| File name: | lockhuntersetup_3-4-3.exe |
| Full analysis: | https://app.any.run/tasks/553d98fc-fb67-4077-afbf-ed90c85c2e76 |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2022, 10:31:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 56FD7145224989B92494A32E8FC6F6B6 |
| SHA1: | D8CB0D5BBEB20E08DF8D2E75D7F4E326961F1BF5 |
| SHA256: | 982DDA5EEC52DD54FF6B0B04FD9BA8F4C566534B78F6A46DADA624AF0316044E |
| SSDEEP: | 49152:m8lKHdlR013v+ykqhNyYVuUpmO7NdBxV+k1ic6ROEpANEZ57vqmGAe:udlC1XzhNnE/qx88CANE3iV |
MALICIOUS
Drops executable file immediately after starts
- lockhuntersetup_3-4-3.exe (PID: 3520)
- lockhuntersetup_3-4-3.exe (PID: 2920)
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Registers / Runs the DLL via REGSVR32.EXE
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2516)
- svchost.exe (PID: 860)
- Explorer.EXE (PID: 1376)
Application was dropped or rewritten from another process
- LockHunter.exe (PID: 2536)
- LockHunter.exe (PID: 976)
- LockHunter.exe (PID: 3744)
SUSPICIOUS
Checks supported languages
- lockhuntersetup_3-4-3.exe (PID: 3520)
- lockhuntersetup_3-4-3.tmp (PID: 3160)
- lockhuntersetup_3-4-3.exe (PID: 2920)
- lockhuntersetup_3-4-3.tmp (PID: 3280)
- LockHunter.exe (PID: 2536)
- LockHunter.exe (PID: 976)
Drops a file with a compile date too recent
- lockhuntersetup_3-4-3.exe (PID: 2920)
- lockhuntersetup_3-4-3.exe (PID: 3520)
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Executable content was dropped or overwritten
- lockhuntersetup_3-4-3.exe (PID: 3520)
- lockhuntersetup_3-4-3.exe (PID: 2920)
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Reads the computer name
- lockhuntersetup_3-4-3.tmp (PID: 3160)
- lockhuntersetup_3-4-3.tmp (PID: 3280)
- LockHunter.exe (PID: 2536)
- LockHunter.exe (PID: 976)
Reads Windows owner or organization settings
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Reads the Windows organization settings
- lockhuntersetup_3-4-3.tmp (PID: 3280)
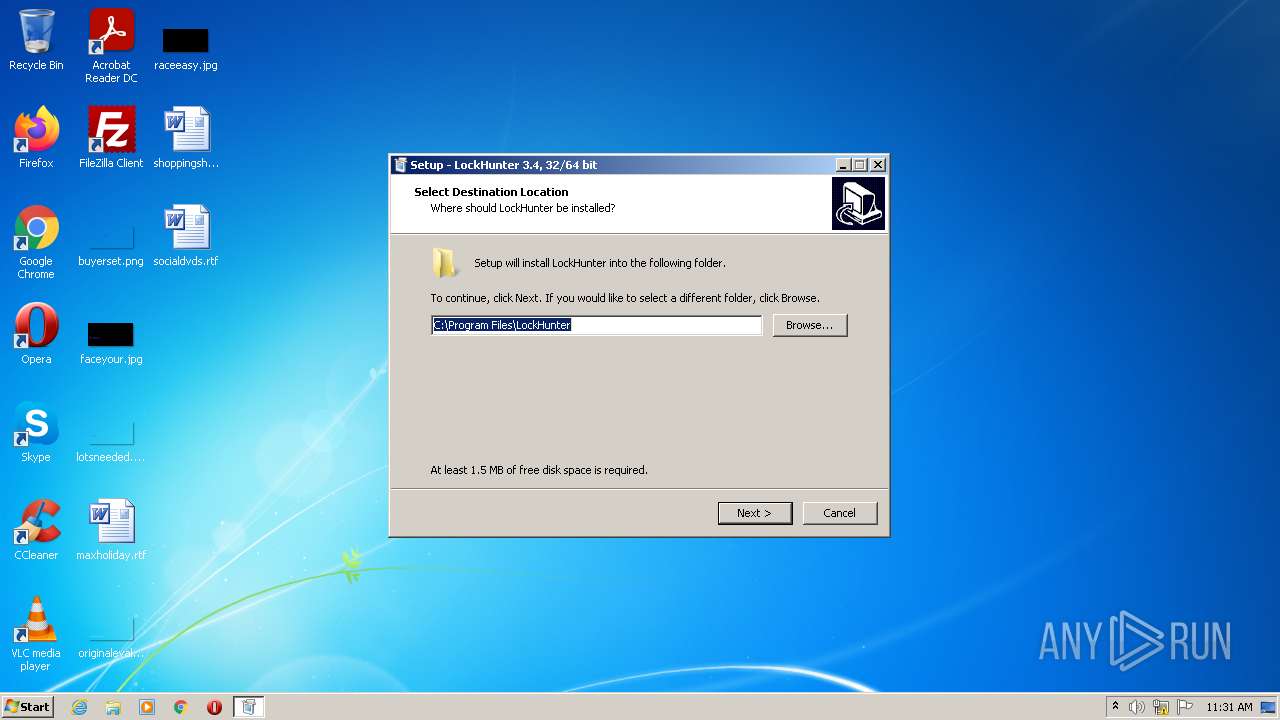
Creates a directory in Program Files
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2516)
Creates files in the user directory
- LockHunter.exe (PID: 2536)
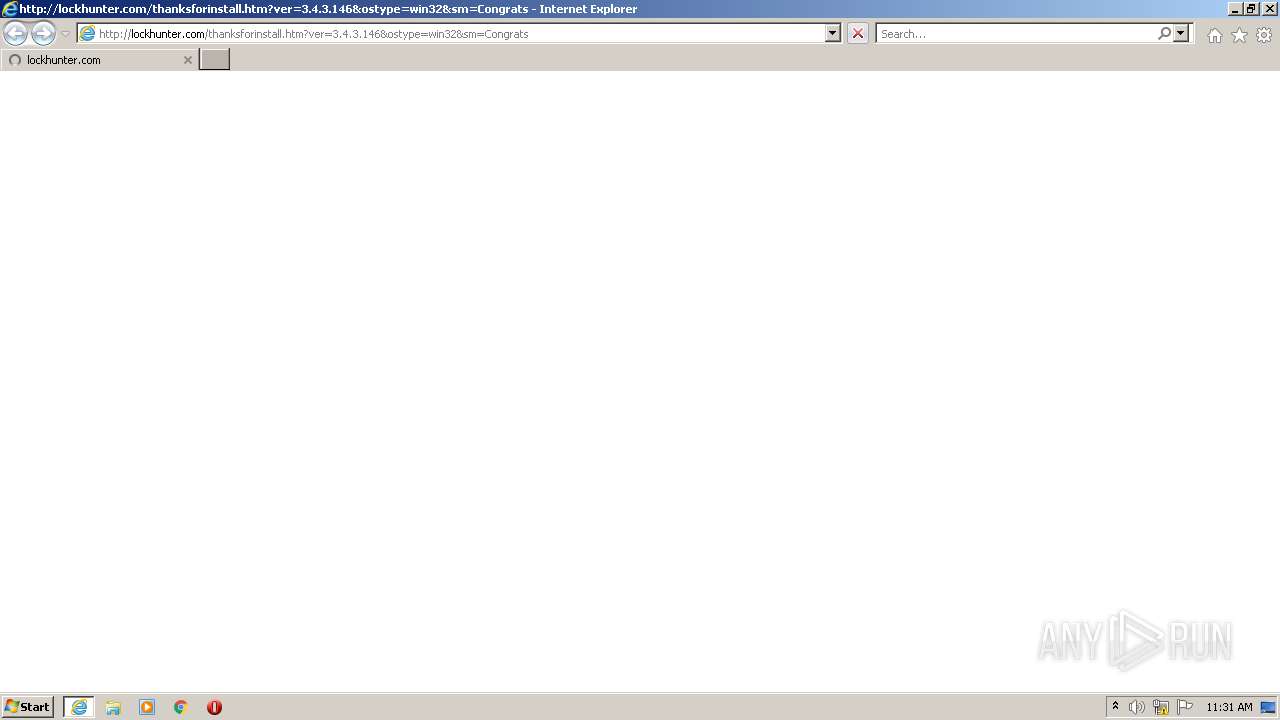
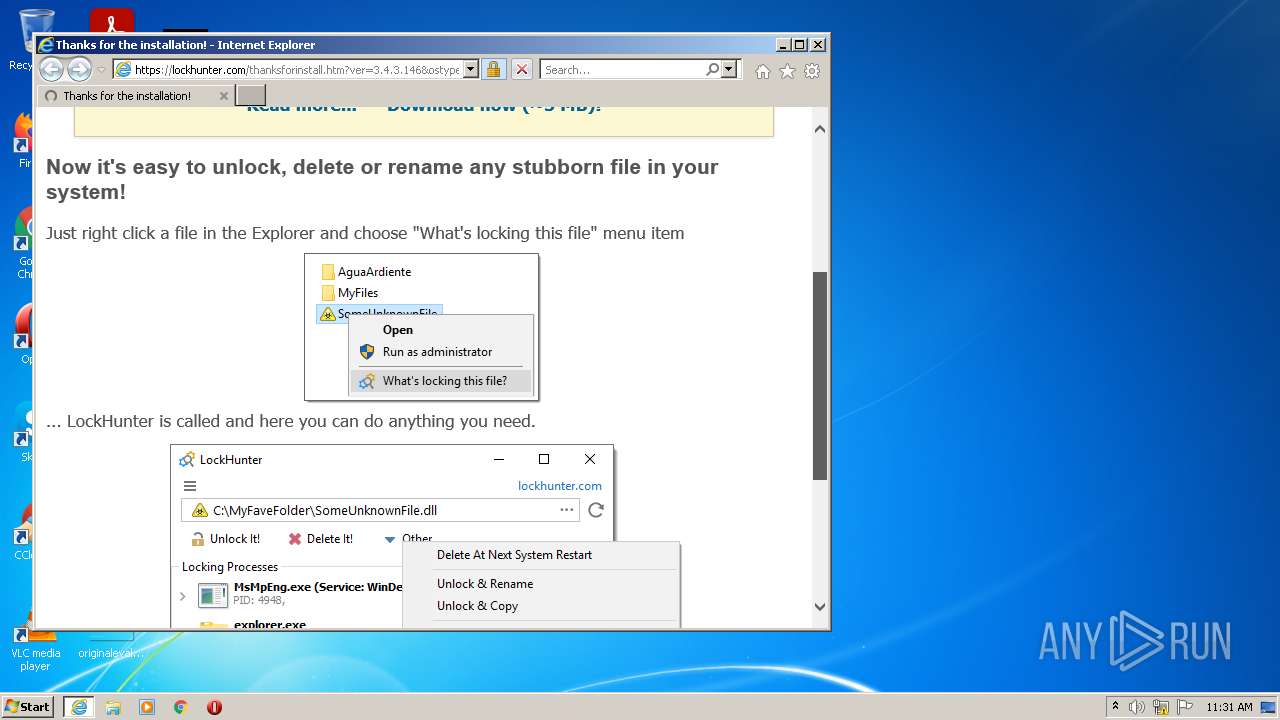
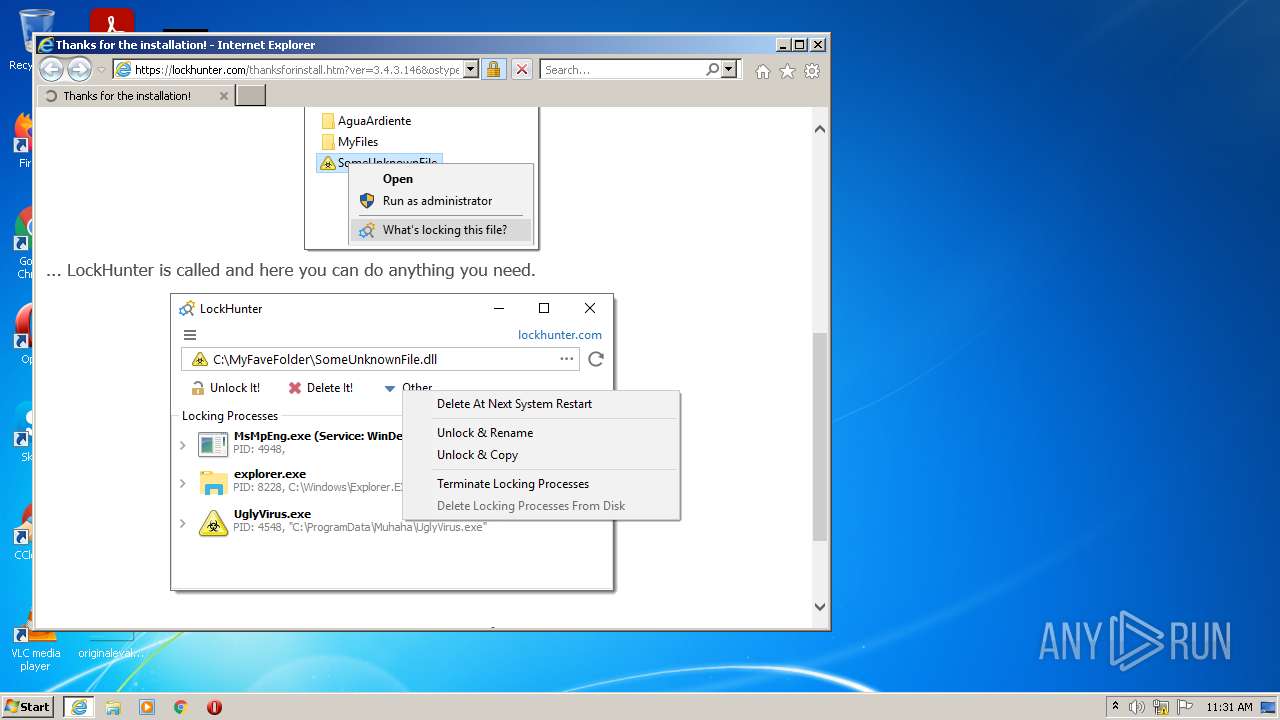
Starts Internet Explorer
- LockHunter.exe (PID: 2536)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3748)
Reads default file associations for system extensions
- Explorer.EXE (PID: 1376)
Application launched itself
- LockHunter.exe (PID: 976)
INFO
Application was dropped or rewritten from another process
- lockhuntersetup_3-4-3.tmp (PID: 3160)
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Creates files in the program directory
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Checks supported languages
- regsvr32.exe (PID: 2516)
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 3748)
- explorer.exe (PID: 1564)
- consent.exe (PID: 1224)
Creates a software uninstall entry
- lockhuntersetup_3-4-3.tmp (PID: 3280)
Reads the computer name
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 3748)
- explorer.exe (PID: 1564)
- consent.exe (PID: 1224)
Changes internet zones settings
- iexplore.exe (PID: 3040)
Application launched itself
- iexplore.exe (PID: 3040)
Checks Windows Trust Settings
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3040)
- consent.exe (PID: 1224)
Reads settings of System Certificates
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3040)
- consent.exe (PID: 1224)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3748)
Changes settings of System certificates
- iexplore.exe (PID: 3748)
Reads internet explorer settings
- iexplore.exe (PID: 3748)
Reads the date of Windows installation
- iexplore.exe (PID: 3040)
Manual execution by user
- explorer.exe (PID: 1564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| ProductVersion: | 3.4.3.146 |
|---|---|
| ProductName: | LockHunter |
| LegalCopyright: | |
| FileVersion: | 3.4.3.146 |
| FileDescription: | LockHunter Setup |
| CompanyName: | Crystal Rich Ltd |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.4.3.146 |
| FileVersionNumber: | 3.4.3.146 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x1181c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 151040 |
| CodeSize: | 66560 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Crystal Rich Ltd |
| FileDescription: | LockHunter Setup |
| FileVersion: | 3.4.3.146 |
| LegalCopyright: | - |
| ProductName: | LockHunter |
| ProductVersion: | 3.4.3.146 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00022C70 | 0x00022E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.7642 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.43851 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.76159 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.7613 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.33777 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.74877 | 13143 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.2097 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.98743 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.18146 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.8259 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
54
Monitored processes
15
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
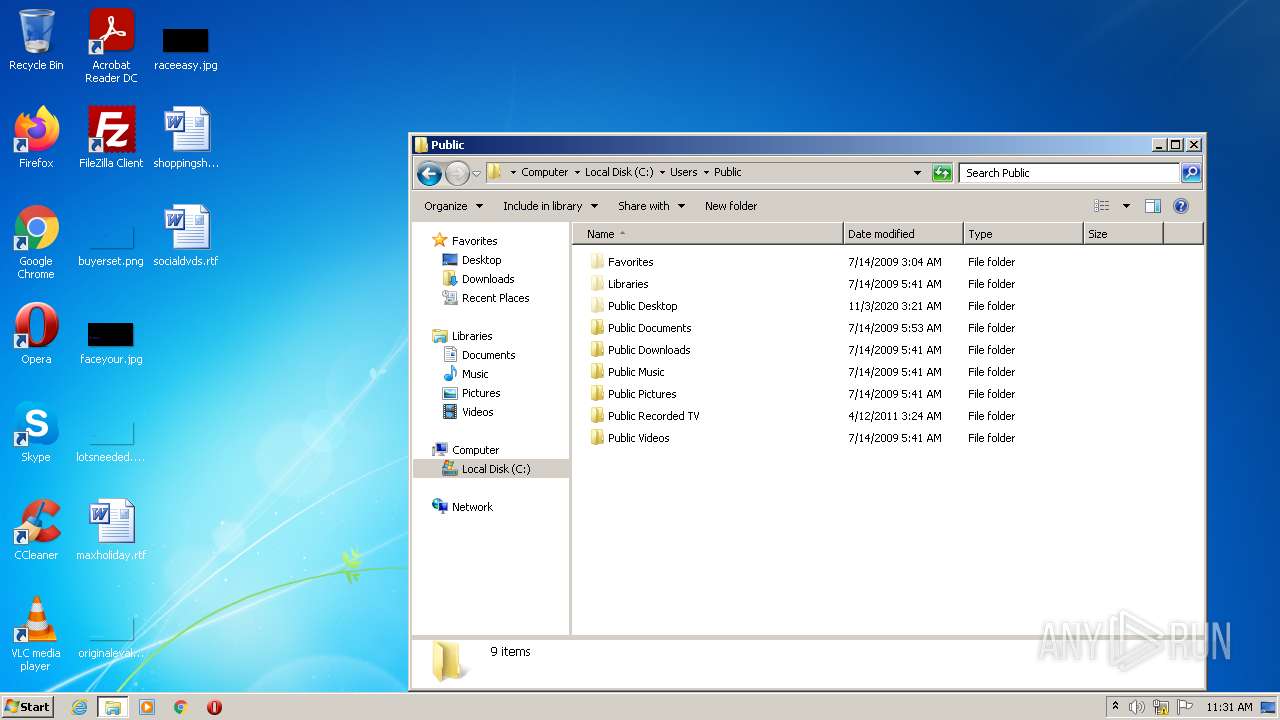
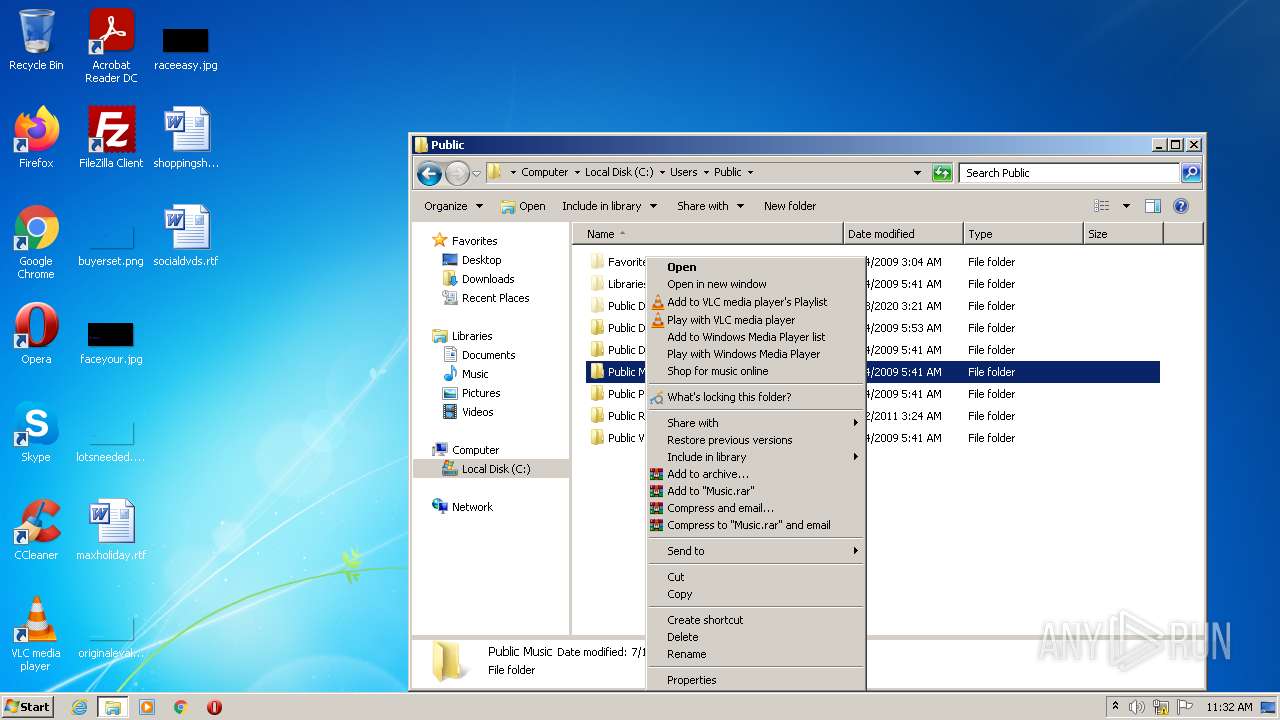
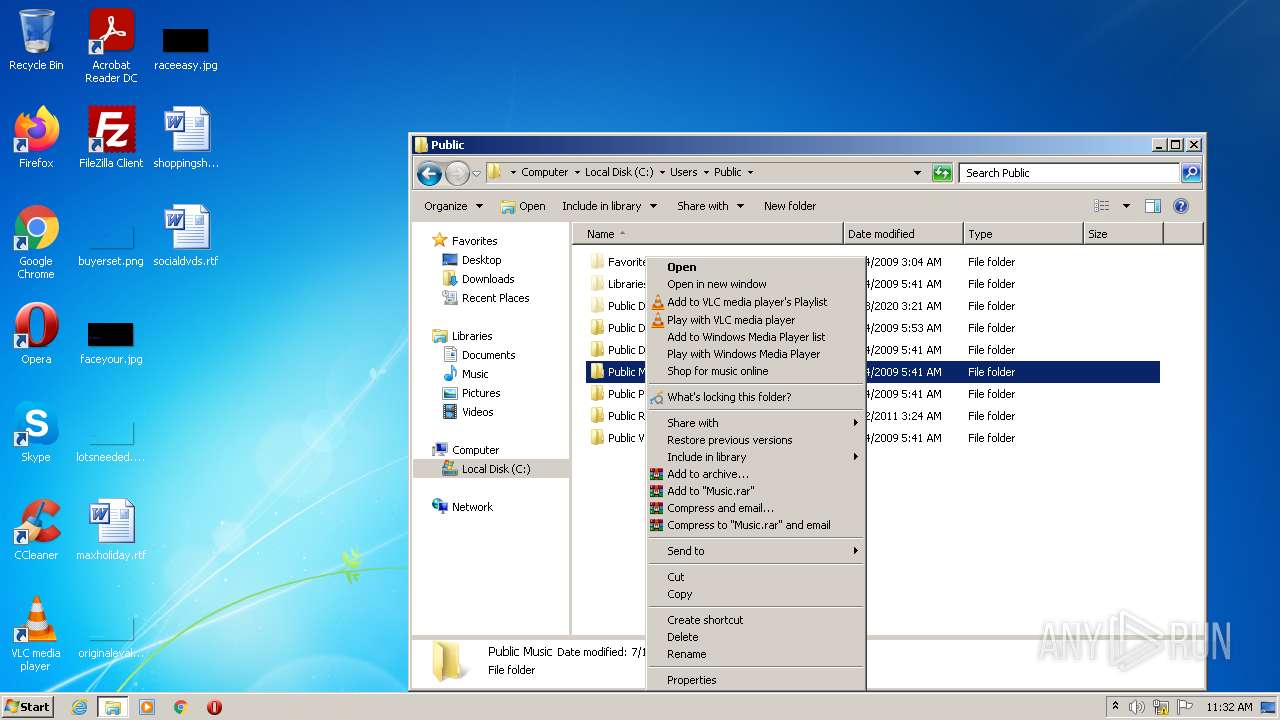
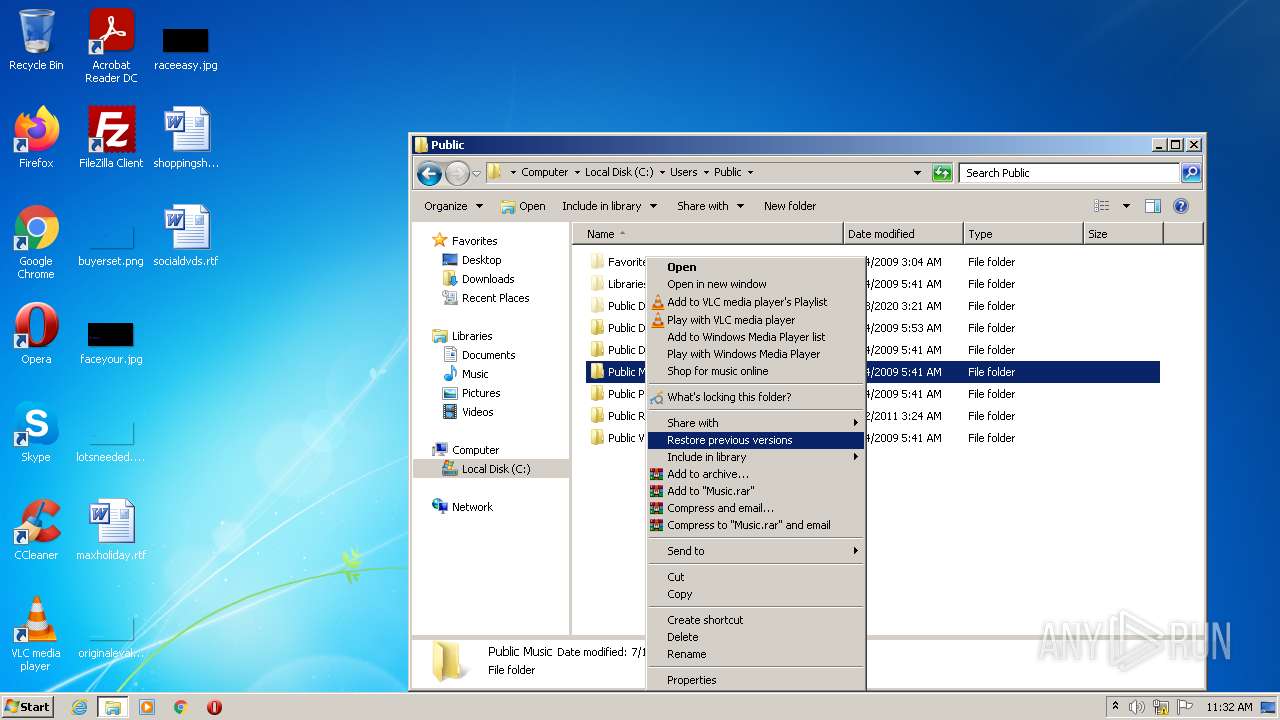
| 976 | "C:\Program Files\LockHunter\LockHunter.exe" "C:\Users\Public\Music" | C:\Program Files\LockHunter\LockHunter.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Crystal Rich Ltd Integrity Level: MEDIUM Description: LockHunter - a foolproof file unlocker Exit code: 0 Version: 3.4.3.146 Modules
| |||||||||||||||
| 1224 | consent.exe 860 426 023F8B20 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1376 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1564 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\LockHunter\LHShellExt32.dll" | C:\Windows\system32\regsvr32.exe | — | lockhuntersetup_3-4-3.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2536 | "C:\Program Files\LockHunter\LockHunter.exe" -thanksforinstall | C:\Program Files\LockHunter\LockHunter.exe | — | lockhuntersetup_3-4-3.tmp | |||||||||||
User: admin Company: Crystal Rich Ltd Integrity Level: HIGH Description: LockHunter - a foolproof file unlocker Exit code: 0 Version: 3.4.3.146 Modules
| |||||||||||||||
| 2920 | "C:\Users\admin\AppData\Local\Temp\lockhuntersetup_3-4-3.exe" | C:\Users\admin\AppData\Local\Temp\lockhuntersetup_3-4-3.exe | Explorer.EXE | ||||||||||||
User: admin Company: Crystal Rich Ltd Integrity Level: MEDIUM Description: LockHunter Setup Exit code: 0 Version: 3.4.3.146 Modules
| |||||||||||||||
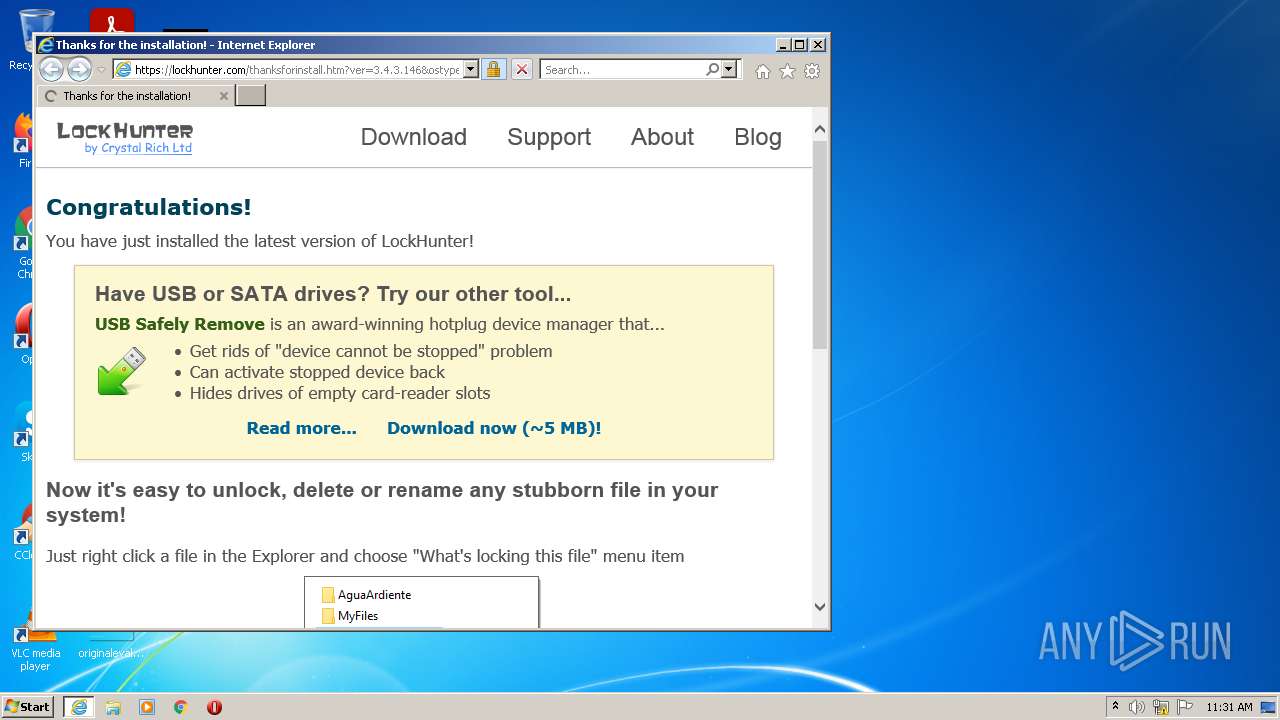
| 3040 | "C:\Program Files\Internet Explorer\iexplore.exe" http://lockhunter.com/thanksforinstall.htm?ver=3.4.3.146&ostype=win32&sm=Congrats | C:\Program Files\Internet Explorer\iexplore.exe | LockHunter.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\AppData\Local\Temp\is-GVDJ4.tmp\lockhuntersetup_3-4-3.tmp" /SL5="$20138,2872040,218624,C:\Users\admin\AppData\Local\Temp\lockhuntersetup_3-4-3.exe" | C:\Users\admin\AppData\Local\Temp\is-GVDJ4.tmp\lockhuntersetup_3-4-3.tmp | — | lockhuntersetup_3-4-3.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
24 810
Read events
24 433
Write events
373
Delete events
4
Modification events
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 2 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 1 | |||
| (PID) Process: | (1376) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1376) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | write | Name: | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\LockHunter\LockHunter.lnk |
Value: 1 | |||
| (PID) Process: | (1376) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | write | Name: | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\LockHunter\LockHunter.lnk |
Value: 1 | |||
| (PID) Process: | (1376) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3280) lockhuntersetup_3-4-3.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\LockHunter_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (u) | |||
| (PID) Process: | (3280) lockhuntersetup_3-4-3.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\LockHunter_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\LockHunter | |||
| (PID) Process: | (3280) lockhuntersetup_3-4-3.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\LockHunter_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\LockHunter\ | |||
| (PID) Process: | (3280) lockhuntersetup_3-4-3.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\LockHunter_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: LockHunter | |||
Executable files
14
Suspicious files
10
Text files
16
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3280 | lockhuntersetup_3-4-3.tmp | C:\Program Files\LockHunter\LockHunter.exe | executable | |
MD5:B32869A6AF4B306B52FC6D7AB7004695 | SHA256:AD6094A7C0B72AE972C6E2F9B8948FF9DACDAEB02EBAB1E0B69F894CB48E58E3 | |||
| 2920 | lockhuntersetup_3-4-3.exe | C:\Users\admin\AppData\Local\Temp\is-GVDJ4.tmp\lockhuntersetup_3-4-3.tmp | executable | |
MD5:62CD9C2E077D0662999413F0233E2B91 | SHA256:690A801B77922CD70FCDC8E1DBCF54F7614CFB1E7F011474D2CF9B32A58A90C2 | |||
| 3520 | lockhuntersetup_3-4-3.exe | C:\Users\admin\AppData\Local\Temp\is-BCQSH.tmp\lockhuntersetup_3-4-3.tmp | executable | |
MD5:62CD9C2E077D0662999413F0233E2B91 | SHA256:690A801B77922CD70FCDC8E1DBCF54F7614CFB1E7F011474D2CF9B32A58A90C2 | |||
| 3280 | lockhuntersetup_3-4-3.tmp | C:\Program Files\LockHunter\is-VVHDQ.tmp | executable | |
MD5:B32869A6AF4B306B52FC6D7AB7004695 | SHA256:AD6094A7C0B72AE972C6E2F9B8948FF9DACDAEB02EBAB1E0B69F894CB48E58E3 | |||
| 3280 | lockhuntersetup_3-4-3.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\LockHunter\LockHunter.lnk | lnk | |
MD5:1EB11FF8861398D12CBE8A49BCF5FC40 | SHA256:BCA3646F7C0DC01282AA6145999FE02831F1AD92D00D87ABC6F961E7C7836C41 | |||
| 3280 | lockhuntersetup_3-4-3.tmp | C:\Program Files\LockHunter\is-MHB6C.tmp | executable | |
MD5:894DF84FC1F9F4DF20B936FF56381321 | SHA256:21F1ABCE748ABFF3CFC220097A99FB4C11A54E3D042DE77AACDE1442F7E88A2F | |||
| 3280 | lockhuntersetup_3-4-3.tmp | C:\Program Files\LockHunter\unins000.exe | executable | |
MD5:894DF84FC1F9F4DF20B936FF56381321 | SHA256:21F1ABCE748ABFF3CFC220097A99FB4C11A54E3D042DE77AACDE1442F7E88A2F | |||
| 3280 | lockhuntersetup_3-4-3.tmp | C:\Program Files\LockHunter\CRDllUnload32.dll | executable | |
MD5:D8DD179683C4BD6438D63F6CCAF61482 | SHA256:3F520EADC583E20B4ED6AB4CACDA3E8AC90A6EB107F7BB417E513A7B7ED13C69 | |||
| 3280 | lockhuntersetup_3-4-3.tmp | C:\Program Files\LockHunter\LHShellExt32.dll | executable | |
MD5:D1AB06340866A08476D309E757363599 | SHA256:7B1A27A833E4A16AC54E07C1723D0E1417EFE7CE98B1C179D5DE5FCCBDB1CB66 | |||
| 3280 | lockhuntersetup_3-4-3.tmp | C:\Program Files\LockHunter\USRFindHandle32.sys | executable | |
MD5:160C21DCAE22356C4E423353A5C1CEAF | SHA256:B2FFB0E75A34E8DD36E7C908E126D99C4BD6E792457431E78D9BCC7A7ED4049E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3748 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
3748 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3748 | iexplore.exe | GET | 302 | 67.222.5.154:80 | http://lockhunter.com/thanksforinstall.htm?ver=3.4.3.146&ostype=win32&sm=Congrats | US | html | 274 b | suspicious |
3748 | iexplore.exe | GET | 200 | 8.252.42.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?61c17d3a27aee3b1 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | iexplore.exe | 67.222.5.154:80 | lockhunter.com | PrivateSystems Networks | US | suspicious |
3748 | iexplore.exe | 67.222.5.154:443 | lockhunter.com | PrivateSystems Networks | US | suspicious |
3748 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3748 | iexplore.exe | 8.252.42.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3040 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3040 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | iexplore.exe | 172.217.18.8:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
3748 | iexplore.exe | 142.250.185.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3748 | iexplore.exe | 142.250.185.163:80 | crl.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lockhunter.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crl.pki.goog |
| whitelisted |