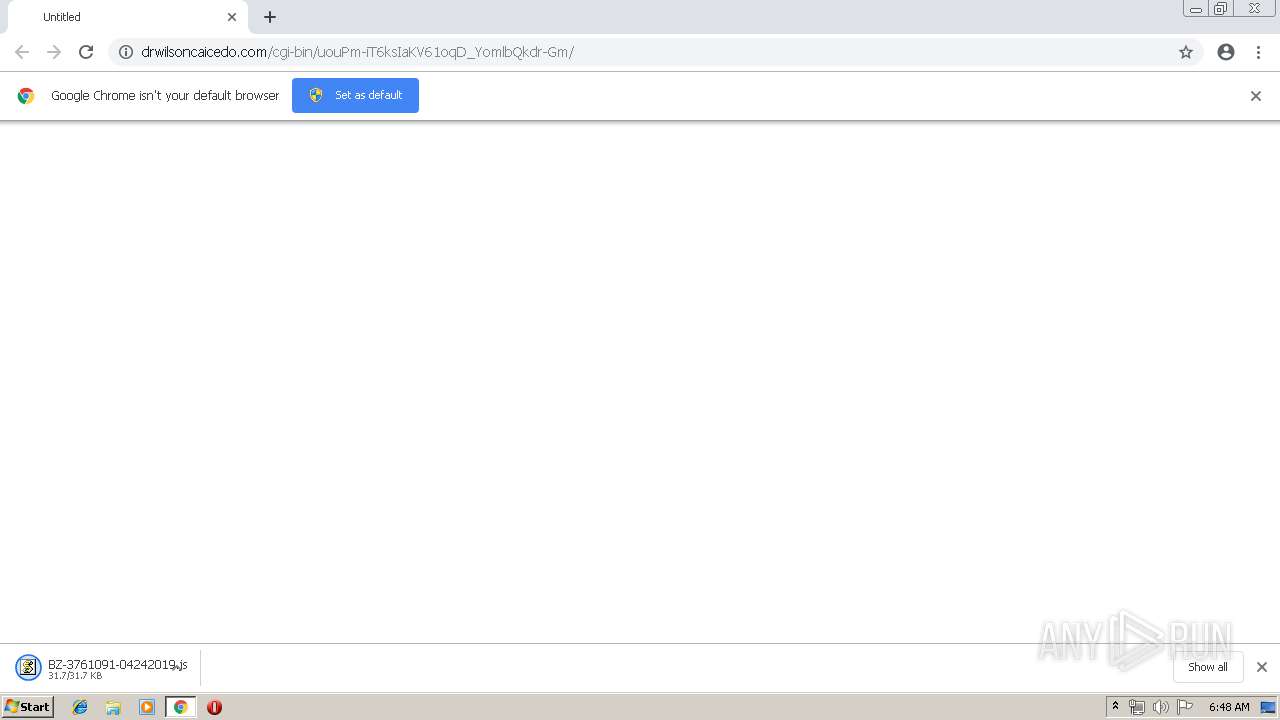
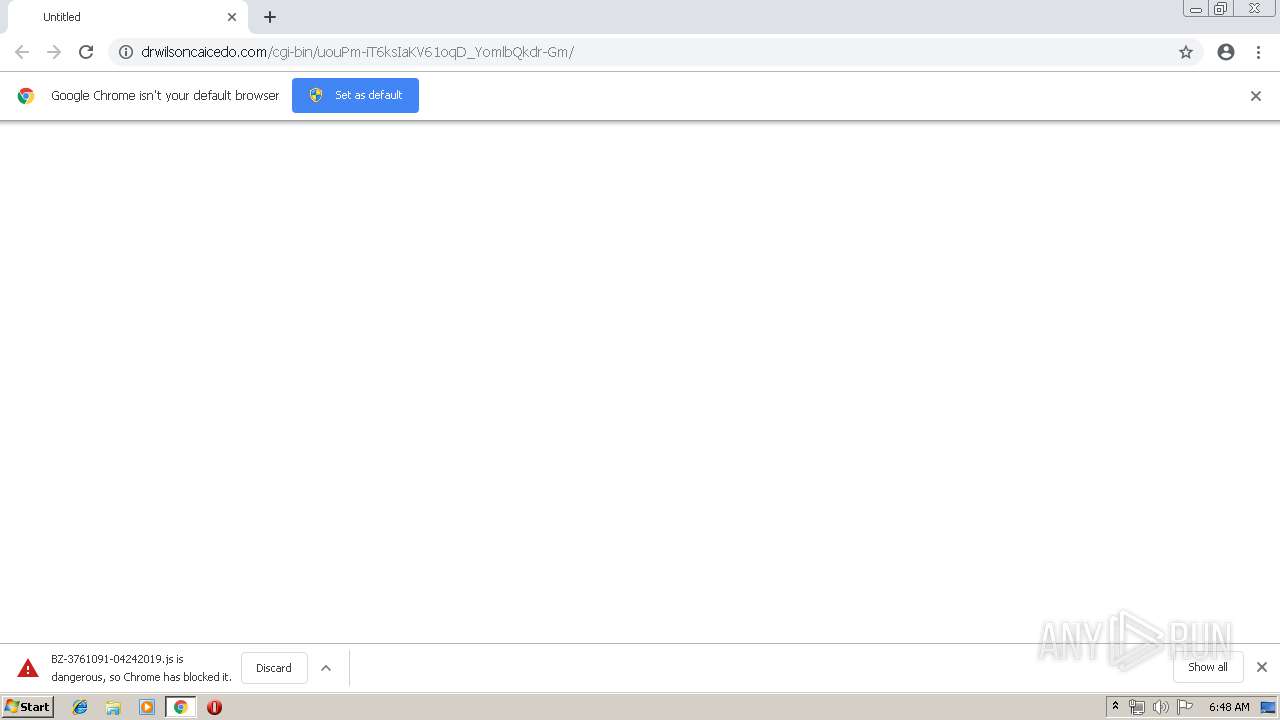
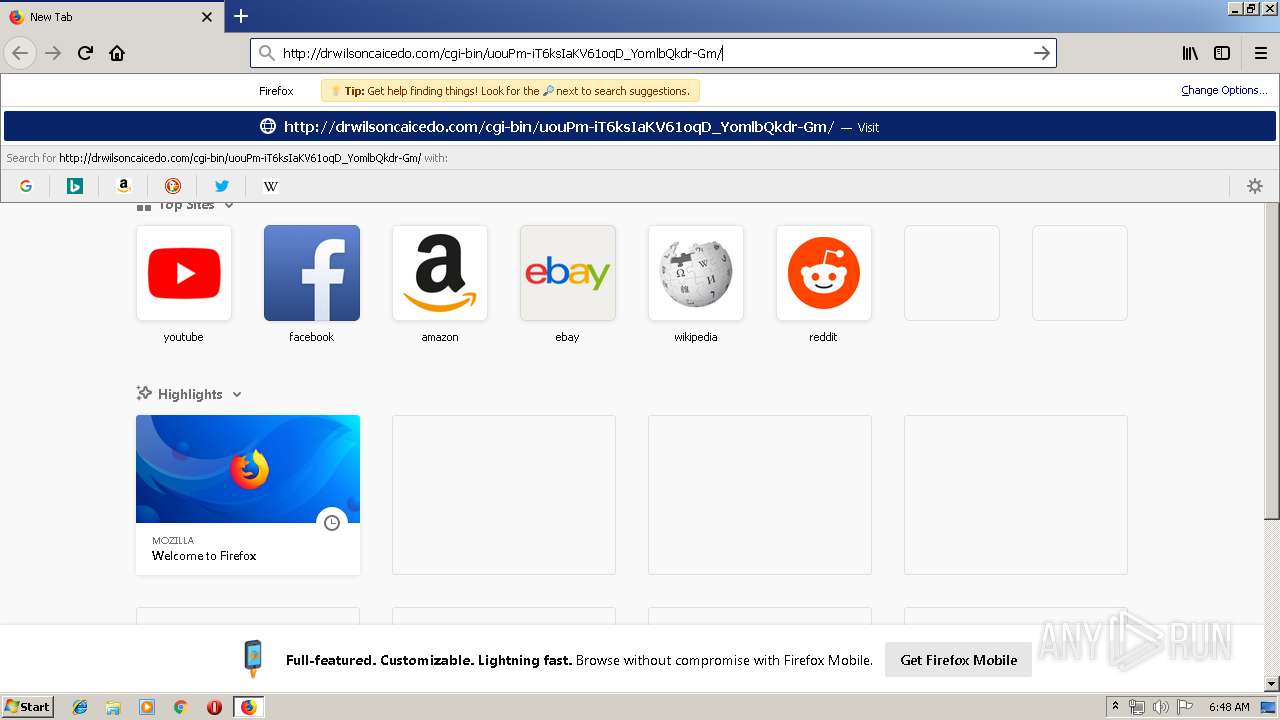
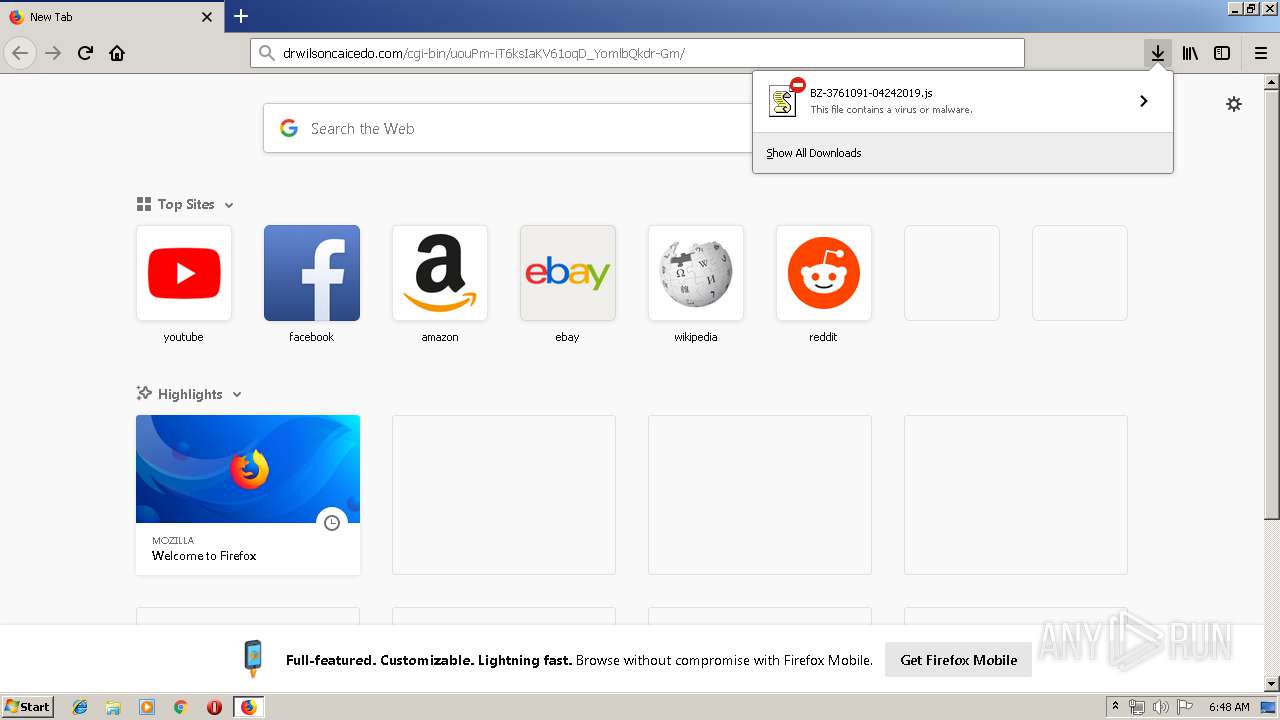
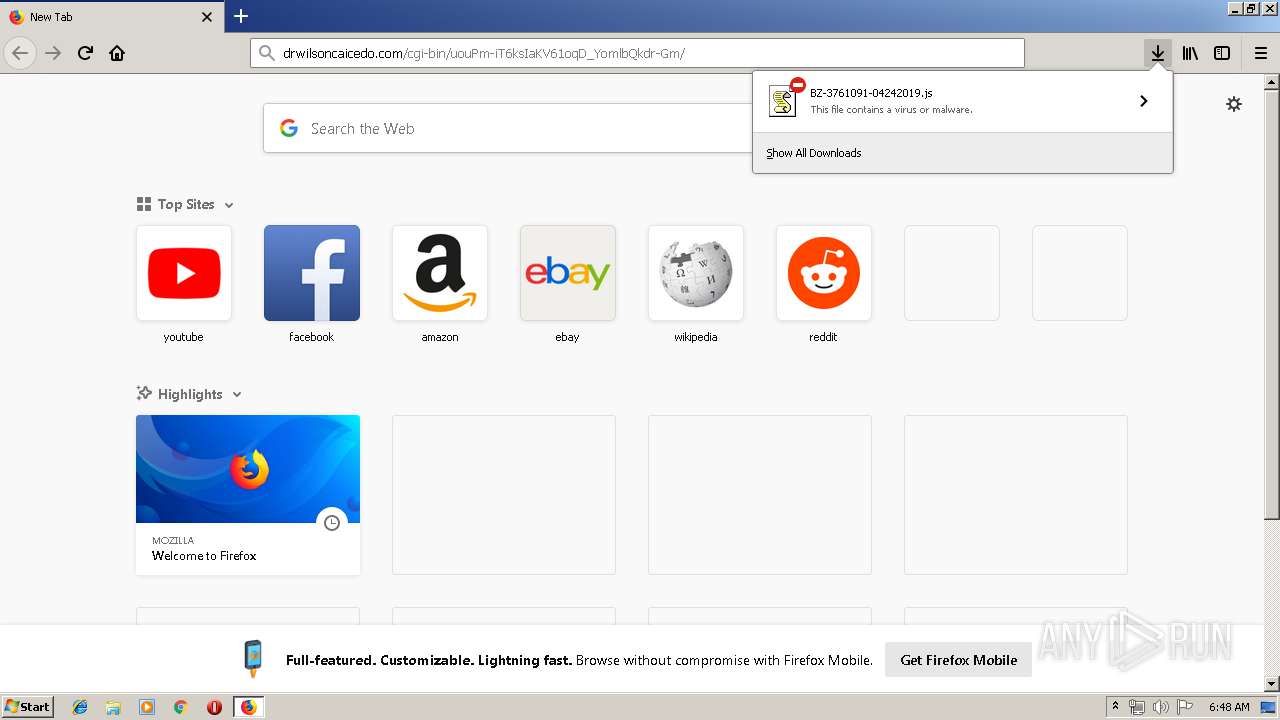
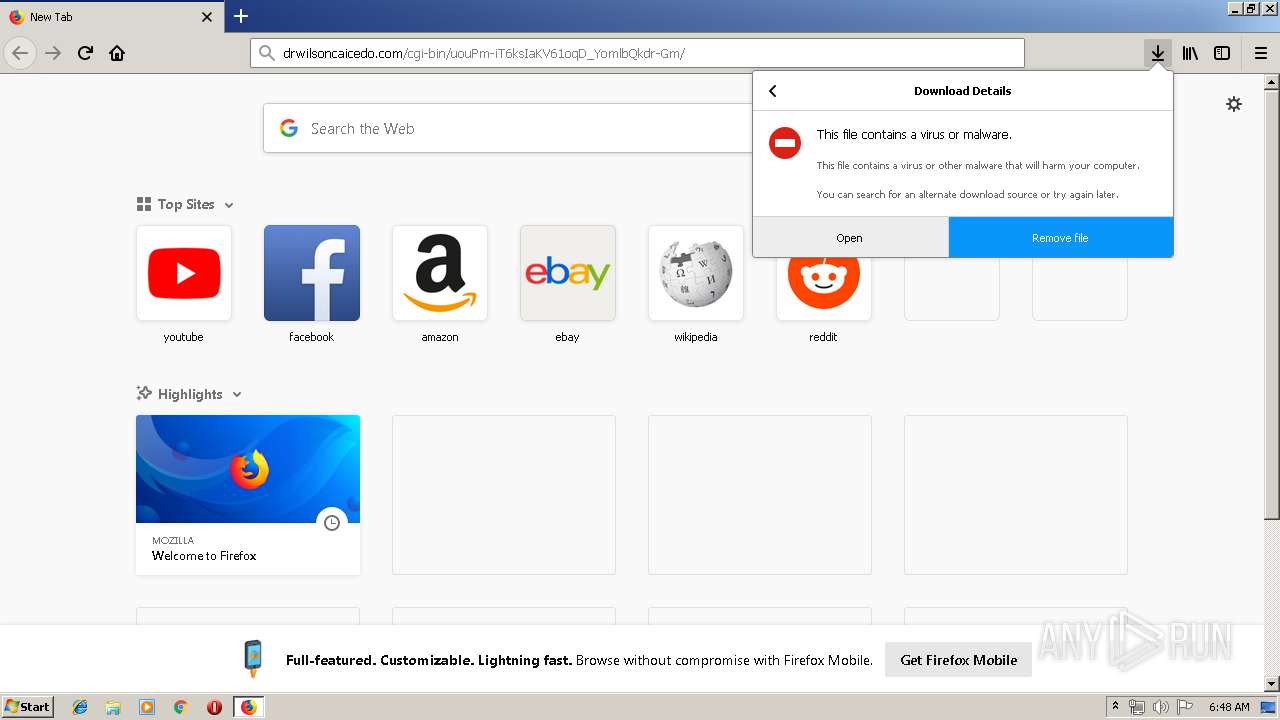
| URL: | http://drwilsoncaicedo.com/cgi-bin/uouPm-iT6ksIaKV61oqD_YomlbQkdr-Gm/ |
| Full analysis: | https://app.any.run/tasks/ba62fdcc-18eb-47bd-ba6f-5bbfa798855b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 24, 2019, 05:47:56 |
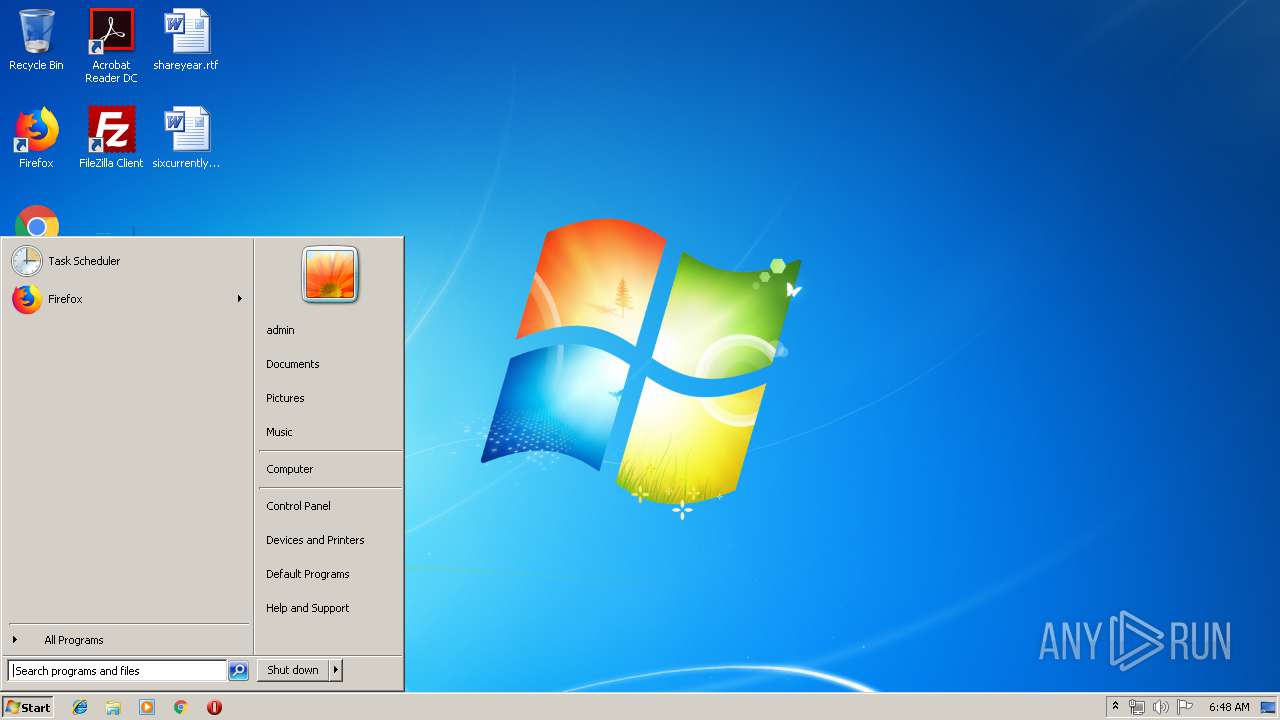
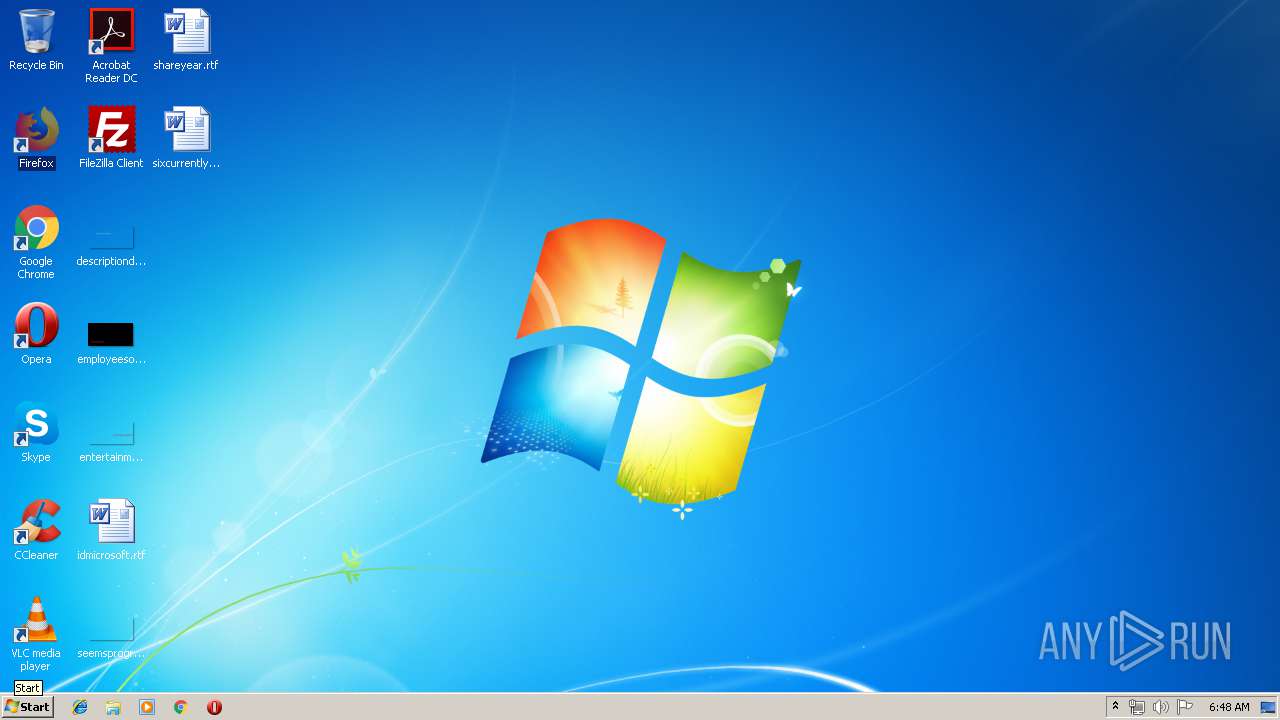
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E91D4B1B3E914F1E2305813C68C6A4E3 |
| SHA1: | 9DA0069AEF970E1F2A3BDE14A5DC741AFDF02F48 |
| SHA256: | 9873A6205BBB0888CDF9B4B1540CFBA0BFA6499FD60556B36EEF7E802E501095 |
| SSDEEP: | 3:N1KaX/YTEj2AMIqLKQCxxVK38TbXgK:CaX/yEjU6xxVKggK |
MALICIOUS
Downloads executable files from the Internet
- WScript.exe (PID: 2332)
Application was dropped or rewritten from another process
- e1acw6r26.exe (PID: 3312)
- e1acw6r26.exe (PID: 3820)
- soundser.exe (PID: 2600)
- soundser.exe (PID: 1260)
- zJygtykGt4VmyCnmc.exe (PID: 1924)
- zJygtykGt4VmyCnmc.exe (PID: 3024)
- soundser.exe (PID: 916)
- soundser.exe (PID: 1916)
Emotet process was detected
- soundser.exe (PID: 2600)
- soundser.exe (PID: 916)
Connects to CnC server
- soundser.exe (PID: 1260)
- soundser.exe (PID: 1916)
EMOTET was detected
- soundser.exe (PID: 1260)
- soundser.exe (PID: 1916)
Changes the autorun value in the registry
- soundser.exe (PID: 1260)
- soundser.exe (PID: 1916)
SUSPICIOUS
Executes scripts
- firefox.exe (PID: 3128)
Creates files in the user directory
- WScript.exe (PID: 2332)
Starts itself from another location
- e1acw6r26.exe (PID: 3312)
- zJygtykGt4VmyCnmc.exe (PID: 1924)
Executable content was dropped or overwritten
- WScript.exe (PID: 2332)
- e1acw6r26.exe (PID: 3312)
- firefox.exe (PID: 3128)
- soundser.exe (PID: 1260)
- zJygtykGt4VmyCnmc.exe (PID: 1924)
Connects to server without host name
- soundser.exe (PID: 1260)
- soundser.exe (PID: 1916)
Application launched itself
- zJygtykGt4VmyCnmc.exe (PID: 3024)
- soundser.exe (PID: 916)
INFO
Application launched itself
- chrome.exe (PID: 3044)
- firefox.exe (PID: 3128)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3128)
Creates files in the user directory
- firefox.exe (PID: 3128)
Reads CPU info
- firefox.exe (PID: 3128)
Reads settings of System Certificates
- firefox.exe (PID: 3128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
21
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fae0f18,0x6fae0f28,0x6fae0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 916 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | zJygtykGt4VmyCnmc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3128.20.2056679174\405016826" -childID 3 -isForBrowser -prefsHandle 3292 -prefMapHandle 3288 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3128 "\\.\pipe\gecko-crash-server-pipe.3128" 3300 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1260 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,4151292831935682418,5600099318842161013,131072 --enable-features=PasswordImport --service-pipe-token=6701768762584909762 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6701768762584909762 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1916 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | --f7014c05 | C:\Users\admin\AppData\Local\soundser\zJygtykGt4VmyCnmc.exe | zJygtykGt4VmyCnmc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,4151292831935682418,5600099318842161013,131072 --enable-features=PasswordImport --service-pipe-token=6003273395632544971 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6003273395632544971 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
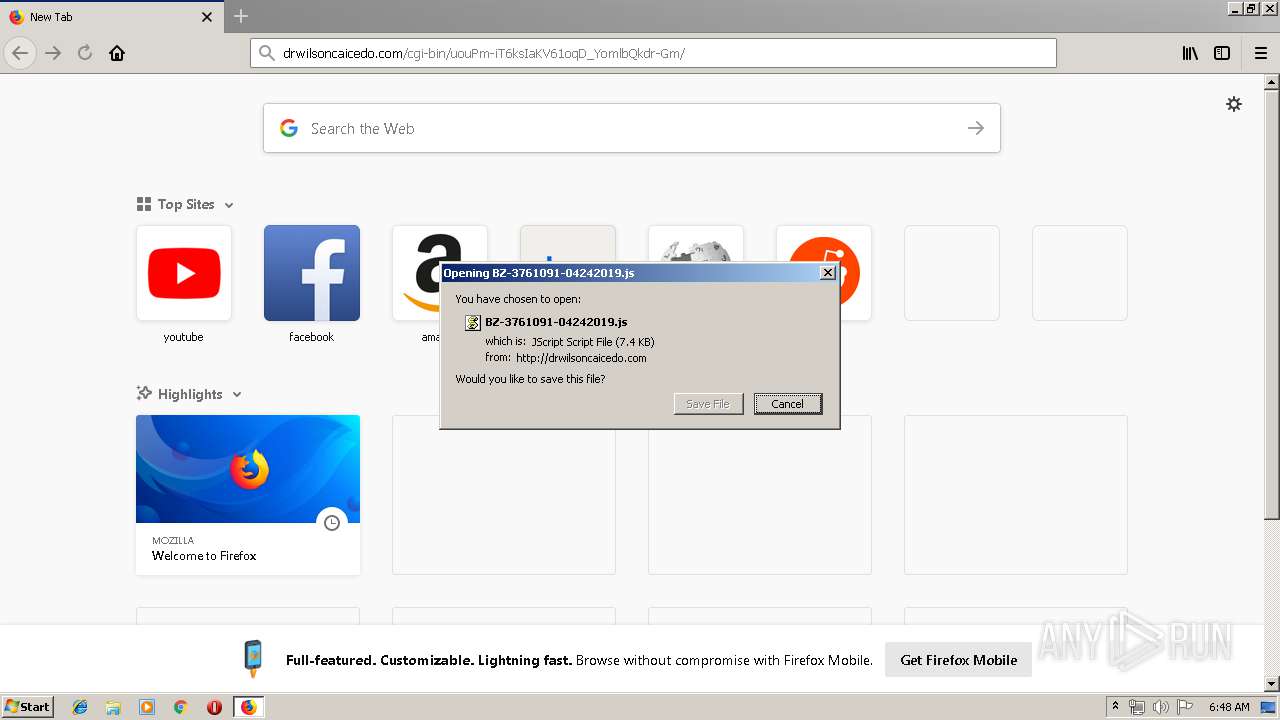
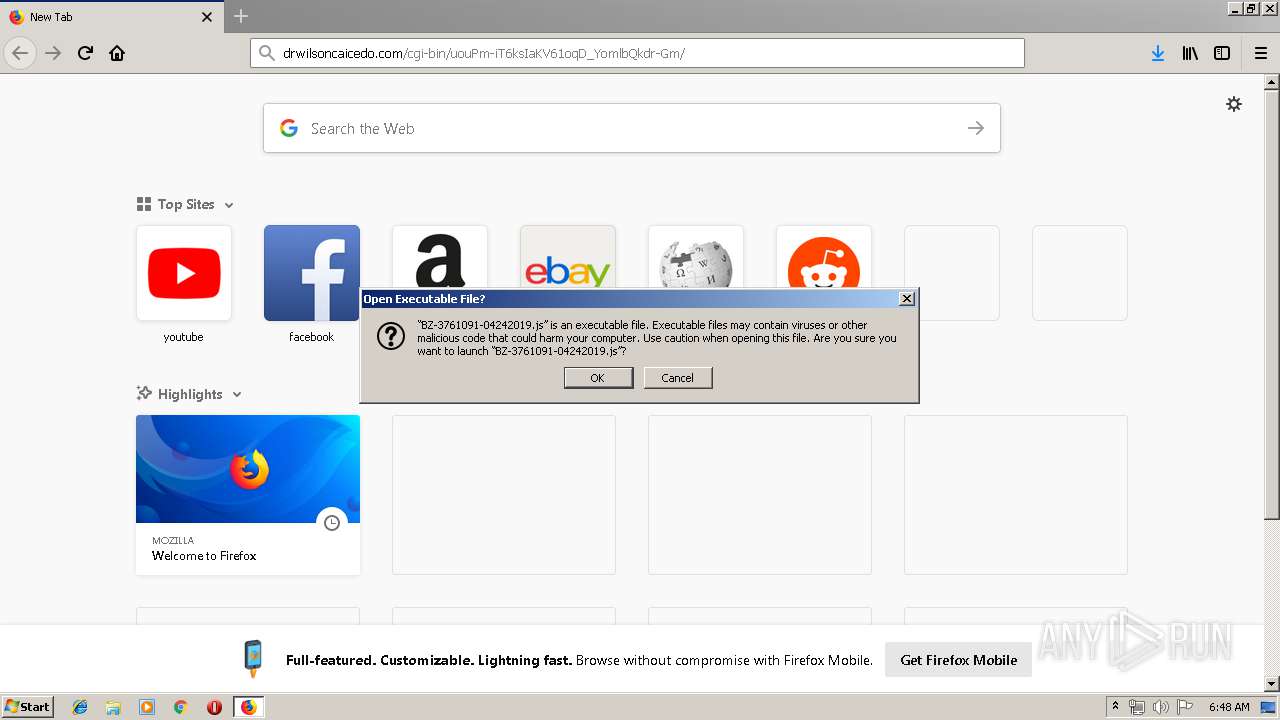
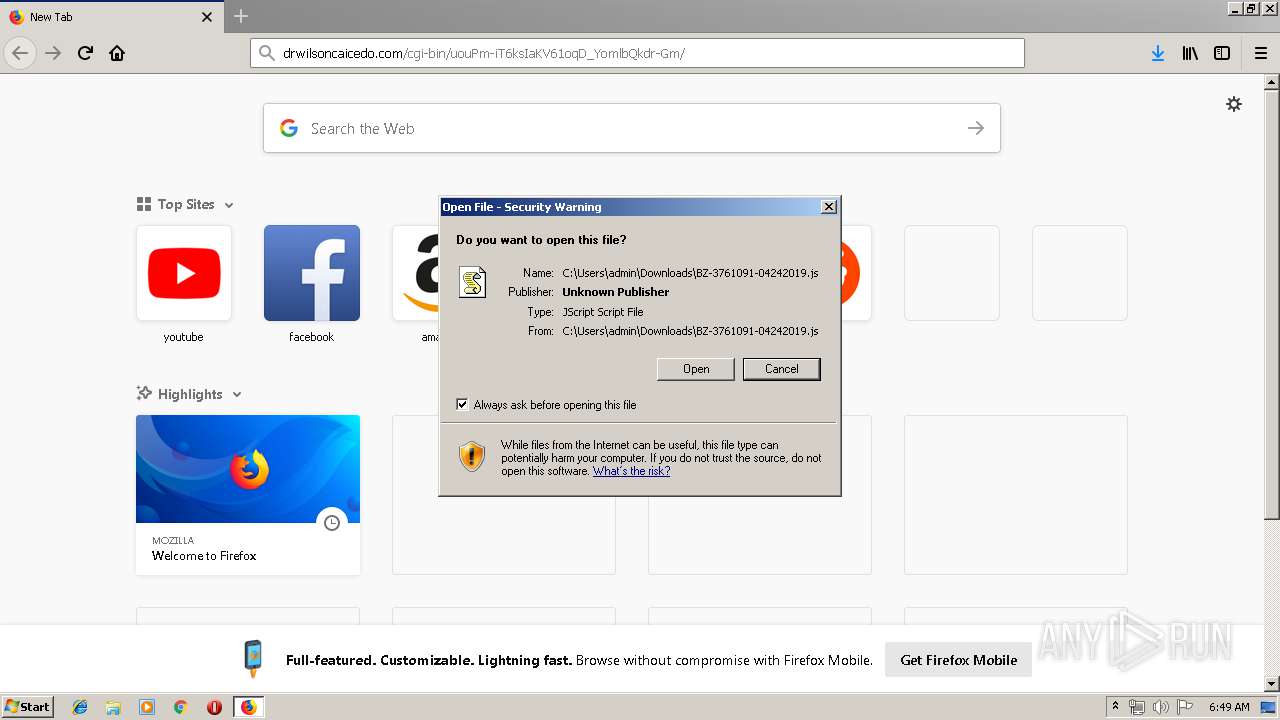
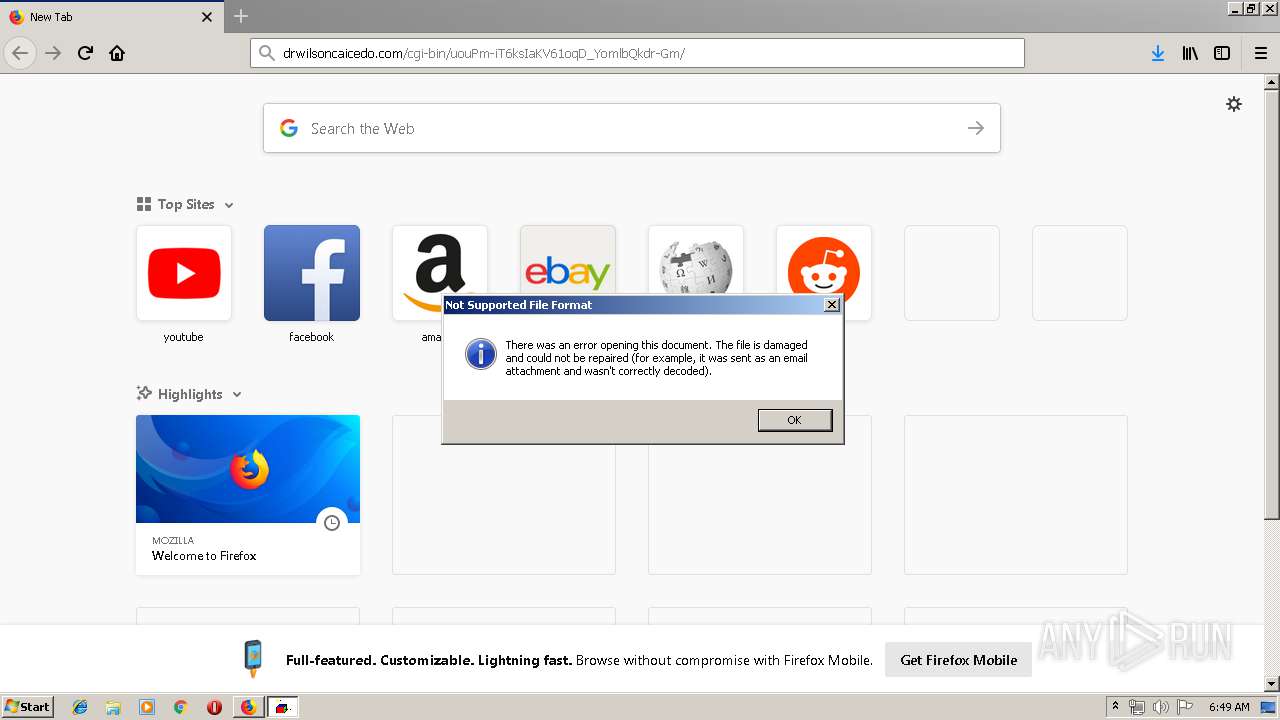
| 2332 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\BZ-3761091-04242019.js" | C:\Windows\System32\WScript.exe | firefox.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3128.13.2019000760\145855785" -childID 2 -isForBrowser -prefsHandle 2496 -prefMapHandle 2504 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3128 "\\.\pipe\gecko-crash-server-pipe.3128" 2520 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
Total events
1 432
Read events
1 333
Write events
96
Delete events
3
Modification events
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3044-13200558491216625 |
Value: 259 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
5
Suspicious files
73
Text files
89
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\23ffa518-7fe0-4893-bca8-4c2257ce31a2.tmp | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
37
DNS requests
88
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3044 | chrome.exe | GET | 200 | 192.185.226.188:80 | http://drwilsoncaicedo.com/cgi-bin/uouPm-iT6ksIaKV61oqD_YomlbQkdr-Gm/ | US | text | 7.44 Kb | suspicious |
3128 | firefox.exe | POST | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3128 | firefox.exe | GET | 200 | 192.185.226.188:80 | http://drwilsoncaicedo.com/cgi-bin/uouPm-iT6ksIaKV61oqD_YomlbQkdr-Gm/ | US | text | 7.44 Kb | suspicious |
3128 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3128 | firefox.exe | POST | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3128 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2332 | WScript.exe | GET | 200 | 164.52.146.13:80 | http://potterspots.com/cgi-bin/8MnY/ | US | executable | 78.0 Kb | suspicious |
1260 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/mult/ | CA | binary | 120 Kb | malicious |
1916 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/tpt/child/ringin/merge/ | CA | binary | 148 b | malicious |
3128 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3044 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3044 | chrome.exe | 192.185.226.188:80 | drwilsoncaicedo.com | Unified Layer | US | suspicious |
3044 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3044 | chrome.exe | 172.217.22.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3044 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3044 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3128 | firefox.exe | 54.200.51.65:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3128 | firefox.exe | 52.88.59.160:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3128 | firefox.exe | 173.223.11.150:80 | detectportal.firefox.com | Akamai International B.V. | NL | whitelisted |
3128 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
drwilsoncaicedo.com |
| suspicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2332 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2332 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2332 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2332 | WScript.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1260 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1916 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
5 ETPRO signatures available at the full report