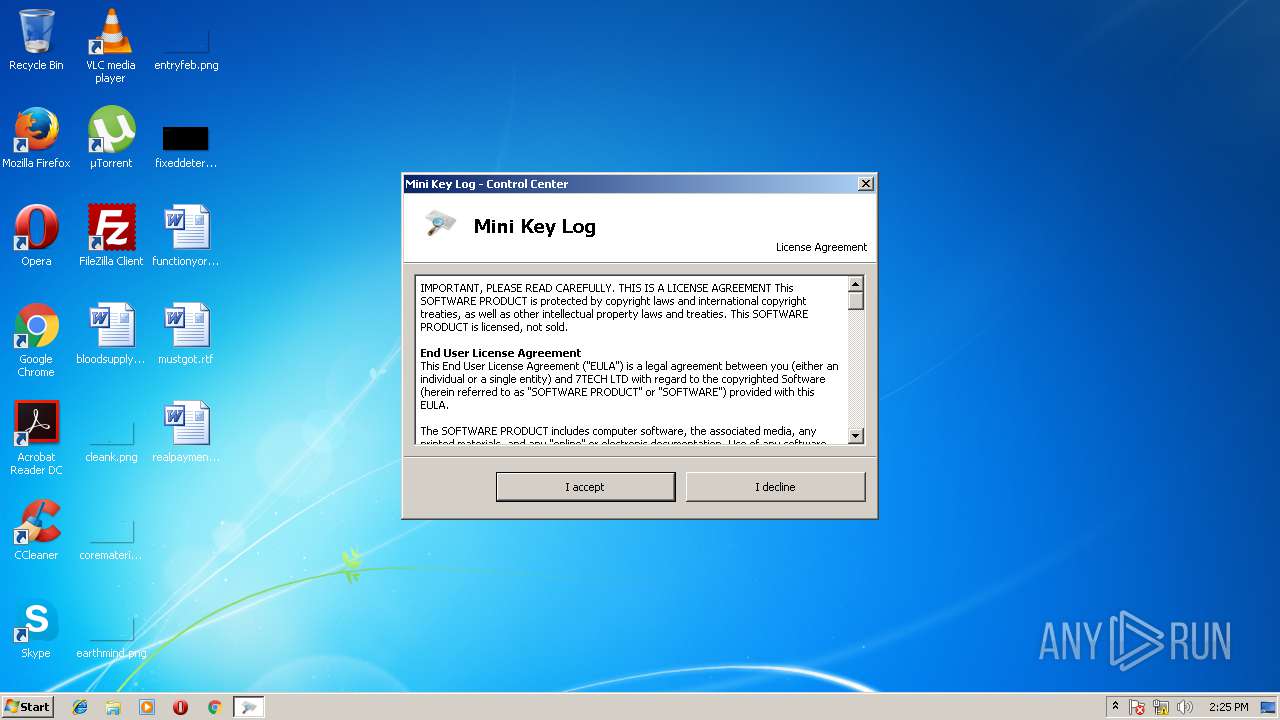
| download: | MiniKeyLog.exe |
| Full analysis: | https://app.any.run/tasks/28023362-4173-496c-9b11-d26d185b1c98 |
| Verdict: | Malicious activity |
| Analysis date: | May 03, 2018, 13:25:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6846EC302F18CF3AE9A3A078055F317E |
| SHA1: | 41378B5D8E9FB17ABD7B3ADA8F9A20FC2ADCF4BA |
| SHA256: | 987959CA623374EE89F22C8CDC68E32CD045D2272C7349EA9326B1E299338DFF |
| SSDEEP: | 98304:kZ56+IQvWxoneckTboM595A9jV8I2Oy10PZG2zjWoIAfWQV1x1j3qV33BGwNcPB:G56+I3BdXT0xHF8OM2moIAfWIt30Xcp |
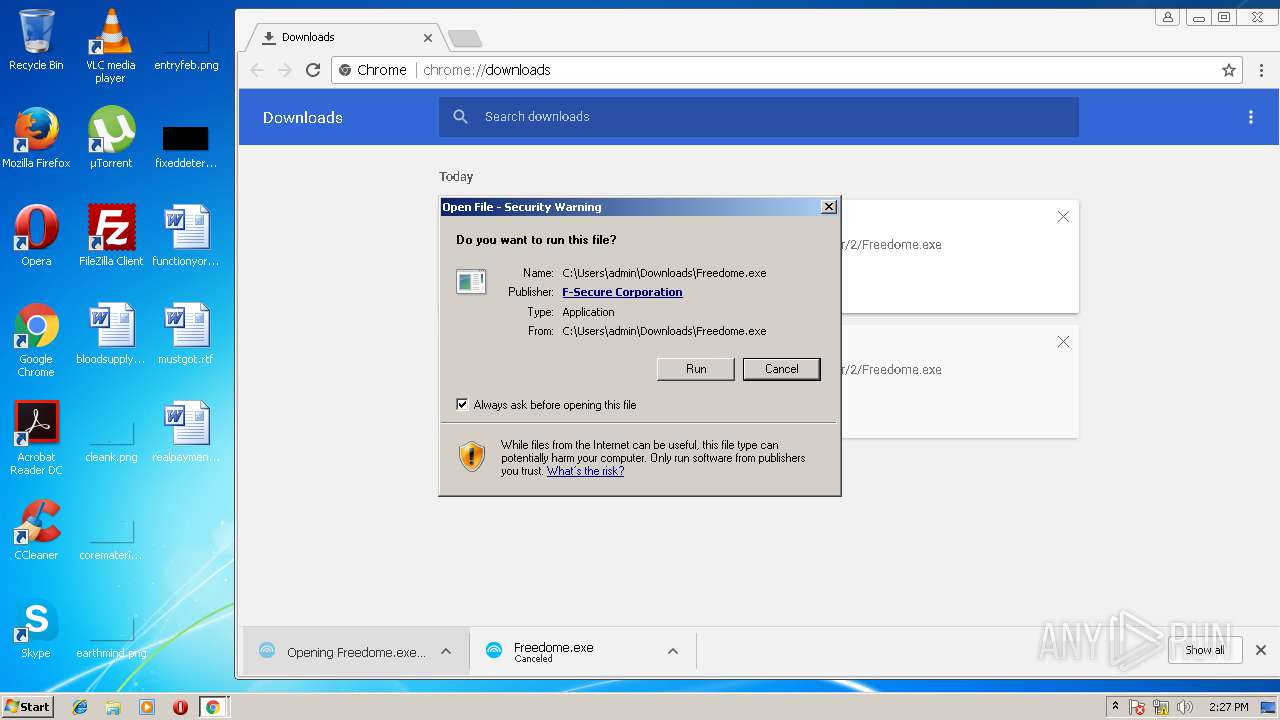
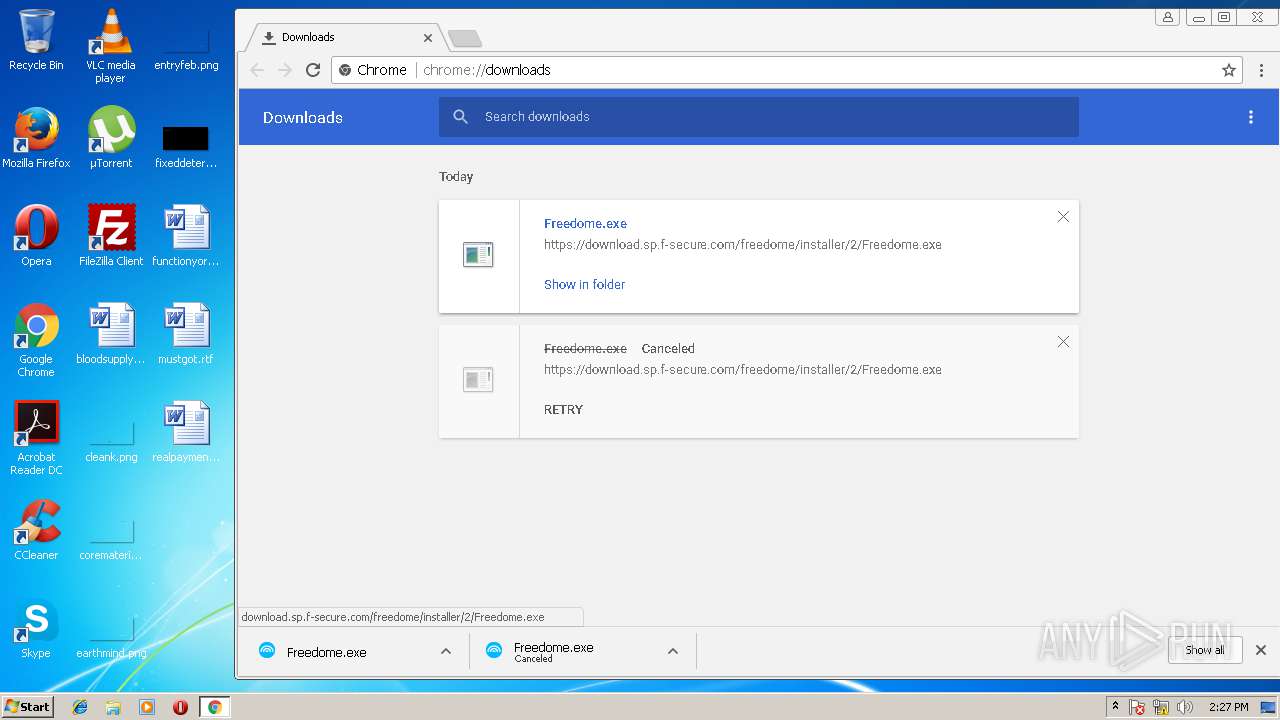
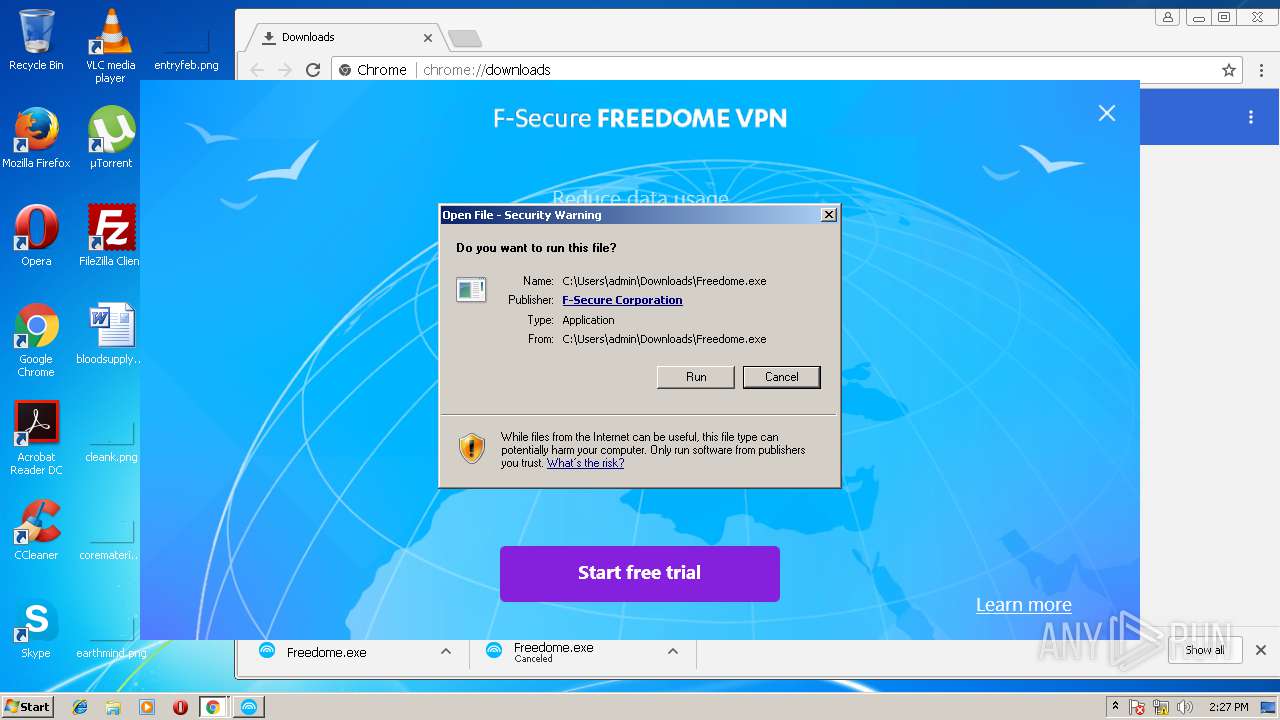
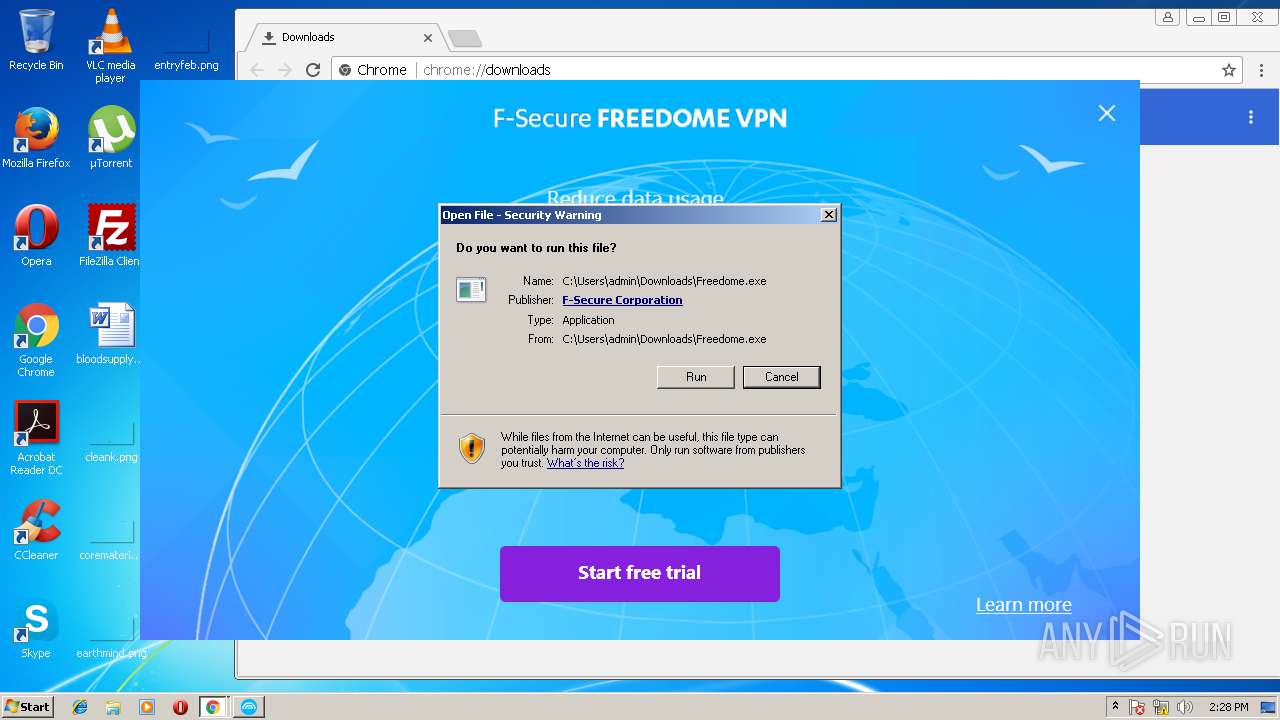
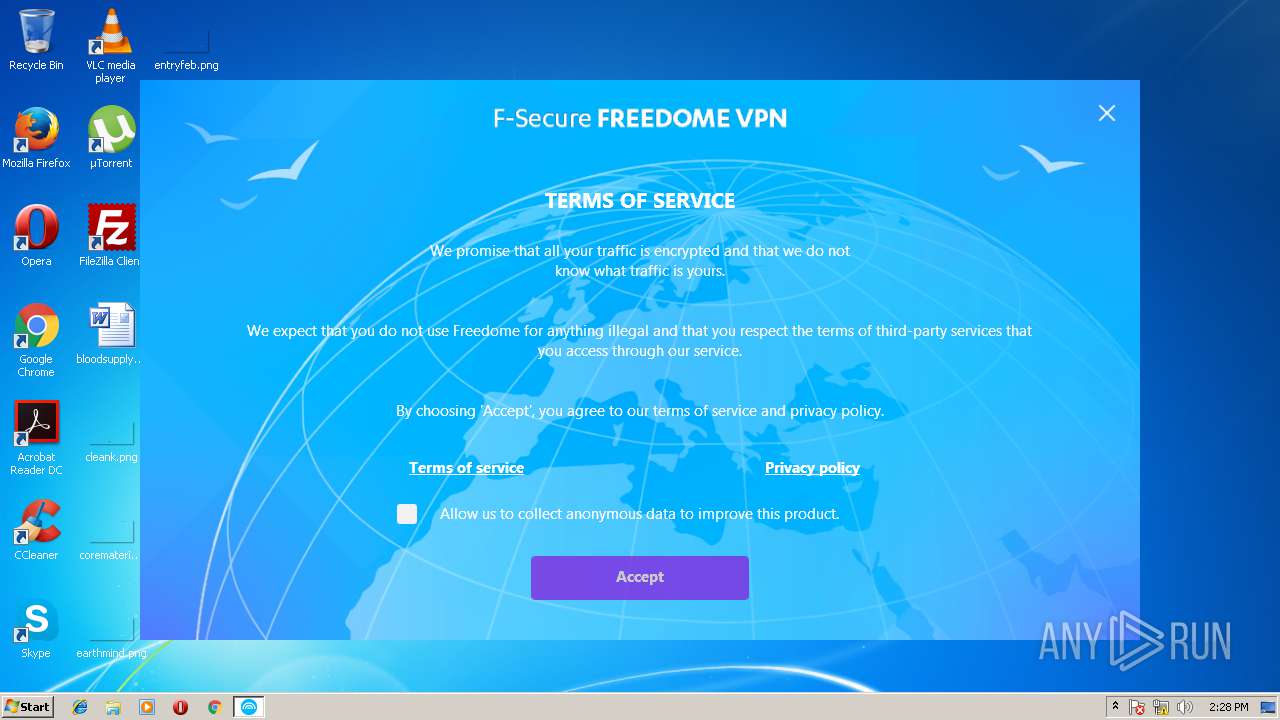
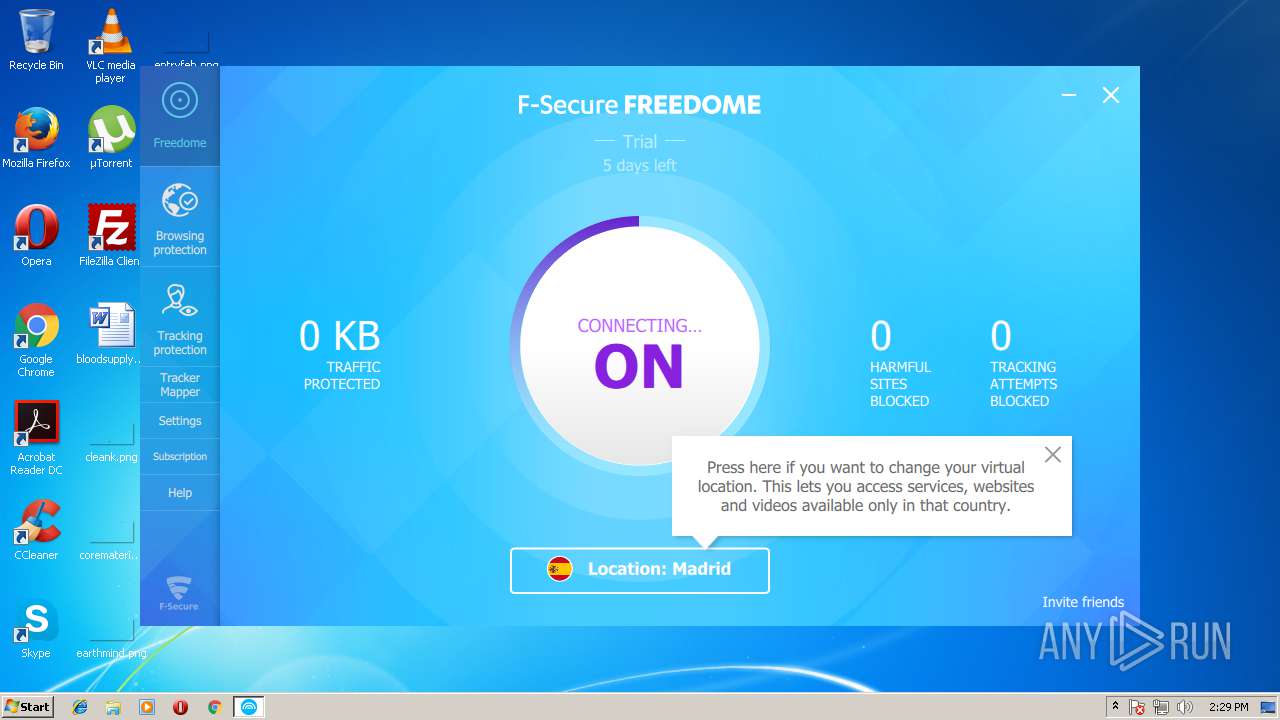
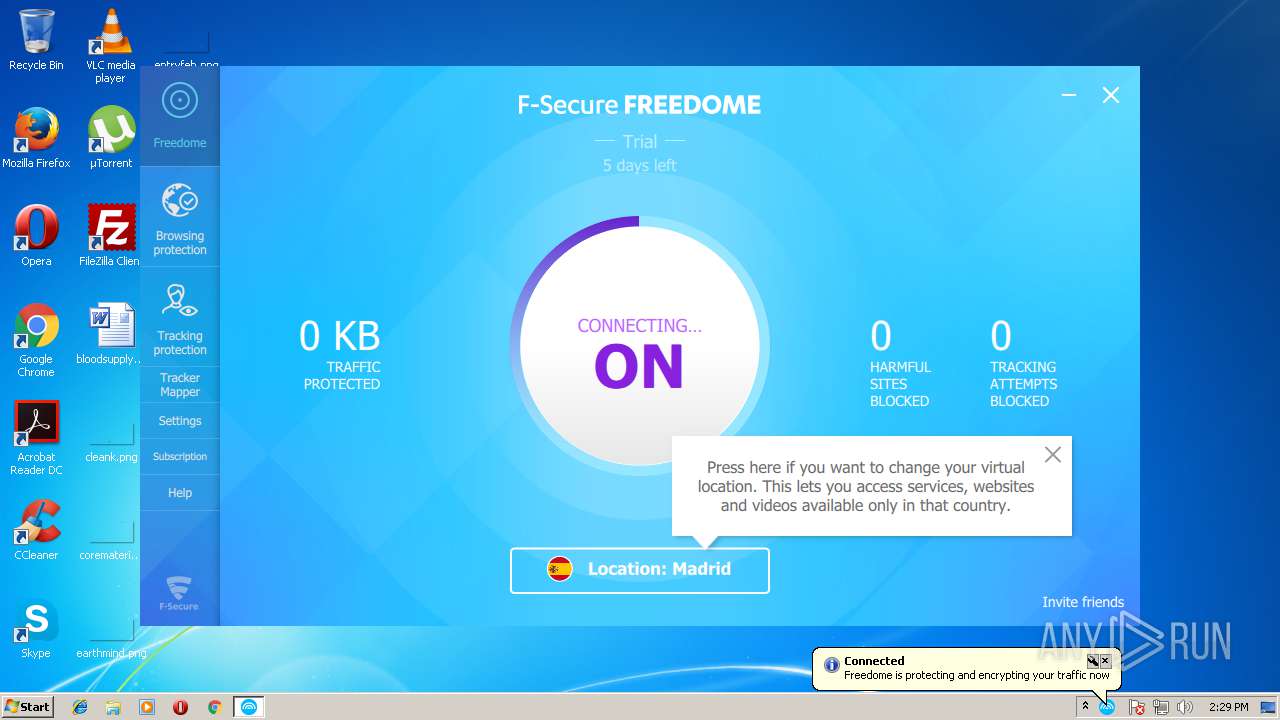
MALICIOUS
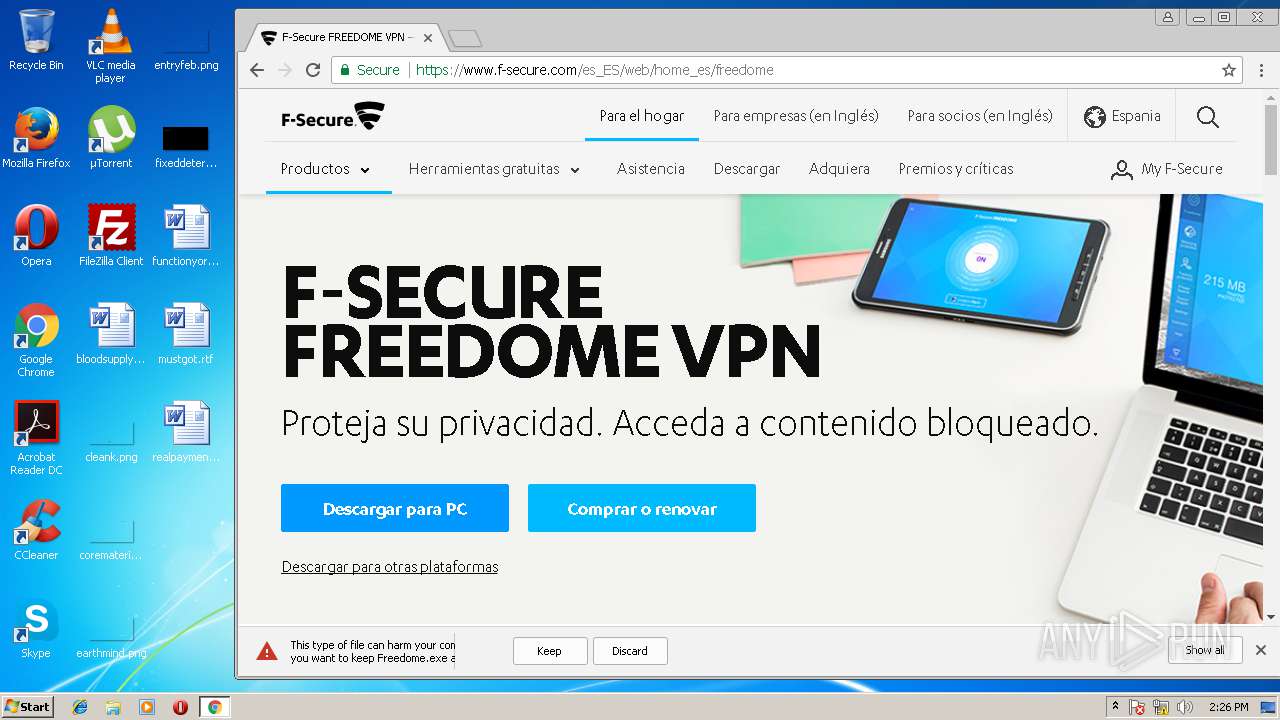
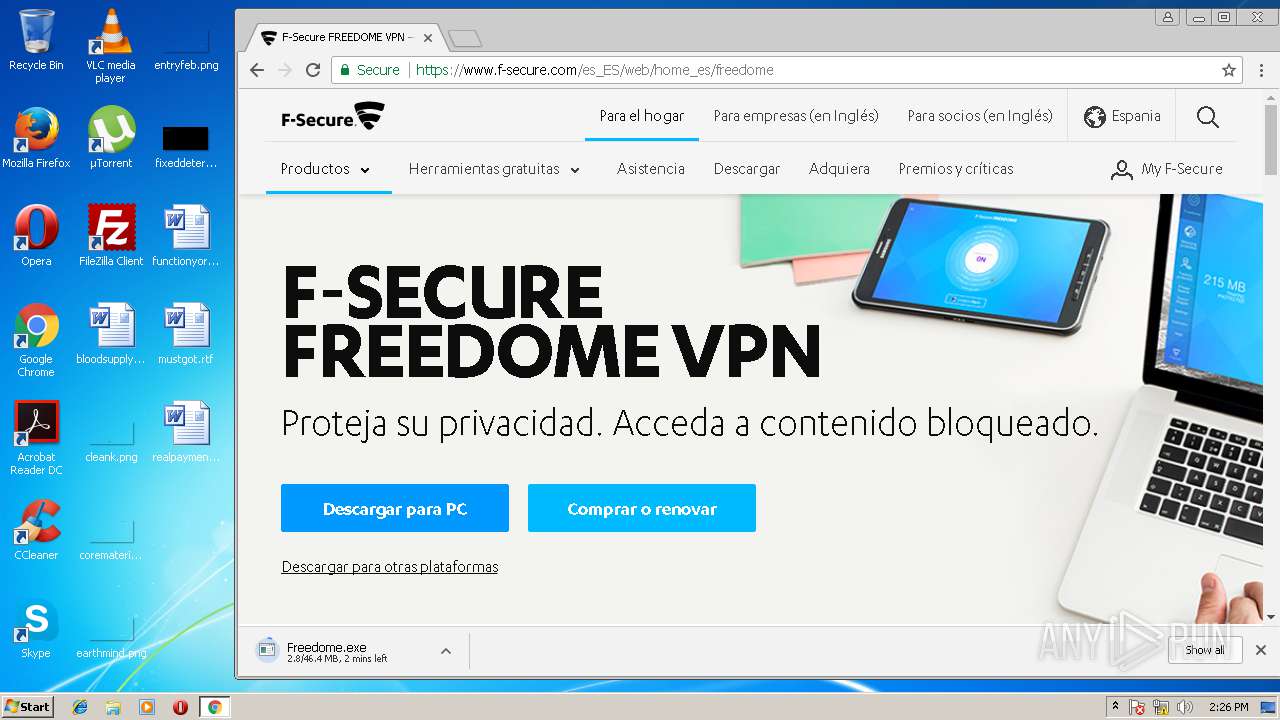
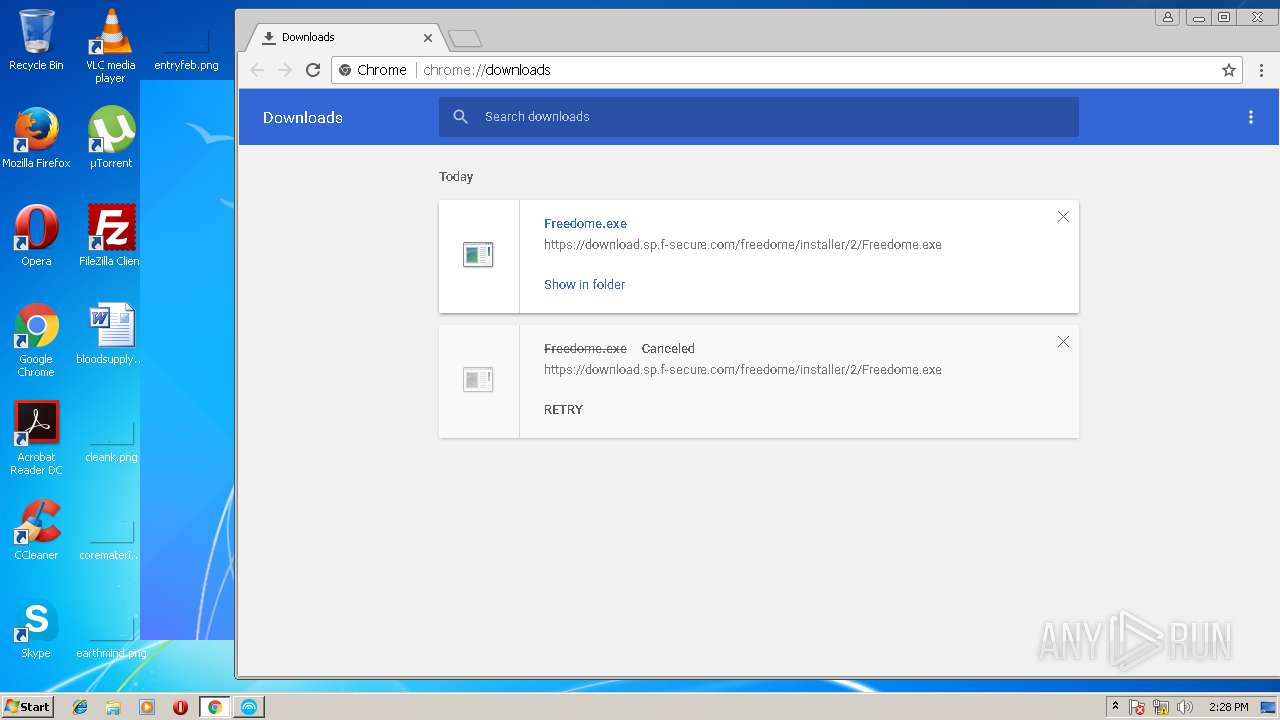
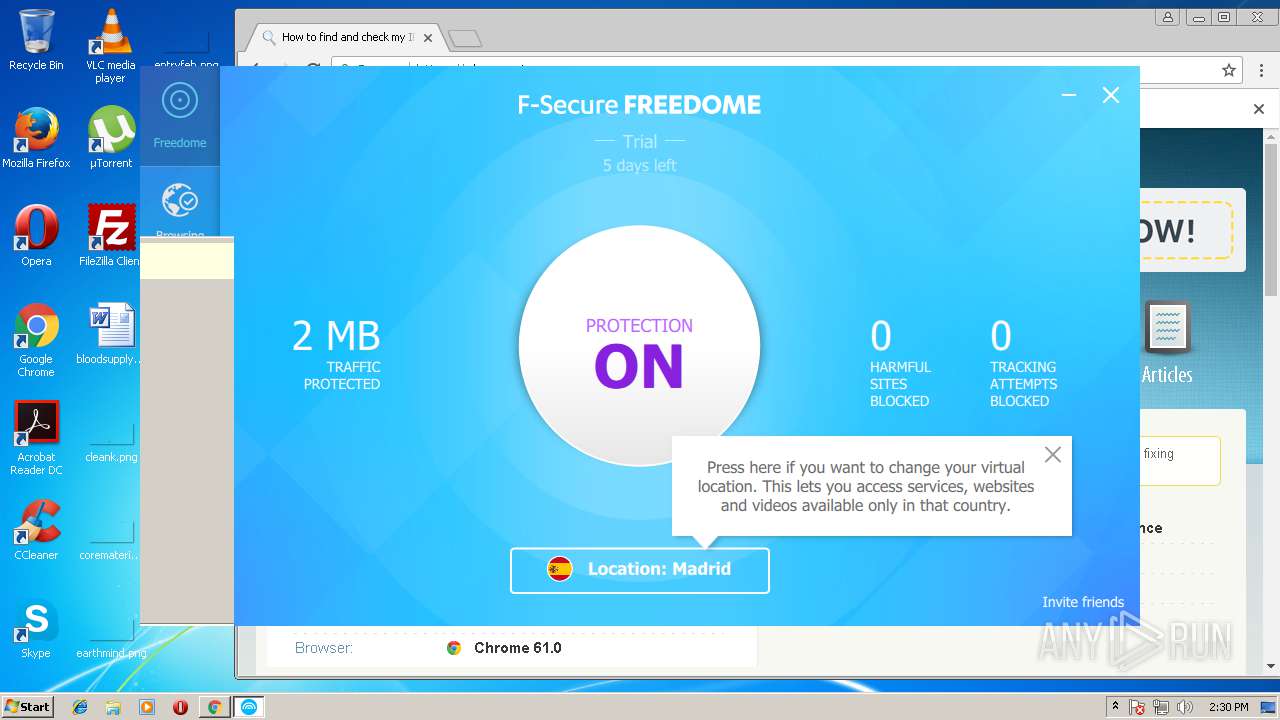
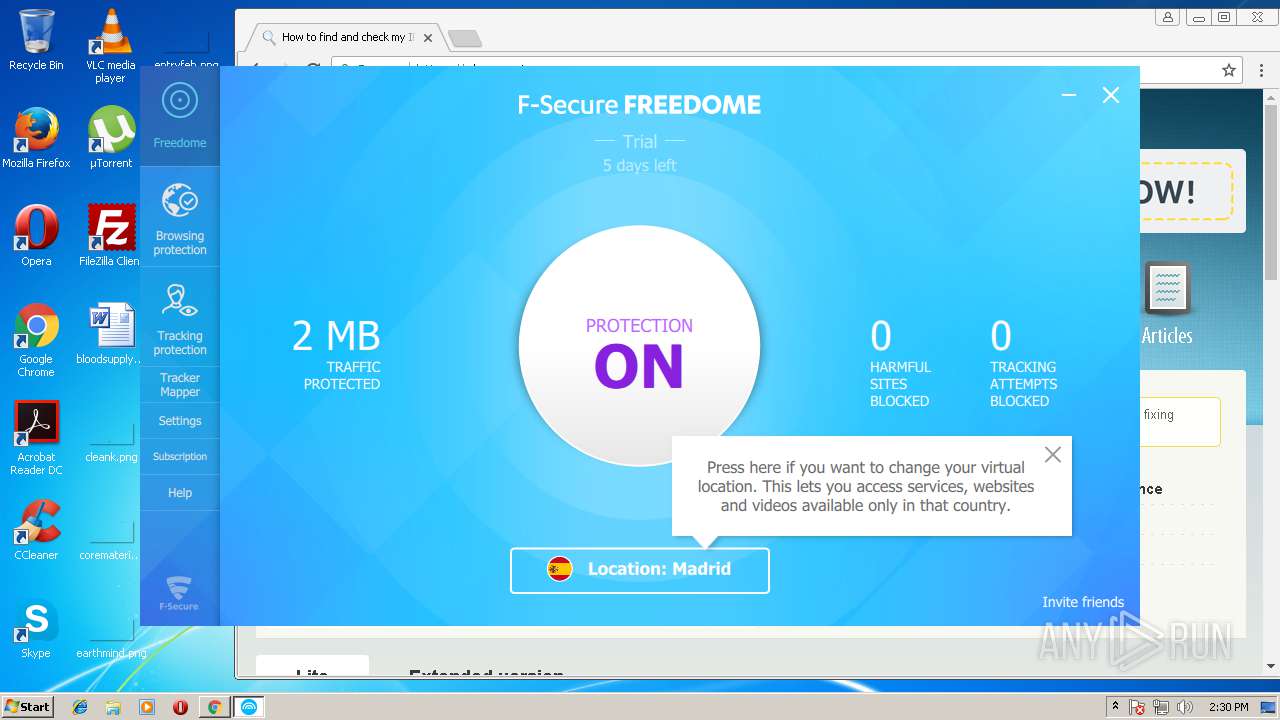
Application was dropped or rewritten from another process
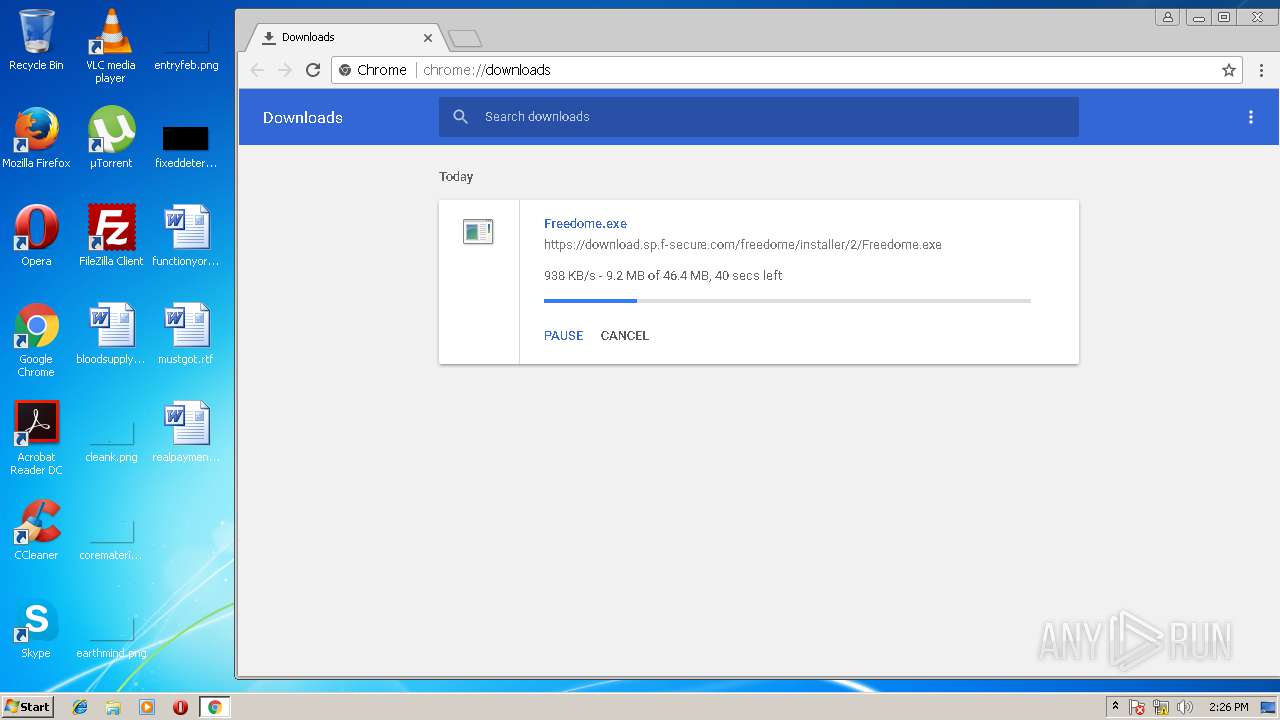
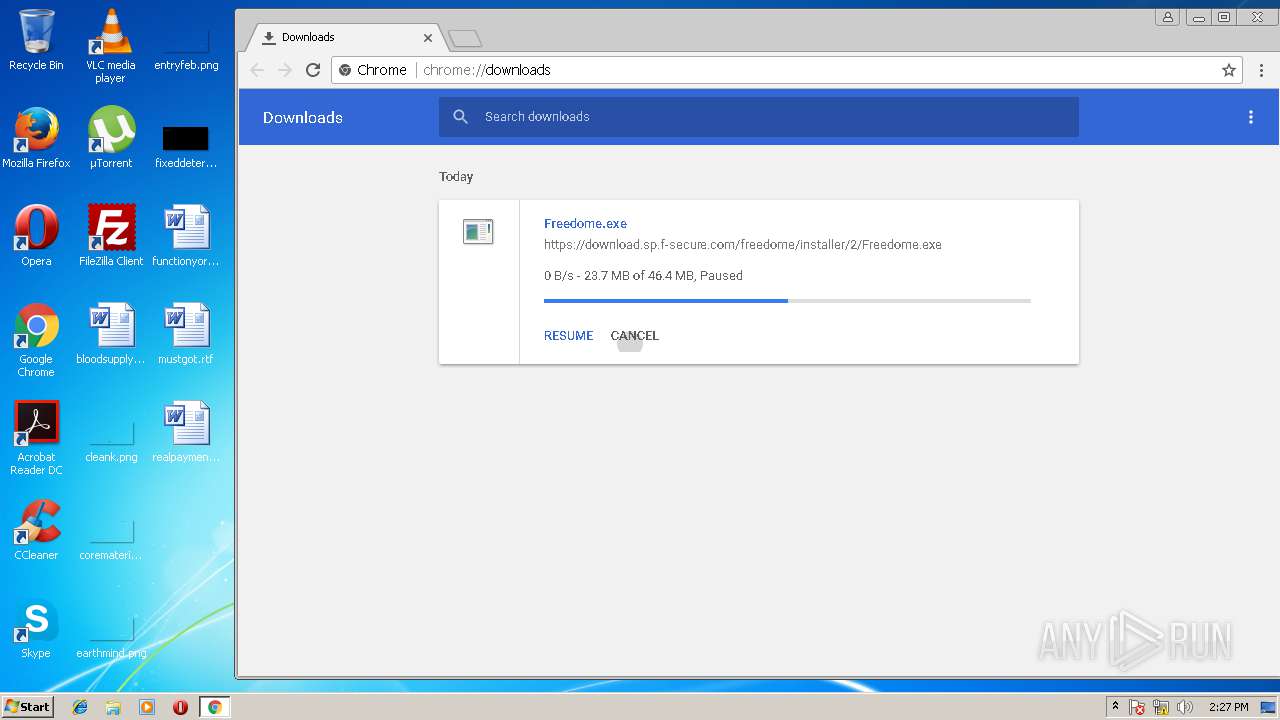
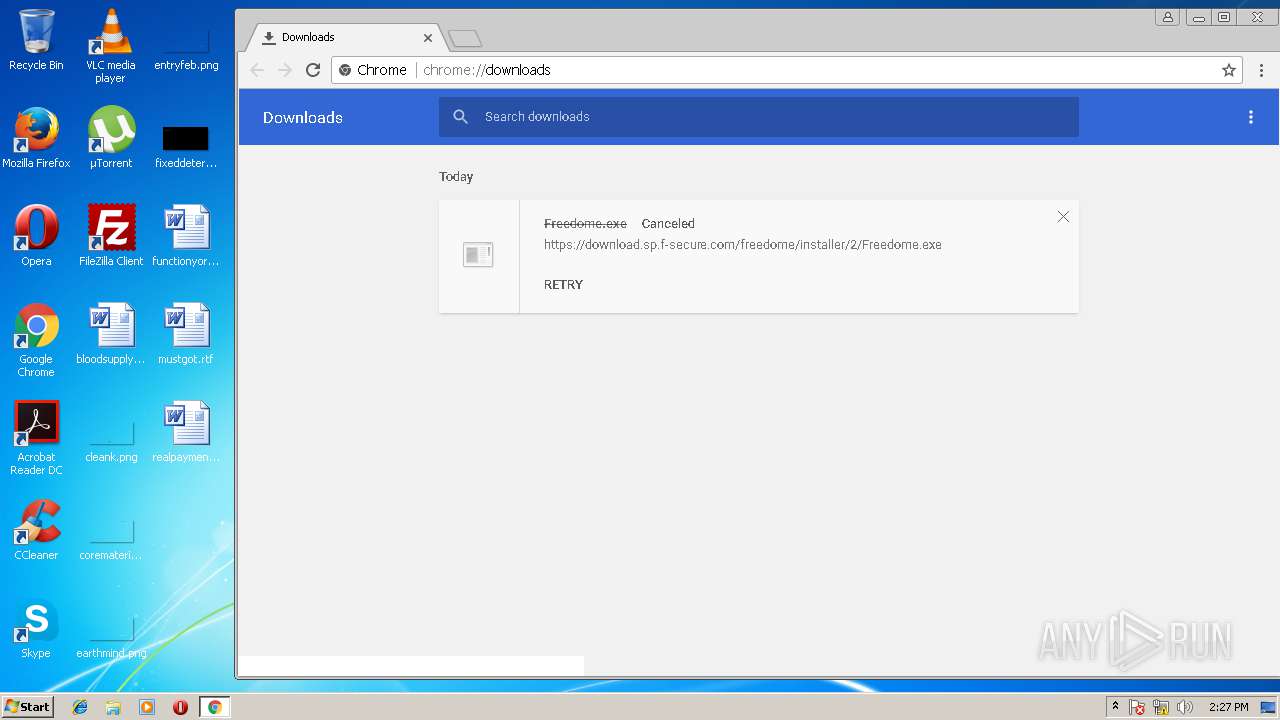
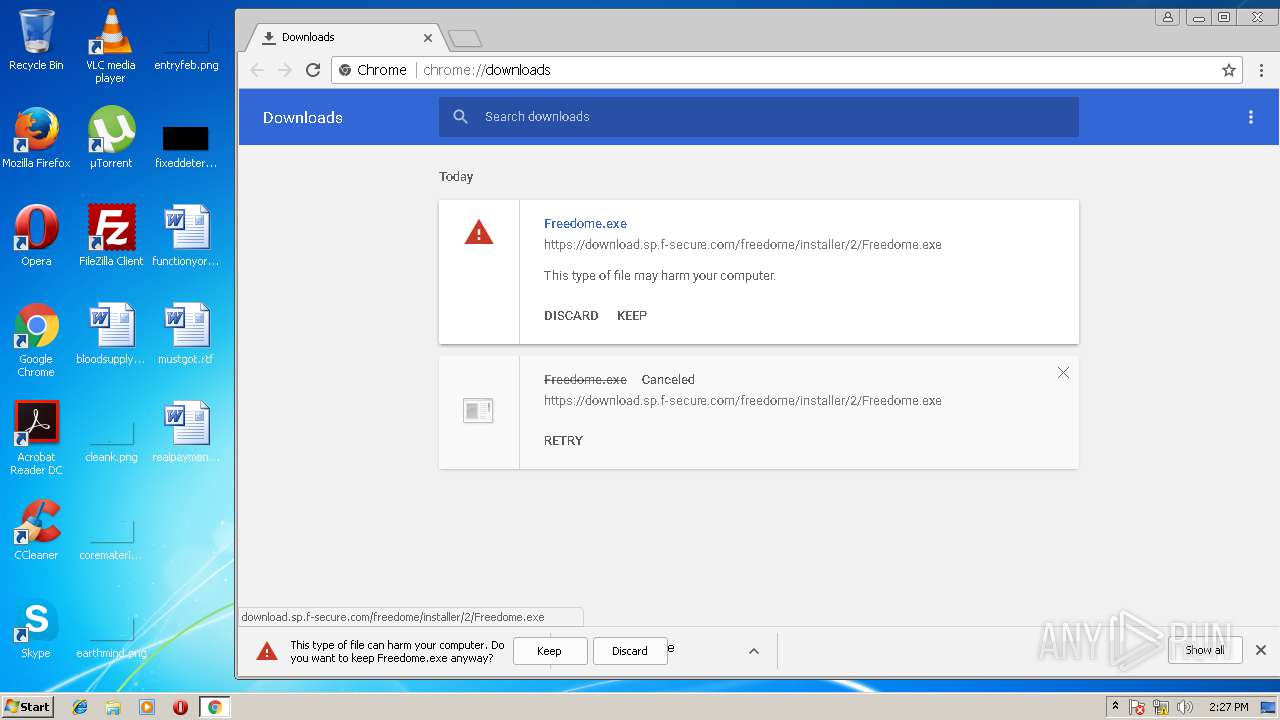
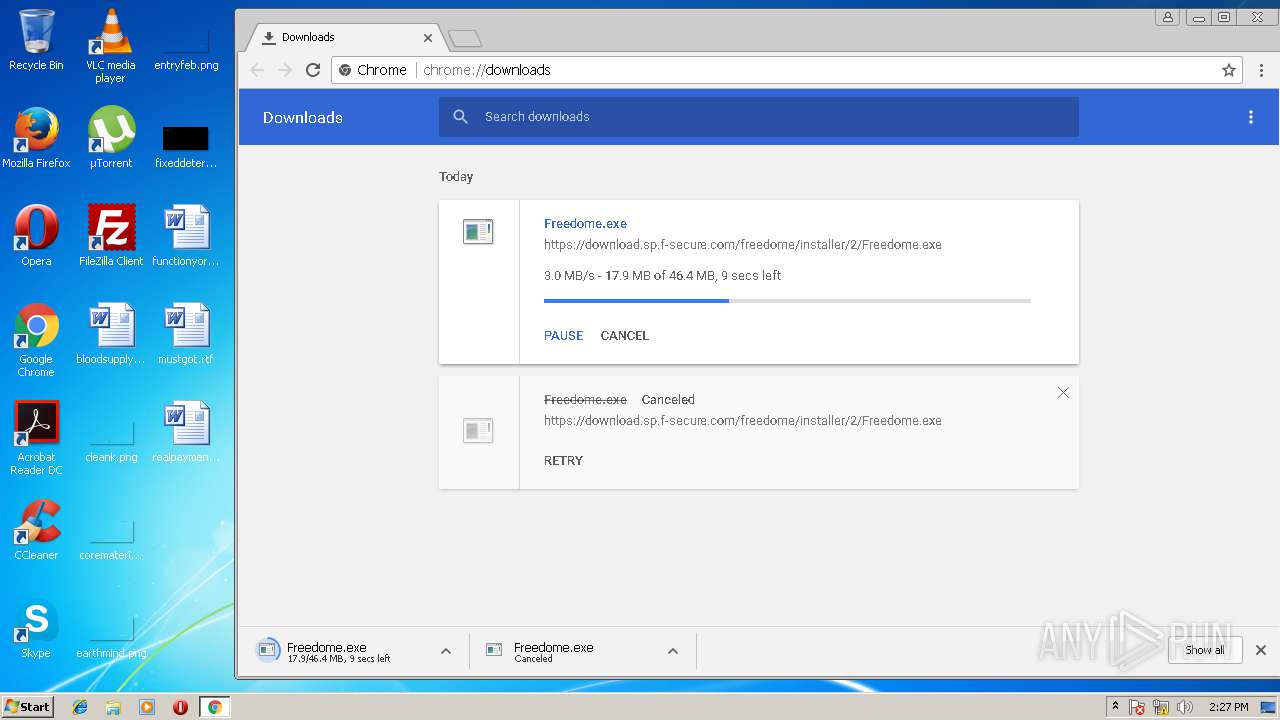
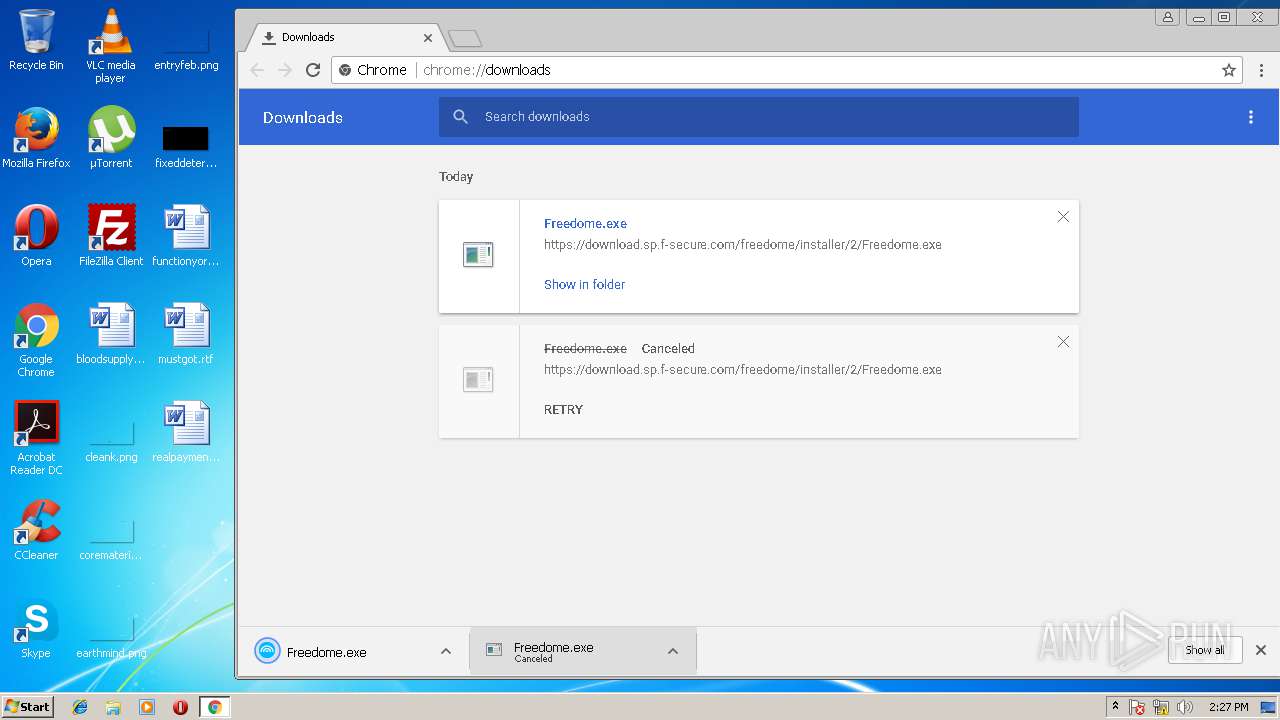
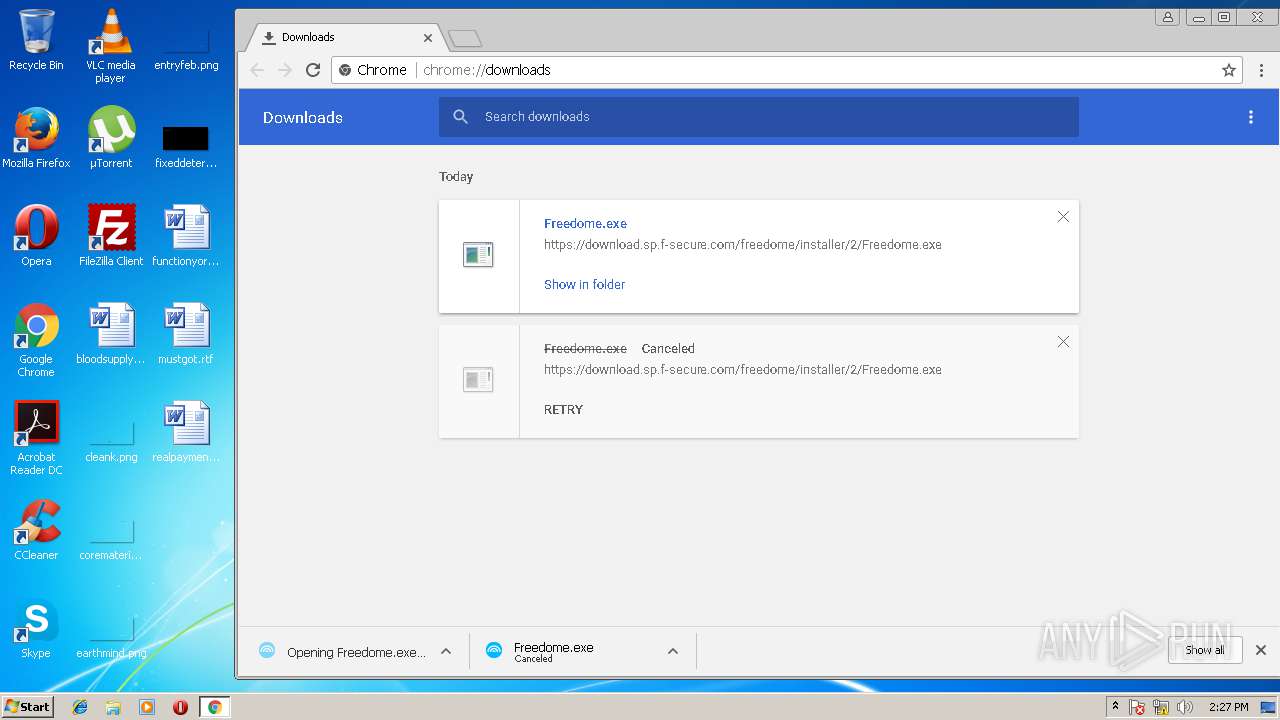
- Freedome.exe (PID: 2828)
- FreedomeInstallerUI.exe (PID: 3192)
- Freedome.exe (PID: 3940)
- drivertool32.exe (PID: 3860)
- fsvpnservice.exe (PID: 328)
- Freedome.exe (PID: 3052)
- Freedome.exe (PID: 2296)
