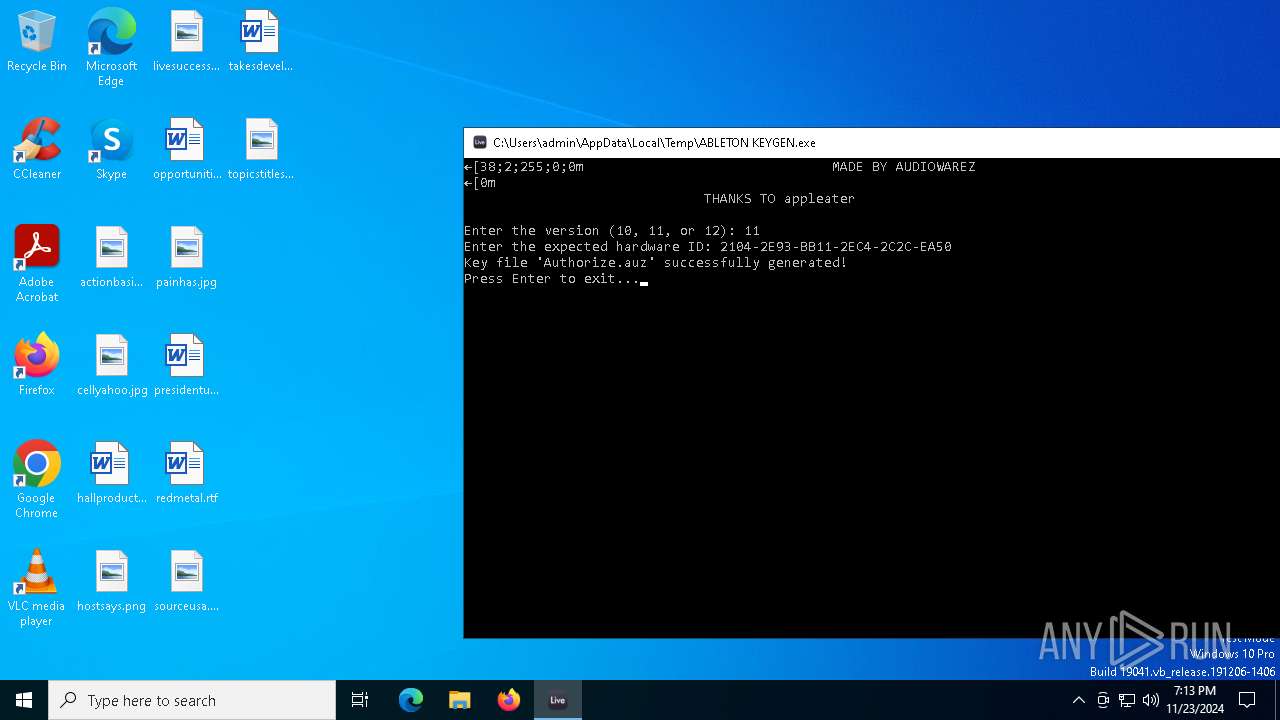
| File name: | ABLETON KEYGEN.exe |
| Full analysis: | https://app.any.run/tasks/190cf6d6-b143-4060-8855-982935a5aed9 |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2024, 19:12:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | BEF1E3AD5AB1F1DB255AF1A5E5851CDB |
| SHA1: | 1089364EDC57F3C6B962C64EF59D4AD8AD34DC91 |
| SHA256: | 98860AB48BDF40AE51BB4B3608A4FB2F1D37A6F9ED417805932DEEE2D85A67EE |
| SSDEEP: | 98304:3Su//4Om/3woyfSjy+yrlm/KazuO+49jqwMPQARgpiXXjAMeiAtJPga+LzF+SoVk:HiaNBW/1T8cpaT8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- ABLETON KEYGEN.exe (PID: 4504)
Process drops python dynamic module
- ABLETON KEYGEN.exe (PID: 4504)
Process drops legitimate windows executable
- ABLETON KEYGEN.exe (PID: 4504)
Executable content was dropped or overwritten
- ABLETON KEYGEN.exe (PID: 4504)
Application launched itself
- ABLETON KEYGEN.exe (PID: 4504)
Loads Python modules
- ABLETON KEYGEN.exe (PID: 2800)
INFO
Checks supported languages
- ABLETON KEYGEN.exe (PID: 4504)
- ABLETON KEYGEN.exe (PID: 2800)
Reads the computer name
- ABLETON KEYGEN.exe (PID: 4504)
Create files in a temporary directory
- ABLETON KEYGEN.exe (PID: 4504)
- ABLETON KEYGEN.exe (PID: 2800)
Reads the machine GUID from the registry
- ABLETON KEYGEN.exe (PID: 2800)
PyInstaller has been detected (YARA)
- ABLETON KEYGEN.exe (PID: 4504)
- ABLETON KEYGEN.exe (PID: 2800)
Application based on Rust
- ABLETON KEYGEN.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:12:07 19:03:09+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.37 |
| CodeSize: | 171520 |
| InitializedDataSize: | 97792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb680 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
127
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ABLETON KEYGEN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\AppData\Local\Temp\ABLETON KEYGEN.exe" | C:\Users\admin\AppData\Local\Temp\ABLETON KEYGEN.exe | — | ABLETON KEYGEN.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4504 | "C:\Users\admin\AppData\Local\Temp\ABLETON KEYGEN.exe" | C:\Users\admin\AppData\Local\Temp\ABLETON KEYGEN.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4976 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
251
Read events
251
Write events
0
Delete events
0
Modification events
Executable files
13
Suspicious files
1
Text files
9
Unknown types
0
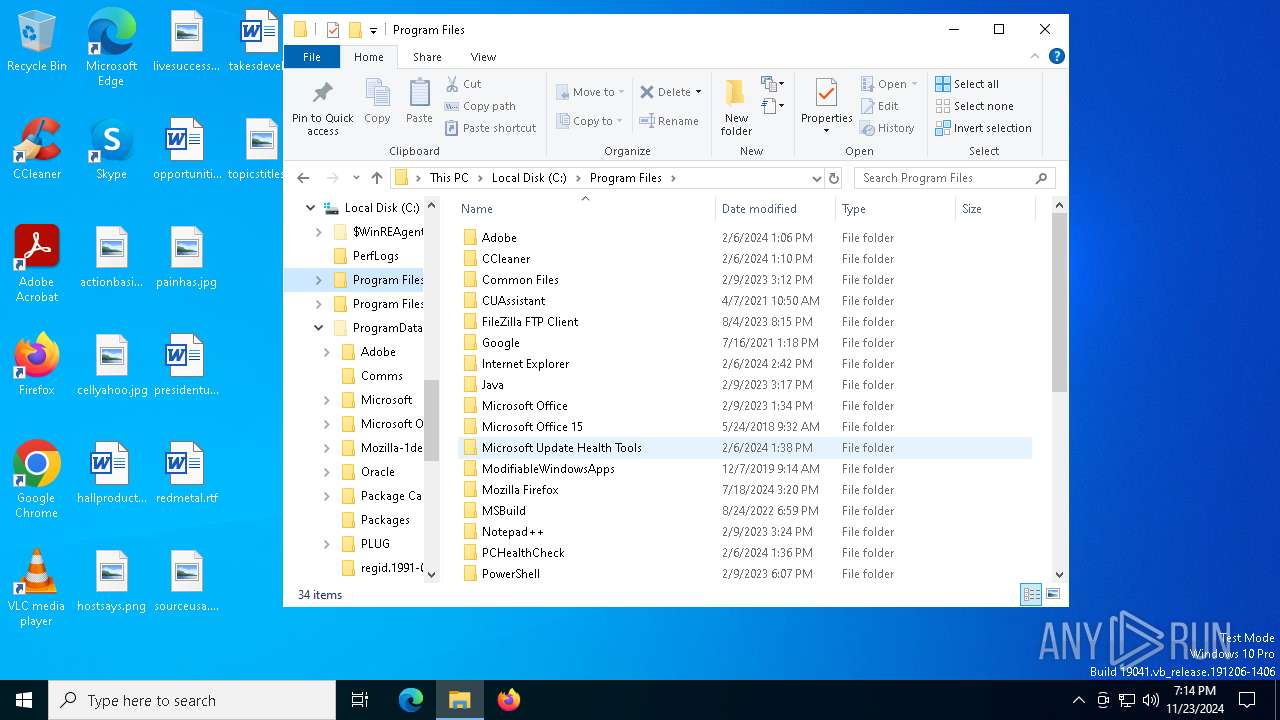
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\_cffi_backend.cp310-win_amd64.pyd | executable | |
MD5:6F1B90884343F717C5DC14F94EF5ACEA | SHA256:2093E7E4F5359B38F0819BDEF8314FDA332A1427F22E09AFC416E1EDD5910FE1 | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\_decimal.pyd | executable | |
MD5:10F7B96C666F332EC512EDADE873EECB | SHA256:6314C99A3EFA15307E7BDBE18C0B49BC841C734F42923A0B44AAB42ED7D4A62D | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\_hashlib.pyd | executable | |
MD5:49CE7A28E1C0EB65A9A583A6BA44FA3B | SHA256:1BE5CFD06A782B2AE8E4629D9D035CBC487074E8F63B9773C85E317BE29C0430 | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\_lzma.pyd | executable | |
MD5:B5FBC034AD7C70A2AD1EB34D08B36CF8 | SHA256:80A6EBE46F43FFA93BBDBFC83E67D6F44A44055DE1439B06E4DD2983CB243DF6 | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\_socket.pyd | executable | |
MD5:E137DF498C120D6AC64EA1281BCAB600 | SHA256:8046BF64E463D5AA38D13525891156131CF997C2E6CDF47527BC352F00F5C90A | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\VCRUNTIME140.dll | executable | |
MD5:F12681A472B9DD04A812E16096514974 | SHA256:D66C3B47091CEB3F8D3CC165A43D285AE919211A0C0FCB74491EE574D8D464F8 | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\cryptography\hazmat\bindings\_rust.pyd | executable | |
MD5:23B2D3AAC2A873E981C0539EEA21D2B3 | SHA256:58339E750FD6CEE450AA21FBBD1657C78EF84B9D35503750696372C8AA845EC7 | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\base_library.zip | compressed | |
MD5:D588EC43695A4571E2BCB17C183A767A | SHA256:1036B9A6A53021902D4563FA968F48041CB99F0E9650C3D6EBB7B1129F07CB70 | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\cryptography-41.0.3.dist-info\RECORD | csv | |
MD5:D135049F78F883F22BB21DFBFDC64D91 | SHA256:F44809121757BD237D0850DD01901FD1A2F6717849203A5EE54CCE3EFBD0DA24 | |||
| 4504 | ABLETON KEYGEN.exe | C:\Users\admin\AppData\Local\Temp\_MEI45042\cryptography-41.0.3.dist-info\METADATA | text | |
MD5:5FD999CE35D911A5B8024F8B37325743 | SHA256:B73BBFE161BE8116A983104049C67260C1DF4DC87A55906B08C2BAE258C0AA3B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
30
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3836 | svchost.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3836 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4876 | SIHClient.exe | GET | 200 | 184.28.66.24:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4876 | SIHClient.exe | GET | 200 | 184.28.66.24:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4816 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
3836 | svchost.exe | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3836 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |