| URL: | https://slack.com/downloads/windows |
| Full analysis: | https://app.any.run/tasks/657b2c0e-38f2-4e80-b7a1-86bd02705daa |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 21:23:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C3475A0D4A00B3ED8E2BED19818994D8 |
| SHA1: | 82E658DAE04A0AE1404F2B679954228C2D3A1248 |
| SHA256: | 9814DE1E30932DBAE8ABB4F79803196A924F20E417EBCC65108F10BB6BE14BDC |
| SSDEEP: | 3:N8EvkdIBXK/1Kl:2EMKBaIl |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2412)
- SlackSetup.exe (PID: 976)
- Update.exe (PID: 3076)
Application was dropped or rewritten from another process
- SlackSetup.exe (PID: 976)
- Update.exe (PID: 3076)
- Squirrel.exe (PID: 3192)
- update.exe (PID: 3888)
Loads dropped or rewritten executable
- slack.exe (PID: 2092)
- slack.exe (PID: 1464)
- slack.exe (PID: 2280)
- slack.exe (PID: 4068)
- slack.exe (PID: 2528)
- slack.exe (PID: 3936)
- slack.exe (PID: 3260)
- slack.exe (PID: 3296)
- slack.exe (PID: 1592)
- slack.exe (PID: 3336)
Changes the autorun value in the registry
- slack.exe (PID: 2092)
- slack.exe (PID: 2280)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2340)
- chrome.exe (PID: 1644)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2412)
Executable content was dropped or overwritten
- chrome.exe (PID: 2412)
- SlackSetup.exe (PID: 976)
- Update.exe (PID: 3076)
Drops a file with a compile date too recent
- chrome.exe (PID: 2412)
- Update.exe (PID: 3076)
- SlackSetup.exe (PID: 976)
Checks supported languages
- SlackSetup.exe (PID: 976)
- Update.exe (PID: 3076)
- Squirrel.exe (PID: 3192)
- slack.exe (PID: 2092)
- slack.exe (PID: 1464)
- update.exe (PID: 3888)
- slack.exe (PID: 2280)
- slack.exe (PID: 4068)
- slack.exe (PID: 3936)
- slack.exe (PID: 2528)
- slack.exe (PID: 3296)
- slack.exe (PID: 3260)
- slack.exe (PID: 1592)
- slack.exe (PID: 3336)
Reads the computer name
- Update.exe (PID: 3076)
- Squirrel.exe (PID: 3192)
- slack.exe (PID: 2092)
- update.exe (PID: 3888)
- slack.exe (PID: 1464)
- slack.exe (PID: 2280)
- slack.exe (PID: 3936)
- slack.exe (PID: 2528)
- slack.exe (PID: 3260)
- slack.exe (PID: 1592)
Reads Environment values
- slack.exe (PID: 2092)
- slack.exe (PID: 2280)
- Update.exe (PID: 3076)
Creates files in the user directory
- slack.exe (PID: 2092)
- update.exe (PID: 3888)
- slack.exe (PID: 2280)
- slack.exe (PID: 4068)
- slack.exe (PID: 2528)
Application launched itself
- slack.exe (PID: 2092)
- slack.exe (PID: 2280)
Reads CPU info
- slack.exe (PID: 2280)
Changes default file association
- slack.exe (PID: 2280)
Creates a software uninstall entry
- Update.exe (PID: 3076)
INFO
Reads the computer name
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 2340)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 1724)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2200)
- WISPTIS.EXE (PID: 2388)
- chrome.exe (PID: 3076)
Checks supported languages
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 2340)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 124)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 1724)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 1192)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 3736)
- WISPTIS.EXE (PID: 2388)
- chrome.exe (PID: 1912)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 2012)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 3252)
Changes internet zones settings
- iexplore.exe (PID: 3040)
Application launched itself
- iexplore.exe (PID: 3040)
- chrome.exe (PID: 2412)
Reads the hosts file
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3132)
- slack.exe (PID: 2092)
- slack.exe (PID: 2280)
- slack.exe (PID: 2528)
Manual execution by user
- chrome.exe (PID: 2412)
Reads settings of System Certificates
- chrome.exe (PID: 3132)
- iexplore.exe (PID: 2340)
- chrome.exe (PID: 2412)
- iexplore.exe (PID: 3040)
- slack.exe (PID: 2280)
- Update.exe (PID: 3076)
Checks Windows Trust Settings
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 3040)
- chrome.exe (PID: 2412)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2412)
- Update.exe (PID: 3076)
Creates files in the user directory
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 3040)
Reads the date of Windows installation
- chrome.exe (PID: 1724)
Changes settings of System certificates
- iexplore.exe (PID: 3040)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3040)
Reads internet explorer settings
- iexplore.exe (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
57
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1012,2375214874709432018,5304088623510522056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2848 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
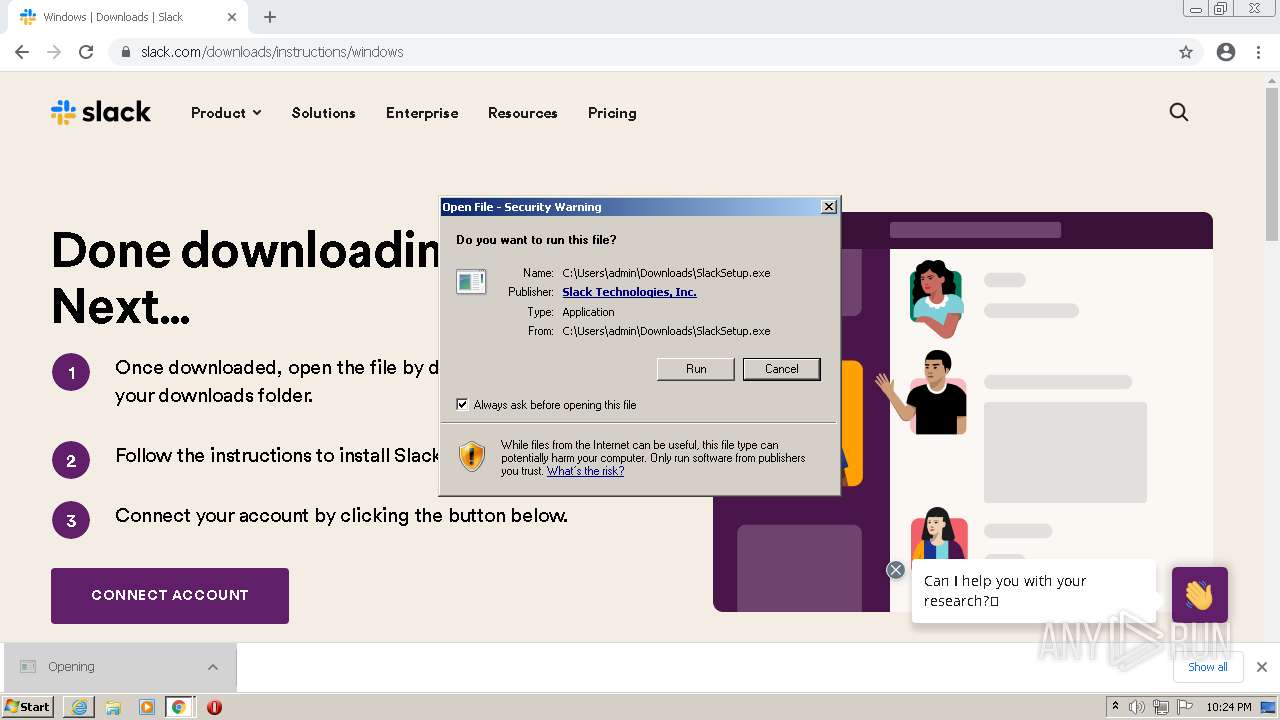
| 976 | "C:\Users\admin\Downloads\SlackSetup.exe" | C:\Users\admin\Downloads\SlackSetup.exe | chrome.exe | ||||||||||||
User: admin Company: Slack Technologies Inc. Integrity Level: MEDIUM Description: Slack Desktop Exit code: 0 Version: 4.28.184 Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1012,2375214874709432018,5304088623510522056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1040 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1368 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\AppData\Local\slack\app-4.28.184\slack.exe" --type=gpu-process --enable-logging --user-data-dir="C:\Users\admin\AppData\Roaming\Slack" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --enable-logging --log-file="C:\Users\admin\AppData\Roaming\Slack\logs\default\electron_debug.log" --mojo-platform-channel-handle=984 --field-trial-handle=1036,i,11755146242601792603,7350312972439423231,131072 --disable-features=AllowAggressiveThrottlingWithWebSocket,CalculateNativeWinOcclusion,HardwareMediaKeyHandling,IntensiveWakeUpThrottling,LogJsConsoleMessages,RequestInitiatorSiteLockEnfocement,SpareRendererForSitePerProcess,WebRtcHideLocalIpsWithMdns,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\slack\app-4.28.184\slack.exe | — | slack.exe | |||||||||||
User: admin Company: Slack Technologies Inc. Integrity Level: LOW Description: Slack Exit code: 0 Version: 4.28.184 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f42d988,0x6f42d998,0x6f42d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1592 | "C:\Users\admin\AppData\Local\slack\app-4.28.184\slack.exe" --type=gpu-process --enable-logging --user-data-dir="C:\Users\admin\AppData\Roaming\Slack" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --enable-logging --log-file="C:\Users\admin\AppData\Roaming\Slack\logs\default\electron_debug.log" --mojo-platform-channel-handle=1900 --field-trial-handle=1092,i,2853299885008617178,4417654437623939887,131072 --disable-features=AllowAggressiveThrottlingWithWebSocket,CalculateNativeWinOcclusion,HardwareMediaKeyHandling,IntensiveWakeUpThrottling,LogJsConsoleMessages,RequestInitiatorSiteLockEnfocement,SpareRendererForSitePerProcess,WebRtcHideLocalIpsWithMdns,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\slack\app-4.28.184\slack.exe | — | slack.exe | |||||||||||
User: admin Company: Slack Technologies Inc. Integrity Level: LOW Description: Slack Exit code: 0 Version: 4.28.184 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1012,2375214874709432018,5304088623510522056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4432 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1012,2375214874709432018,5304088623510522056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3144 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,2375214874709432018,5304088623510522056,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
58 307
Read events
57 862
Write events
433
Delete events
12
Modification events
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988343 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988343 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
97
Suspicious files
297
Text files
321
Unknown types
124
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633CA44E-96C.pma | — | |
MD5:— | SHA256:— | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4cf9b18f-f35d-4a2a-a3e2-9261b4fc8718.tmp | text | |
MD5:— | SHA256:— | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\61c2aa06-065d-41f6-8ca0-d7feabe72e6c.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_1 | vxd | |
MD5:259E7ED5FB3C6C90533B963DA5B2FC1B | SHA256:35BB2F189C643DCF52ECF037603D104035ECDC490BF059B7736E58EF7D821A09 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF136871.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
304
DNS requests
150
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3132 | chrome.exe | GET | — | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?da25d2901b12a693 | US | — | — | whitelisted |
3132 | chrome.exe | GET | — | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9a13d97735fa828b | US | — | — | whitelisted |
2340 | iexplore.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | — | — | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
3132 | chrome.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2340 | iexplore.exe | GET | 200 | 99.86.1.61:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAvnhX%2FmVhH670%2FVKk6vh5E%3D | US | der | 471 b | whitelisted |
2340 | iexplore.exe | GET | 200 | 65.9.58.231:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3132 | chrome.exe | GET | 200 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5ee1c7392ba449f8 | US | compressed | 4.70 Kb | whitelisted |
3132 | chrome.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | iexplore.exe | 3.68.124.168:443 | slack.com | AMAZON-02 | DE | unknown |
— | — | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3132 | chrome.exe | 142.250.187.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
3132 | chrome.exe | 172.217.16.206:443 | apis.google.com | GOOGLE | US | whitelisted |
3132 | chrome.exe | 104.18.41.98:443 | geolocation.onetrust.com | CLOUDFLARENET | — | shared |
3132 | chrome.exe | 104.16.149.64:443 | cdn.cookielaw.org | CLOUDFLARENET | — | unknown |
3132 | chrome.exe | 96.16.142.89:443 | cdn3.optimizely.com | AKAMAI-AS | DE | unknown |
3132 | chrome.exe | 142.250.185.106:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
3132 | chrome.exe | 23.206.209.10:443 | a11179690159.cdn.optimizely.com | AKAMAI-AS | DE | suspicious |
3132 | chrome.exe | 142.250.186.45:443 | accounts.google.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
slack.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |