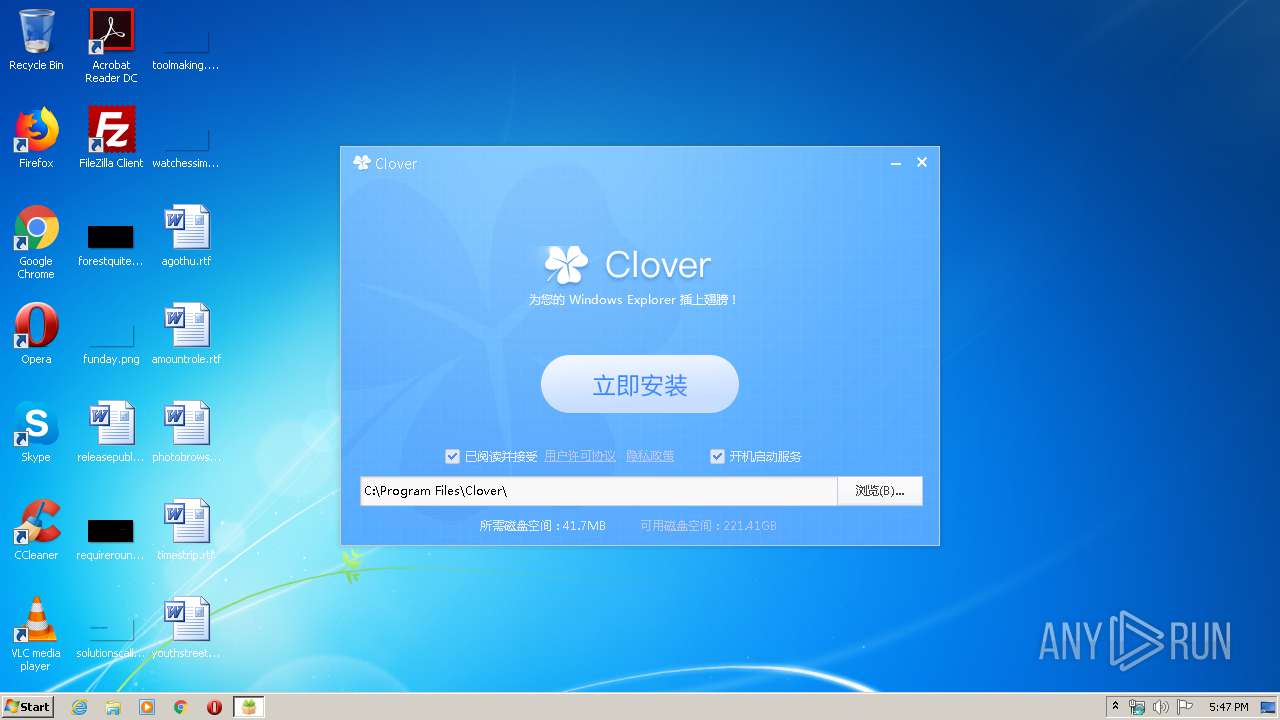
| File name: | setup_clover@3.5.4.exe |
| Full analysis: | https://app.any.run/tasks/ad2b185f-3a80-481e-a7a3-b9fb1048d296 |
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2020, 16:47:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 12A57F152E0FC65517B1C22629F87430 |
| SHA1: | F5CF35BF021675B02C8299CFF95E53DC6DB95890 |
| SHA256: | 9847281C4CACA7B50D73839B8D1A8426A16D55C551EBD55C5854F29BCF517910 |
| SSDEEP: | 196608:fgJIqr+XnTHTDwTnH01T6yzGAKV+WRjgtgEYcK7yEbDj0Hm+9/3OeuWLKCgOEFaV:2Iqr+XT601T62CUgEYcgyC0H39Bl5gbQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- setup_clover@3.5.4.exe (PID: 2488)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (46.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (41) |
| .exe | | | Win32 Executable (generic) (6.6) |
| .exe | | | Generic Win/DOS Executable (2.9) |
| .exe | | | DOS Executable Generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:04:22 13:23:06+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 819200 |
| InitializedDataSize: | 11587584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x45ae8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.4.20416 |
| ProductVersionNumber: | 3.5.4.20416 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| Comments: | Clover 安装程序 |
| CompanyName: | ejie.me |
| FileDescription: | Clover 安装程序 |
| FileVersion: | 3.5.4.20416 |
| InternalName: | Clover |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFileName: | Clover.exe |
| ProductName: | Clover |
| ProductVersion: | 3.5.4.20416 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Apr-2020 11:23:06 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | Clover 安装程序 |
| CompanyName: | ejie.me |
| FileDescription: | Clover 安装程序 |
| FileVersion: | 3.5.4.20416 |
| InternalName: | Clover |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFilename: | Clover.exe |
| ProductName: | Clover |
| ProductVersion: | 3.5.4.20416 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Apr-2020 11:23:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000C7DF7 | 0x000C8000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63964 |
.rdata | 0x000C9000 | 0x0003EDCD | 0x0003F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.59911 |
.data | 0x00108000 | 0x0000B37C | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.21968 |
.rsrc | 0x00114000 | 0x00AC9F28 | 0x00ACA000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99616 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.38137 | 1029 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 5.92989 | 38056 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.92522 | 21640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.80675 | 16936 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 6.02365 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 5.93799 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 2.09229 | 66 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 6.08658 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 3.02695 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
10 | 2.74274 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
??0CActiveXUI@DuiLib@@QAE@ABV01@@Z | 1 | 0x00093876 |
??0CActiveXUI@DuiLib@@QAE@XZ | 2 | 0x000B1E97 |
??0CButtonGifUI@DuiLib@@QAE@ABV01@@Z | 3 | 0x00092FB5 |
??0CButtonGifUI@DuiLib@@QAE@XZ | 4 | 0x000AC863 |
??0CButtonUI@DuiLib@@QAE@ABV01@@Z | 5 | 0x00092D9A |
??0CButtonUI@DuiLib@@QAE@XZ | 6 | 0x000ABBD2 |
??0CCheckBoxUI@DuiLib@@QAE@ABV01@@Z | 7 | 0x00093287 |
??0CCheckBoxUI@DuiLib@@QAE@XZ | 8 | 0x00093223 |
??0CChildLayoutUI@DuiLib@@QAE@ABV01@@Z | 9 | 0x00094425 |
??0CChildLayoutUI@DuiLib@@QAE@XZ | 10 | 0x000B4DAC |
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2488 | "C:\Users\admin\AppData\Local\Temp\setup_clover@3.5.4.exe" | C:\Users\admin\AppData\Local\Temp\setup_clover@3.5.4.exe | explorer.exe | ||||||||||||
User: admin Company: ejie.me Integrity Level: HIGH Description: Clover 安装程序 Exit code: 0 Version: 3.5.4.20416 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\Temp\setup_clover@3.5.4.exe" | C:\Users\admin\AppData\Local\Temp\setup_clover@3.5.4.exe | — | explorer.exe | |||||||||||
User: admin Company: ejie.me Integrity Level: MEDIUM Description: Clover 安装程序 Exit code: 3221226540 Version: 3.5.4.20416 Modules
| |||||||||||||||
Total events
18
Read events
18
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2488 | setup_clover@3.5.4.exe | C:\Program Files\Common Files\Clover\Clover.ini | text | |
MD5:7AE7390B4FD7F79667F40101E174E7E0 | SHA256:4EE0E8B8789E61C80CC151D54CB8C6ACE2A6B744703A46CAF3D63C8CD85AED73 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2488 | setup_clover@3.5.4.exe | GET | 200 | 106.75.47.98:80 | http://tjv1.ejie.me/statistics/timestamp | CN | text | 26 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2488 | setup_clover@3.5.4.exe | 106.75.47.98:80 | tjv1.ejie.me | China Unicom Beijing Province Network | CN | malicious |
2488 | setup_clover@3.5.4.exe | 47.89.39.18:80 | config.ejie.me | Alibaba (China) Technology Co., Ltd. | HK | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tjv1.ejie.me |
| unknown |
config.ejie.me |
| unknown |