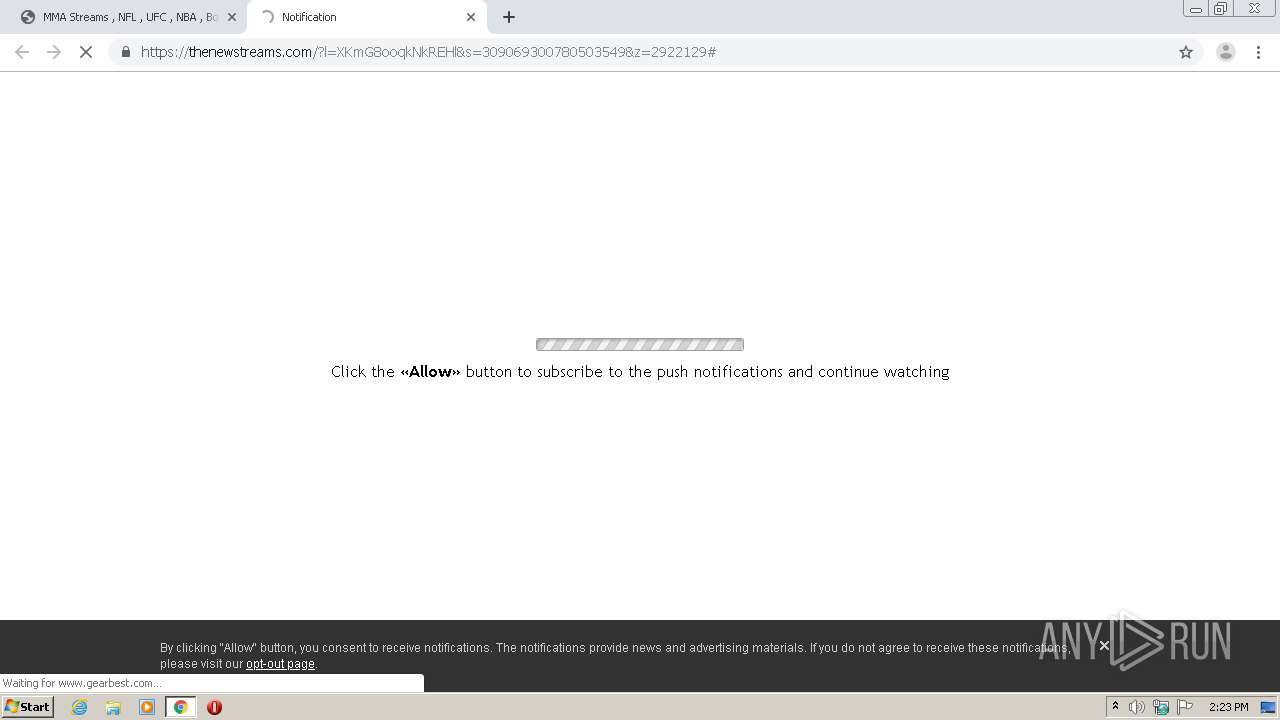
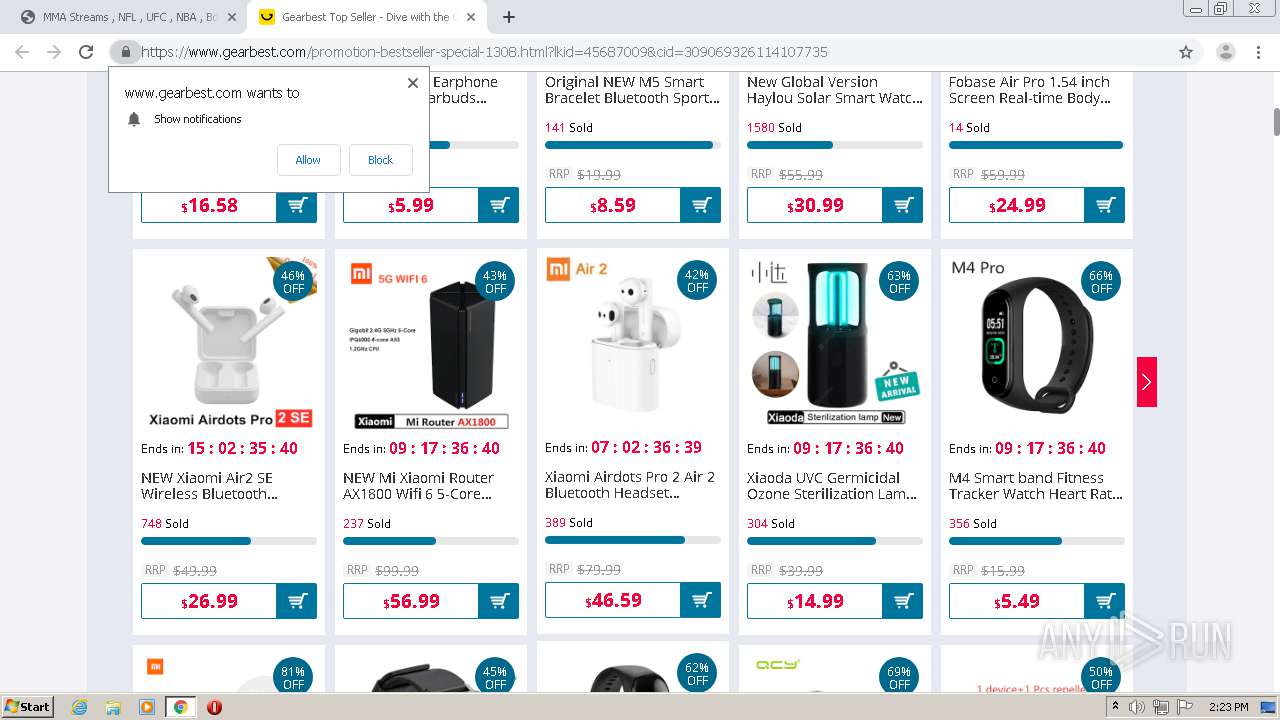
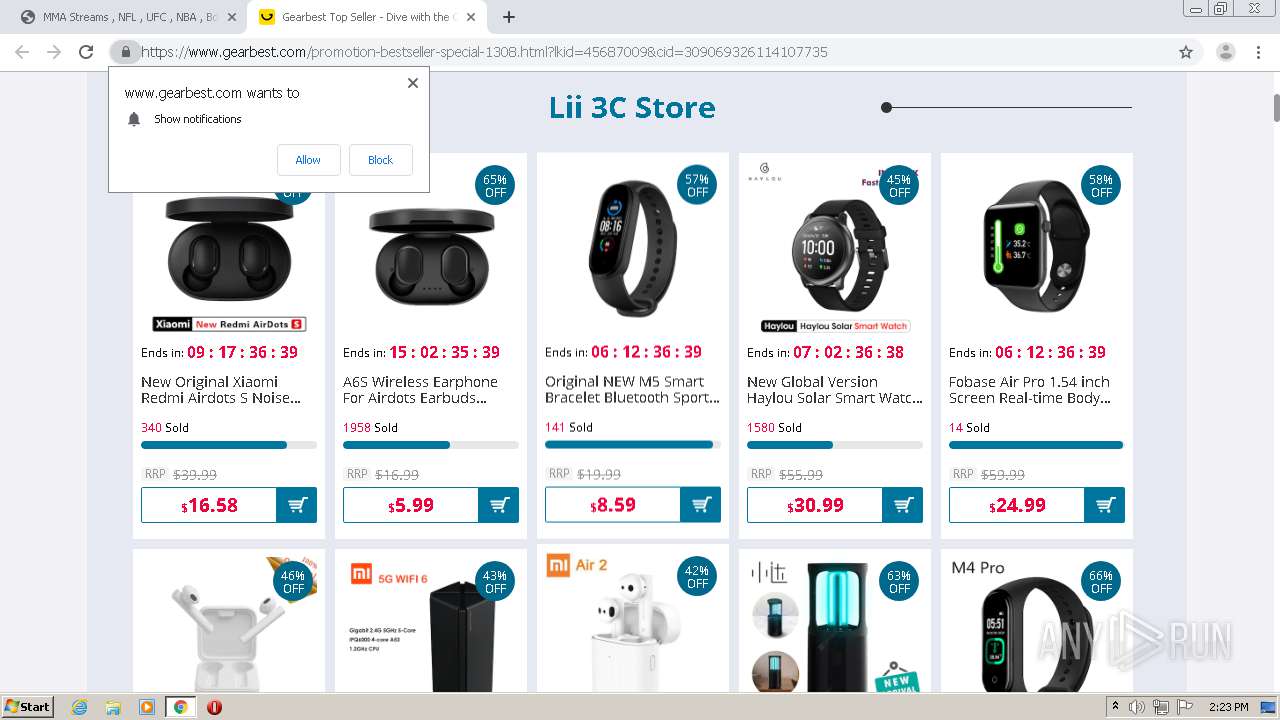
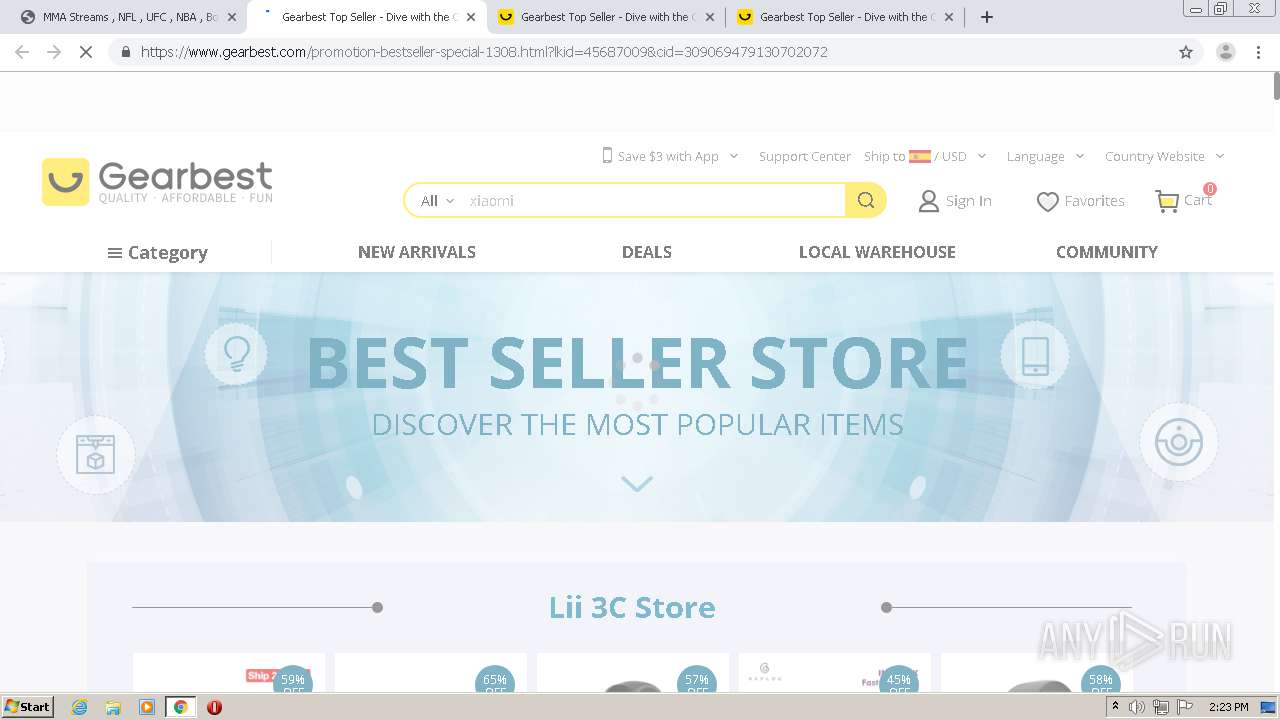
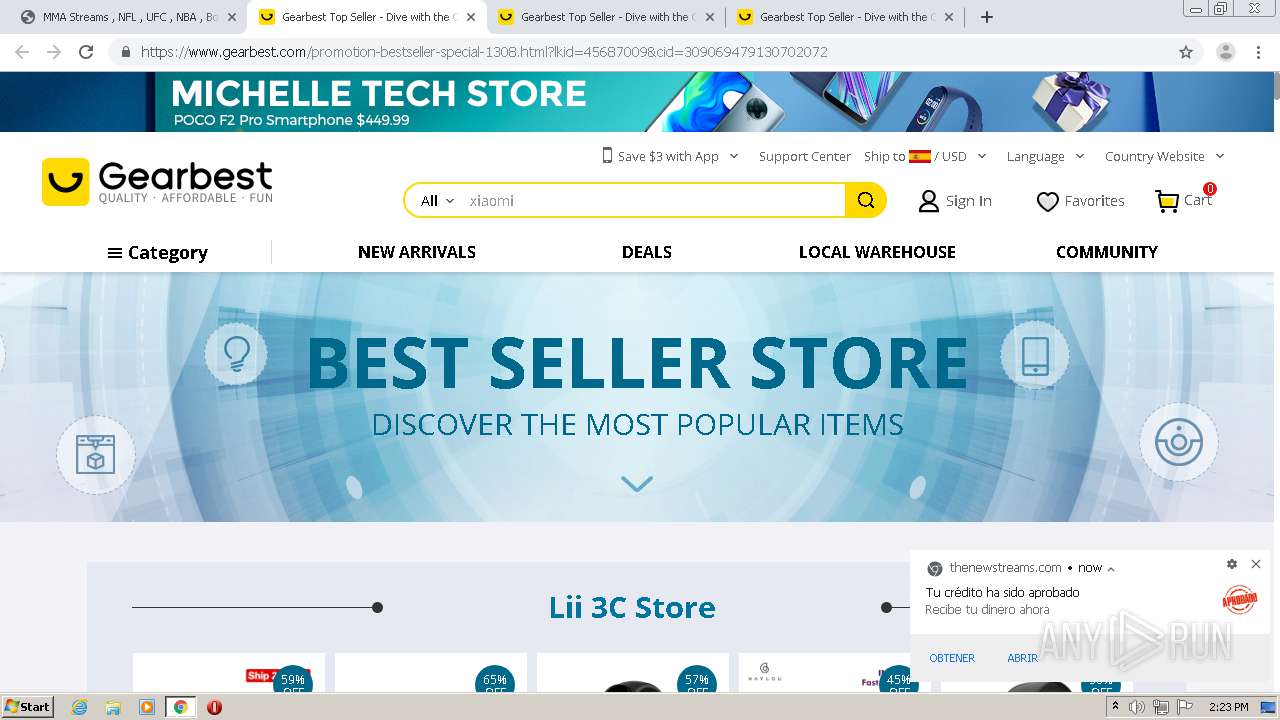
4024 | chrome.exe | GET | 200 | 104.27.153.218:80 | http://scienceandtechnology.xyz/wp-content/uploads/2019/09/Screen-Shot-2019-09-08-at-11.22.27-PM.png | US | image | 50.8 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4024 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
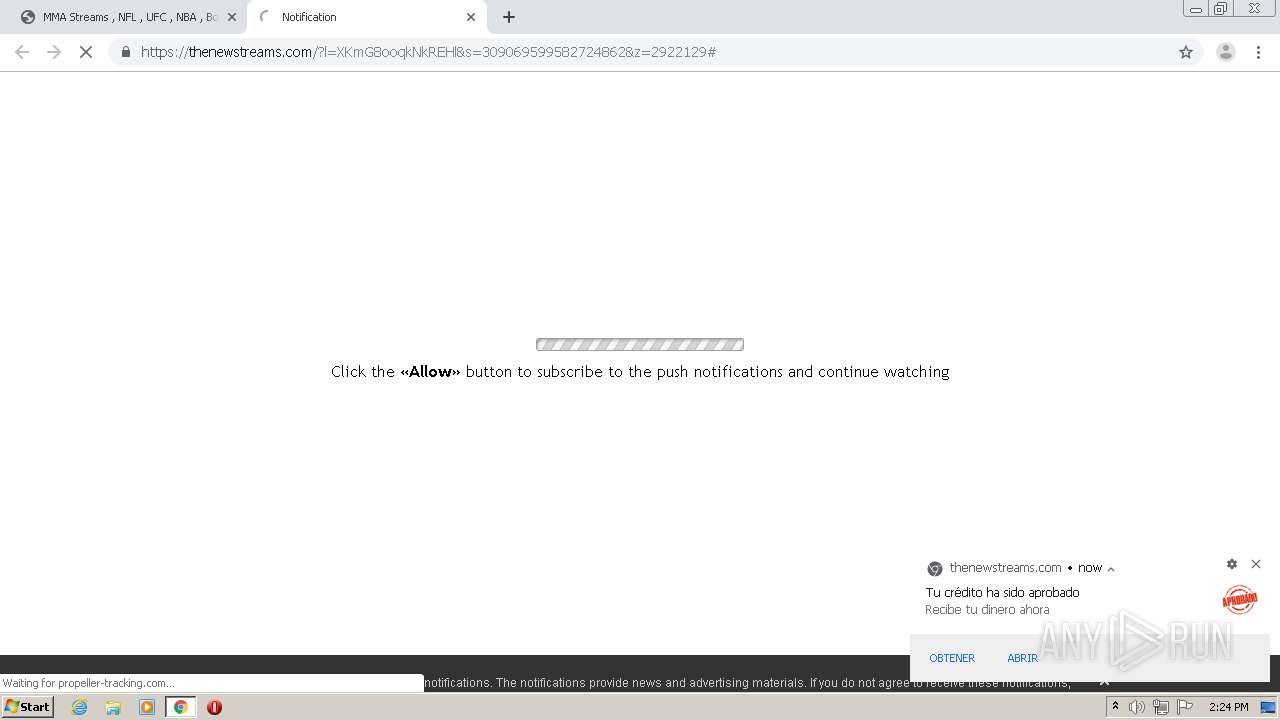
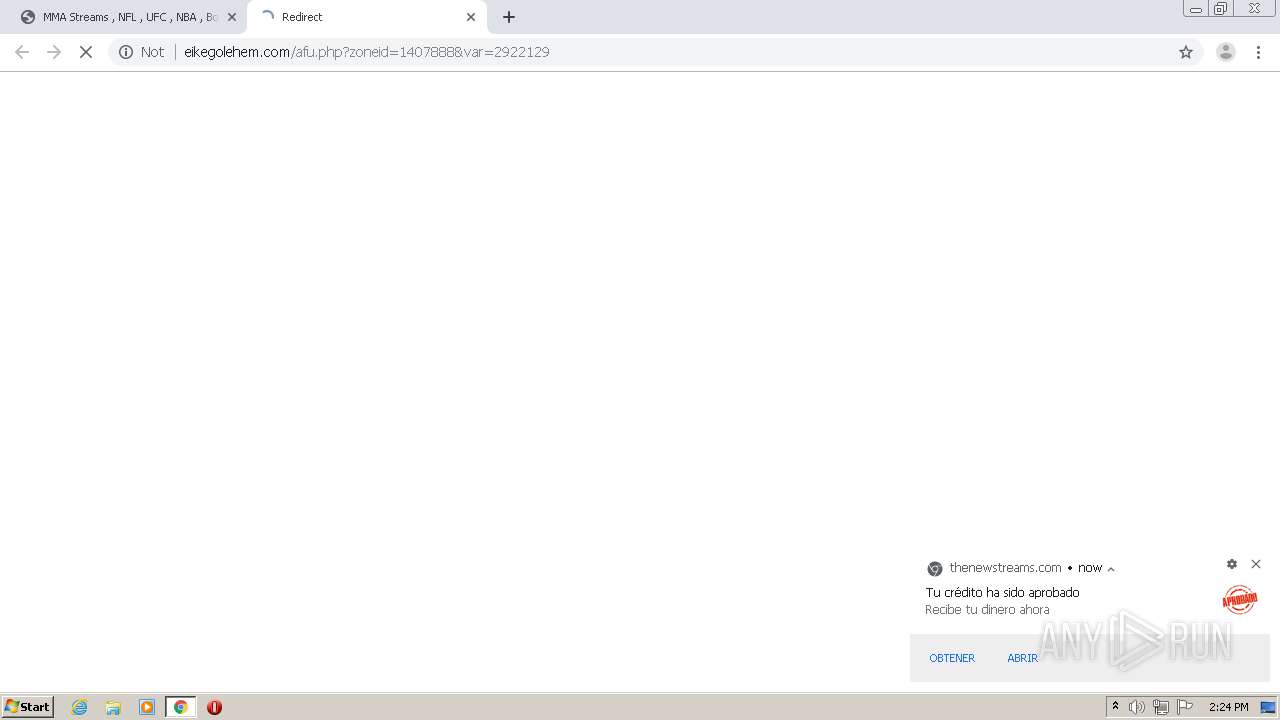
4024 | chrome.exe | 139.45.195.82:443 | bedrapiona.com | — | US | unknown |
4024 | chrome.exe | 74.125.168.39:80 | r2---sn-h5q7knee.gvt1.com | Google Inc. | US | whitelisted |
4024 | chrome.exe | 172.217.21.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
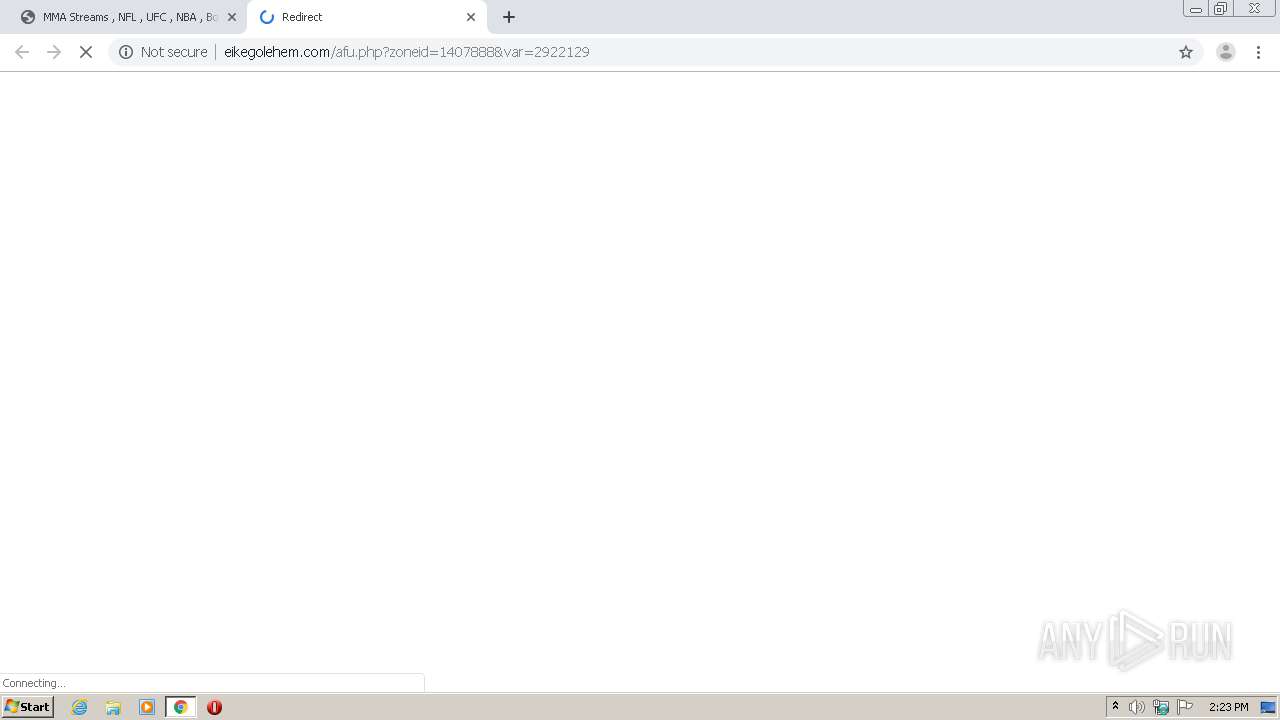
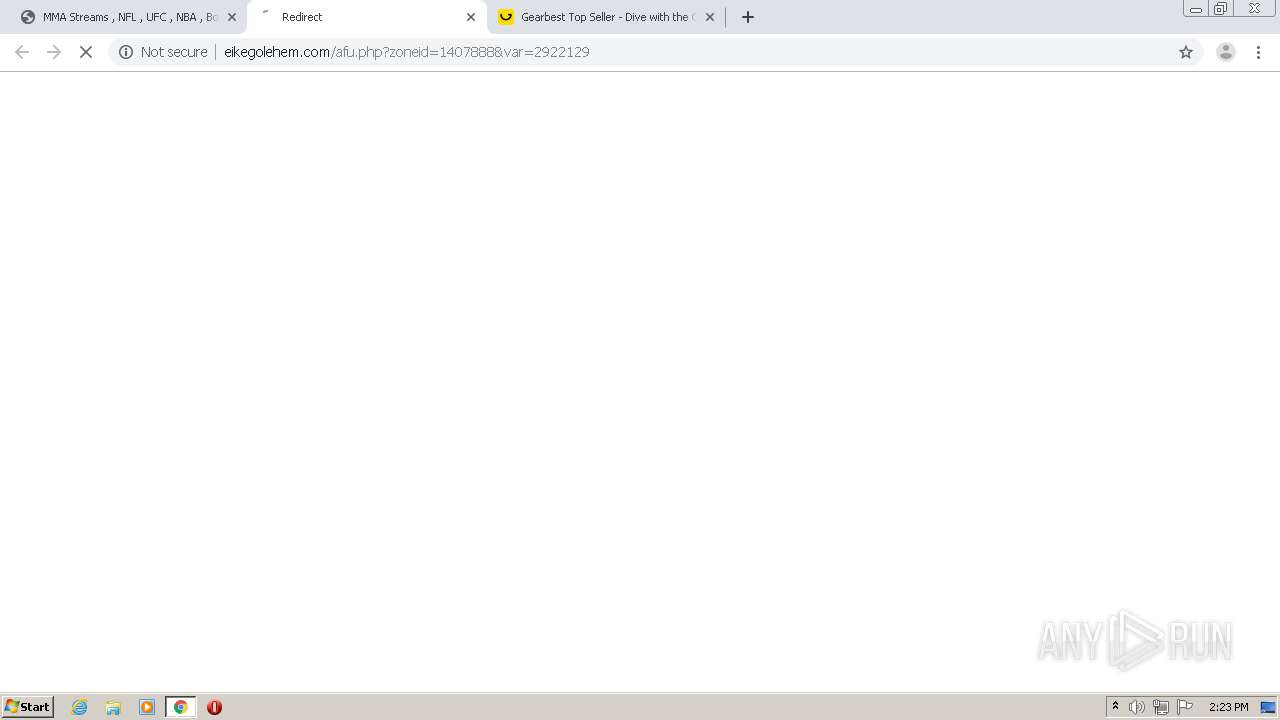
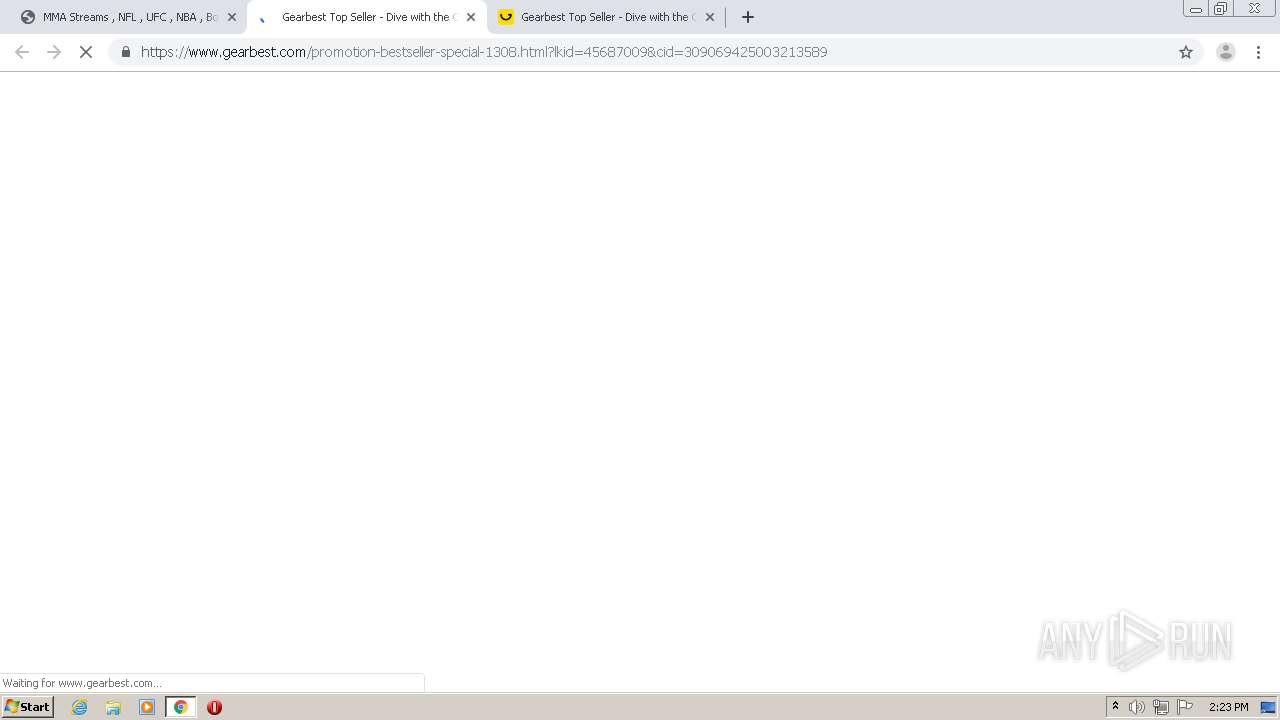
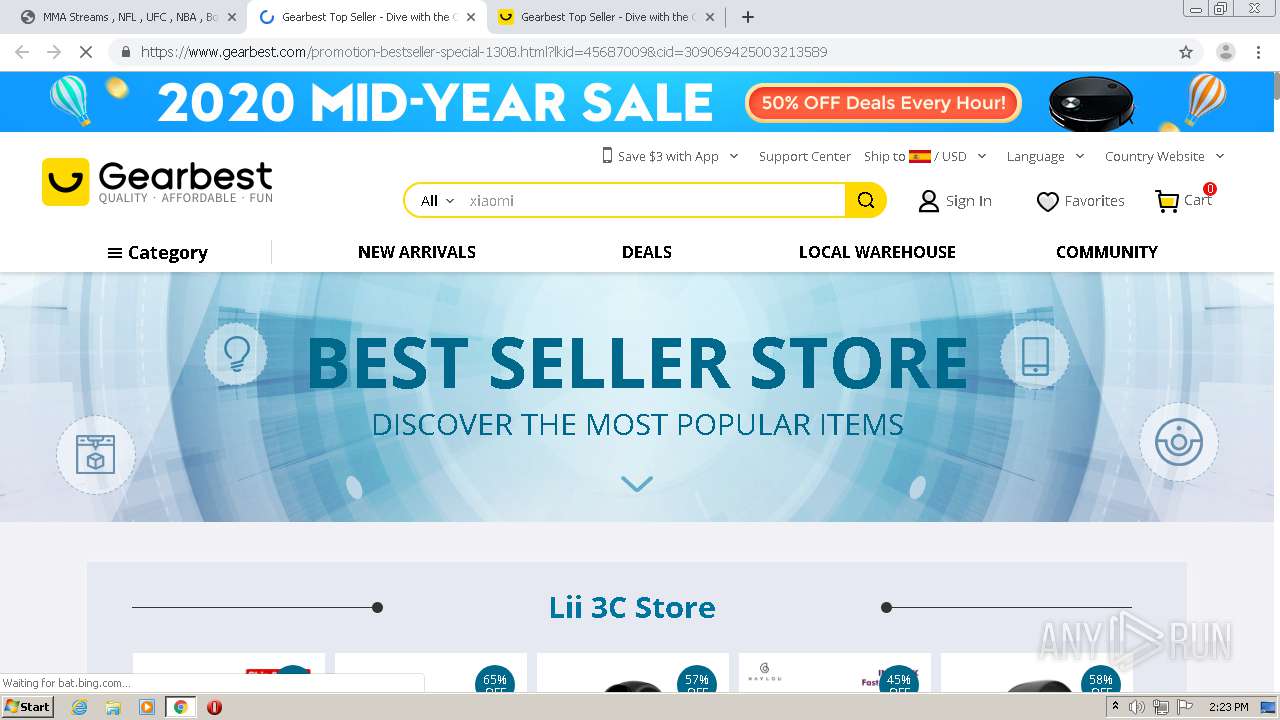
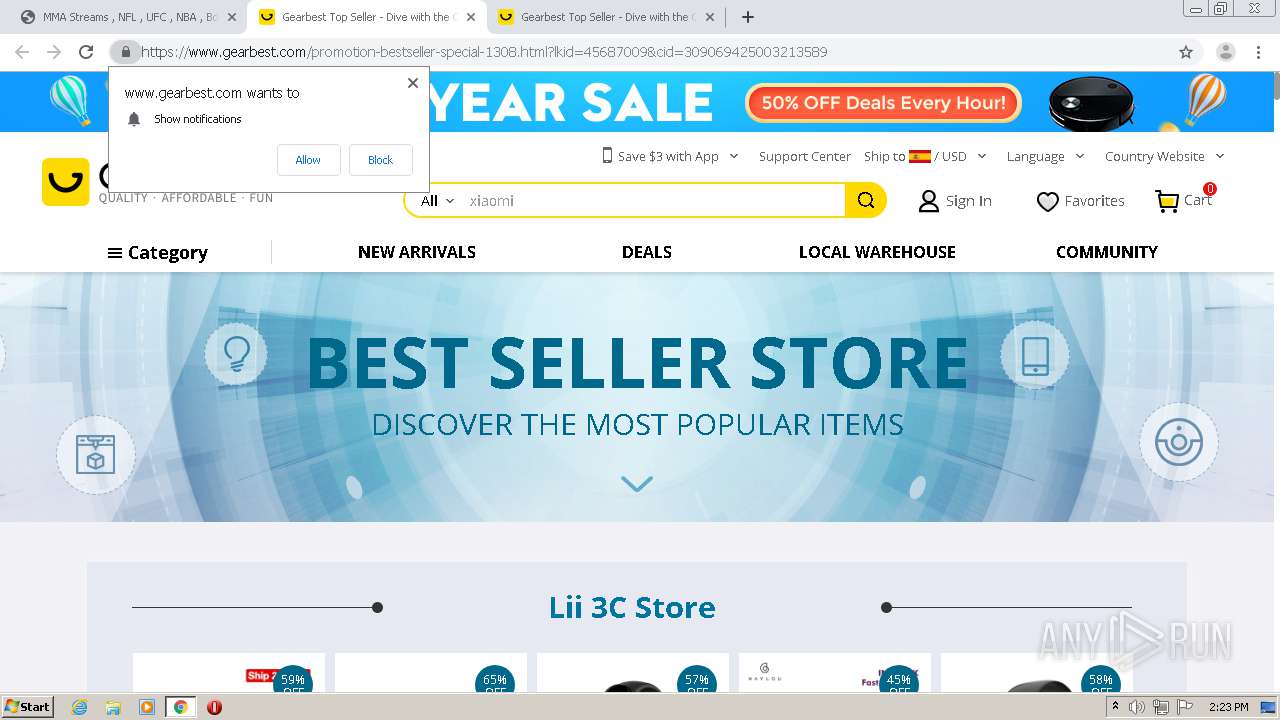
4024 | chrome.exe | 139.45.195.94:80 | eikegolehem.com | — | US | unknown |
4024 | chrome.exe | 185.49.145.156:80 | perf.cdnads.com | Webzilla B.V. | NL | unknown |
4024 | chrome.exe | 52.208.186.41:443 | e2ertt.com | Amazon.com, Inc. | IE | unknown |
4024 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4024 | chrome.exe | 104.27.187.146:80 | givemereddit.stream | Cloudflare Inc | US | shared |
4024 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
givemereddit.stream |
| suspicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
i.imgur.com |
| malicious |
scienceandtechnology.xyz |
| malicious |
ajax.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
home.footybite.com |
| suspicious |
home.nflbite.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4024 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |