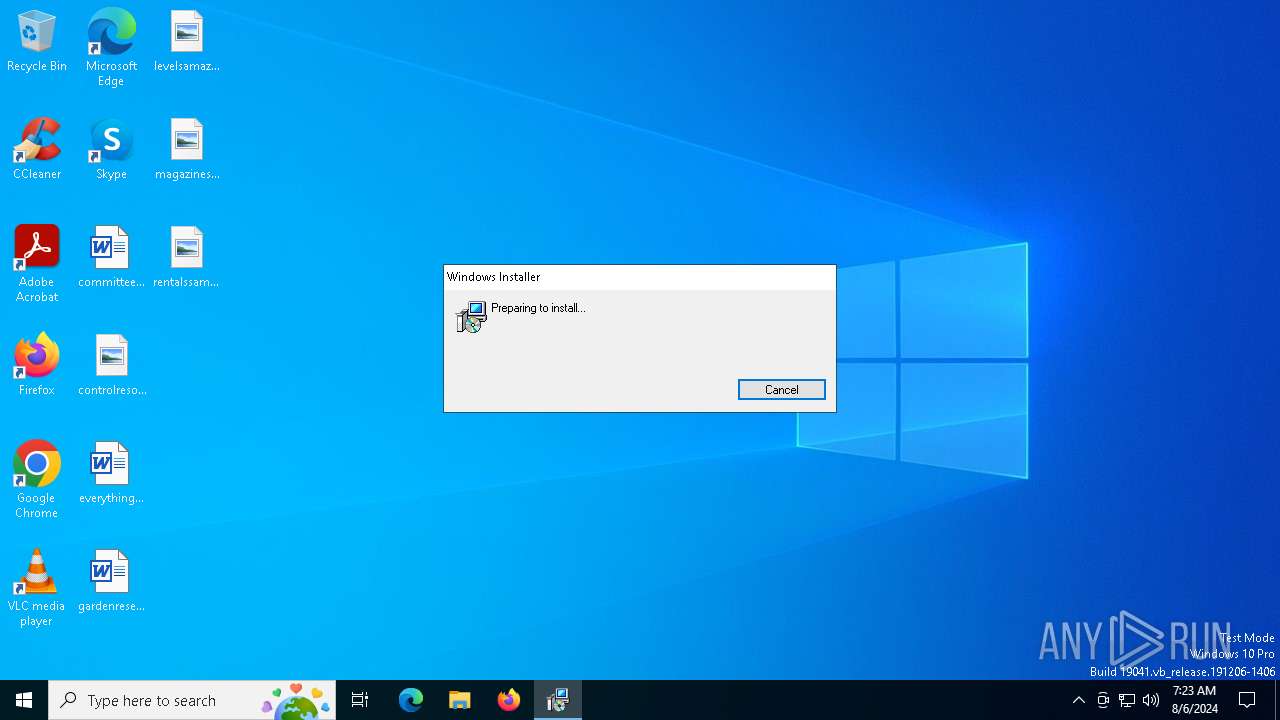
| File name: | Recibo.S.P.E.I_Ref.829137.msi |
| Full analysis: | https://app.any.run/tasks/65a9b5fd-1c1c-4aa2-9583-236600ddb8fd |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2024, 07:22:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Revision Number: {2CFEB00E-64CA-48C5-BF6B-379992800226}, Number of Words: 10, Subject: ERROR CODE HG423, Author: ERROR CODE HG423, Name of Creating Application: ERROR CODE HG423, Template: ;1033, Title: Installation Database, Keywords: Installer, MSI, Database, Security: 0, Create Time/Date: Mon Aug 5 15:58:26 2024, Last Saved Time/Date: Mon Aug 5 15:58:26 2024, Last Printed: Mon Aug 5 15:58:26 2024, Number of Pages: 200 |
| MD5: | 324A2E3F8D76C44B1D7B0E983255A196 |
| SHA1: | 1DB564EE2CBA57983BF62057B8B6CA1E73A3A89A |
| SHA256: | 98A23D306C5169BC4B5772C7B946D61F2C9F552D63BE7D88DD404B87E21D7626 |
| SSDEEP: | 98304:nO6i3FiW+T40rrqqh+S9yIr9UIlXQiNC9m/pF0uzoyDHSZMJT1uAeZdSRzAGcg+o:cUrriOf |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 6600)
- msiexec.exe (PID: 6792)
Scans artifacts that could help determine the target
- msiexec.exe (PID: 644)
SUSPICIOUS
Reads security settings of Internet Explorer
- msiexec.exe (PID: 644)
Executes application which crashes
- msiexec.exe (PID: 644)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6792)
Executes as Windows Service
- VSSVC.exe (PID: 6872)
Checks Windows Trust Settings
- msiexec.exe (PID: 6792)
INFO
Reads the software policy settings
- msiexec.exe (PID: 6600)
- msiexec.exe (PID: 6792)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6600)
Checks proxy server information
- msiexec.exe (PID: 6600)
- msiexec.exe (PID: 644)
Checks supported languages
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 644)
Reads the computer name
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 644)
Creates files or folders in the user directory
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 6600)
Reads Environment values
- msiexec.exe (PID: 644)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6792)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (67.7) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (7.6) |
| .msp | | | Windows Installer Patch (6.3) |
| .mswmm | | | Windows Movie Maker project (5.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| RevisionNumber: | {2CFEB00E-64CA-48C5-BF6B-379992800226} |
| Words: | 10 |
| Subject: | ERROR CODE HG423 |
| Author: | ERROR CODE HG423 |
| LastModifiedBy: | - |
| Software: | ERROR CODE HG423 |
| Template: | ;1033 |
| Comments: | - |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Security: | None |
| CreateDate: | 2024:08:05 15:58:26 |
| ModifyDate: | 2024:08:05 15:58:26 |
| LastPrinted: | 2024:08:05 15:58:26 |
| Pages: | 200 |
Total processes
144
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | C:\Windows\syswow64\MsiExec.exe -Embedding 4132B57DF329878455AF9F561EC39B5F | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 644 -s 1500 | C:\Windows\SysWOW64\WerFault.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 2147942405 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6600 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\Recibo.S.P.E.I_Ref.829137.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1603 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6792 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6840 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6872 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7004 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 644 -s 1492 | C:\Windows\SysWOW64\WerFault.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 2147942405 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 661
Read events
12 438
Write events
199
Delete events
24
Modification events
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000FFC5867CD1E7DA01881A0000AC1A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000FFC5867CD1E7DA01881A0000AC1A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000008796FB7CD1E7DA01881A0000AC1A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000008796FB7CD1E7DA01881A0000AC1A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000E7FAFD7CD1E7DA01881A0000AC1A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000922B057DD1E7DA01881A0000AC1A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000BE50A77DD1E7DA01881A0000AC1A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C7A3A97DD1E7DA01881A0000601B0000E8030000010000000000000000000000CF6491FBD08B724C86ED1527DC01839B00000000000000000000000000000000 | |||
| (PID) Process: | (6872) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003D56BA7DD1E7DA01D81A0000101B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
17
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6792 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6792 | msiexec.exe | C:\Windows\Installer\ed55d.msi | — | |
MD5:— | SHA256:— | |||
| 6600 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | der | |
MD5:15DF9382A3699FE0045F47582E1F4BD0 | SHA256:0F951B2B5CF86E1D19A58C6A5662BA27EDEEEB261D430637228EA12315D54872 | |||
| 6600 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\357F04AD41BCF5FE18FCB69F60C6680F_C065DB5614549C17B6418A4E2F5D744B | der | |
MD5:51EC92747427E1D115B9F22226909D6C | SHA256:B5ABC32D2664090434A3FB0B9423EFEA9DB19F0BC49B08D85BC9FDDF7D9E6AE2 | |||
| 6792 | msiexec.exe | C:\Windows\Temp\~DF215D26F870942461.TMP | binary | |
MD5:001281C4CF2417863F914BA073622047 | SHA256:982399623B20AE3AD46CC60CAC1FCD5275579CE6D40AB44048B23CC22F019C8D | |||
| 6792 | msiexec.exe | C:\Windows\Installer\MSID9F3.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 6600 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:01E5BA6CEE5FB0ADC41521CA85D1F050 | SHA256:1E6E63047DAD1DD63D01584415B551D6682CC5D14A46C7C3C43575615ADB21D8 | |||
| 6600 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\357F04AD41BCF5FE18FCB69F60C6680F_C065DB5614549C17B6418A4E2F5D744B | binary | |
MD5:E18B76024F318EF0ECB23FC15C1B2A46 | SHA256:C8B352D36635CBEC7134254E9B8BB25C575141E675AAC109CA9B6E84309AE2B0 | |||
| 6792 | msiexec.exe | C:\Windows\Temp\~DFEB077F71D9DC98D4.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 6792 | msiexec.exe | C:\Windows\Installer\MSID8E8.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
47
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6600 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6600 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDBHSEhF8fFrMWVTJEA%3D%3D | unknown | — | — | whitelisted |
6232 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
644 | msiexec.exe | GET | 404 | 147.45.78.104:80 | http://147.45.78.104/down2/zaa0508.zip?DESKTOP-JGLLJLD | unknown | — | — | unknown |
3376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6208 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2656 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1120 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1884 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 104.18.20.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | shared |
5336 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |