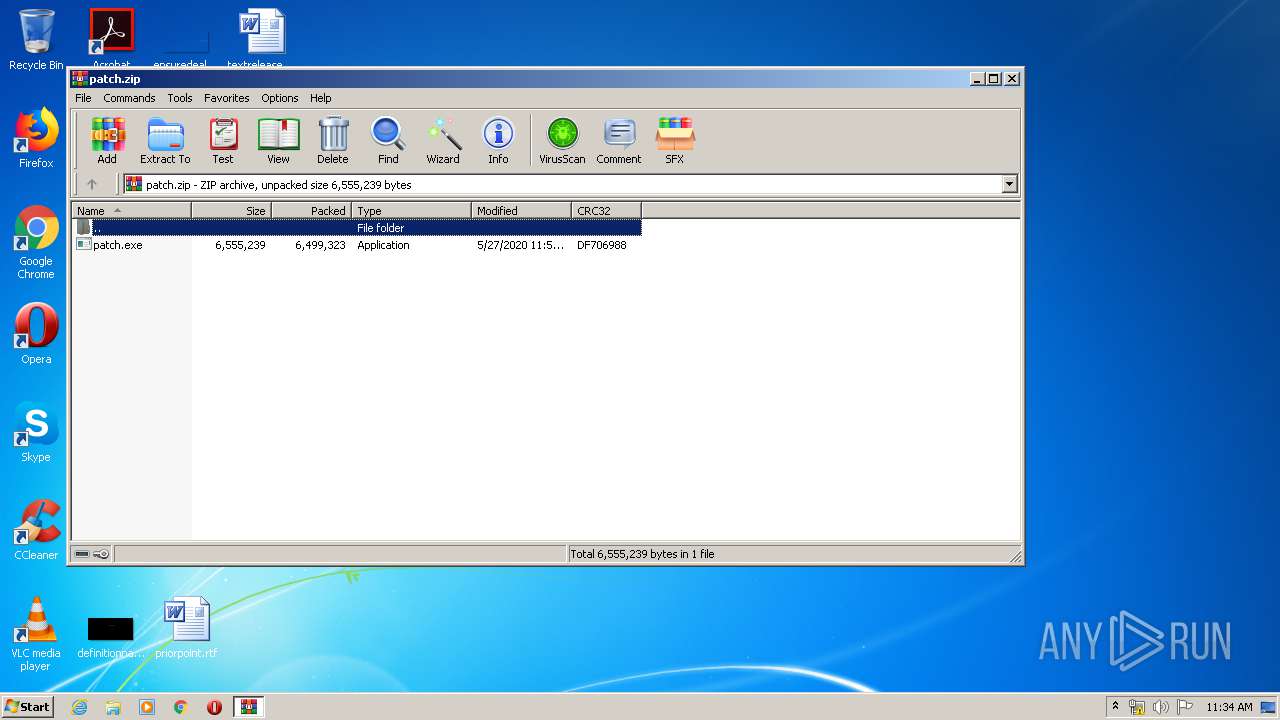
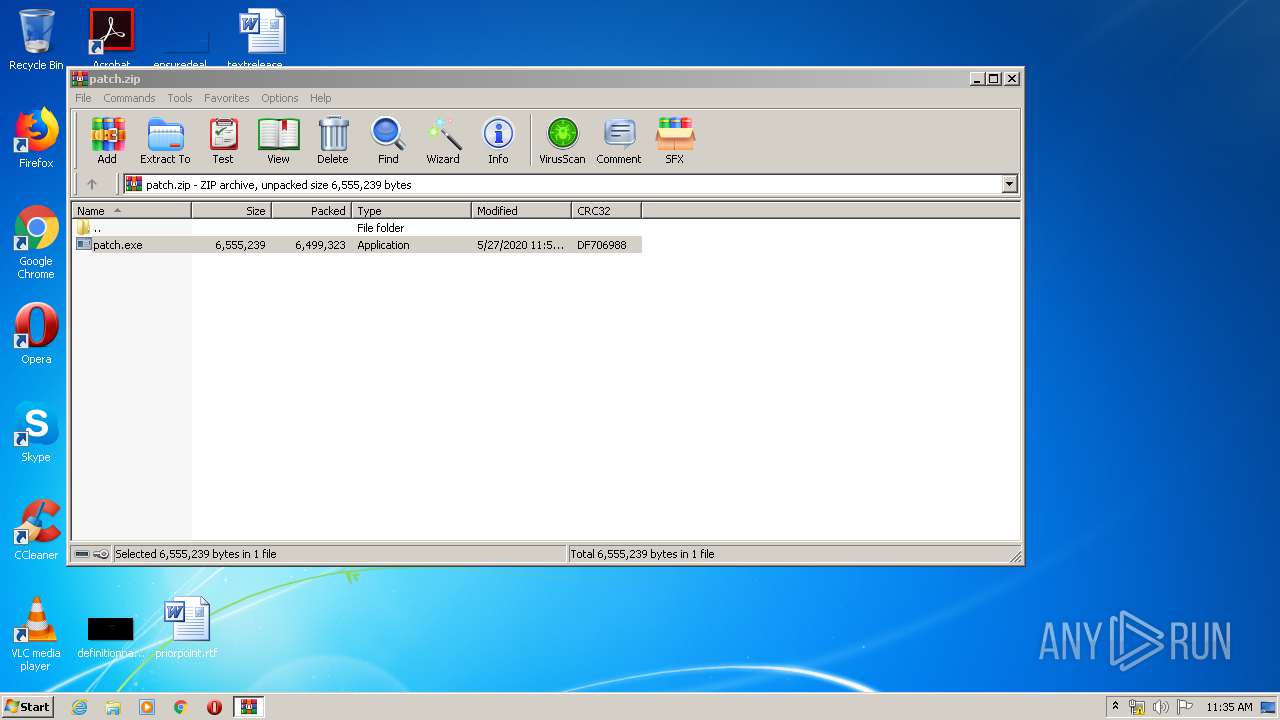
| File name: | patch.zip |
| Full analysis: | https://app.any.run/tasks/6a6e4989-c103-4d25-9912-71117be45cd8 |
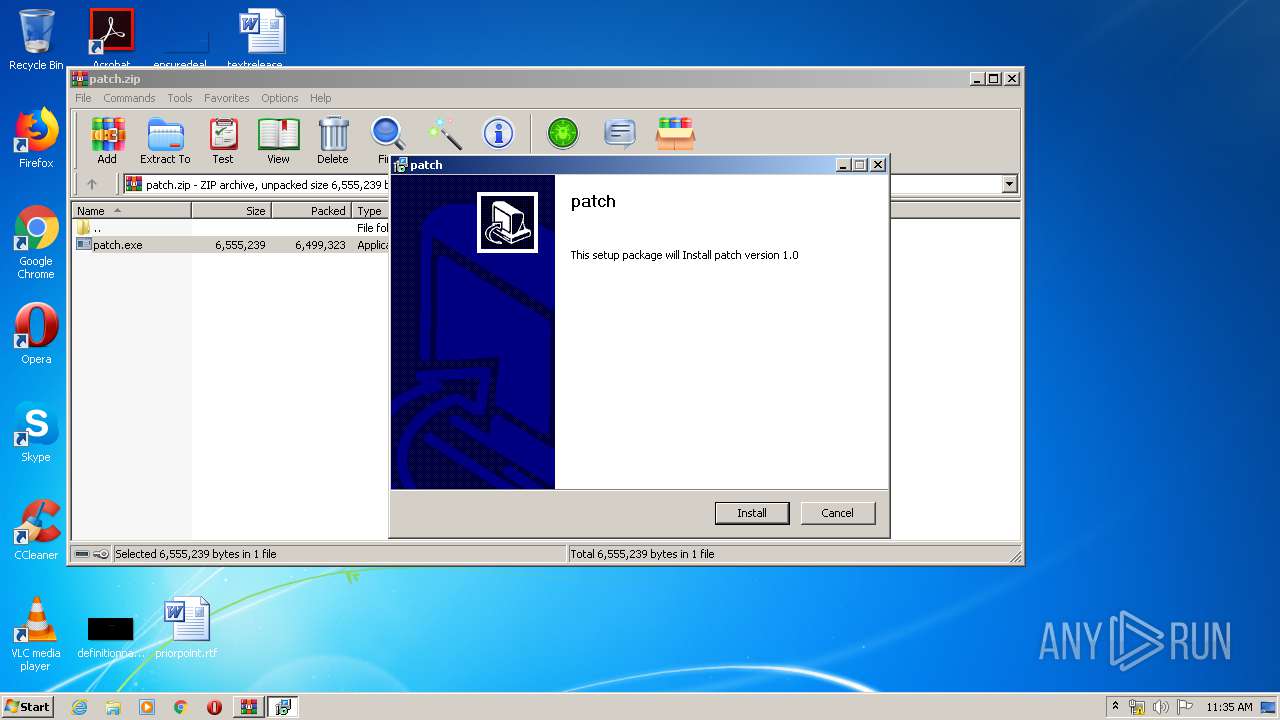
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2020, 10:34:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E39603F6C7ECE18EC87C8FCB5B003772 |
| SHA1: | 5AE8FC79B2F546E22AC9BCE7522961A08E8A6163 |
| SHA256: | 989DAB01753E382C4279AAA8D98A06C1BBCF260A33245BABAAEA2204AFC85998 |
| SSDEEP: | 196608:s3wD9c+/KKHYOHf4C8XwF5VyM+TTSDWVF6nmWYR7SeSTtie3oPj:swWLK4WfUw3QMuuyVF6mxRocxj |
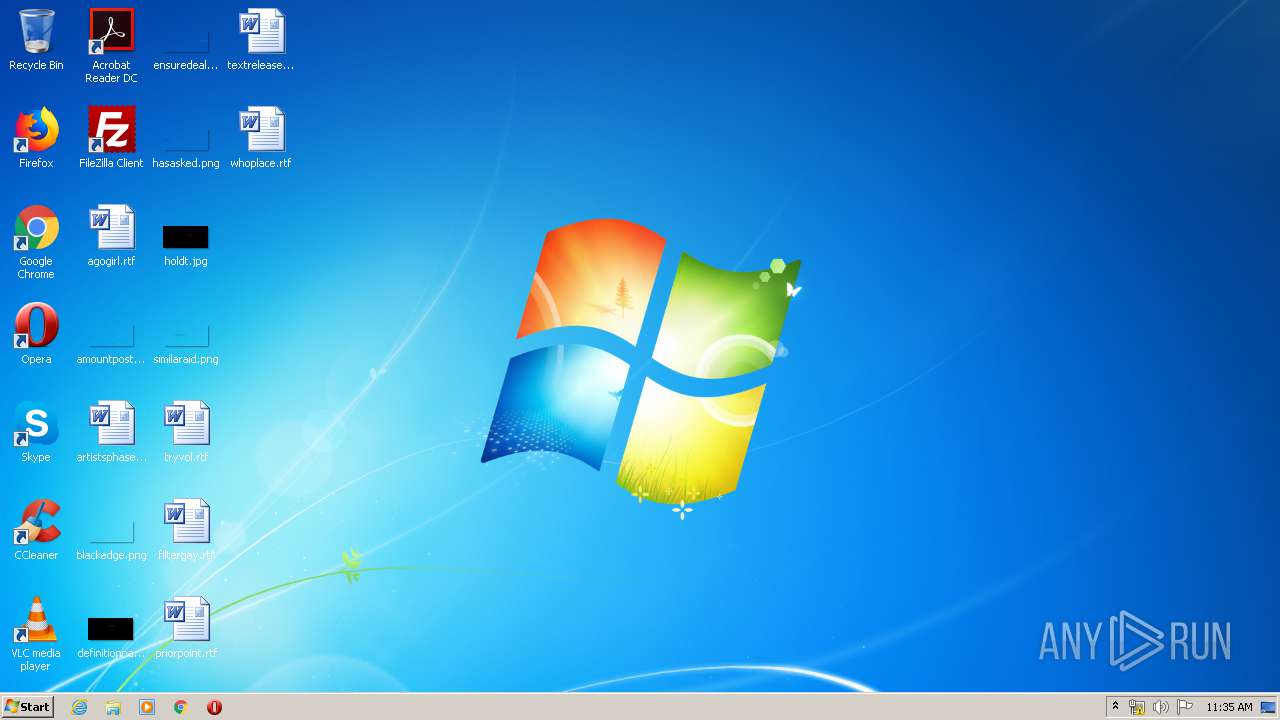
MALICIOUS
Loads dropped or rewritten executable
- patch.exe (PID: 4064)
- patch.exe (PID: 2268)
Changes settings of System certificates
- svctcom.exe (PID: 1352)
- msiexec.exe (PID: 3768)
Application was dropped or rewritten from another process
- svctcom.exe (PID: 1352)
- syschk.exe (PID: 2472)
- scthost.exe (PID: 2144)
- patch.exe (PID: 2268)
- patch.exe (PID: 4064)
Writes to the hosts file
- svctcom.exe (PID: 1352)
Actions looks like stealing of personal data
- WinRAR.exe (PID: 1348)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1348)
- msiexec.exe (PID: 3768)
- patch.exe (PID: 2268)
- patch.exe (PID: 4064)
Creates files in the Windows directory
- svctcom.exe (PID: 1352)
- msiexec.exe (PID: 3768)
- syschk.exe (PID: 2472)
Executed as Windows Service
- svctcom.exe (PID: 1352)
Executed via COM
- DllHost.exe (PID: 3848)
- DeviceDisplayObjectProvider.exe (PID: 784)
Application launched itself
- patch.exe (PID: 2268)
Removes files from Windows directory
- svctcom.exe (PID: 1352)
Starts CMD.EXE for commands execution
- svctcom.exe (PID: 1352)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1220)
- cmd.exe (PID: 2496)
Adds / modifies Windows certificates
- svctcom.exe (PID: 1352)
- msiexec.exe (PID: 3768)
Creates files in the user directory
- scthost.exe (PID: 2144)
Starts Microsoft Installer
- patch.exe (PID: 4064)
Creates a software uninstall entry
- patch.exe (PID: 4064)
INFO
Reads settings of System Certificates
- msiexec.exe (PID: 3768)
Application launched itself
- msiexec.exe (PID: 3768)
Creates a software uninstall entry
- msiexec.exe (PID: 3768)
Reads the hosts file
- svctcom.exe (PID: 1352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
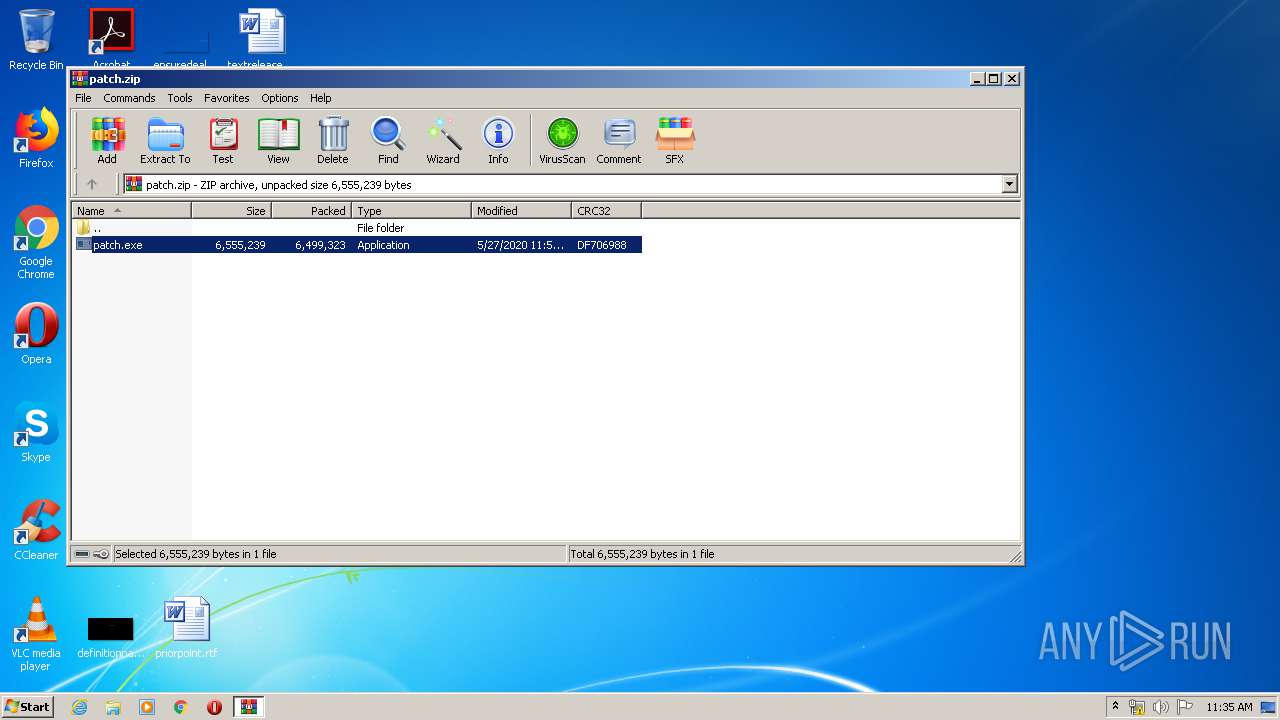
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:05:27 11:53:17 |
| ZipCRC: | 0xdf706988 |
| ZipCompressedSize: | 6499323 |
| ZipUncompressedSize: | 6555239 |
| ZipFileName: | patch.exe |
Total processes
56
Monitored processes
16
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
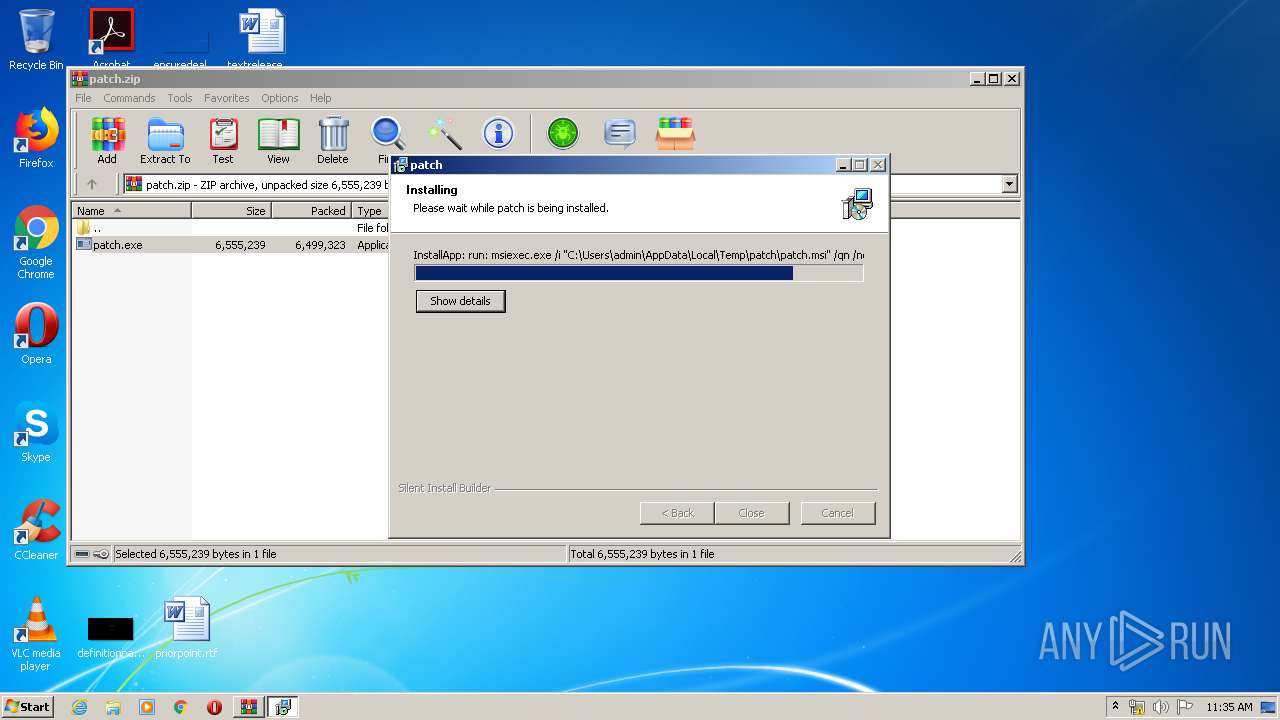
| 676 | msiexec.exe /i "C:\Users\admin\AppData\Local\Temp\patch\patch.msi" /qn /norestart | C:\Windows\system32\msiexec.exe | — | patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 784 | C:\Windows\system32\DeviceDisplayObjectProvider.exe -Embedding | C:\Windows\system32\DeviceDisplayObjectProvider.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Display Object Function Discovery Provider Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | C:\Windows\system32\MsiExec.exe -Embedding 3833C95EDC4FDFDD03DEE515FCB6A92E M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1220 | C:\Windows\system32\cmd.exe /c taskkill /F /IM scthost.exe | C:\Windows\system32\cmd.exe | — | svctcom.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1348 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\patch.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1352 | C:\Windows\system32\svctcom.exe | C:\Windows\system32\svctcom.exe | services.exe | ||||||||||||
User: SYSTEM Company: Birch Grove Software, Inc. Integrity Level: SYSTEM Description: Host Process for Com Exit code: 0 Version: 8.1.2.0 Modules
| |||||||||||||||
| 2144 | scthost.exe | C:\Windows\system32\scthost.exe | svctcom.exe | ||||||||||||
User: admin Company: Birch Grove Software, Inc. Integrity Level: HIGH Description: Host Process for Modules Exit code: 0 Version: 8.1.2.0 Modules
| |||||||||||||||
| 2268 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1348.2888\patch.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1348.2888\patch.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2332 | C:\Windows\system32\MsiExec.exe -Embedding 494DC4D481712734C1A4D91B637D7424 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | taskkill /F /IM scthost.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 884
Read events
1 504
Write events
1 366
Delete events
14
Modification events
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\patch.zip | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
14
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4064 | patch.exe | C:\Users\admin\AppData\Local\Temp\patch\patch.msi | — | |
MD5:— | SHA256:— | |||
| 3768 | msiexec.exe | C:\Windows\Installer\10b96e.msi | — | |
MD5:— | SHA256:— | |||
| 3768 | msiexec.exe | C:\Windows\Installer\MSIC8E0.tmp | — | |
MD5:— | SHA256:— | |||
| 3768 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF19C225AD05A77BE0.TMP | — | |
MD5:— | SHA256:— | |||
| 3768 | msiexec.exe | C:\Windows\Installer\MSICA49.tmp | — | |
MD5:— | SHA256:— | |||
| 3768 | msiexec.exe | C:\Windows\Installer\10b972.msi | — | |
MD5:— | SHA256:— | |||
| 1352 | svctcom.exe | C:\Windows\system32\aamdata\aamfetch-journal | — | |
MD5:— | SHA256:— | |||
| 3768 | msiexec.exe | C:\Config.Msi\10b971.rbs | — | |
MD5:— | SHA256:— | |||
| 3768 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF697C7601069F57B2.TMP | — | |
MD5:— | SHA256:— | |||
| 1348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1348.2888\patch.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4064 | patch.exe | POST | — | 216.58.207.46:80 | http://www.google-analytics.com/collect | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4064 | patch.exe | 216.58.207.46:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
1352 | svctcom.exe | 35.241.40.95:443 | backend.activtrak.net | — | US | unknown |
2144 | scthost.exe | 3.213.25.167:443 | ws.activtrak.net | — | US | unknown |
1352 | svctcom.exe | 216.239.38.21:443 | backend-gcp-us.activtrak.net | Google Inc. | US | whitelisted |
2144 | scthost.exe | 35.241.40.95:443 | backend.activtrak.net | — | US | unknown |
2144 | scthost.exe | 216.239.36.21:443 | backend-gcp-us.activtrak.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
backend.activtrak.net |
| malicious |
ws.activtrak.net |
| unknown |
backend-gcp-us.activtrak.net |
| malicious |