- install.exe (PID: 3336)
- drivertool32.exe (PID: 2380)
- openvpn.exe (PID: 3068)
- netsh.exe (PID: 3728)
- openvpn.exe (PID: 1512)
- netsh.exe (PID: 3492)
- netsh.exe (PID: 2332)
- netsh.exe (PID: 2184)
- netsh.exe (PID: 2672)
- netsh.exe (PID: 604)
- netsh.exe (PID: 2572)
- netsh.exe (PID: 3360)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 3856)
Changes settings of System certificates
- drivertool32.exe (PID: 3860)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3628)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 2832)
- cmd.exe (PID: 3712)
- cmd.exe (PID: 3352)
- cmd.exe (PID: 2220)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 3140)
Application loaded dropped or rewritten executable
- fsvpnservice.exe (PID: 328)
- Freedome.exe (PID: 2296)
- Freedome.exe (PID: 3052)
- openvpn.exe (PID: 3068)
- openvpn.exe (PID: 1512)
SUSPICIOUS
Changes IE settings (feature browser emulation)
- MiniKeyLog.exe (PID: 3508)
Creates files in the user directory
- chrome.exe (PID: 1988)
Cleans NTFS data-stream (Zone Identifier)
- chrome.exe (PID: 1988)
Application launched itself
- Freedome.exe (PID: 2828)
- software_reporter_tool.exe (PID: 3856)
- Freedome.exe (PID: 3052)
- openvpn.exe (PID: 3068)
Creates files in the program directory
- install.exe (PID: 3336)
- drivertool32.exe (PID: 3860)
- Freedome.exe (PID: 3940)
- fsvpnservice.exe (PID: 328)
- Freedome.exe (PID: 3052)
- Freedome.exe (PID: 2296)
- netsh.exe (PID: 3728)
Creates files in the Windows directory
- drivertool32.exe (PID: 3860)
- DrvInst.exe (PID: 3380)
- DrvInst.exe (PID: 680)
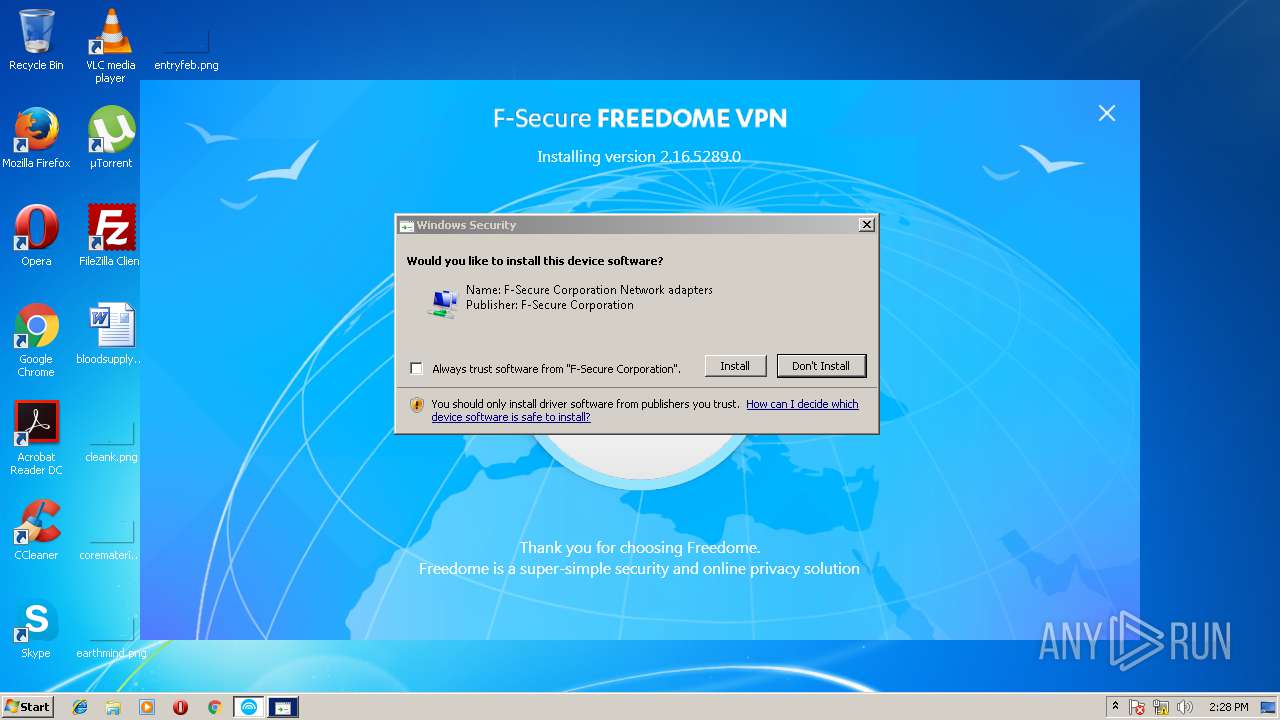
Creates or modifies windows services
- install.exe (PID: 3336)
- DrvInst.exe (PID: 680)
- netsh.exe (PID: 3008)
- DrvInst.exe (PID: 3380)
- fsvpnservice.exe (PID: 328)
Adds / modifies Windows certificates
- drivertool32.exe (PID: 3860)
Removes files from Windows directory
- DrvInst.exe (PID: 680)
- DrvInst.exe (PID: 3380)
Creates files in the driver directory
- DrvInst.exe (PID: 680)
- DrvInst.exe (PID: 3380)
Starts CMD.EXE for commands execution
- drivertool32.exe (PID: 3860)
- netsh.exe (PID: 2332)
- netsh.exe (PID: 3728)
- netsh.exe (PID: 3492)
- netsh.exe (PID: 2184)
- netsh.exe (PID: 2672)
- netsh.exe (PID: 604)
- netsh.exe (PID: 2572)
- netsh.exe (PID: 3360)
Creates a software uninstall entry
- install.exe (PID: 3336)
INFO
Application launched itself
- chrome.exe (PID: 1988)
- chrome.exe (PID: 2844)
Dropped object may contain Bitcoin addresses
- Freedome.exe (PID: 3940)
- fsvpnservice.exe (PID: 328)
Dropped object may contain URL's
- Freedome.exe (PID: 2828)
- drivertool32.exe (PID: 3860)
- chrome.exe (PID: 1988)
- DrvInst.exe (PID: 680)
- DrvInst.exe (PID: 3380)
- Freedome.exe (PID: 3940)
- Freedome.exe (PID: 2296)
- chrome.exe (PID: 2844)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1492)
Reads settings of System Certificates
- Freedome.exe (PID: 2296)
Creates or modifies windows services
- vssvc.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:03 09:05:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 5308928 |
| InitializedDataSize: | 4430336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x510fe8 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.30.0.0 |
| ProductVersionNumber: | 6.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | 7tech Ltd . |
| FileDescription: | MiniKeyLog . |
| FileVersion: | 6.30.0.0 |
| InternalName: | MKL . |
| LegalCopyright: | © 7tech Ltd . |
| ProductName: | MiniKeyLog . |
| ProductVersion: | 6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-May-2018 07:05:50 |
| Detected languages: |
|
| CompanyName: | 7tech Ltd . |
| FileDescription: | MiniKeyLog . |
| FileVersion: | 6.30.0.0 |
| InternalName: | MKL . |
| LegalCopyright: | © 7tech Ltd . |
| ProductName: | MiniKeyLog . |
| ProductVersion: | 6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 03-May-2018 07:05:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0050CEF8 | 0x0050D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.2776 |
.itext | 0x0050E000 | 0x0000306C | 0x00003200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.28998 |
.data | 0x00512000 | 0x0032D438 | 0x0032D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9872 |
.bss | 0x00840000 | 0x00007864 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00848000 | 0x00005224 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21944 |
.didata | 0x0084E000 | 0x0000090E | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.94206 |
.tls | 0x0084F000 | 0x0000004C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00850000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.195869 |
.reloc | 0x00851000 | 0x0004F670 | 0x0004F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64412 |
.rsrc | 0x008A1000 | 0x000B6A58 | 0x000B6C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.67817 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13558 | 1361 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.22556 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 4.0632 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.84508 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.60815 | 67624 | UNKNOWN | English - United States | RT_ICON |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.77296 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
9 | 2.34875 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
10 | 1.55564 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
Imports
AVIFIL32.DLL |
MSVFW32.DLL |
SHELL32.DLL |
URLMON.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
Total processes
131
Monitored processes
67
Malicious processes
11
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1656,11493160992088374344,6125377585149810254,131072 --service-pipe-token=3C7BA425CA0577175ECDEA0F543756A4 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=3C7BA425CA0577175ECDEA0F543756A4 --renderer-client-id=5 --mojo-platform-channel-handle=3384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 328 | "C:\Program Files\F-Secure\Freedome\Freedome\1\fsvpnservice.exe" | C:\Program Files\F-Secure\Freedome\Freedome\1\fsvpnservice.exe | — | services.exe | |||||||||||
User: SYSTEM Company: F-Secure Corporation Integrity Level: SYSTEM Description: F-Secure VPN Service Exit code: 0 Version: 2.16.5289.0 Modules
| |||||||||||||||
| 332 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{23096eed-8c0d-5e88-505b-c32d2d26c04a} Global\{61f96b58-0771-09ba-0cb6-ce64ad55301b} C:\Windows\System32\DriverStore\Temp\{75877966-9714-6546-7982-902c101f4969}\fsfreedometap.inf C:\Windows\System32\DriverStore\Temp\{75877966-9714-6546-7982-902c101f4969}\fsfreedometap.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | "C:/Program Files/F-Secure/Freedome/Freedome/1\system32\netsh.exe" interface ipv6 delete route 8000::/1 interface=18 fe80::8 store=active | C:\Program Files\F-Secure\Freedome\Freedome\1\system32\netsh.exe | — | openvpn.exe | |||||||||||
User: SYSTEM Company: F-Secure Corporation Integrity Level: SYSTEM Description: F-Secure VPN netsh proxy Exit code: 0 Version: 2.16.5289.0 Modules
| |||||||||||||||
| 680 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{6dbe7c93-2cb9-731c-d95f-93588d82b823}\fsfreedometap.inf" "0" "6dacbe12b" "000004A0" "WinSta0\Default" "000003C8" "208" "c:\program files\f-secure\freedome\freedome\1\driver-x86" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1492 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1512 | openvpn --verb 3 --register-dns --rdns-internal | C:\Program Files\F-Secure\Freedome\Freedome\1\openvpn.exe | — | openvpn.exe | |||||||||||
User: SYSTEM Company: The OpenVPN Project Integrity Level: SYSTEM Description: OpenVPN Daemon Exit code: 0 Version: 2.4._fs3.0 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1592,4511875733828782584,10837141110659999498,131072 --service-pipe-token=8D02D2FDD1F76EE6B3347DD6B0F0854F --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=8D02D2FDD1F76EE6B3347DD6B0F0854F --renderer-client-id=5 --mojo-platform-channel-handle=2684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1976 | C:\Windows\system32\netsh interface ipv6 add route ::/1 interface=18 fe80::8 store=active | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
3 953
Read events
2 615
Write events
1 261
Delete events
77
Modification events
| (PID) Process: | (3508) MiniKeyLog.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | MiniKeyLog.exe |
Value: 11000 | |||
| (PID) Process: | (3508) MiniKeyLog.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | delete value | Name: | MiniKeyLog.exe |
Value: 11000 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1924-13166792512537109 |
Value: 0 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1988-13169827551736500 |
Value: 259 | |||
Executable files
70
Suspicious files
114
Text files
264
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000038.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\edf3360c-6dfc-483e-b759-e491f358fa86.tmp | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFfefa6.TMP | text | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\65d4133b-183b-4ac5-a435-b1a99c254814.tmp | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\f_000009 | compressed | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e850a7ff-6e72-4016-b602-4c9a76d495ff.tmp | — | |
MD5:— | SHA256:— | |||
| 1988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Session | binary | |
MD5:— | SHA256:— | |||
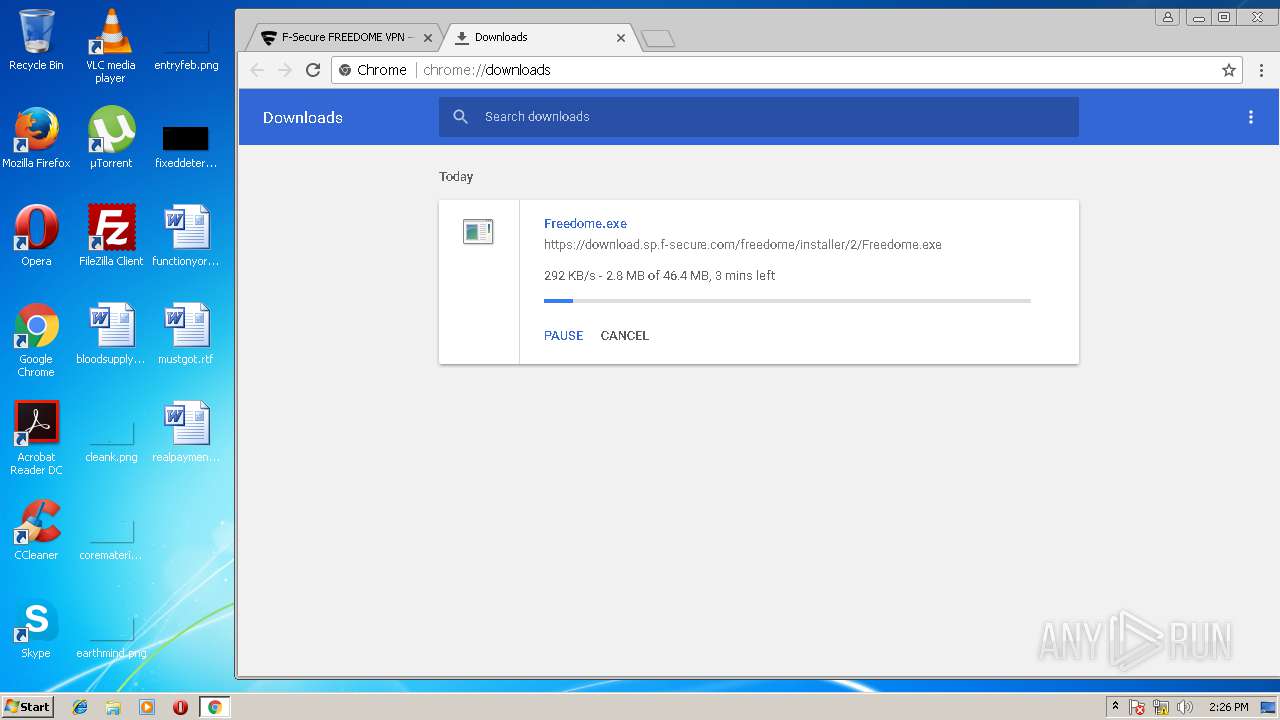
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
69
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAka%2FOtyVO1t1Fp86KGfB9M%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAPxtOFfOoLxFJZ4s9fYR1w%3D | US | der | 471 b | whitelisted |
— | — | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSPwl%2BrBFlJbvzLXU1bGW08VysJ2wQUj%2Bh%2B8G0yagAFI8dwl2o6kP9r6tQCEAQbuUXZv077DKD9YzdR24o%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 216.58.208.46:80 | http://clients1.google.com/tools/pso/ping?as=chrome&brand=GCEA&pid=&hl=en&rep=2&rlz=C1:1C1GCEA_enDE765UA770,C2:1C2GCEA_enDE765,C7:1C7GCEA_enDE765 | US | text | 124 b | whitelisted |
— | — | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 52.4 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSPwl%2BrBFlJbvzLXU1bGW08VysJ2wQUj%2Bh%2B8G0yagAFI8dwl2o6kP9r6tQCEAQbuUXZv077DKD9YzdR24o%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 52.85.177.232:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
— | — | GET | 200 | 52.85.177.232:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.16.195:443 | www.google.ru | Google Inc. | US | whitelisted |
— | — | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 104.108.54.20:443 | www.f-secure.com | Akamai Technologies, Inc. | NL | whitelisted |
— | — | 216.58.208.46:443 | consent.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.194:443 | adservice.google.es | Google Inc. | US | whitelisted |
— | — | 216.58.205.226:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 23.44.105.130:443 | assets.adobedtm.com | Akamai Technologies, Inc. | US | whitelisted |
— | — | 52.166.11.26:443 | addsearch.com | Microsoft Corporation | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.ru |
| whitelisted |
www.google.com |
| malicious |
www.google.es |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
adservice.google.es |
| whitelisted |
www.f-secure.com |
| suspicious |