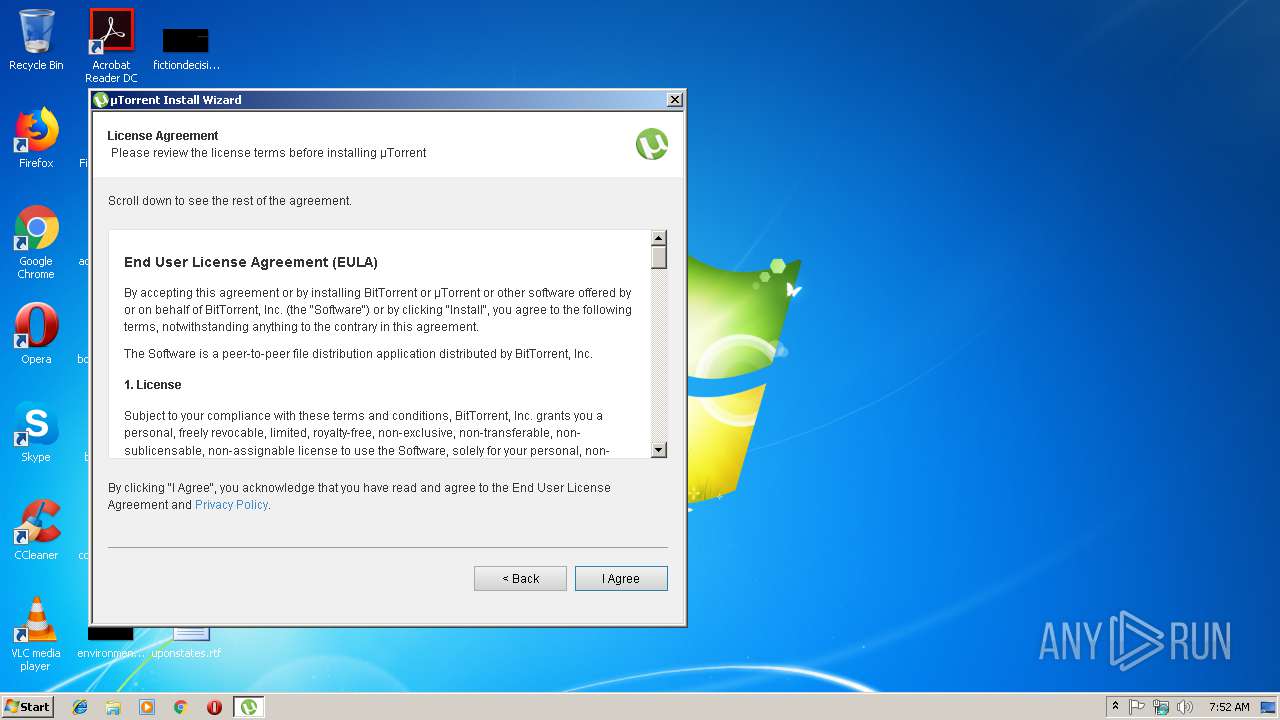
| File name: | uTorrent.exe |
| Full analysis: | https://app.any.run/tasks/765e0e99-7330-48e3-a24a-eae674c39279 |
| Verdict: | Malicious activity |
| Analysis date: | November 18, 2018, 07:52:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | BBF865B2B40FF6251425916A680FCDDC |
| SHA1: | 754B1B4A7780114421E2873F51CBA9CF002442E3 |
| SHA256: | 9861D6B2DB55A3596C006F46D874207EC27481D81120CEFB41F1BCCDA7C7ED49 |
| SSDEEP: | 49152:myzfgKcALHZYz/G6OavB3Ny+FQNsVu7GoL4hO:7+AjZYz/Goy6QAu7GUsO |
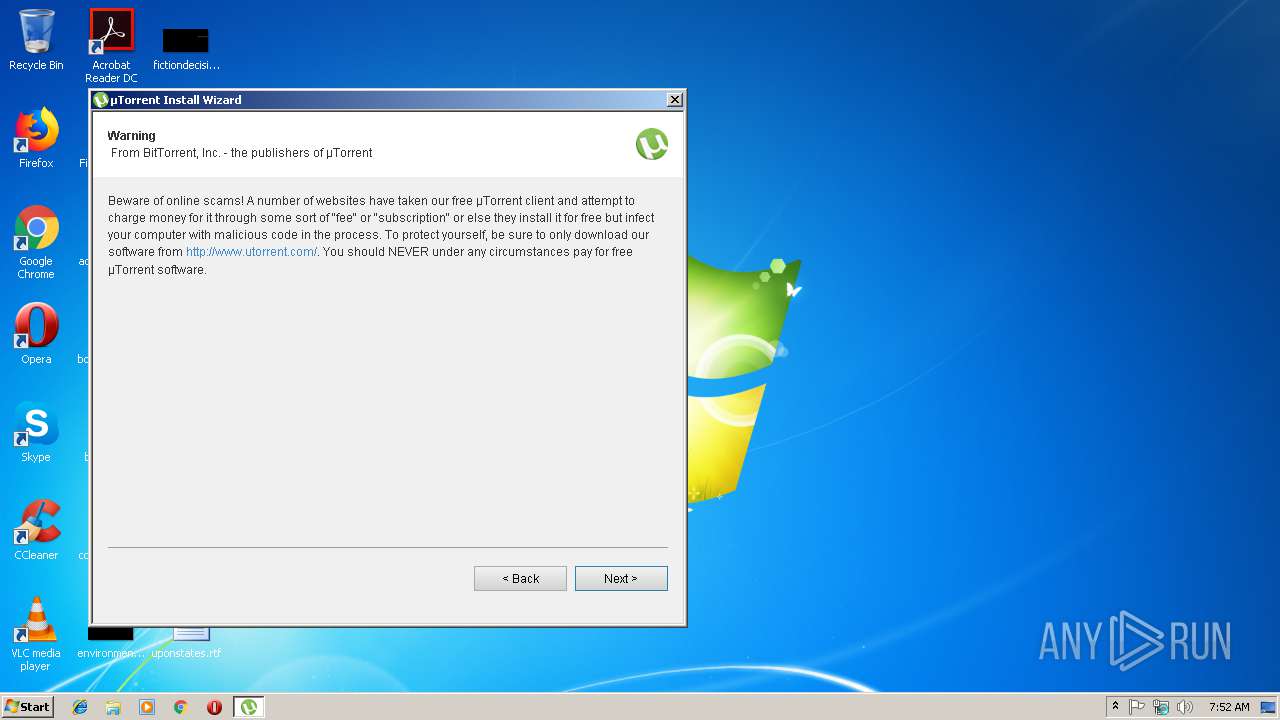
MALICIOUS
Runs PING.EXE for delay simulation
- mshta.exe (PID: 2496)
SUSPICIOUS
Application launched itself
- uTorrent.exe (PID: 3792)
Executable content was dropped or overwritten
- uTorrent.exe (PID: 3792)
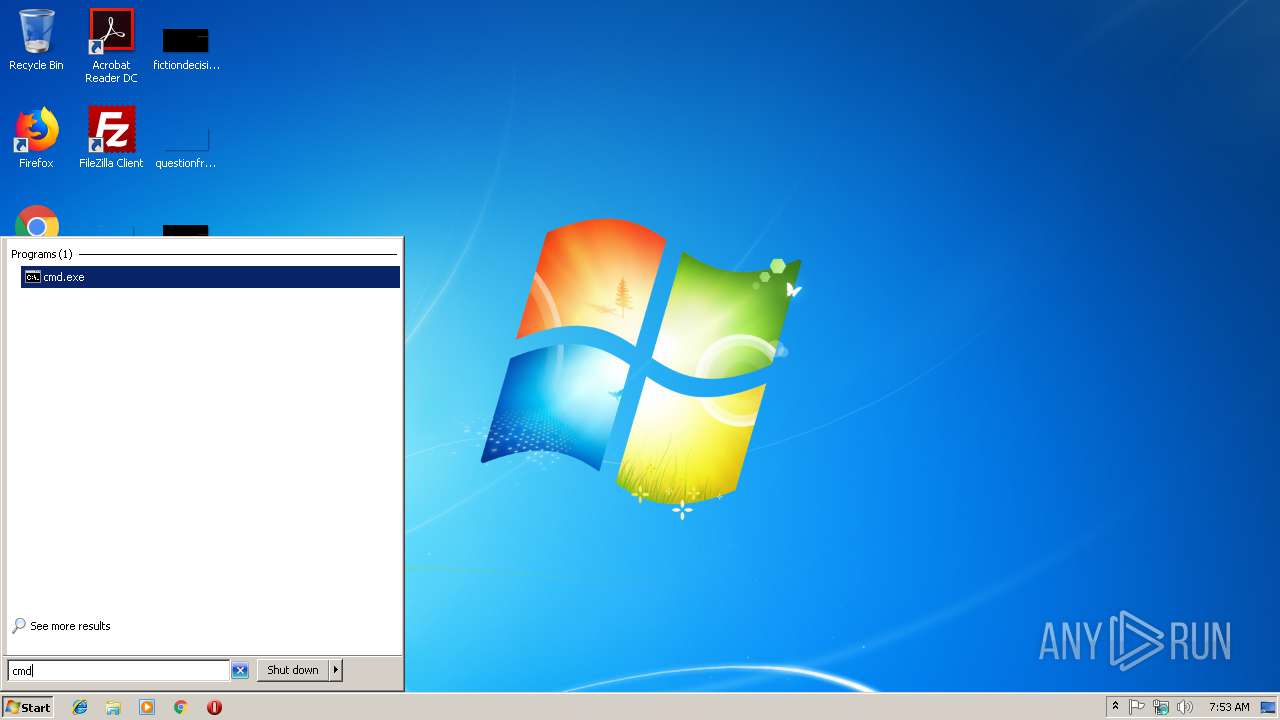
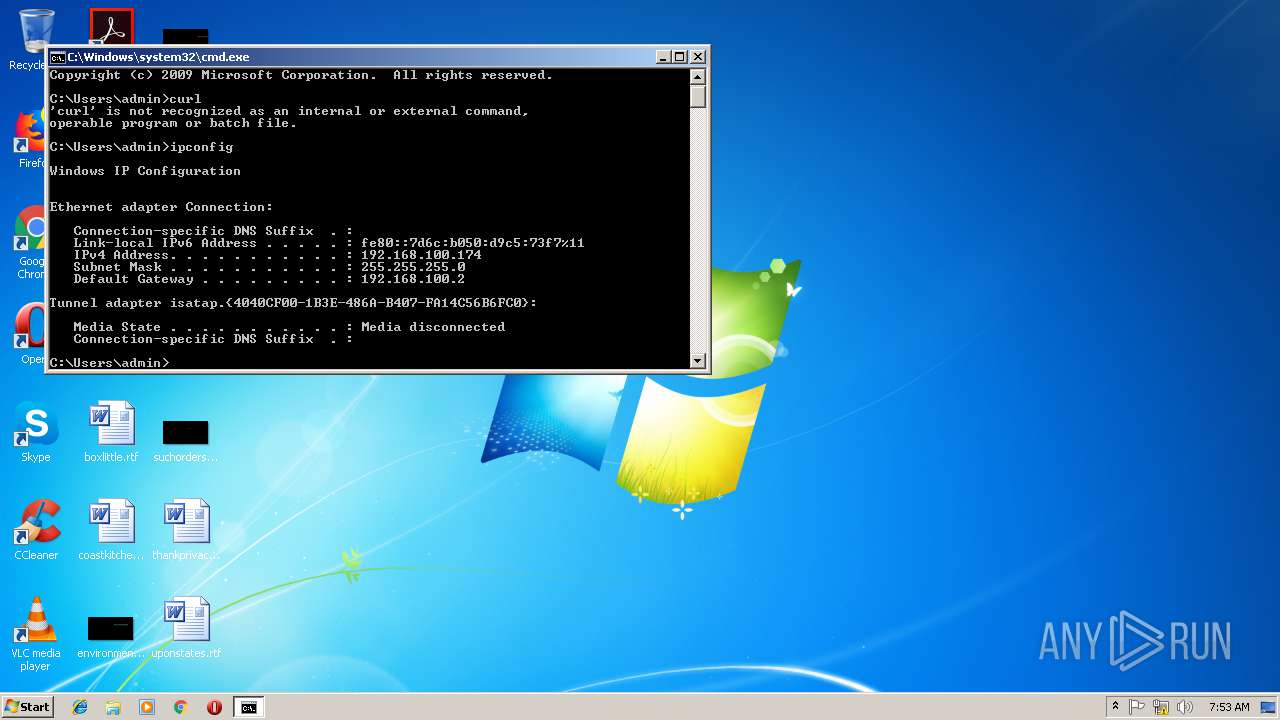
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3076)
Creates files in the user directory
- uTorrent.exe (PID: 3792)
- uTorrent.exe (PID: 4064)
Executes scripts
- mshta.exe (PID: 2496)
Checks for external IP
- mshta.exe (PID: 2496)
Starts MSHTA.EXE for opening HTA or HTMLS files
- uTorrent.exe (PID: 4064)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:27 20:16:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1843200 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | 3420160 |
| EntryPoint: | 0x505360 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
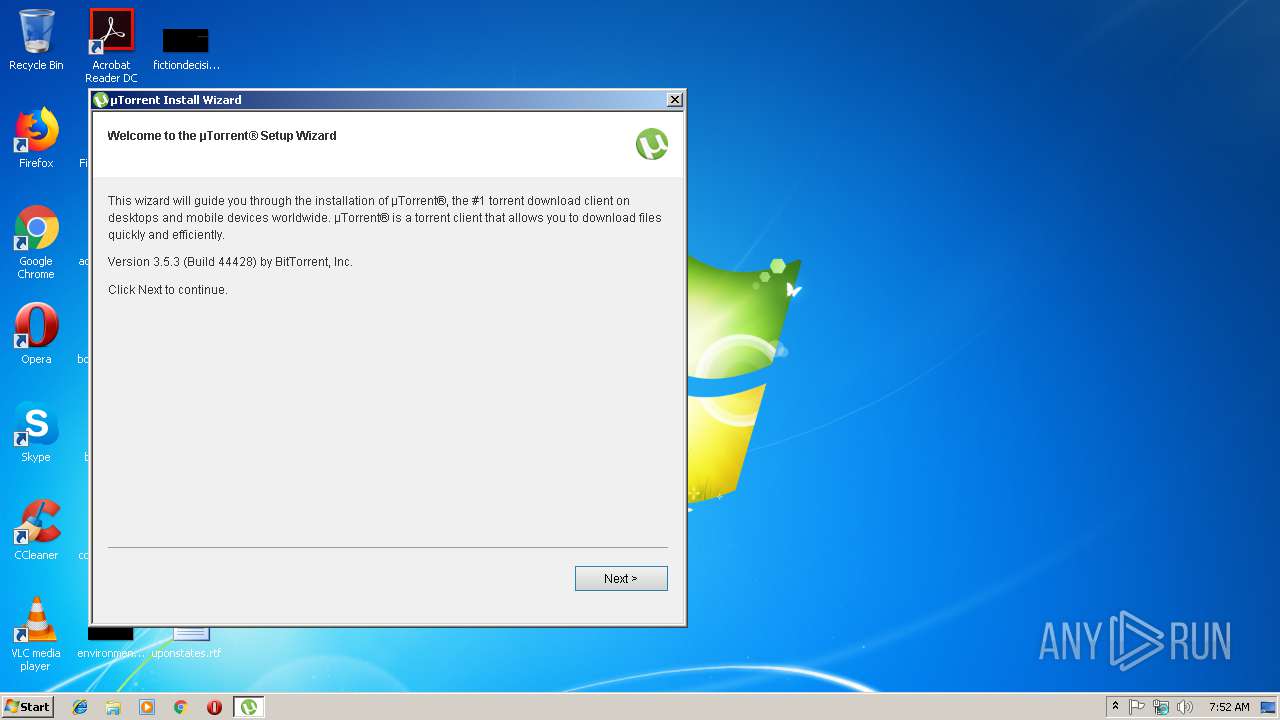
| FileVersionNumber: | 3.5.3.44428 |
| ProductVersionNumber: | 3.5.3.44428 |
| FileFlagsMask: | 0x002b |
| FileFlags: | Special build |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | BitTorrent Inc. |
| FileDescription: | µTorrent |
| FileVersion: | 3.5.3.44428 |
| InternalName: | uTorrent.exe |
| OriginalFileName: | uTorrent.exe |
| LegalCopyright: | ©2018 BitTorrent, Inc. All Rights Reserved. |
| ProductName: | µTorrent |
| ProductVersion: | 3.5.3.44428 |
| SpecialBuild: | stable34 stable |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2018 18:16:16 |
| Detected languages: |
|
| CompanyName: | BitTorrent Inc. |
| FileDescription: | µTorrent |
| FileVersion: | 3.5.3.44428 |
| InternalName: | uTorrent.exe |
| OriginalFilename: | uTorrent.exe |
| LegalCopyright: | ©2018 BitTorrent, Inc. All Rights Reserved. |
| ProductName: | µTorrent |
| ProductVersion: | 3.5.3.44428 |
| SpecialBuild: | stable34 stable |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000150 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 27-Apr-2018 18:16:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00343000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00344000 | 0x001C2000 | 0x001C2000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99989 |
.rsrc | 0x00506000 | 0x0001F000 | 0x0001EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.01903 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11079 | 1835 | UNKNOWN | Swedish - Sweden | RT_MANIFEST |
2 | 7.80177 | 1003 | UNKNOWN | Swedish - Sweden | RT_HTML |
3 | 5.68396 | 62 | UNKNOWN | Swedish - Sweden | RT_GROUP_ICON |
4 | 7.9813 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.22193 | 20 | UNKNOWN | Swedish - Sweden | RT_GROUP_ICON |
6 | 7.98047 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 7.98153 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 7.98277 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 7.97825 | 9640 | UNKNOWN | English - United States | RT_ICON |
10 | 6.37443 | 114 | UNKNOWN | Swedish - Sweden | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
DNSAPI.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSIMG32.dll |
OLEAUT32.dll |
PSAPI.DLL |
Total processes
48
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | ipconfig | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2228 | "C:\Windows\System32\PING.EXE" 8.8.8.8 -n 2 -w 500 | C:\Windows\System32\PING.EXE | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\HYD9B4F.tmp.1542527541\HTA\index.hta?utorrent" "C:\Users\admin\AppData\Local\Temp\uTorrent.exe" /LOG "C:\Users\admin\AppData\Local\Temp\HYD9B4F.tmp.1542527541\index.hta.log" /PID "4064" /CID "j5K40Ta2kir1Gg8E" /VERSION "111652236" /BUCKET "0" /SSB "3" /COUNTRY "US" /OS "6.1" /BROWSERS "\"C:\Program Files\Mozilla Firefox\firefox.exe\",\"C:\Program Files\Google\Chrome\Application\chrome.exe\",C:\Program Files\Internet Explorer\iexplore.exe,\"C:\Program Files\Opera\Opera.exe\"" /ARCHITECTURE "32" /LANG "en" /USERNAME "admin" /SID "S-1-5-21-1302019708-1500728564-335382590-1000" /CLIENT "utorrent" | C:\Windows\System32\mshta.exe | uTorrent.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Windows\System32\cscript.exe" "shell_scripts/check_if_cscript_is_working.js" | C:\Windows\System32\cscript.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 99 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3076 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3140 | "C:\Windows\System32\cscript.exe" shell_scripts/shell_ping_after_close.js "http://i-50.b-000.XYZ.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFiZWdpbiIsInBpZCI6IjQwNjQiLCJoIjoiajVLNDBUYTJraXIxR2c4RSIsInYiOiIxMTE2NTIyMzYiLCJiIjo0NDQyOCwiY2wiOiJ1VG9ycmVudCIsIm9zYSI6IjMyIiwic2xuZyI6ImVuIiwiZGIiOiJXaW5kb3dzIEludGVybmV0IEV4cGxvcmVyIiwiZGJ2IjoiOC4wIiwiaWJyIjpbeyJuYW1lIjoiRmlyZWZveCIsInZlcnNpb24iOiI2MS4wIiwiZXhlTmFtZSI6ImZpcmVmb3gifSx7Im5hbWUiOiJHb29nbGUgQ2hyb21lIiwidmVyc2lvbiI6IjY4LjAiLCJleGVOYW1lIjoiY2hyb21lIn0seyJuYW1lIjoiV2luZG93cyBJbnRlcm5ldCBFeHBsb3JlciIsInZlcnNpb24iOiI4LjAiLCJleGVOYW1lIjoiaWV4cGxvcmUifSx7Im5hbWUiOiJPcGVyYSBJbnRlcm5ldCBCcm93c2VyIiwidmVyc2lvbiI6IjEyLjE1IiwiZXhlTmFtZSI6Im9wZXJhIn1dLCJpcCI6IjE4NS4xMDQuMTg2LjkzIiwiY24iOiJCZWxnaXVtIiwicGFja2lkIjoibGF2YXNvZnRfYmluZyJ9" | C:\Windows\System32\cscript.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3300 | "C:\Windows\System32\cscript.exe" shell_scripts/shell_ping_after_close.js "http://i-50.b-000.XYZ.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFDYW5jZWxsZWQiLCJwaWQiOiI0MDY0IiwiaCI6Imo1SzQwVGEya2lyMUdnOEUiLCJ2IjoiMTExNjUyMjM2IiwiYiI6NDQ0MjgsImNsIjoidVRvcnJlbnQiLCJvc2EiOiIzMiIsInNsbmciOiJlbiIsImRiIjoiV2luZG93cyBJbnRlcm5ldCBFeHBsb3JlciIsImRidiI6IjguMCIsImliciI6W3sibmFtZSI6IkZpcmVmb3giLCJ2ZXJzaW9uIjoiNjEuMCIsImV4ZU5hbWUiOiJmaXJlZm94In0seyJuYW1lIjoiR29vZ2xlIENocm9tZSIsInZlcnNpb24iOiI2OC4wIiwiZXhlTmFtZSI6ImNocm9tZSJ9LHsibmFtZSI6IldpbmRvd3MgSW50ZXJuZXQgRXhwbG9yZXIiLCJ2ZXJzaW9uIjoiOC4wIiwiZXhlTmFtZSI6ImlleHBsb3JlIn0seyJuYW1lIjoiT3BlcmEgSW50ZXJuZXQgQnJvd3NlciIsInZlcnNpb24iOiIxMi4xNSIsImV4ZU5hbWUiOiJvcGVyYSJ9XSwiaXAiOiIxODUuMTA0LjE4Ni45MyIsImNuIjoiQmVsZ2l1bSIsInBhY2tpZCI6ImxhdmFzb2Z0X2JpbmcifQ==" | C:\Windows\System32\cscript.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3792 | "C:\Users\admin\AppData\Local\Temp\uTorrent.exe" | C:\Users\admin\AppData\Local\Temp\uTorrent.exe | explorer.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: MEDIUM Description: µTorrent Exit code: 0 Version: 3.5.3.44428 Modules
| |||||||||||||||
| 4064 | "C:\Users\admin\AppData\Local\Temp\uTorrent.exe" /HYDRA_PERMISSIONS_RESTART /HYDRA_LOG "C:\Users\admin\AppData\Local\Temp\HYD9B4F.tmp.1542527541\index.hta.log" /HYDRA_HTADIR "C:\Users\admin\AppData\Local\Temp\HYD9B4F.tmp.1542527541\HTA" | C:\Users\admin\AppData\Local\Temp\uTorrent.exe | uTorrent.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: HIGH Description: µTorrent Exit code: 0 Version: 3.5.3.44428 Modules
| |||||||||||||||
Total events
699
Read events
666
Write events
33
Delete events
0
Modification events
| (PID) Process: | (3792) uTorrent.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4064) uTorrent.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2496) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2496) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2496) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2496) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2496) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: mshta.exe | |||
| (PID) Process: | (2496) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 1247528542 | |||
| (PID) Process: | (2496) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: mshta.exe | |||
Executable files
1
Suspicious files
11
Text files
37
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\Cab99B2.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\Tar99B3.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\Cab99C4.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\Tar99C5.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\Cab9A53.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\Tar9A54.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\Roaming\uTorrent\settings.dat.new | — | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\Roaming\uTorrent\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94308059B57B3142E455B38A6EB92015 | compressed | |
MD5:— | SHA256:— | |||
| 3792 | uTorrent.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
13
DNS requests
9
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | uTorrent.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
4064 | uTorrent.exe | POST | 200 | 174.129.255.167:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
2496 | mshta.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json?callback=jQuery19103005742095023638_1542527544828&_=1542527544829 | DE | text | 327 b | malicious |
4064 | uTorrent.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
3140 | cscript.exe | GET | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFiZWdpbiIsInBpZCI6IjQwNjQiLCJoIjoiajVLNDBUYTJraXIxR2c4RSIsInYiOiIxMTE2NTIyMzYiLCJiIjo0NDQyOCwiY2wiOiJ1VG9ycmVudCIsIm9zYSI6IjMyIiwic2xuZyI6ImVuIiwiZGIiOiJXaW5kb3dzIEludGVybmV0IEV4cGxvcmVyIiwiZGJ2IjoiOC4wIiwiaWJyIjpbeyJuYW1lIjoiRmlyZWZveCIsInZlcnNpb24iOiI2MS4wIiwiZXhlTmFtZSI6ImZpcmVmb3gifSx7Im5hbWUiOiJHb29nbGUgQ2hyb21lIiwidmVyc2lvbiI6IjY4LjAiLCJleGVOYW1lIjoiY2hyb21lIn0seyJuYW1lIjoiV2luZG93cyBJbnRlcm5ldCBFeHBsb3JlciIsInZlcnNpb24iOiI4LjAiLCJleGVOYW1lIjoiaWV4cGxvcmUifSx7Im5hbWUiOiJPcGVyYSBJbnRlcm5ldCBCcm93c2VyIiwidmVyc2lvbiI6IjEyLjE1IiwiZXhlTmFtZSI6Im9wZXJhIn1dLCJpcCI6IjE4NS4xMDQuMTg2LjkzIiwiY24iOiJCZWxnaXVtIiwicGFja2lkIjoibGF2YXNvZnRfYmluZyJ9 | US | text | 21 b | whitelisted |
3300 | cscript.exe | GET | 200 | 54.235.208.27:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFDYW5jZWxsZWQiLCJwaWQiOiI0MDY0IiwiaCI6Imo1SzQwVGEya2lyMUdnOEUiLCJ2IjoiMTExNjUyMjM2IiwiYiI6NDQ0MjgsImNsIjoidVRvcnJlbnQiLCJvc2EiOiIzMiIsInNsbmciOiJlbiIsImRiIjoiV2luZG93cyBJbnRlcm5ldCBFeHBsb3JlciIsImRidiI6IjguMCIsImliciI6W3sibmFtZSI6IkZpcmVmb3giLCJ2ZXJzaW9uIjoiNjEuMCIsImV4ZU5hbWUiOiJmaXJlZm94In0seyJuYW1lIjoiR29vZ2xlIENocm9tZSIsInZlcnNpb24iOiI2OC4wIiwiZXhlTmFtZSI6ImNocm9tZSJ9LHsibmFtZSI6IldpbmRvd3MgSW50ZXJuZXQgRXhwbG9yZXIiLCJ2ZXJzaW9uIjoiOC4wIiwiZXhlTmFtZSI6ImlleHBsb3JlIn0seyJuYW1lIjoiT3BlcmEgSW50ZXJuZXQgQnJvd3NlciIsInZlcnNpb24iOiIxMi4xNSIsImV4ZU5hbWUiOiJvcGVyYSJ9XSwiaXAiOiIxODUuMTA0LjE4Ni45MyIsImNuIjoiQmVsZ2l1bSIsInBhY2tpZCI6ImxhdmFzb2Z0X2JpbmcifQ== | US | text | 21 b | whitelisted |
4064 | uTorrent.exe | POST | 200 | 54.235.208.27:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
4064 | uTorrent.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
3792 | uTorrent.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
3792 | uTorrent.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | uTorrent.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
3792 | uTorrent.exe | 54.235.208.27:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | whitelisted |
3792 | uTorrent.exe | 67.215.238.66:80 | download-lb.utorrent.com | QuadraNet, Inc | US | suspicious |
4064 | uTorrent.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
2496 | mshta.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
3140 | cscript.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
4064 | uTorrent.exe | 54.235.208.27:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | whitelisted |
3300 | cscript.exe | 54.235.208.27:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | whitelisted |
4064 | uTorrent.exe | 174.129.255.167:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | whitelisted |
3792 | uTorrent.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
router.bittorrent.com |
| shared |
router.utorrent.com |
| whitelisted |
i-50.b-000.xyz.bench.utorrent.com |
| whitelisted |
download-lb.utorrent.com |
| whitelisted |
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3792 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3792 | uTorrent.exe | A Network Trojan was detected | MALWARE [PTsecurity] P2P uTorrent Hydra Client |
3792 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client response_code |
3792 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3792 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client response_code |
3792 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3792 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client response_code |
3792 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3792 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client response_code |
4064 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
9 ETPRO signatures available at the full report