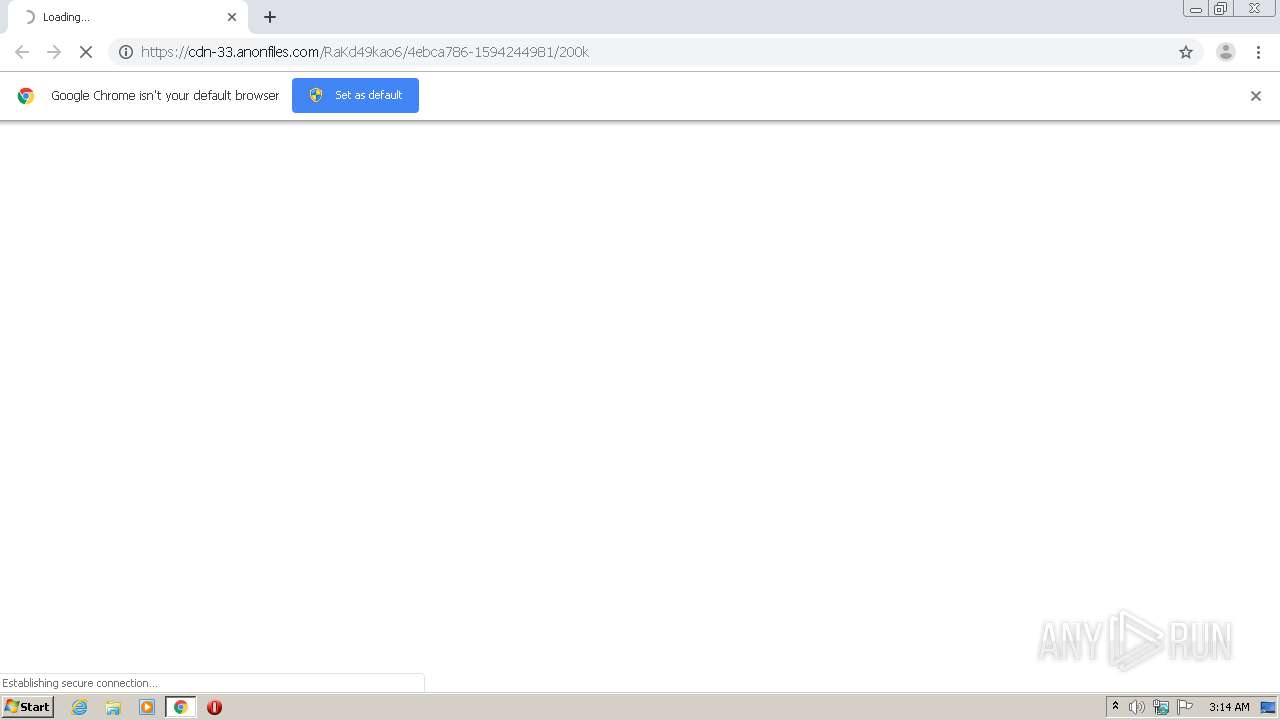
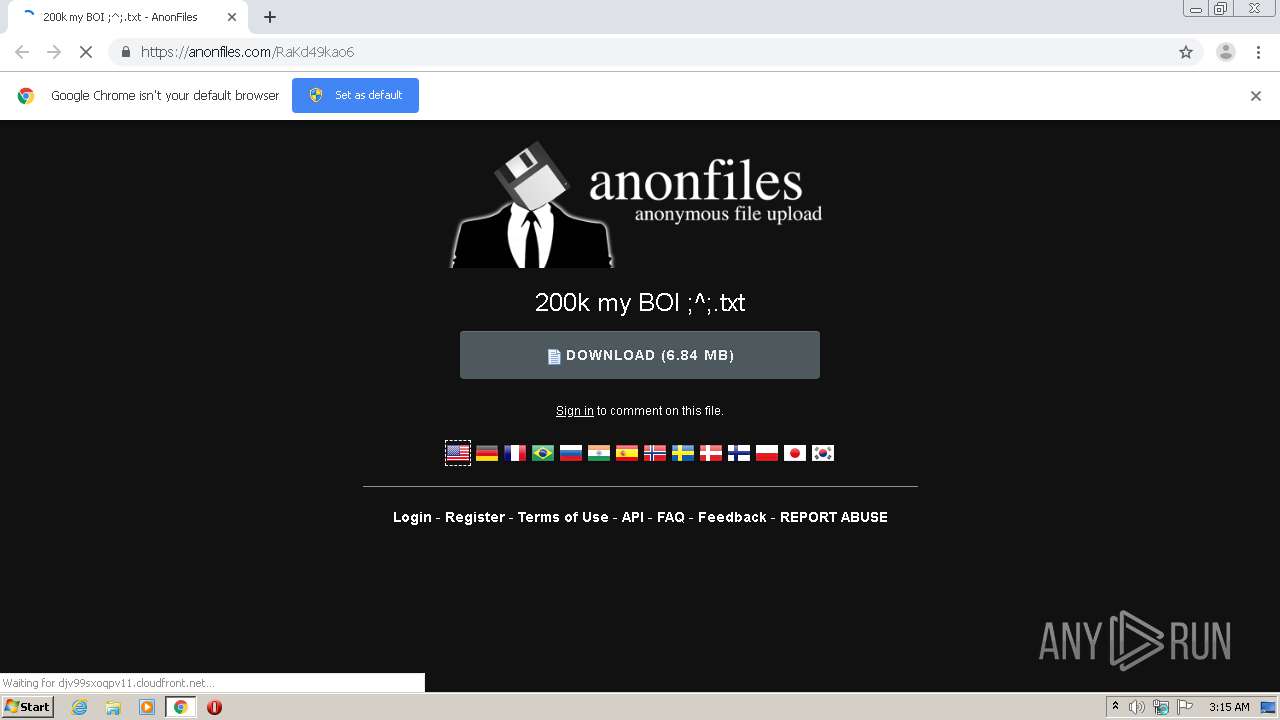
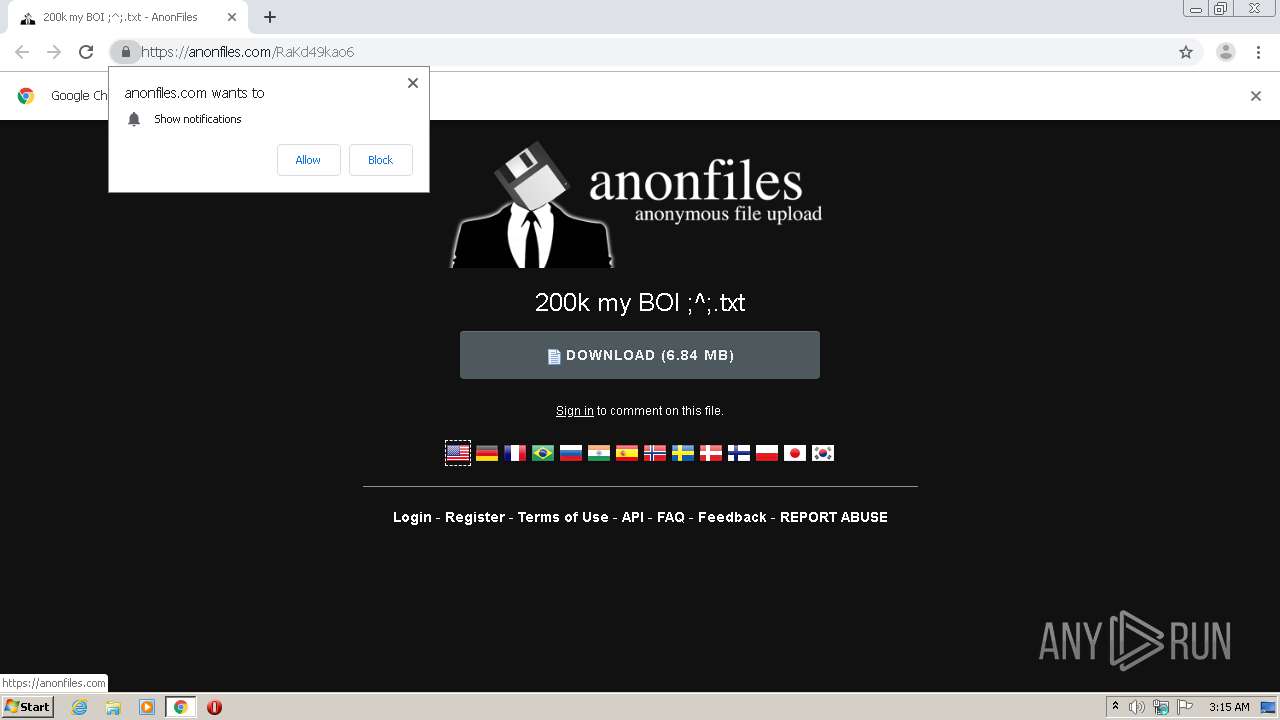
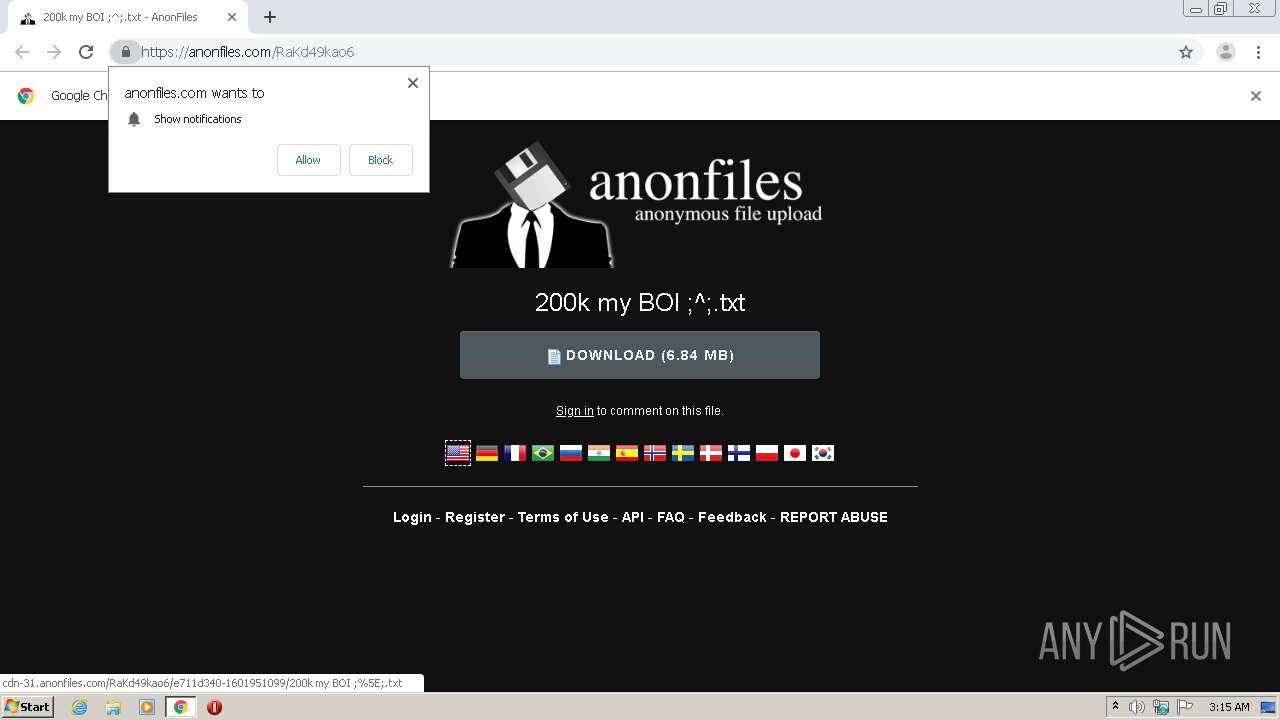
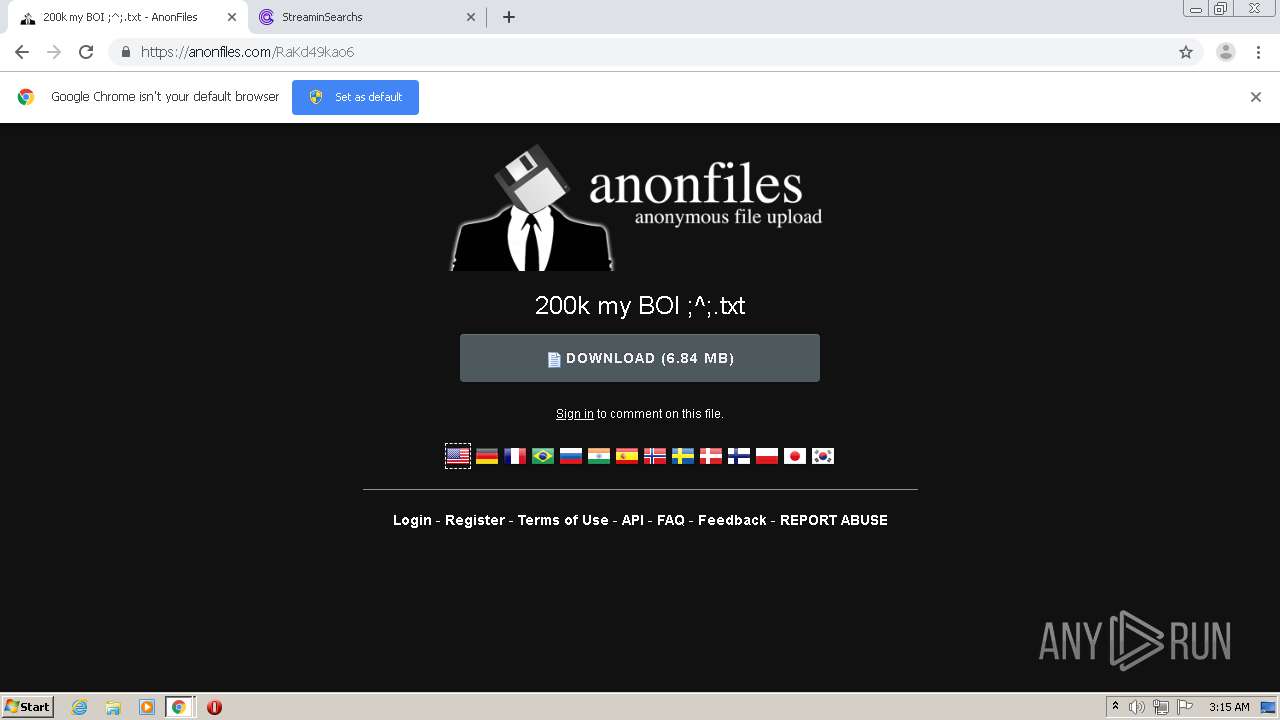
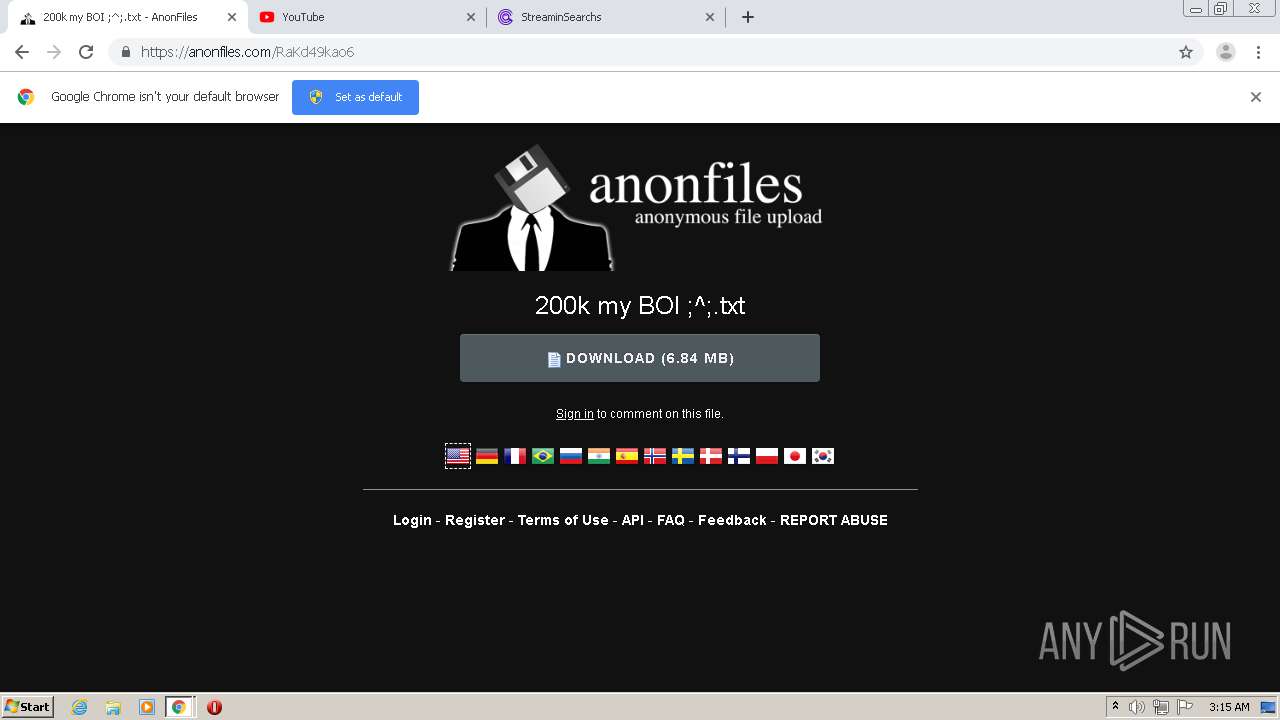
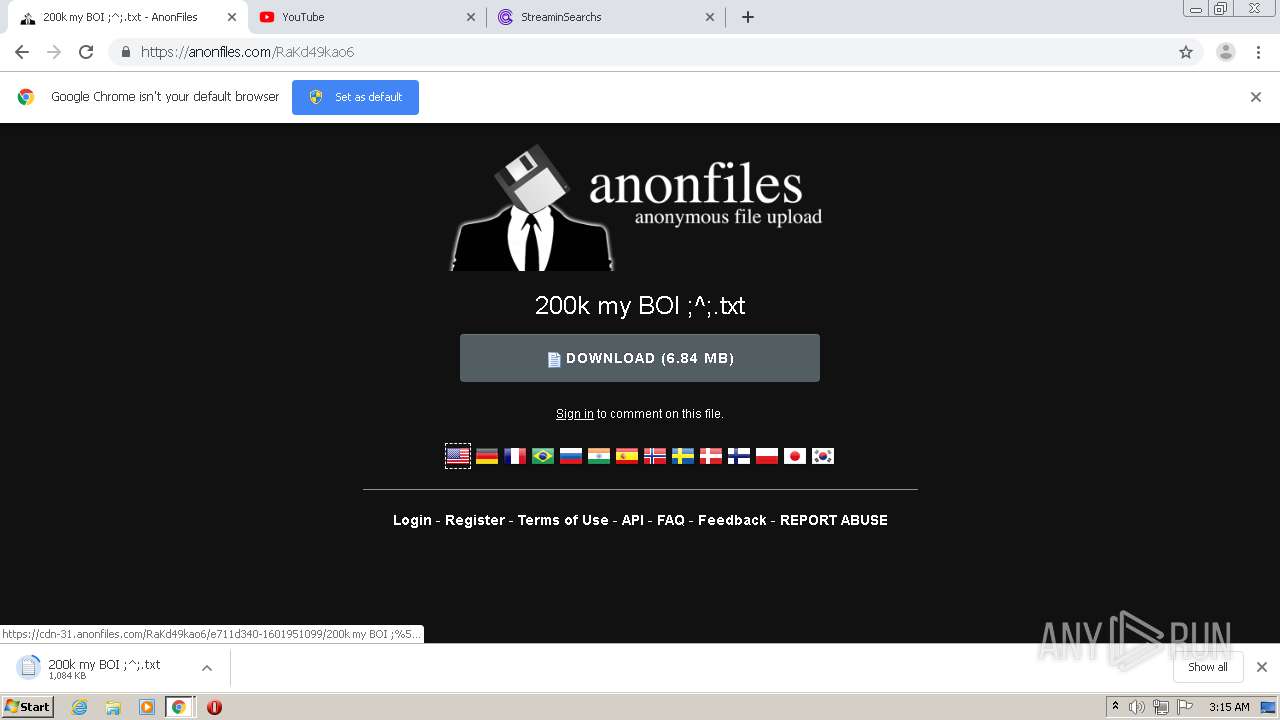
| URL: | https://cdn-33.anonfiles.com/RaKd49kao6/4ebca786-1594244981/200k |
| Full analysis: | https://app.any.run/tasks/d88f8541-98f5-44be-81ff-c7430fa4cdbe |
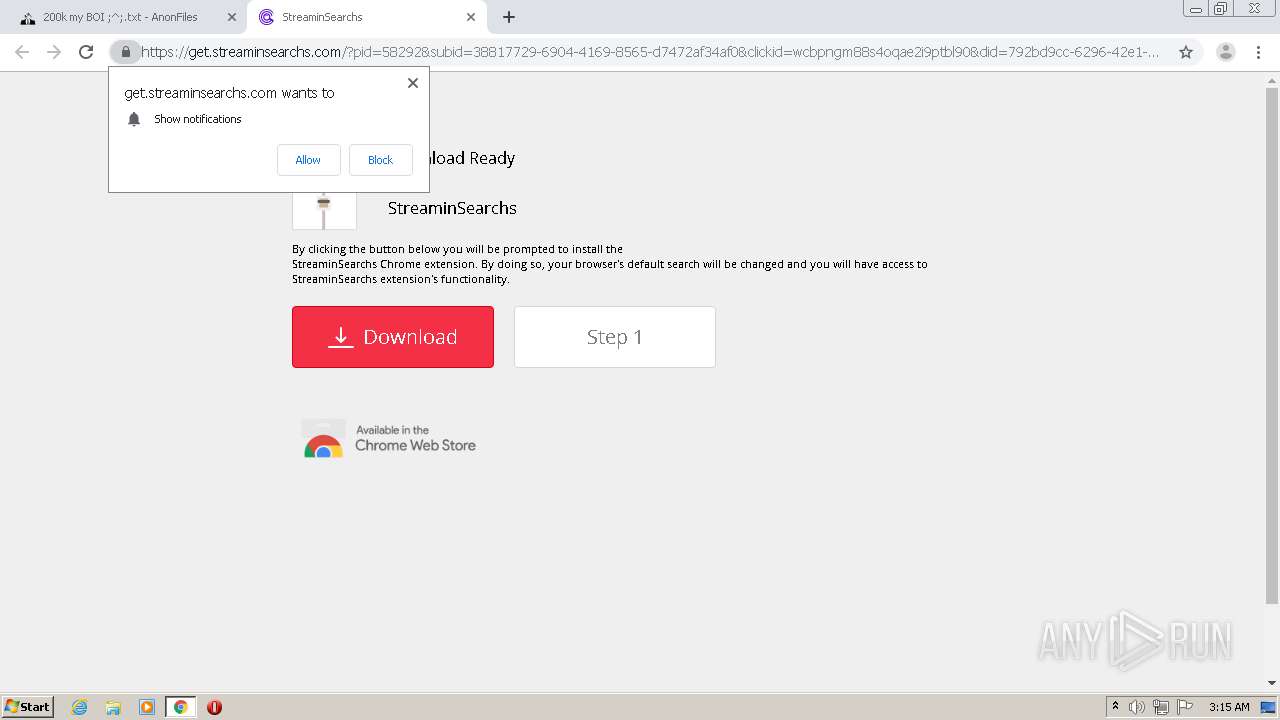
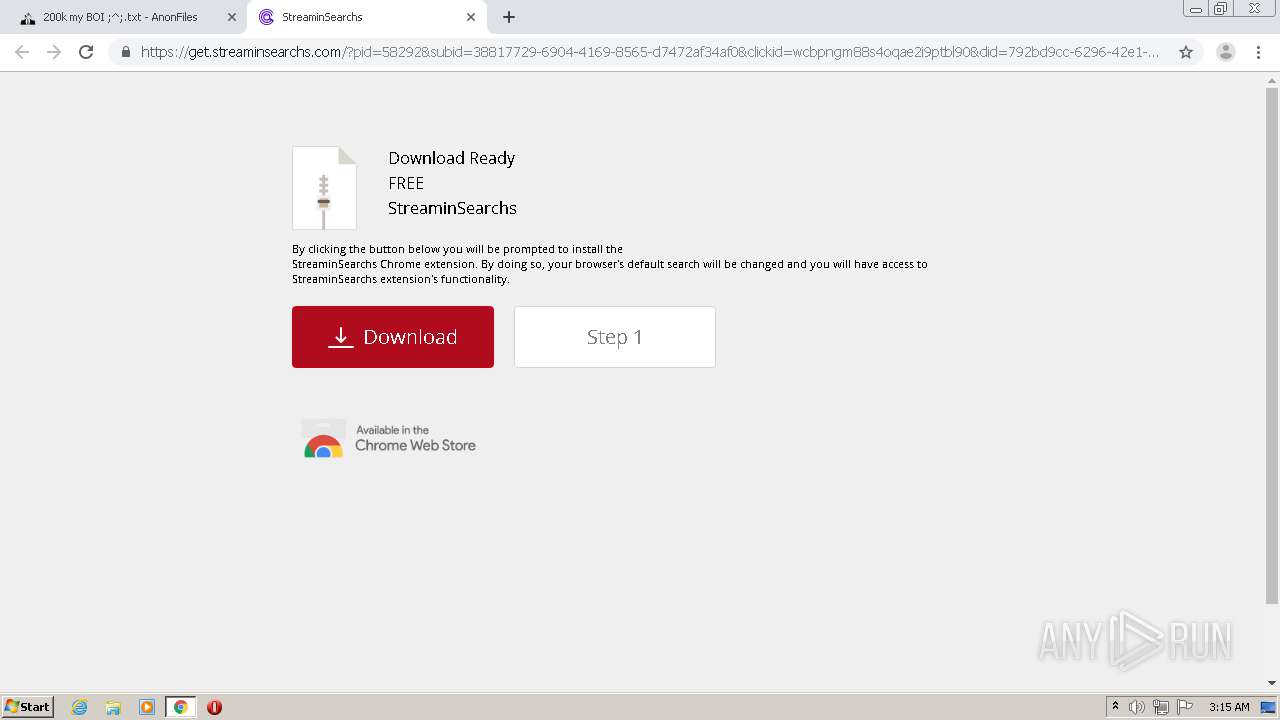
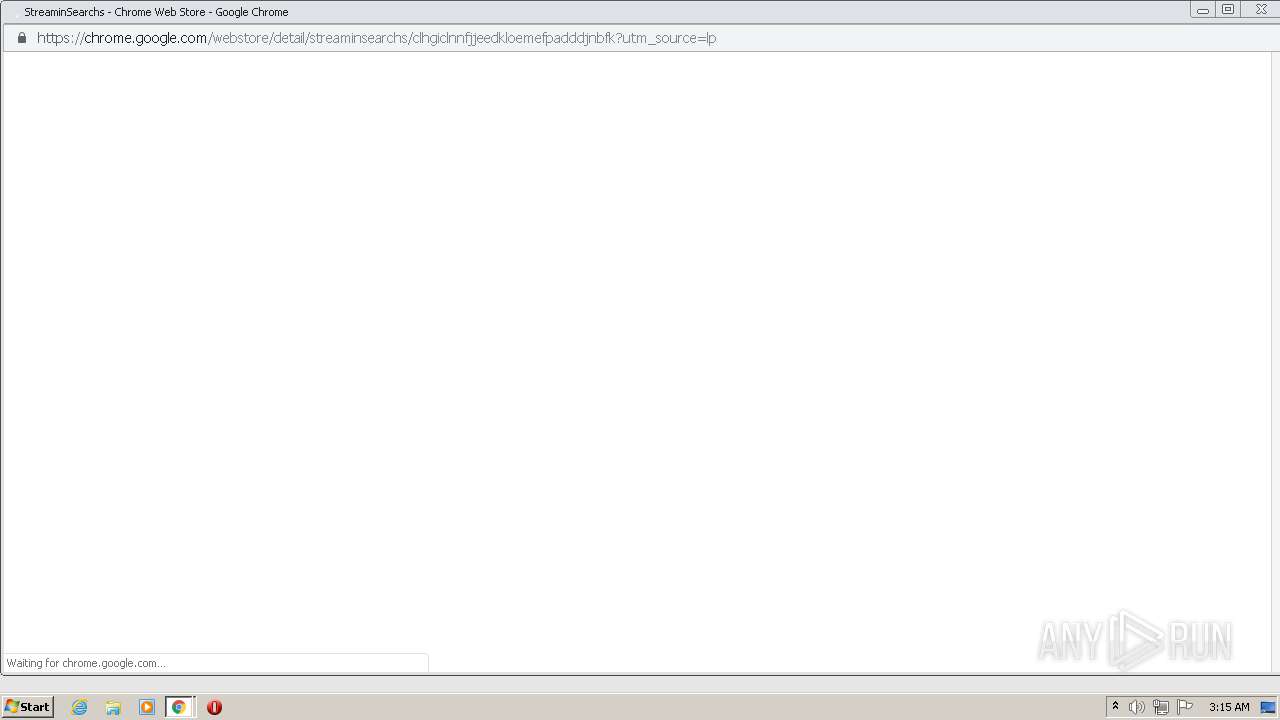
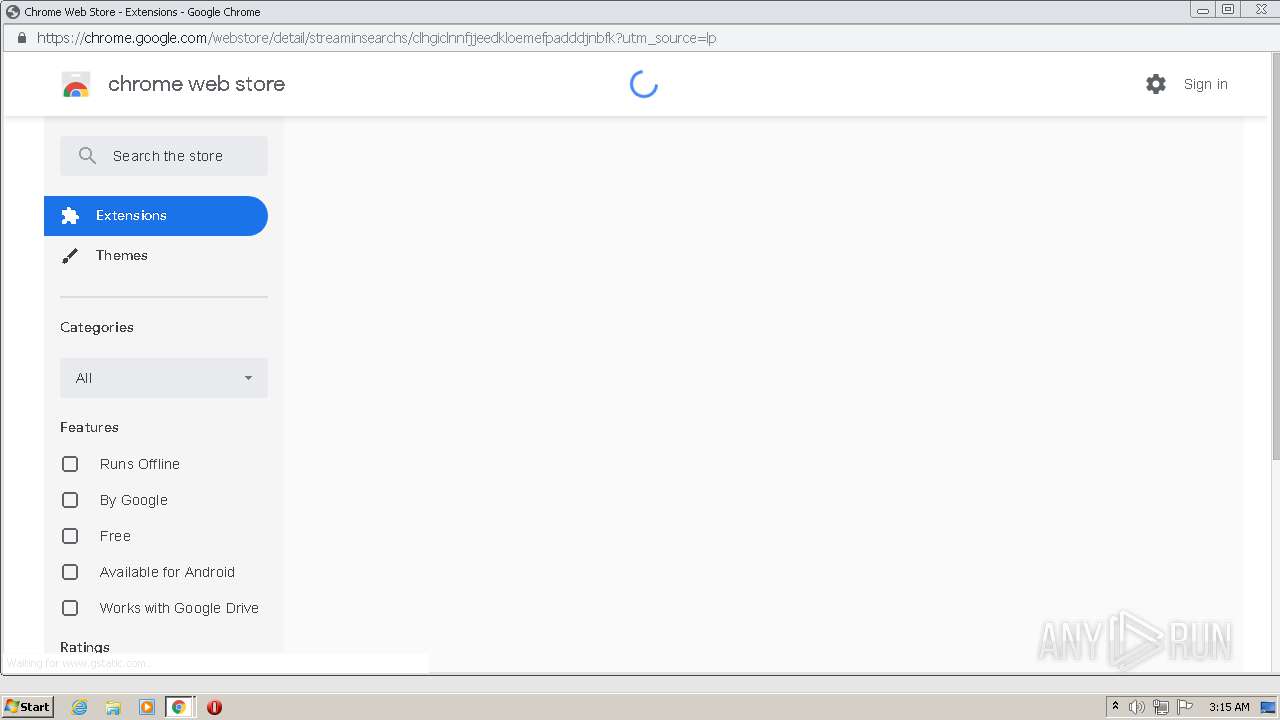
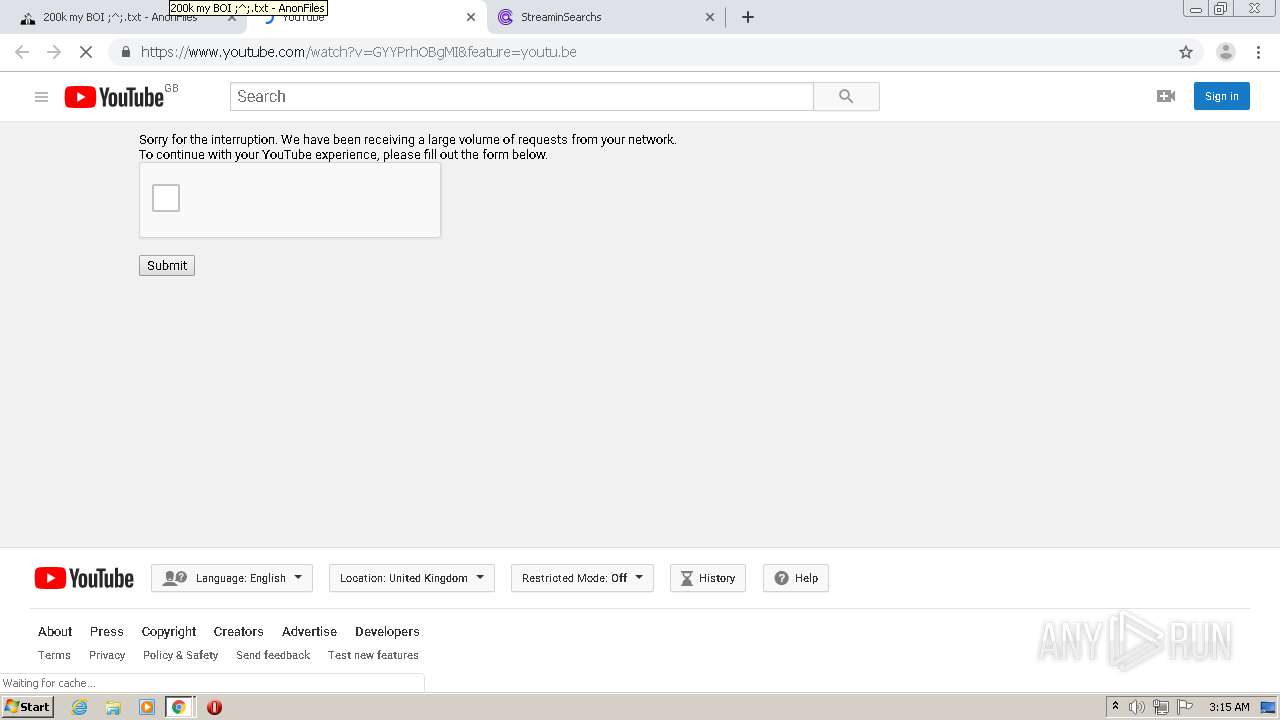
| Verdict: | Malicious activity |
| Analysis date: | October 06, 2020, 02:14:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6CBA4AB394D6B83DADE720B8455CCC1D |
| SHA1: | A6A7613B776E21746AC24A890ABB5D654F3027A9 |
| SHA256: | 9866D39DF0A5D559CCBA03FF12663F0392DBEB8FC35862087520ED4A8B647A87 |
| SSDEEP: | 3:N8cHWLE0D02l+n67bZRyVk:2cHWBQ2lz/vyG |
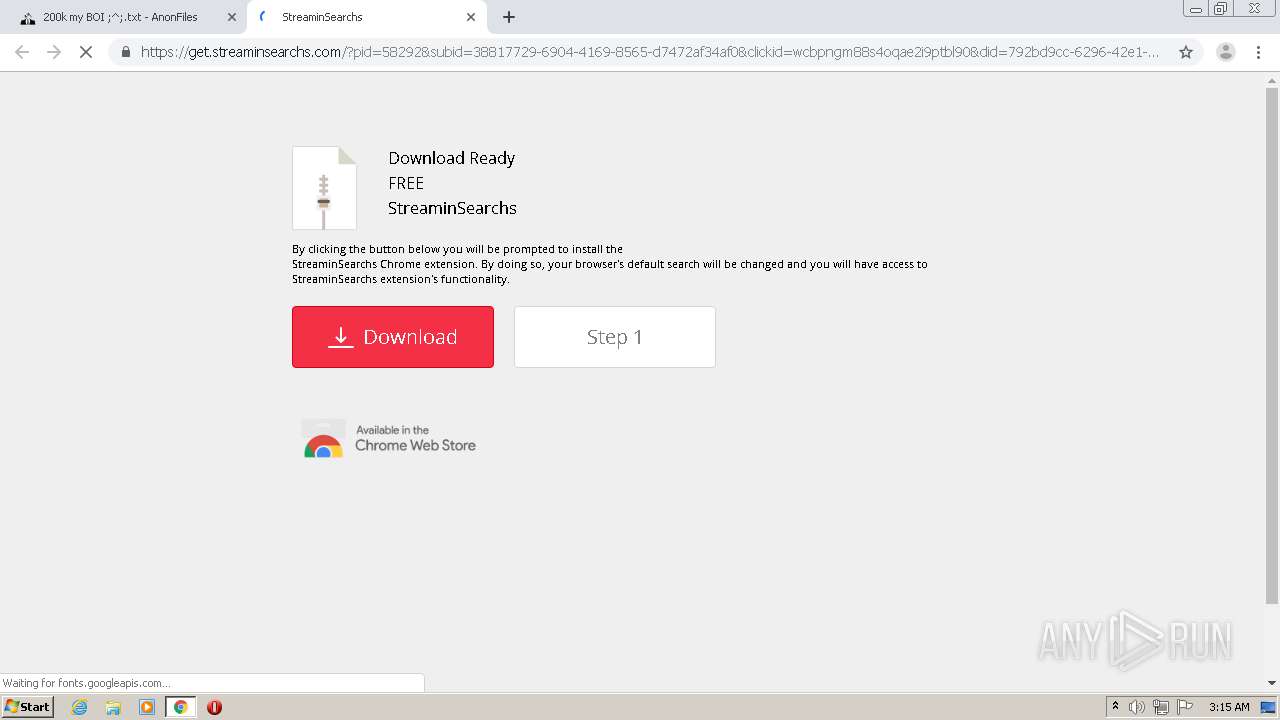
MALICIOUS
Loads dropped or rewritten executable
- software_reporter_tool.exe (PID: 2328)
SUSPICIOUS
Application launched itself
- software_reporter_tool.exe (PID: 2768)
Executable content was dropped or overwritten
- software_reporter_tool.exe (PID: 2328)
INFO
Reads the hosts file
- chrome.exe (PID: 1352)
- chrome.exe (PID: 2448)
- software_reporter_tool.exe (PID: 2328)
Reads settings of System Certificates
- chrome.exe (PID: 1352)
Reads Internet Cache Settings
- chrome.exe (PID: 2448)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 2768)
Application launched itself
- chrome.exe (PID: 2448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
33
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16079353481638593213 --mojo-platform-channel-handle=1084 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12890289512817048894 --mojo-platform-channel-handle=3696 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 612 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\85.244.200\software_reporter_tool.exe" --use-crash-handler-with-id="\\.\pipe\crashpad_2768_JWOAEILQIIPQCOZA" --sandboxed-process-id=3 --init-done-notifier=648 --sandbox-mojo-pipe-token=559415511061711165 --mojo-platform-channel-handle=644 | c:\users\admin\appdata\local\google\chrome\user data\swreporter\85.244.200\software_reporter_tool.exe | — | software_reporter_tool.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 85.244.200 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=694735690470647057 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4386143082819161717 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10666769259822013776 --mojo-platform-channel-handle=1652 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17956846070174941576 --mojo-platform-channel-handle=4408 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16338813664700270296 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14631676731926999367 --mojo-platform-channel-handle=4816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7955736288763540258,2873060626198905285,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8740458435067156553 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 722
Read events
1 581
Write events
136
Delete events
5
Modification events
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2448-13246424096504625 |
Value: 259 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
7
Suspicious files
70
Text files
120
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7BD321-990.pma | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d6b447da-6d97-43fa-8417-182ba3bc4b72.tmp | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF227c2f.TMP | text | |
MD5:C5C3F347BDC11EA7A5BF62BCEA89896F | SHA256:EAE604A1C662FF82AD4B2D1056179FD77587159FDD7F1674404C0465E0610BC1 | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:D55489ED6031D8B188E37B0B59F5CED3 | SHA256:365B01D1B3333E366EEA50106551AAC8721156CB2572C173E2F501D8255093F4 | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D33038DC70A58F2AC0EA1823980691AE | SHA256:6EE5DB5588EB879D13CE5A0DB3CA1744079C1BE3F73959A3B900684C56061D97 | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF227ba3.TMP | text | |
MD5:D55489ED6031D8B188E37B0B59F5CED3 | SHA256:365B01D1B3333E366EEA50106551AAC8721156CB2572C173E2F501D8255093F4 | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF227bc2.TMP | text | |
MD5:D33038DC70A58F2AC0EA1823980691AE | SHA256:6EE5DB5588EB879D13CE5A0DB3CA1744079C1BE3F73959A3B900684C56061D97 | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF227bd1.TMP | text | |
MD5:4AFC066387D33D5264F8E796393B223B | SHA256:BB3E0F925E883318FB09FC498CACEA57F0F71548C9D42FF07634DC30D87F2D86 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
74
DNS requests
46
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1352 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://p38959.infopicked.com/adServe/adClick?ai=0ZZYOQncnLLygYaeN_ogCEWPjLAdPW32tdDgEHrlCRf1VVxiAihgctp6_ZxcTEnP4uGkhojmOu1qgEE0f5Fjh8XnLiFpVgC8Bvf4RIcbQkeDZG8TCuTZ6pDoEwlyap2k9L7wOxwEDQ9BfltkFZI6N4rtiFWCJ0y_eub2udAkMGYfs6Cn0z345rIpji393ajEk-V6deFDbkjcZIG_Ly15tFE_VEqSqib4vsB0iuJvaA4l_jIE1GWrF0-cSEhrDbOxEkcnN0O_o7n7N9RLydVTTh8VzEnRK1KGnazT_fgIBNS4dnN5JBOCTIW_9plALkDivgUM53Dzny0iZs55fPbhlVFjRcsj7Dbq1aOuLzwF6DpmidZ79W2X0a0UsLykwuxQDlFQO5HpzDylIYjrVuUqBuIqupiDgyg5cfv9rkpXfEQ&ui=hiGmeMjYzIlAaSSkI8iNoYBVNmK1S2tVjfM2xjdriHncZIG_Ly15tLJqHafQWAef0hwjbiArSZIMnRdpq49kYQP8O6EKhacW9L10I_PigsAN4D6ropPLPg&si=1&oref=30286164771eb5a68a047c937c01cb0e&rb=SZ6PmHOhBzc&rr=0&isco=t | US | — | — | suspicious |
1352 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://infopicked.com/aS/feedclick?s=hiGmeMjYzIlKXjyk3vOPJ8jqPpYD9LTmGCJeMqQw6rka0zymz_z9HJ1B-kb1vwChg2RvEwrk2epbC7U30TJp2Vxkt_oJ3Fy87jh-44tx_Ptt8hoBlUReV6YZ_8dAZcE416Cb7hxfzEM4RfiIYZyFTV0WfNhsVgysik5v6sWwxOrU-u1UlsHMunFHHKl4A1HPxpAmoPWwW09NaVWizTMv8BQNw9qzQgJTdtCPVuHwqR0QtFRGWrboUPZY6k_PJQh_4VOGxntPBB7qLTEqL2zDEZAeDhYUSrJJU9vuK6LUSYBhLkoSY0NWgUbcJ2CUh6x7NczERX-MDqHDJe0MfQ58fp-fdZ9TUaxQJUN0GUQEO6H6CT6TWwOM3l_YSSYoJ4ksIS6k1A_qNTYnYaBnM6KyzXZupPAIBT3bwhFxmRaYHSUNzViGrhVO7p6O6MZrW94bEqLoNjeeTiSia_iPu8zVsGoV4lvZAilST6qQhsbHGYRf0HB3f36b9G0CNYi0b2biPTUH2IPk6zHoNiYd6UTexsV0iYoT9eEbokFV1AabnQZZ-UESwxHfP0I5tUmsDxzmWnaJm8wZeJbFYkmdyeiIc1wSqdUe-79w67LEGTHnujSJsOO_eZzMDhTtDTjDXMLU7S6wmW6p6oHzkv0aXIF_-82LwVRZL0Q_Yq5r6Uah3lUyk2Itk1he--q-YWrZXK1SmTEJTCx0T8k6z5XMZozKFwDmx_BHqn0DvN7xH6uzPcBYUeA8uZ6oqwoPY_BMZZ3RcP3xDGKKU9c---ZGbydw_p7xWX1aedA9Sud5XZ9xENCk-DwvqBEPX4MM4zZWzlUJAH6Jfh8-XiH-Rz2Y0tt-HkF7_p0u7MZDi3n5Gd5amg2wk5DhEG2BbS723bAEJynartg5Yuugvl7nAA319rQT5cwGXvlfKPPUbBIVfTqqiWazTE56hdN7AFPTLyEquuhjIerNKT4pGDupvY895NyWiNeY_JnsouBr9mn05_3sEJ-M43HctUWGfKT6Ifj6CGUXDd6khgw1xizex3btw87HaAp4fFE_zlx7_Kbc8xtuWKx-wwWZE6djSweIx6tRiLMQVrpRduPoD8AQvEzNJDopS07PspS4ce5Ih2wApnarYZDboge6B5BeXWGKtkyD3Tx42zgR1Avg6tDbwvvbE7RQ6YbqWD6qn0jRKR9hdWwA1ZpomvM_97p_95FbbPGz0pVNvZjHVhXKzGIdzIXFRcYr3dxkgb8vLXm0XMI_gTAeUe4iYKVJ68R9GtDkxL52zj9CxoQ1aUtfzVSHVDv-ud4rYbkcEcAYjxpLlpK2VK0hYxrYgG7afTXkyA | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1352 | chrome.exe | 45.148.16.55:443 | cdn-33.anonfiles.com | — | — | suspicious |
1352 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1352 | chrome.exe | 104.24.117.23:443 | anonfiles.com | Cloudflare Inc | US | malicious |
1352 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
1352 | chrome.exe | 13.224.186.5:443 | djv99sxoqpv11.cloudfront.net | — | US | suspicious |
1352 | chrome.exe | 52.206.71.220:443 | baconaces.pro | Amazon.com, Inc. | US | suspicious |
1352 | chrome.exe | 143.204.94.112:443 | nesjournin.top | — | US | unknown |
— | — | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1352 | chrome.exe | 74.125.140.188:5228 | mtalk.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
cdn-33.anonfiles.com |
| suspicious |
accounts.google.com |
| shared |
anonfiles.com |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
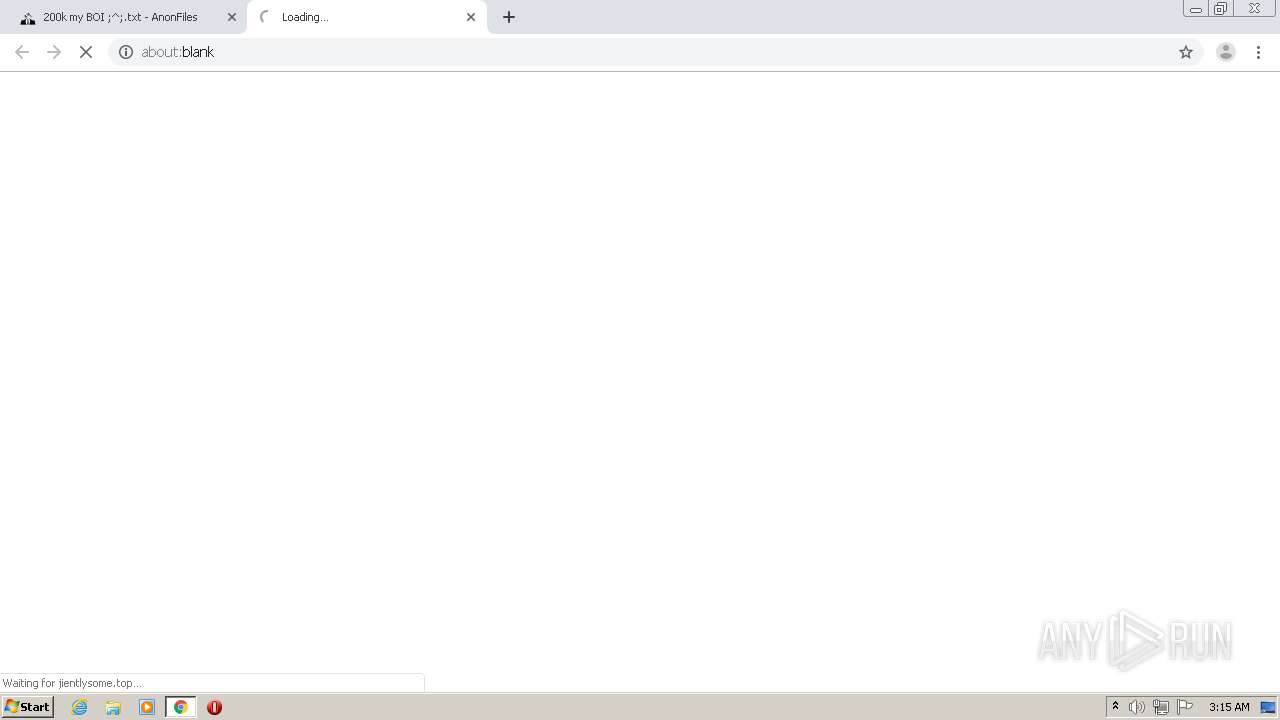
jientlysome.top |
| suspicious |
ratesphospit.club |
| suspicious |
providentsopport.site |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |